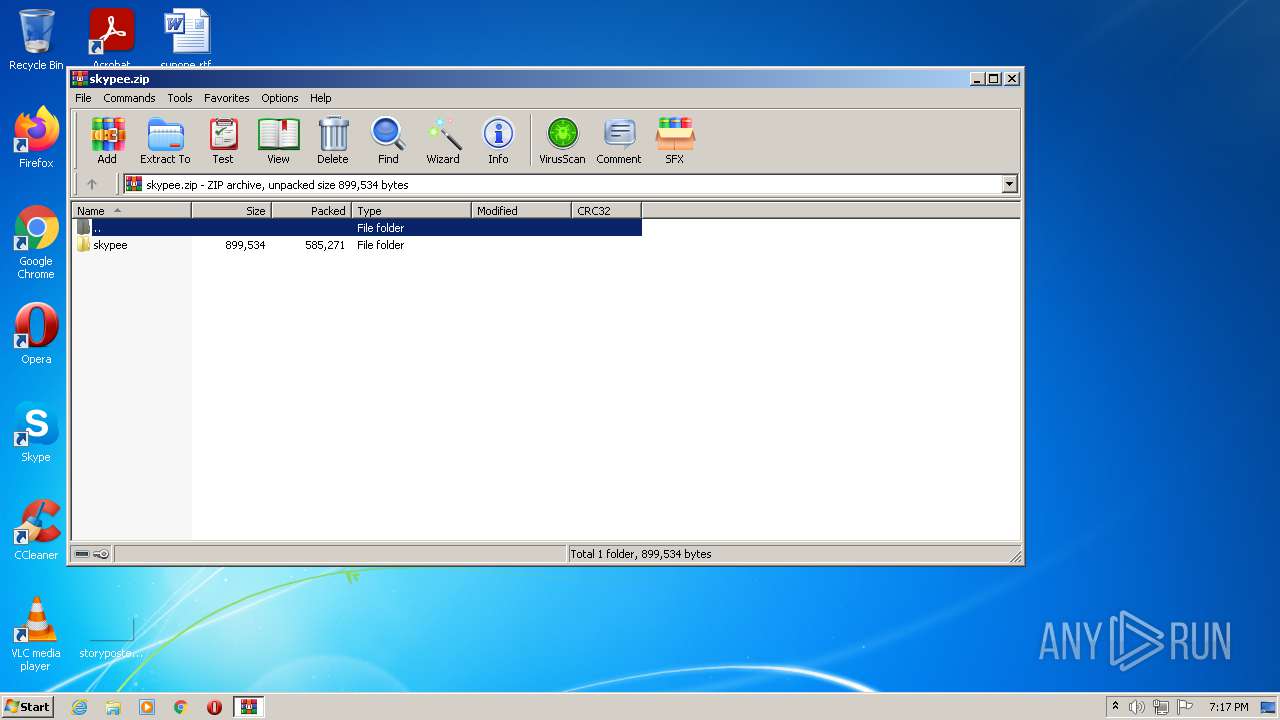
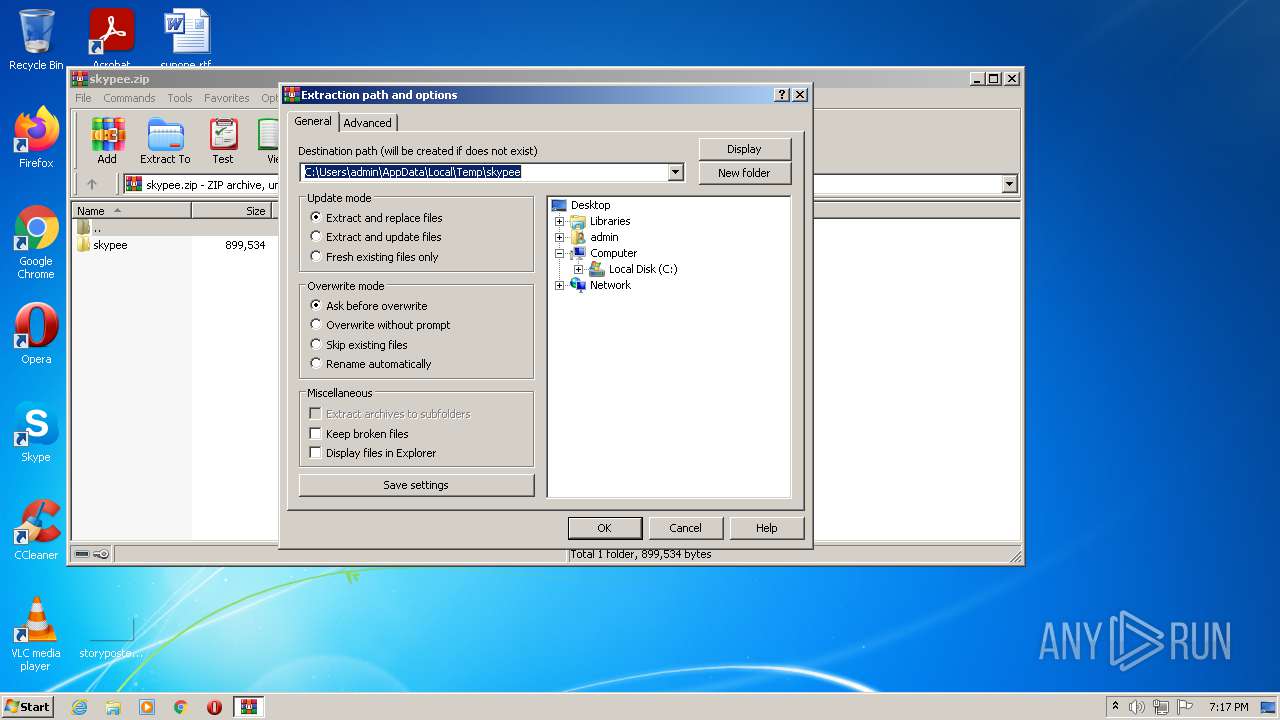
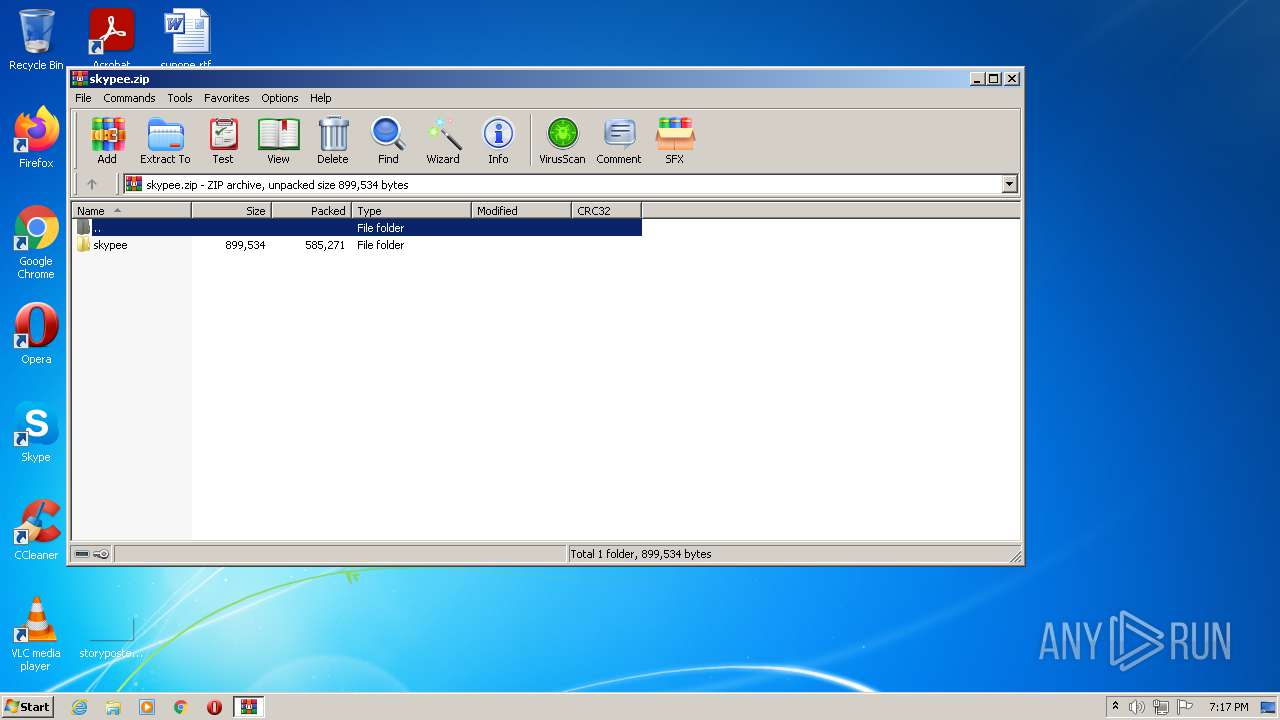
| File name: | skypee.zip |
| Full analysis: | https://app.any.run/tasks/e8f7cb59-34d2-42ef-843b-7bb0a54e1ec9 |
| Verdict: | Malicious activity |
| Analysis date: | August 24, 2021, 18:17:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | BE6B84BACB572066A23B79F28BF350C0 |
| SHA1: | 299E4A8BE5D48EF40E2161B22F323E79DD9D6F89 |
| SHA256: | 028DE5BC58FEF53BCF1AE70F1C2A8B624275FD3106EF3A2E54D16D25C37A0E21 |
| SSDEEP: | 12288:tJXhfE7Ogrp5lzSmx6jxe09WgPneUqIy+Q9ph6+2h:tJXZWzrvlzSmxngmH2Q992h |
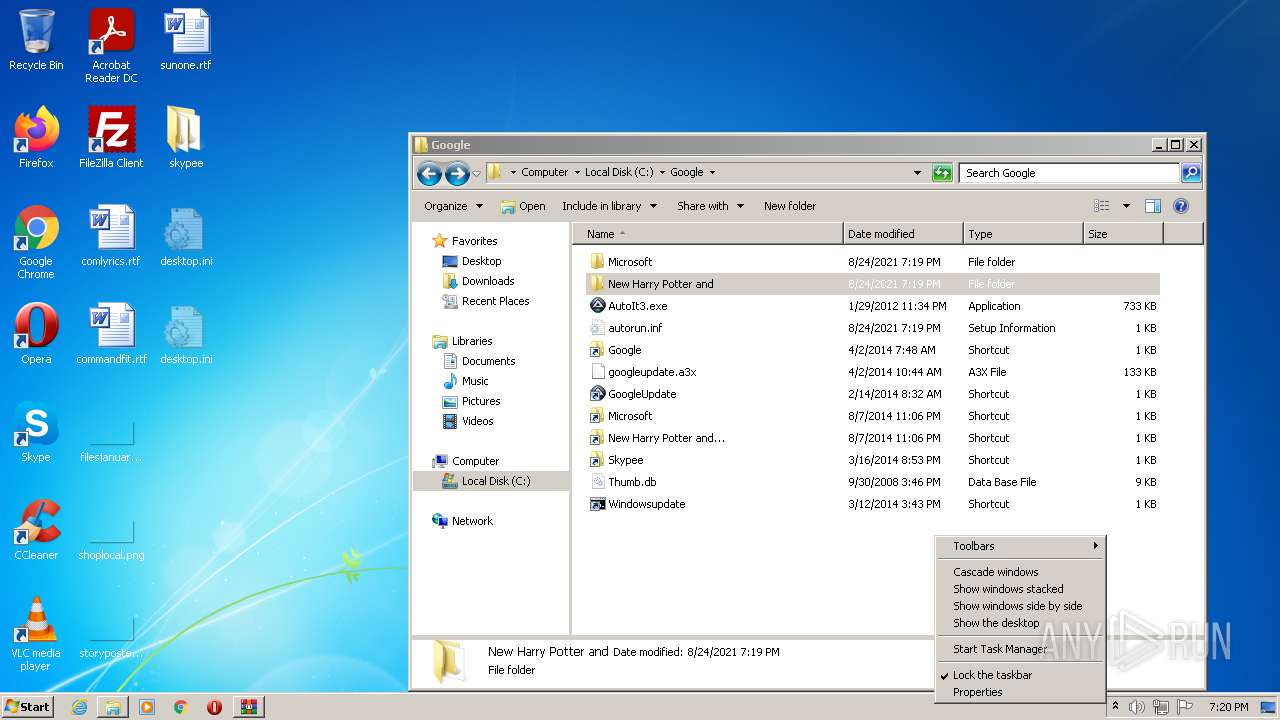
MALICIOUS
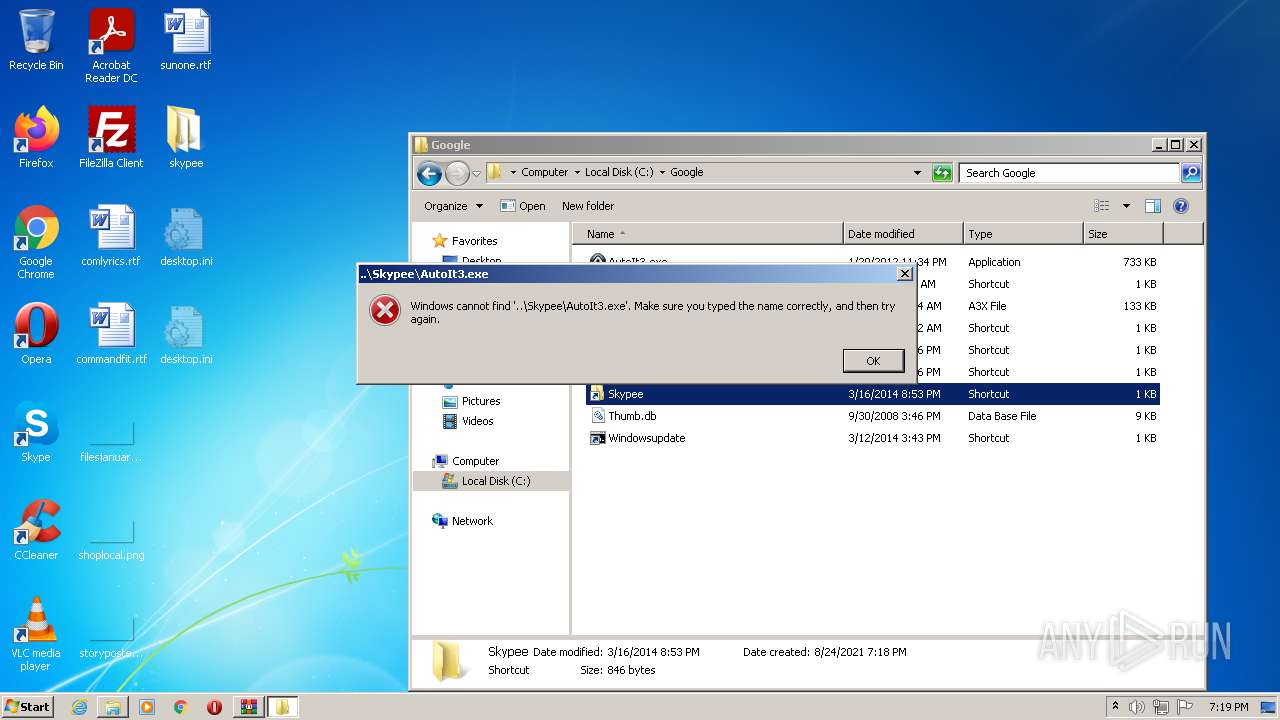
Application was dropped or rewritten from another process
- AutoIt3.exe (PID: 3064)
- AutoIt3.exe (PID: 1956)
- AutoIt3.exe (PID: 3308)
- AutoIt3.exe (PID: 2436)
- AutoIt3.exe (PID: 2856)
Changes the autorun value in the registry
- AutoIt3.exe (PID: 1956)
- wscript.exe (PID: 2824)
- wscript.exe (PID: 3656)
- wscript.exe (PID: 1888)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 3928)
- AutoIt3.exe (PID: 3064)
- AutoIt3.exe (PID: 1956)
- AutoIt3.exe (PID: 3308)
- AutoIt3.exe (PID: 2436)
- wscript.exe (PID: 2016)
- wscript.exe (PID: 2824)
- cmd.exe (PID: 1656)
- wscript.exe (PID: 3656)
- AutoIt3.exe (PID: 2856)
- wscript.exe (PID: 744)
- wscript.exe (PID: 1888)
- wscript.exe (PID: 996)
Checks supported languages
- WinRAR.exe (PID: 3928)
- cmd.exe (PID: 2540)
- AutoIt3.exe (PID: 3064)
- cmd.exe (PID: 3932)
- AutoIt3.exe (PID: 1956)
- cmd.exe (PID: 2892)
- AutoIt3.exe (PID: 3308)
- cmd.exe (PID: 1636)
- cmd.exe (PID: 3960)
- AutoIt3.exe (PID: 2436)
- wscript.exe (PID: 2824)
- cmd.exe (PID: 1656)
- wscript.exe (PID: 2016)
- wscript.exe (PID: 3656)
- AutoIt3.exe (PID: 2856)
- wscript.exe (PID: 744)
- wscript.exe (PID: 1888)
- wscript.exe (PID: 996)
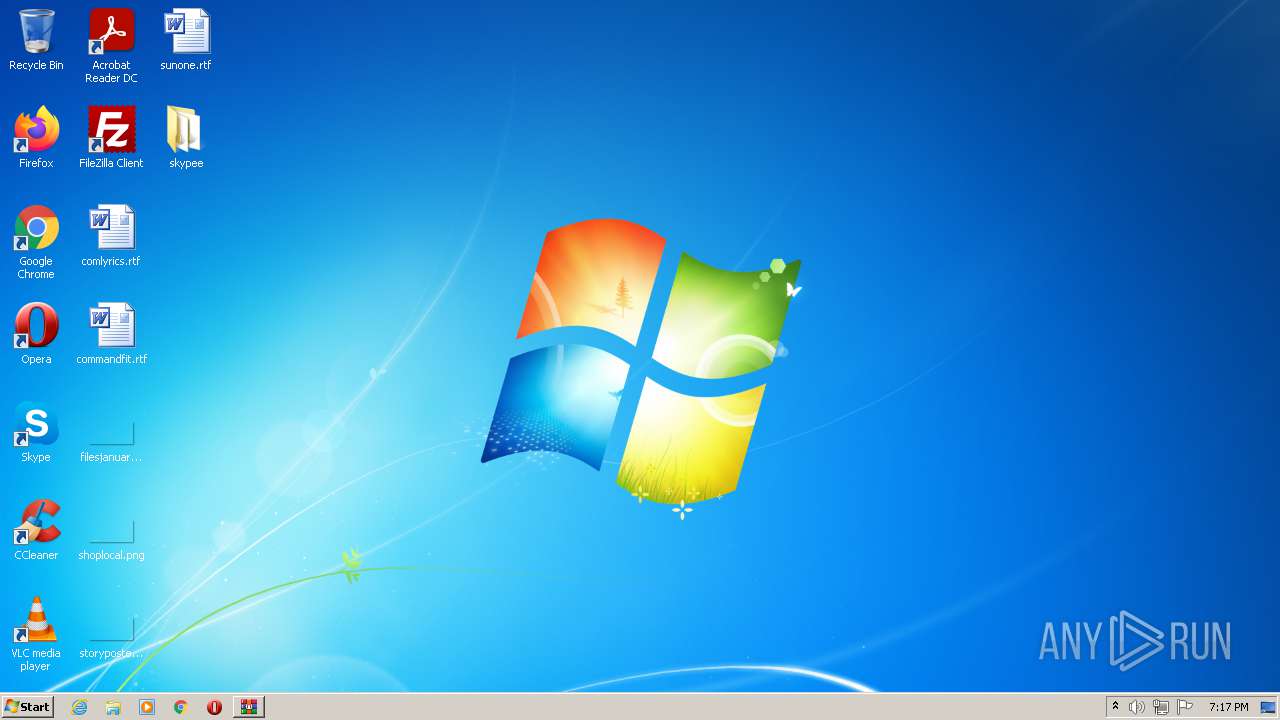
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3928)
- AutoIt3.exe (PID: 3064)
- AutoIt3.exe (PID: 1956)
Reads mouse settings
- AutoIt3.exe (PID: 3064)
- AutoIt3.exe (PID: 1956)
- AutoIt3.exe (PID: 3308)
- AutoIt3.exe (PID: 2436)
- AutoIt3.exe (PID: 2856)
Drop AutoIt3 executable file
- WinRAR.exe (PID: 3928)
- AutoIt3.exe (PID: 3064)
- AutoIt3.exe (PID: 1956)
Uses SYSTEMINFO.EXE to read environment
- cmd.exe (PID: 3932)
- cmd.exe (PID: 1636)
Starts CMD.EXE for commands execution
- AutoIt3.exe (PID: 3064)
- AutoIt3.exe (PID: 1956)
Starts itself from another location
- AutoIt3.exe (PID: 3064)
Application launched itself
- wscript.exe (PID: 2016)
- wscript.exe (PID: 744)
- wscript.exe (PID: 996)
- taskmgr.exe (PID: 1660)
Executes scripts
- wscript.exe (PID: 2016)
- wscript.exe (PID: 744)
- wscript.exe (PID: 996)
Creates files in the program directory
- wscript.exe (PID: 2824)
- AutoIt3.exe (PID: 1956)
- wscript.exe (PID: 3656)
Creates files in the Windows directory
- wscript.exe (PID: 3656)
- wscript.exe (PID: 2824)
Reads the date of Windows installation
- rundll32.exe (PID: 3940)
INFO
Manual execution by user
- cmd.exe (PID: 2540)
- cmd.exe (PID: 3960)
- wscript.exe (PID: 2016)
- cmd.exe (PID: 1656)
- AutoIt3.exe (PID: 2856)
- wscript.exe (PID: 996)
- wscript.exe (PID: 744)
- taskmgr.exe (PID: 1660)
- rundll32.exe (PID: 3940)
Checks supported languages
- systeminfo.exe (PID: 3164)
- systeminfo.exe (PID: 3092)
- taskmgr.exe (PID: 1660)
- taskmgr.exe (PID: 2936)
- NOTEPAD.EXE (PID: 4084)
- rundll32.exe (PID: 3940)
Reads the computer name
- systeminfo.exe (PID: 3164)
- systeminfo.exe (PID: 3092)
- taskmgr.exe (PID: 1660)
- taskmgr.exe (PID: 2936)
- rundll32.exe (PID: 3940)
Checks Windows Trust Settings
- wscript.exe (PID: 2016)
- wscript.exe (PID: 2824)
- wscript.exe (PID: 3656)
- wscript.exe (PID: 744)
- wscript.exe (PID: 996)
- wscript.exe (PID: 1888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
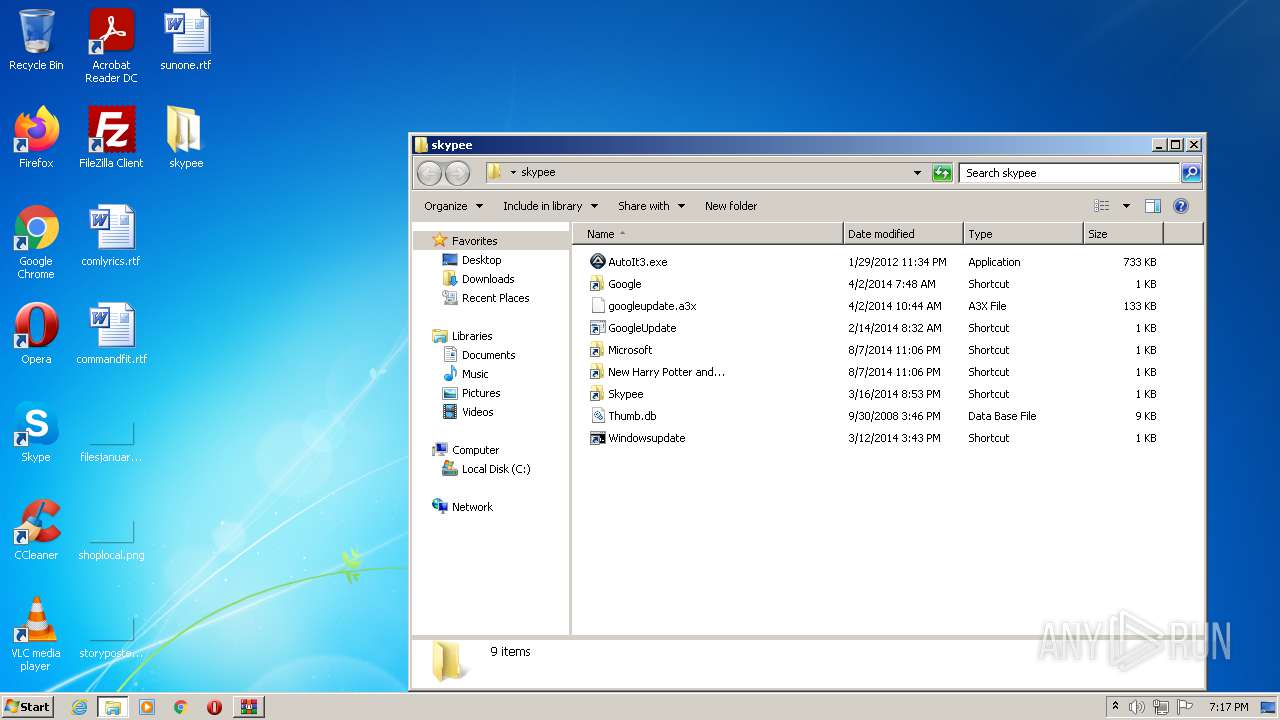
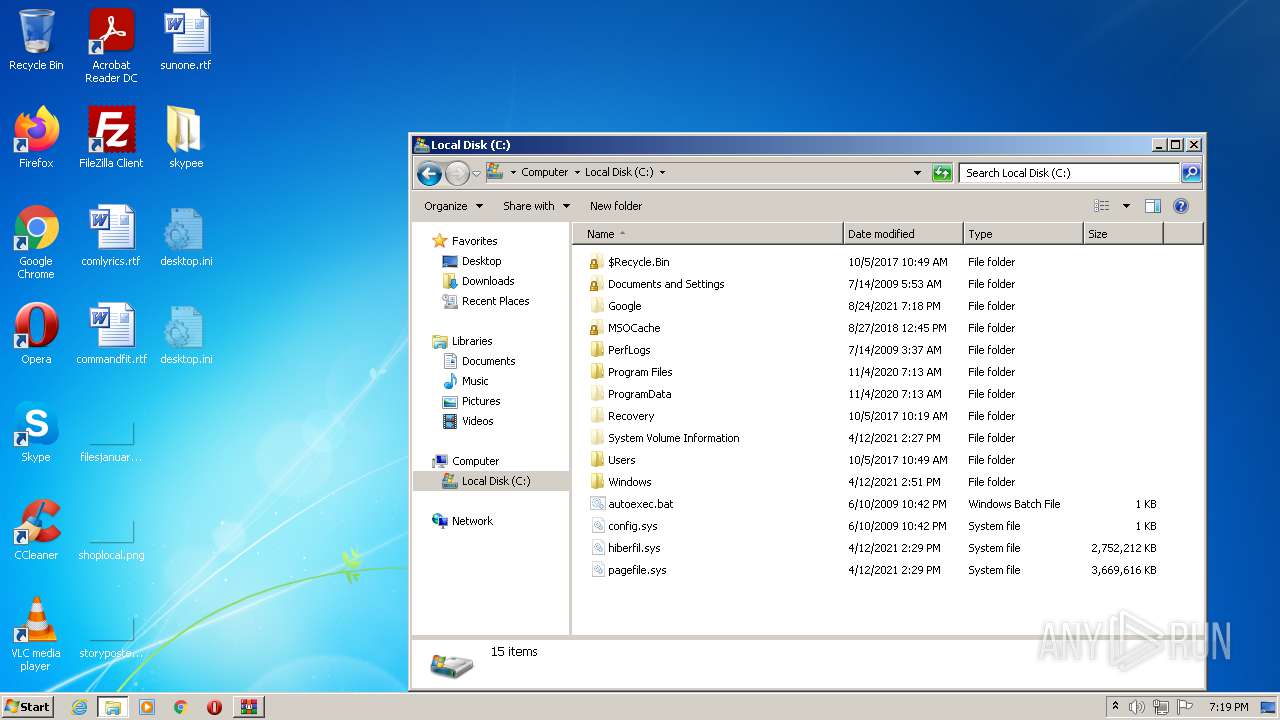
| ZipFileName: | skypee\AutoIt3.exe |
|---|---|
| ZipUncompressedSize: | 750320 |
| ZipCompressedSize: | 442953 |
| ZipCRC: | 0x4aca8fdb |
| ZipModifyDate: | 2012:01:29 23:34:10 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
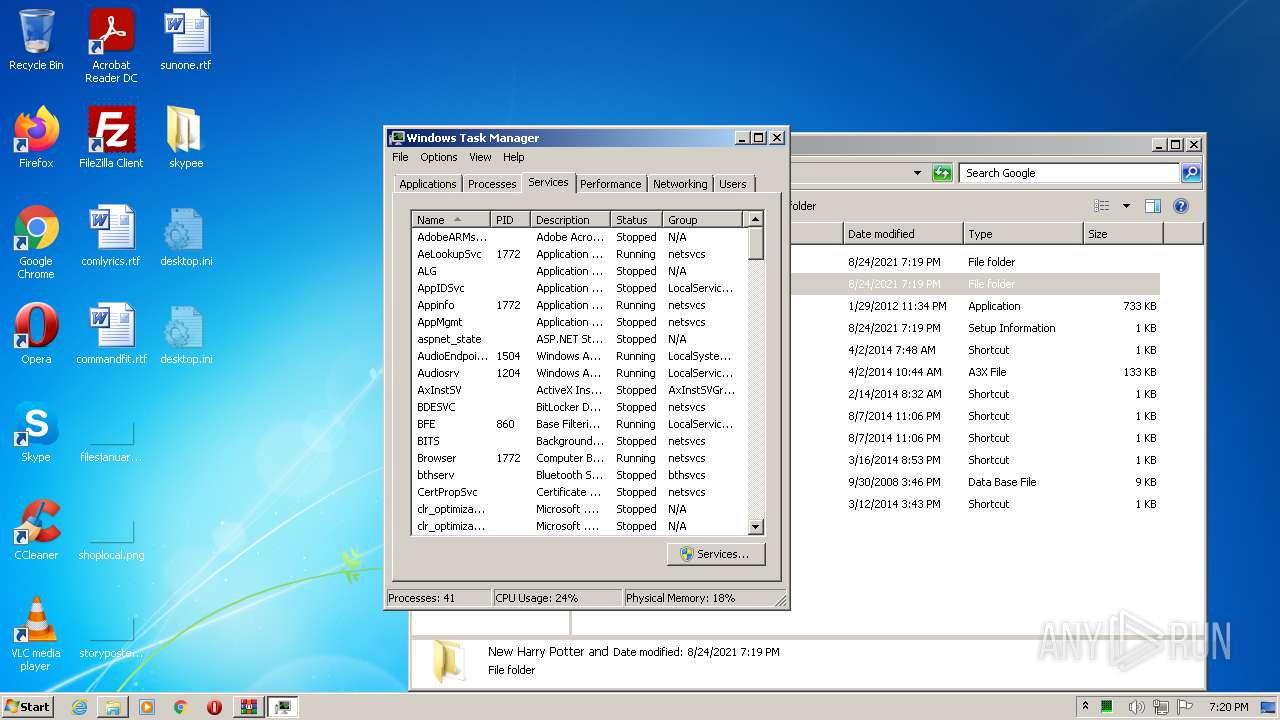
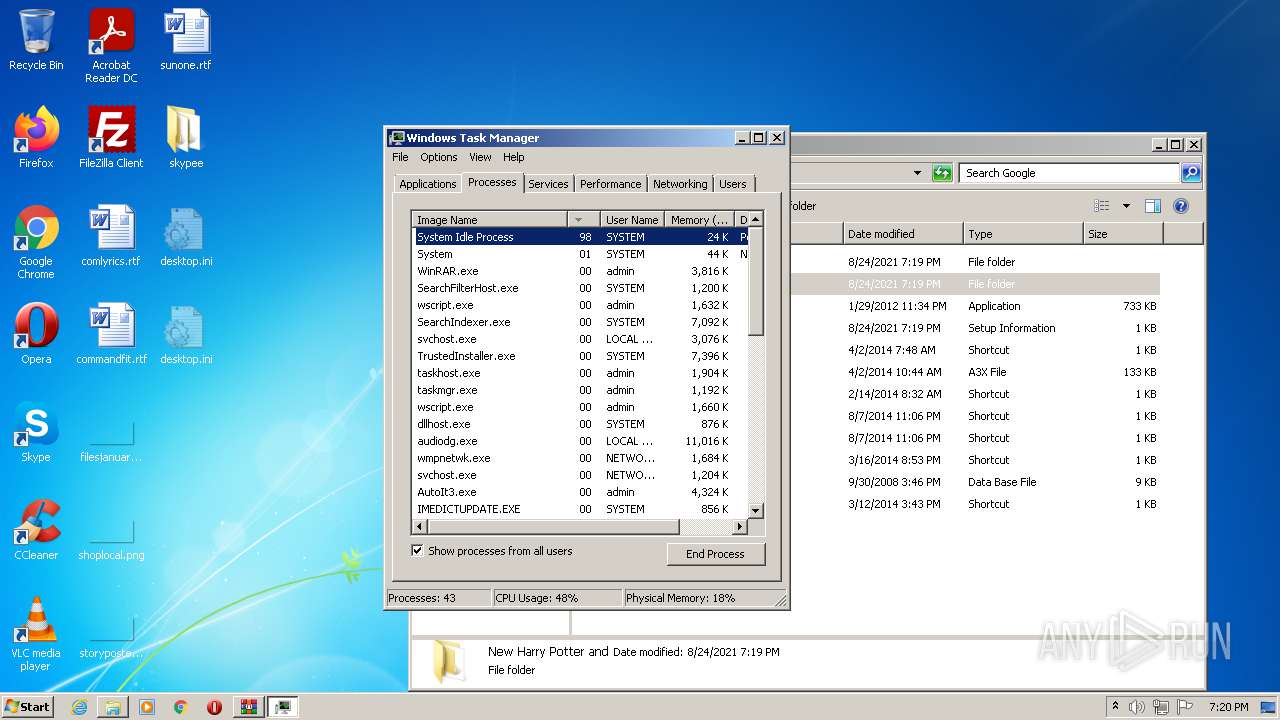
Total processes
80
Monitored processes
24
Malicious processes
6
Suspicious processes
4
Behavior graph
Click at the process to see the details
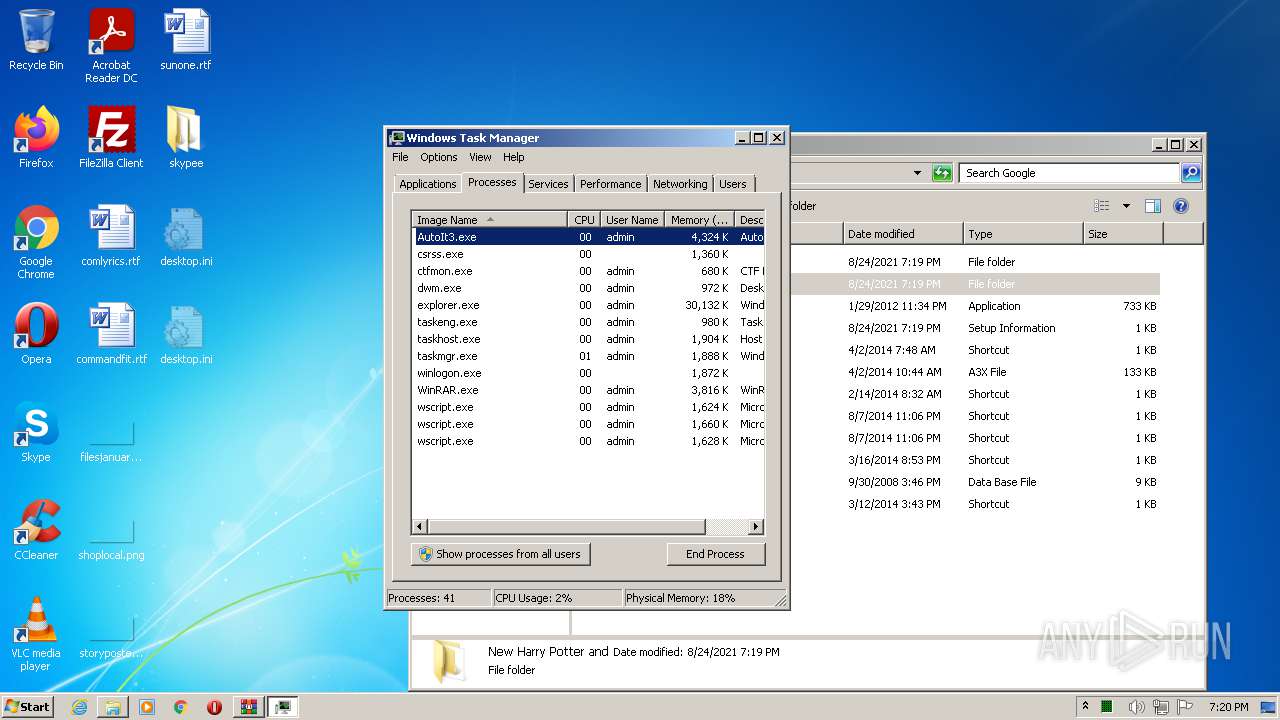
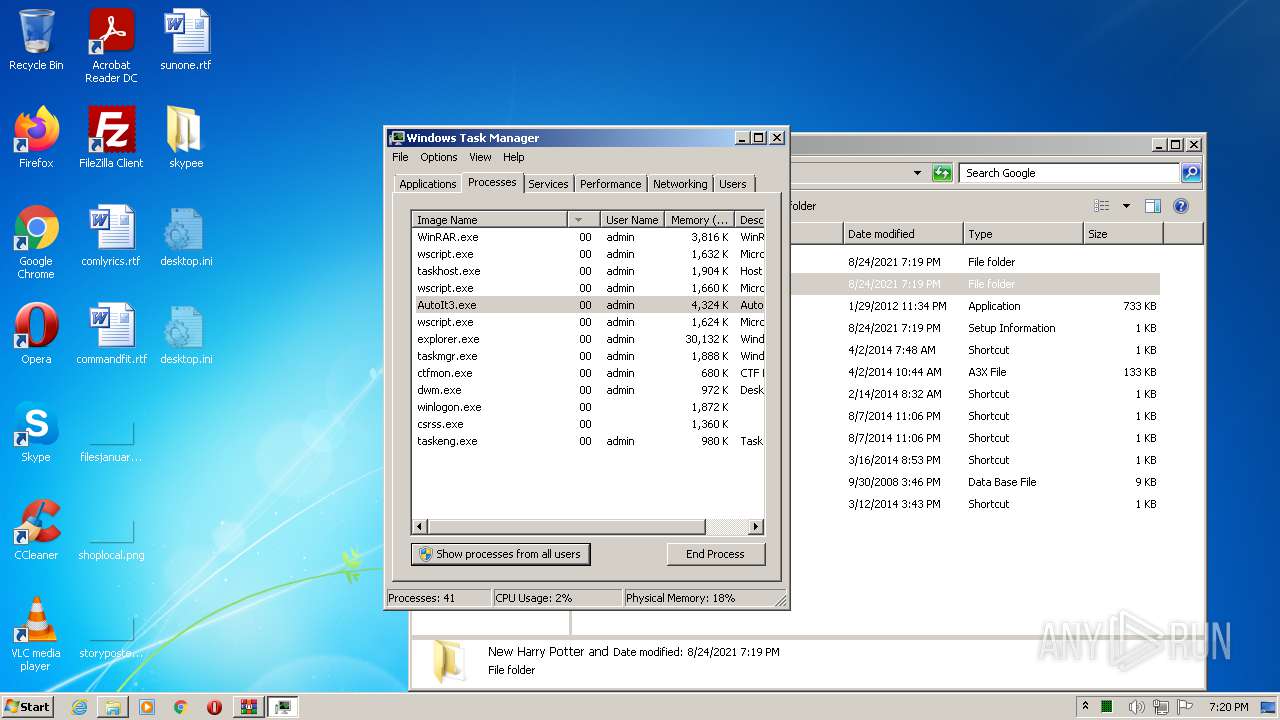
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
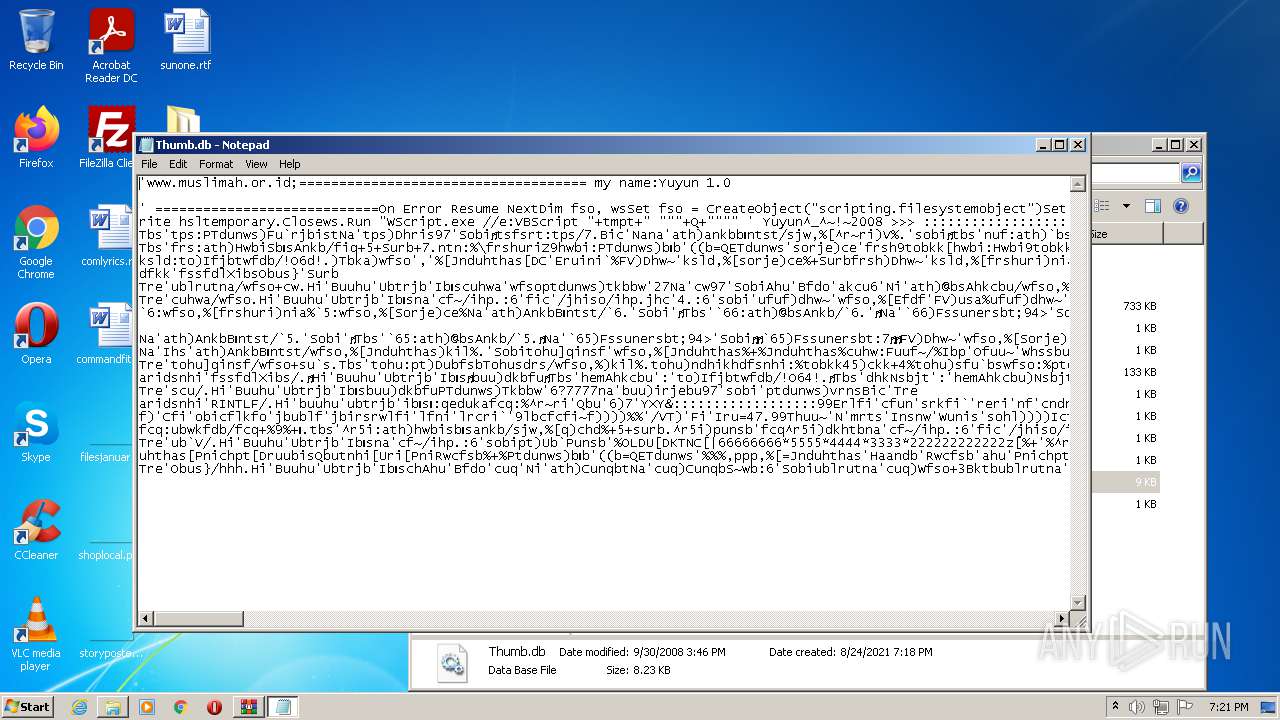
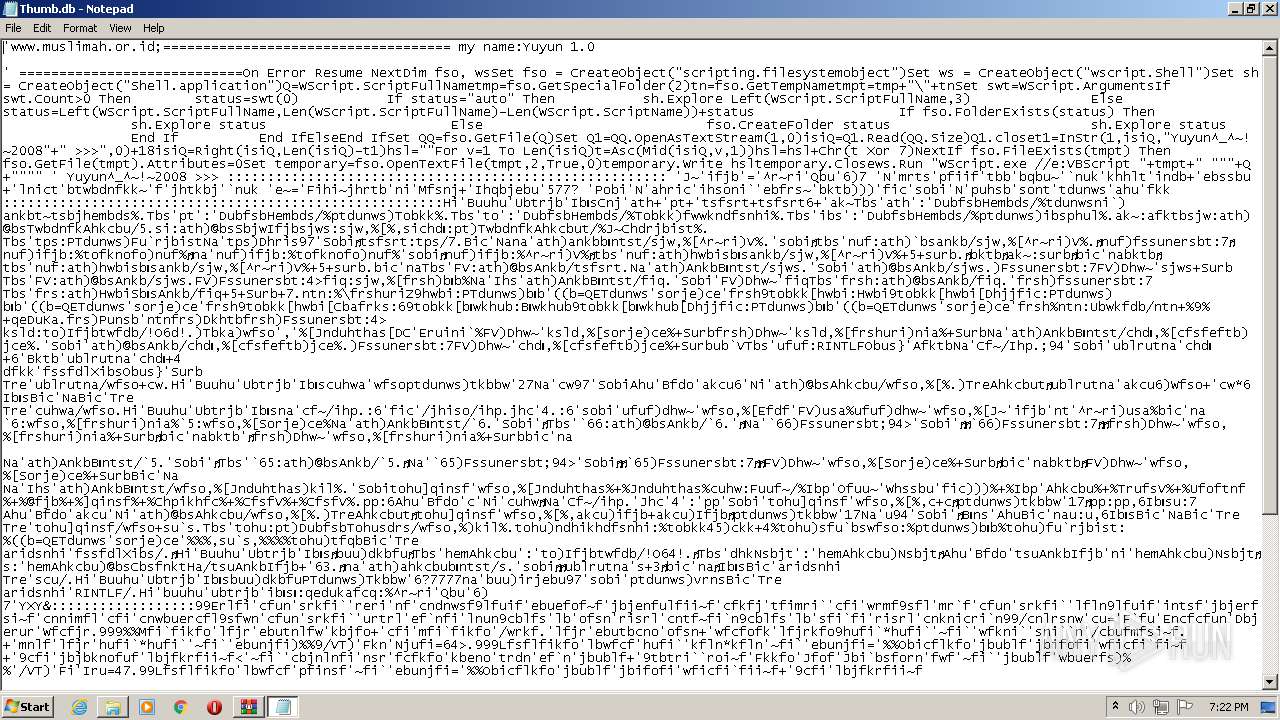
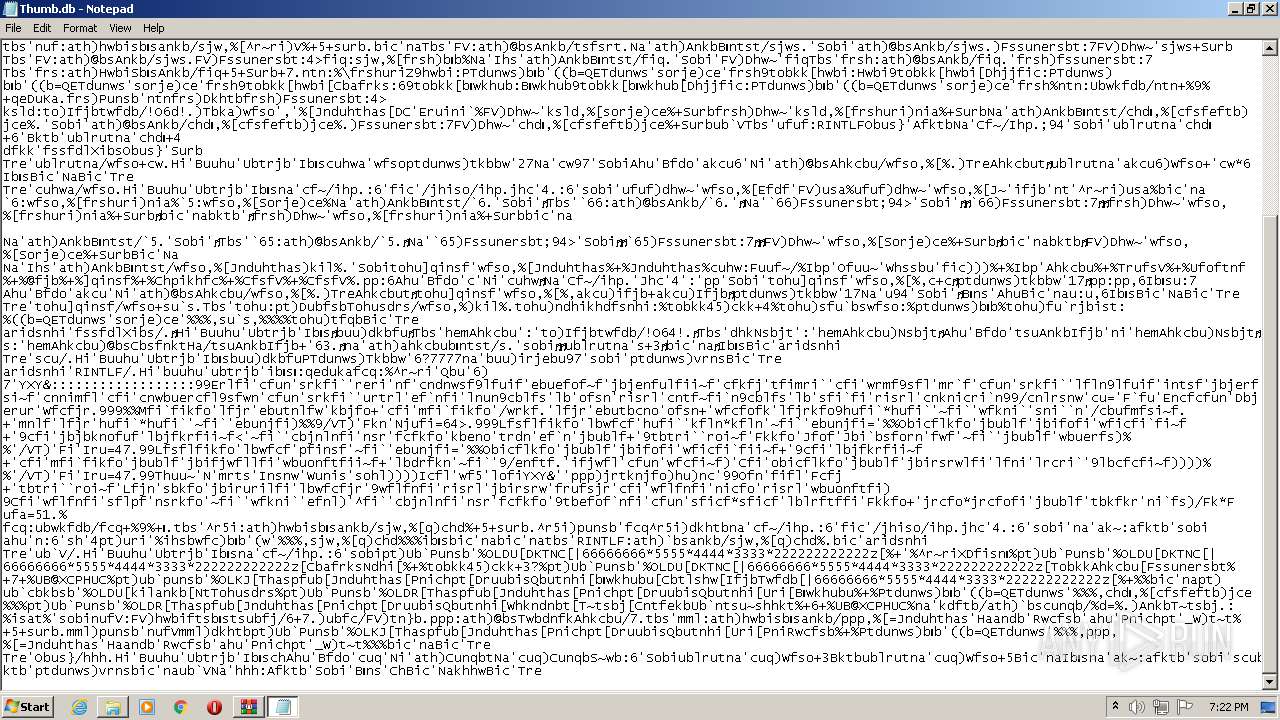
| 744 | "C:\Windows\system32\wscript.exe" //e:VBScript thumb.db "Microsoft" | C:\Windows\system32\wscript.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 996 | "C:\Windows\system32\wscript.exe" //e:VBScript thumb.db "Microsoft" | C:\Windows\system32\wscript.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1636 | C:\Windows\system32\cmd.exe /c SystemInfo | C:\Windows\system32\cmd.exe | — | AutoIt3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
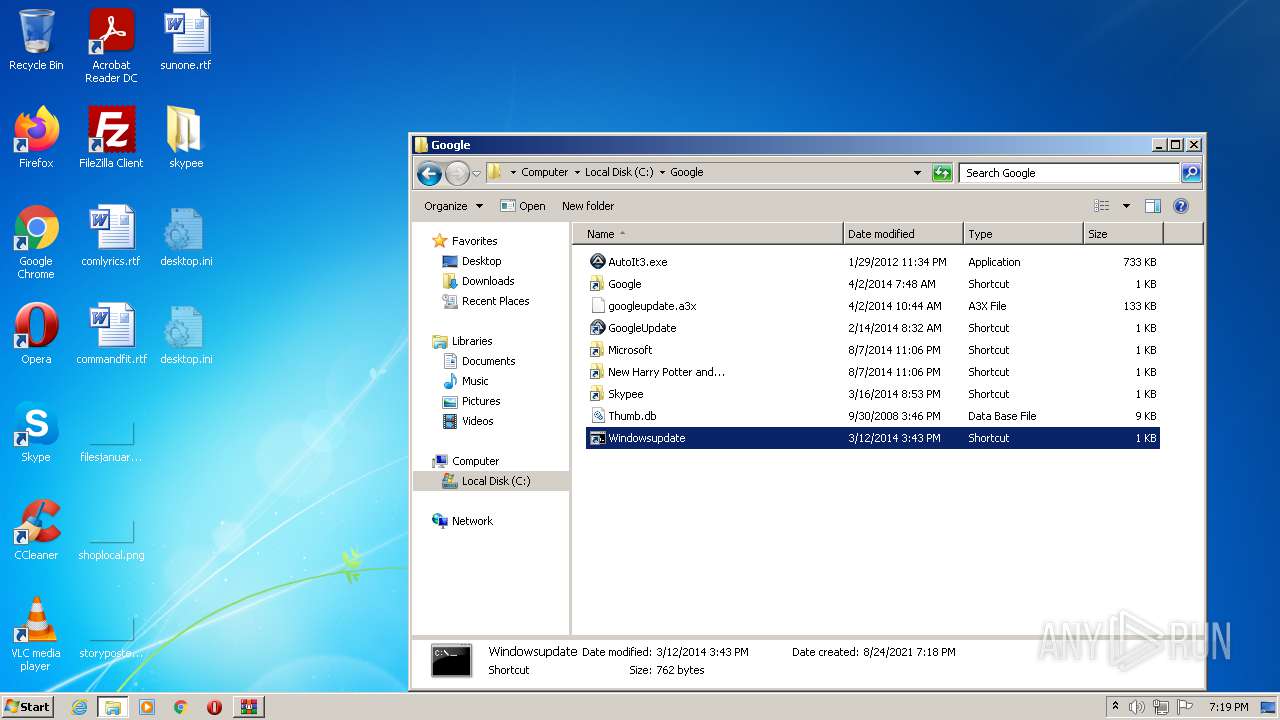
| 1656 | "C:\Windows\system32\cmd.exe" /c start ..\Skypee\AutoIt3.exe /AutoIt3ExecuteScript ..\Skypee\googleupdate.a3x explorer "%CD%" & exit | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 9059 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1660 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1888 | "C:\Windows\System32\wscript.exe" //e:VBScript C:\Users\admin\AppData\Local\Temp\rad4278A.tmp "C:\Google\New Harry Potter and\thumb.db" | C:\Windows\System32\wscript.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1956 | "C:\Google\AutoIt3.exe" /AutoIt3ExecuteScript C:\Google\googleupdate.a3x | C:\Google\AutoIt3.exe | AutoIt3.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 2016 | "C:\Windows\system32\wscript.exe" //e:VBScript thumb.db "New Harry Potter and..." | C:\Windows\system32\wscript.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2436 | C:\Google\AutoIt3.exe C:\Google\googleupdate.a3x | C:\Google\AutoIt3.exe | — | cmd.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 2540 | "C:\windows\system32\cmd.exe" /c start ..\Skypee\AutoIt3.exe /AutoIt3ExecuteScript ..\Skypee\googleupdate.a3x explorer "%CD%" & exit | C:\windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
5 661
Read events
5 489
Write events
169
Delete events
3
Modification events
| (PID) Process: | (3928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3928) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\171\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\skypee.zip | |||
| (PID) Process: | (3928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (3164) systeminfo.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\171\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
3
Suspicious files
69
Text files
5
Unknown types
89
Dropped files
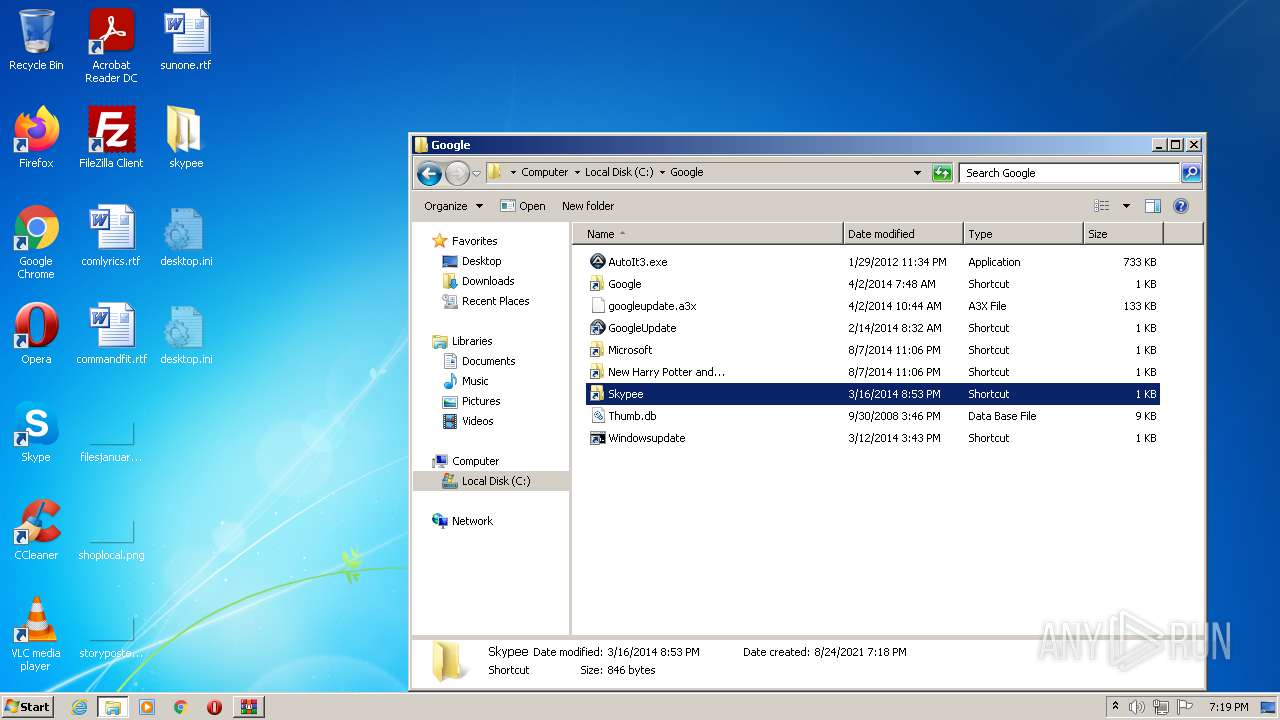
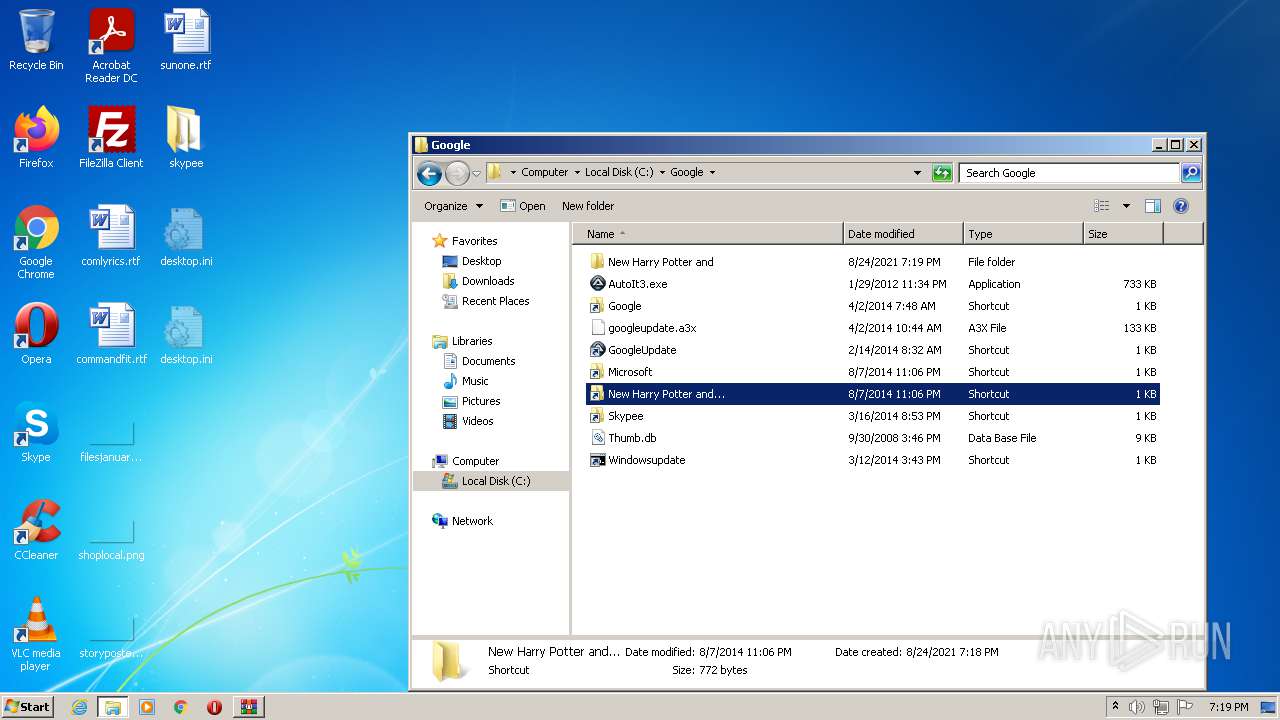
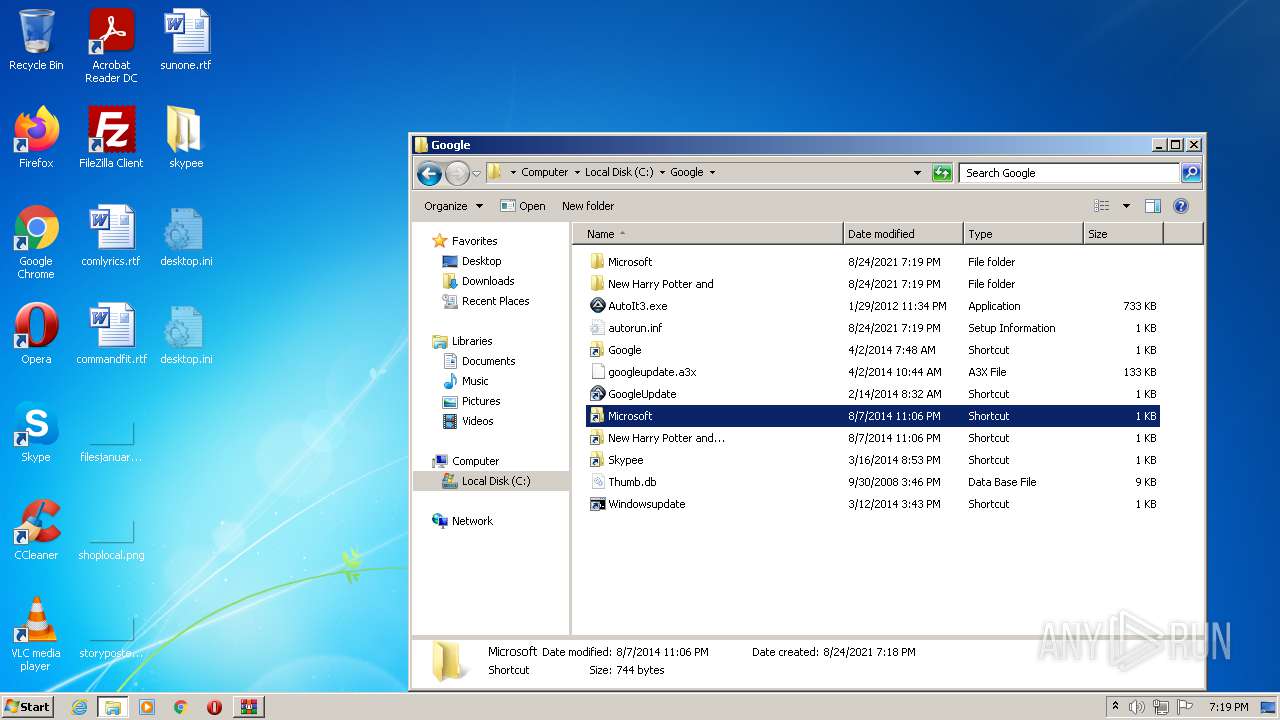
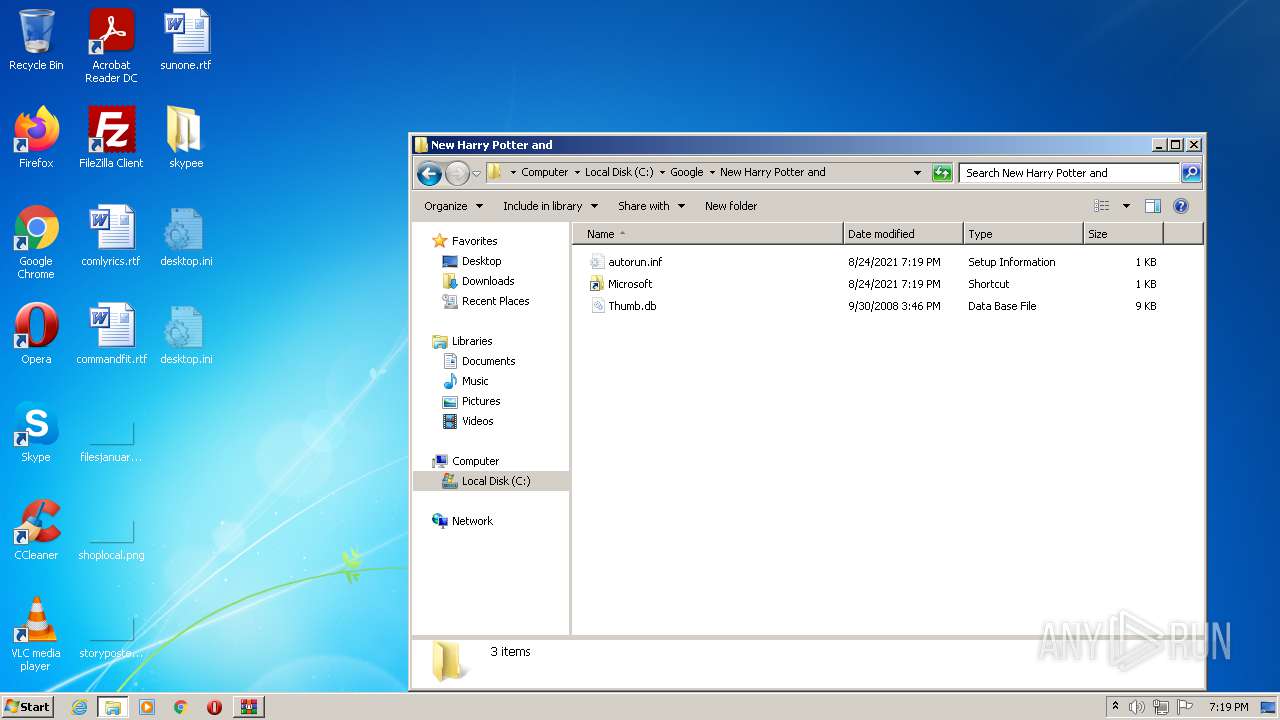
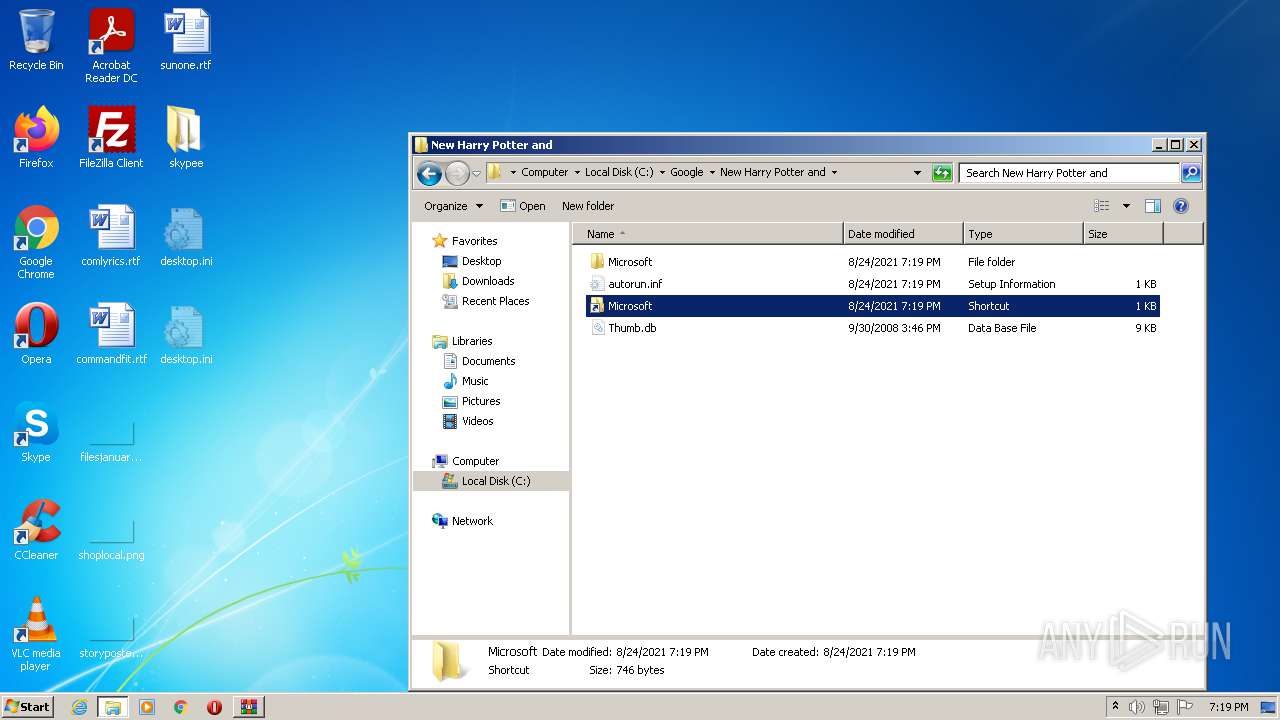
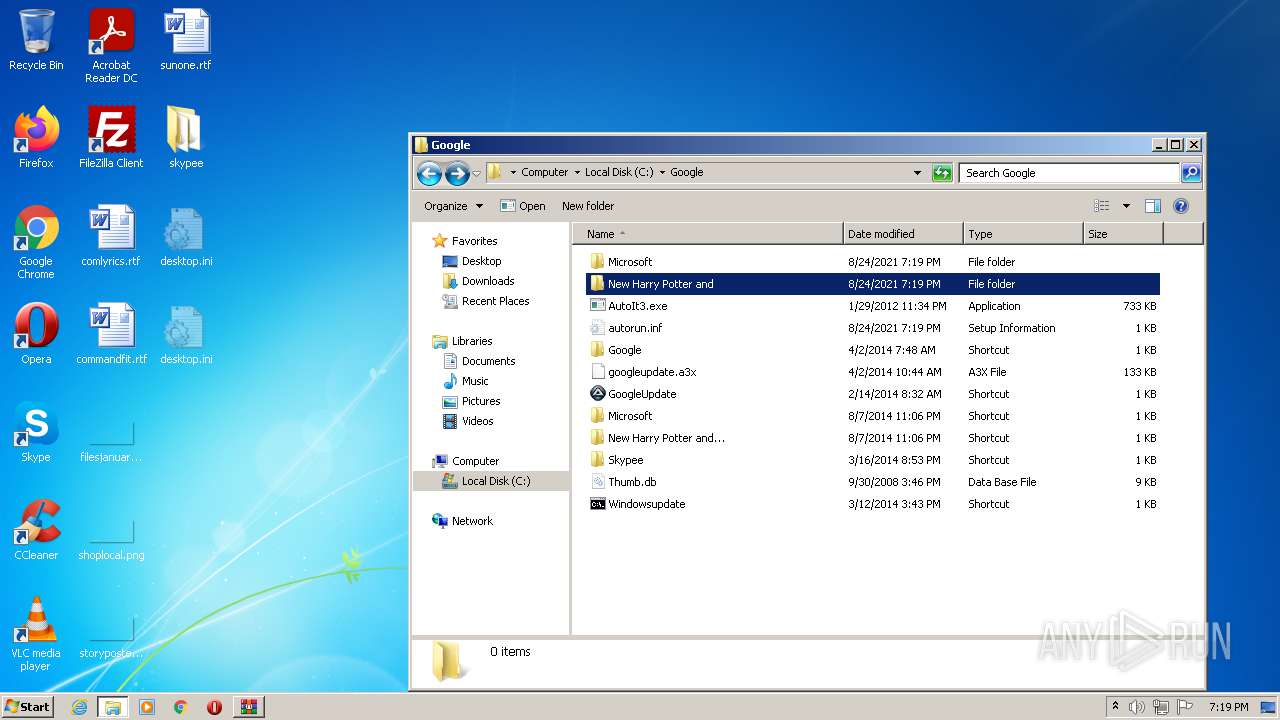
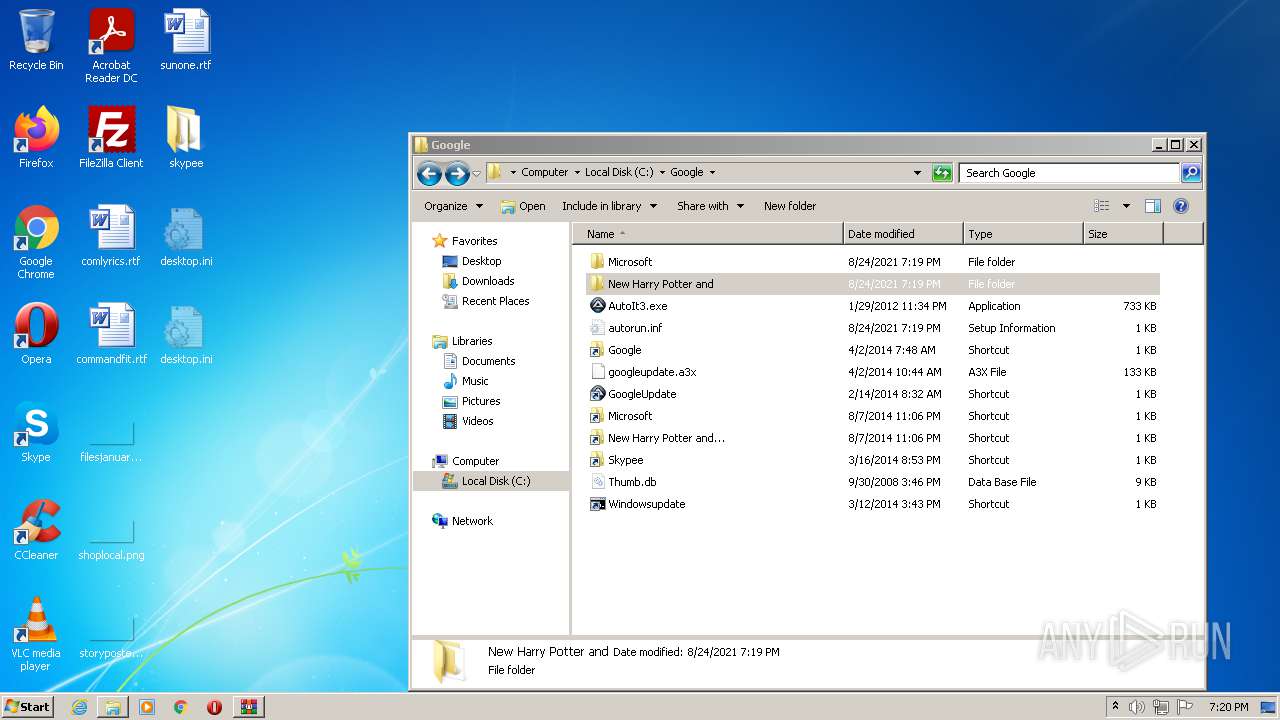
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3928 | WinRAR.exe | C:\Users\admin\Desktop\skypee\GoogleUpdate.lnk | lnk | |
MD5:C824F4226B6CCF9DA593A51B031529B2 | SHA256:D0E5378FE063FBFF6B71C9D69018CB278A91E26F03A230978B49917B4C63AB66 | |||
| 3928 | WinRAR.exe | C:\Users\admin\Desktop\skypee\googleupdate.a3x | a3x | |
MD5:E58C5E3F461089CA9688D3ACA204EA70 | SHA256:A388A6CBBEC942B0A772D7D1E0A3C0F3B9ADF93DD56DDB9F60B0B30D27915576 | |||
| 3928 | WinRAR.exe | C:\Users\admin\Desktop\skypee\Google.lnk | lnk | |
MD5:CC1F90DEF60C5FDE86F0E37FFC537148 | SHA256:CFC5F4A051AB563F1F97A634A909FC1D311EA2A7476103D0B10782974C58D7CD | |||
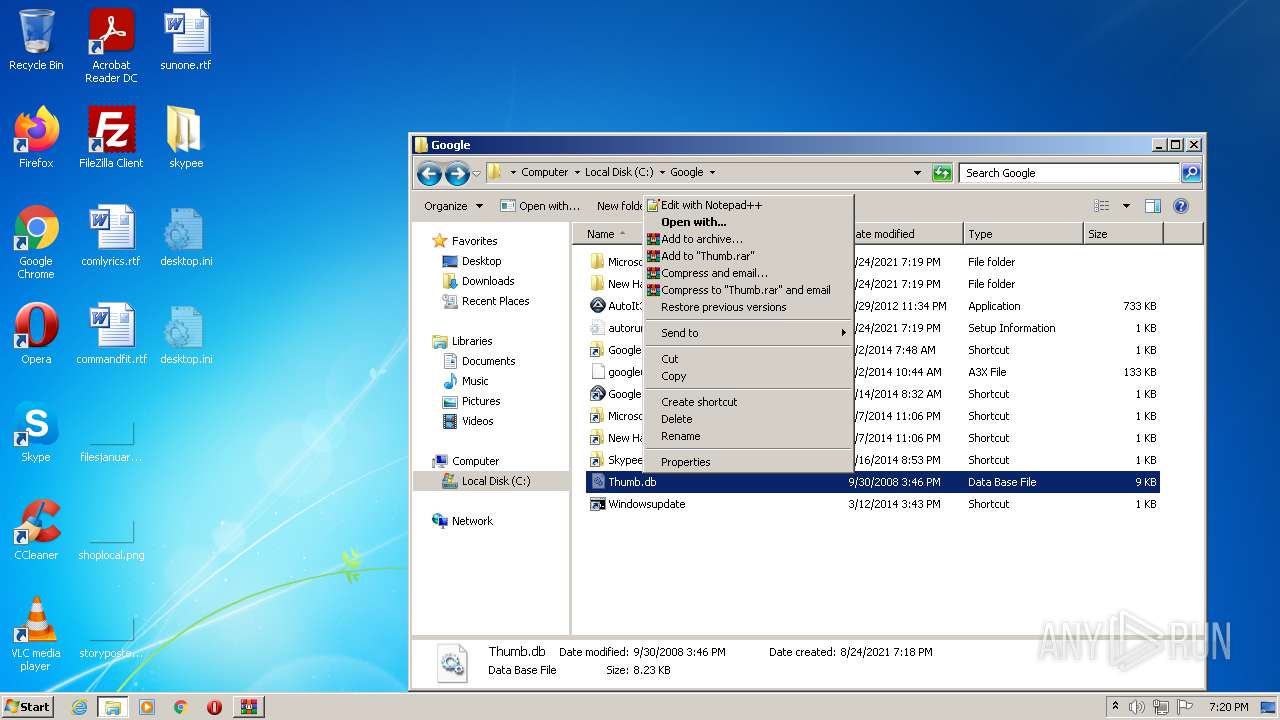
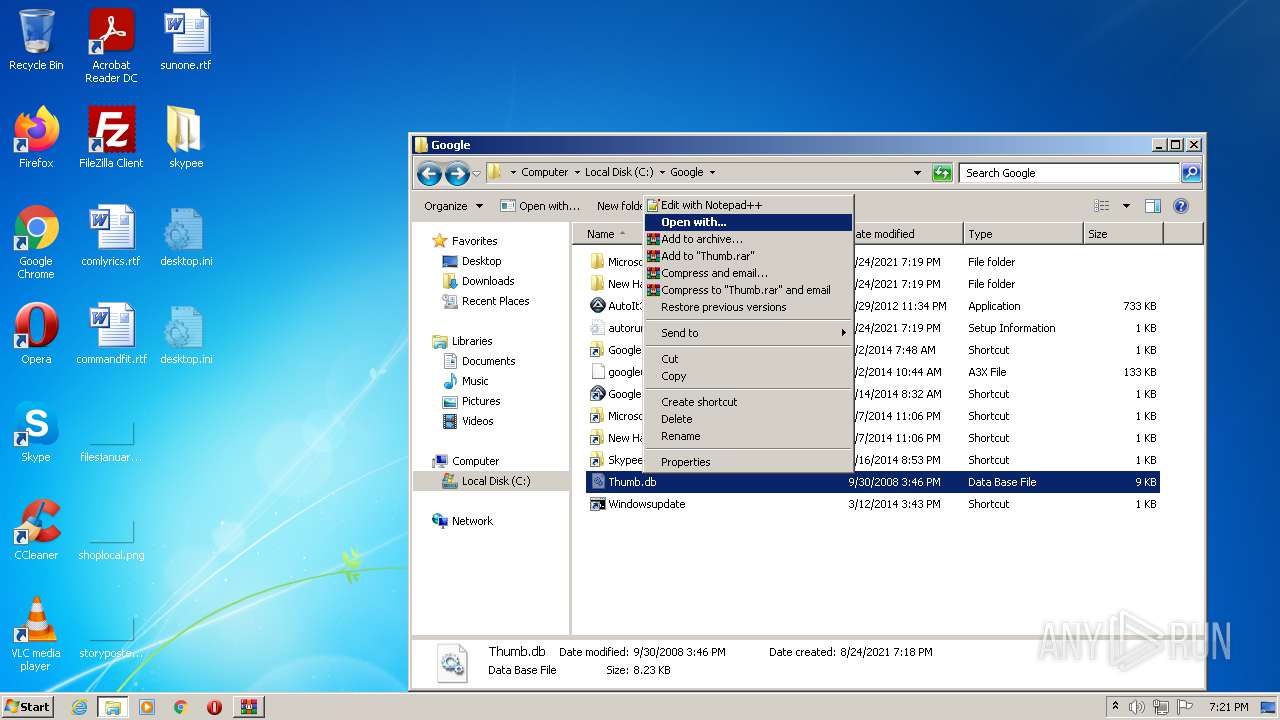
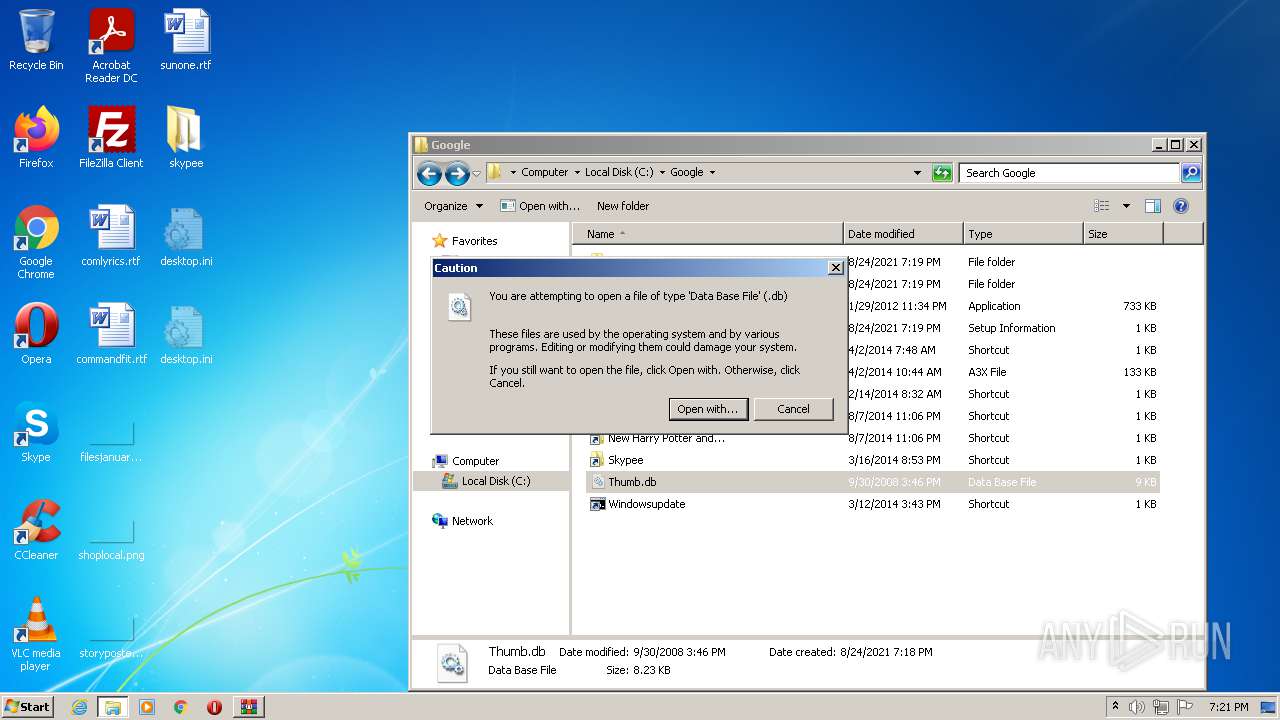
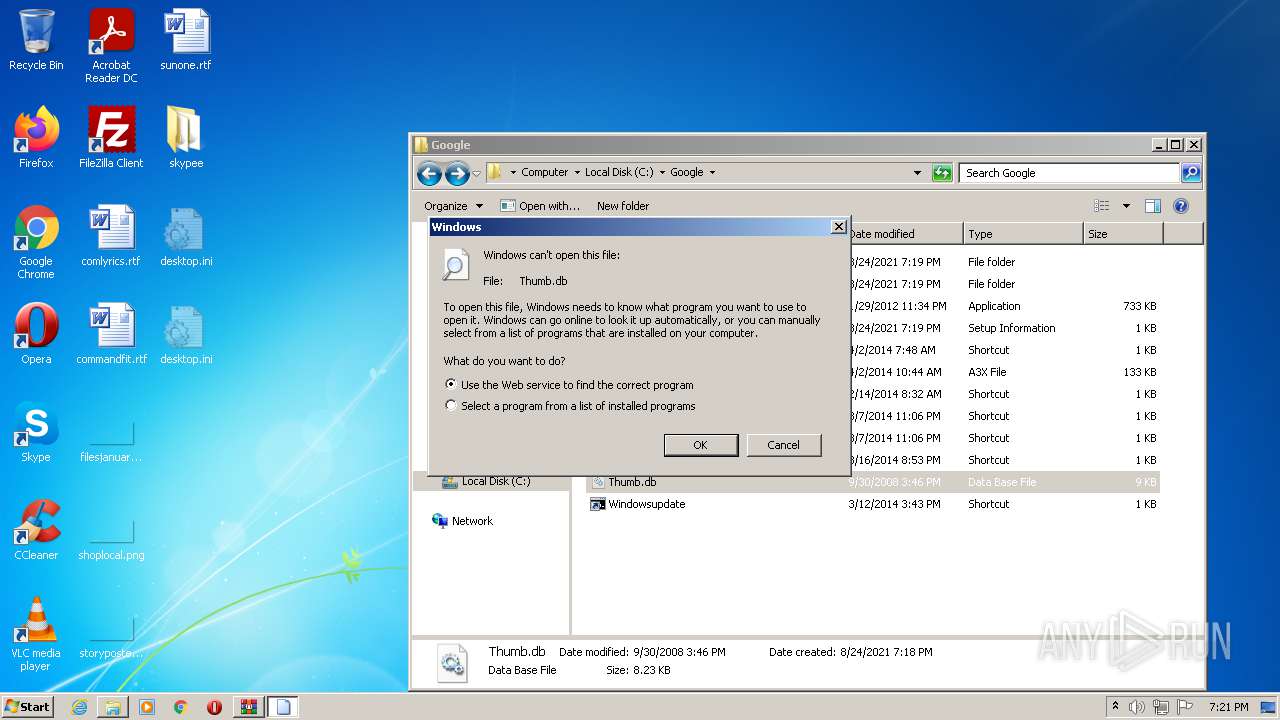
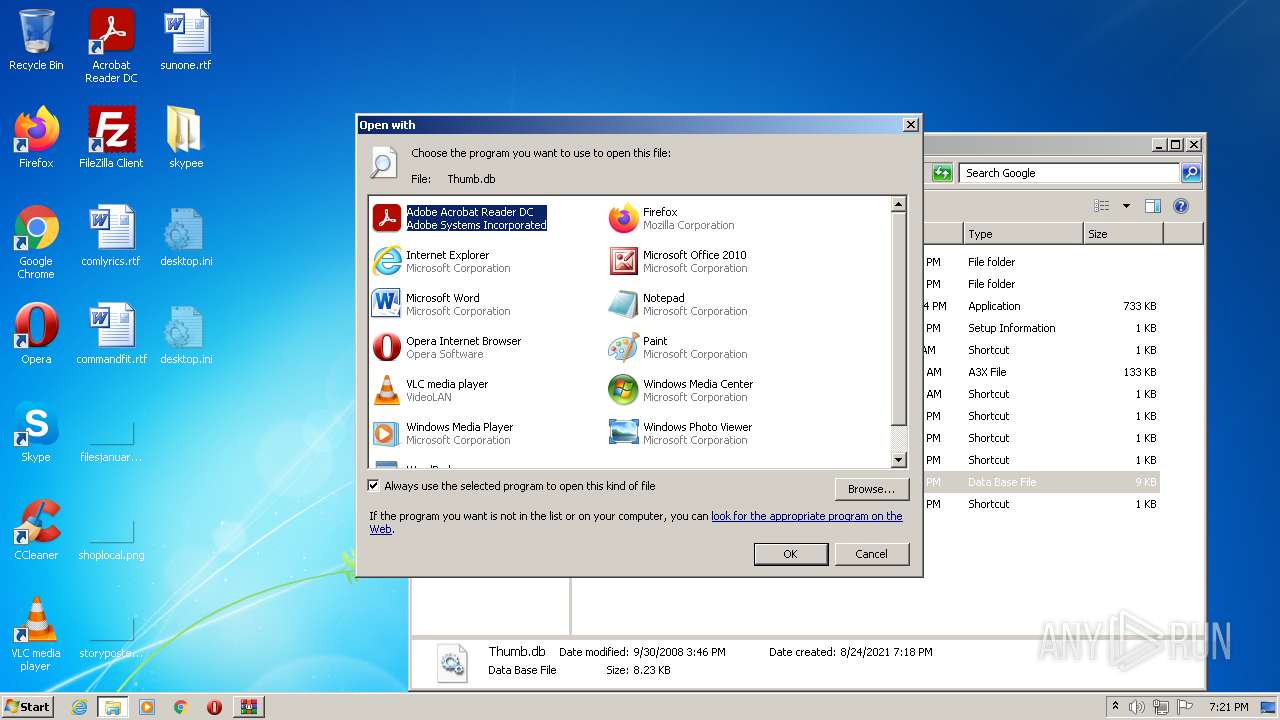
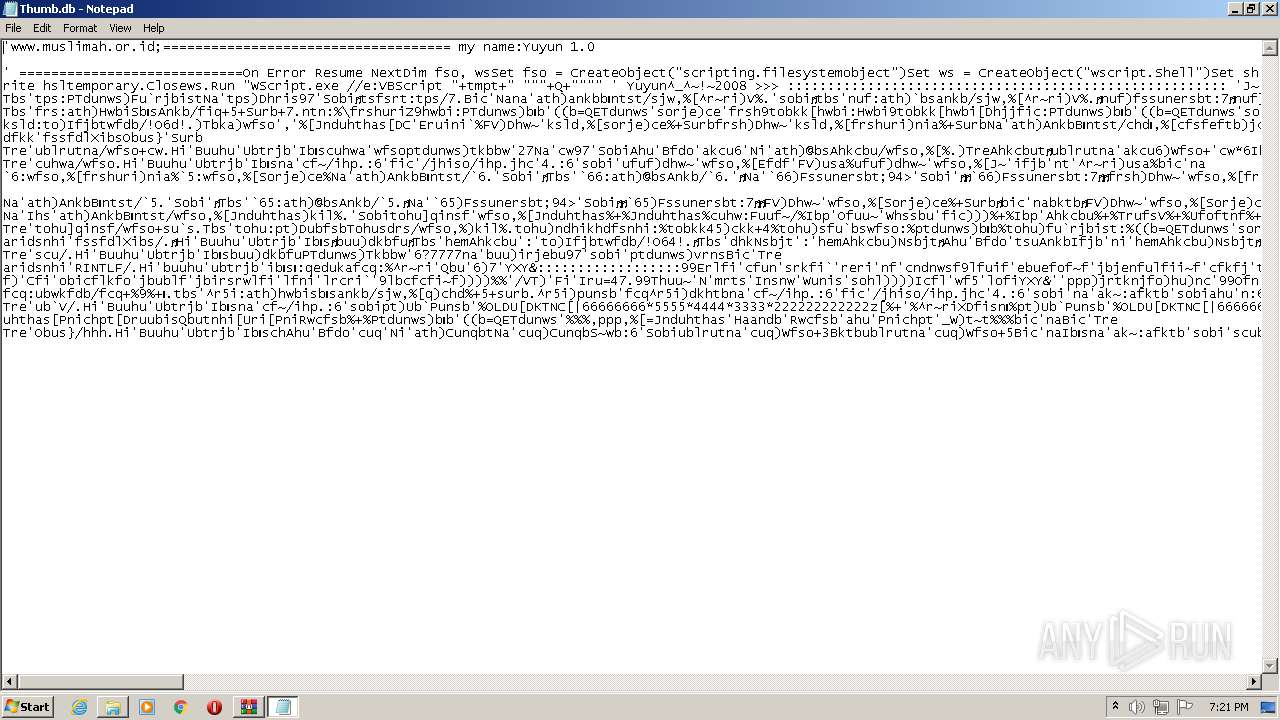
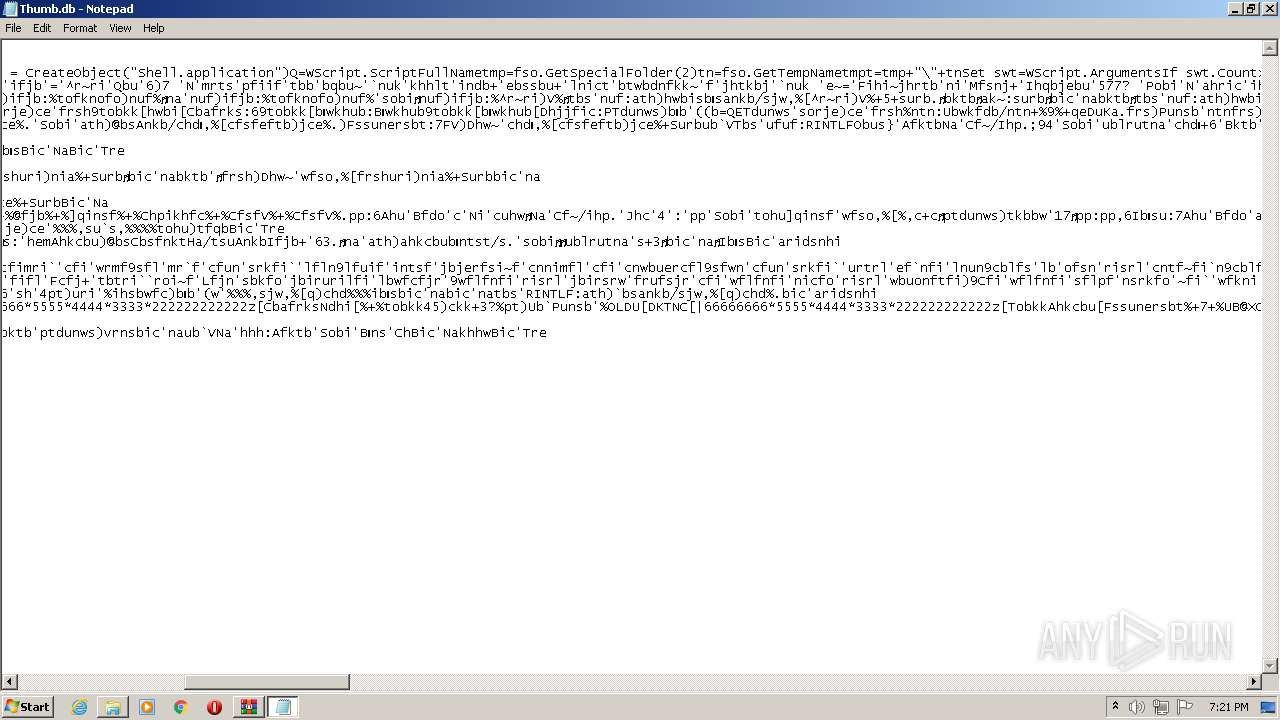
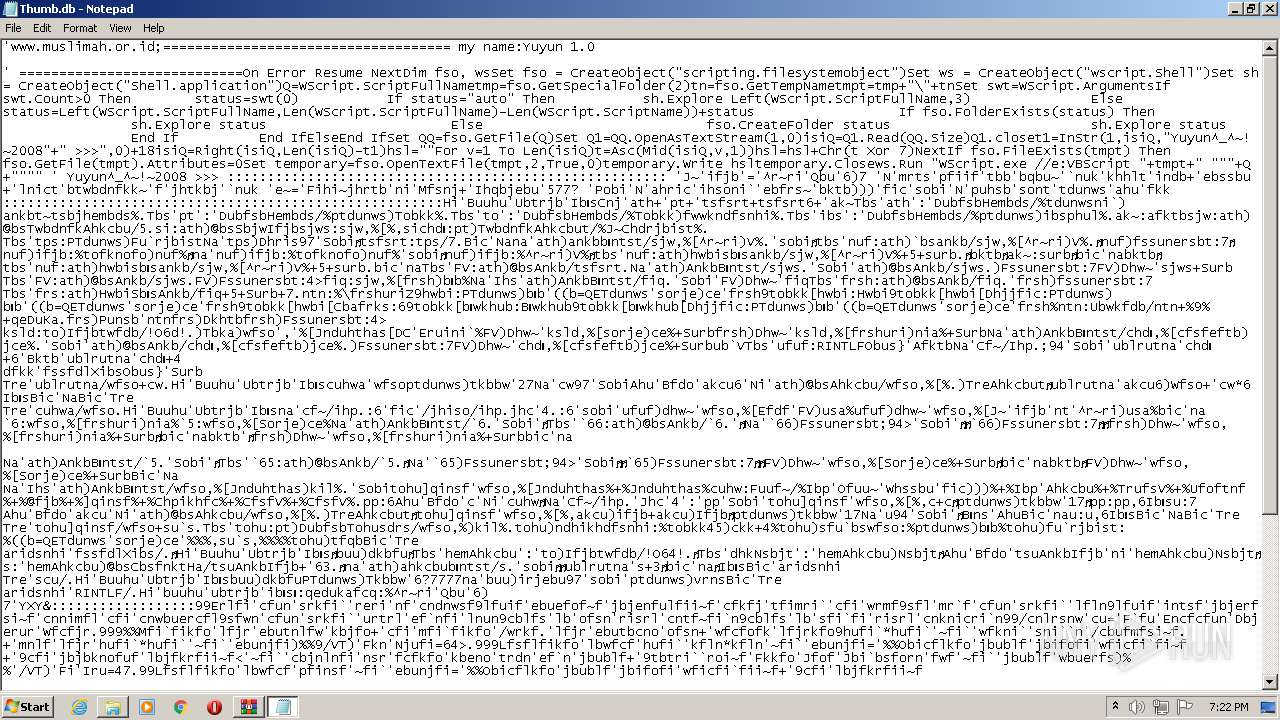
| 3928 | WinRAR.exe | C:\Users\admin\Desktop\skypee\Thumb.db | binary | |
MD5:0A456FFFF1D3FD522457C187EBCF41E4 | SHA256:3D929FBD23378F3246F6643F503E48AE8ECE5BDD8899E7DDF86568EBD044A2F2 | |||
| 3928 | WinRAR.exe | C:\Users\admin\Desktop\skypee\Windowsupdate.lnk | lnk | |
MD5:7682370F012DE5141FF702E60EE01016 | SHA256:3E9EDE4282541566A50158448E74390B8487AD71616EC1A3CCB4779A798196EA | |||
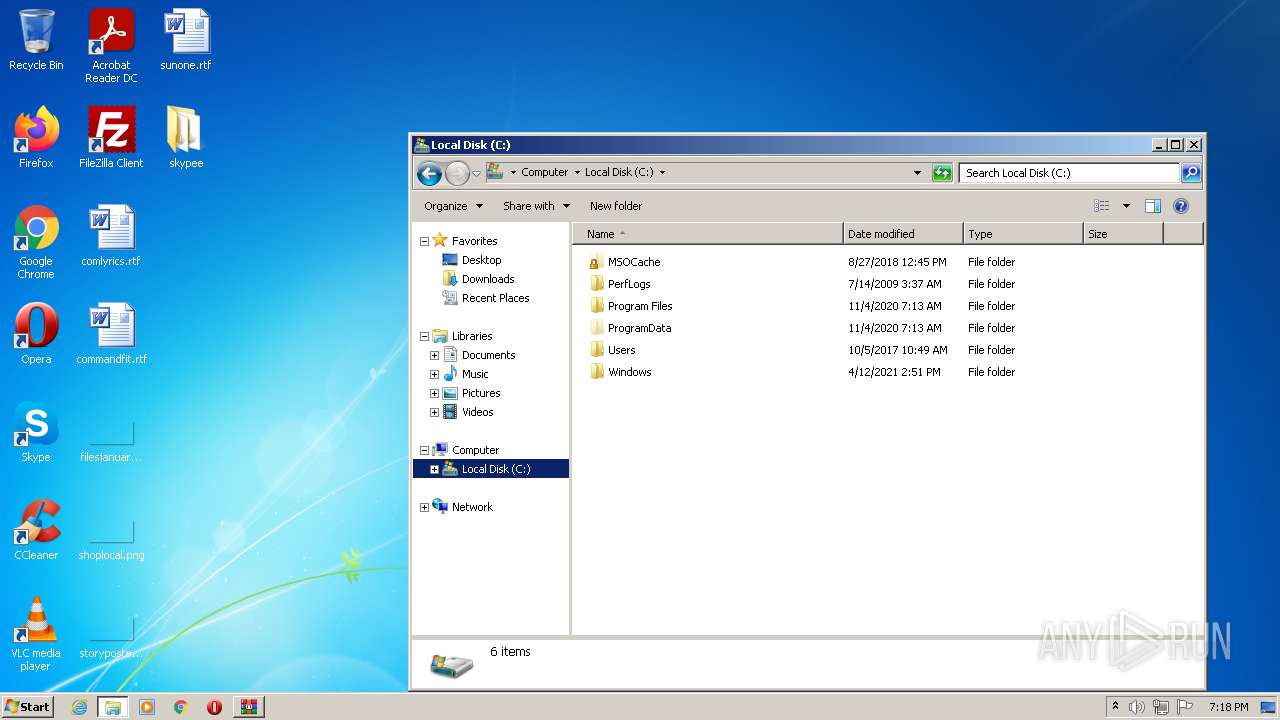
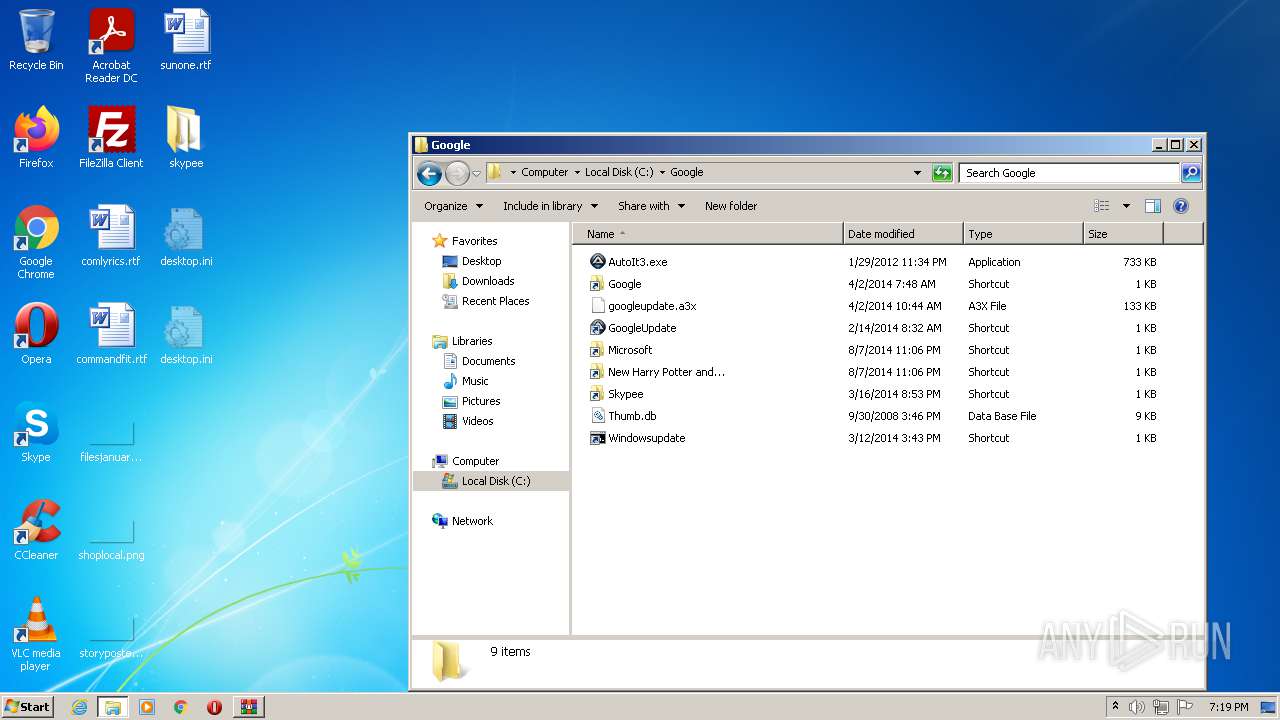
| 3064 | AutoIt3.exe | C:\Google\Google.lnk | lnk | |
MD5:CC1F90DEF60C5FDE86F0E37FFC537148 | SHA256:CFC5F4A051AB563F1F97A634A909FC1D311EA2A7476103D0B10782974C58D7CD | |||
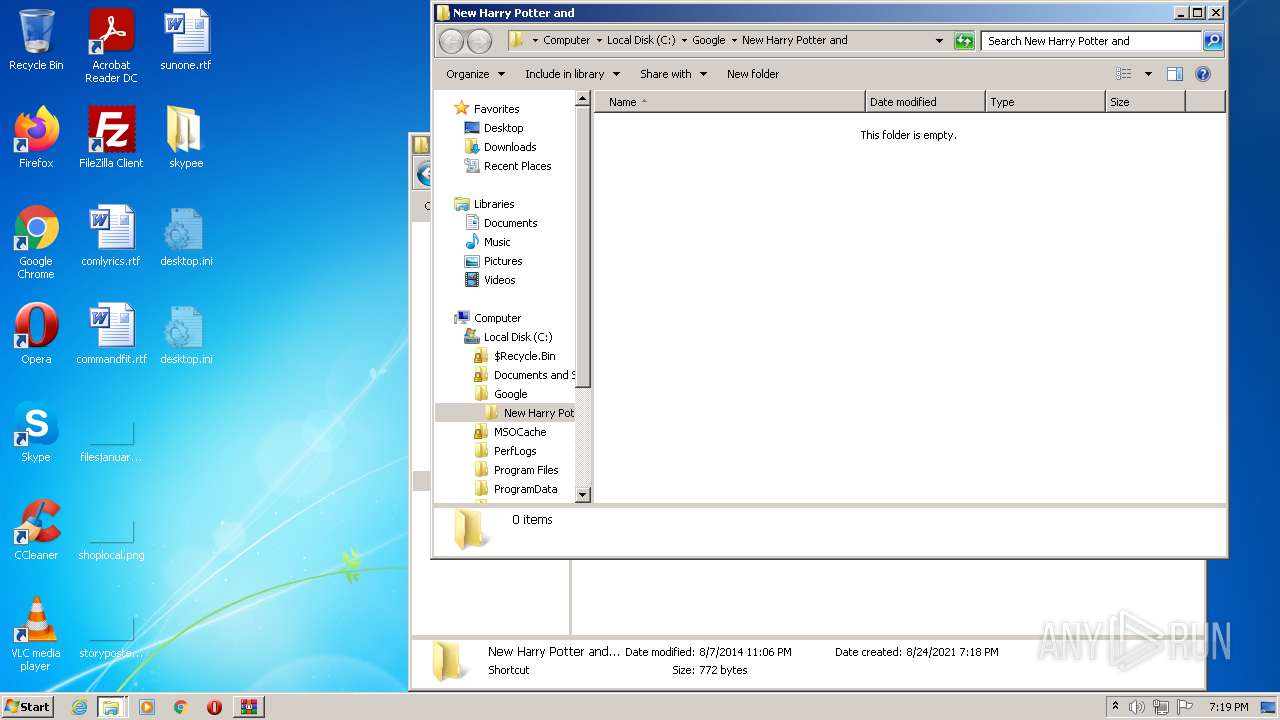
| 3928 | WinRAR.exe | C:\Users\admin\Desktop\skypee\New Harry Potter and....lnk | lnk | |
MD5:3B0F368CC604400C27A77A238AAE9414 | SHA256:AAED11B801ACCC88F4D37865722B9CA441128AD484C8458CE412EE87CAF26F03 | |||
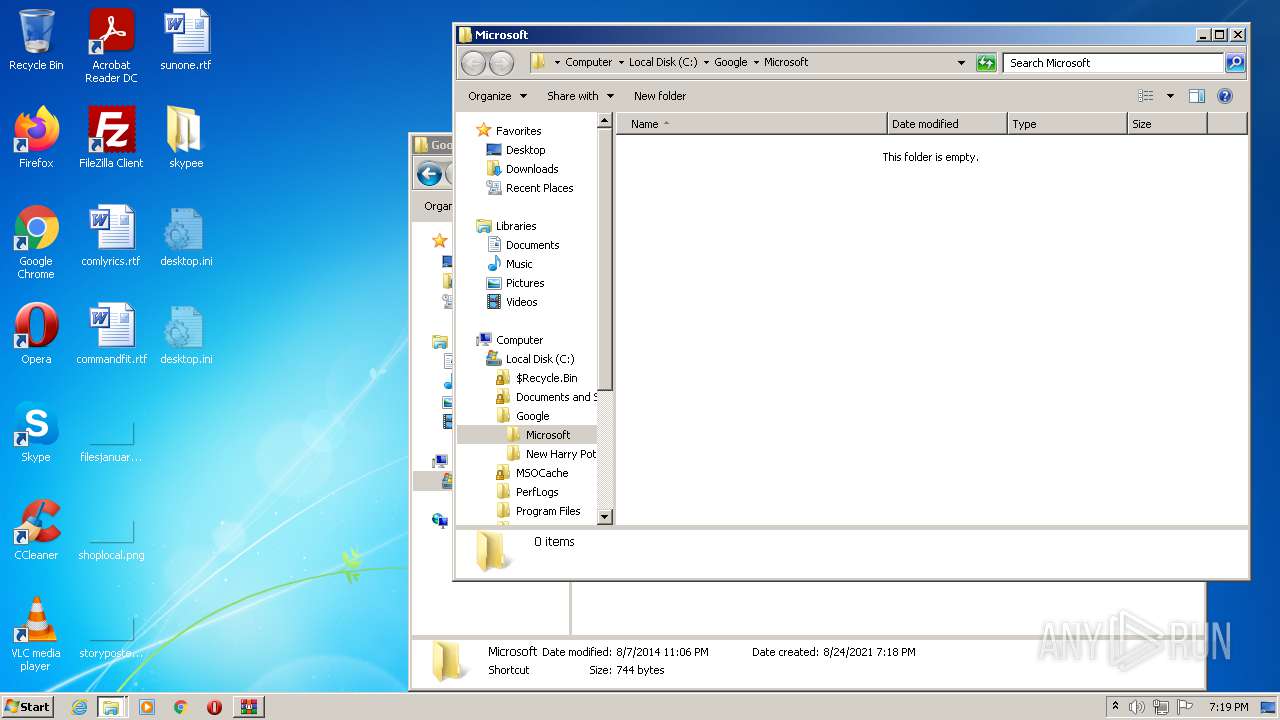
| 3928 | WinRAR.exe | C:\Users\admin\Desktop\skypee\Microsoft.lnk | lnk | |
MD5:AE5E3A3A103F7583EF946627DCD234D5 | SHA256:D75C443ECA5E2D32A74184F6F7DF54D5E72788DBF64FFB07B2315D1E79C64B70 | |||
| 3928 | WinRAR.exe | C:\Users\admin\Desktop\skypee\Skypee.lnk | lnk | |
MD5:E9C73F8BEFF9346EF1BF97E14C33A6D3 | SHA256:053681D3B052F5A7035F92E8040E6FB91570F48CCA257B3300F0D4012723AA57 | |||
| 3064 | AutoIt3.exe | C:\Google\Microsoft.lnk | lnk | |
MD5:AE5E3A3A103F7583EF946627DCD234D5 | SHA256:D75C443ECA5E2D32A74184F6F7DF54D5E72788DBF64FFB07B2315D1E79C64B70 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1956 | AutoIt3.exe | GET | 200 | 178.237.33.50:80 | http://www.geoplugin.net/json.gp | NL | html | 963 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1956 | AutoIt3.exe | 178.237.33.50:80 | www.geoplugin.net | Schuberg Philis B.V. | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
superyou.zapto.org |
| unknown |
www.geoplugin.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.zapto .org |
1956 | AutoIt3.exe | Potential Corporate Privacy Violation | ET POLICY Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
1 ETPRO signatures available at the full report