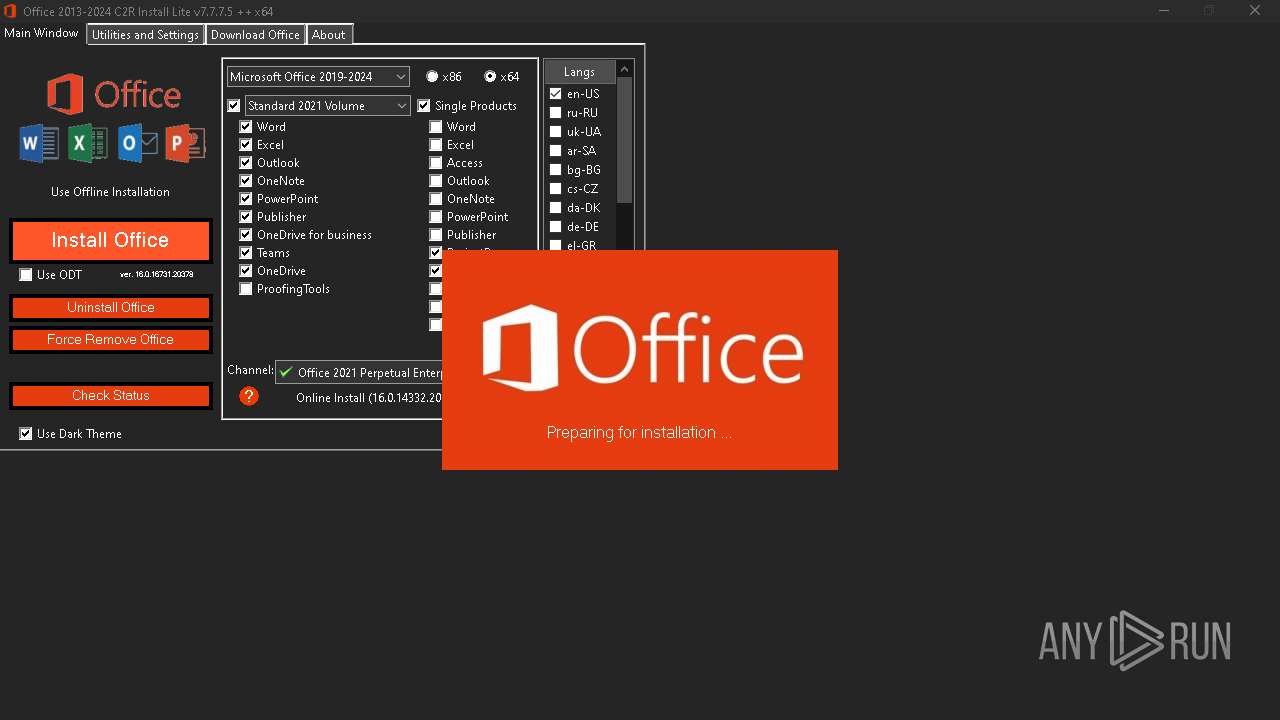
| File name: | OInstallLite_x64.exe |
| Full analysis: | https://app.any.run/tasks/ee51c112-354a-4775-9fe9-68d6509f4b5a |
| Verdict: | Malicious activity |
| Analysis date: | August 30, 2024, 19:00:47 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 8AC6E3E2059145EEEC60F7D5FF3ABB0B |
| SHA1: | 69DF4F0157432616E9E0019B46ED1A285034FA9E |
| SHA256: | 0289ED449236C270AFB004AF5A3E483B2C8D778C7A001B07181951EC12E50A68 |
| SSDEEP: | 98304:P9W98e7b8zKtHucp+r4laH0hWD9yfsIB+O7xEj6A6aKJqMBOjfE3MvOIeUAZreZe:17bRl/Z4/ |
MALICIOUS
Uses WMIC.EXE to add exclusions to the Windows Defender
- cmd.exe (PID: 6844)
- cmd.exe (PID: 6636)
SUSPICIOUS
Starts CMD.EXE for commands execution
- OInstallLite_x64.exe (PID: 7052)
Process drops legitimate windows executable
- OInstallLite_x64.exe (PID: 7052)
- files.dat (PID: 4540)
- expand.exe (PID: 4688)
Drops 7-zip archiver for unpacking
- OInstallLite_x64.exe (PID: 7052)
Uses REG/REGEDIT.EXE to modify registry
- OInstallLite_x64.exe (PID: 7052)
Found strings related to reading or modifying Windows Defender settings
- OInstallLite_x64.exe (PID: 7052)
Executable content was dropped or overwritten
- OInstallLite_x64.exe (PID: 7052)
- files.dat (PID: 4540)
- expand.exe (PID: 4688)
Drops the executable file immediately after the start
- OInstallLite_x64.exe (PID: 7052)
- files.dat (PID: 4540)
- expand.exe (PID: 4688)
Starts application with an unusual extension
- cmd.exe (PID: 6560)
The executable file from the user directory is run by the CMD process
- files.dat (PID: 4540)
The process drops C-runtime libraries
- files.dat (PID: 4540)
- expand.exe (PID: 4688)
The process bypasses the loading of PowerShell profile settings
- OInstallLite_x64.exe (PID: 7052)
Starts SC.EXE for service management
- cmd.exe (PID: 5700)
Probably download files using WebClient
- OInstallLite_x64.exe (PID: 7052)
Starts POWERSHELL.EXE for commands execution
- OInstallLite_x64.exe (PID: 7052)
Uses TASKKILL.EXE to kill process
- OInstallLite_x64.exe (PID: 7052)
Unpacks CAB file
- expand.exe (PID: 4688)
- expand.exe (PID: 872)
Reads security settings of Internet Explorer
- OInstallLite_x64.exe (PID: 7052)
Reads the date of Windows installation
- OInstallLite_x64.exe (PID: 7052)
INFO
Reads Microsoft Office registry keys
- OInstallLite_x64.exe (PID: 7052)
- OfficeClickToRun.exe (PID: 2660)
- OfficeClickToRun.exe (PID: 5744)
Checks supported languages
- OInstallLite_x64.exe (PID: 7052)
- files.dat (PID: 4540)
- expand.exe (PID: 4688)
- expand.exe (PID: 872)
- OfficeClickToRun.exe (PID: 2660)
- OfficeClickToRun.exe (PID: 5744)
Reads Environment values
- OInstallLite_x64.exe (PID: 7052)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 2232)
- WMIC.exe (PID: 6216)
Create files in a temporary directory
- OInstallLite_x64.exe (PID: 7052)
- files.dat (PID: 4540)
- OfficeClickToRun.exe (PID: 2660)
Reads the computer name
- OInstallLite_x64.exe (PID: 7052)
- OfficeClickToRun.exe (PID: 2660)
- OfficeClickToRun.exe (PID: 5744)
Disables trace logs
- powershell.exe (PID: 6948)
- powershell.exe (PID: 6156)
- powershell.exe (PID: 6796)
Checks proxy server information
- powershell.exe (PID: 6948)
- powershell.exe (PID: 6156)
- powershell.exe (PID: 6796)
- OfficeClickToRun.exe (PID: 5744)
- OfficeClickToRun.exe (PID: 2660)
Creates files in the program directory
- OInstallLite_x64.exe (PID: 7052)
- expand.exe (PID: 872)
- expand.exe (PID: 4688)
- OfficeClickToRun.exe (PID: 5744)
Reads the machine GUID from the registry
- expand.exe (PID: 872)
- expand.exe (PID: 4688)
- OfficeClickToRun.exe (PID: 5744)
Process checks computer location settings
- OInstallLite_x64.exe (PID: 7052)
The process uses the downloaded file
- OInstallLite_x64.exe (PID: 7052)
Executes as Windows Service
- OfficeClickToRun.exe (PID: 5744)
Creates files or folders in the user directory
- OfficeClickToRun.exe (PID: 2660)
Reads the software policy settings
- OfficeClickToRun.exe (PID: 5744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:01:07 13:13:40+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 2.5 |
| CodeSize: | 1390080 |
| InitializedDataSize: | 13568512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x77b70 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.7.7.5 |
| ProductVersionNumber: | 7.7.7.5 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| ProductName: | Office 2013-2024 C2R Install Lite |
| FileDescription: | Office 2013-2024 C2R Install Lite |
Total processes
180
Monitored processes
50
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | sc.exe stop ClickToRunSvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 252 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | "taskkill.exe" /t /f /IM IntegratedOffice.exe | C:\Windows\System32\taskkill.exe | — | OInstallLite_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | "expand" i641033.cab -F:* "C:\Program Files\Common Files\Microsoft Shared\ClickToRun" | C:\Windows\System32\expand.exe | — | OInstallLite_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 5.00 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 964 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2132 | "taskkill.exe" /t /f /IM OfficeC2RClient.exe | C:\Windows\System32\taskkill.exe | — | OInstallLite_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2232 | WMIC /NAMESPACE:\\root\Microsoft\Windows\Defender PATH MSFT_MpPreference call Add ExclusionPath="C:\Users\admin\AppData\Local\Temp\OInstallLite_x64.exe" | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 2147749889 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | "C:\WINDOWS\System32\reg.exe" add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /v KeyManagementServiceName /t REG_SZ /d kms.loli.best /f | C:\Windows\System32\reg.exe | — | OInstallLite_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
34 273
Read events
34 000
Write events
147
Delete events
126
Modification events
| (PID) Process: | (4996) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (6948) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6948) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6948) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6948) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6948) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6948) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6948) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6948) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6948) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
230
Suspicious files
30
Text files
49
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6156 | powershell.exe | C:\Users\admin\AppData\Local\Temp\over592263\i640.cab | — | |
MD5:— | SHA256:— | |||
| 7052 | OInstallLite_x64.exe | C:\Users\admin\AppData\Local\Temp\files\Configure.xml | text | |
MD5:F693E4FB8D3907E6CC44A34E1CC87296 | SHA256:CDCD3FA3CB1EBFAFC98273AE52632F80B95CB9D25933EE1C7D2FDEC640B264D0 | |||
| 7052 | OInstallLite_x64.exe | C:\Users\admin\AppData\Local\Temp\files\setup.exe | executable | |
MD5:6B6F44E4EF1EE8FB94EA28AED02964FB | SHA256:CAF295438040ECA0632D475EEECF51A16307A23CB87DCFCE796D274E8E8FF221 | |||
| 6948 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ver.txt | text | |
MD5:3665AC70F8EA7D7730BE7589C963BFFD | SHA256:83D89198DA6437ED226DCBB3F64FBB1CAD8773CAA6F460E01543B87031300BEF | |||
| 6948 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lvbnbw32.2cp.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4540 | files.dat | C:\Users\admin\AppData\Local\Temp\files\x86\cleanospp.exe | executable | |
MD5:98821A7A5737D656633D10A3AFB724BD | SHA256:04BA4487F95290E0B0557B44300C18F637FBAF0872EE96E3111013B8A1539F25 | |||
| 6156 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jqkkyck3.4k4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4540 | files.dat | C:\Users\admin\AppData\Local\Temp\files\x64\msvcr100.dll | executable | |
MD5:DF3CA8D16BDED6A54977B30E66864D33 | SHA256:1D1A1AE540BA132F998D60D3622F0297B6E86AE399332C3B47462D7C0F560A36 | |||
| 6948 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_t2ecv0wm.iwr.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7052 | OInstallLite_x64.exe | C:\Users\admin\AppData\Local\Temp\files\files.dat | executable | |
MD5:BB5569B15D68C10B7FF2D96B45825120 | SHA256:4E3B13B56BEC0E41778E6506430282BBBD75CCAA600FD4B645CE37DD95B44C8E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
45
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6156 | powershell.exe | GET | — | 152.199.21.175:80 | http://officecdn.microsoft.com/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/i640.cab | unknown | — | — | whitelisted |
1828 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1044 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1044 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6796 | powershell.exe | GET | 200 | 152.199.21.175:80 | http://officecdn.microsoft.com/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/i641033.cab | unknown | — | — | whitelisted |
6140 | svchost.exe | GET | 206 | 95.168.195.202:80 | http://95.168.195.202/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/s640.cab?cacheHostOrigin=officecdn.microsoft.com | unknown | — | — | unknown |
6140 | svchost.exe | GET | 206 | 95.168.195.202:80 | http://95.168.195.202/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/s640.cab?cacheHostOrigin=officecdn.microsoft.com | unknown | — | — | unknown |
6140 | svchost.exe | GET | 206 | 95.168.195.202:80 | http://95.168.195.202/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/s640.cab?cacheHostOrigin=officecdn.microsoft.com | unknown | — | — | unknown |
6140 | svchost.exe | GET | 200 | 95.168.195.202:80 | http://95.168.195.202/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/s640.cab.phf?cacheHostOrigin=officecdn.microsoft.com | unknown | — | — | unknown |
6140 | svchost.exe | GET | 206 | 95.168.195.202:80 | http://95.168.195.202/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/s640.cab?cacheHostOrigin=officecdn.microsoft.com | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7008 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6260 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
7008 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6948 | powershell.exe | 52.109.89.117:443 | mrodevicemgr.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 52.137.106.217:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1828 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1828 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
mrodevicemgr.officeapps.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
officecdn.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |