| File name: | notpetya |
| Full analysis: | https://app.any.run/tasks/bbcb2d55-64fd-4b77-95c9-e252eb45ef39 |
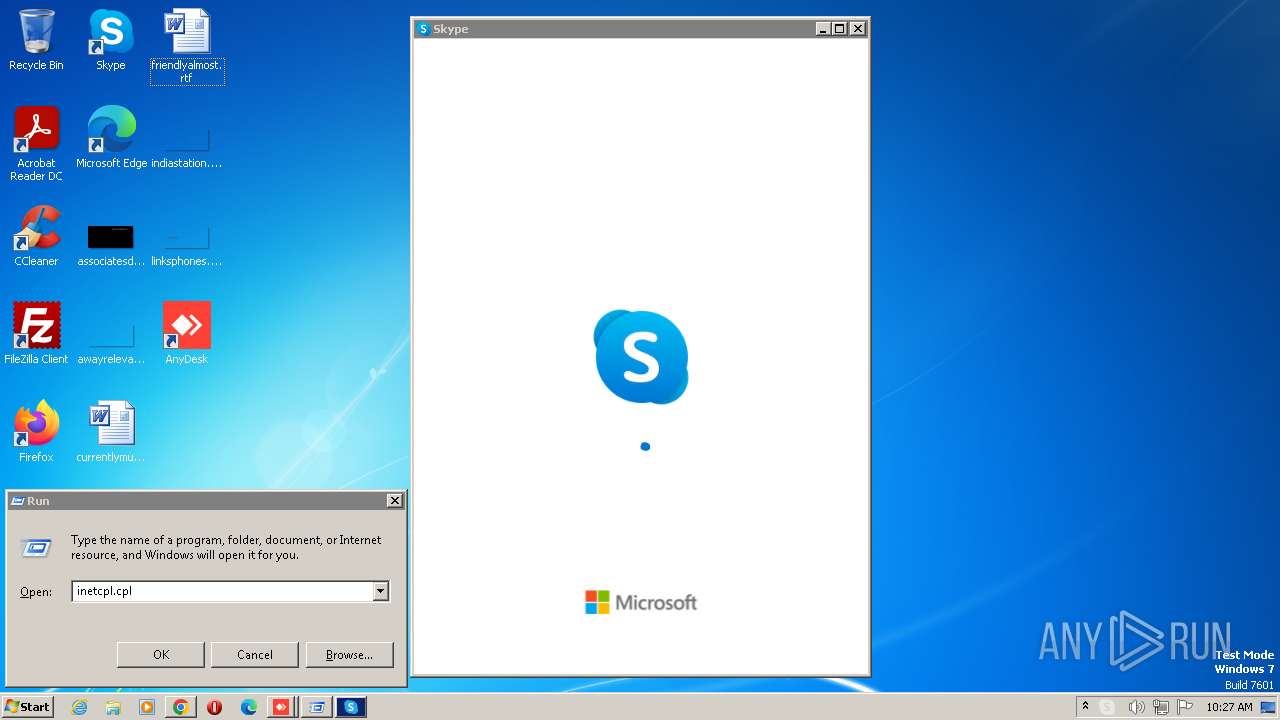
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2023, 09:22:46 |
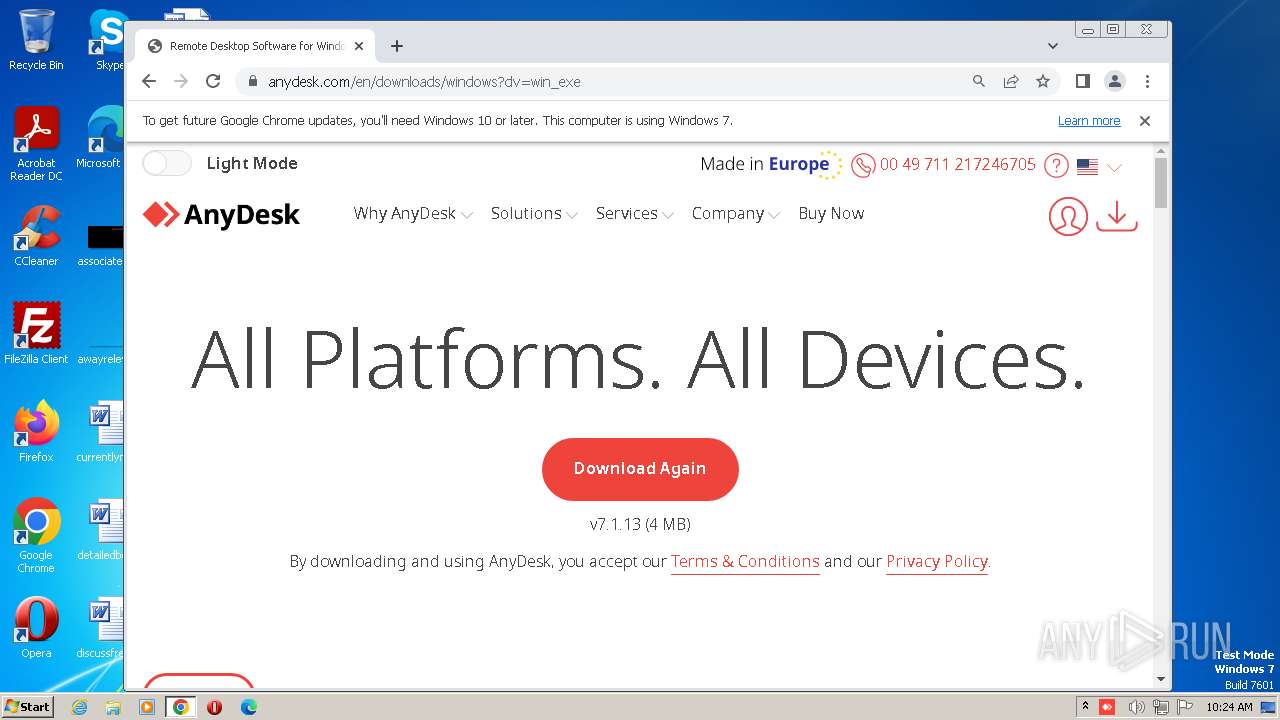
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (console) Intel 80386, for MS Windows |
| MD5: | 71B6A493388E7D0B40C83CE903BC6B04 |
| SHA1: | 34F917AABA5684FBE56D3C57D48EF2A1AA7CF06D |
| SHA256: | 027CC450EF5F8C5F653329641EC1FED91F694E0D229928963B30F6B0D7D3A745 |
| SSDEEP: | 6144:y/Bt80VmNTBo/x95ZjAetGDN3VFNq7pC+9OqFoK30b3ni5rdQY/CdUOs2:y/X4NTS/x9jNG+w+9OqFoK323qdQYKUG |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3576)
Unusual connection from system programs
- rundll32.exe (PID: 3752)
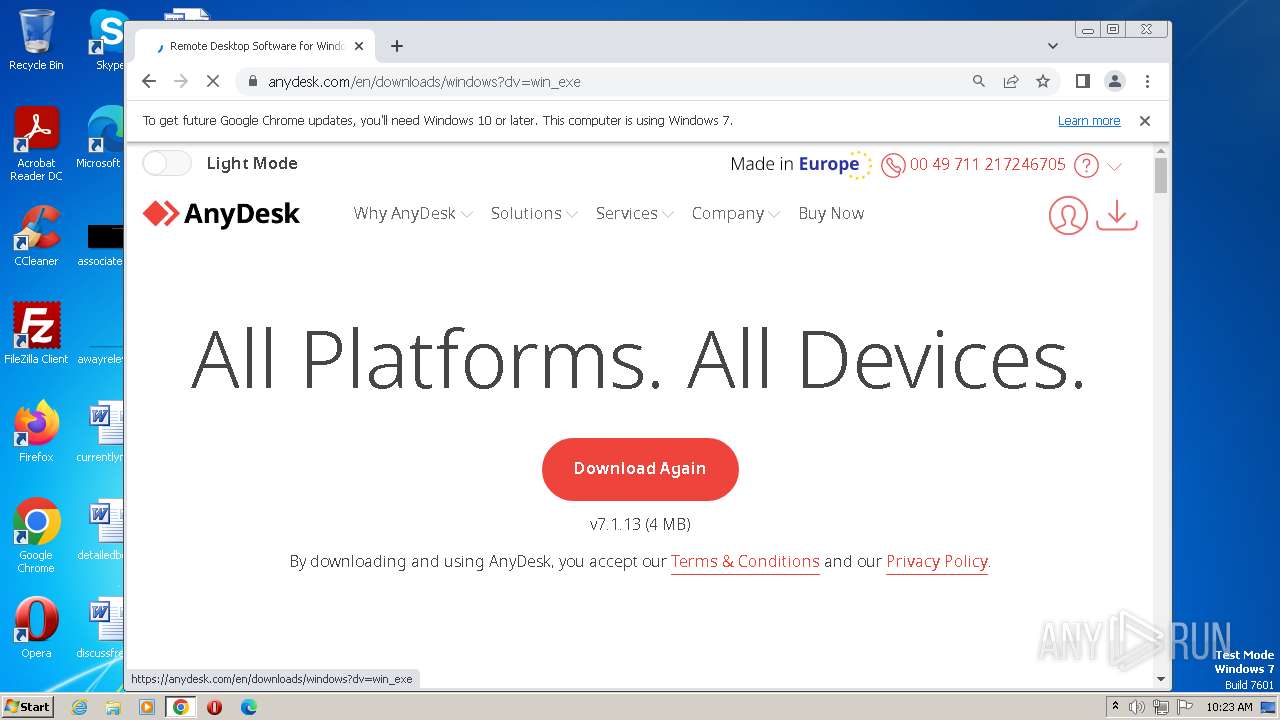
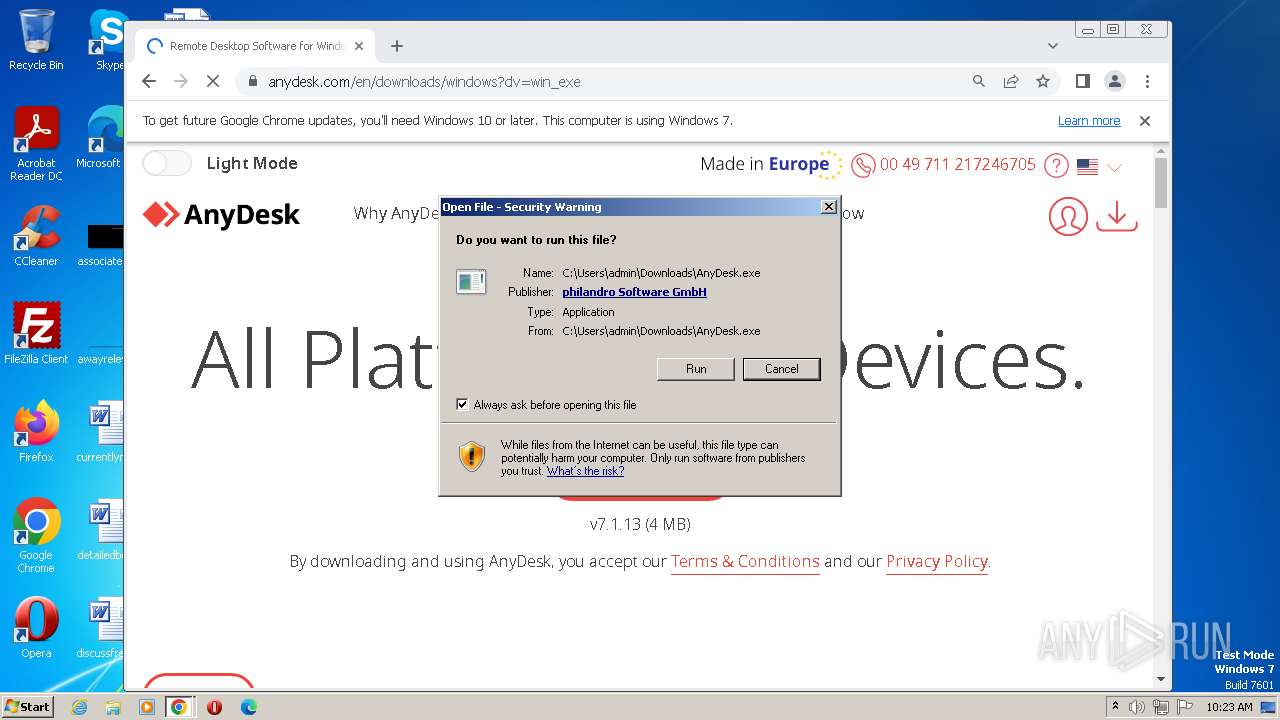
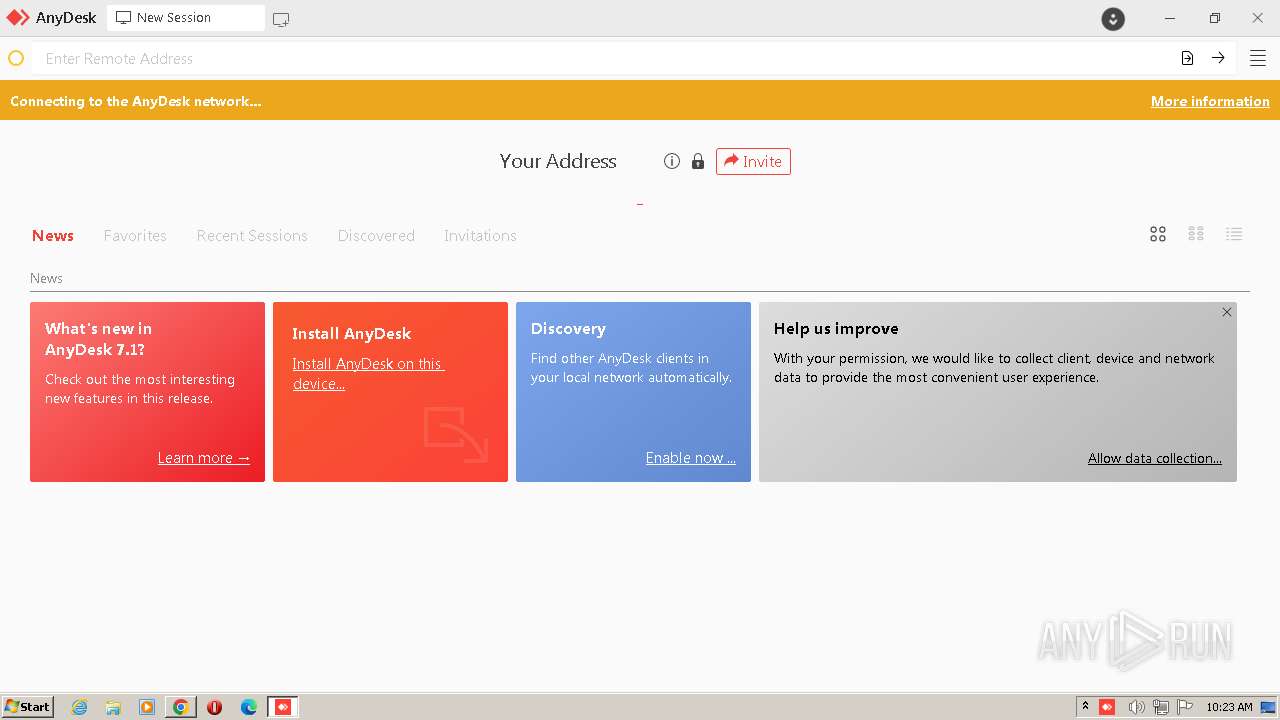
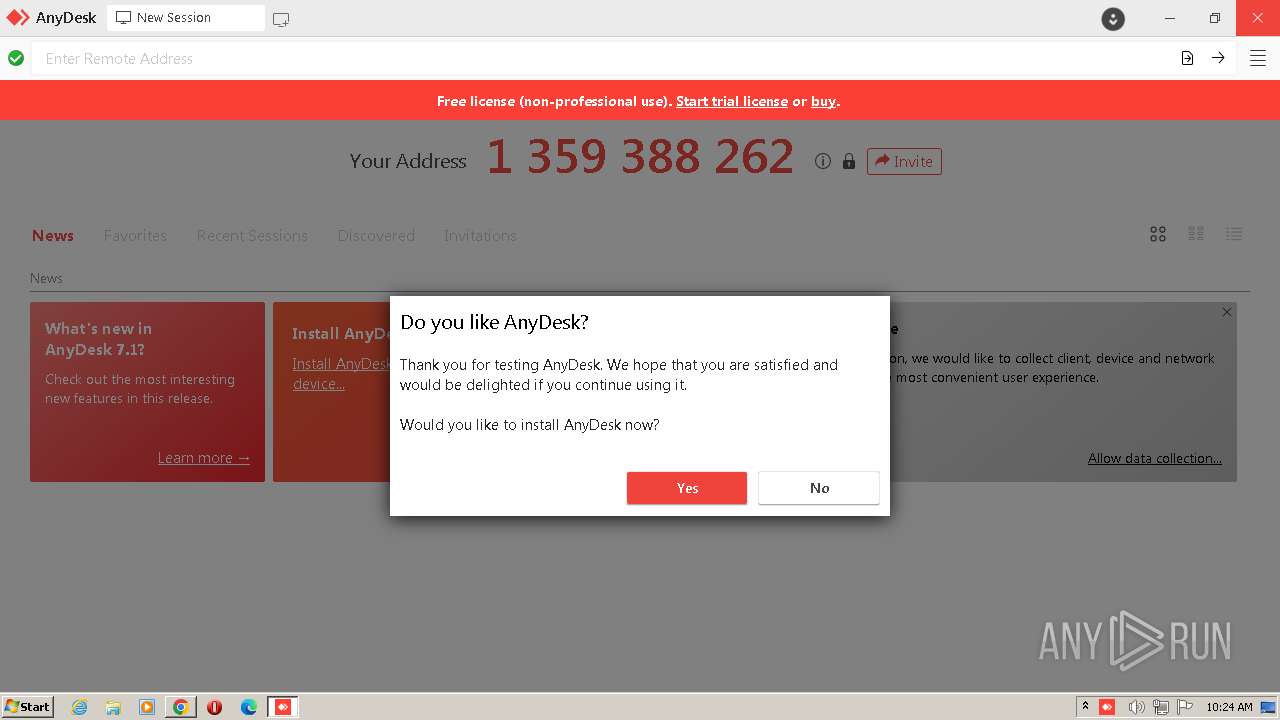
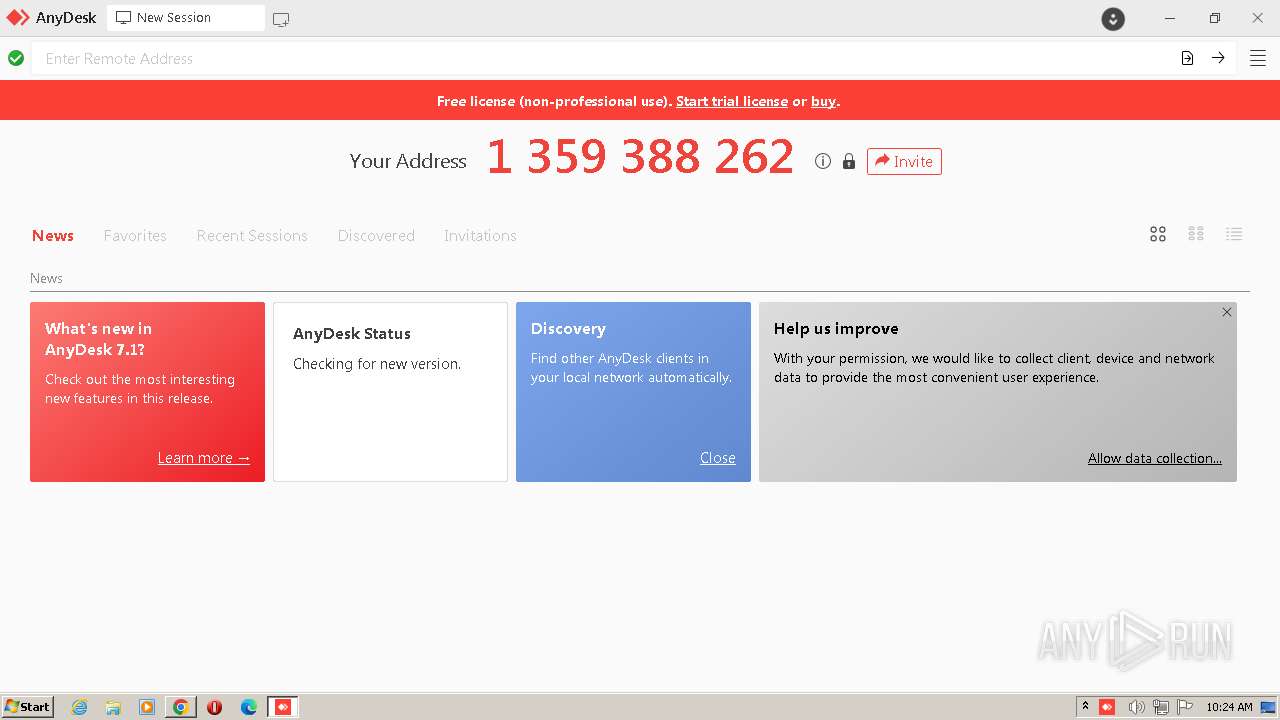
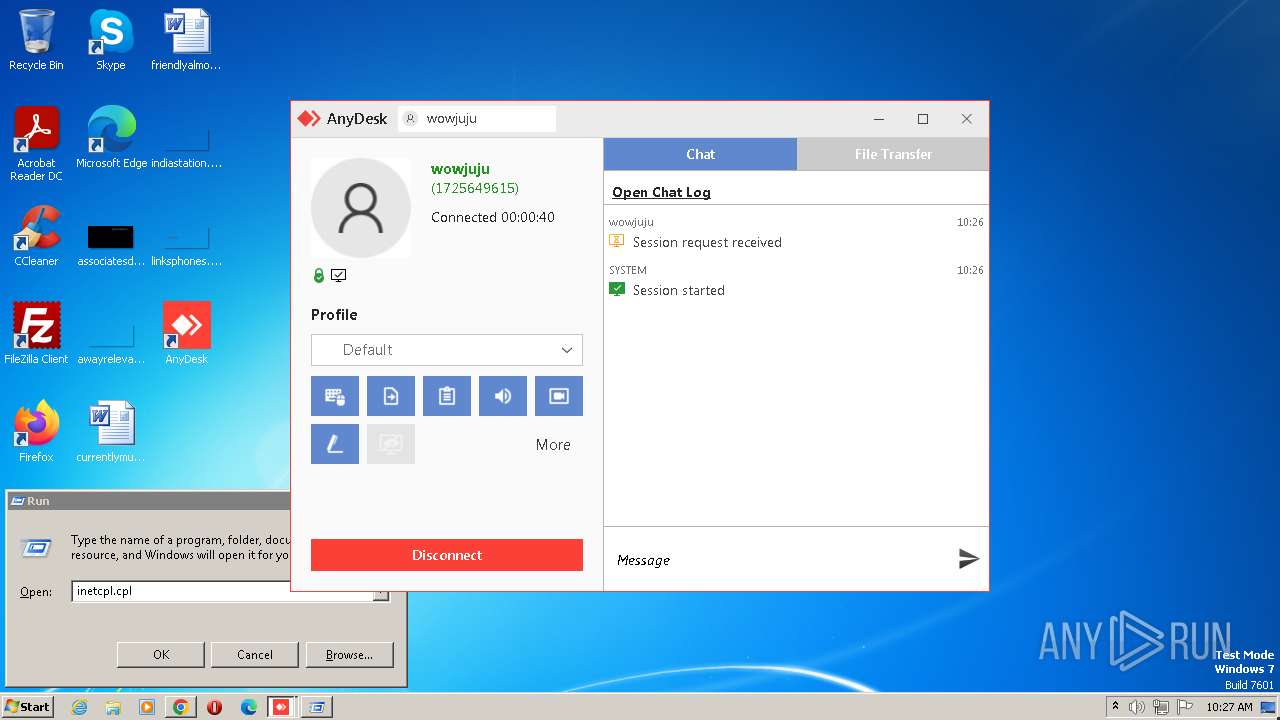
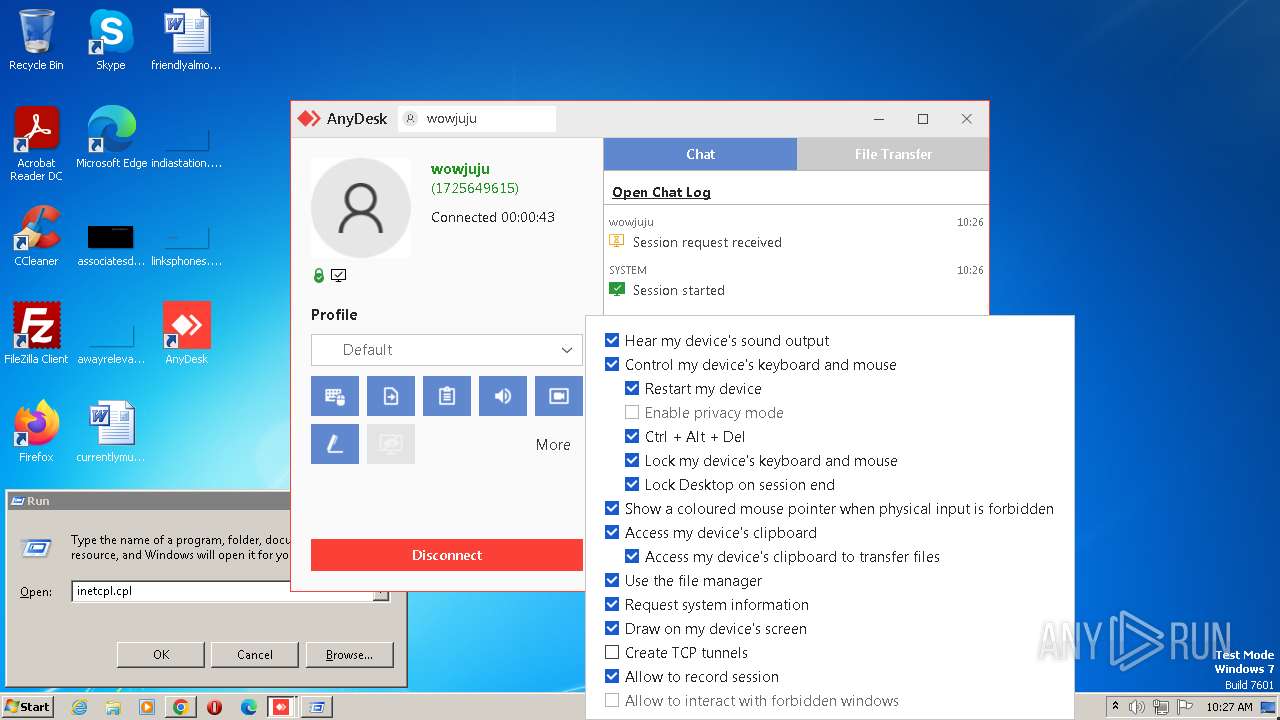
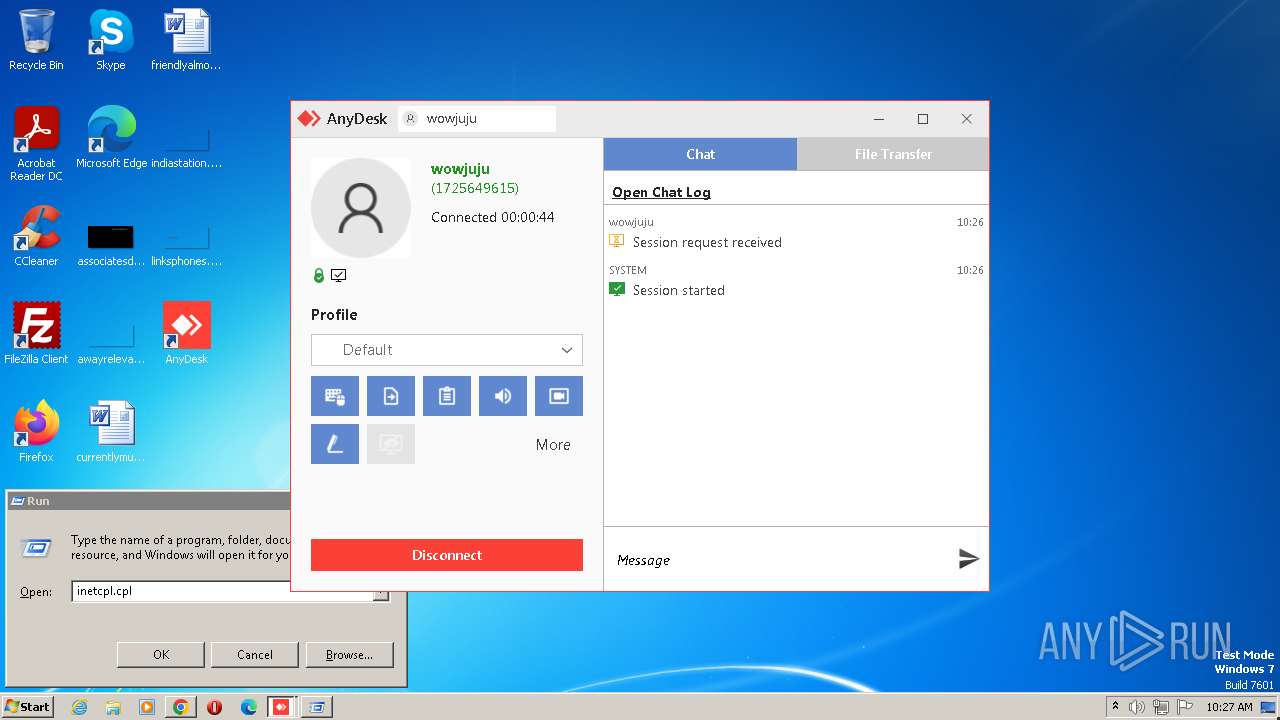
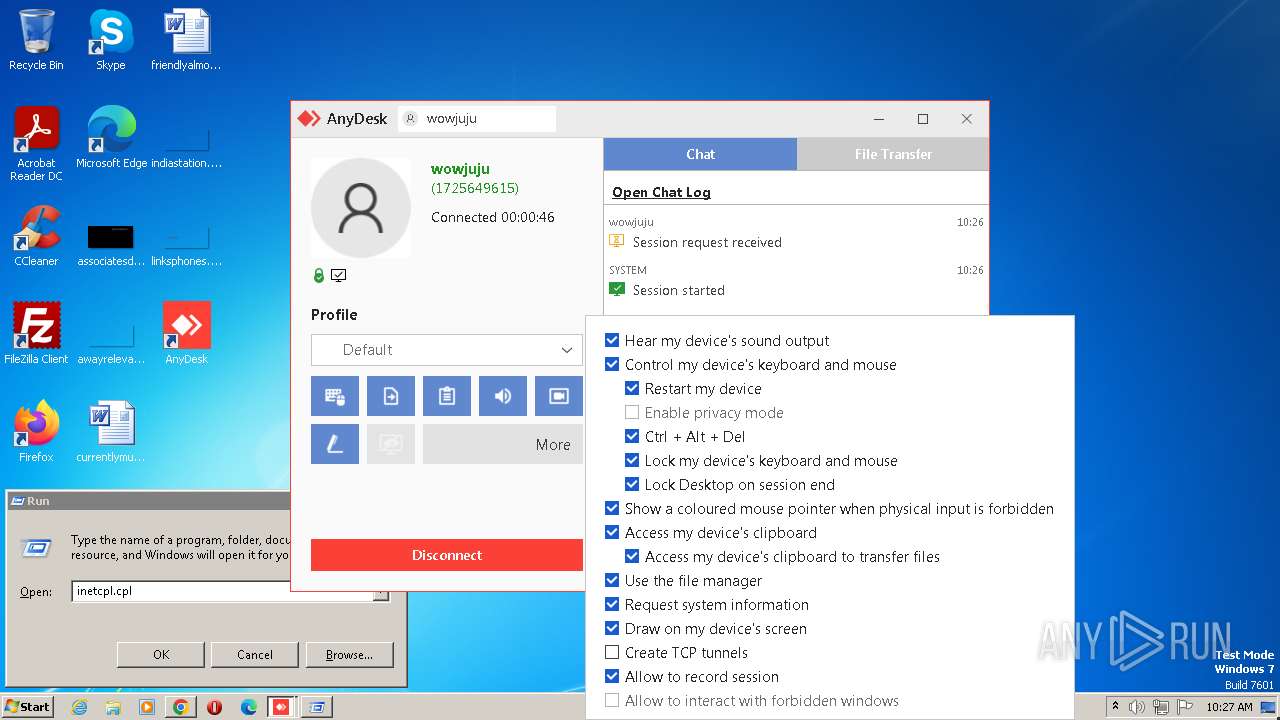
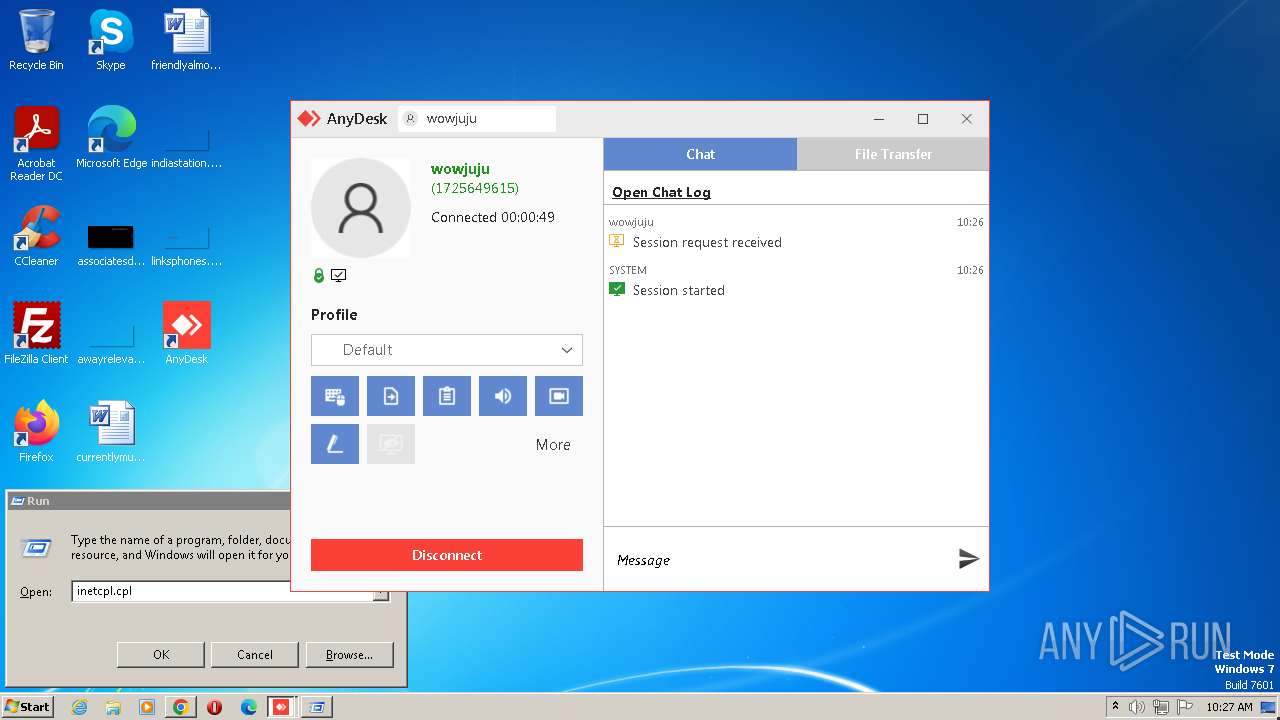
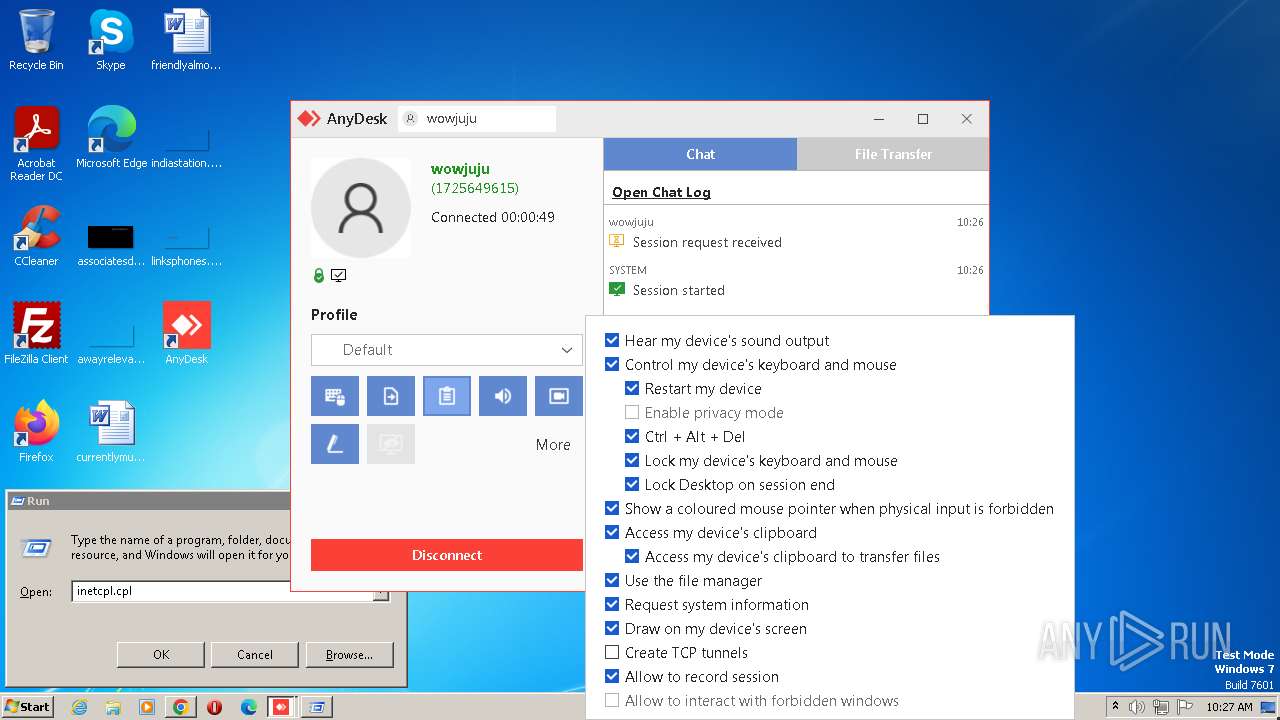
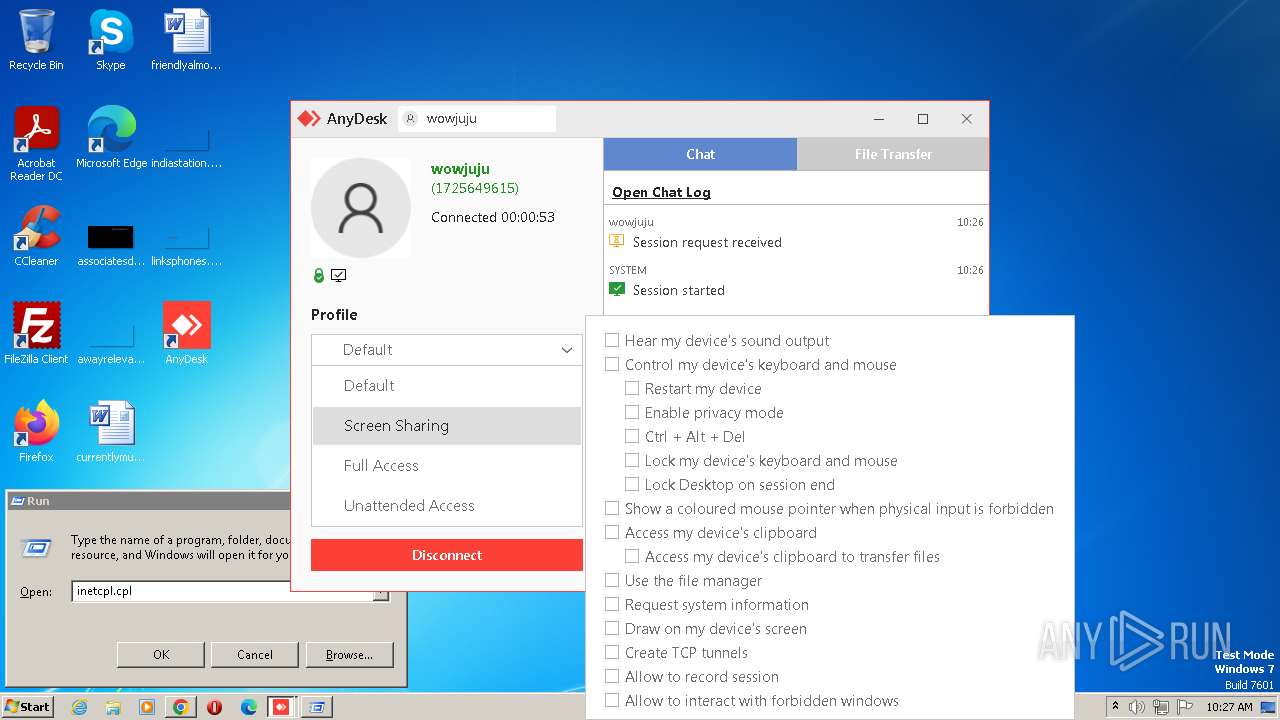
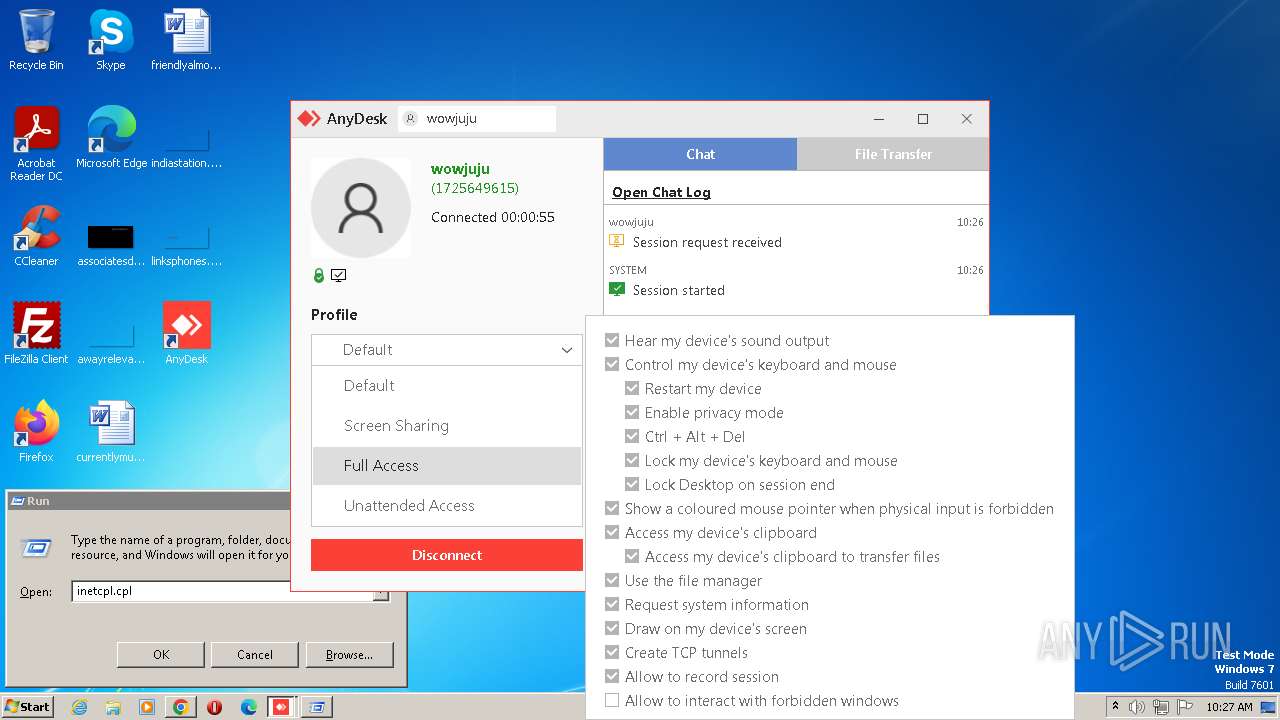
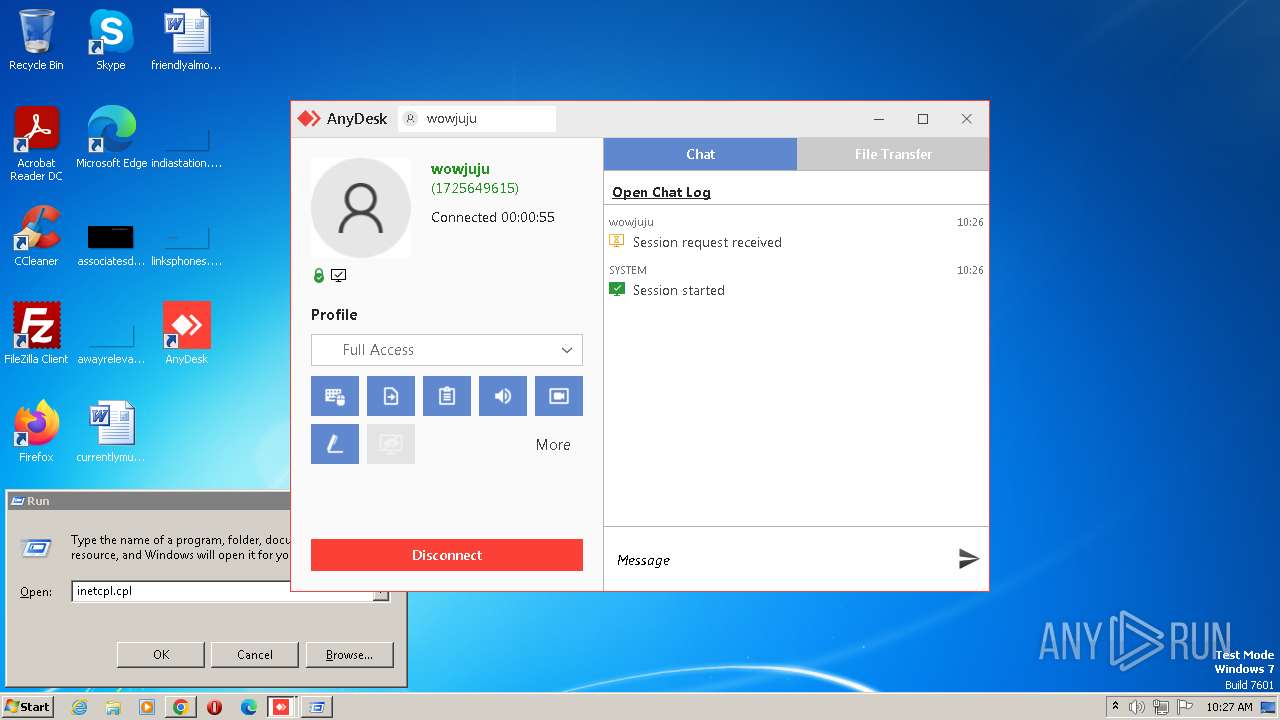
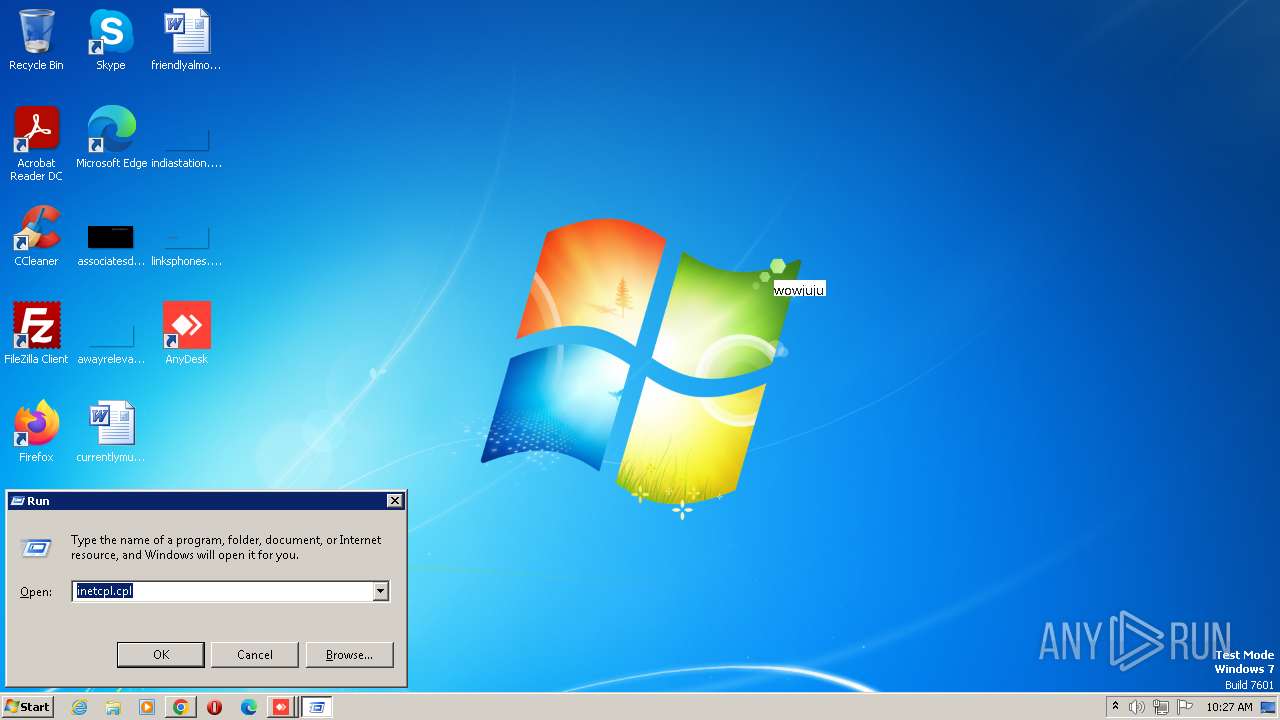
Application was dropped or rewritten from another process
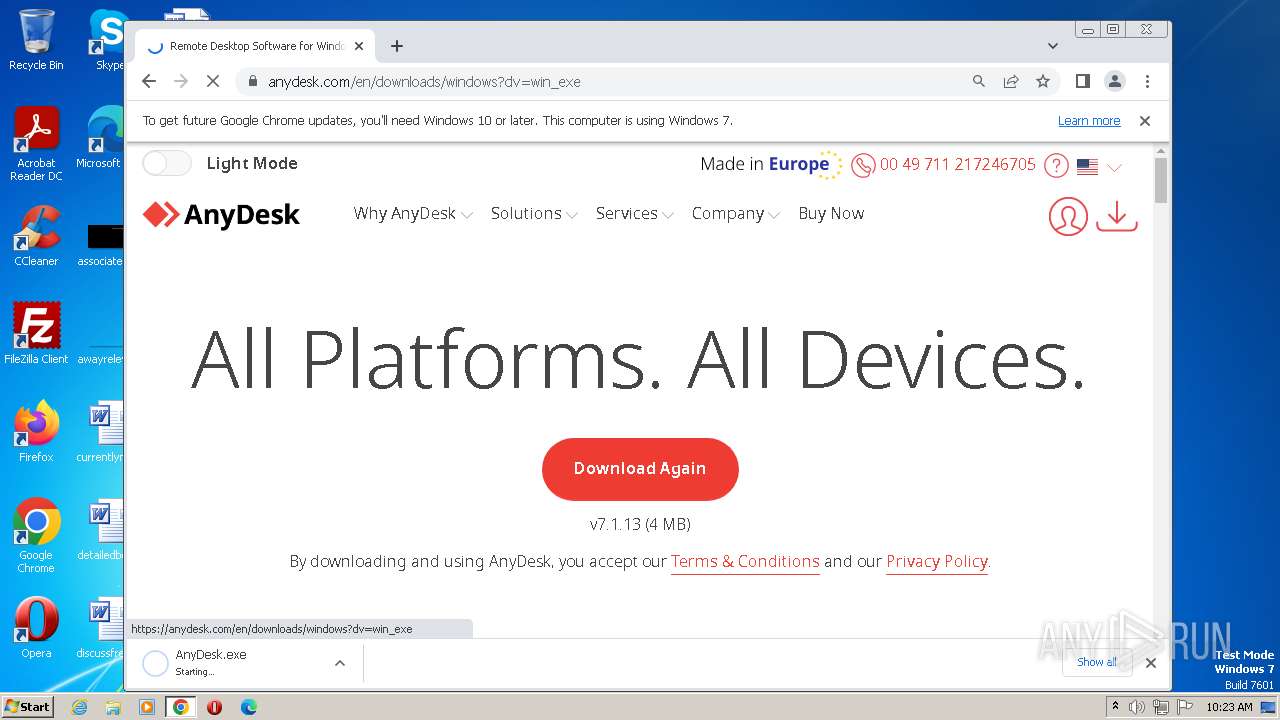
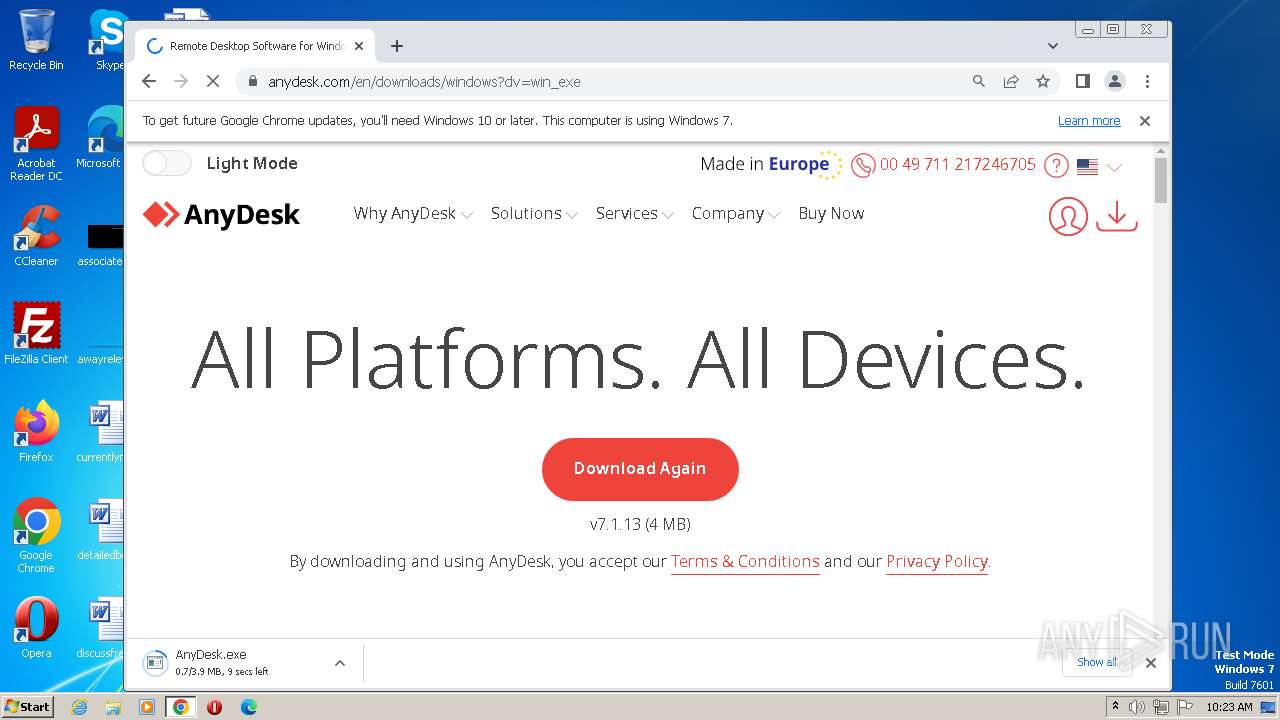
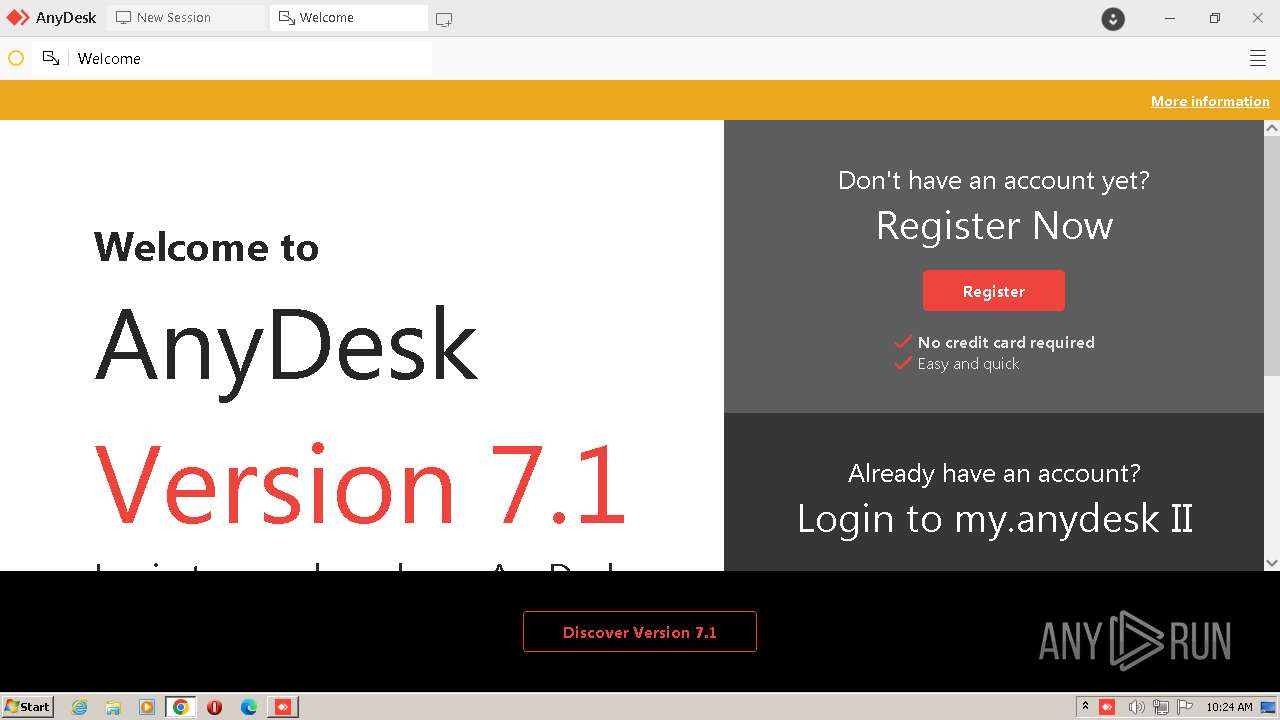
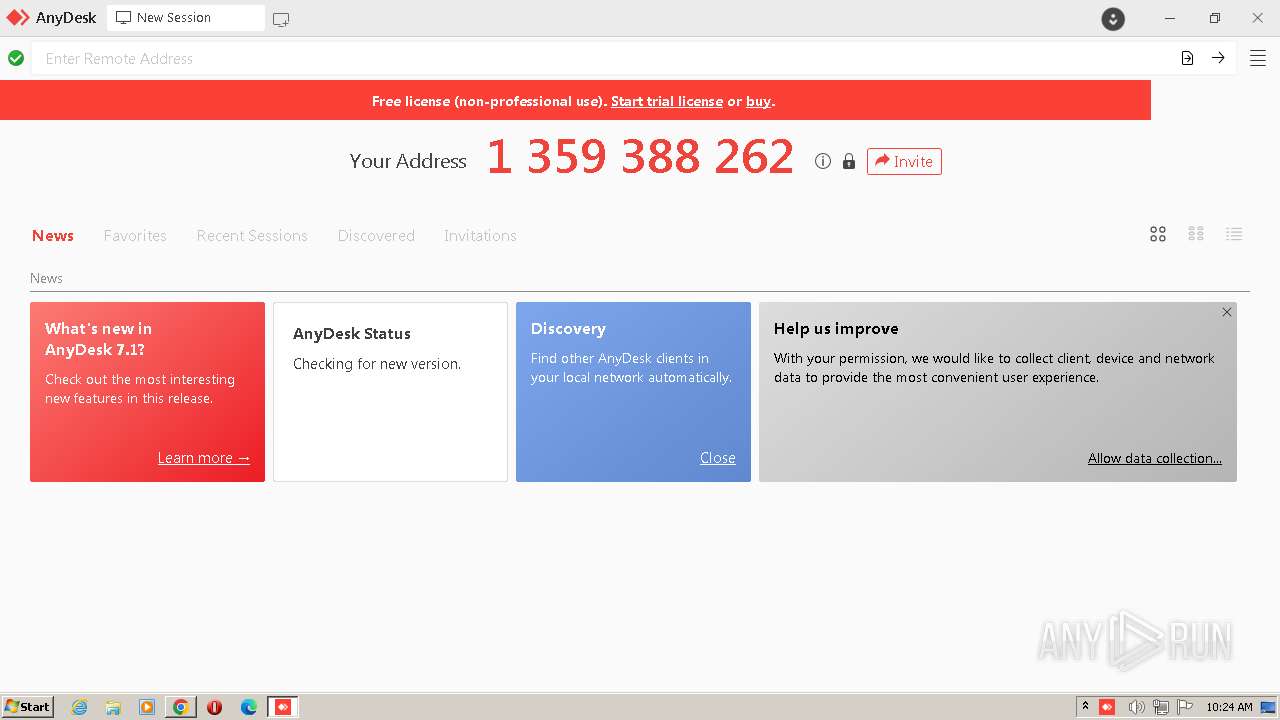
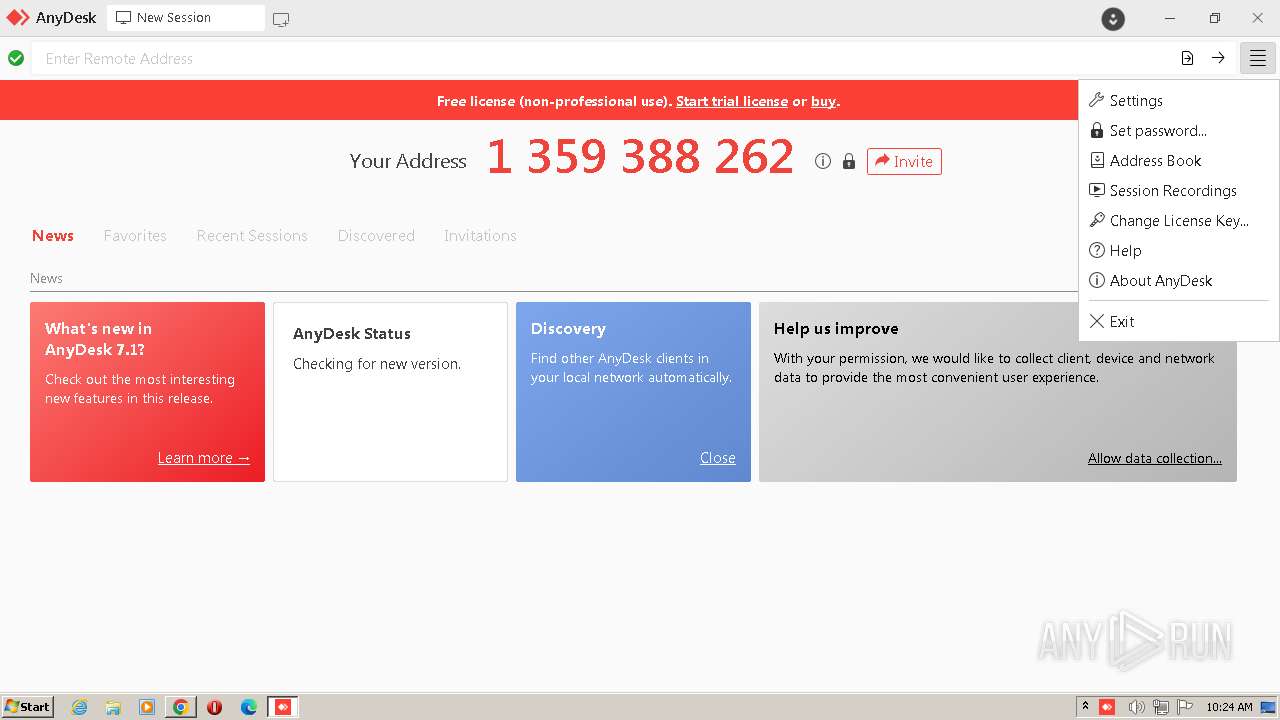
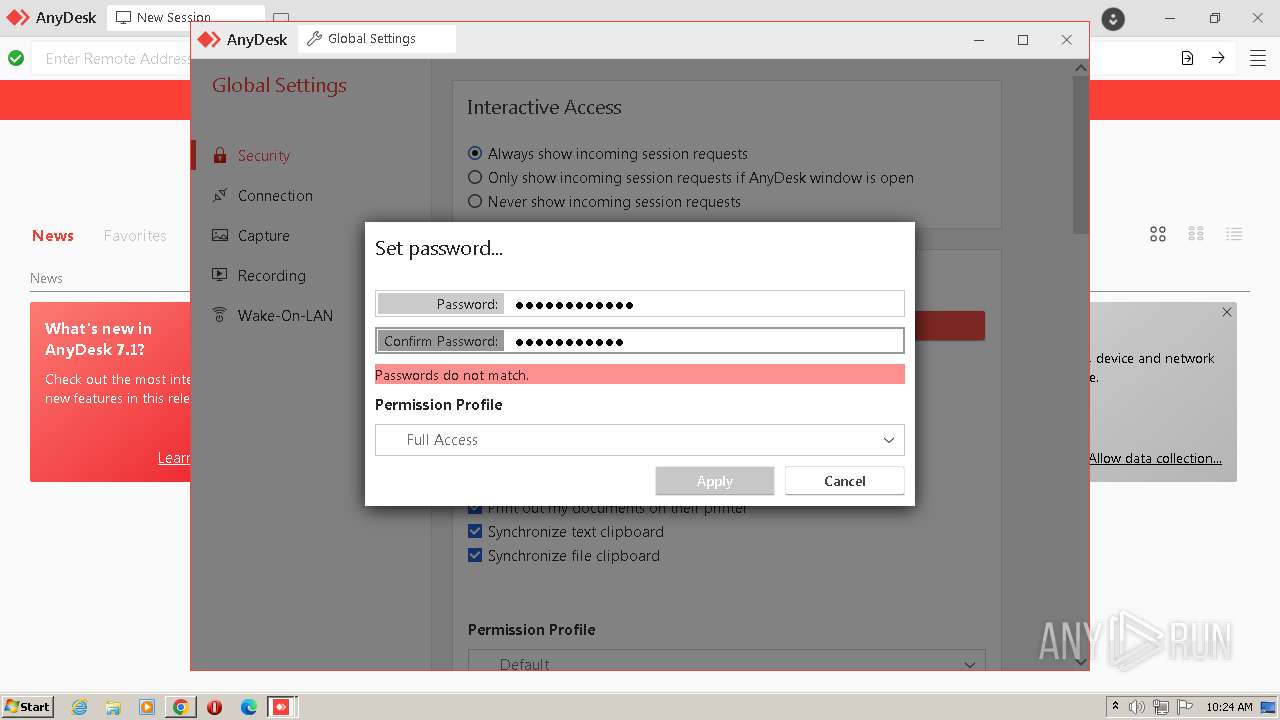
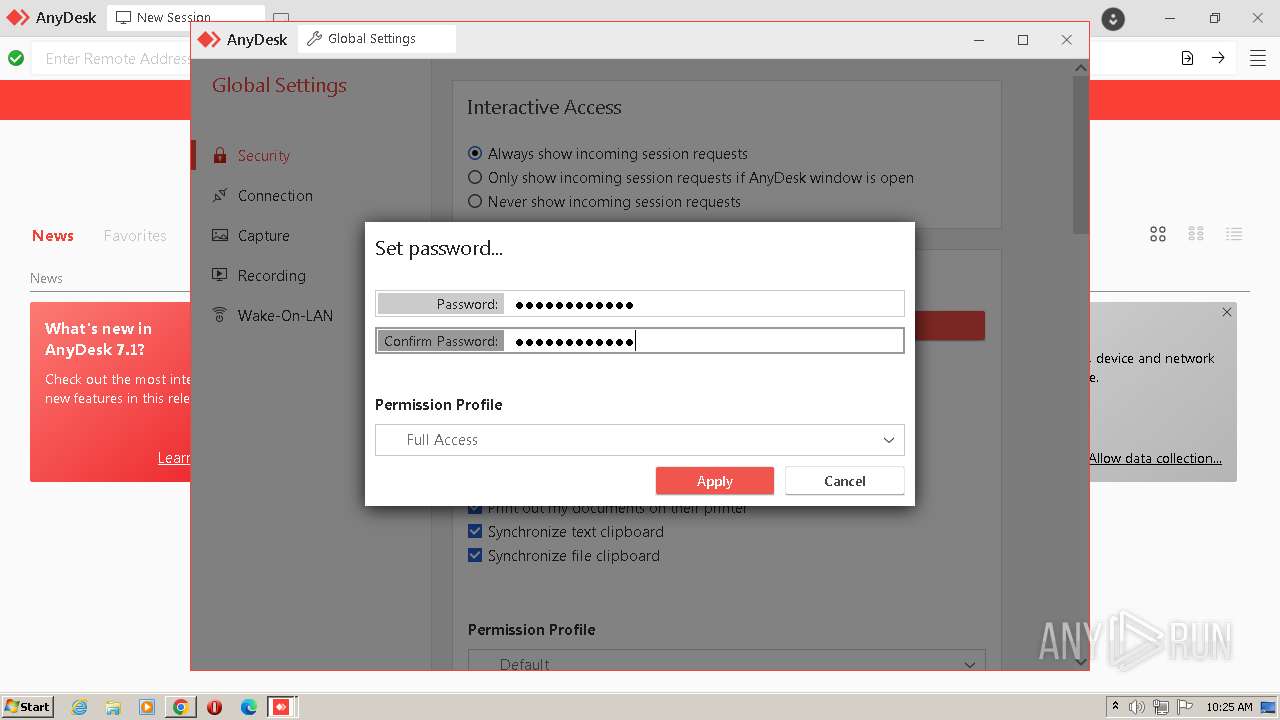
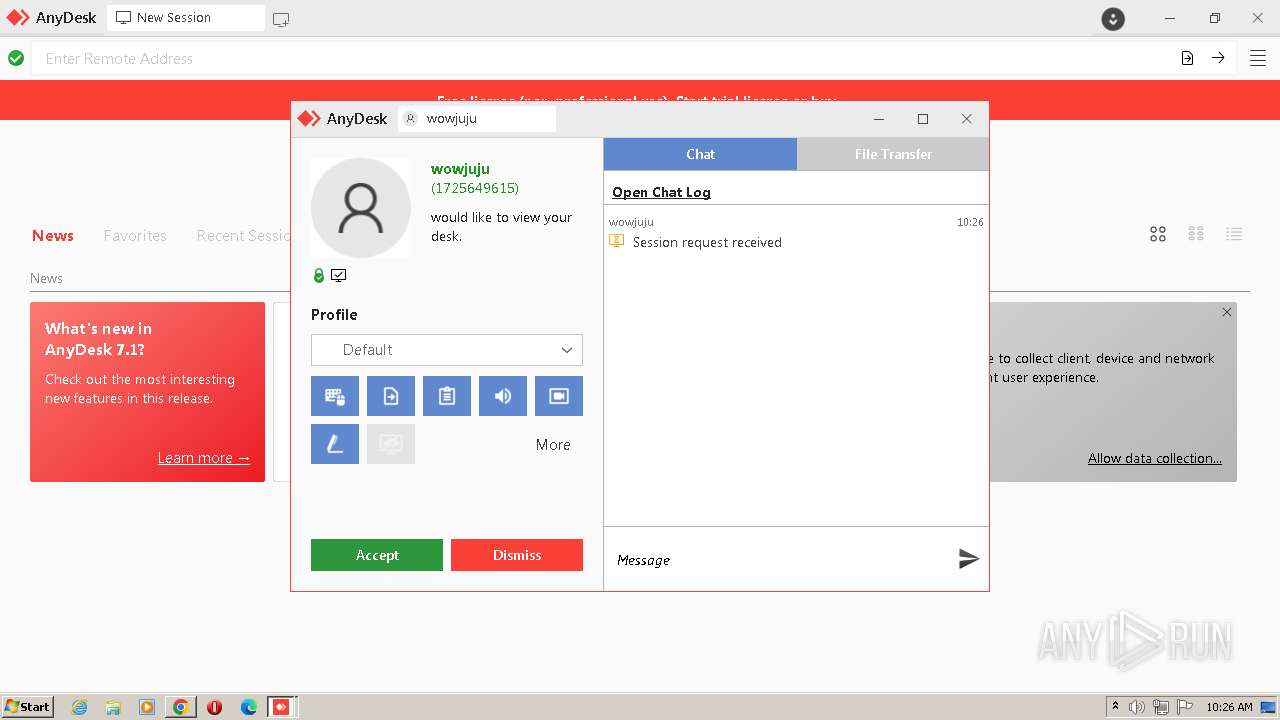
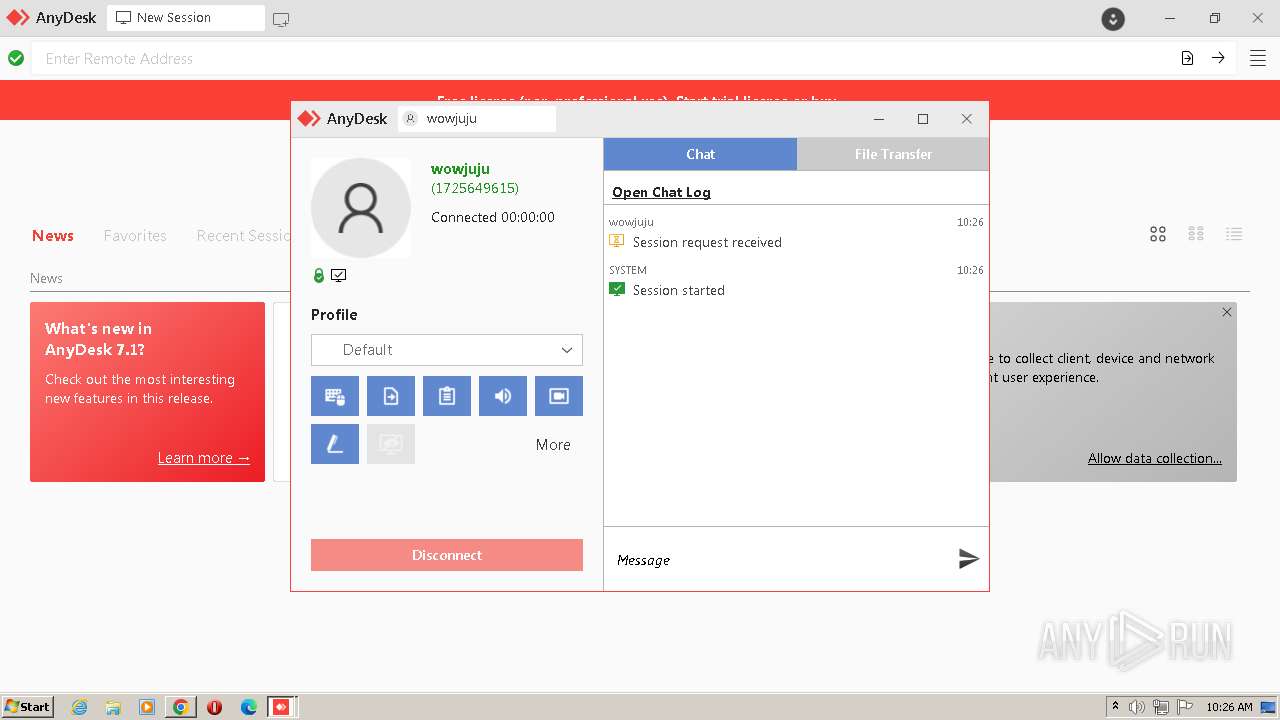
- AnyDesk.exe (PID: 3548)
- AnyDesk.exe (PID: 3640)
- AnyDesk.exe (PID: 4072)
- AnyDesk.exe (PID: 608)
- AnyDesk.exe (PID: 588)
- AnyDesk.exe (PID: 3628)
- AnyDesk.exe (PID: 620)
- AnyDesk.exe (PID: 2696)
- AnyDesk.exe (PID: 3472)
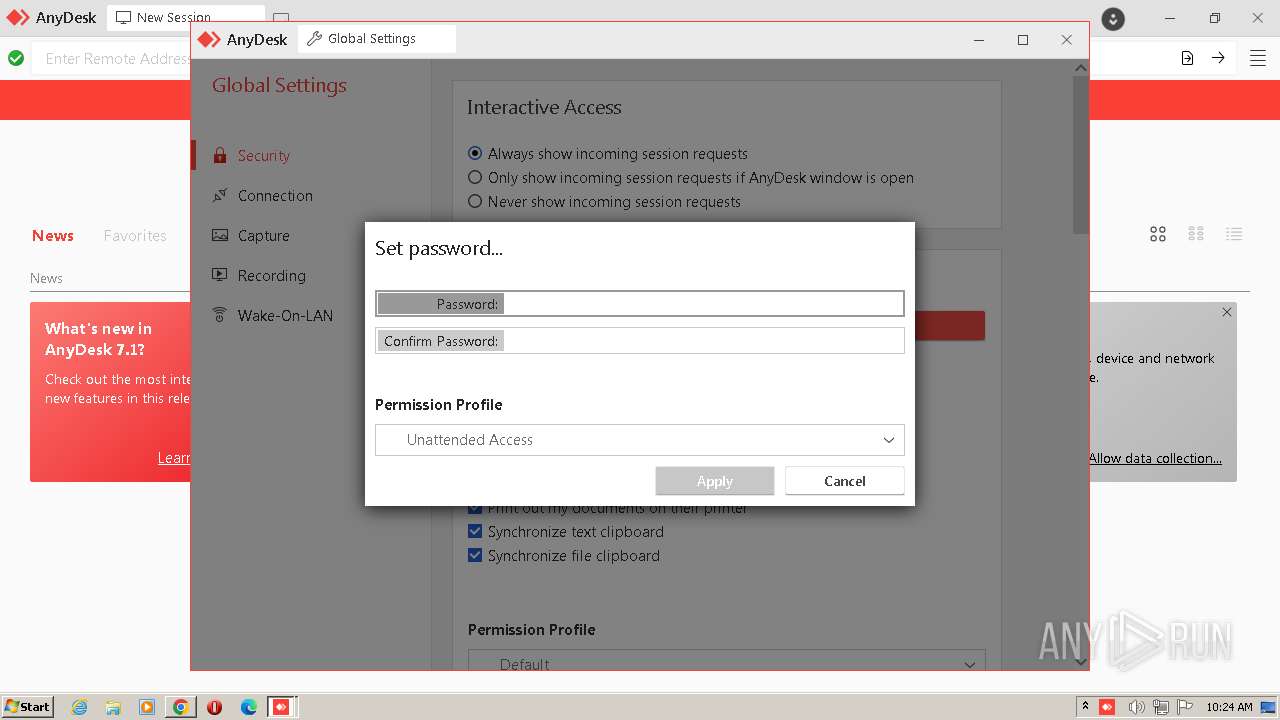
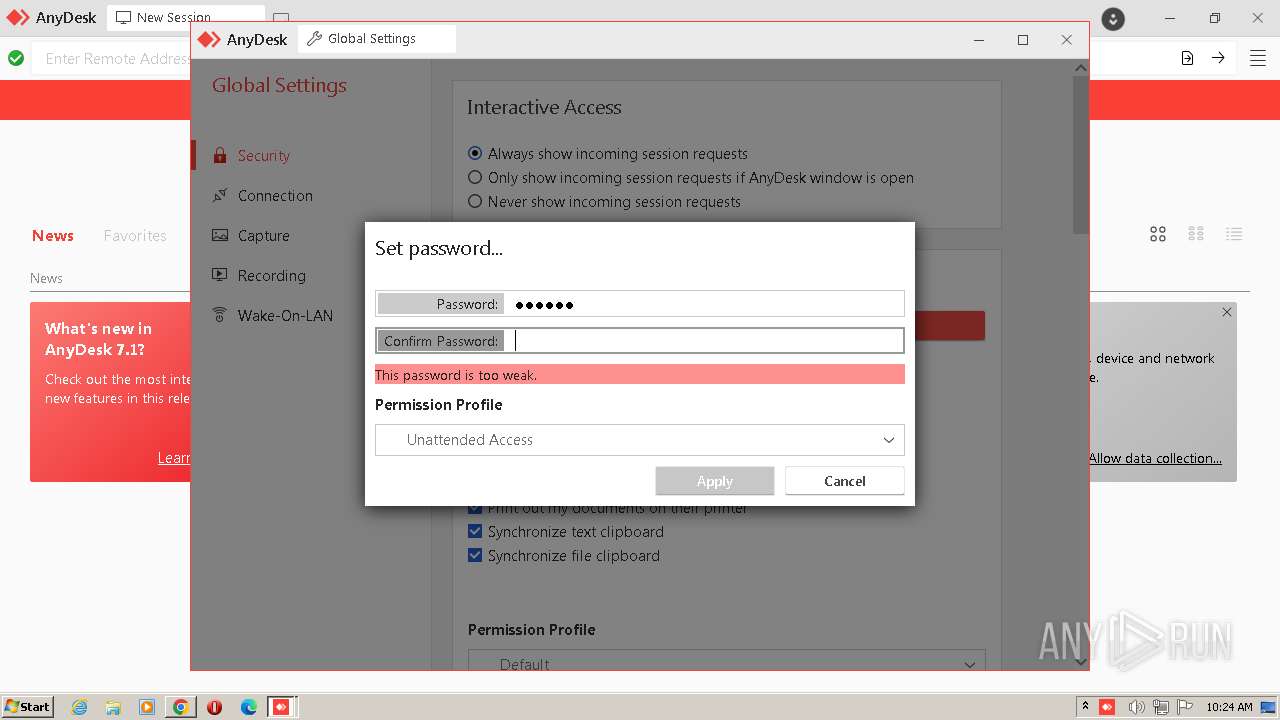
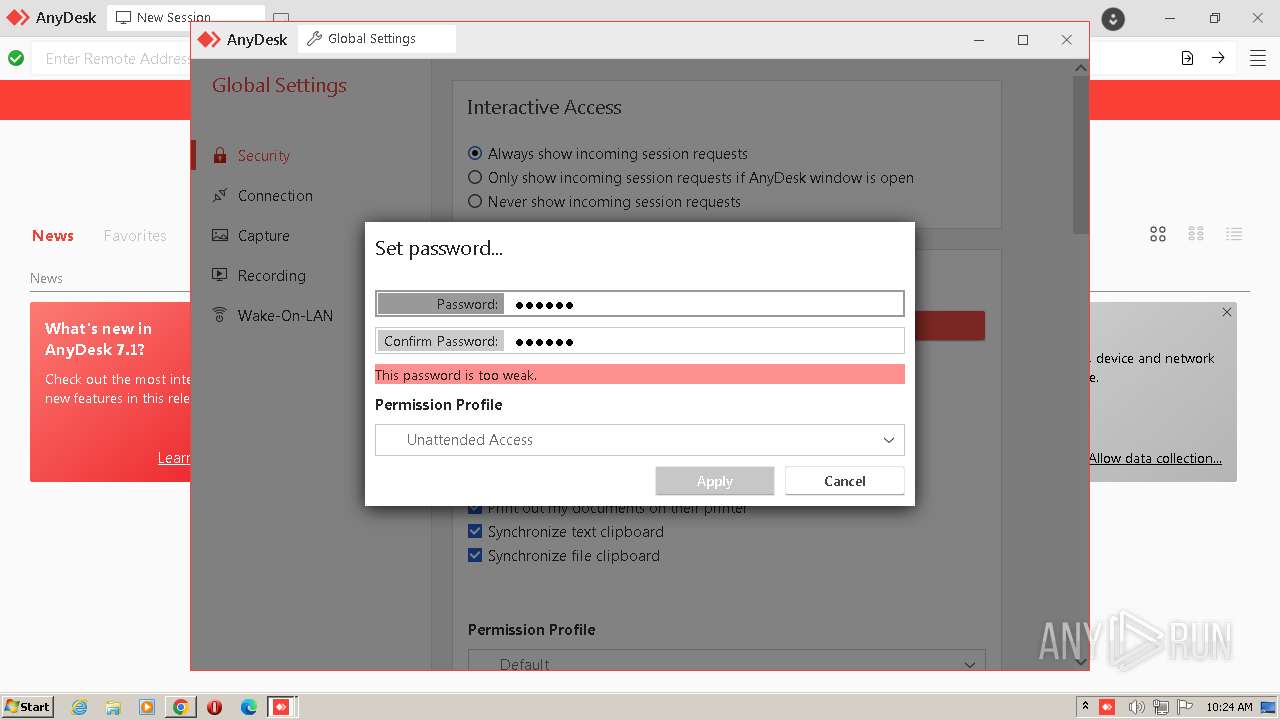
Actions looks like stealing of personal data
- rundll32.exe (PID: 3752)
- Skype.exe (PID: 3444)
- Skype-Setup.tmp (PID: 2816)
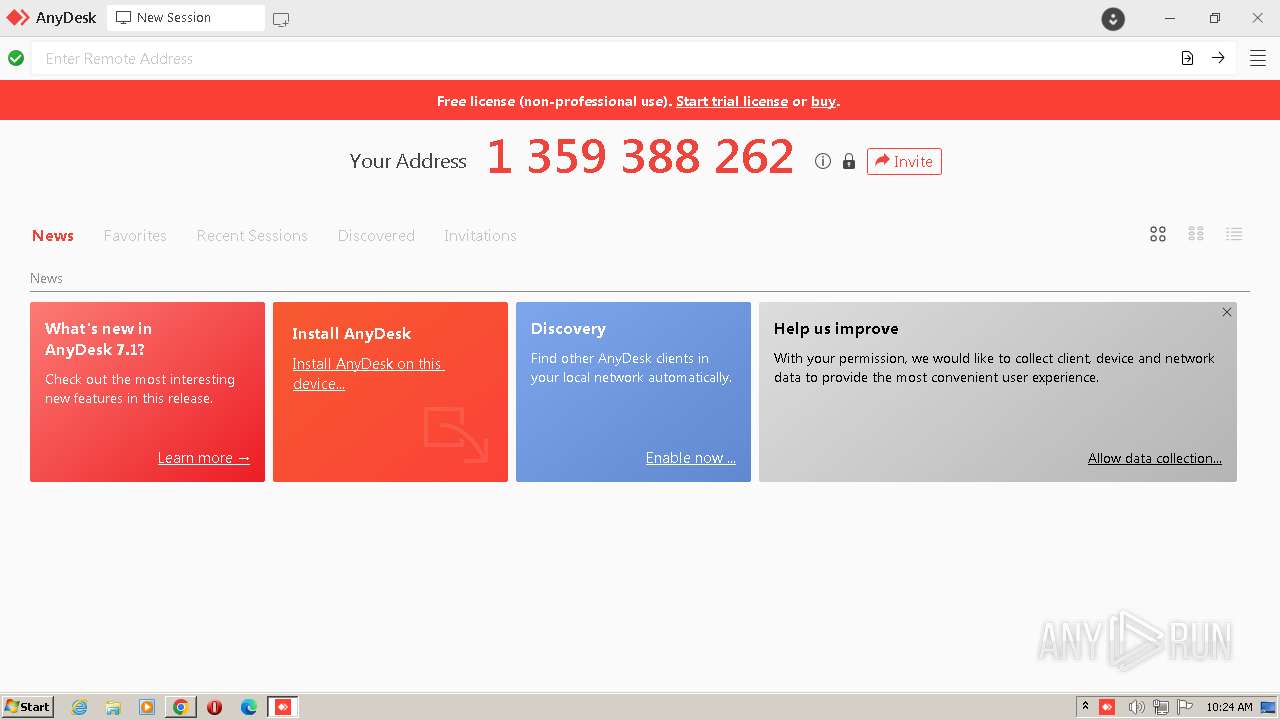
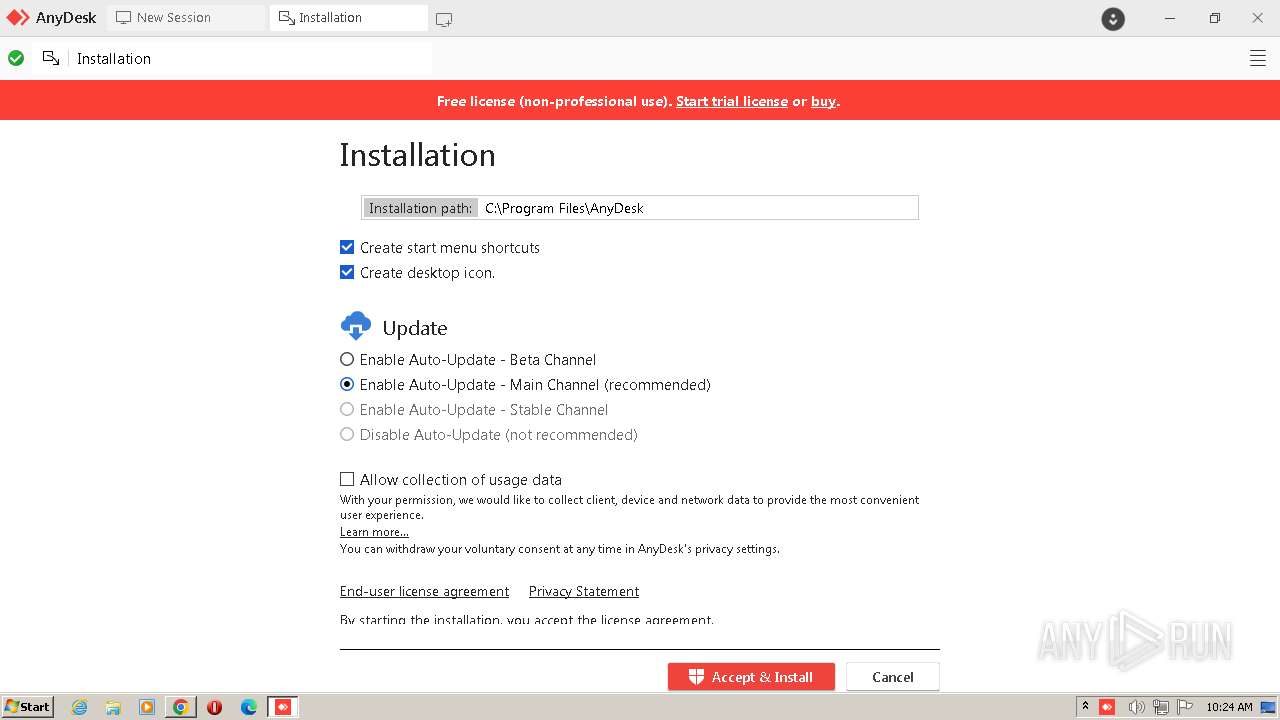
Create files in the Startup directory
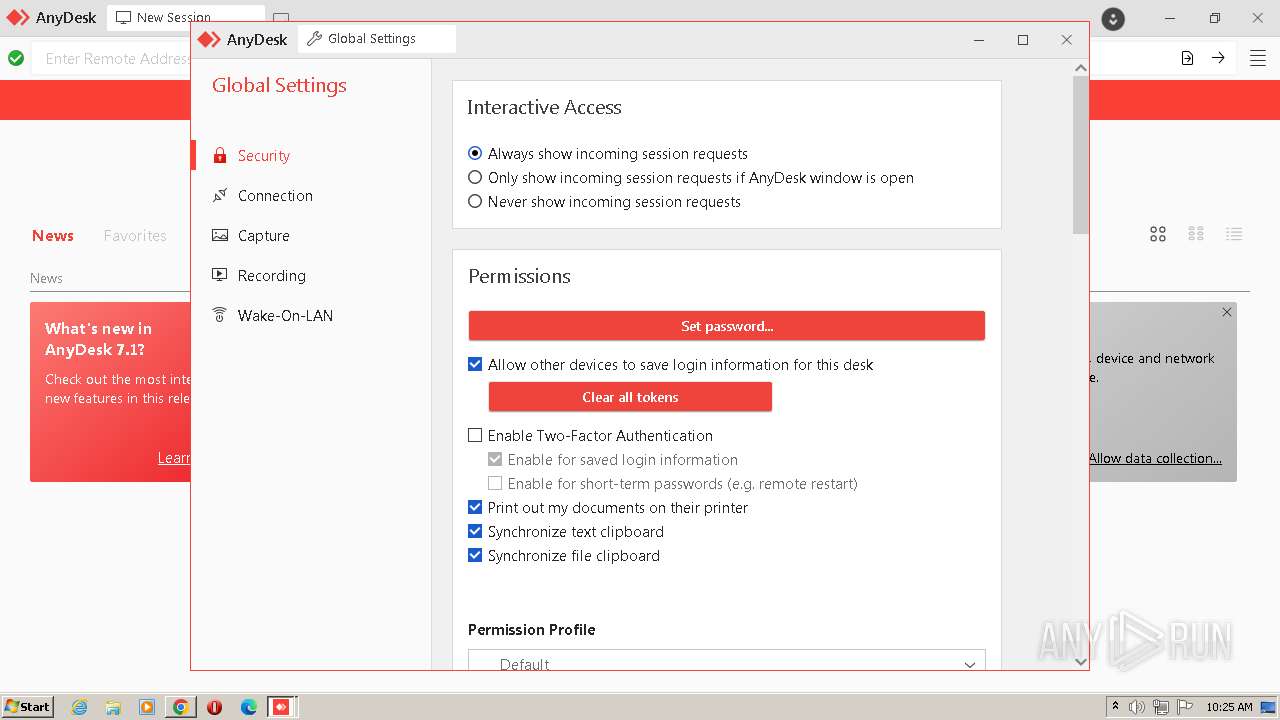
- AnyDesk.exe (PID: 608)
Loads dropped or rewritten executable
- Skype.exe (PID: 2376)
- Skype.exe (PID: 3156)
- Skype.exe (PID: 1884)
- Skype.exe (PID: 1004)
- Skype.exe (PID: 792)
- Skype.exe (PID: 1700)
Changes the autorun value in the registry
- reg.exe (PID: 3948)
SUSPICIOUS
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 3752)
Executable content was dropped or overwritten
- rundll32.exe (PID: 3752)
- AnyDesk.exe (PID: 608)
- AnyDesk.exe (PID: 588)
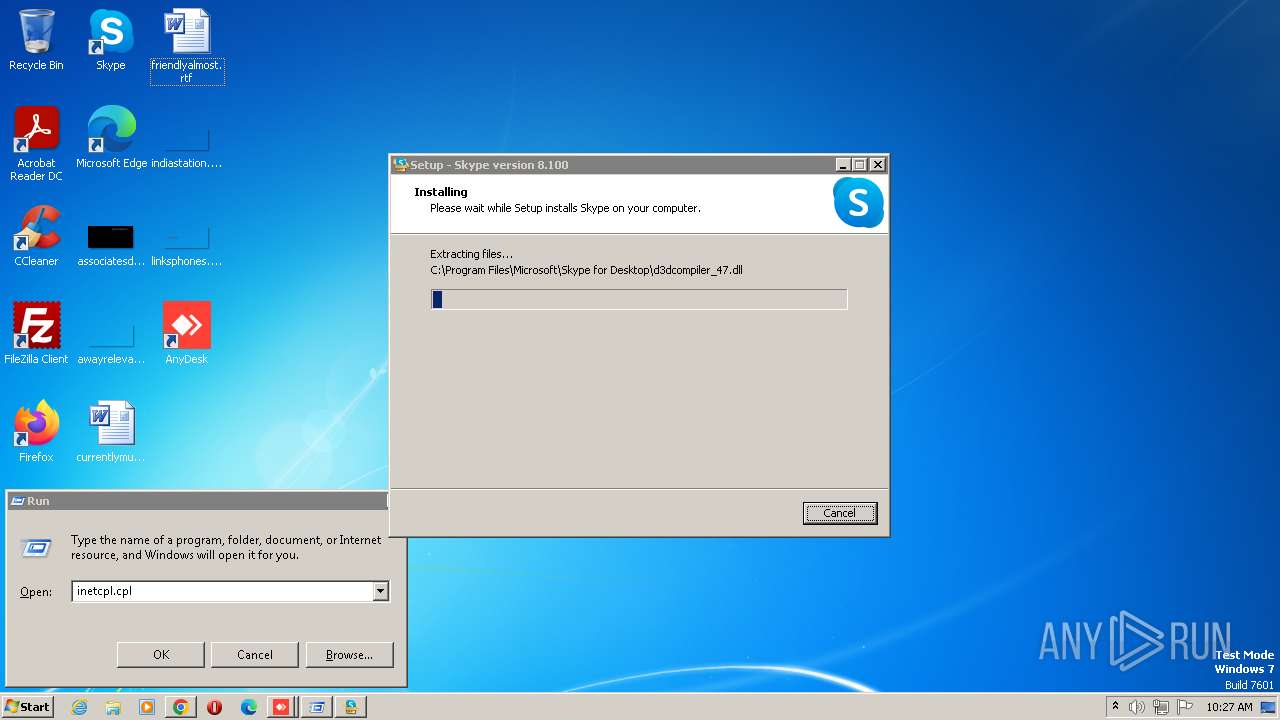
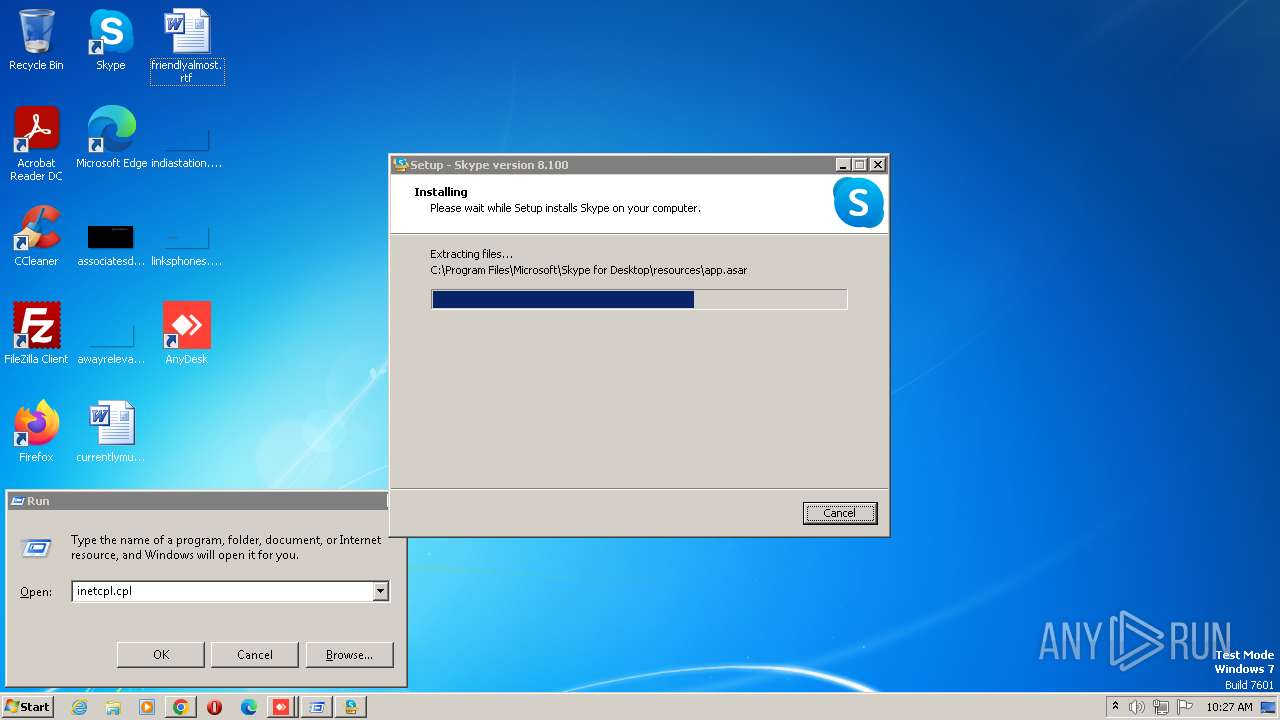
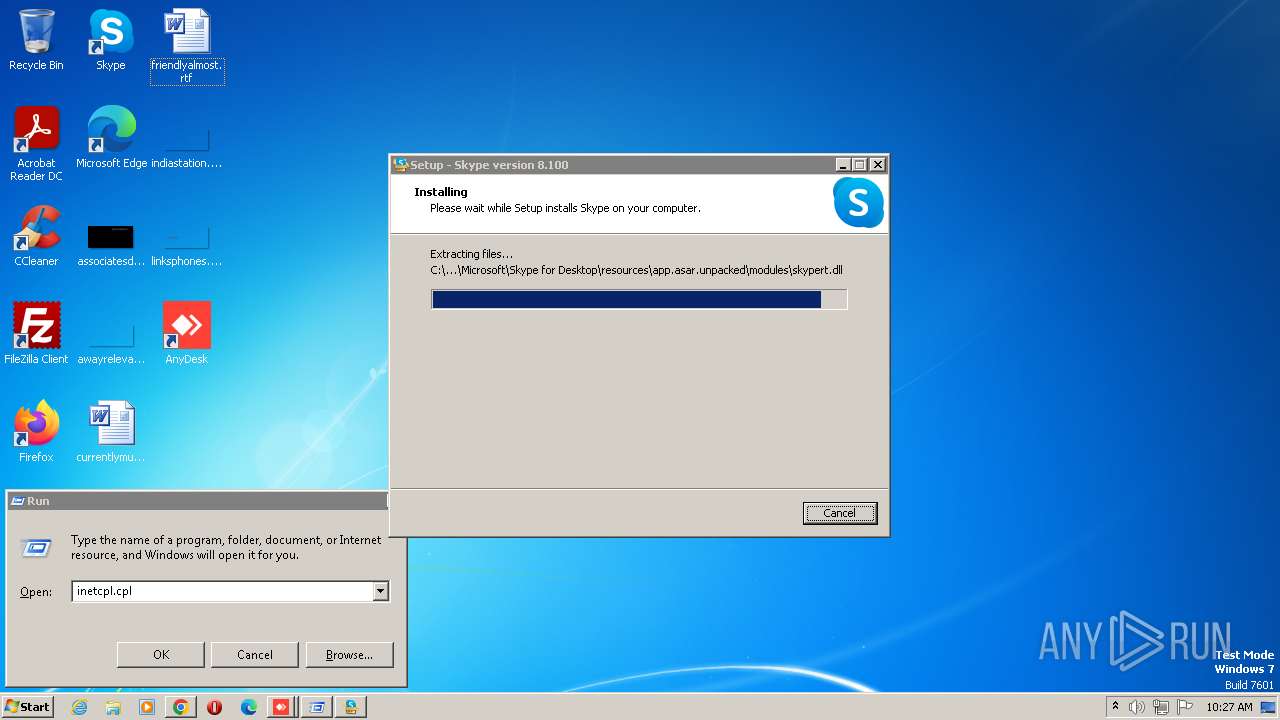
- Skype-Setup.exe (PID: 2484)
- Skype-Setup.exe (PID: 292)
- Skype-Setup.tmp (PID: 2816)
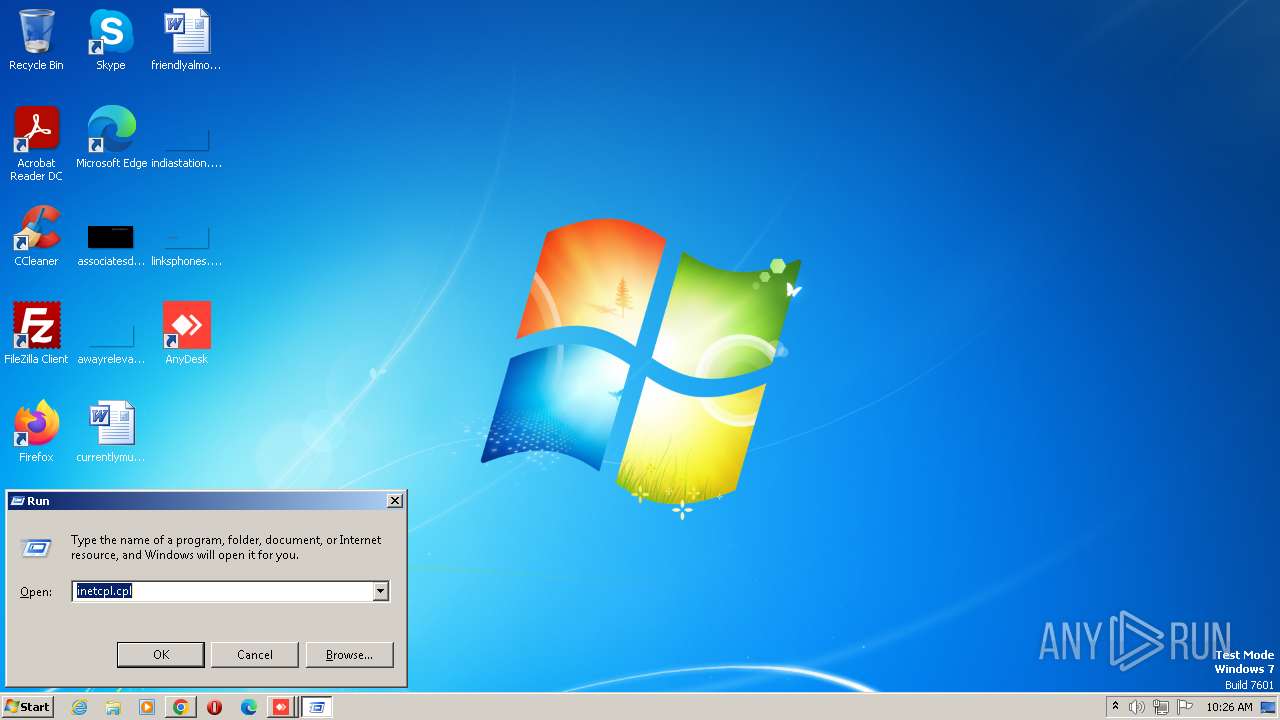
Reads the Internet Settings
- rundll32.exe (PID: 3752)
- AnyDesk.exe (PID: 3640)
- AnyDesk.exe (PID: 3548)
- AnyDesk.exe (PID: 3628)
- AnyDesk.exe (PID: 620)
- Skype-Setup.tmp (PID: 2816)
- Skype-Setup.tmp (PID: 1128)
- Skype.exe (PID: 2376)
Cleans NTFS data stream (Zone Identifier)
- AnyDesk.exe (PID: 3548)
Application launched itself
- AnyDesk.exe (PID: 3548)
- AnyDesk.exe (PID: 3628)
- AnyDesk.exe (PID: 588)
- Skype.exe (PID: 3444)
- Skype.exe (PID: 2376)
Creates a software uninstall entry
- AnyDesk.exe (PID: 588)
Executes as Windows Service
- AnyDesk.exe (PID: 588)
Searches for installed software
- AnyDesk.exe (PID: 588)
- AnyDesk.exe (PID: 3628)
- AnyDesk.exe (PID: 620)
- AnyDesk.exe (PID: 2696)
- AnyDesk.exe (PID: 3472)
- Skype-Setup.tmp (PID: 2816)
Connects to unusual port
- AnyDesk.exe (PID: 588)
Connects to the server without a host name
- rundll32.exe (PID: 3752)
Reads the Windows owner or organization settings
- Skype-Setup.tmp (PID: 2816)
Uses TASKKILL.EXE to kill process
- Skype-Setup.tmp (PID: 2816)
Uses REG/REGEDIT.EXE to modify registry
- Skype.exe (PID: 2376)
Reads settings of System Certificates
- Skype.exe (PID: 2376)
INFO
Loads main object executable
- rundll32.exe (PID: 3752)
The process checks LSA protection
- rundll32.exe (PID: 3752)
- AnyDesk.exe (PID: 3548)
- AnyDesk.exe (PID: 4072)
- AnyDesk.exe (PID: 3640)
- AnyDesk.exe (PID: 608)
- AnyDesk.exe (PID: 588)
- AnyDesk.exe (PID: 3628)
- AnyDesk.exe (PID: 620)
- AnyDesk.exe (PID: 2696)
- AnyDesk.exe (PID: 3472)
- Skype.exe (PID: 3444)
- Skype-Setup.tmp (PID: 1128)
- Skype-Setup.tmp (PID: 2816)
- taskkill.exe (PID: 3860)
- Skype.exe (PID: 2376)
- Skype.exe (PID: 1004)
- Skype.exe (PID: 792)
Create files in a temporary directory
- rundll32.exe (PID: 3752)
- Skype-Setup.exe (PID: 292)
- Skype-Setup.tmp (PID: 2816)
- Skype-Setup.exe (PID: 2484)
- Skype.exe (PID: 2376)
The process uses the downloaded file
- chrome.exe (PID: 2896)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 2232)
- AnyDesk.exe (PID: 3548)
- chrome.exe (PID: 620)
Creates files in the program directory
- rundll32.exe (PID: 3752)
- AnyDesk.exe (PID: 608)
- AnyDesk.exe (PID: 588)
- Skype-Setup.tmp (PID: 2816)
Executable content was dropped or overwritten
- chrome.exe (PID: 2604)
- chrome.exe (PID: 3668)
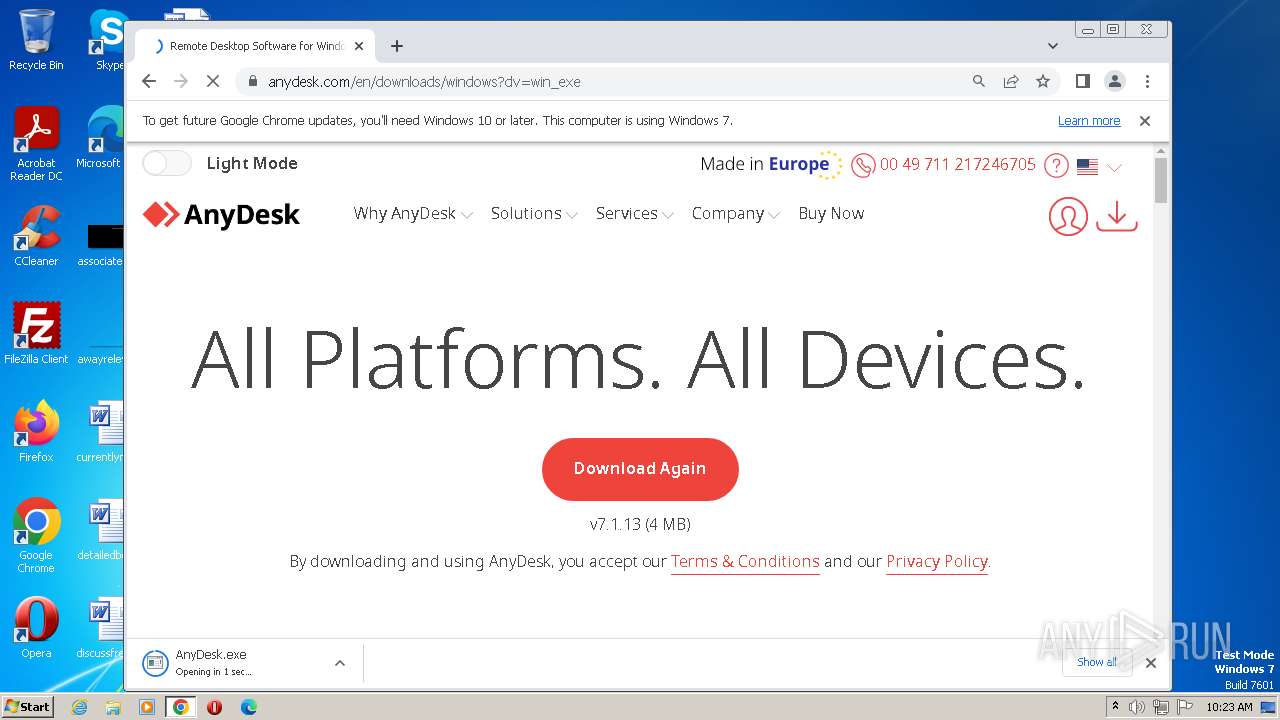
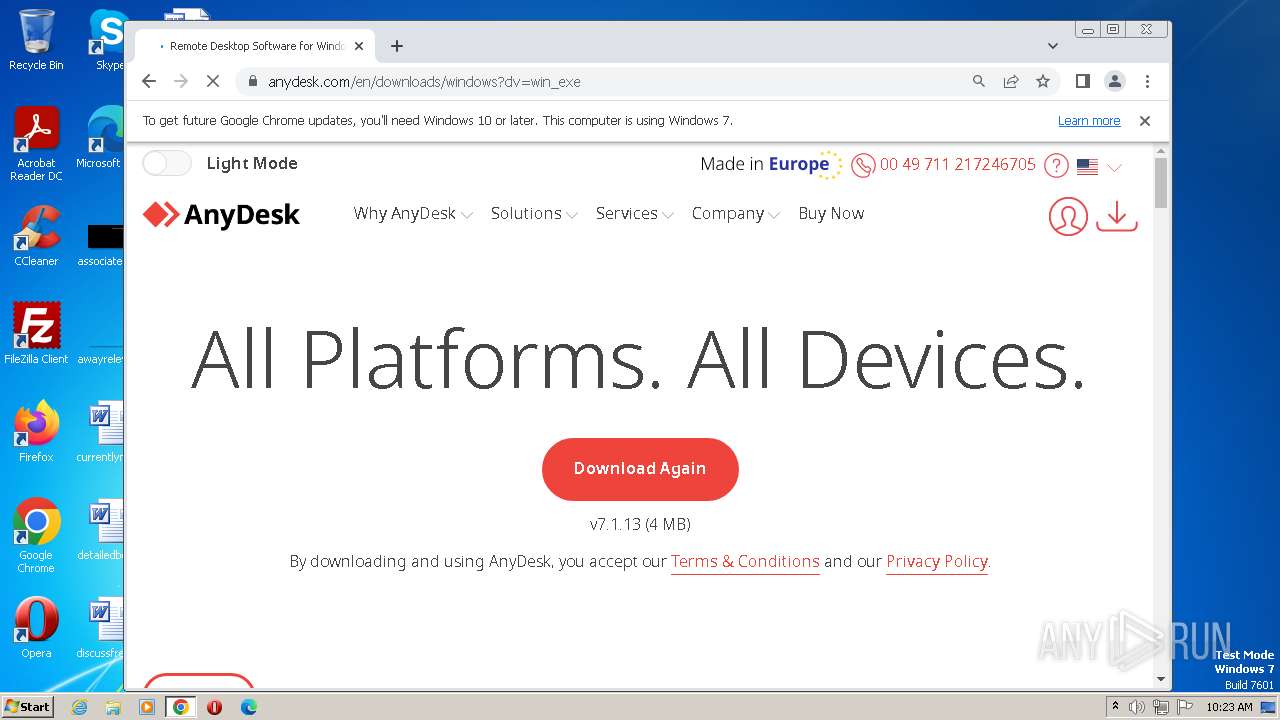
Manual execution by a user
- chrome.exe (PID: 3668)
- AnyDesk.exe (PID: 620)
- AnyDesk.exe (PID: 3628)
- Skype.exe (PID: 3444)
Application launched itself
- chrome.exe (PID: 3668)
Checks supported languages
- AnyDesk.exe (PID: 3548)
- AnyDesk.exe (PID: 4072)
- AnyDesk.exe (PID: 3640)
- AnyDesk.exe (PID: 608)
- AnyDesk.exe (PID: 588)
- AnyDesk.exe (PID: 620)
- AnyDesk.exe (PID: 3628)
- AnyDesk.exe (PID: 2696)
- AnyDesk.exe (PID: 3472)
- Skype.exe (PID: 328)
- Skype.exe (PID: 3444)
- Skype-Setup.exe (PID: 2484)
- Skype-Setup.exe (PID: 292)
- Skype-Setup.tmp (PID: 2816)
- Skype-Setup.tmp (PID: 1128)
- Skype.exe (PID: 2376)
- Skype.exe (PID: 3156)
- Skype.exe (PID: 1004)
- Skype.exe (PID: 1884)
- Skype.exe (PID: 792)
- Skype.exe (PID: 1700)
Reads the computer name
- AnyDesk.exe (PID: 3548)
- AnyDesk.exe (PID: 3640)
- AnyDesk.exe (PID: 4072)
- AnyDesk.exe (PID: 608)
- AnyDesk.exe (PID: 588)
- AnyDesk.exe (PID: 620)
- AnyDesk.exe (PID: 3628)
- AnyDesk.exe (PID: 3472)
- AnyDesk.exe (PID: 2696)
- Skype.exe (PID: 328)
- Skype.exe (PID: 3444)
- Skype-Setup.tmp (PID: 1128)
- Skype-Setup.tmp (PID: 2816)
- Skype.exe (PID: 2376)
- Skype.exe (PID: 1884)
- Skype.exe (PID: 1004)
- Skype.exe (PID: 792)
- Skype.exe (PID: 1700)
Creates files or folders in the user directory
- AnyDesk.exe (PID: 3548)
- Skype.exe (PID: 2376)
- Skype.exe (PID: 3156)
- Skype.exe (PID: 1004)
- Skype.exe (PID: 792)
- Skype.exe (PID: 3444)
Process checks are UAC notifies on
- AnyDesk.exe (PID: 3548)
Reads the machine GUID from the registry
- AnyDesk.exe (PID: 3548)
- AnyDesk.exe (PID: 4072)
- AnyDesk.exe (PID: 588)
- AnyDesk.exe (PID: 608)
- AnyDesk.exe (PID: 3628)
- AnyDesk.exe (PID: 2696)
- Skype.exe (PID: 3444)
- Skype.exe (PID: 2376)
Reads CPU info
- AnyDesk.exe (PID: 3548)
- AnyDesk.exe (PID: 3628)
- Skype.exe (PID: 3444)
- Skype.exe (PID: 2376)
Process checks computer location settings
- AnyDesk.exe (PID: 620)
- AnyDesk.exe (PID: 588)
- Skype.exe (PID: 2376)
- Skype.exe (PID: 792)
Application was dropped or rewritten from another process
- Skype-Setup.tmp (PID: 1128)
- Skype-Setup.tmp (PID: 2816)
Loads dropped or rewritten executable
- chrome.exe (PID: 1396)
- chrome.exe (PID: 300)
Reads product name
- Skype.exe (PID: 2376)
- Skype.exe (PID: 792)
Reads Environment values
- Skype.exe (PID: 2376)
- Skype.exe (PID: 792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x7d39 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 306688 |
| CodeSize: | 48640 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit, DLL |
| TimeStamp: | 2017:06:18 07:14:36+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 18-Jun-2017 07:14:36 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-Jun-2017 07:14:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000BD63 | 0x0000BE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54653 |
.rdata | 0x0000D000 | 0x00008546 | 0x00008600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.99213 |
.data | 0x00016000 | 0x00009B4A | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.42699 |
.rsrc | 0x00020000 | 0x0003C738 | 0x0003C800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99829 |
.reloc | 0x0005D000 | 0x00000C02 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.77168 |
Imports
ADVAPI32.dll |
CRYPT32.dll |
DHCPSAPI.DLL |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
NETAPI32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
1 | 0x00007DEB |
Total processes
112
Monitored processes
57
Malicious processes
16
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3660 --field-trial-handle=1060,i,14276644771976559175,2912750116160969094,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 292 | "C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop\Skype-Setup.exe" /SPAWNWND=$602C6 /NOTIFYWND=$D02B0 /silent !desktopicon | C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop\Skype-Setup.exe | Skype-Setup.tmp | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: HIGH Description: Skype Setup Exit code: 0 Version: 8.100.0.203 Modules
| |||||||||||||||
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1068 --field-trial-handle=1060,i,14276644771976559175,2912750116160969094,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 328 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Skype.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
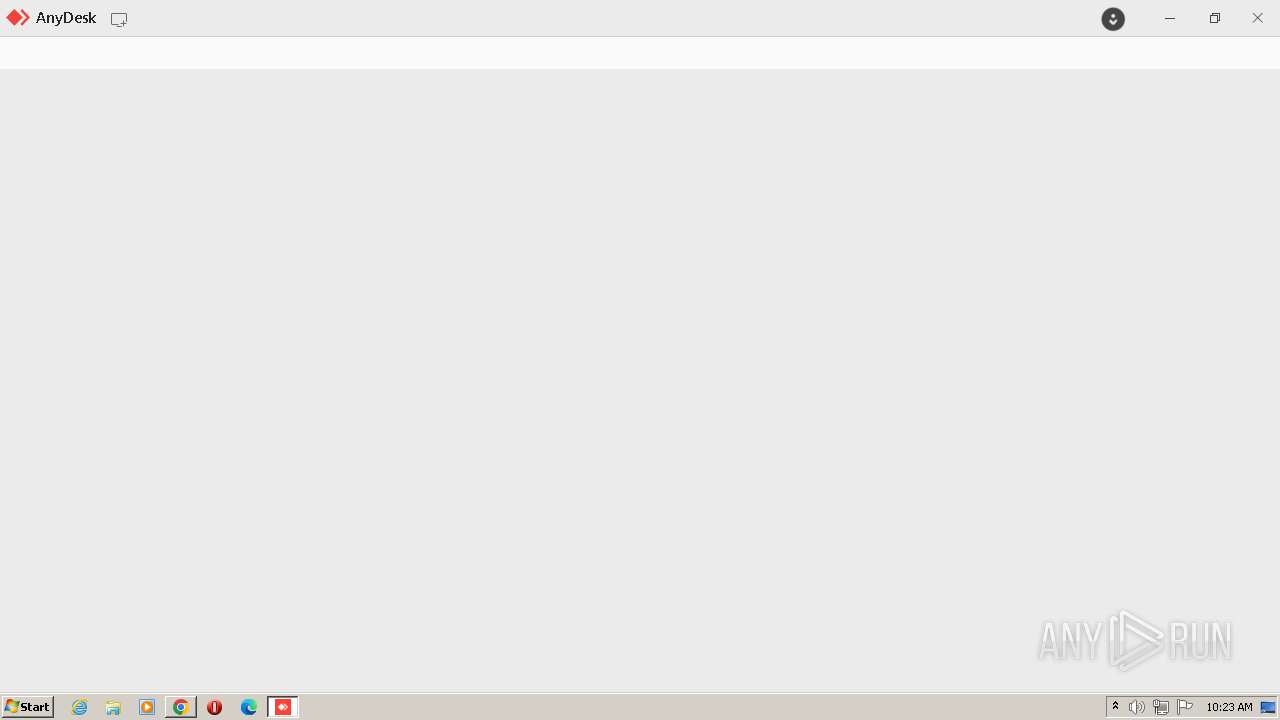
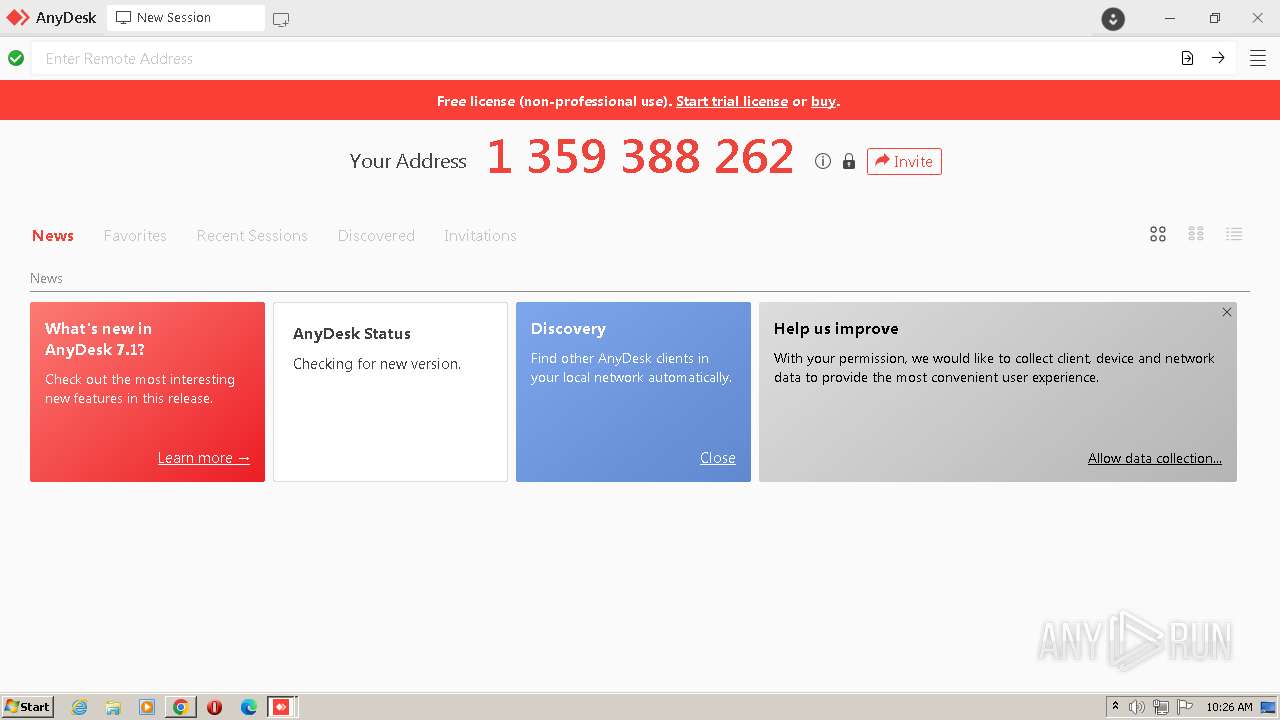
| 588 | "C:\Program Files\AnyDesk\AnyDesk.exe" --service | C:\Program Files\AnyDesk\AnyDesk.exe | services.exe | ||||||||||||
User: SYSTEM Company: AnyDesk Software GmbH Integrity Level: SYSTEM Description: AnyDesk Exit code: 0 Version: 7.1.13 Modules
| |||||||||||||||
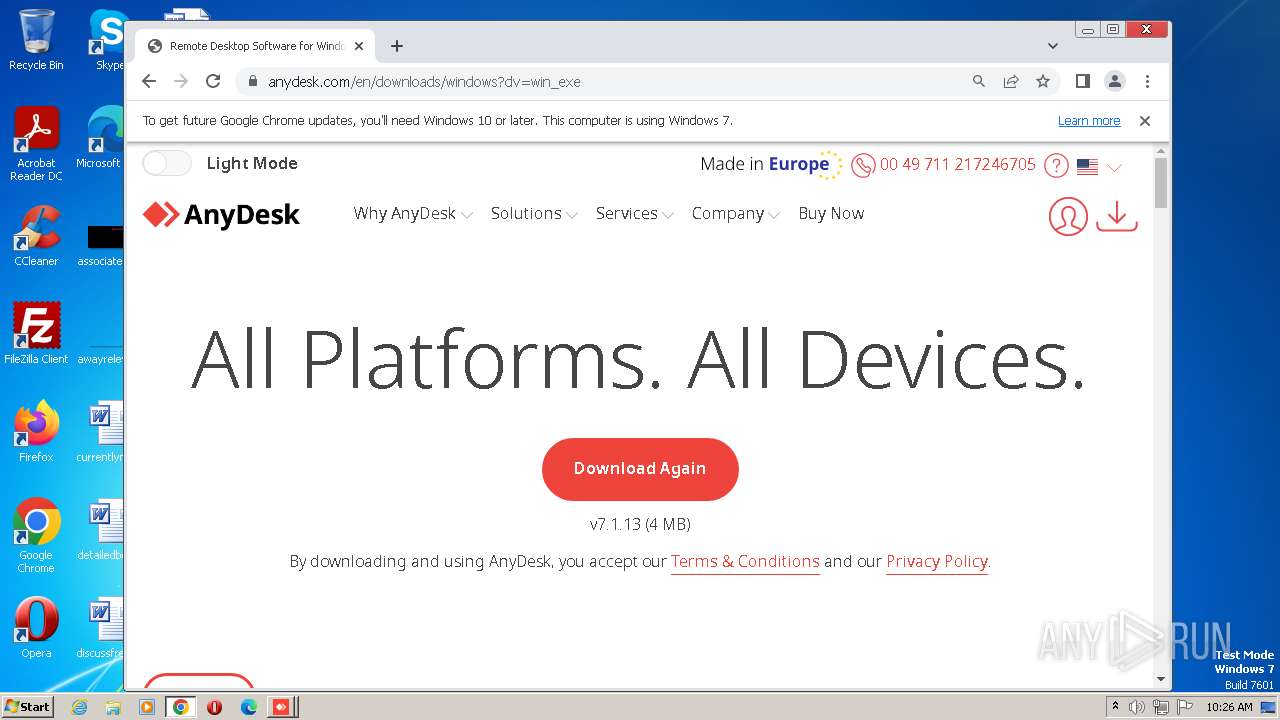
| 608 | "C:\Users\admin\Downloads\AnyDesk.exe" --install "C:\Program Files\AnyDesk" --start-with-win --create-shortcuts --create-taskbar-icon --create-desktop-icon --install-driver:mirror --update-main --svc-conf "C:\Users\admin\AppData\Roaming\AnyDesk\service.conf" --sys-conf "C:\Users\admin\AppData\Roaming\AnyDesk\system.conf" | C:\Users\admin\Downloads\AnyDesk.exe | AnyDesk.exe | ||||||||||||
User: admin Company: AnyDesk Software GmbH Integrity Level: HIGH Description: AnyDesk Exit code: 0 Version: 7.1.13 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2092 --field-trial-handle=1060,i,14276644771976559175,2912750116160969094,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 620 | "C:\Program Files\AnyDesk\AnyDesk.exe" --control | C:\Program Files\AnyDesk\AnyDesk.exe | — | explorer.exe | |||||||||||
User: admin Company: AnyDesk Software GmbH Integrity Level: MEDIUM Description: AnyDesk Exit code: 0 Version: 7.1.13 Modules
| |||||||||||||||
| 792 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop" --app-user-model-id=Microsoft.Skype.SkypeDesktop --app-path="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar" --no-sandbox --no-zygote --autoplay-policy=no-user-gesture-required --disable-background-timer-throttling --ms-disable-indexeddb-transaction-timeout --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=1856 --field-trial-handle=1320,i,11744680787154189420,16944190105290531440,131072 --enable-features=WinUseBrowserSpellChecker,WinUseHybridSpellChecker,WinrtGeolocationImplementation --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand --skype-process-type=Main --skype-window-id=__MAIN_ROOT_VIEW_ID__ /prefetch:1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.100.0.203 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4160 --field-trial-handle=1060,i,14276644771976559175,2912750116160969094,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
17 854
Read events
17 667
Write events
171
Delete events
16
Modification events
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
162
Suspicious files
304
Text files
177
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF46a2f2.TMP | — | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:513218482935B0D388C0A990D868387A | SHA256:8E39CBAAF4AACC3A01AFA74EA8C30FB24FE69A22B8B30728AFB1614FD68809D9 | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF46a2f2.TMP | text | |
MD5:D5C9ECBD2DCA29D89266782824D7AF99 | SHA256:D22D1243ACC064A30823180D0E583C853E9395367C78C2AD9DE59A463904F702 | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF46a4e6.TMP | — | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3752 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\notpetya.exe | binary | |
MD5:9A7FFE65E0912F9379BA6E8E0B079FDE | SHA256:4B336C3CC9B6C691FE581077E3DD9EA7DF3BF48F79E35B05CF87E079EC8E0651 | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5e7c886b-c714-4807-866d-7c94d833a825.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3752 | rundll32.exe | C:\ProgramData\dllhost.dat | executable | |
MD5:AEEE996FD3484F28E5CD85FE26B6BDCD | SHA256:F8DBABDFA03068130C277CE49C60E35C029FF29D9E3C74C362521F3FB02670D5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
129
DNS requests
102
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | HEAD | 200 | 142.250.178.14:80 | http://dl.google.com/release2/chrome_component/accn2h7r7qrqz4xqkrxfxappoyxq_404/lmelglejhemejginpboagddgdfbepgmp_404_all_ZZ_acqoo7fimcapp2l6txhzjzvmp5zq.crx3 | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6pajjne3v63kkjachrj3yh6txa_665/efniojlnjndmcbiieegkicadnoecjjef_665_all_nq2nhvadjptybw3cmwg4cxdzsi.crx3 | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/accn2h7r7qrqz4xqkrxfxappoyxq_404/lmelglejhemejginpboagddgdfbepgmp_404_all_ZZ_acqoo7fimcapp2l6txhzjzvmp5zq.crx3 | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/cxpsjblnoxgjoqggdsbvujtof4_58/khaoiebndkojlmppeemjhbpbandiljpe_58_win_advr4ucepztwtigvw3fduftsvbeq.crx3 | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 200 | 142.250.178.14:80 | http://dl.google.com/release2/chrome_component/cxpsjblnoxgjoqggdsbvujtof4_58/khaoiebndkojlmppeemjhbpbandiljpe_58_win_advr4ucepztwtigvw3fduftsvbeq.crx3 | US | binary | 1.26 Kb | whitelisted |
3752 | rundll32.exe | OPTIONS | 405 | 142.250.180.3:80 | http://142.250.180.3/ | US | html | 1.55 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 142.250.178.14:80 | http://dl.google.com/release2/chrome_component/ac6pajjne3v63kkjachrj3yh6txa_665/efniojlnjndmcbiieegkicadnoecjjef_665_all_nq2nhvadjptybw3cmwg4cxdzsi.crx3 | US | binary | 26.0 Kb | whitelisted |
860 | svchost.exe | HEAD | 200 | 142.250.178.14:80 | http://dl.google.com/release2/chrome_component/ac6pajjne3v63kkjachrj3yh6txa_665/efniojlnjndmcbiieegkicadnoecjjef_665_all_nq2nhvadjptybw3cmwg4cxdzsi.crx3 | US | binary | 5.46 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 142.250.178.14:80 | http://dl.google.com/release2/chrome_component/ac6pajjne3v63kkjachrj3yh6txa_665/efniojlnjndmcbiieegkicadnoecjjef_665_all_nq2nhvadjptybw3cmwg4cxdzsi.crx3 | US | binary | 32.1 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 142.250.178.14:80 | http://dl.google.com/release2/chrome_component/accn2h7r7qrqz4xqkrxfxappoyxq_404/lmelglejhemejginpboagddgdfbepgmp_404_all_ZZ_acqoo7fimcapp2l6txhzjzvmp5zq.crx3 | US | binary | 6.04 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 192.168.100.138:49308 | — | — | — | malicious |
— | — | 192.168.100.138:49313 | — | — | — | malicious |
— | — | 192.168.100.138:49310 | — | — | — | malicious |
3752 | rundll32.exe | 192.168.100.1:139 | — | — | — | unknown |
3752 | rundll32.exe | 192.168.100.1:445 | — | — | — | unknown |
4 | System | 192.168.100.2:445 | — | — | — | whitelisted |
3752 | rundll32.exe | 192.168.100.2:445 | — | — | — | whitelisted |
2604 | chrome.exe | 142.250.187.227:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
3668 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
www.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
id.google.com |
| whitelisted |
anydesk.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
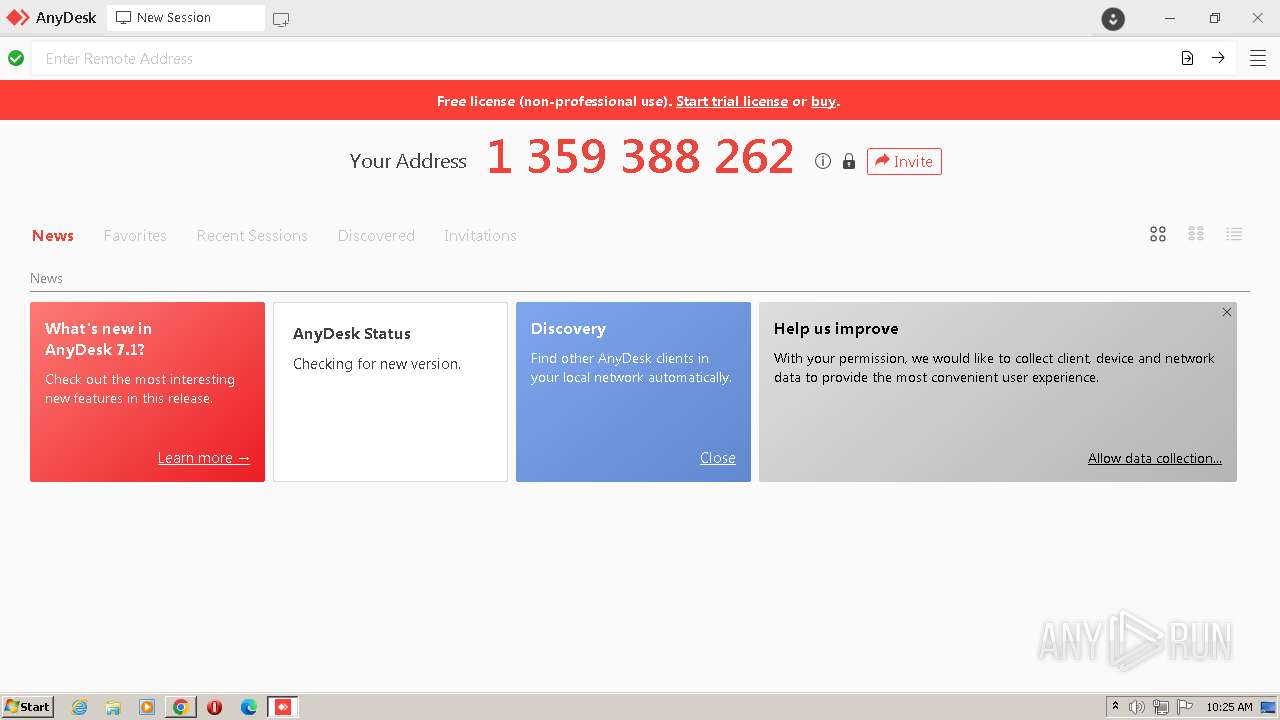
588 | AnyDesk.exe | Potential Corporate Privacy Violation | ET USER_AGENTS AnyDesk Remote Desktop Software User-Agent |
4 | System | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempt to connect to an external SMB server |
4 | System | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempt to connect to an external SMB server |
4 | System | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempt to connect to an external SMB server |
4 | System | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempt to connect to an external SMB server |
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
Skype.exe | [328:4032:0805/102738.358:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [328:4032:0805/102738.361:VERBOSE1:crash_service.cc(145)] window handle is 000E040A
|
Skype.exe | [328:4032:0805/102738.361:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|
Skype.exe | [328:4032:0805/102738.361:VERBOSE1:crash_service_main.cc(94)] Ready to process crash requests
|
Skype.exe | [328:4032:0805/102738.361:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\crash_checkpoint.txt
server is https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload
maximum 128 reports/day
reporter is electron-crash-service
|
Skype.exe | [328:1792:0805/102738.363:VERBOSE1:crash_service.cc(333)] client start. pid = 3444
|
Skype.exe | [328:3176:0805/102739.780:VERBOSE1:crash_service.cc(341)] client end. pid = 3444
|
Skype.exe | [328:4032:0805/102740.783:VERBOSE1:crash_service.cc(538)] session ending..
|
Skype.exe | [328:4032:0805/102740.783:VERBOSE1:crash_service_main.cc(99)] Session end. return code is 0
|
Skype.exe | [328:4032:0805/102740.783:VERBOSE1:crash_service.cc(543)] clients connected :1
clients terminated :1
dumps serviced :0
dumps reported :0
|