| File name: | 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe |
| Full analysis: | https://app.any.run/tasks/8c0adfc4-4b19-43e9-9e1f-b92e5af18a47 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 03:02:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 5 sections |
| MD5: | 4C4A327F5A048A7B137B8E508299CB3D |
| SHA1: | 35F471D2F557296829CEEC5F5CC43A784B448AAB |
| SHA256: | 027582A71F826A9B41026B8EB57470861BDF8B0E77587E940738346924DB7003 |
| SSDEEP: | 384:HilAdwJrnU/HOpQy4i89ZR+3TW7g1TNGZ7:HYJr0HI4i89ZROW7G |
MALICIOUS
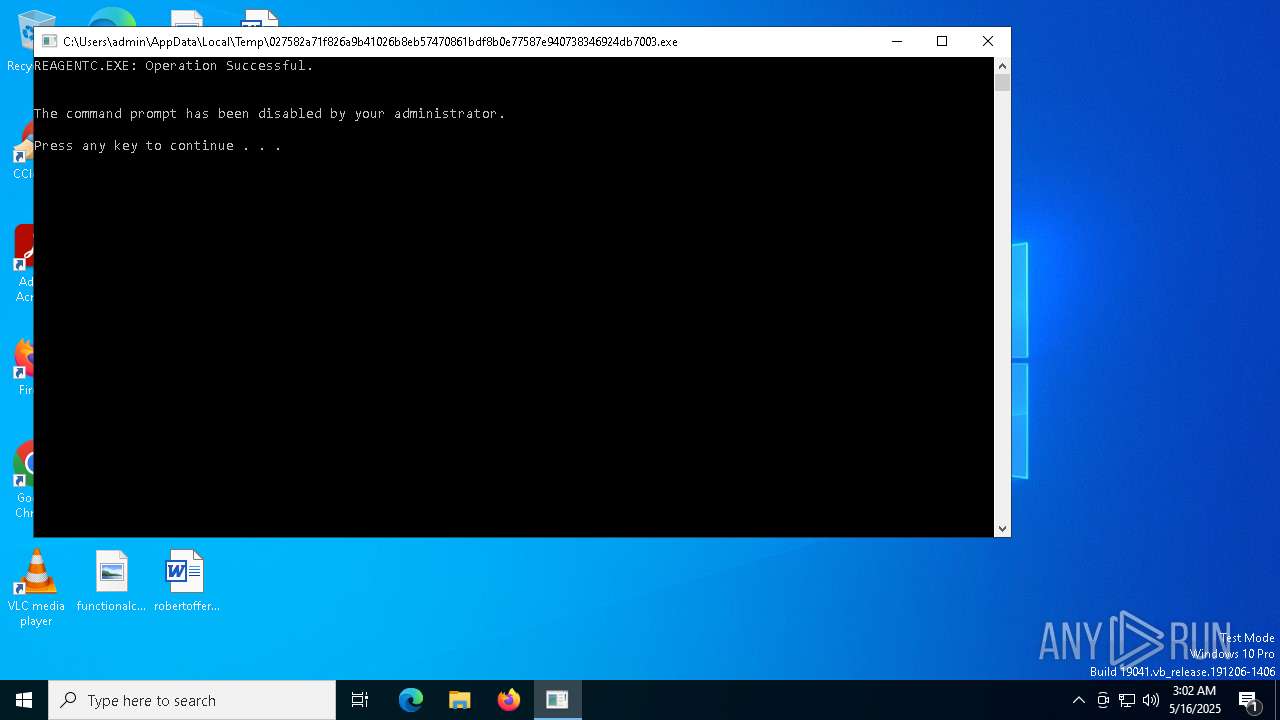
Starts REAGENTC.EXE to disable the Windows Recovery Environment
- ReAgentc.exe (PID: 7604)
Disables the Shutdown in the Start menu
- 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe (PID: 7500)
Changes the autorun value in the registry
- 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe (PID: 7500)
Disables the Run the Start menu
- 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe (PID: 7500)
Disables task manager
- 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe (PID: 7500)
Disables the Find the Start menu
- 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe (PID: 7500)
Disables the Command Prompt (cmd)
- 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe (PID: 7500)
UAC/LUA settings modification
- 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe (PID: 7500)
Disables Windows Defender
- 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe (PID: 7500)
SUSPICIOUS
Starts CMD.EXE for commands execution
- 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe (PID: 7500)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 7804)
INFO
Checks supported languages
- 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe (PID: 7500)
- ShellExperienceHost.exe (PID: 7804)
Reads the computer name
- ShellExperienceHost.exe (PID: 7804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:07:22 05:23:22+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 5632 |
| InitializedDataSize: | 8704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x197c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
139
Monitored processes
10
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7396 | "C:\Users\admin\AppData\Local\Temp\027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe" | C:\Users\admin\AppData\Local\Temp\027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 7500 | "C:\Users\admin\AppData\Local\Temp\027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe" | C:\Users\admin\AppData\Local\Temp\027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7512 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7568 | C:\WINDOWS\system32\cmd.exe /c @echo off | C:\Windows\SysWOW64\cmd.exe | — | 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7588 | C:\WINDOWS\system32\cmd.exe /c C:\Windows\System32\ReAgentc.exe /disable | C:\Windows\SysWOW64\cmd.exe | — | 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7604 | C:\Windows\System32\ReAgentc.exe /disable | C:\Windows\SysWOW64\ReAgentc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Recovery Agent Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7636 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7668 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7712 | C:\WINDOWS\system32\cmd.exe /c C:\Windows\System32\taskkill.exe /f /im explorer.exe | C:\Windows\SysWOW64\cmd.exe | — | 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7804 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 723
Read events
2 634
Write events
29
Delete events
60
Modification events
| (PID) Process: | (7500) 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | StartUpConfig |
Value: C:\Windows\System32\Crazy\Crazy.exe | |||
| (PID) Process: | (7500) 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (7500) 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableMsConfig |
Value: 1 | |||
| (PID) Process: | (7500) 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 1 | |||
| (PID) Process: | (7500) 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoRun |
Value: 1 | |||
| (PID) Process: | (7500) 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoFind |
Value: 1 | |||
| (PID) Process: | (7500) 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoFolderOptions |
Value: 1 | |||
| (PID) Process: | (7500) 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoClose |
Value: 1 | |||
| (PID) Process: | (7500) 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoControlPanel |
Value: 1 | |||
| (PID) Process: | (7500) 027582a71f826a9b41026b8eb57470861bdf8b0e77587e940738346924db7003.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoViewContextMenu |
Value: 1 | |||
Executable files
0
Suspicious files
1
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7604 | ReAgentc.exe | C:\Windows\SysWOW64\Recovery\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 7604 | ReAgentc.exe | C:\Windows\Panther\UnattendGC\diagwrn.xml | text | |
MD5:874B1B3415E221A33DCE150E2DEF8507 | SHA256:E2B2607F879EE4BF8BA7E8AED1A2046DC920194D2EA785D618F0F317894DB84D | |||
| 7604 | ReAgentc.exe | C:\Windows\Logs\ReAgent\ReAgent.log | csv | |
MD5:D20948729F39C0EF0080B801489C2B1E | SHA256:76C342B6E62AD36C0F75D31ABBF2F435249F08120B7F2859D5018B7BF7B38DD4 | |||
| 7604 | ReAgentc.exe | C:\Windows\Panther\UnattendGC\diagerr.xml | text | |
MD5:3A8D2D92D67445734789F82D6E6D90A6 | SHA256:E80AA5A43C517844228A67E8A49E30EE8CF68979E54BA0A3FE660C80978808C6 | |||
| 7604 | ReAgentc.exe | \\?\Volume{2f5c5e71-85a9-11eb-90a8-9a9b76358421}\EFI\Microsoft\Recovery\BCD | binary | |
MD5:2F8E7041932207878CD4F72914B54919 | SHA256:54903C0533AEC4D2872ECA84D86C9CCF290D7F4B9FEE3922B612299FA12049F3 | |||
| 7604 | ReAgentc.exe | C:\Windows\SysWOW64\Recovery\ReAgent.xml | xml | |
MD5:7BA1A1AE453E18669377CBD6EB101109 | SHA256:0F7D35D68A237B9C7D6D24C736E9A758761BB0840C113686B81E2CE33928EF65 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
18
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7388 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7388 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7388 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |