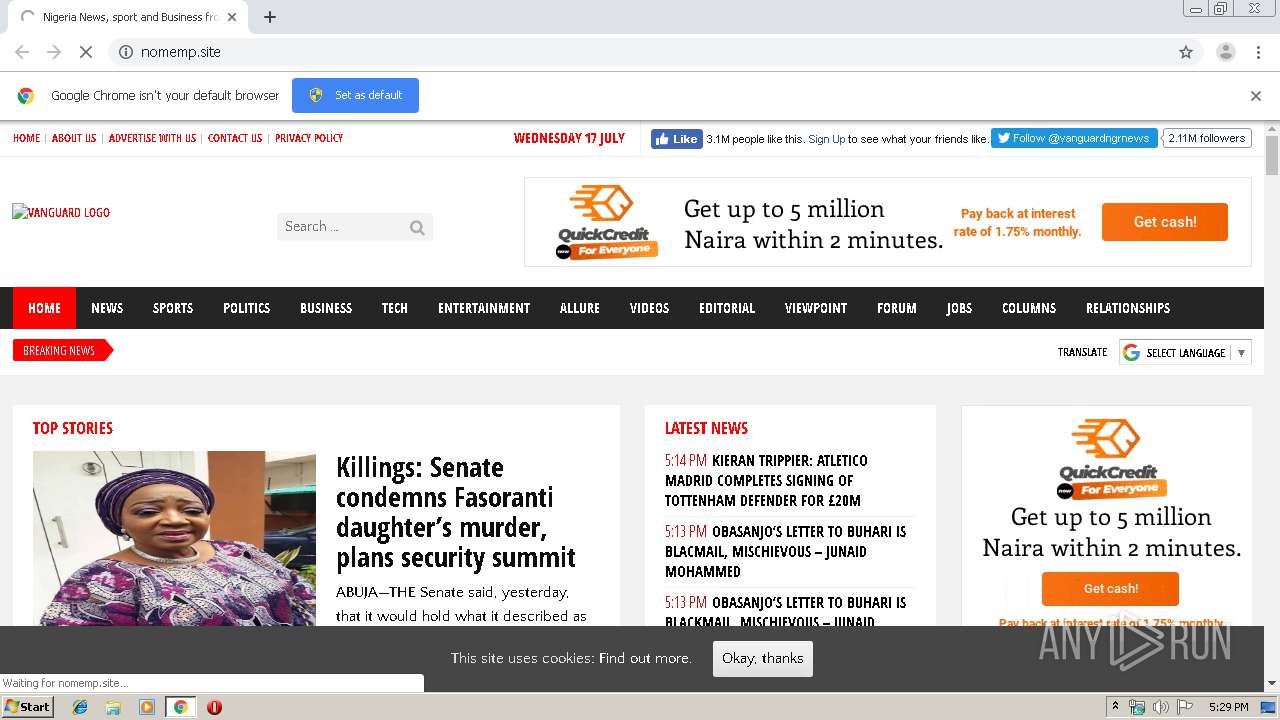
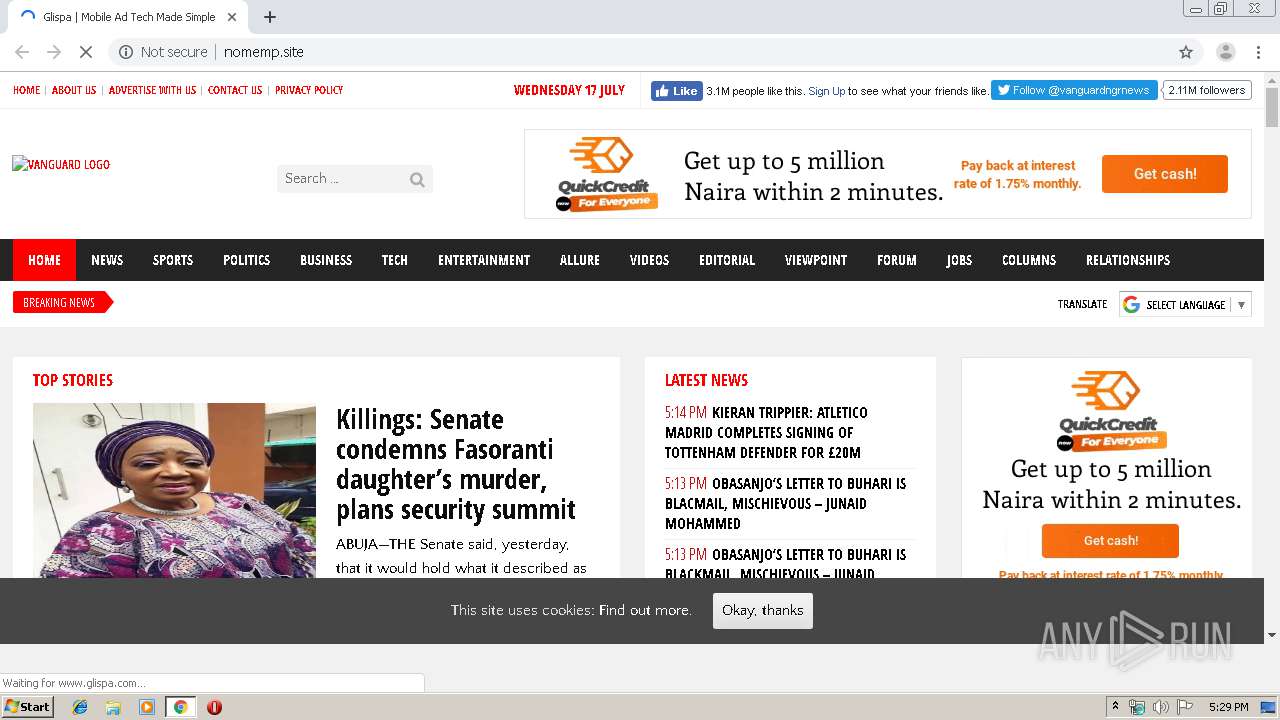
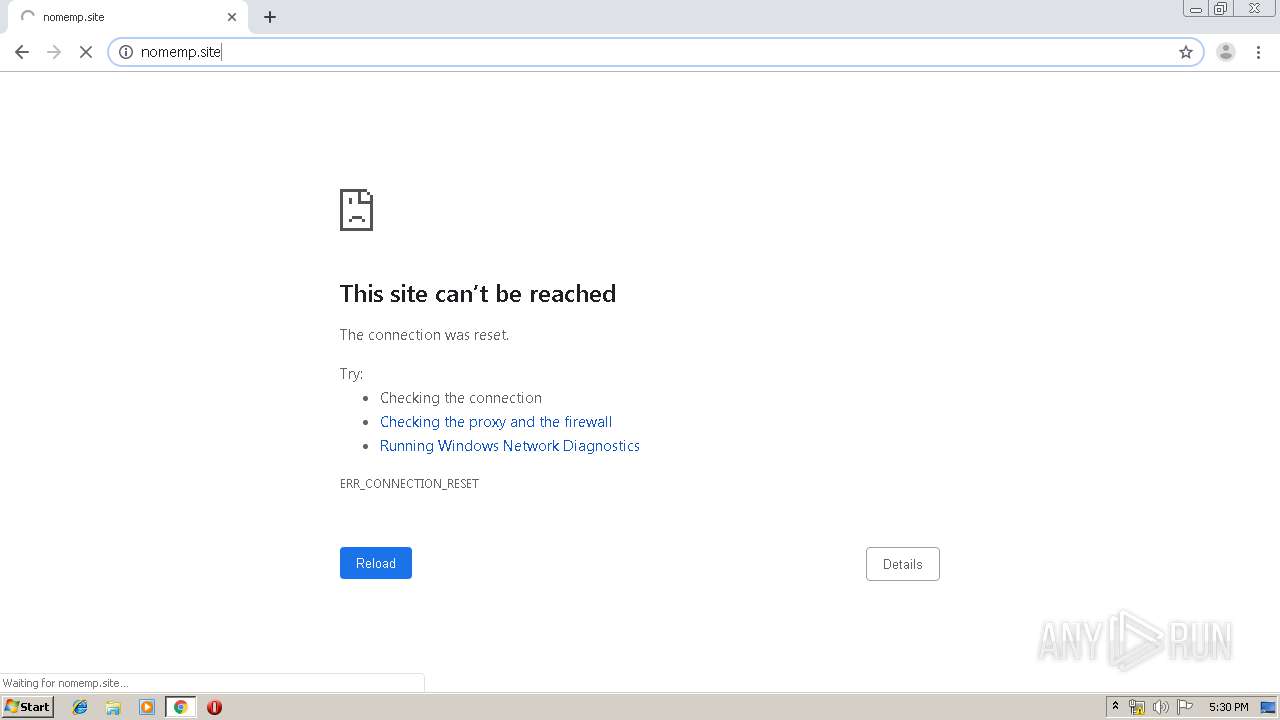
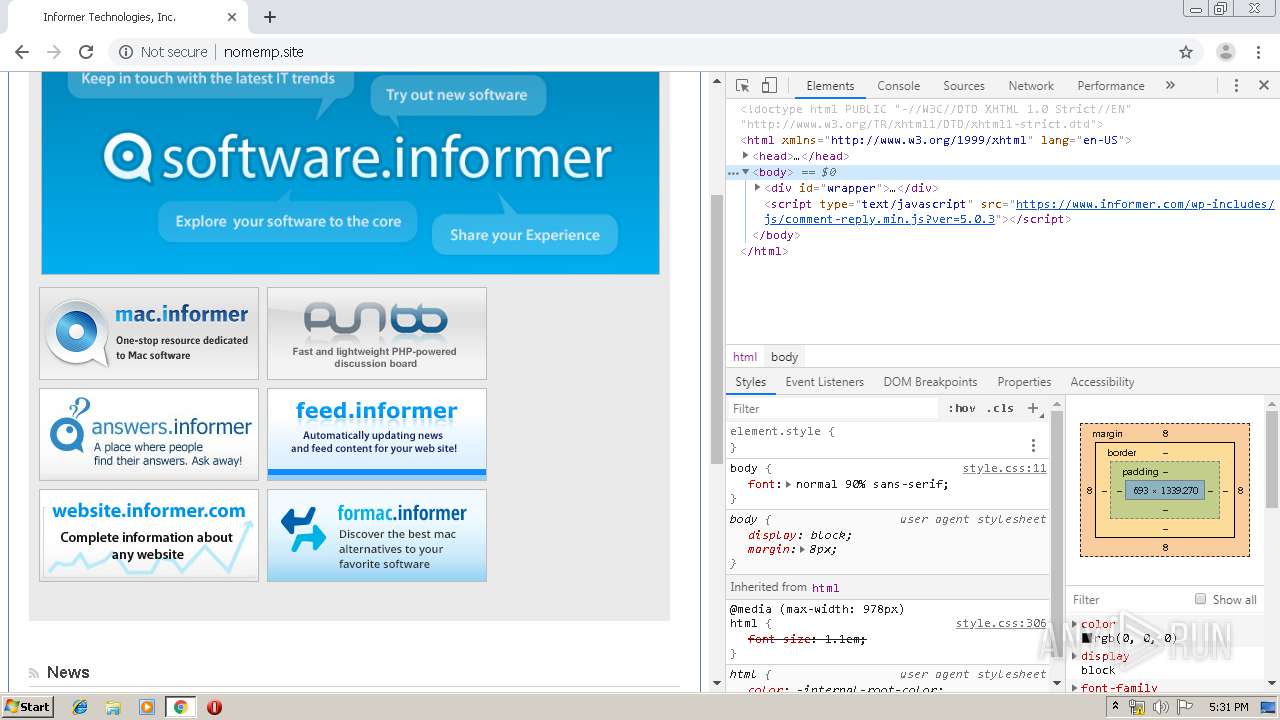
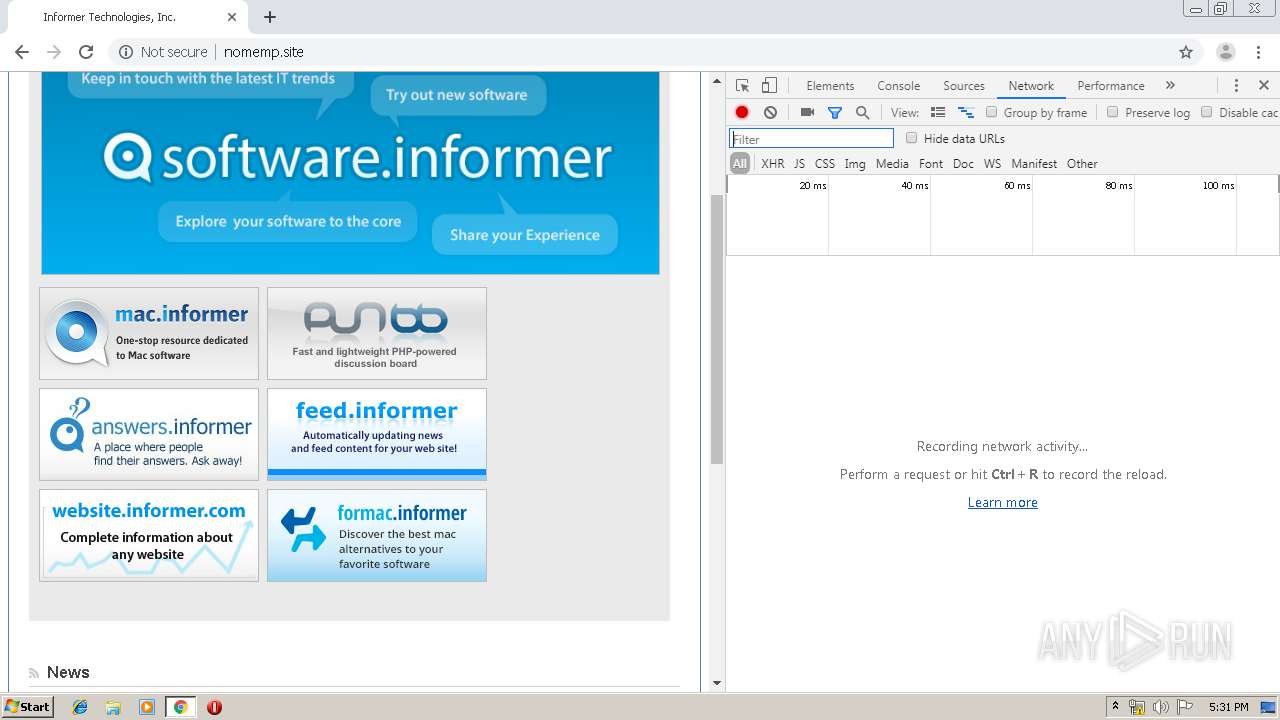
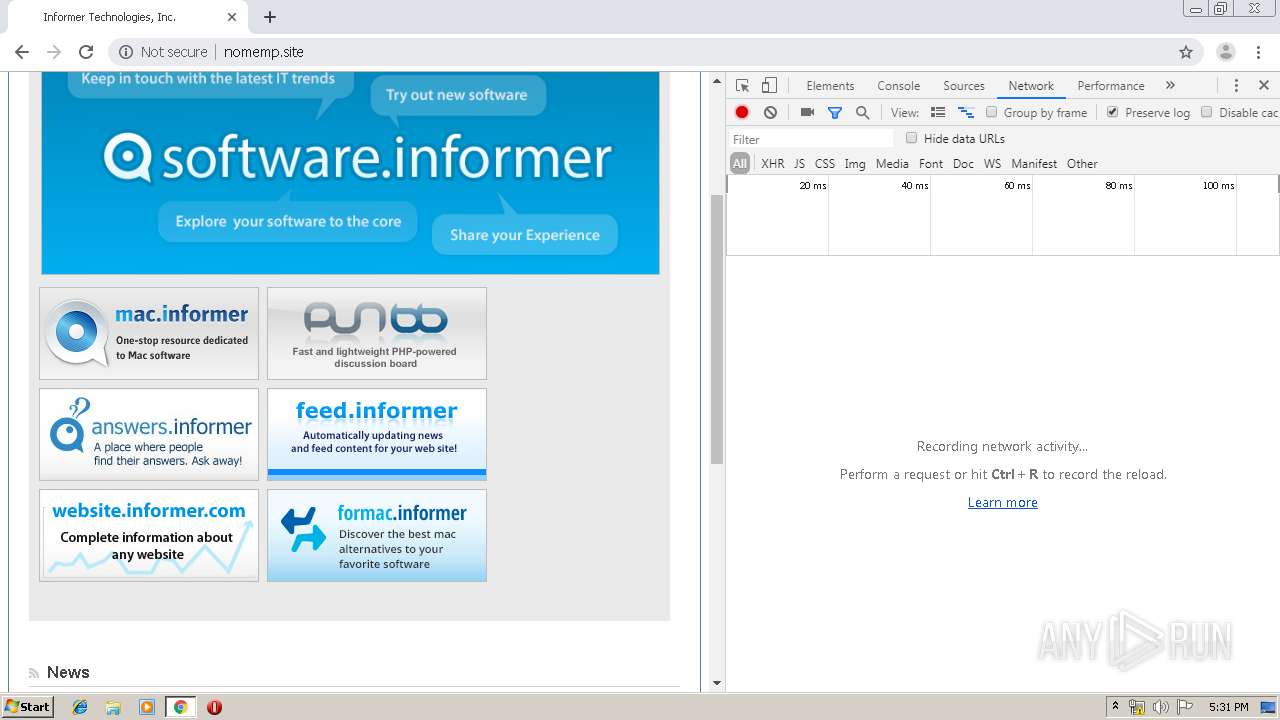
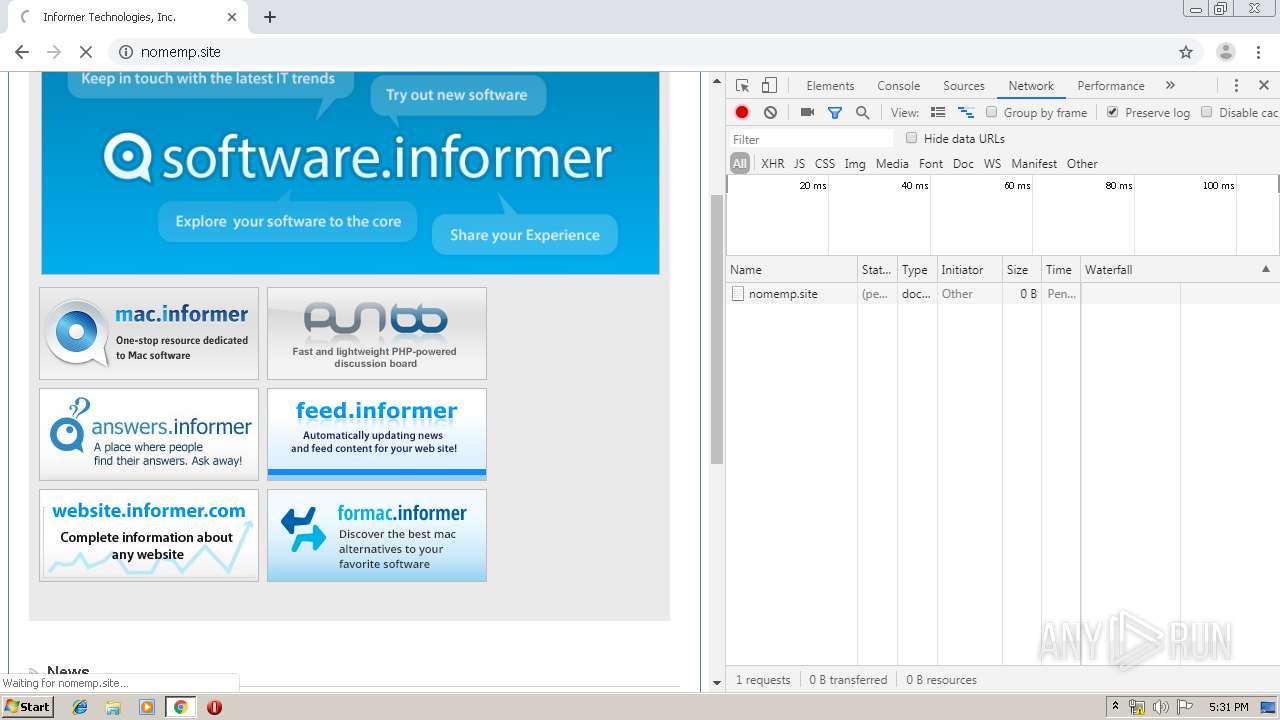
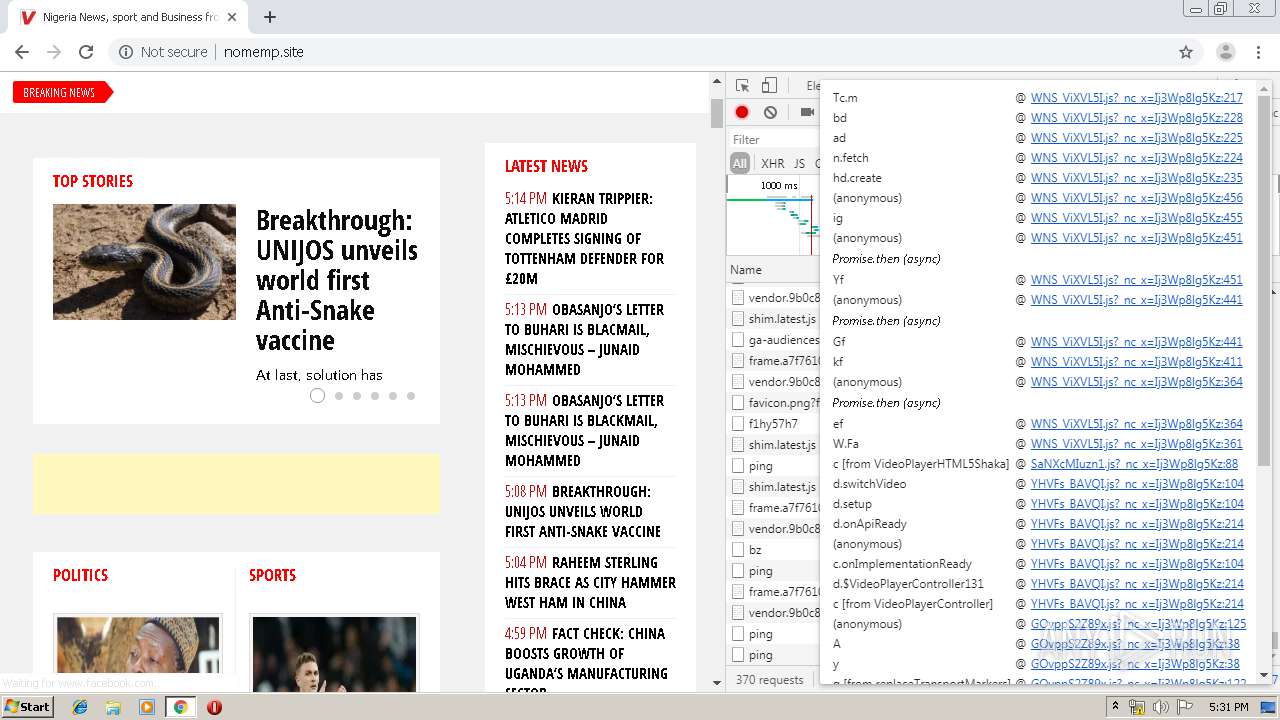
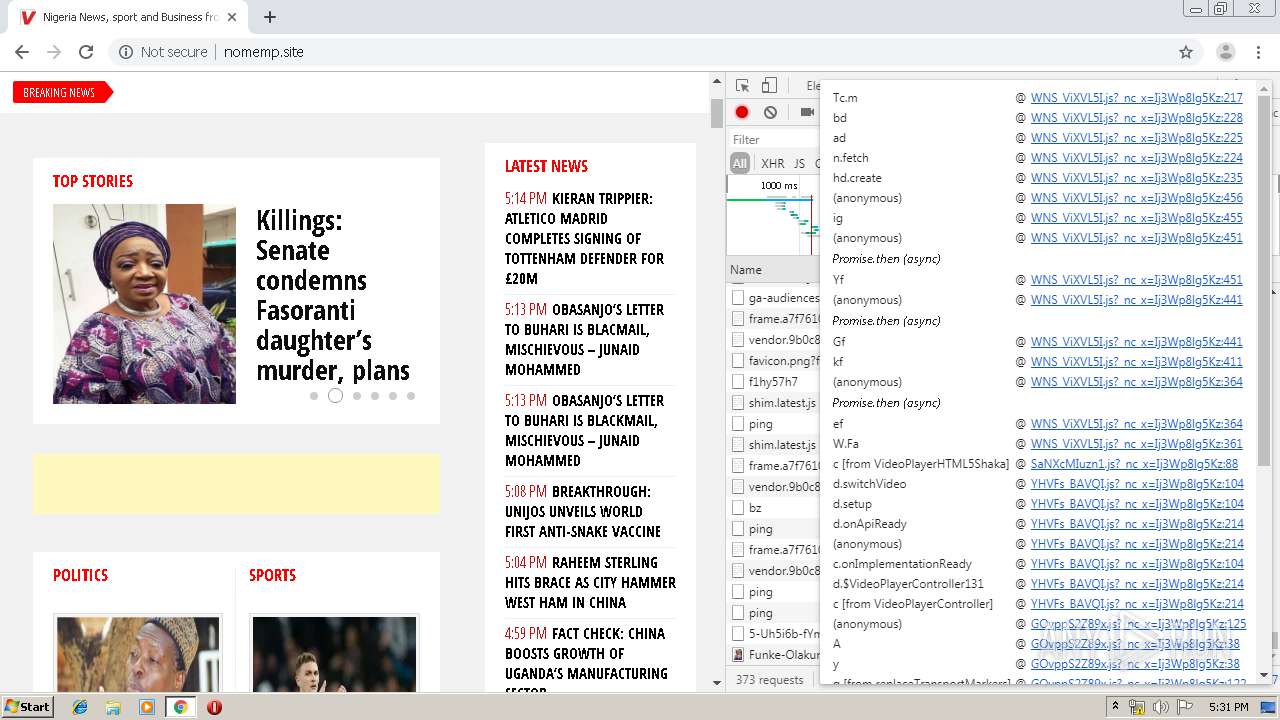
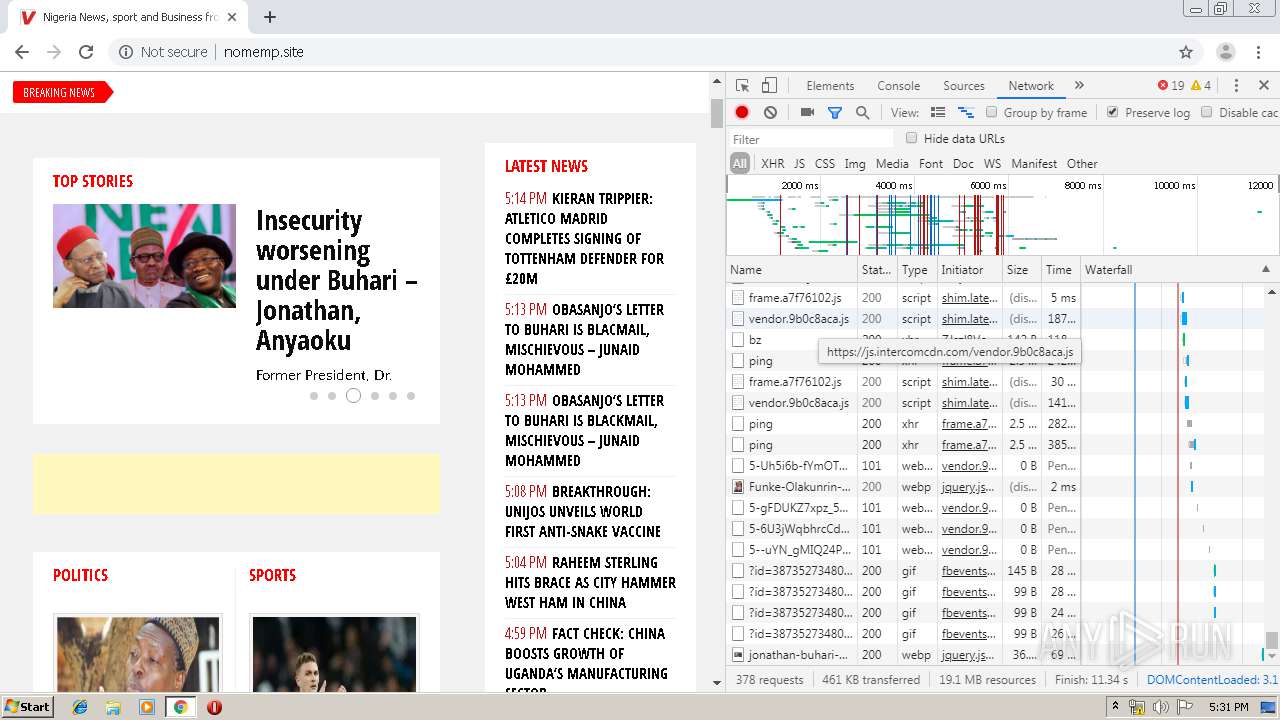
| URL: | http://nomemp.site |
| Full analysis: | https://app.any.run/tasks/2bf93041-55a9-453a-9ba8-330a9fb60d3c |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 16:29:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AABB6D02AE24684F442EF9CBC26E22FF |
| SHA1: | 99CE1C05F864BF7C9410D2355B3221977208E865 |
| SHA256: | 0273F1979002F73B7BD07C0CC9A5668DACB595512EFEC46896EC77A2747DF761 |
| SSDEEP: | 3:N1KQbLWMRA:CQOMm |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3528)
INFO
Dropped object may contain TOR URL's
- chrome.exe (PID: 3528)
Application launched itself
- chrome.exe (PID: 3528)
Reads settings of System Certificates
- chrome.exe (PID: 2888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
44
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,3917396547712858164,8123099806048693045,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16987246256158658244 --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,3917396547712858164,8123099806048693045,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17520770327250899271 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,3917396547712858164,8123099806048693045,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5865523620004507557 --mojo-platform-channel-handle=2820 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,3917396547712858164,8123099806048693045,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14908581594110107129 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4104 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,3917396547712858164,8123099806048693045,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17678557283211164150 --mojo-platform-channel-handle=3820 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f43a9d0,0x6f43a9e0,0x6f43a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,3917396547712858164,8123099806048693045,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10309172682676238831 --mojo-platform-channel-handle=4076 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,3917396547712858164,8123099806048693045,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2518217105807396304 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,3917396547712858164,8123099806048693045,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7400736722849088739 --mojo-platform-channel-handle=3660 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,3917396547712858164,8123099806048693045,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5443094487213743594 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
695
Read events
580
Write events
110
Delete events
5
Modification events
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3528-13207854584364875 |
Value: 259 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
369
Text files
263
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10e968.TMP | — | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9b889c6b-6cc5-4dbe-8c30-deb5d3440760.tmp | — | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF10eb0e.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
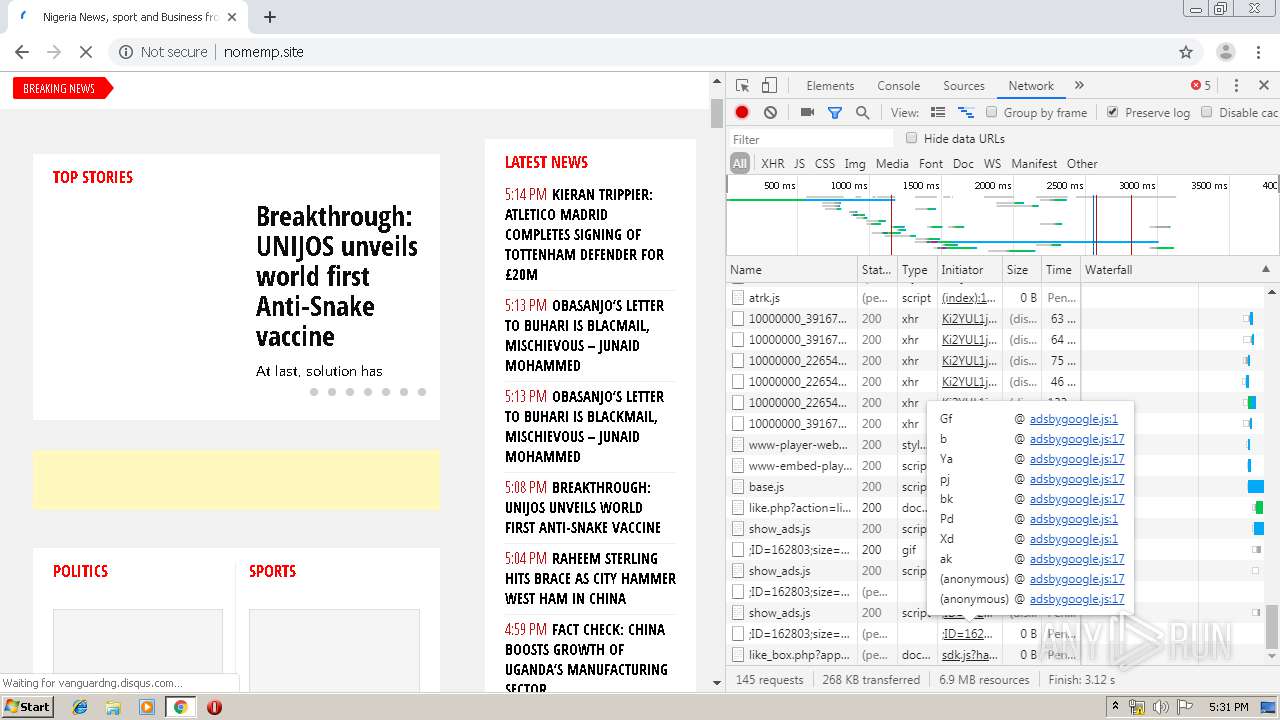
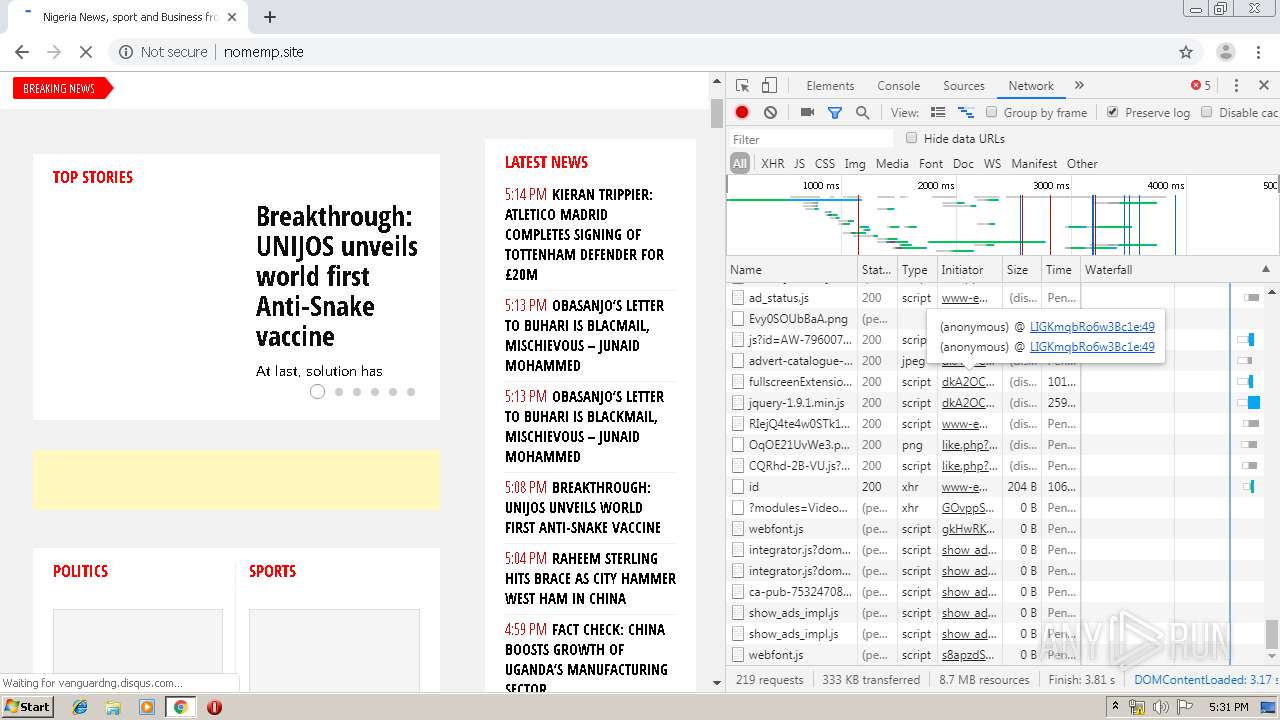
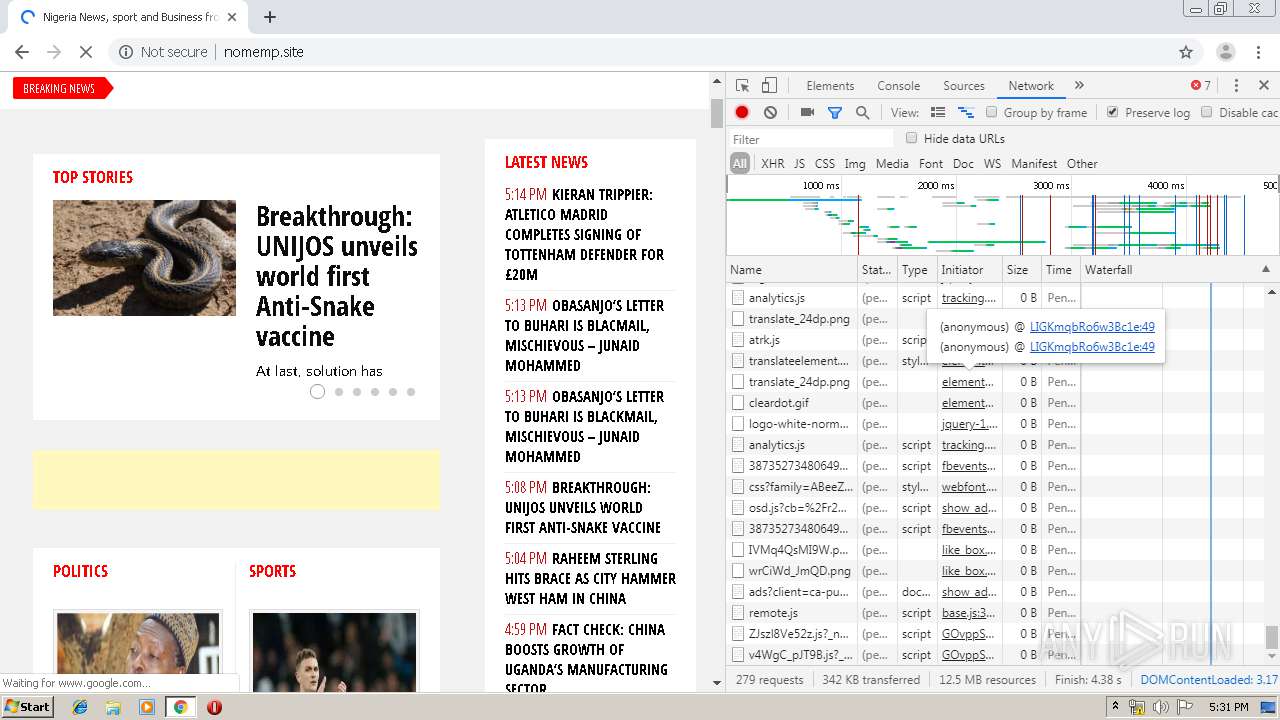
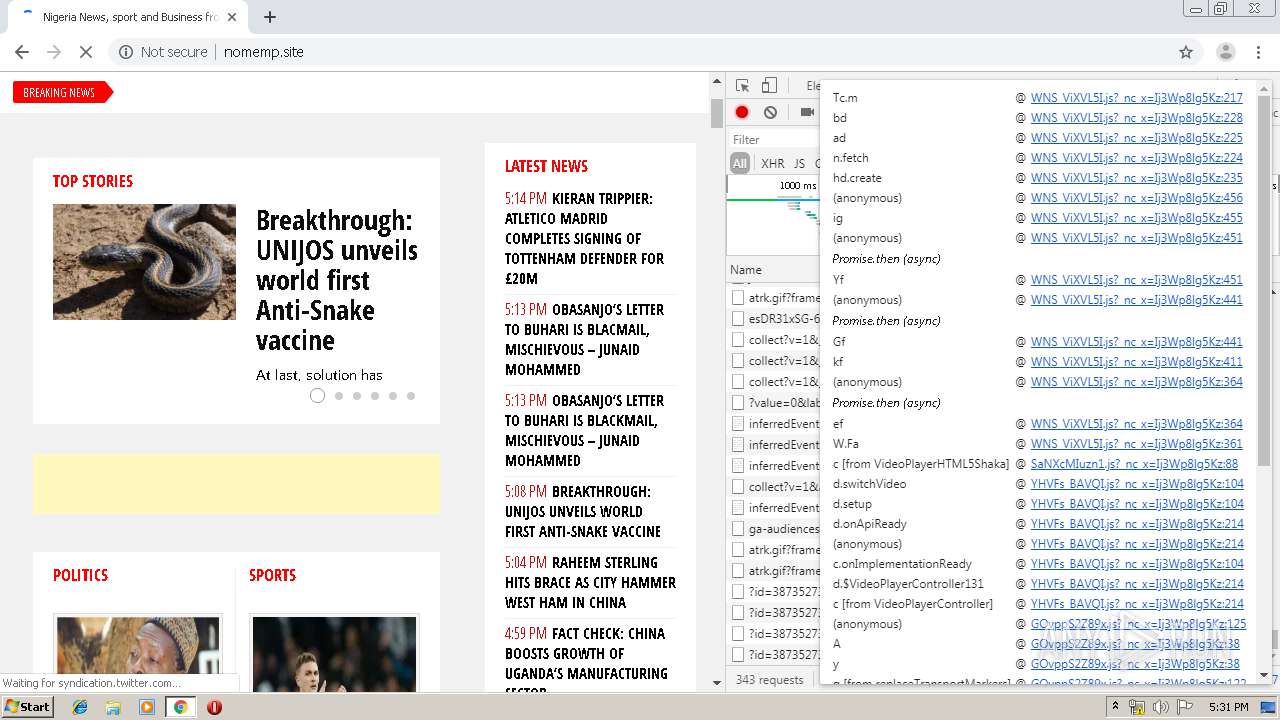
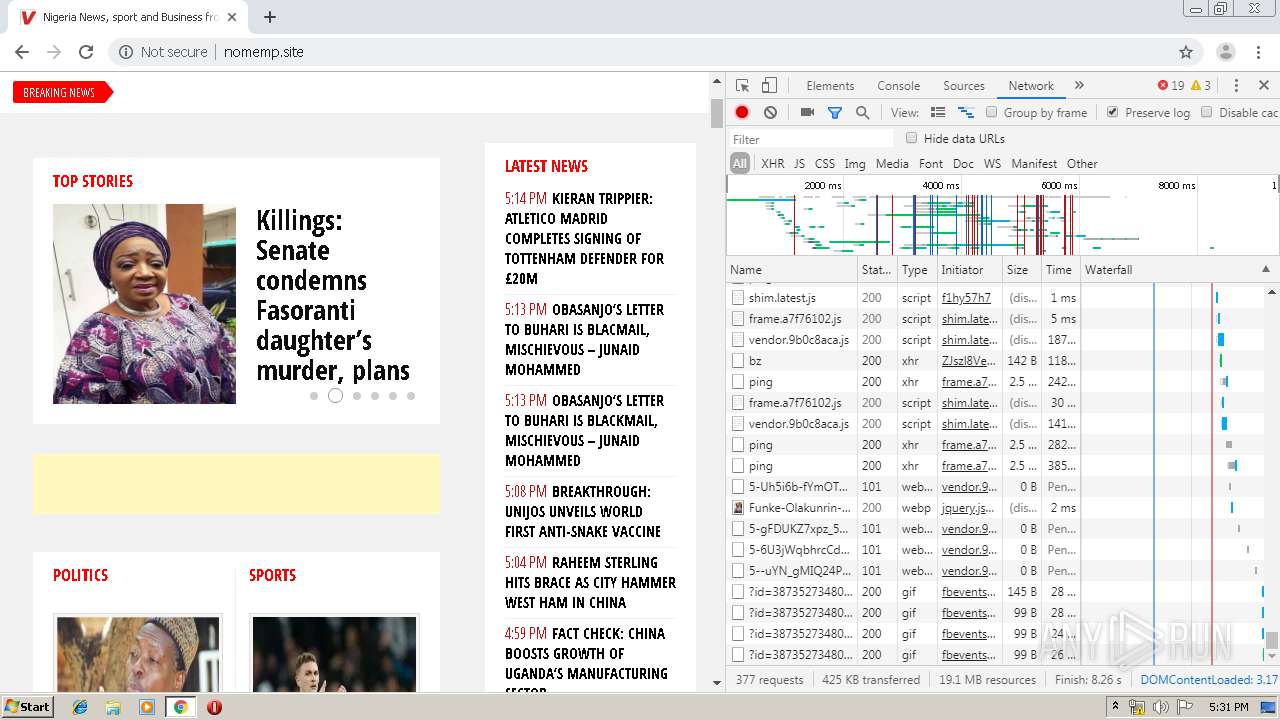
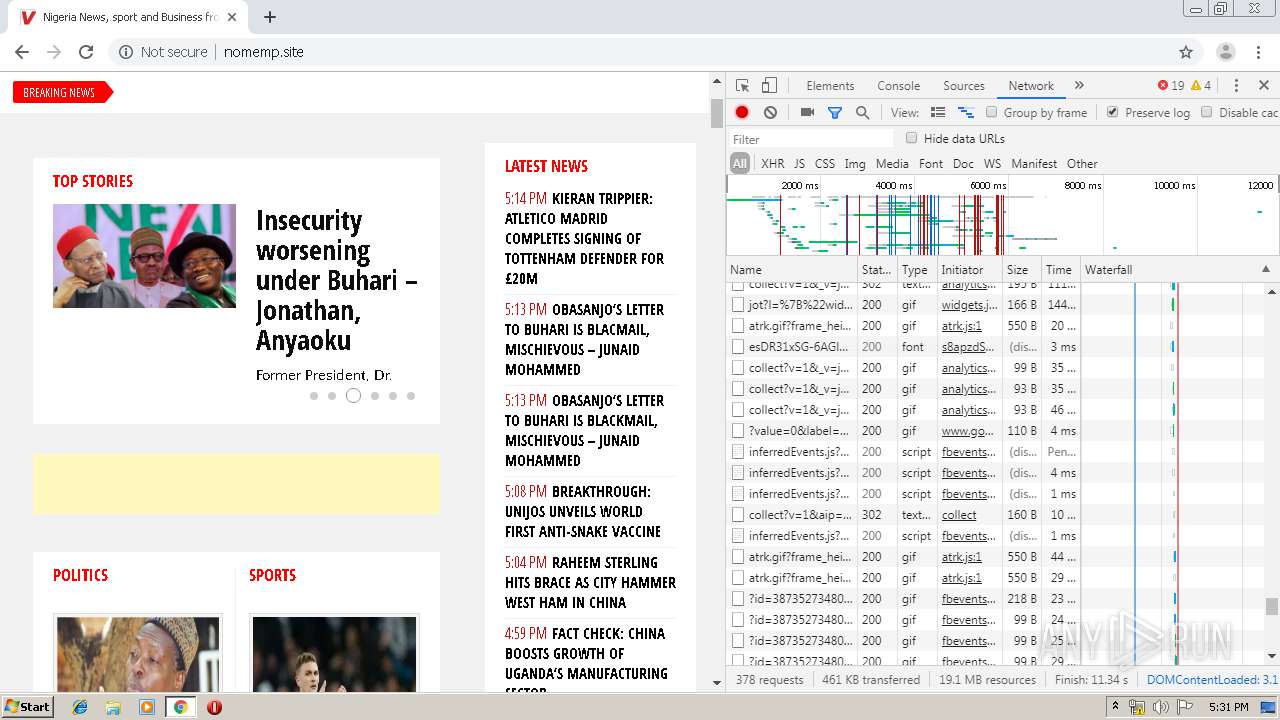
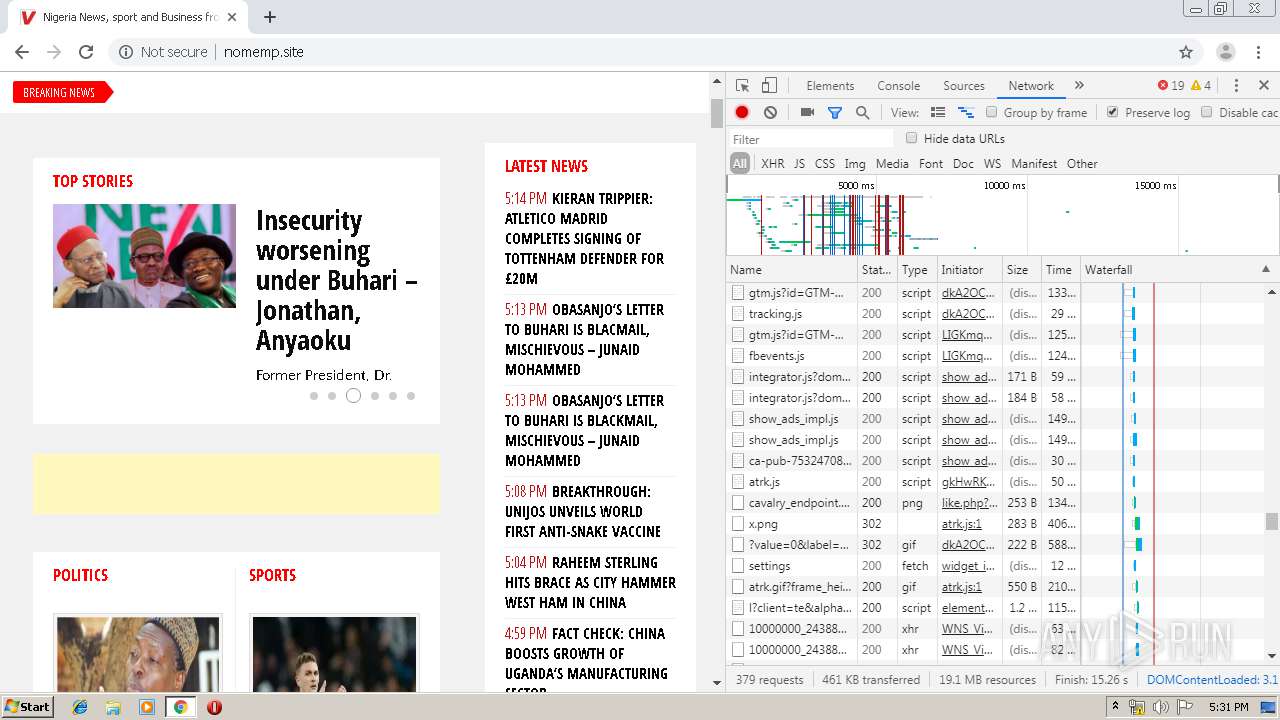
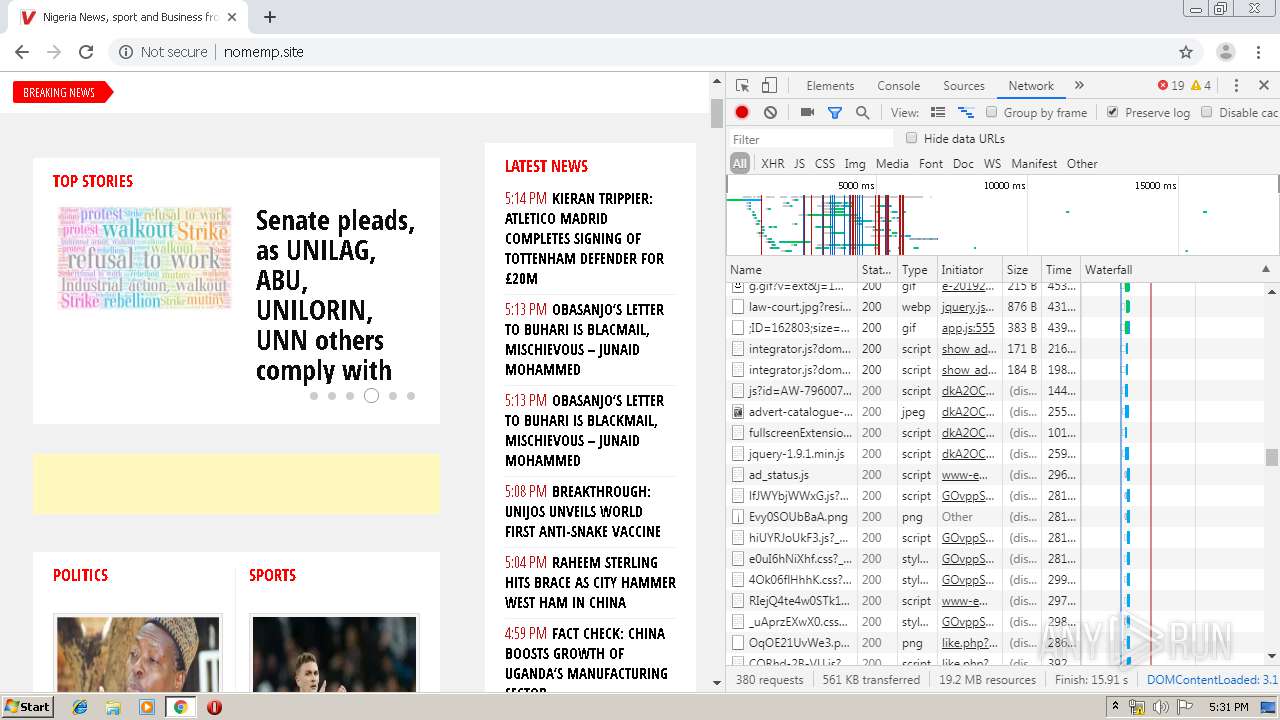
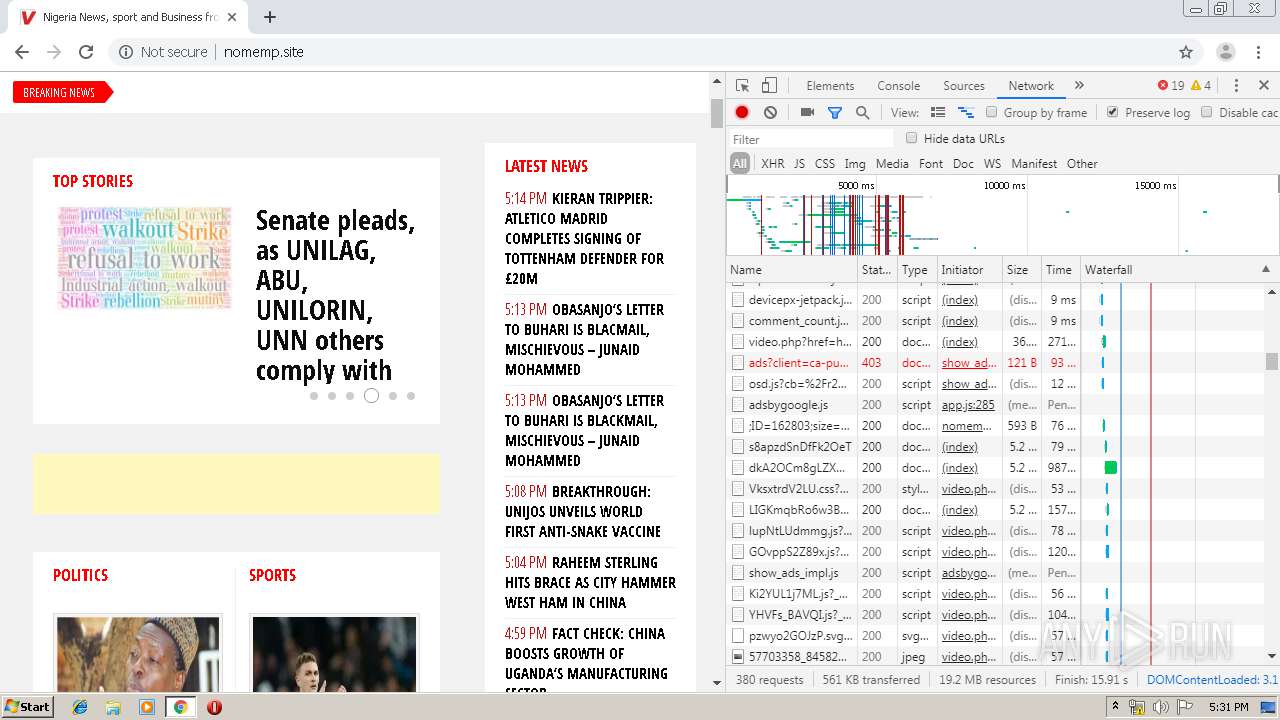
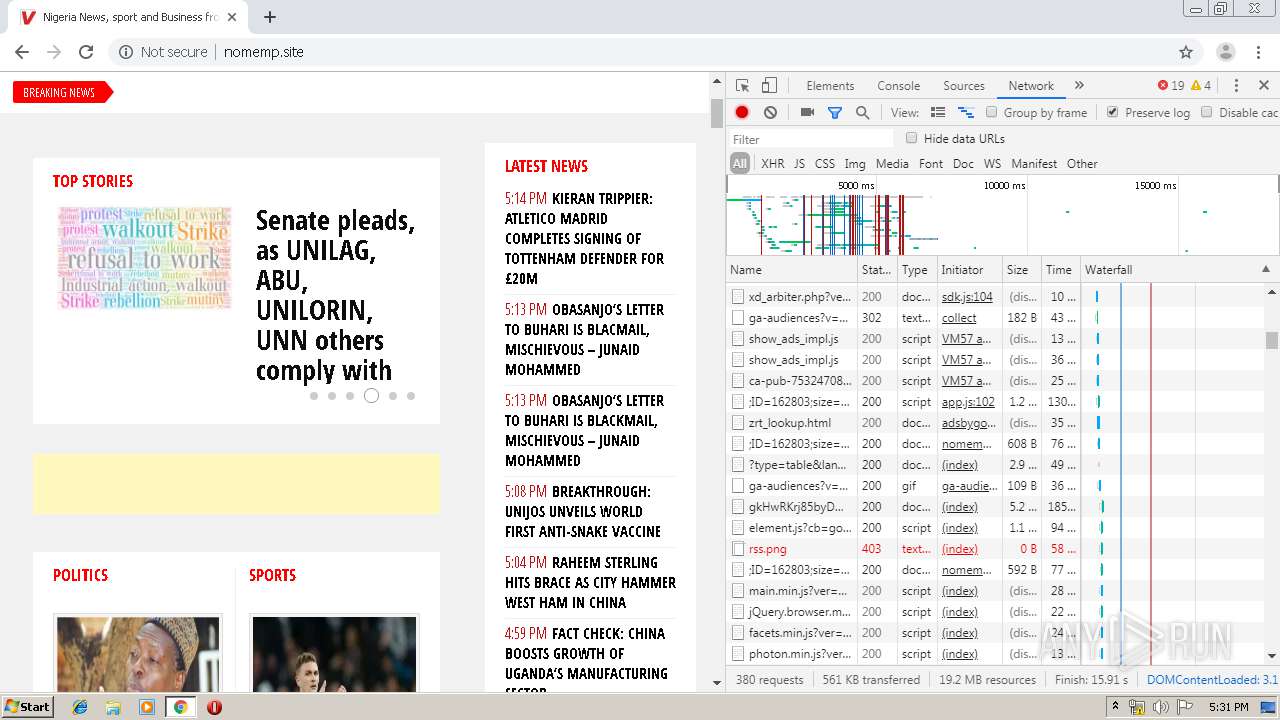
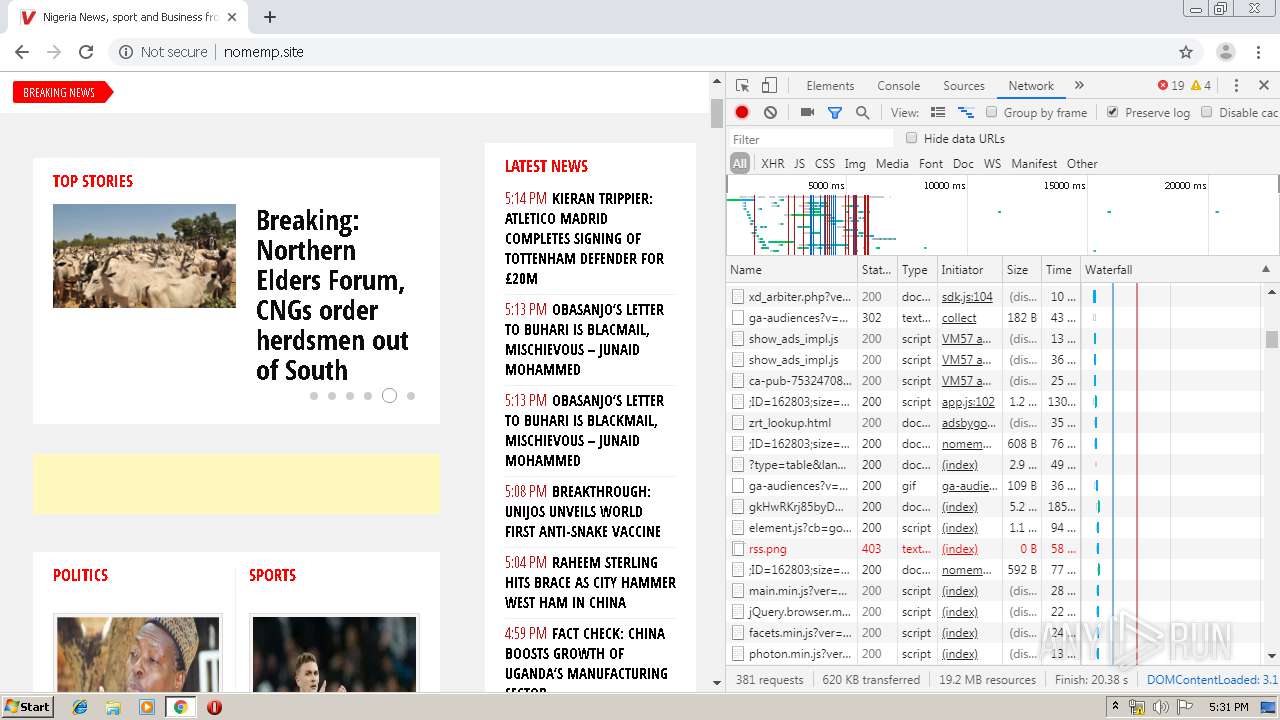
HTTP(S) requests
46
TCP/UDP connections
157
DNS requests
114
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
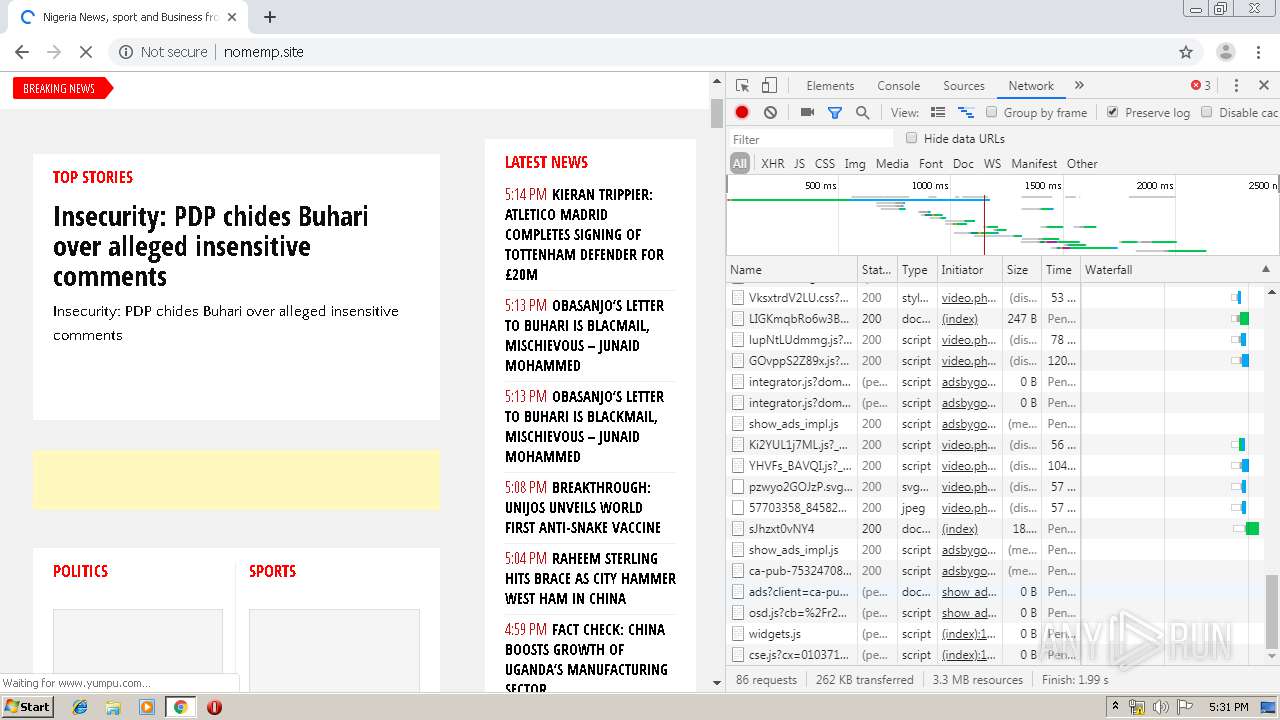
2888 | chrome.exe | OPTIONS | 200 | 185.86.138.16:80 | http://www14.smartadserver.com/3369/call | FR | — | — | whitelisted |
2888 | chrome.exe | OPTIONS | 200 | 185.86.138.16:80 | http://www14.smartadserver.com/3369/call?cklb=1 | FR | — | — | whitelisted |
2888 | chrome.exe | GET | 302 | 52.94.234.174:80 | http://cloudfront-labs.amazonaws.com/x.png | US | — | — | shared |
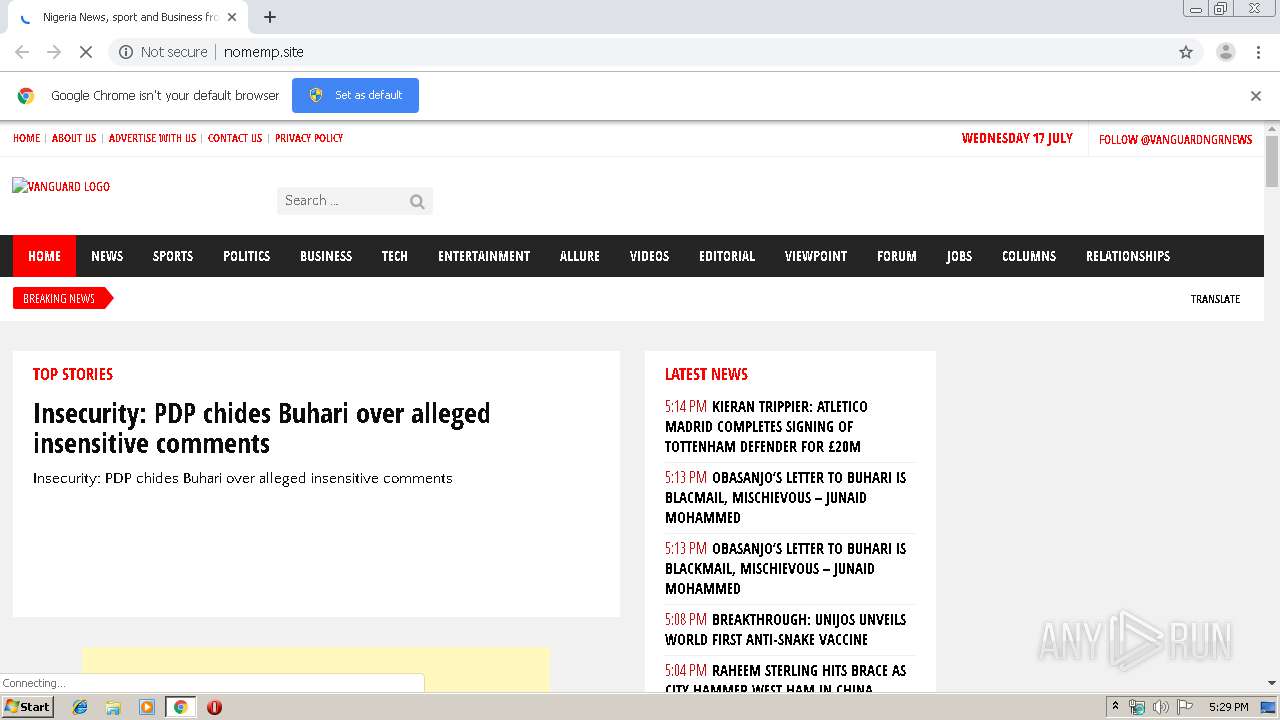
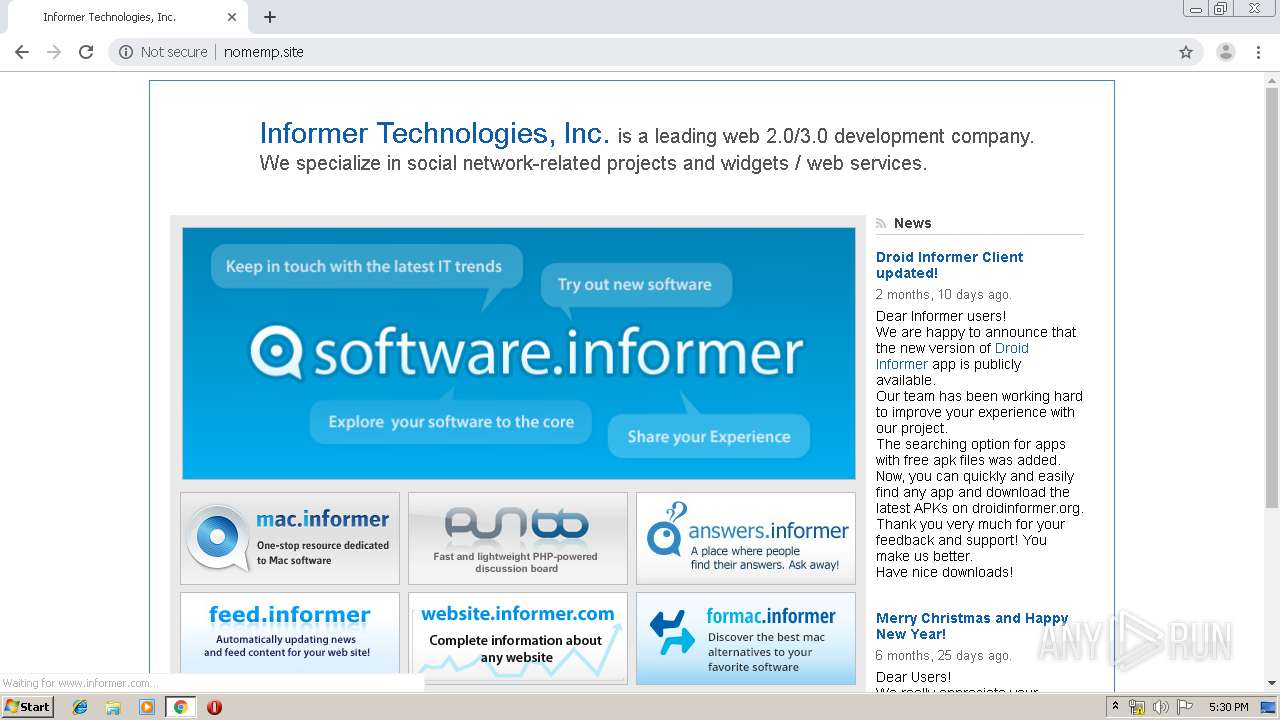
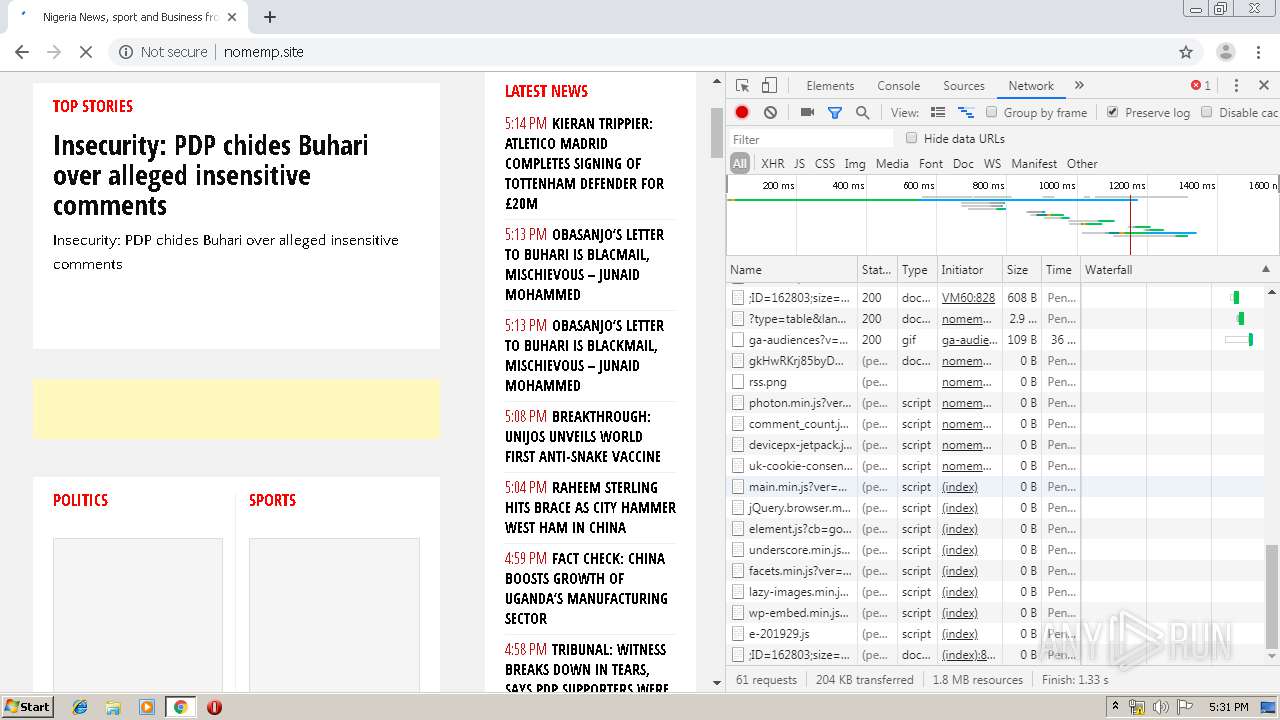
2888 | chrome.exe | GET | 200 | 194.34.107.76:80 | http://nomemp.site/ | unknown | html | 197 Kb | suspicious |
2888 | chrome.exe | GET | 200 | 116.202.46.88:80 | http://servedbyadbutler.com/adserve/;ID=162803;size=728x90;setID=151332;type=async;domid=placement_151332_0;place=0;pid=7600394;sw=1280;sh=720;spr=1;rnd=7600394;click=CLICK_MACRO_PLACEHOLDER | IN | html | 833 b | whitelisted |
2888 | chrome.exe | GET | 200 | 216.58.207.46:80 | http://cse.google.com/cse.js?cx=010371049068120156370:q16tcaebkls | US | text | 3.64 Kb | whitelisted |
2888 | chrome.exe | GET | 200 | 172.217.18.162:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 33.4 Kb | whitelisted |
2888 | chrome.exe | POST | 307 | 185.86.138.16:80 | http://www14.smartadserver.com/3369/call | FR | — | — | whitelisted |
2888 | chrome.exe | GET | 200 | 116.202.46.88:80 | http://servedbyadbutler.com/getad.img/;libID=680618 | IN | image | 30.0 Kb | whitelisted |
2888 | chrome.exe | GET | 200 | 68.232.35.16:80 | http://ced.sascdn.com/tag/3369/smart.js | US | text | 9.83 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
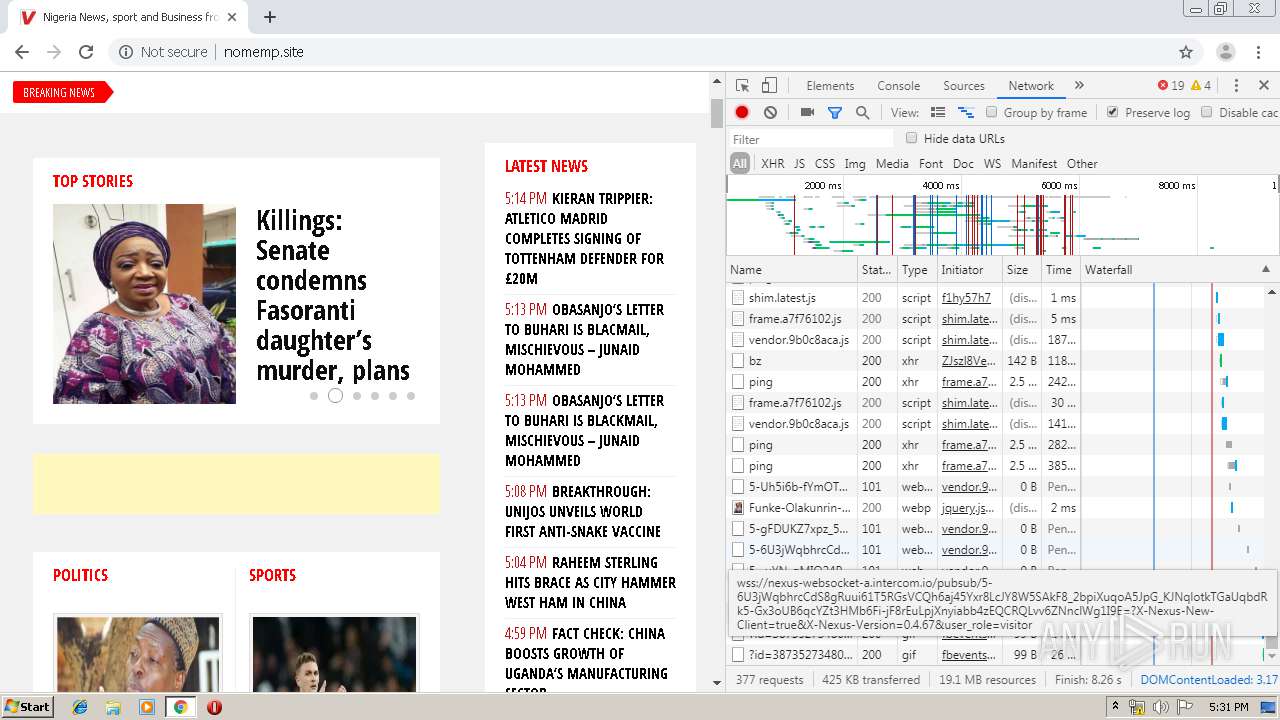
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2888 | chrome.exe | 194.34.107.76:80 | nomemp.site | — | — | suspicious |
2888 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2888 | chrome.exe | 104.28.7.135:443 | www.vanguardngr.com | Cloudflare Inc | US | shared |
2888 | chrome.exe | 172.217.23.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2888 | chrome.exe | 172.217.22.66:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
2888 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2888 | chrome.exe | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2888 | chrome.exe | 192.0.77.32:443 | s0.wp.com | Automattic, Inc | US | suspicious |
2888 | chrome.exe | 104.20.111.39:443 | static.addtoany.com | Cloudflare Inc | US | shared |
2888 | chrome.exe | 172.217.22.14:80 | translate.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
nomemp.site |
| suspicious |
accounts.google.com |
| shared |
www.vanguardngr.com |
| suspicious |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
s.w.org |
| whitelisted |
cdn.vanguardngr.com |
| malicious |
fonts.gstatic.com |
| whitelisted |