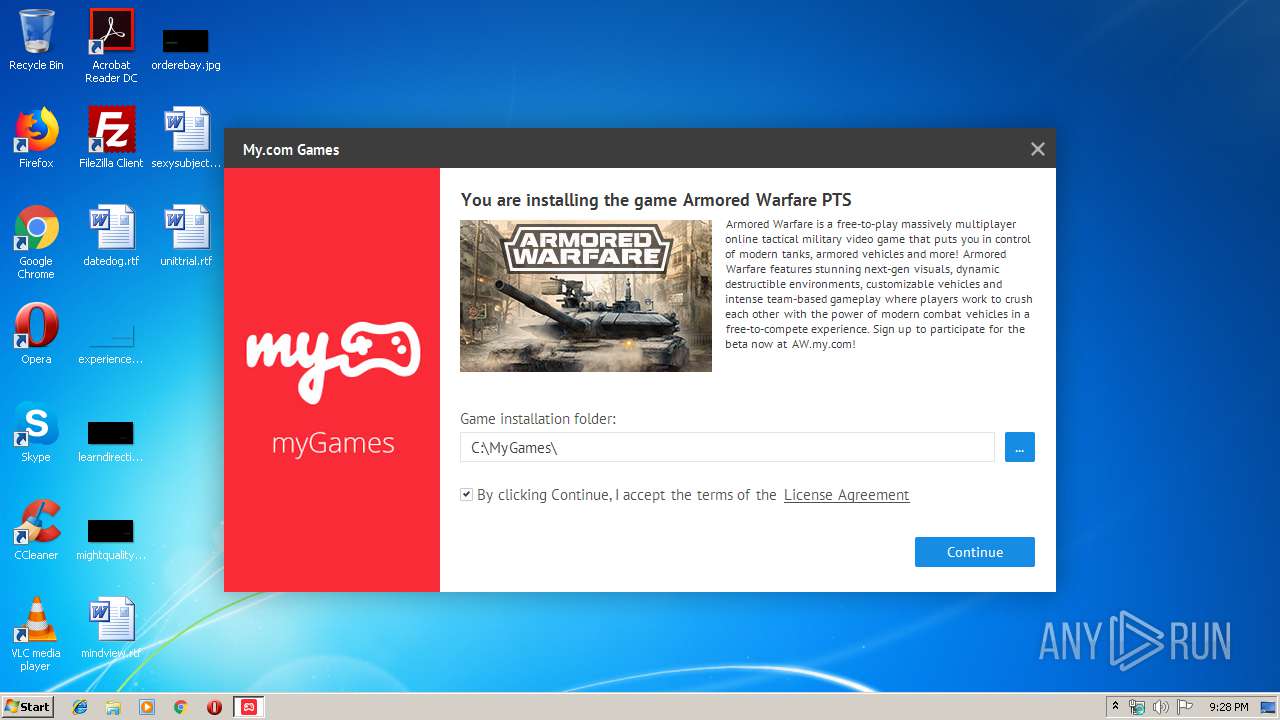
| File name: | ArmwarPtsMycomLoader_1c2ba9393a26a62b78be022cd5ed9340_Test.exe |
| Full analysis: | https://app.any.run/tasks/576978dc-3949-42cd-91a8-28c4dcf0214f |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 21:27:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 76FCECEEDBDEC9CE1837ADCD821B07C0 |
| SHA1: | 4521DA12E1C494A9F5020E19575B54E438361562 |
| SHA256: | 0271D4B54F50549B918F1B58FA45EFFB20E70AA265E25B1D4ECD25532E1474F4 |
| SSDEEP: | 98304:7POcOS6x9ZMC+OFTxurdYexDJvF0KQhl3OZv1/H4sbTpvp9:7PrOJMnWTArdY6mKQhleXPfpB9 |
MALICIOUS
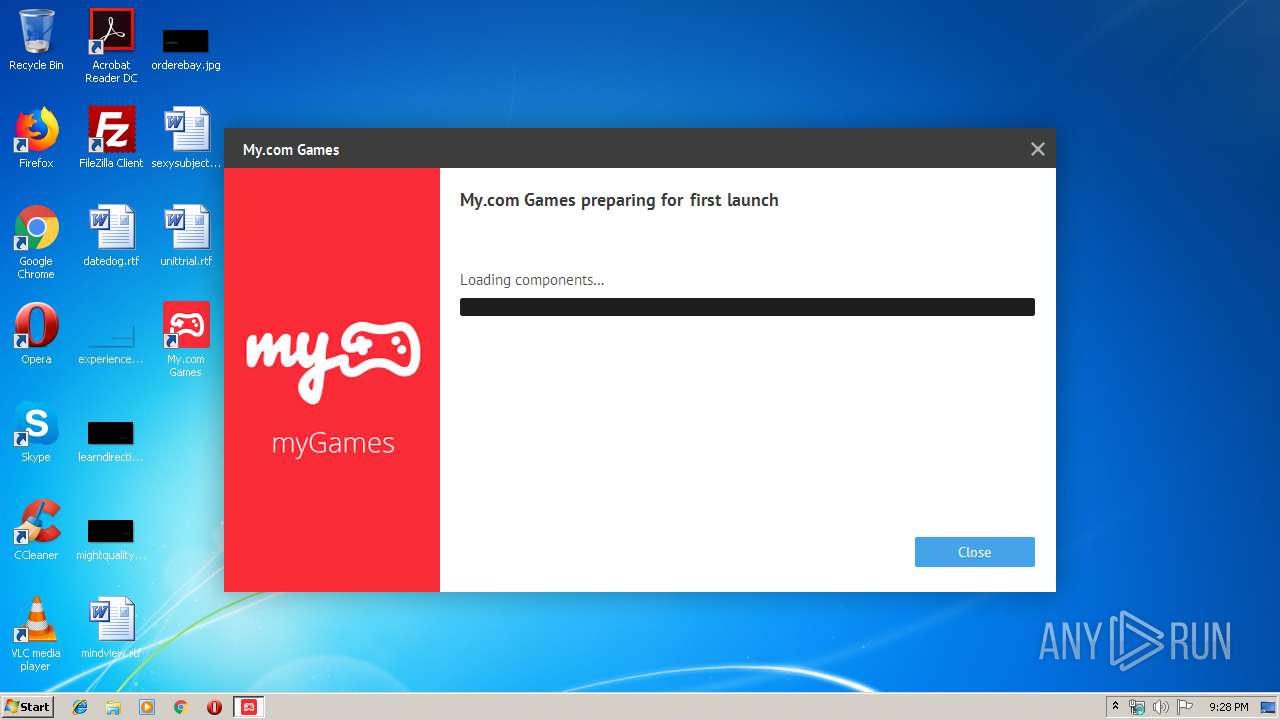
Application was dropped or rewritten from another process
- MyComGames.exe (PID: 2968)
- MyComGames.exe (PID: 3492)
- MyComGames.exe (PID: 2572)
Loads dropped or rewritten executable
- MyComGames.exe (PID: 2968)
- MyComGames.exe (PID: 2572)
- rundll32.exe (PID: 1532)
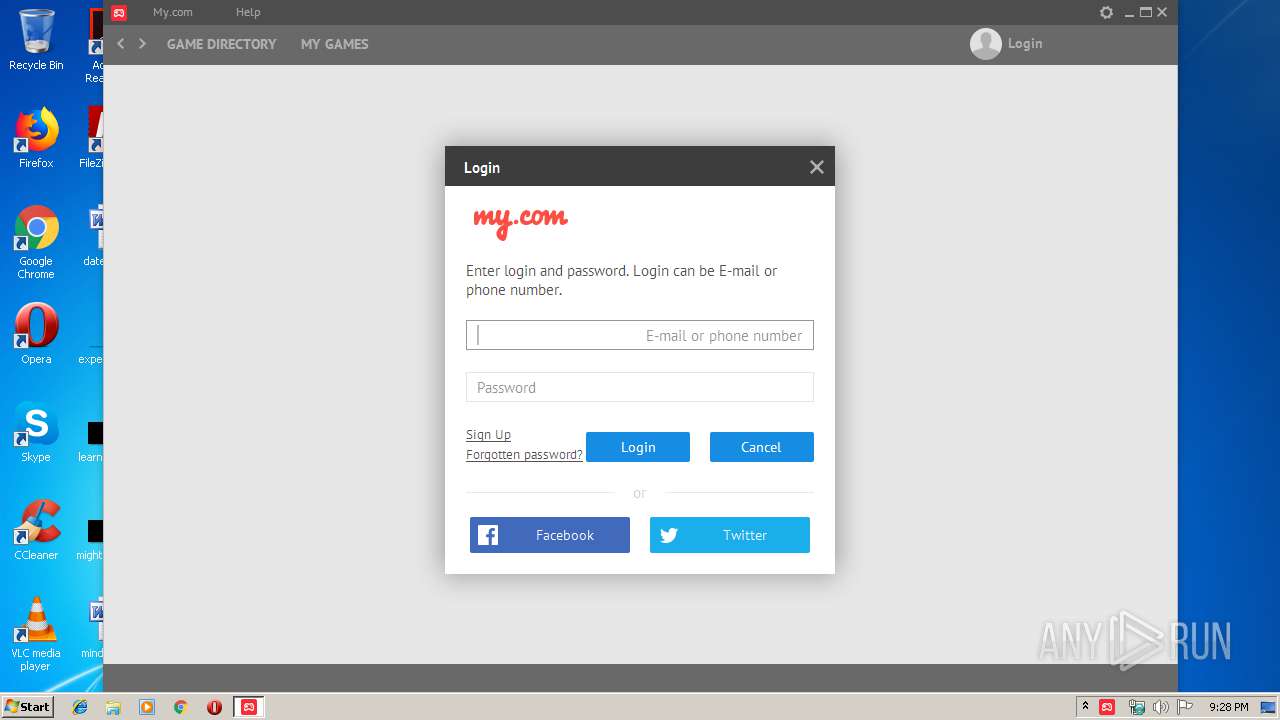
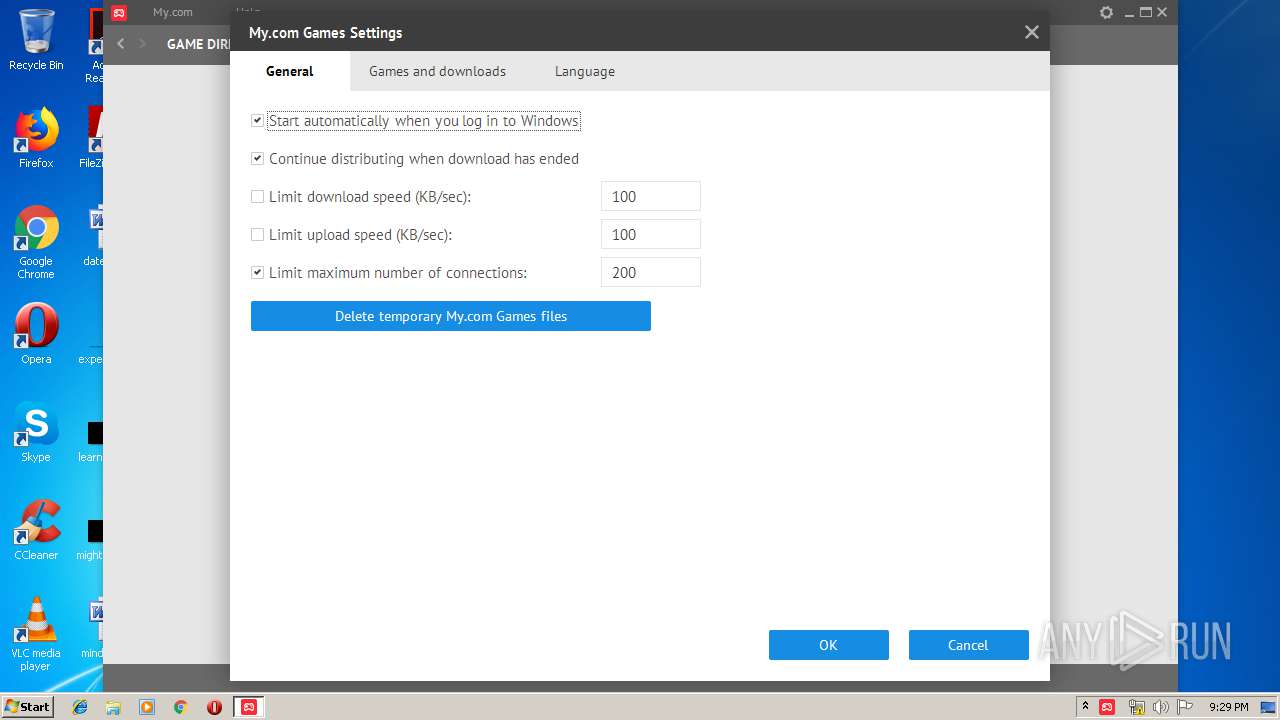
Changes the autorun value in the registry
- MyComGames.exe (PID: 2968)
SUSPICIOUS
Executable content was dropped or overwritten
- ArmwarPtsMycomLoader_1c2ba9393a26a62b78be022cd5ed9340_Test.exe (PID: 3636)
Creates files in the user directory
- MyComGames.exe (PID: 2968)
Application launched itself
- MyComGames.exe (PID: 2968)
Creates a software uninstall entry
- MyComGames.exe (PID: 2968)
Modifies the open verb of a shell class
- MyComGames.exe (PID: 2968)
Uses RUNDLL32.EXE to load library
- MyComGames.exe (PID: 2968)
Creates COM task schedule object
- rundll32.exe (PID: 1532)
Searches for installed software
- MyComGames.exe (PID: 2968)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (42.1) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (41.3) |
| .exe | | | Win32 Executable (generic) (7) |
| .exe | | | Win16/32 Executable Delphi generic (3.2) |
| .exe | | | Generic Win/DOS Executable (3.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:05:29 18:23:36+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 4861952 |
| InitializedDataSize: | 159744 |
| UninitializedDataSize: | 7557120 |
| EntryPoint: | 0xbd7ad0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.124.29102 |
| ProductVersionNumber: | 3.0.124.29102 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | MY.COM B.V. |
| FileDescription: | GAMES.MY.COM APPLICATION |
| FileVersion: | 3.0.124.29102 |
| ProductVersion: | 3.0.124.29102 |
| InternalName: | MyComSetup.exe |
| LegalCopyright: | Copyright (C) 2015 MY.COM B.V. |
| LegalTrademarks: | - |
| OriginalFileName: | MyComGames.exe |
| ProductName: | GAMES.MY.COM APPLICATION |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-May-2015 16:23:36 |
| Detected languages: |
|
| CompanyName: | MY.COM B.V. |
| FileDescription: | GAMES.MY.COM APPLICATION |
| FileVersion: | 3.0.124.29102 |
| ProductVersion: | 3.0.124.29102 |
| InternalName: | MyComSetup.exe |
| LegalCopyright: | Copyright (C) 2015 MY.COM B.V. |
| LegalTrademarks: | - |
| OriginalFilename: | MyComGames.exe |
| ProductName: | GAMES.MY.COM APPLICATION |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 29-May-2015 16:23:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00735000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00736000 | 0x004A3000 | 0x004A2800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99995 |
.rsrc | 0x00BD9000 | 0x00027000 | 0x00026400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.31501 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.39093 | 1296 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.12423 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.54454 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.76066 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.91516 | 6760 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.10191 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.37584 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 4.60843 | 1720 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 4.76021 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4089 | 7.653 | 596 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
KERNEL32.DLL |
advapi32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
35
Monitored processes
5
Malicious processes
4
Suspicious processes
0
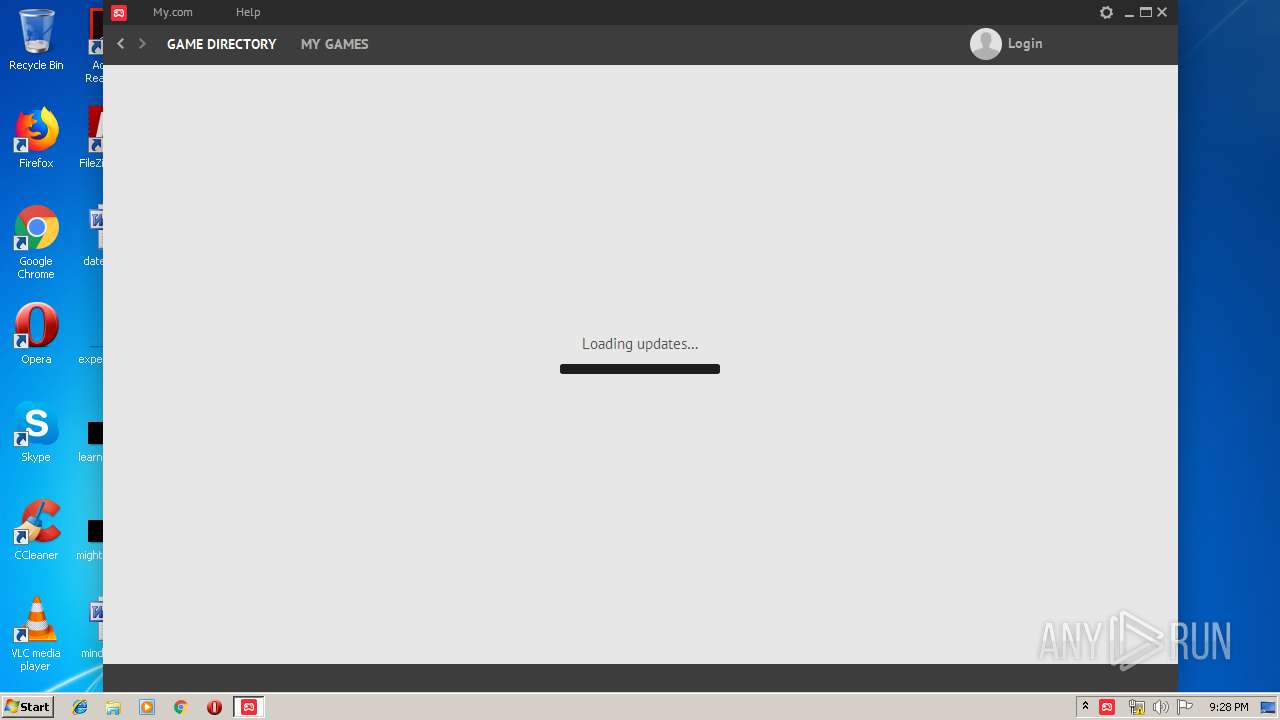
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1532 | "C:\Windows\system32\rundll32.exe" "C:\Users\admin\AppData\Local\MyComGames\NPMyComDetector.dll",DllEntryPoint RegisterPlugin | C:\Windows\system32\rundll32.exe | — | MyComGames.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2572 | "C:\Users\admin\AppData\Local\MyComGames\MyComGames.exe" | C:\Users\admin\AppData\Local\MyComGames\MyComGames.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2968 | "C:\Users\admin\AppData\Local\MyComGames\MyComGames.exe" -startedbysetup "installer=C:\Users\admin\AppData\Local\Temp\ArmwarPtsMycomLoader_1c2ba9393a26a62b78be022cd5ed9340_Test.exe" game=13.2000010 -removeifinstallcanceled | C:\Users\admin\AppData\Local\MyComGames\MyComGames.exe | ArmwarPtsMycomLoader_1c2ba9393a26a62b78be022cd5ed9340_Test.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3492 | "C:\Users\admin\AppData\Local\MyComGames\MyComGames.exe" -rebuildiconcache | C:\Users\admin\AppData\Local\MyComGames\MyComGames.exe | — | MyComGames.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3636 | "C:\Users\admin\AppData\Local\Temp\ArmwarPtsMycomLoader_1c2ba9393a26a62b78be022cd5ed9340_Test.exe" | C:\Users\admin\AppData\Local\Temp\ArmwarPtsMycomLoader_1c2ba9393a26a62b78be022cd5ed9340_Test.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 263
Read events
1 211
Write events
52
Delete events
0
Modification events
| (PID) Process: | (3636) ArmwarPtsMycomLoader_1c2ba9393a26a62b78be022cd5ed9340_Test.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3636) ArmwarPtsMycomLoader_1c2ba9393a26a62b78be022cd5ed9340_Test.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3492) MyComGames.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop\WindowMetrics |
| Operation: | write | Name: | Shell Icon Size |
Value: 31 | |||
| (PID) Process: | (3492) MyComGames.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop\WindowMetrics |
| Operation: | write | Name: | Shell Icon Size |
Value: 32 | |||
| (PID) Process: | (1532) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\MozillaPlugins\@my.com/Games |
| Operation: | write | Name: | Path |
Value: C:\Users\admin\AppData\Local\MyComGames\NPMyComDetector.dll | |||
| (PID) Process: | (1532) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\MozillaPlugins\@my.com/Games |
| Operation: | write | Name: | ProductName |
Value: My.com Games Detector | |||
| (PID) Process: | (1532) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\MozillaPlugins\@my.com/Games |
| Operation: | write | Name: | Vendor |
Value: My.com, Inc | |||
| (PID) Process: | (1532) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\MozillaPlugins\@my.com/Games |
| Operation: | write | Name: | Version |
Value: 2.0.4.0 | |||
| (PID) Process: | (1532) rundll32.exe | Key: | HKEY_CLASSES_ROOT\TypeLib\{1C54CBA4-DB79-427D-8FAD-5FD734506C09}\1.0 |
| Operation: | write | Name: | |
Value: NPMyComDetector | |||
| (PID) Process: | (1532) rundll32.exe | Key: | HKEY_CLASSES_ROOT\TypeLib\{1C54CBA4-DB79-427D-8FAD-5FD734506C09}\1.0\FLAGS |
| Operation: | write | Name: | |
Value: 0 | |||
Executable files
12
Suspicious files
1
Text files
97
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2968 | MyComGames.exe | C:\Users\admin\AppData\Local\MyComGames\writefiletest_2968 | — | |
MD5:— | SHA256:— | |||
| 3636 | ArmwarPtsMycomLoader_1c2ba9393a26a62b78be022cd5ed9340_Test.exe | C:\Users\admin\AppData\Local\MyComGames\main.log | text | |
MD5:— | SHA256:— | |||
| 3636 | ArmwarPtsMycomLoader_1c2ba9393a26a62b78be022cd5ed9340_Test.exe | C:\Users\admin\AppData\Local\MyComGames\npmycomdetector.dll | executable | |
MD5:— | SHA256:— | |||
| 3636 | ArmwarPtsMycomLoader_1c2ba9393a26a62b78be022cd5ed9340_Test.exe | C:\Users\admin\AppData\Local\MyComGames\GCLay64.dll | executable | |
MD5:— | SHA256:— | |||
| 2968 | MyComGames.exe | C:\Users\admin\AppData\Local\MyComGames\Installing\Cache\Big.Img\0904713A | image | |
MD5:— | SHA256:— | |||
| 3636 | ArmwarPtsMycomLoader_1c2ba9393a26a62b78be022cd5ed9340_Test.exe | C:\Users\admin\AppData\Local\MyComGames\MyComGames.exe | executable | |
MD5:— | SHA256:— | |||
| 3636 | ArmwarPtsMycomLoader_1c2ba9393a26a62b78be022cd5ed9340_Test.exe | C:\Users\admin\AppData\Local\MyComGames\gclay.dll | executable | |
MD5:— | SHA256:— | |||
| 2968 | MyComGames.exe | C:\Users\admin\AppData\Local\MyComGames\main.log | text | |
MD5:— | SHA256:— | |||
| 3636 | ArmwarPtsMycomLoader_1c2ba9393a26a62b78be022cd5ed9340_Test.exe | C:\Users\admin\AppData\Local\MyComGames\bigup2.dll | executable | |
MD5:— | SHA256:— | |||
| 3636 | ArmwarPtsMycomLoader_1c2ba9393a26a62b78be022cd5ed9340_Test.exe | C:\Users\admin\AppData\Local\MyComGames\MyComGames.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
21
DNS requests
12
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2968 | MyComGames.exe | GET | 200 | 185.30.176.115:80 | http://games.my.com/gcstat/stat.php?user_id=7974070130954217413&channel_id=35&build_id=124&stand=1&user_id2=15742307191278540529 | NL | — | — | whitelisted |
2968 | MyComGames.exe | GET | 200 | 185.30.176.135:80 | http://static.gc.my.com/torrents/mlfresources.torrent?_c_141369953 | NL | torrent | 344 b | suspicious |
2968 | MyComGames.exe | GET | 200 | 185.30.176.135:80 | http://static.gc.my.com/torrents/revision.txt?_c_375857675 | NL | text | 6 b | suspicious |
2968 | MyComGames.exe | GET | 200 | 185.30.176.115:80 | http://games.my.com/gcstat/stat.php?user_id=7974070130954217413&channel_id=35&build_id=124&stand=1&user_id2=15742307191278540529&distrib_id=2000010&type_id=13&event_id=316 | NL | — | — | whitelisted |
2968 | MyComGames.exe | GET | 200 | 185.30.176.115:80 | http://games.my.com/gcstat/stat.php?user_id=7974070130954217413&channel_id=35&build_id=124&stand=1&user_id2=15742307191278540529&distrib_id=2000010&type_id=13&event_id=302 | NL | — | — | whitelisted |
2968 | MyComGames.exe | GET | 200 | 185.30.176.135:80 | http://static.gc.my.com/torrents/mirrors.xml?_c_1173479713 | NL | xml | 585 b | suspicious |
2968 | MyComGames.exe | GET | 200 | 185.30.176.135:80 | http://static.gc.my.com/torrents/mcsettings.xml?_c_166565945 | NL | xml | 710 b | suspicious |
2968 | MyComGames.exe | GET | 200 | 185.30.176.135:80 | http://static.gc.my.com/torrents/repository.xml?_c_853749676 | NL | xml | 1.40 Kb | suspicious |
2968 | MyComGames.exe | GET | 200 | 198.255.13.10:80 | http://los.pkg.gc.my.com/packages/test.bin?_c_1437586518 | US | image | 16.8 Kb | suspicious |
2968 | MyComGames.exe | GET | 200 | 192.240.105.202:80 | http://chi3.pkg.gc.my.com/packages/test.bin?_c_1191125418 | US | image | 16.8 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2968 | MyComGames.exe | 50.7.69.10:80 | chi.pkg.gc.my.com | Cogent Communications | US | suspicious |
2968 | MyComGames.exe | 50.7.69.234:80 | chi2.pkg.gc.my.com | Cogent Communications | US | suspicious |
2968 | MyComGames.exe | 178.63.38.147:80 | p2p.gc.my.com | Hetzner Online GmbH | DE | suspicious |
2968 | MyComGames.exe | 192.240.105.202:80 | chi3.pkg.gc.my.com | Cogent Communications | US | suspicious |
2968 | MyComGames.exe | 50.7.73.114:80 | sea.pkg.gc.my.com | Cogent Communications | US | suspicious |
2968 | MyComGames.exe | 185.30.176.135:80 | static.gc.my.com | MRG Hosting B.V. | NL | suspicious |
2968 | MyComGames.exe | 198.255.13.10:80 | los.pkg.gc.my.com | Cogent Communications | US | suspicious |
2968 | MyComGames.exe | 192.240.113.50:80 | mia.pkg.gc.my.com | Cogent Communications | US | suspicious |
2968 | MyComGames.exe | 188.93.63.20:80 | msk.pkg.gc.my.com | Limited liability company Mail.Ru | RU | suspicious |
2968 | MyComGames.exe | 185.30.176.115:80 | games.my.com | MRG Hosting B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
static.gc.my.com |
| suspicious |
p2p.gc.my.com |
| suspicious |
chi.pkg.gc.my.com |
| suspicious |
chi2.pkg.gc.my.com |
| suspicious |
chi3.pkg.gc.my.com |
| suspicious |
los.pkg.gc.my.com |
| suspicious |
sea.pkg.gc.my.com |
| suspicious |
mia.pkg.gc.my.com |
| suspicious |
mia2.pkg.gc.my.com |
| suspicious |
msk.pkg.gc.my.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2968 | MyComGames.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent - Torrent File Downloaded |
2968 | MyComGames.exe | Potential Corporate Privacy Violation | GPL P2P BitTorrent announce request |