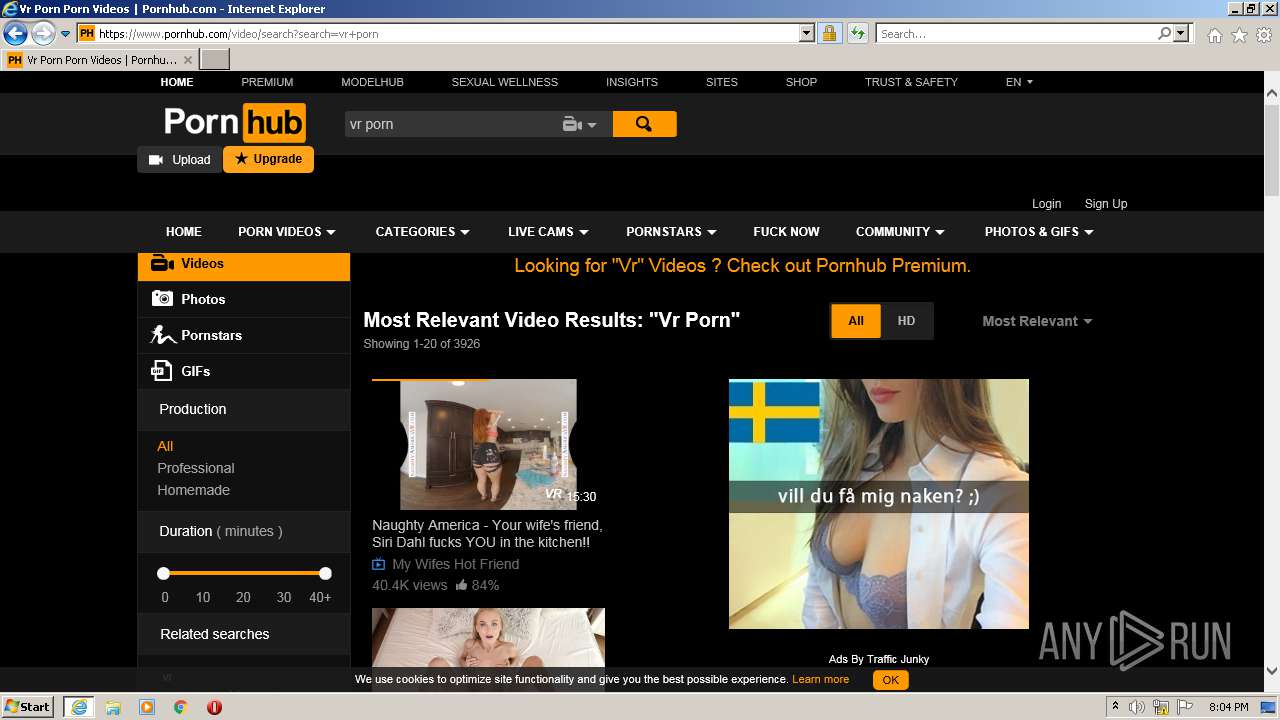
| URL: | https://pornhub.com |
| Full analysis: | https://app.any.run/tasks/5b1314f9-0a84-4e7a-8273-e1014ad63245 |
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2021, 19:04:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D074634084A1556083FCD17C0254B557 |
| SHA1: | 7BBE57E2B76AB33DDD775A3654C017520947B7EA |
| SHA256: | 0244D6D881C5FAB1A496641A6EC8311C3B1F53E722E97FED34D495747977DC2C |
| SSDEEP: | 3:N8OpQH2:2O+W |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3328)
- iexplore.exe (PID: 2108)
INFO
Checks supported languages
- iexplore.exe (PID: 1816)
- iexplore.exe (PID: 3328)
- iexplore.exe (PID: 2108)
Reads the computer name
- iexplore.exe (PID: 1816)
- iexplore.exe (PID: 3328)
- iexplore.exe (PID: 2108)
Changes internet zones settings
- iexplore.exe (PID: 1816)
Reads settings of System Certificates
- iexplore.exe (PID: 3328)
- iexplore.exe (PID: 1816)
- iexplore.exe (PID: 2108)
Checks Windows Trust Settings
- iexplore.exe (PID: 1816)
- iexplore.exe (PID: 2108)
- iexplore.exe (PID: 3328)
Reads internet explorer settings
- iexplore.exe (PID: 3328)
- iexplore.exe (PID: 2108)
Application launched itself
- iexplore.exe (PID: 1816)
Creates files in the user directory
- iexplore.exe (PID: 3328)
- iexplore.exe (PID: 2108)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3328)
Changes settings of System certificates
- iexplore.exe (PID: 1816)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1816 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://pornhub.com" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1816 CREDAT:922897 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3328 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1816 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
29 422
Read events
29 154
Write events
266
Delete events
2
Modification events
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 319804256 | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30895989 | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 619809178 | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30895989 | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
38
Text files
428
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B9C0457FE8FDF881D9EA458DAD3D4142_79C09928C2DEED6D69E117D673E3388B | binary | |
MD5:FDF7ABEEF632A89E63B08080297C7148 | SHA256:37E47334E71381B68DD6E964F74E2EF627479245816AA7BC35240DCB94018727 | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\25WI3Y8Q.txt | text | |
MD5:9ACD0F39471F7367EE498DA6EE372C9A | SHA256:28839198A4A17269715779B03D08796645BC3BB0784824CB0FA4730D86BD2AD9 | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_B514E3306E9B5CC22C1D3DB90570477A | der | |
MD5:65B31D908863FD64B3894B0C7D09F54F | SHA256:668B0661CDA20A490D16C989D22D67F7D32140982A2840072411641564CDE8EC | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\X0GEHY2Z.txt | text | |
MD5:5C24722692057BFAB54FE6900C5B6CC0 | SHA256:81E66A49AF9DB2A2324A820DAE1C954312938B187C3F291DF4244F2D00DC27A5 | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B9C0457FE8FDF881D9EA458DAD3D4142_79C09928C2DEED6D69E117D673E3388B | der | |
MD5:824D8C5DE536481C740A85A48C7E2A43 | SHA256:9CEAFF804C7098B33A199901A3996BD0594FCC4F7250C9E757B8FE95FC556205 | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\DMWQQV78.txt | text | |
MD5:A9F1501E38F7D2A57CFCC5E714DC8AD2 | SHA256:329B78AEA6CA3DEAB4375F3133CFF75F51D3F0B25758A1CB7131C3EA6CE736AF | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:60F3CC950EE31DD1C3F9D86B311BFEF0 | SHA256:52DD562EDEB6263B990B6296122ACCA206158ECBDE3530595E591AFE28532AE4 | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\ph-functions[1].js | text | |
MD5:2A0EABB9948C6073DC306A1E2CA5402F | SHA256:1C30E03A942076B406325B2047DA4CDB7D34C6D0BD1C12C103170C3A95774DC0 | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\C2S5S5YL.txt | text | |
MD5:C15A11B66864D2DB644E4435A4613ACF | SHA256:E277B1A5FE7A00BF24E17CD47B313DFE828FBD4EDCF6B0FD5A71EFA0FF7A012E | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\generated-header[1].css | text | |
MD5:DFFF6B5CBDC91BC3123D2599123EFFFE | SHA256:897F3D34F191316D5C8BE4E72BD771FE5E8D97C128793631B3456142EF05EA13 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
227
DNS requests
59
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3328 | iexplore.exe | GET | 200 | 2.16.186.81:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fbcc6061a0b1d529 | unknown | compressed | 4.70 Kb | whitelisted |
3328 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAwbRijP%2Fi%2FbU8PLz0ngZ50%3D | US | der | 471 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAonX%2BcE1u7LI9XNW0saTgQ%3D | US | der | 471 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAd3SBjpSMd4ojHOUsfJYh8%3D | US | der | 313 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAwPBc0dYg%2Bsu4Yh%2B%2BOb2hA%3D | US | der | 471 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA3hBbqb7pFPfKFAtRUkla4%3D | US | der | 471 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 2.16.186.9:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgQ%2Fjd1EdrQnOwI%2BSDevOv7dYg%3D%3D | unknown | der | 503 b | shared |
3328 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDbXVTrtaQF9AoAAAAA4FGm | US | der | 472 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 13.32.23.206:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3328 | iexplore.exe | 66.254.114.41:443 | pornhub.com | Reflected Networks, Inc. | US | malicious |
3328 | iexplore.exe | 2.16.186.81:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3328 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3328 | iexplore.exe | 205.185.208.79:443 | static.trafficjunky.com | Highwinds Network Group, Inc. | US | unknown |
3328 | iexplore.exe | 142.250.181.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3328 | iexplore.exe | 66.254.122.21:443 | ei.phncdn.com | Reflected Networks, Inc. | US | suspicious |
3328 | iexplore.exe | 13.32.23.69:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
3328 | iexplore.exe | 13.32.23.206:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
3328 | iexplore.exe | 66.254.114.38:443 | ads.trafficjunky.net | Reflected Networks, Inc. | US | unknown |
3328 | iexplore.exe | 66.254.114.156:443 | cdn1-smallimg.phncdn.com | Reflected Networks, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pornhub.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.pornhub.com |
| whitelisted |
ci.phncdn.com |
| whitelisted |
static.trafficjunky.com |
| whitelisted |
ei.phncdn.com |
| whitelisted |
hubt.pornhub.com |
| whitelisted |
ss.phncdn.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |