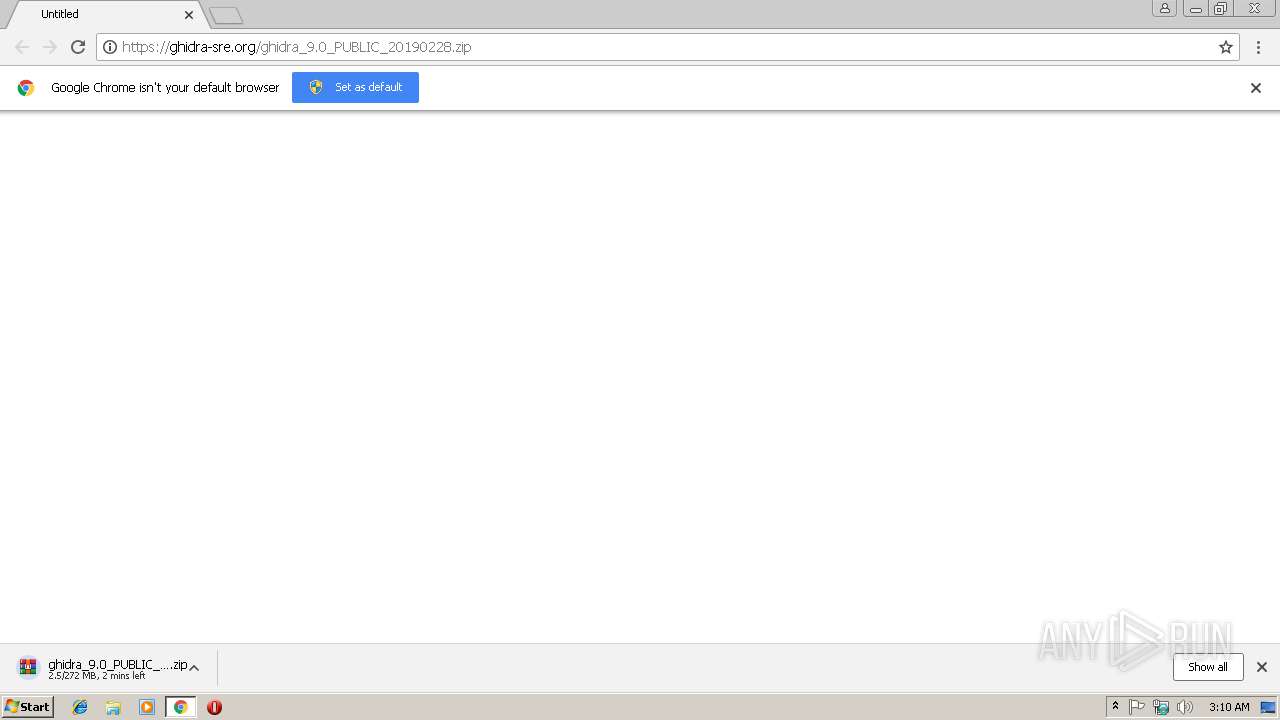
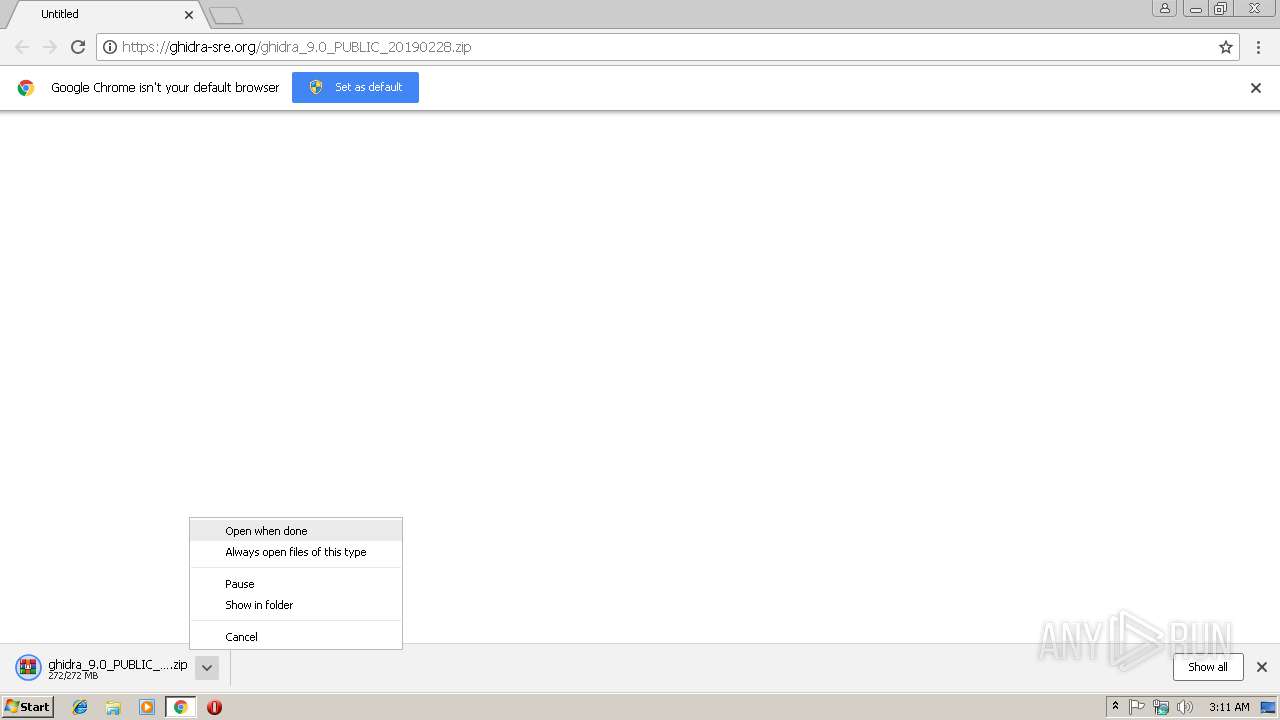
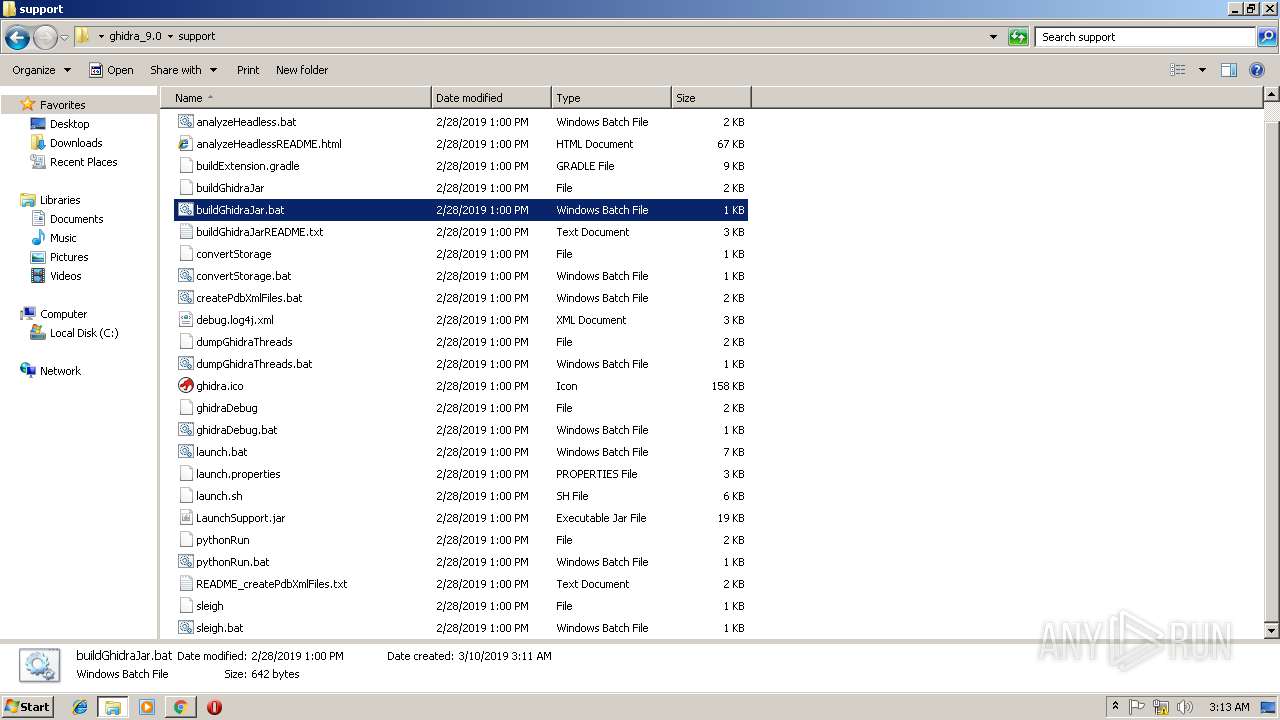
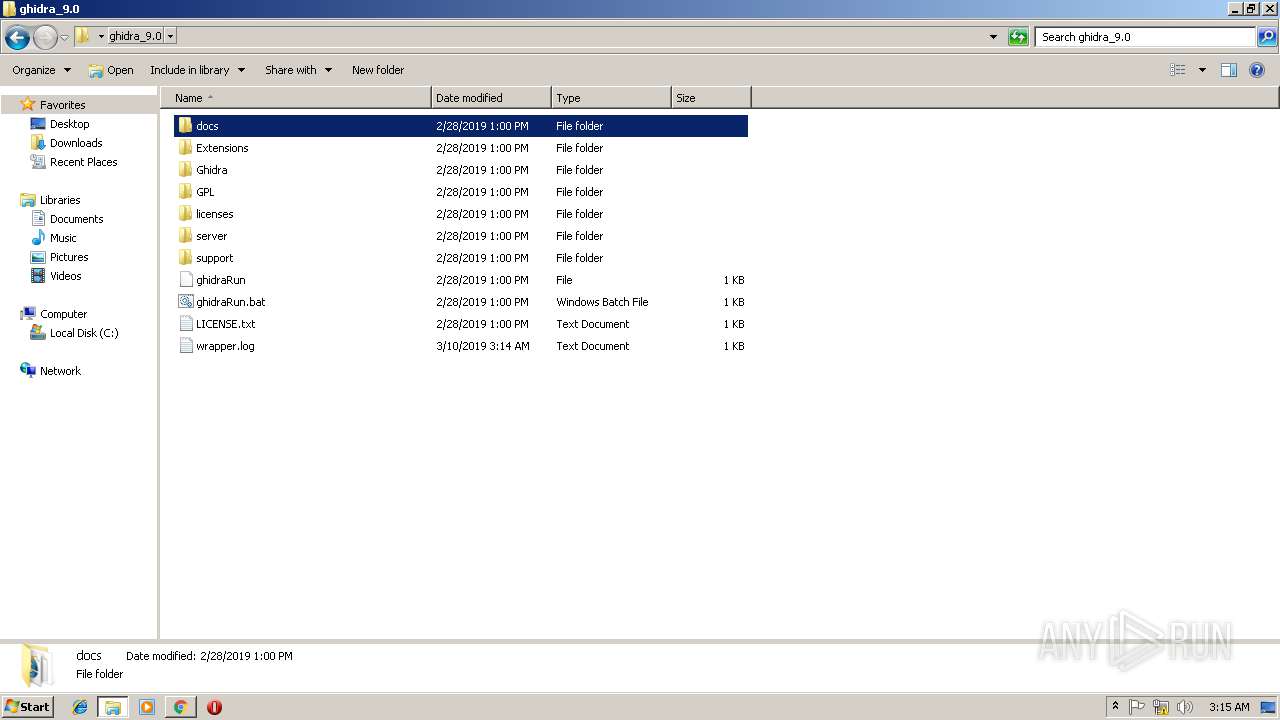
| URL: | https://ghidra-sre.org/ghidra_9.0_PUBLIC_20190228.zip |
| Full analysis: | https://app.any.run/tasks/f77ee644-73c4-4e2d-a58f-ae7cc0019145 |
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2019, 03:10:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DCC4365055FF7392569563B040A4A29D |
| SHA1: | 136F2D26C40A63D578C80E7B7108671D27872F66 |
| SHA256: | 0244BD5A28A3F451172CC8D456352C9EABF343A0941EAB70DF0D7E3434254E29 |
| SSDEEP: | 3:N8syE6DEUcoH6uIRMV:2syE6DEUc/uIqV |
MALICIOUS
No malicious indicators.SUSPICIOUS
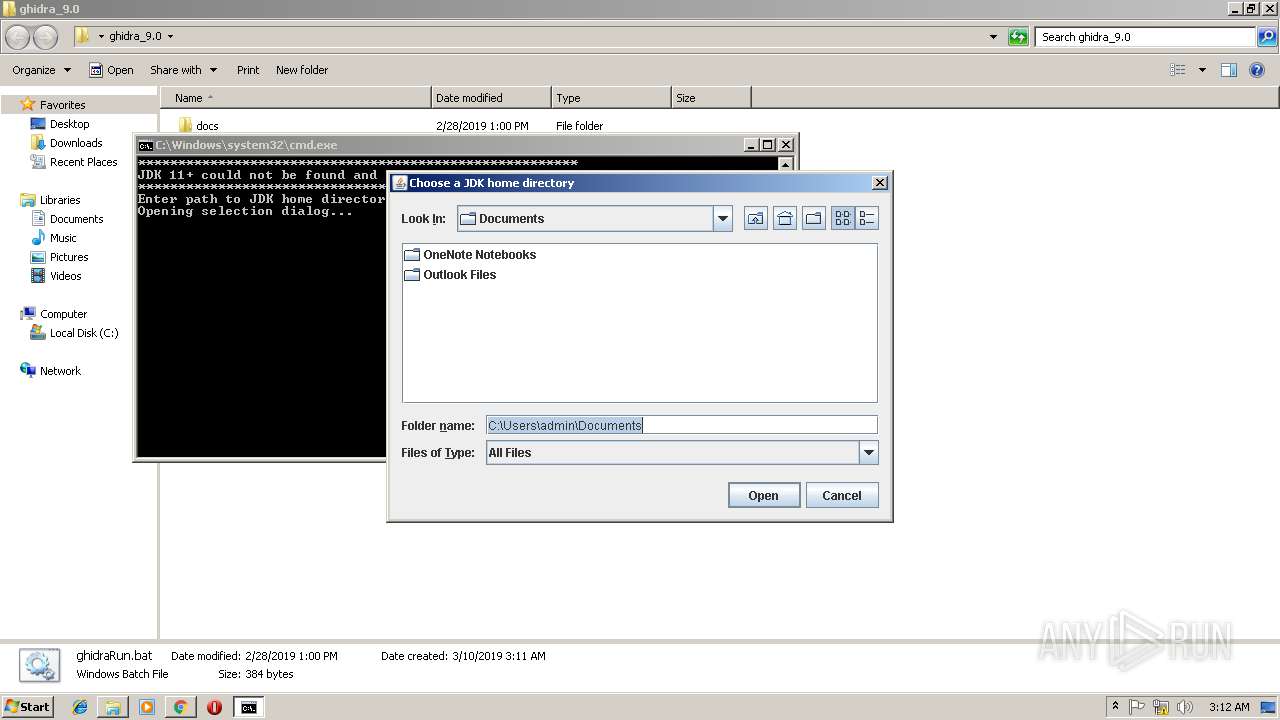
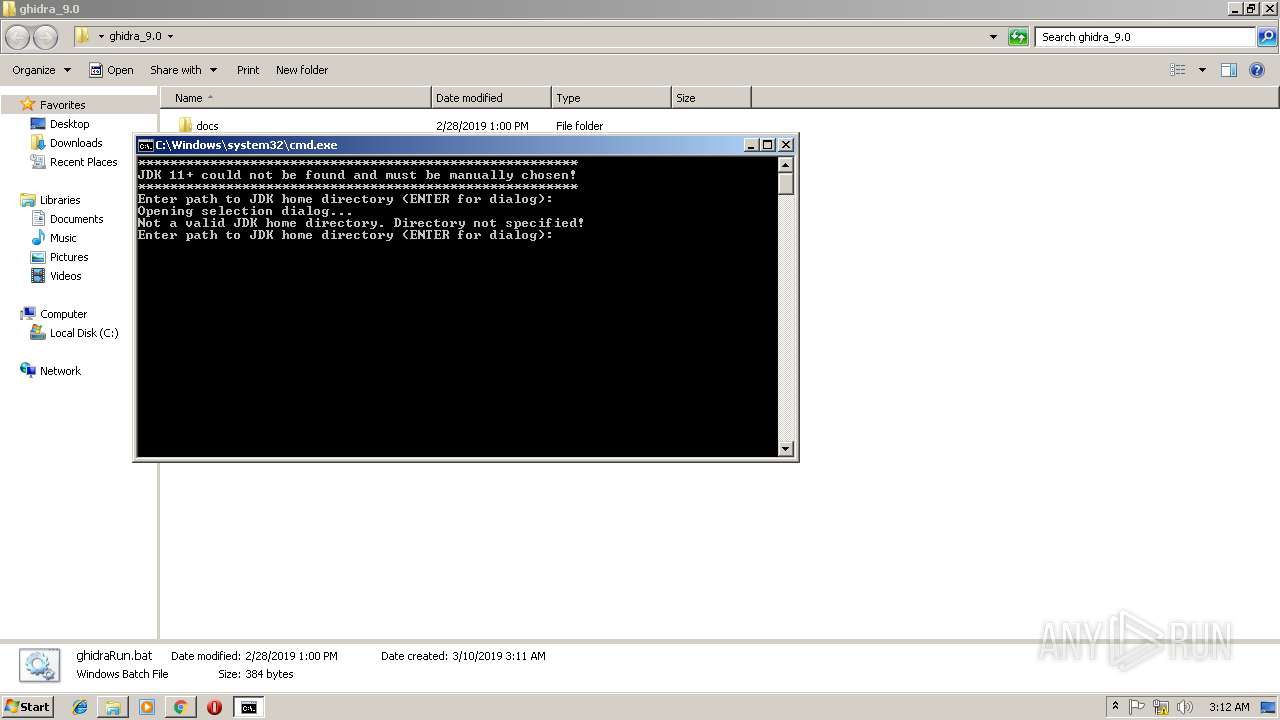
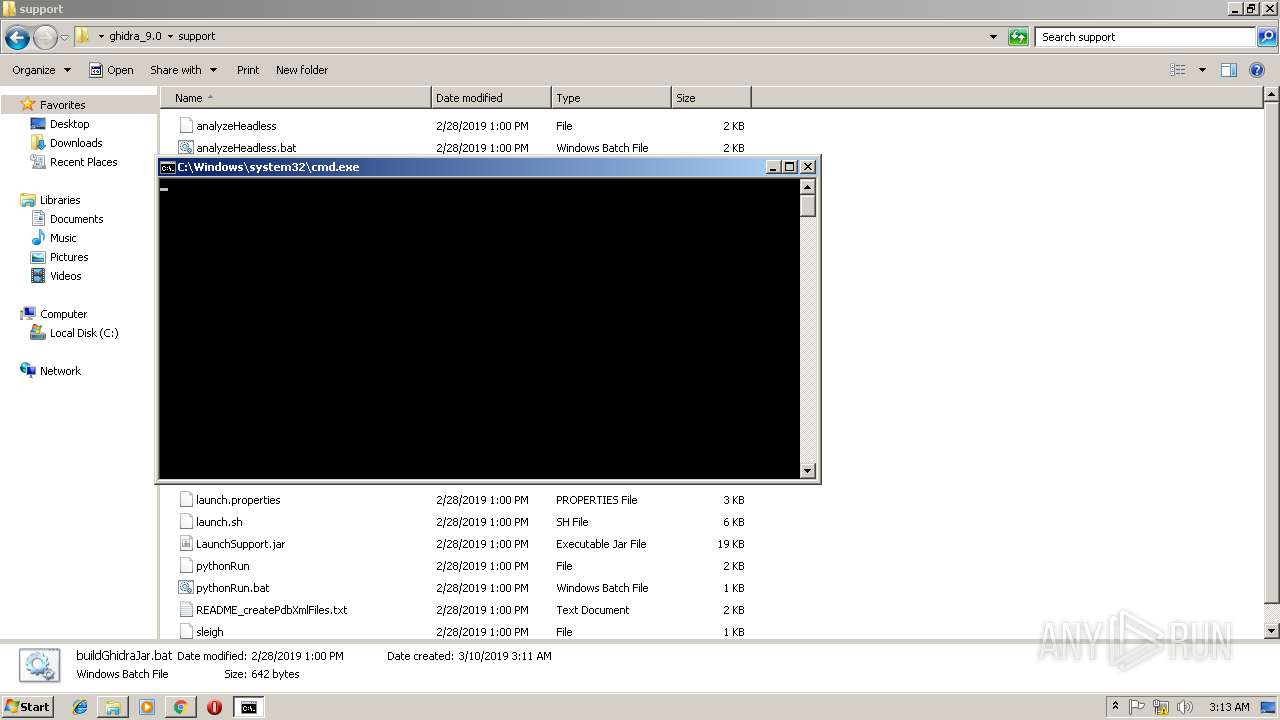
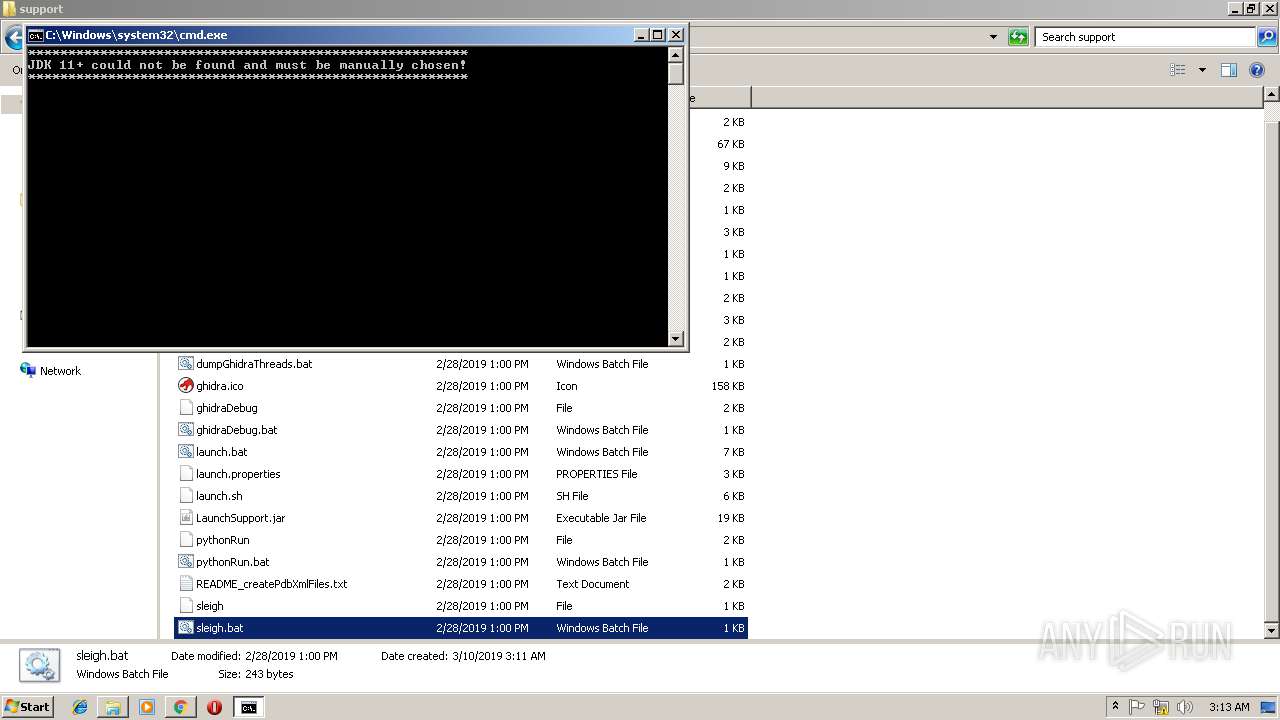
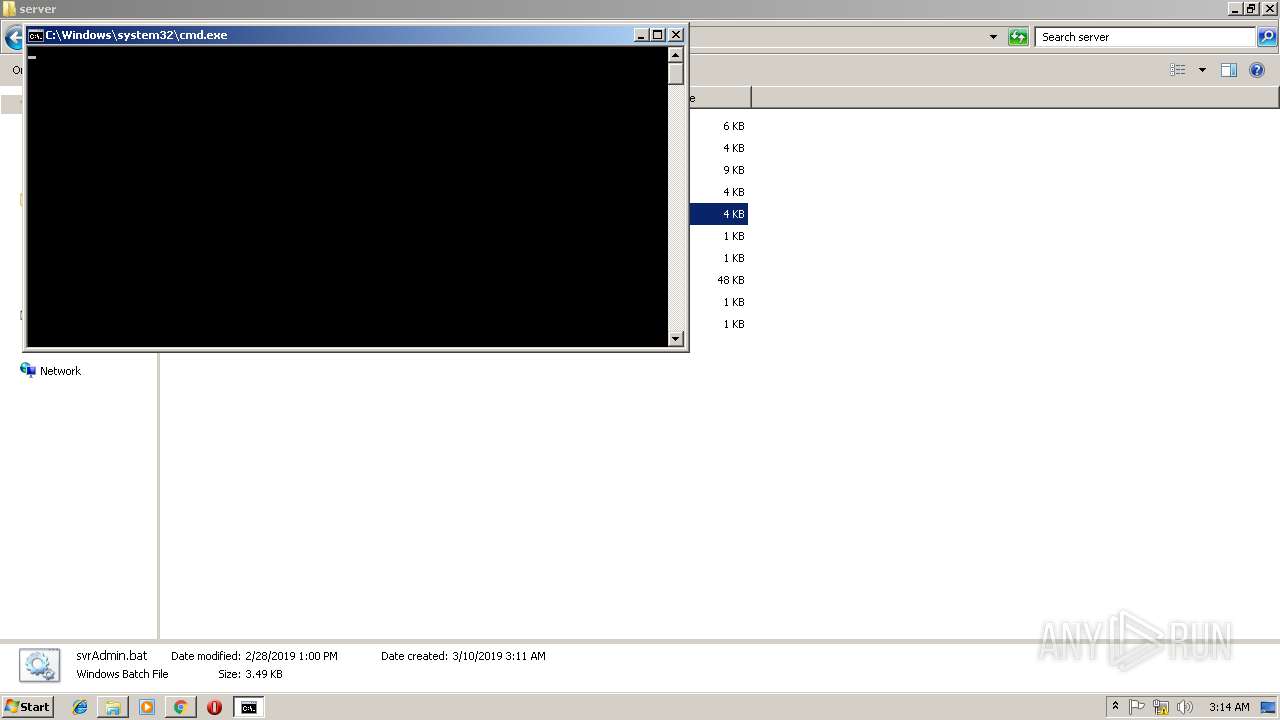
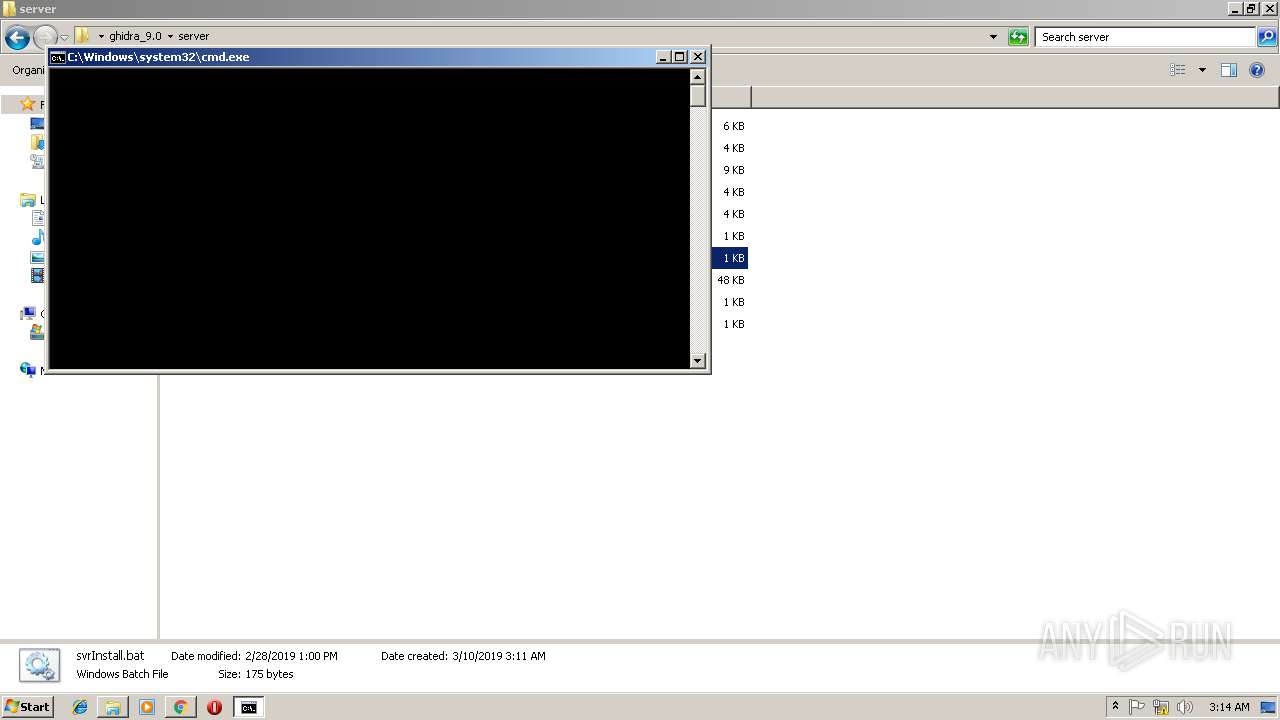
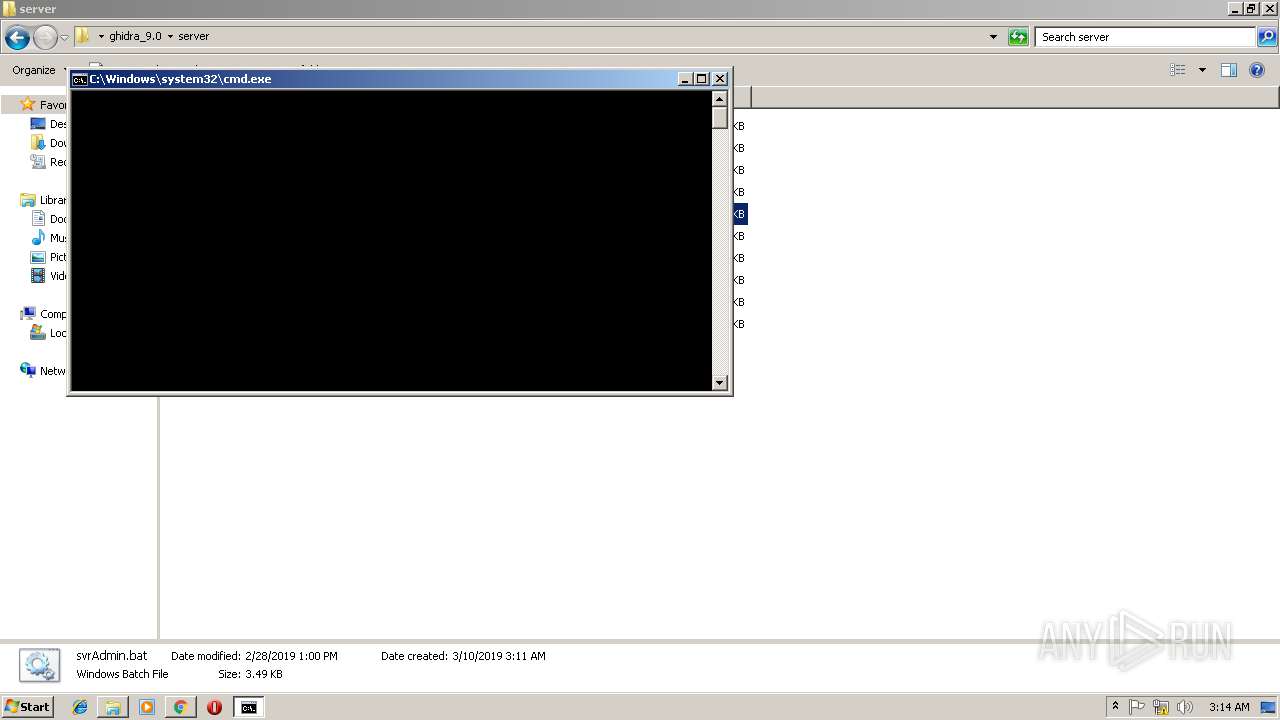
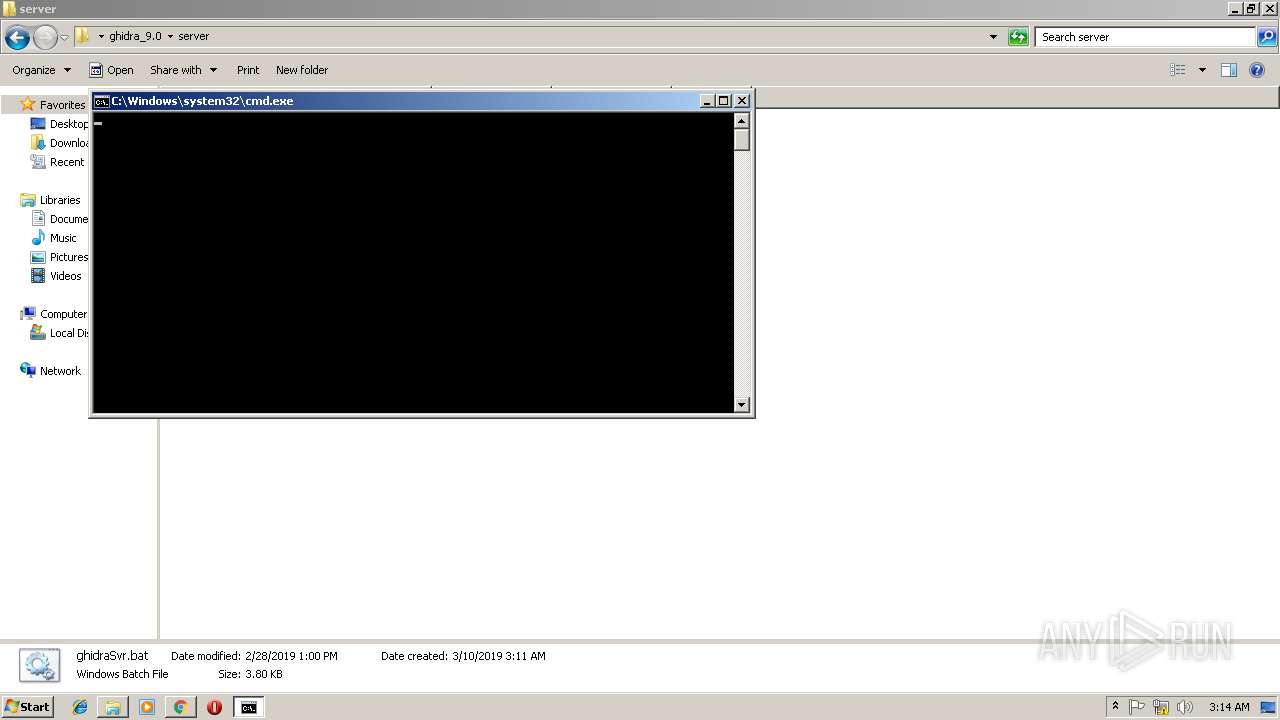
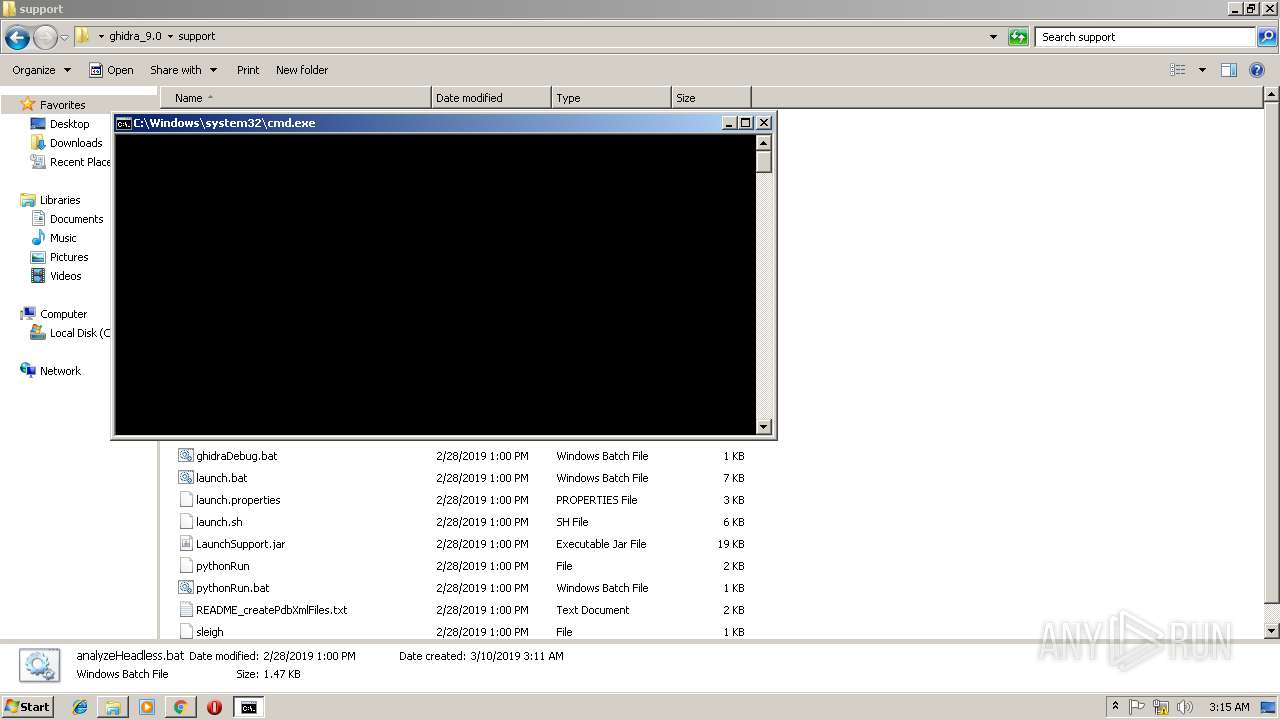
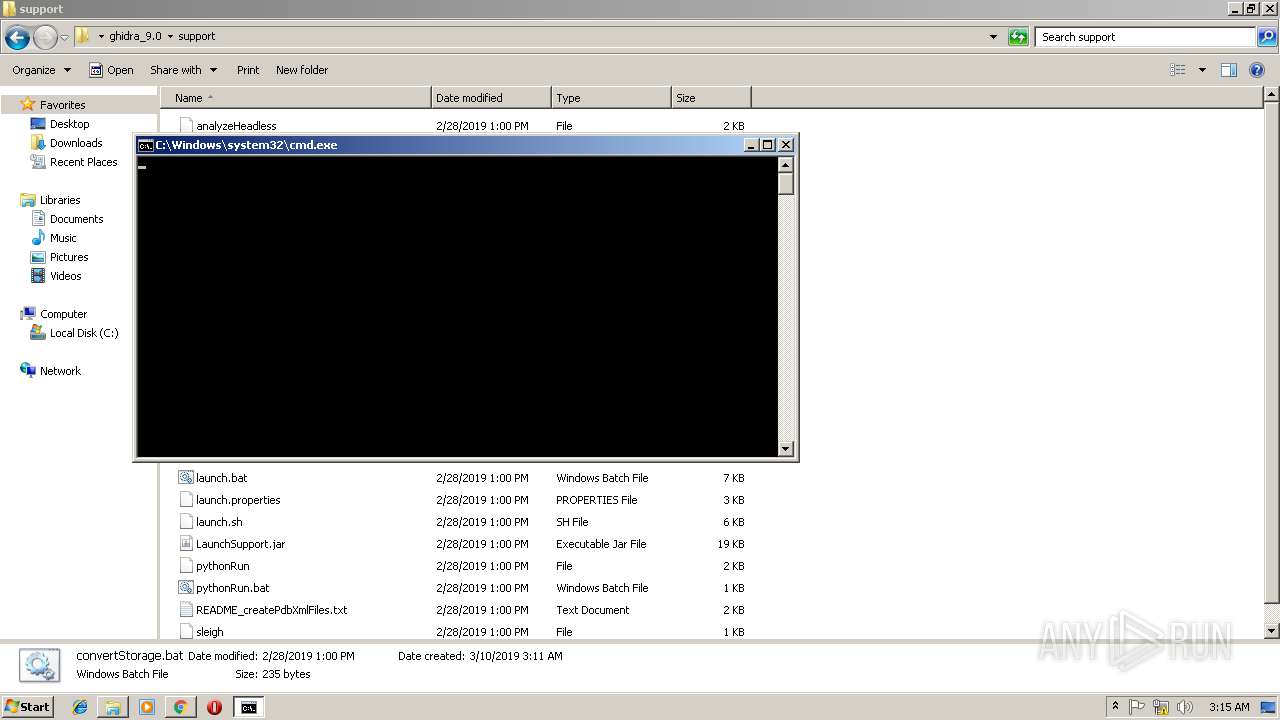
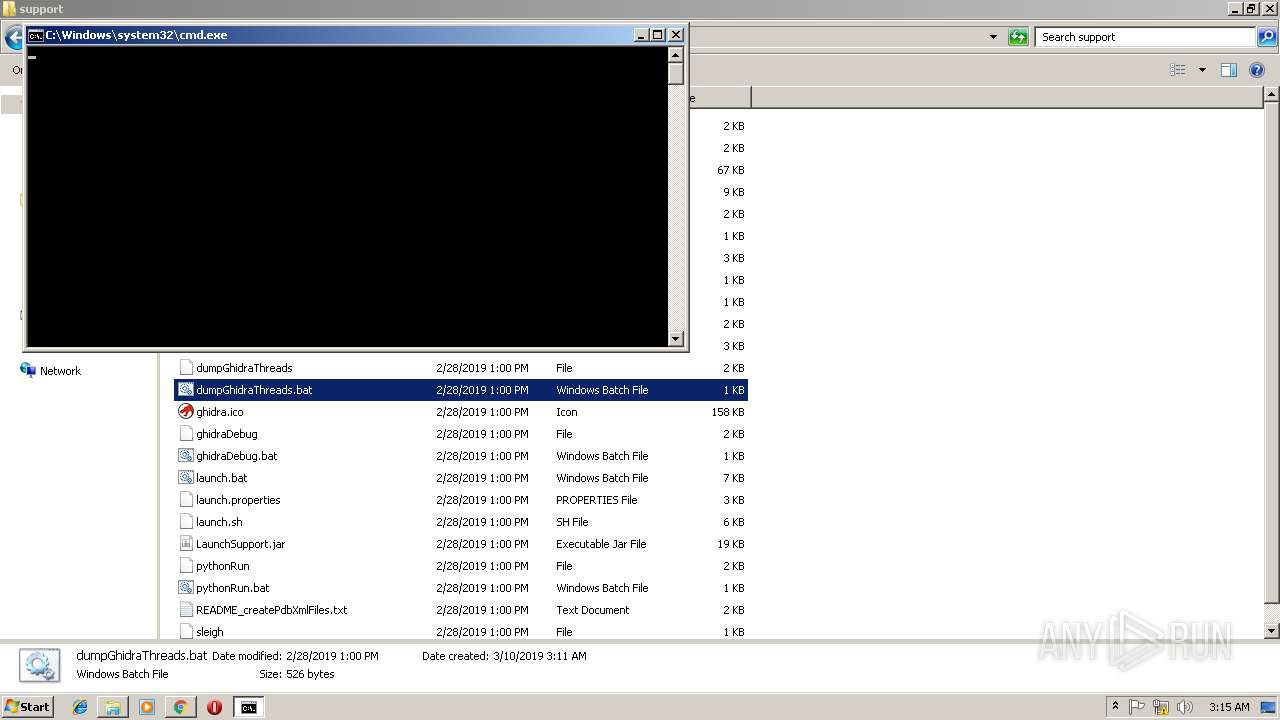
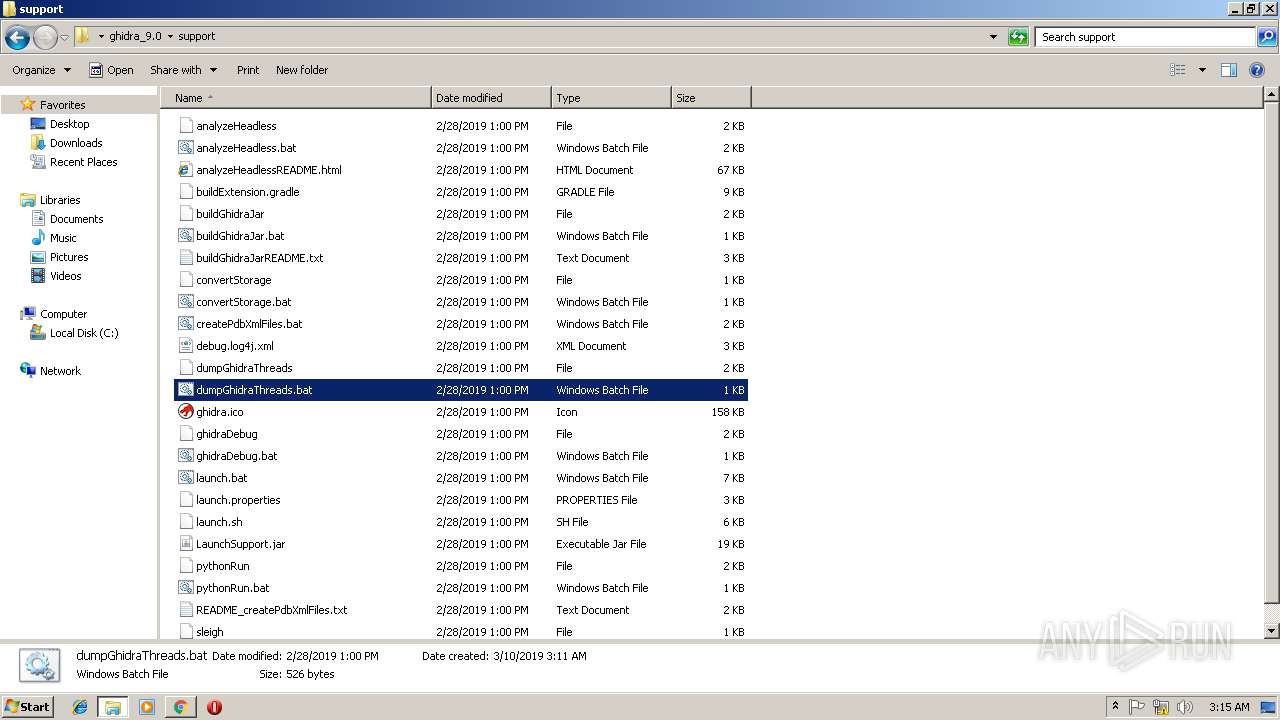
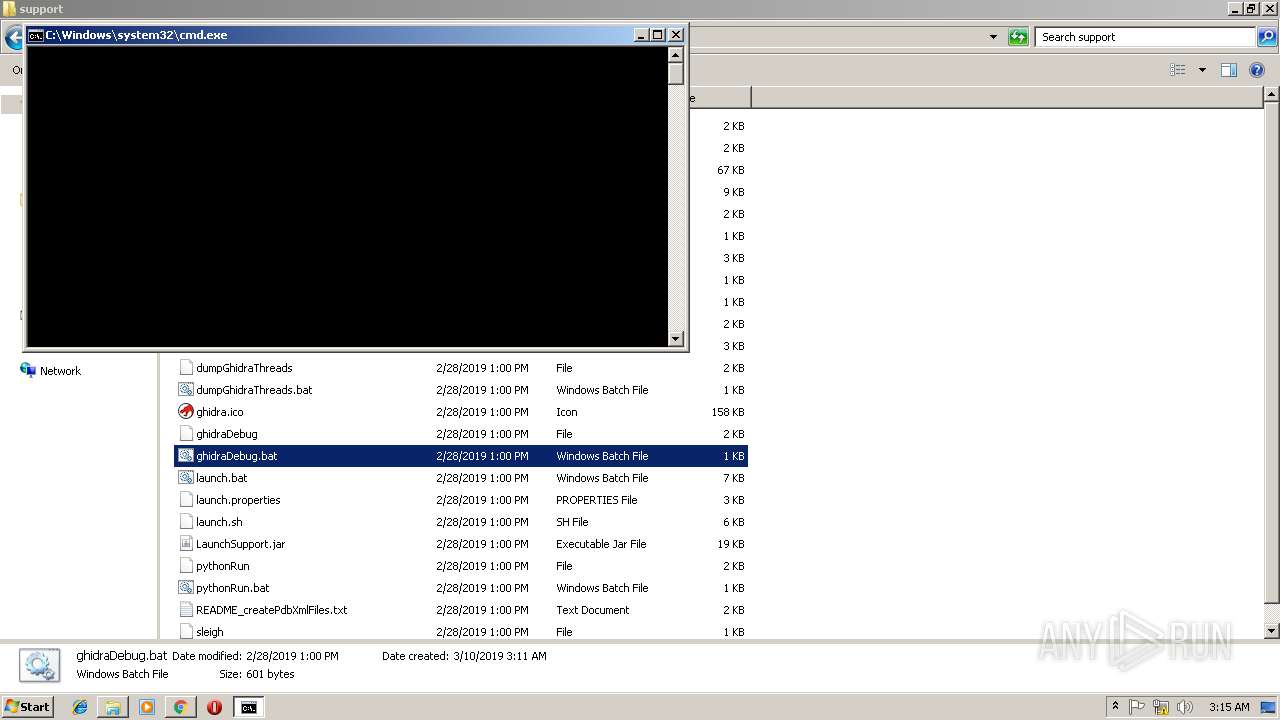
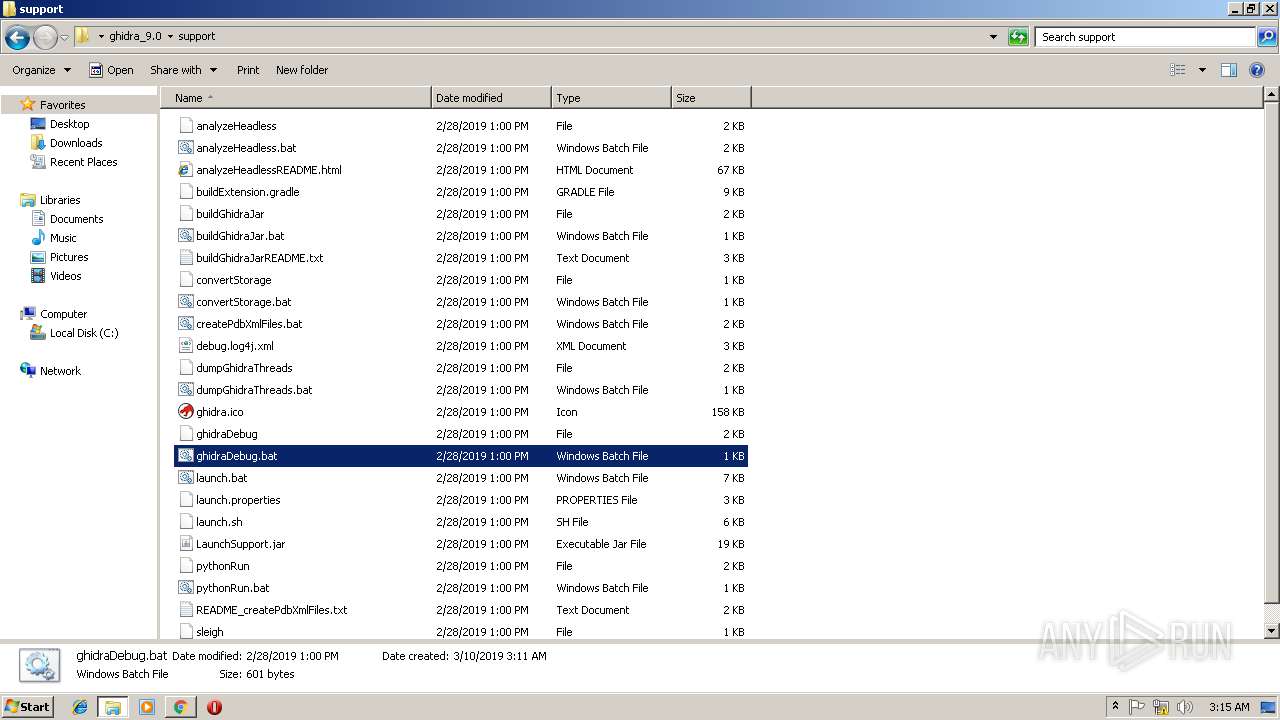
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1476)
- cmd.exe (PID: 3892)
- cmd.exe (PID: 2608)
- cmd.exe (PID: 2356)
- cmd.exe (PID: 2572)
- cmd.exe (PID: 2276)
- cmd.exe (PID: 3096)
- cmd.exe (PID: 3720)
- cmd.exe (PID: 2200)
- cmd.exe (PID: 672)
- cmd.exe (PID: 2156)
Application launched itself
- cmd.exe (PID: 1476)
- cmd.exe (PID: 672)
- cmd.exe (PID: 2356)
- cmd.exe (PID: 2572)
- cmd.exe (PID: 2156)
- cmd.exe (PID: 2608)
- cmd.exe (PID: 2200)
- cmd.exe (PID: 2276)
- cmd.exe (PID: 3096)
- cmd.exe (PID: 3720)
- cmd.exe (PID: 3892)
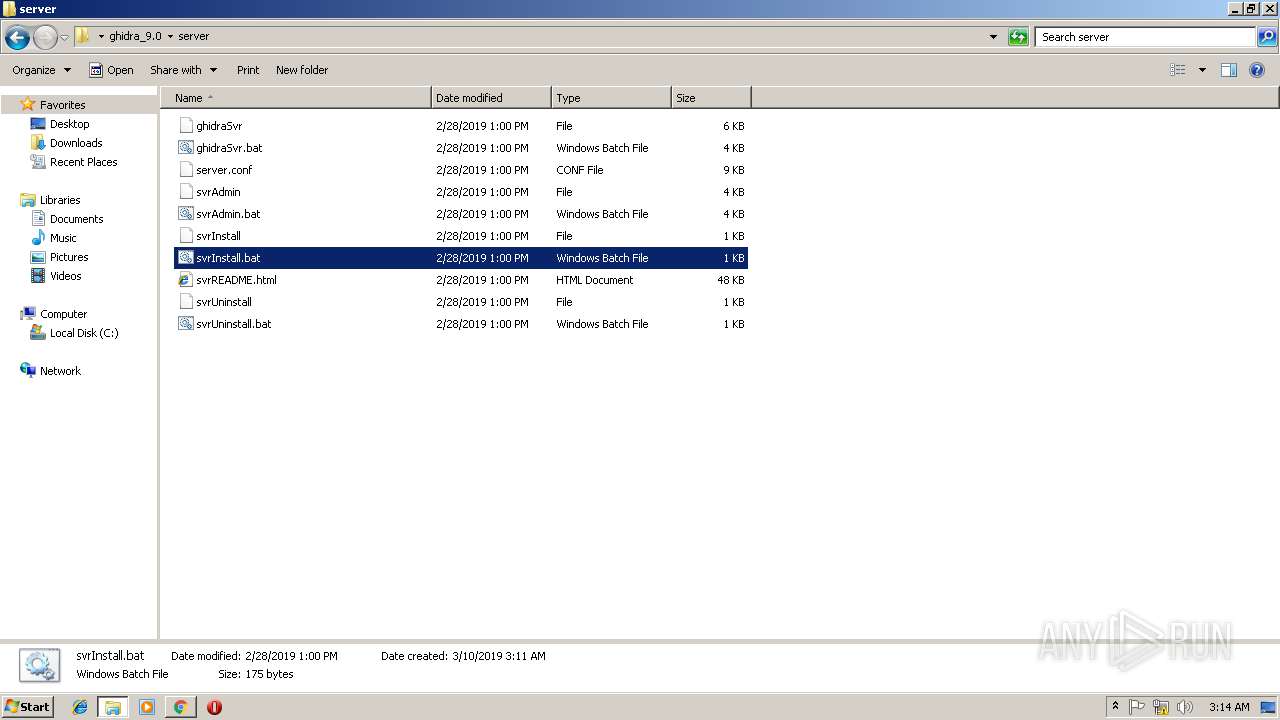
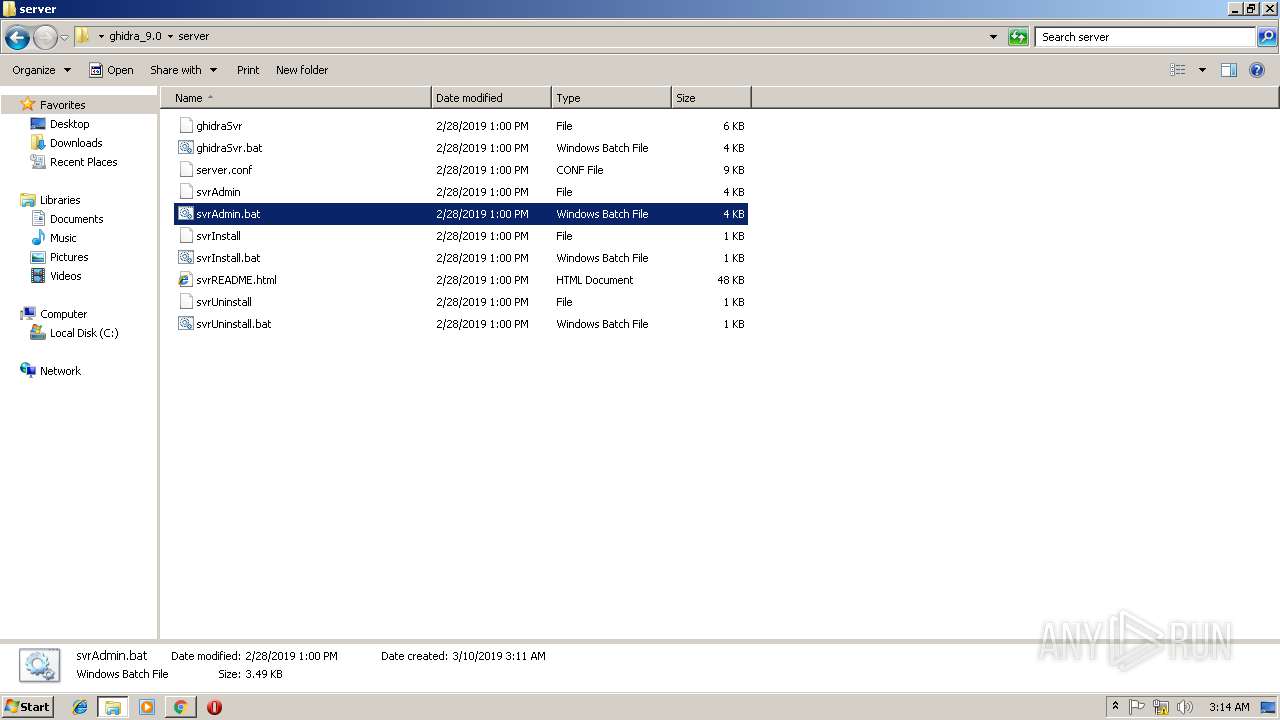
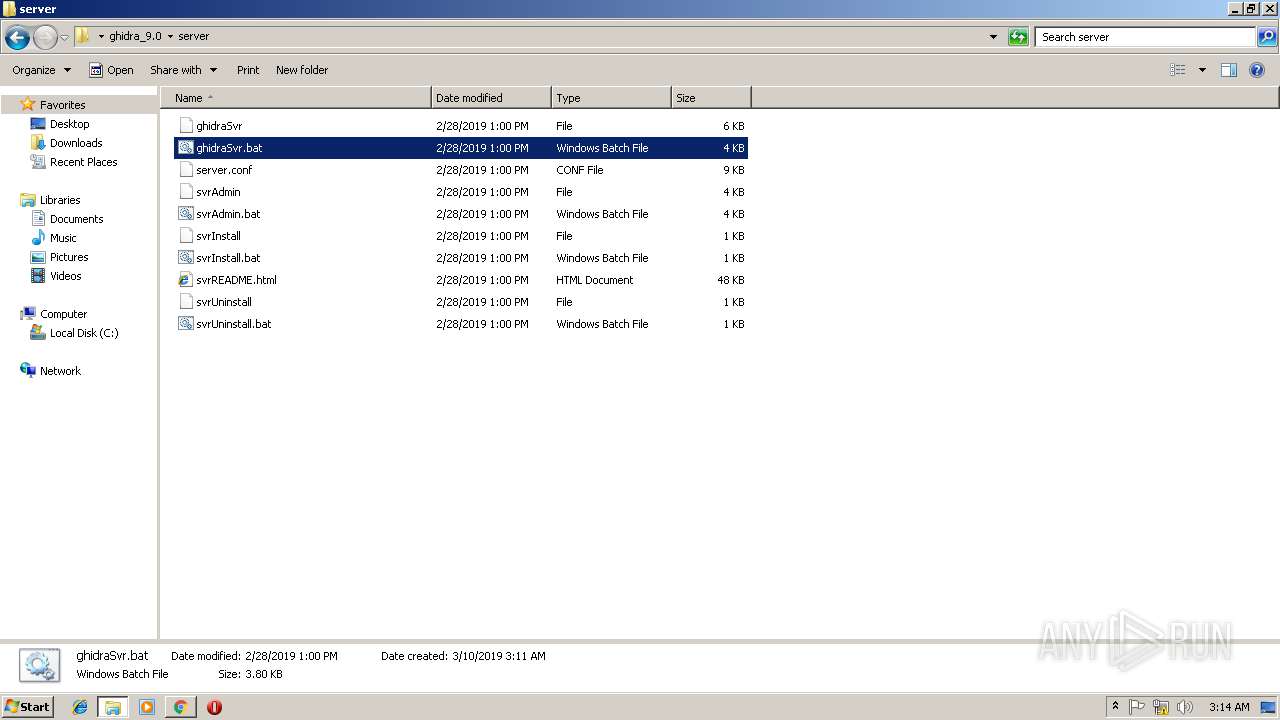
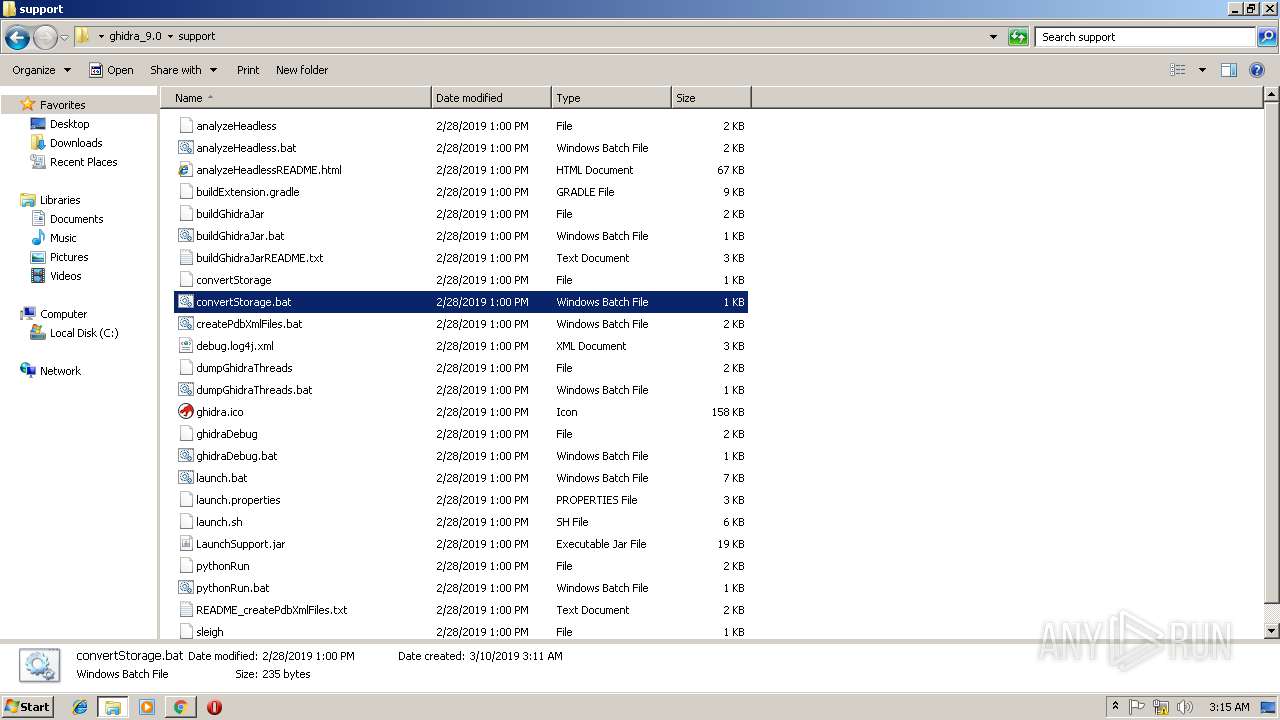
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3220)
Creates files in the user directory
- notepad++.exe (PID: 2152)
Starts itself from another location
- java.exe (PID: 2360)
- java.exe (PID: 3380)
- java.exe (PID: 4056)
- java.exe (PID: 2592)
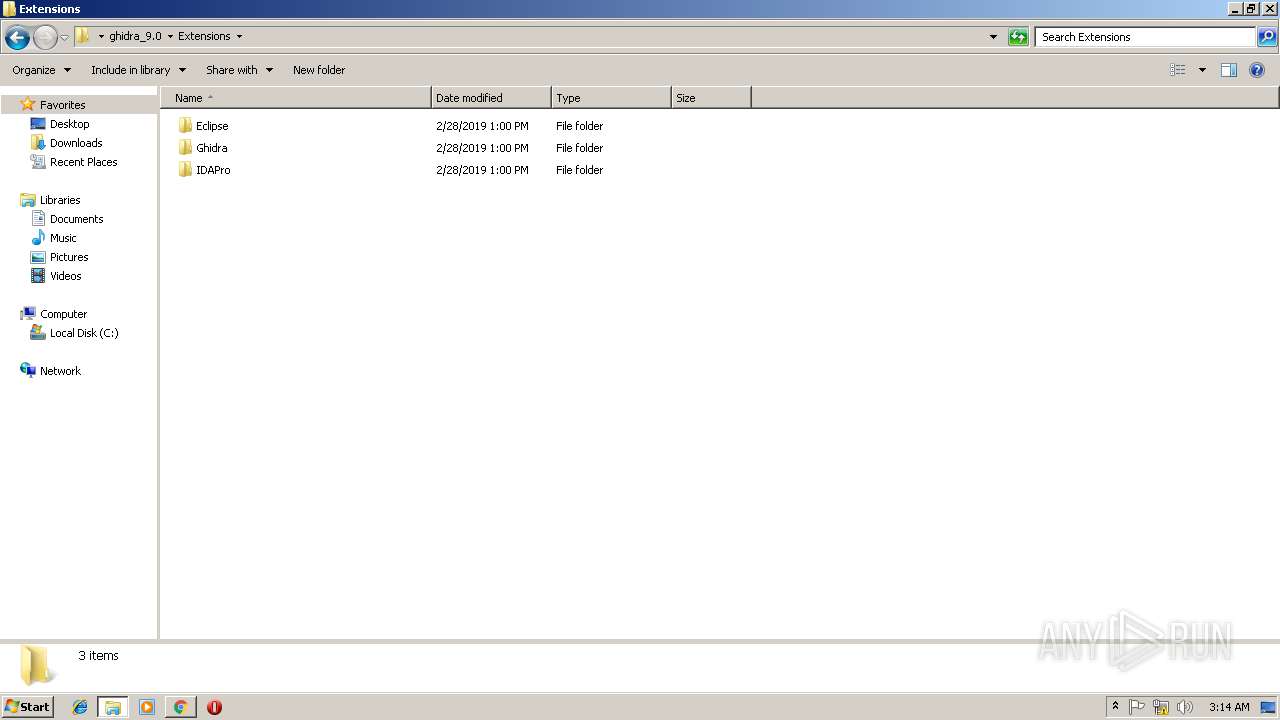
Executes JAVA applets
- java.exe (PID: 4056)
- java.exe (PID: 2592)
- java.exe (PID: 2360)
- java.exe (PID: 3380)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2912)
Application launched itself
- chrome.exe (PID: 2912)
Reads Internet Cache Settings
- chrome.exe (PID: 2912)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
138
Monitored processes
74
Malicious processes
0
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | C:\Windows\system32\cmd.exe /c java -cp "C:\Users\admin\Desktop\ghidra_9.0\support\LaunchSupport.jar" LaunchSupport "C:\Users\admin\Desktop\ghidra_9.0\support\..\\" -jdk_home -save | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 588 | java -version | C:\ProgramData\Oracle\Java\javapath\java.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 656 | C:\Windows\system32\cmd.exe /c java -cp "C:\Users\admin\Desktop\ghidra_9.0\support\LaunchSupport.jar" LaunchSupport "C:\Users\admin\Desktop\ghidra_9.0\support\..\\" -jdk_home -save | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
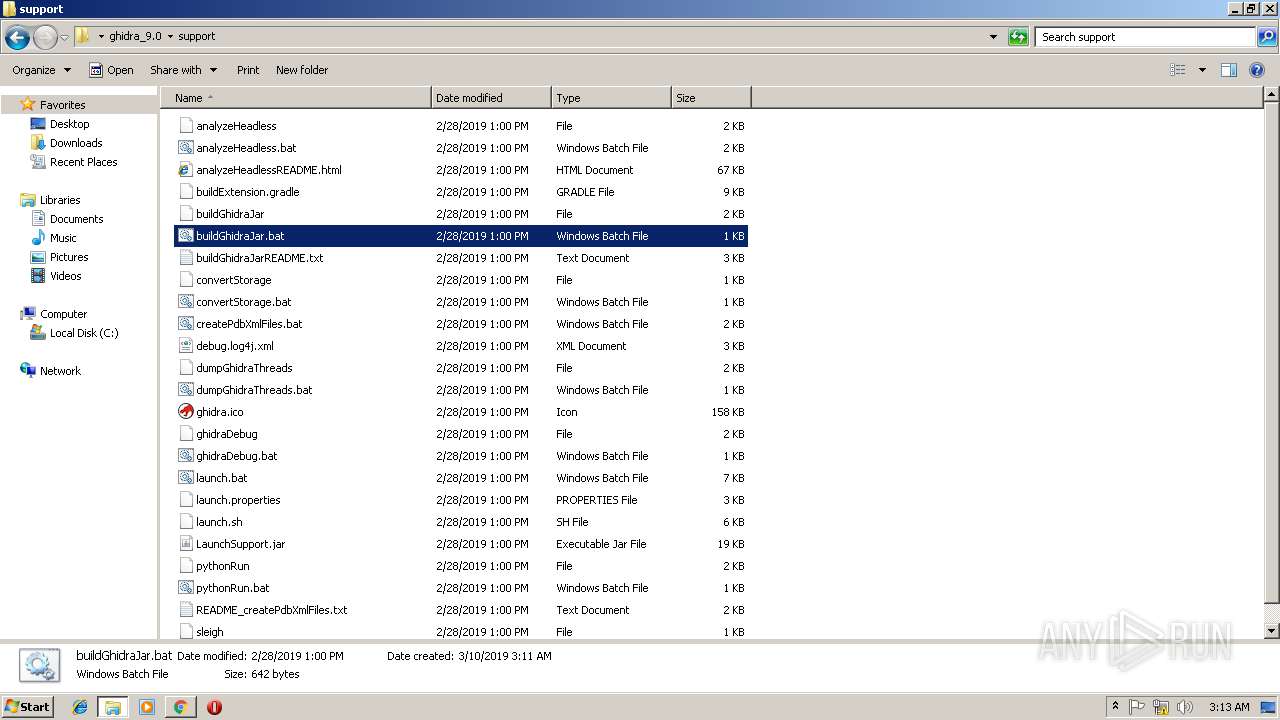
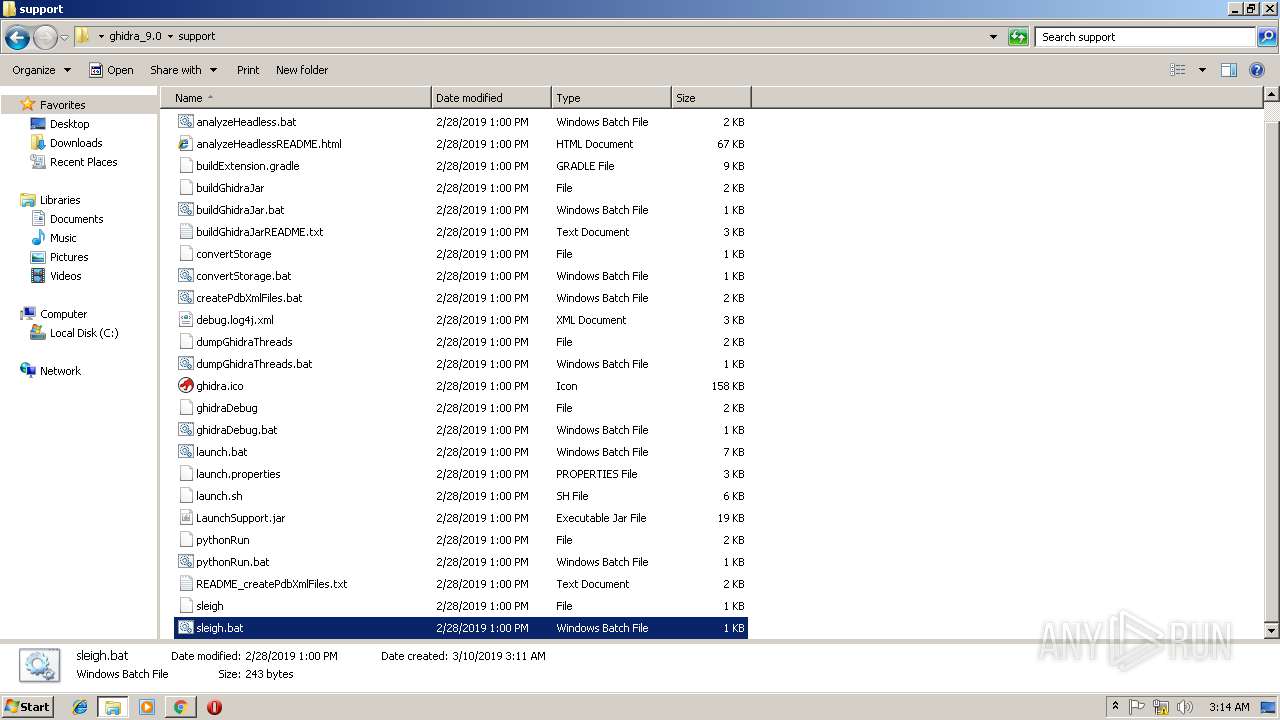
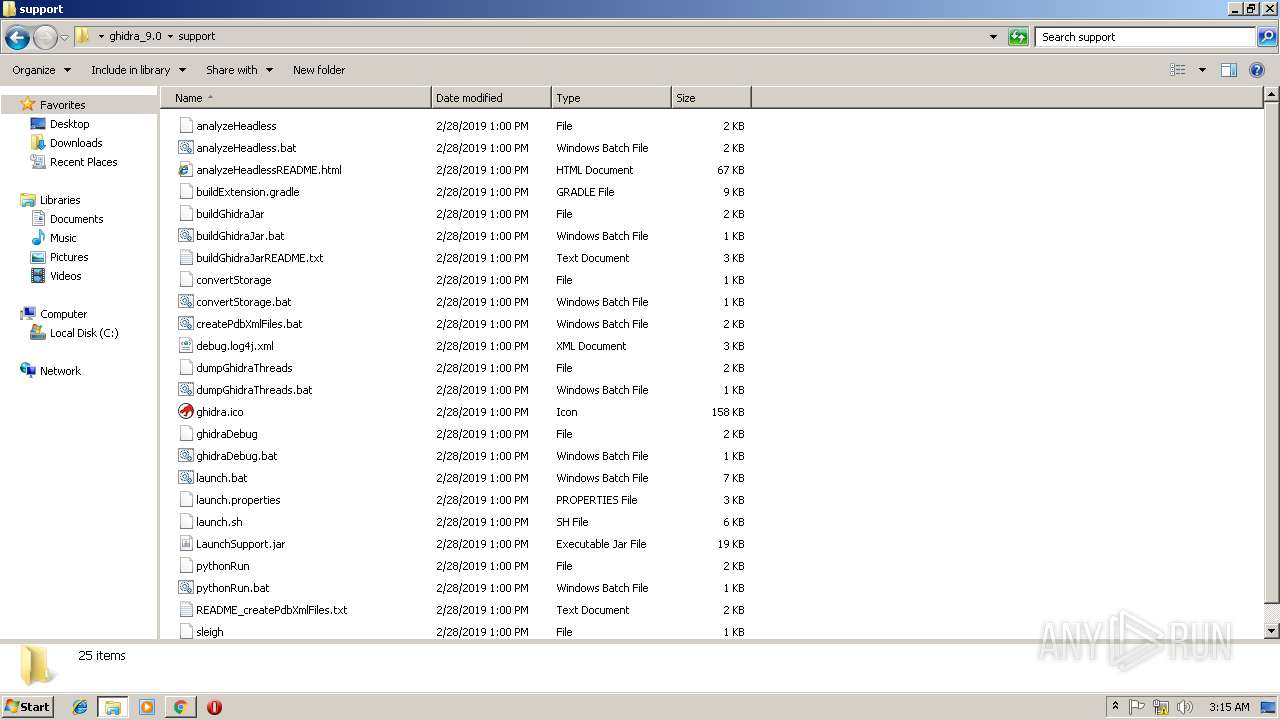
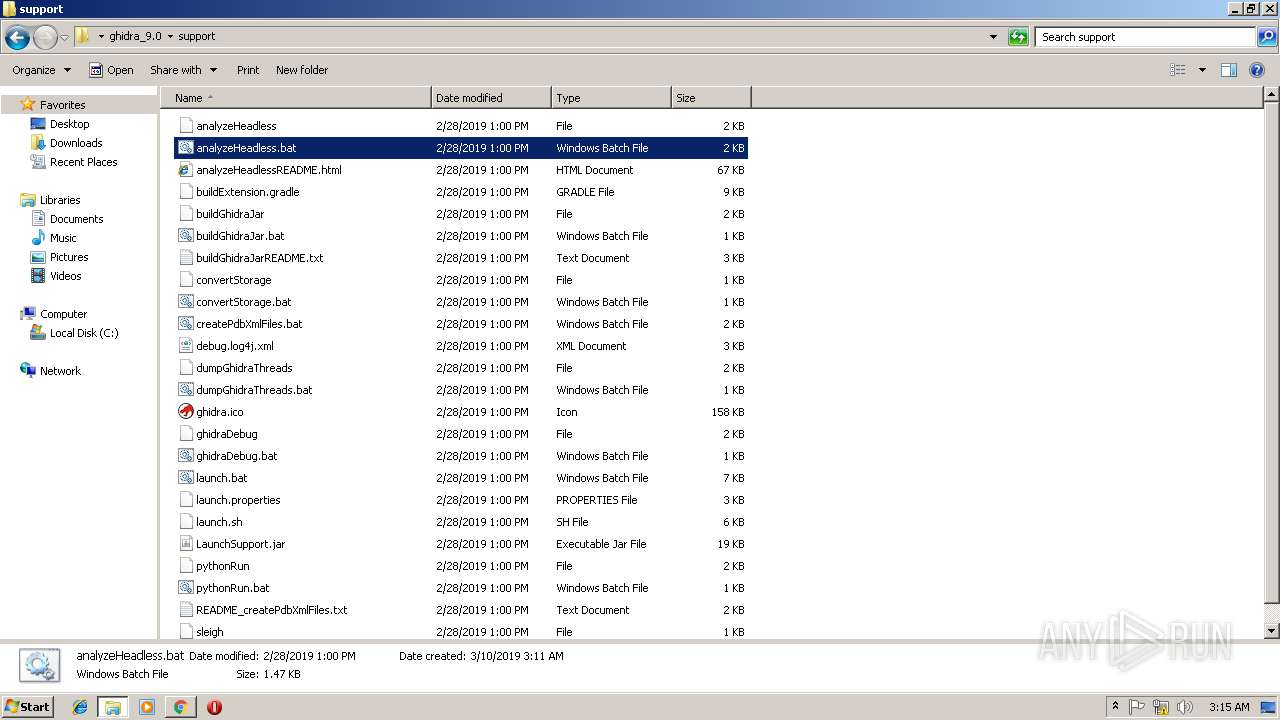
| 672 | cmd /c ""C:\Users\admin\Desktop\ghidra_9.0\support\sleigh.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225547 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=916,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D24AAD625AB16B6FA0E38663173B429A --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
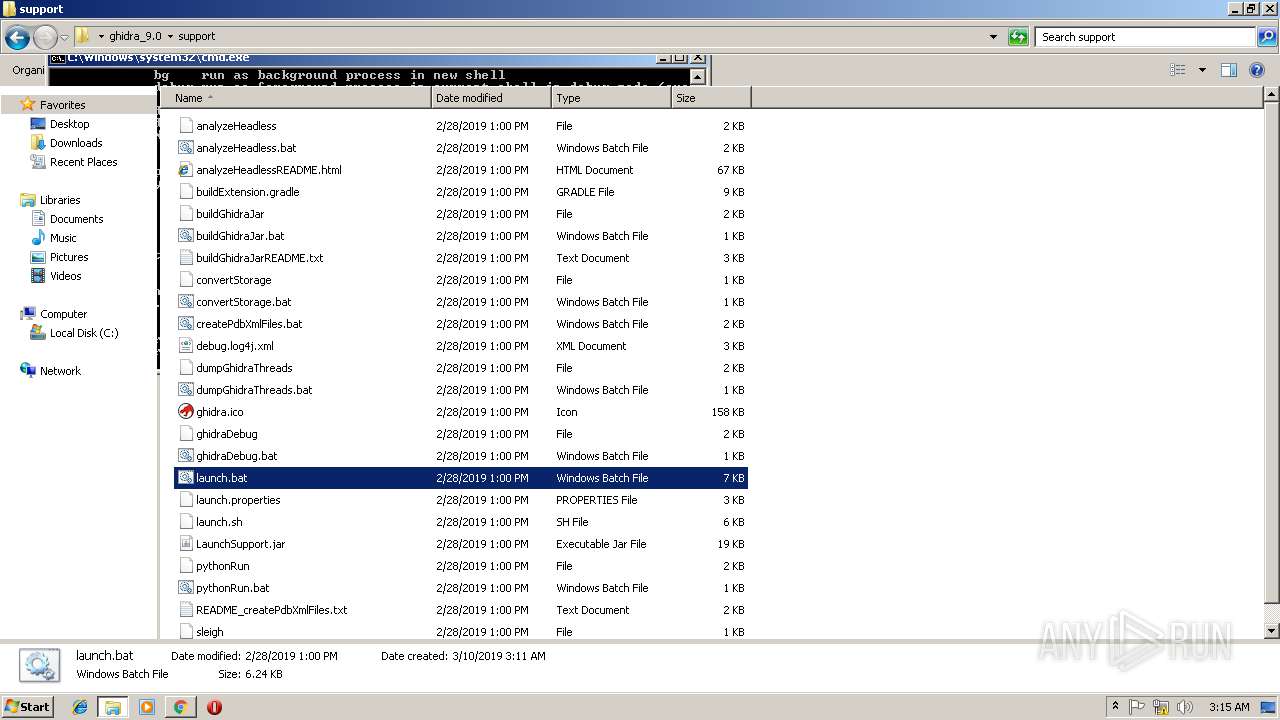
| 1164 | cmd /c ""C:\Users\admin\Desktop\ghidra_9.0\support\launch.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
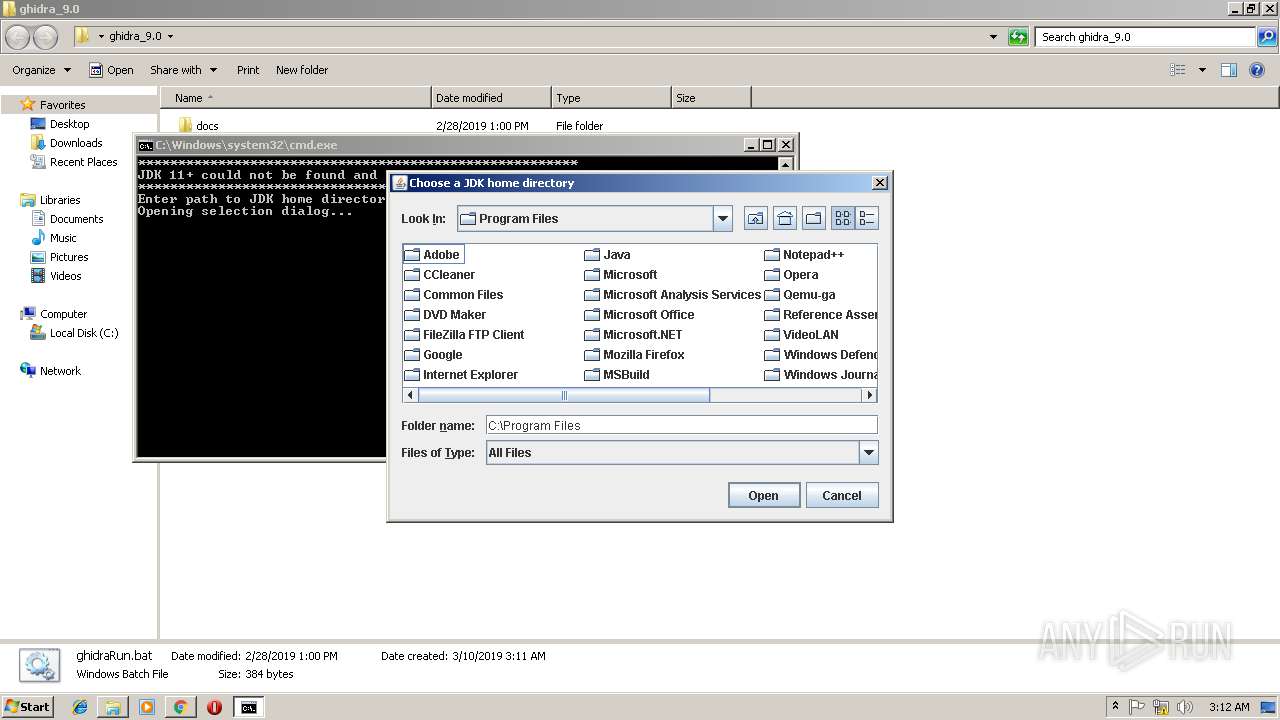
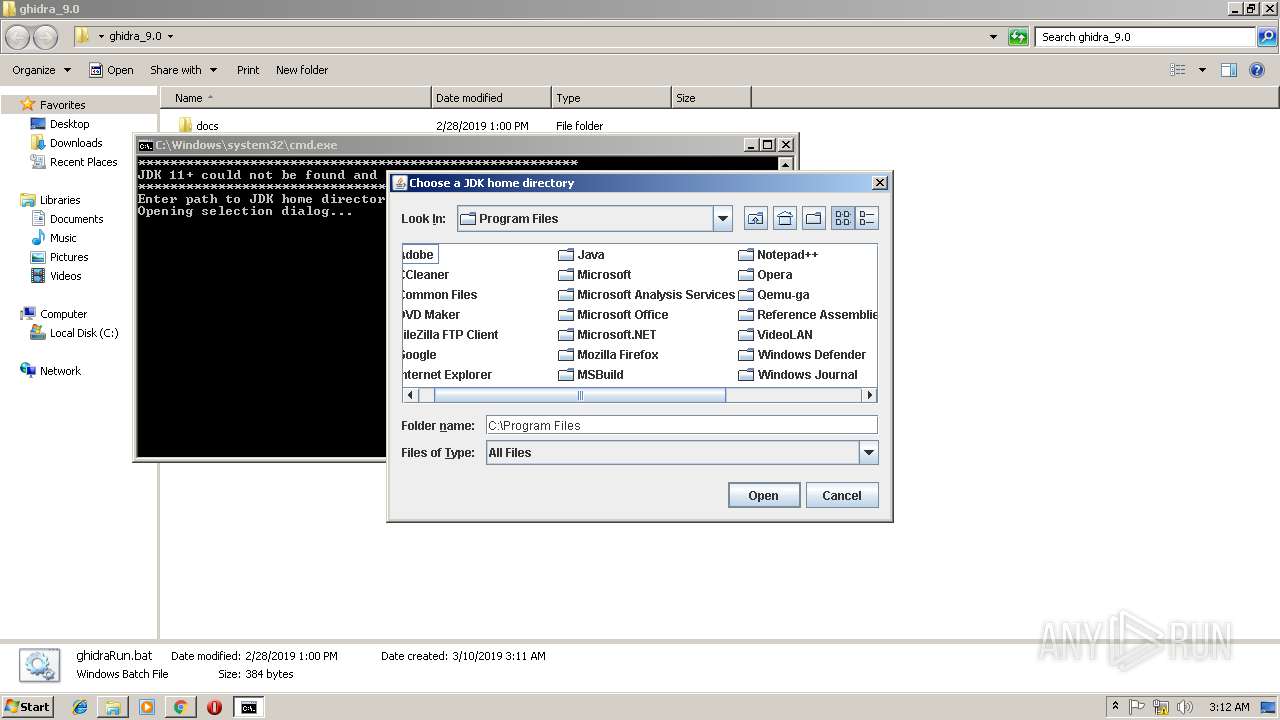
| 1228 | java -cp "C:\Users\admin\Desktop\ghidra_9.0\support\LaunchSupport.jar" LaunchSupport "C:\Users\admin\Desktop\ghidra_9.0\support\..\\" -jdk_home -ask | C:\ProgramData\Oracle\Java\javapath\java.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 3221225786 Version: 8.0.920.14 Modules
| |||||||||||||||
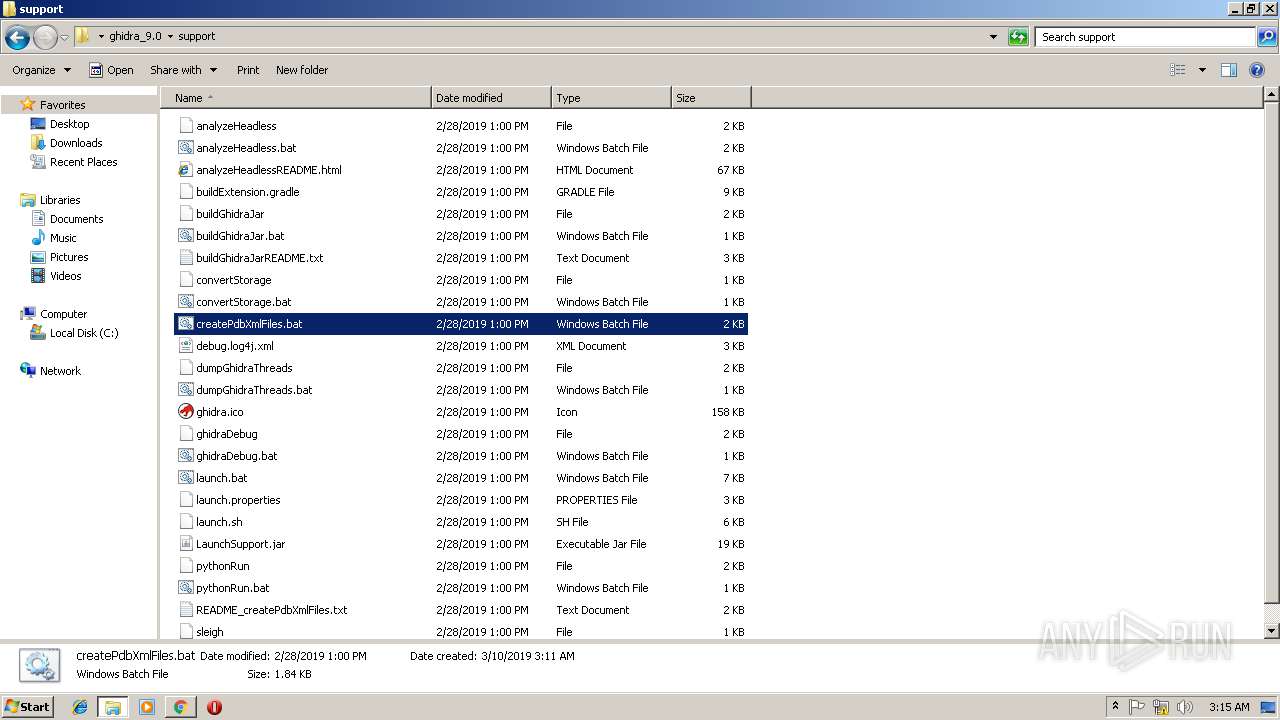
| 1420 | cmd /c ""C:\Users\admin\Desktop\ghidra_9.0\support\createPdbXmlFiles.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
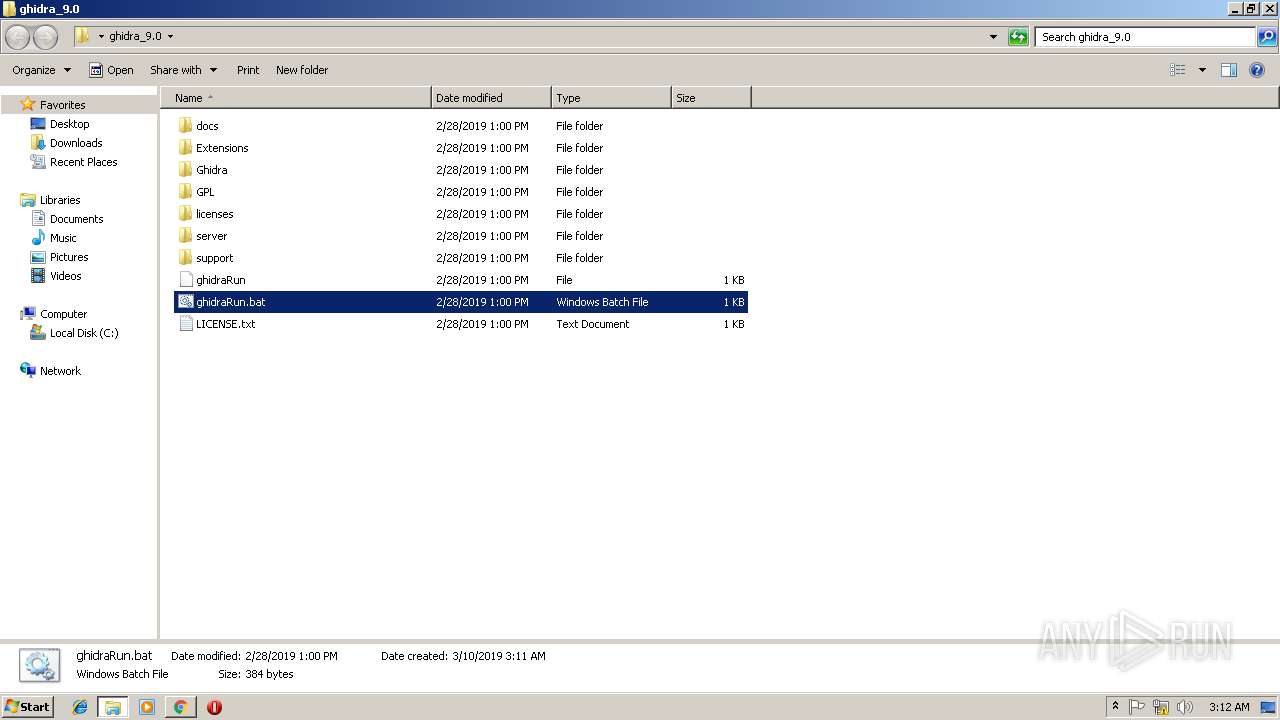
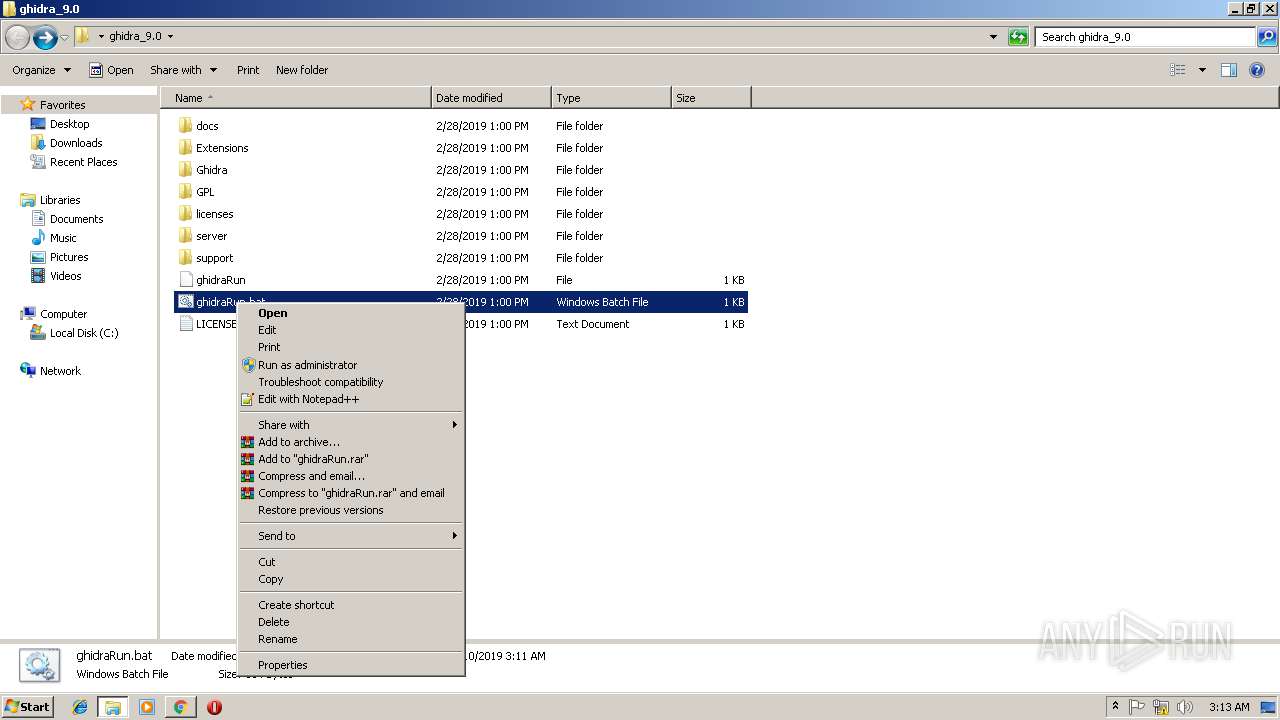
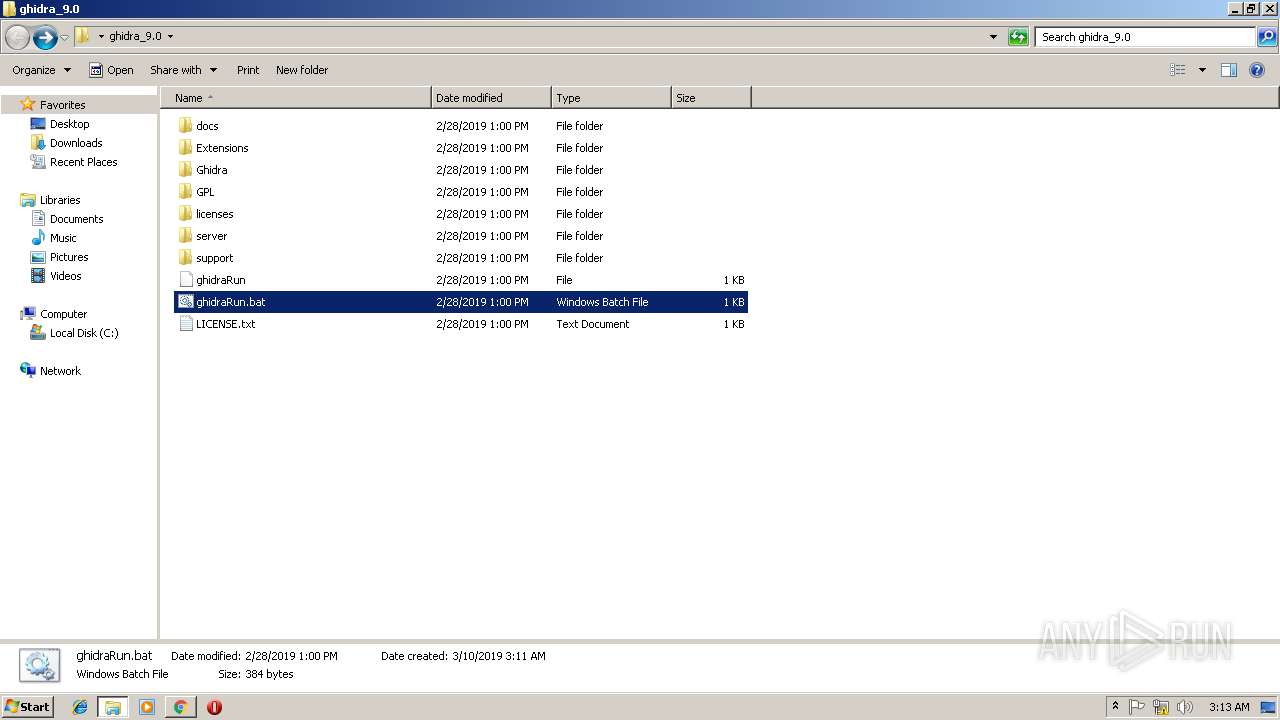
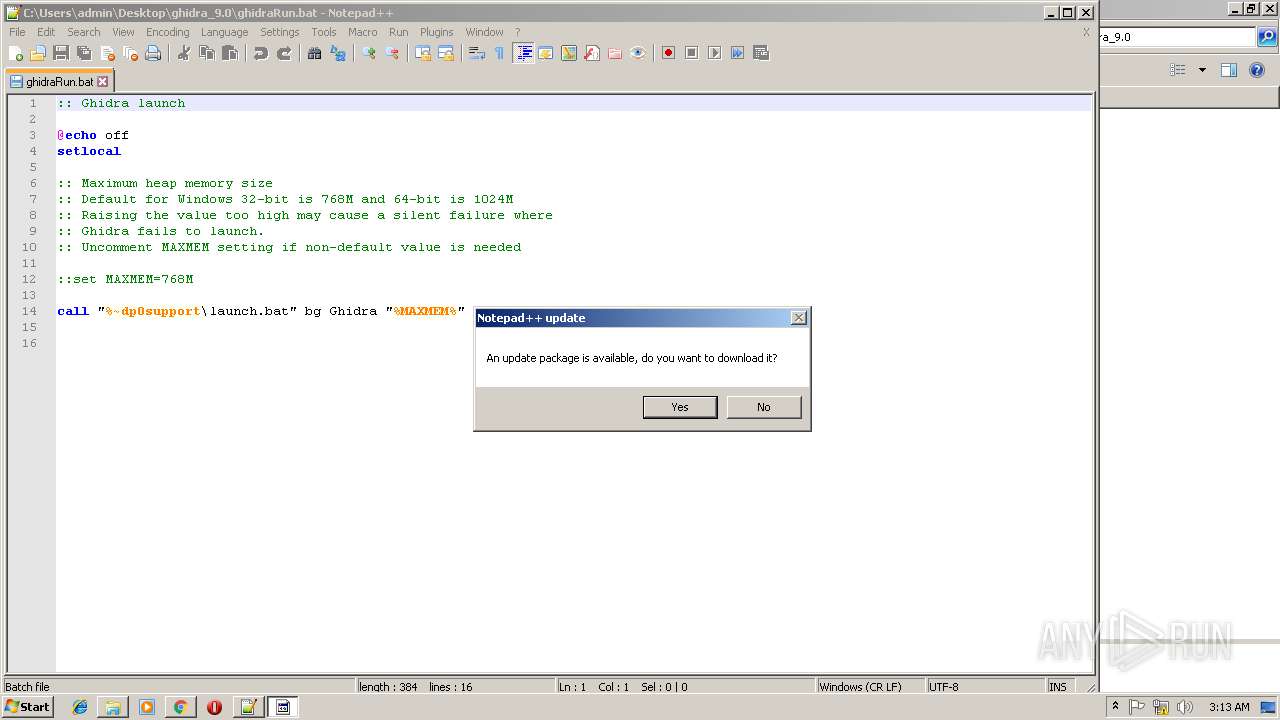
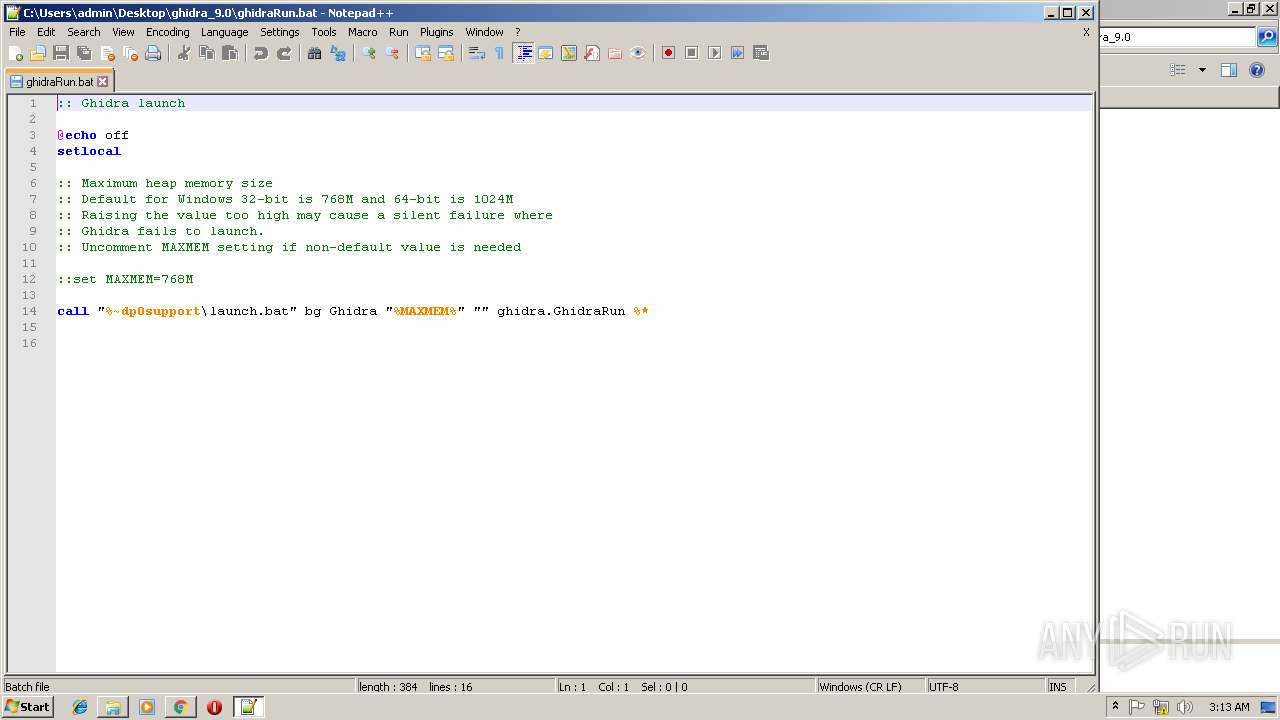
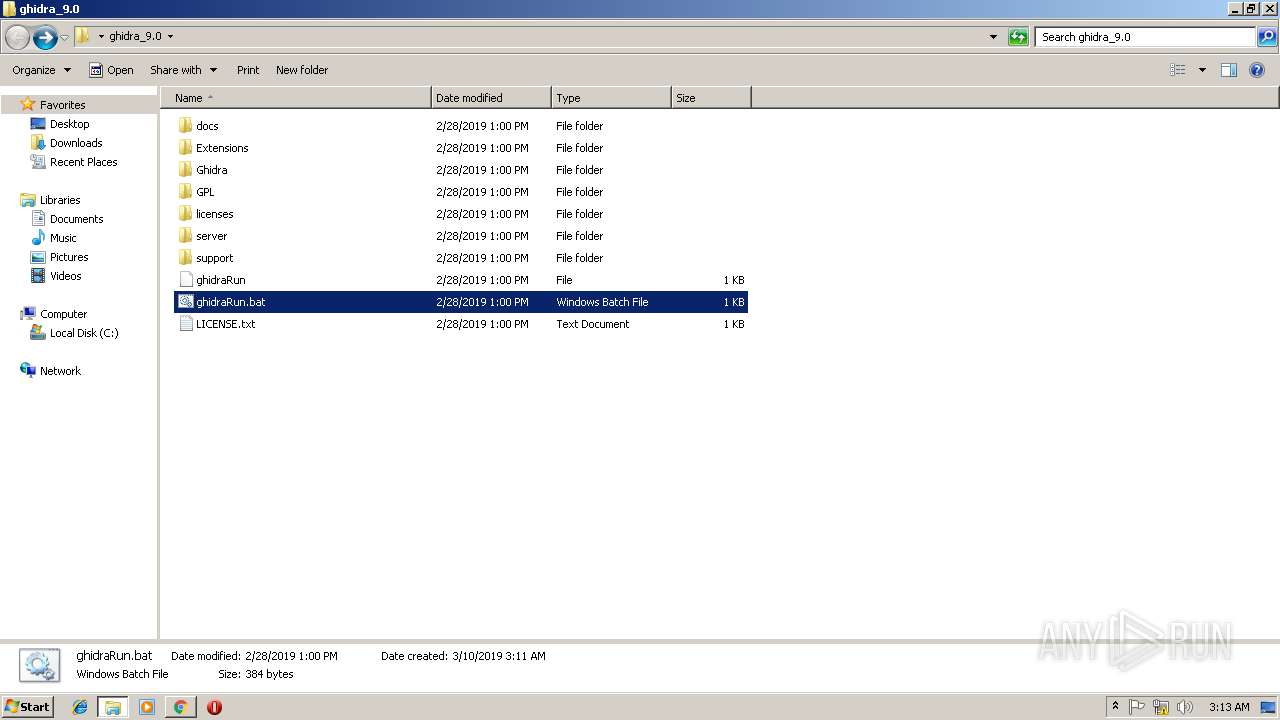
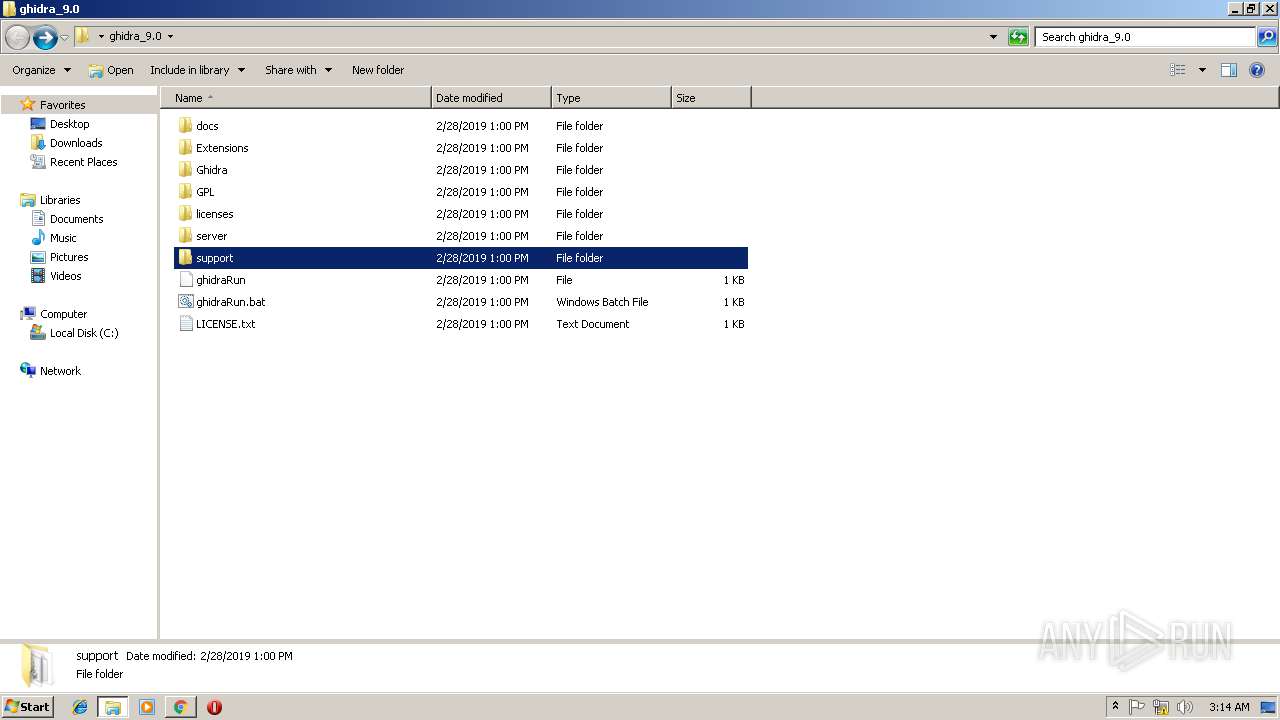
| 1476 | cmd /c ""C:\Users\admin\Desktop\ghidra_9.0\ghidraRun.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -version | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | java.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
1 620
Read events
1 523
Write events
94
Delete events
3
Modification events
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2912-13196661046160500 |
Value: 259 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2912-13196661046160500 |
Value: 259 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
50
Suspicious files
198
Text files
2 017
Unknown types
680
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\57f8607c-6b65-4267-9392-245602fcb6dd.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF199be8.TMP | text | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Temp\Cab9FC0.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Temp\Tar9FC1.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Temp\Cab9FF1.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Temp\Tar9FF2.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
13
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2912 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
2912 | chrome.exe | GET | 200 | 54.230.199.28:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2912 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2912 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2912 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2912 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2912 | chrome.exe | 54.230.199.28:80 | x.ss2.us | Amazon.com, Inc. | US | unknown |
2912 | chrome.exe | 172.217.16.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
2912 | chrome.exe | 216.58.205.238:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3728 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
— | — | 2.16.106.50:80 | ocsp.usertrust.com | Akamai International B.V. | — | whitelisted |
2912 | chrome.exe | 54.239.164.243:443 | ghidra-sre.org | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ghidra-sre.org |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
clients1.google.com |
| whitelisted |
notepad-plus-plus.org |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|