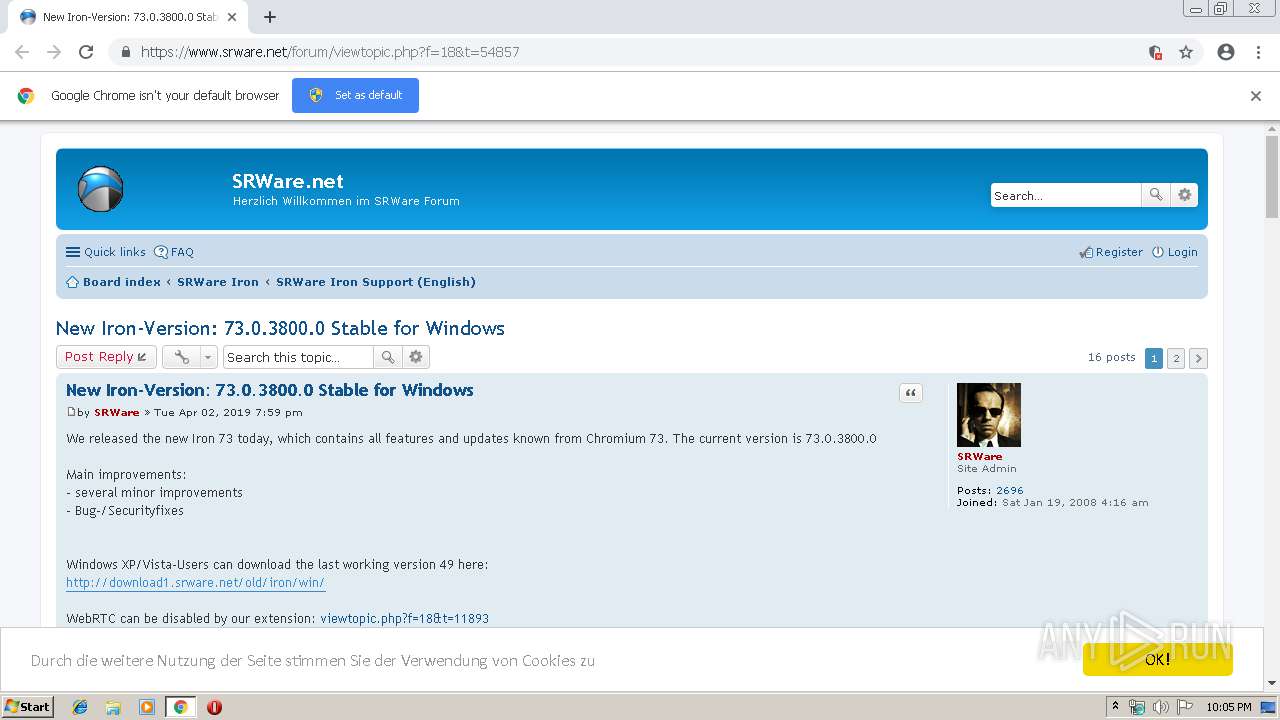
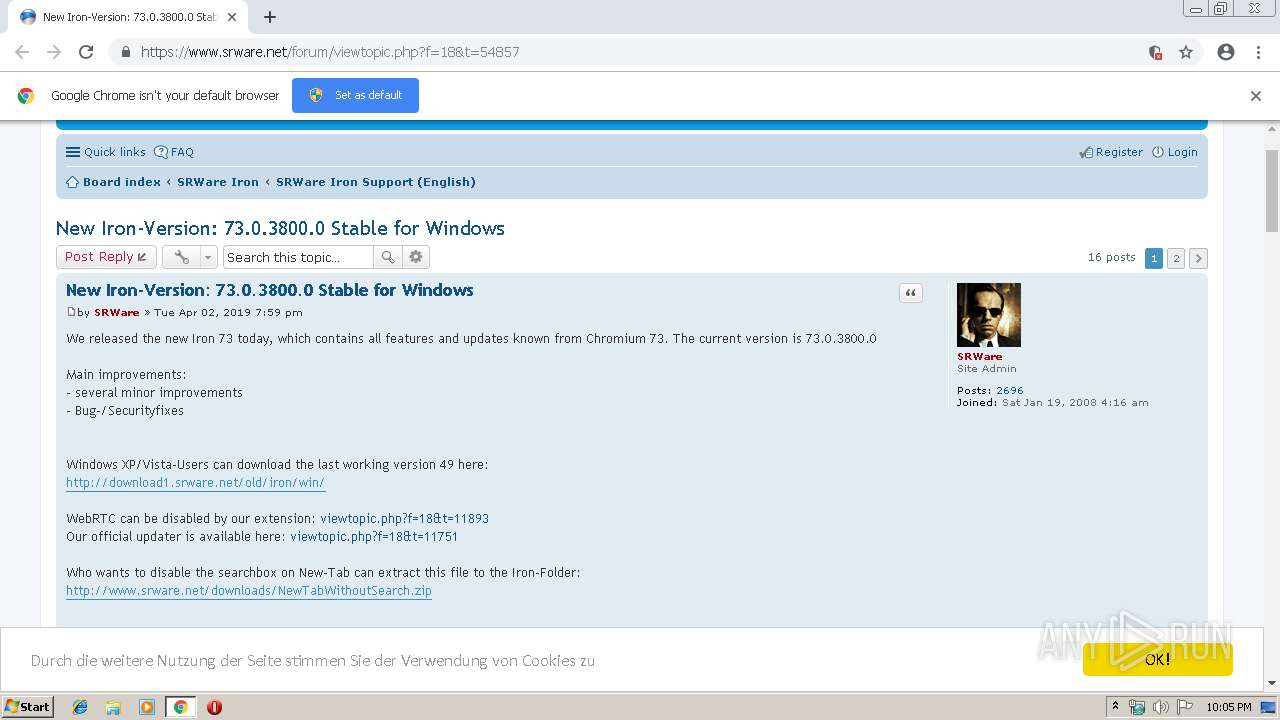
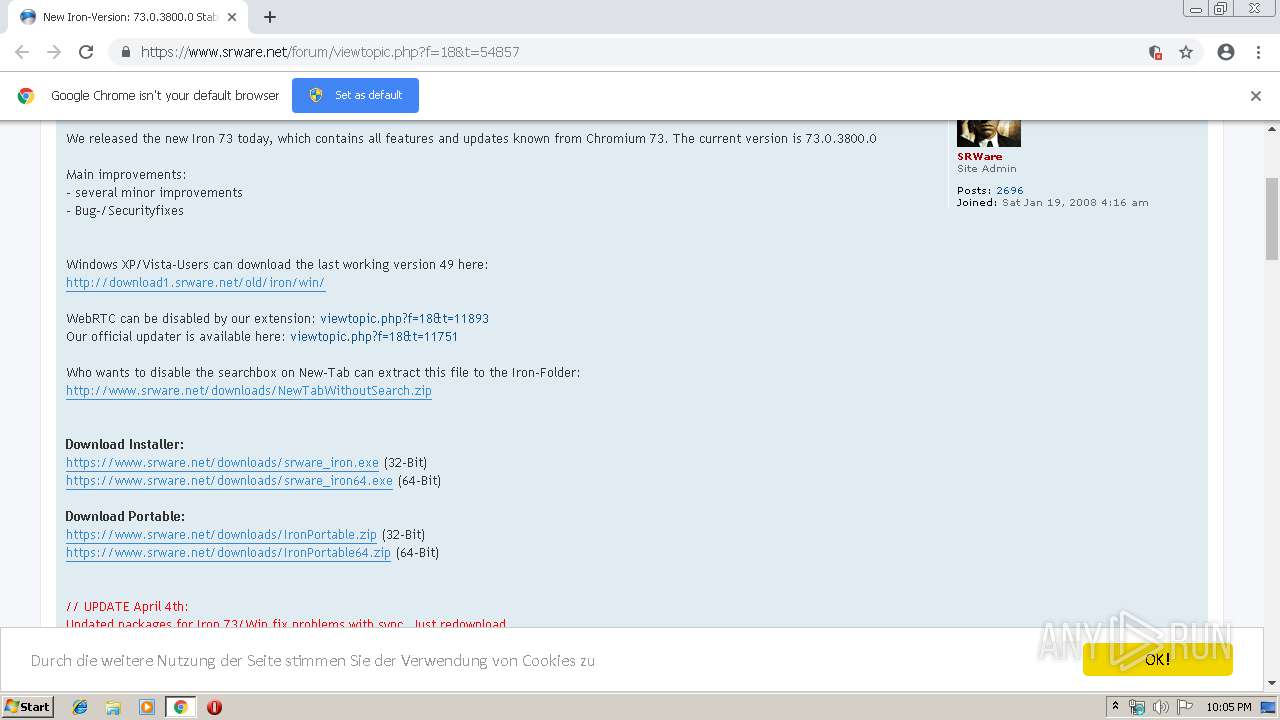
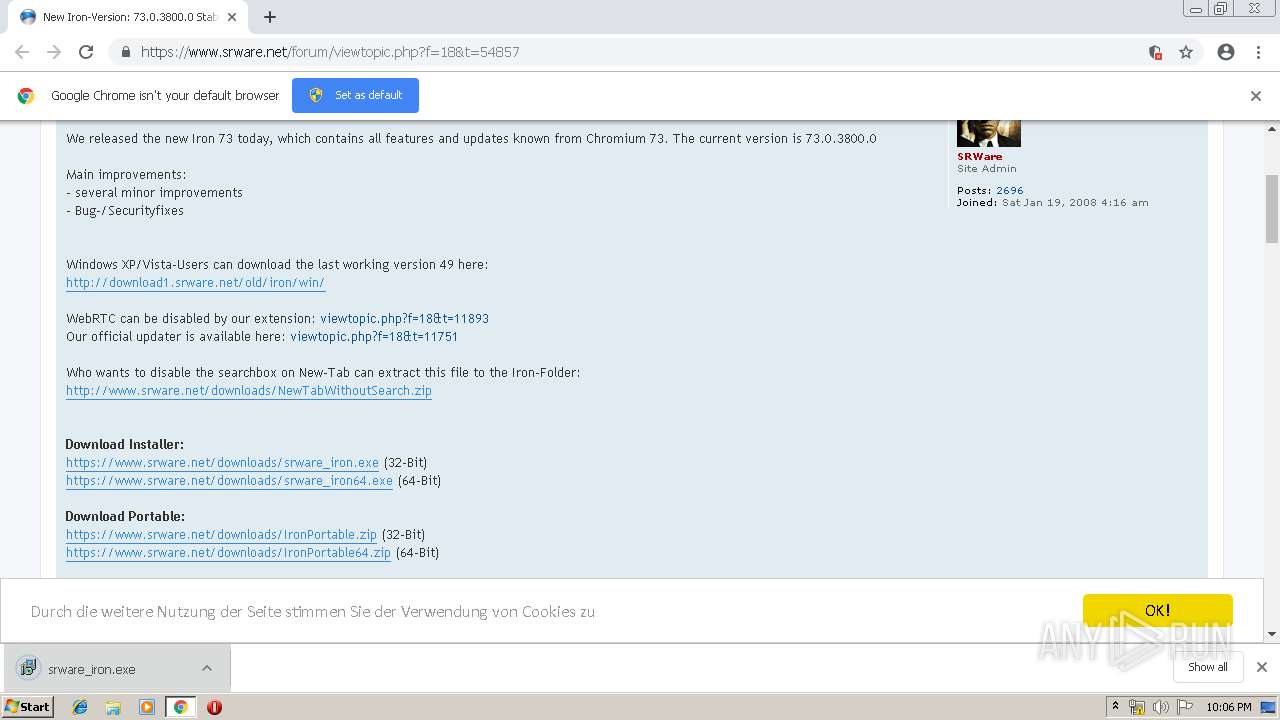
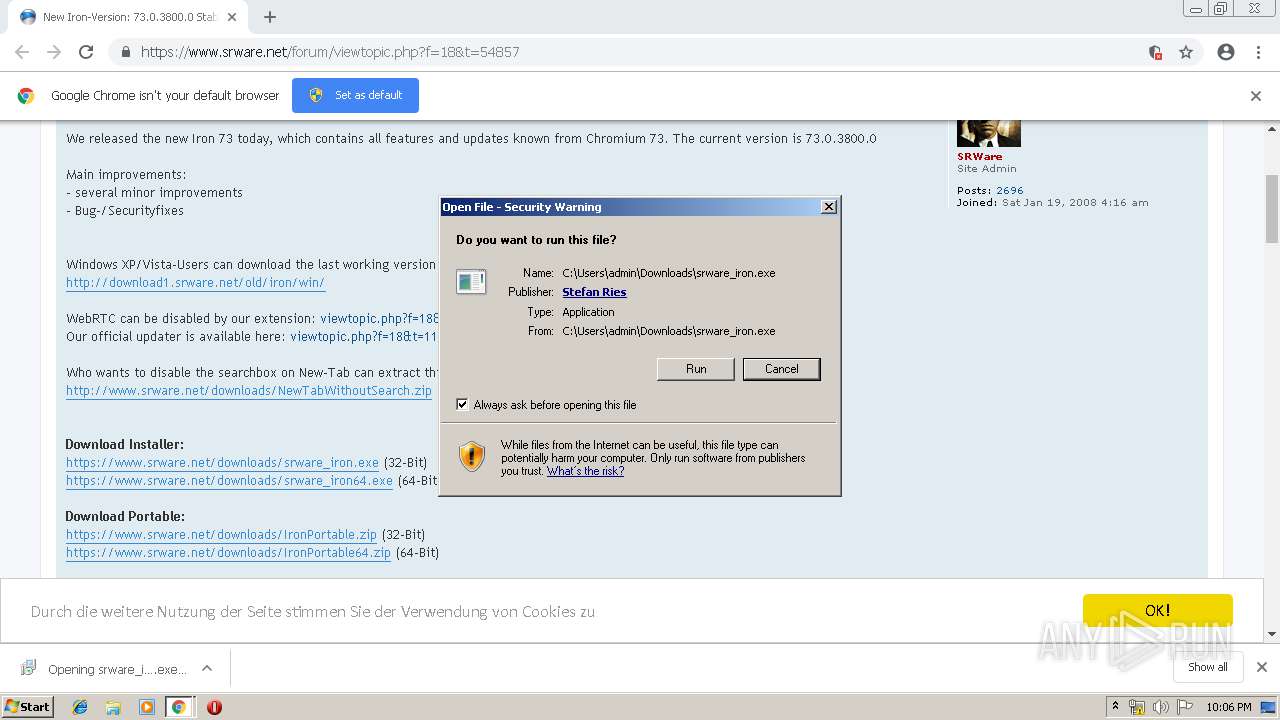
| URL: | https://www.srware.net/forum/viewtopic.php?f=18&t=54857 |
| Full analysis: | https://app.any.run/tasks/76f305a3-fbe8-4498-bbb6-53bed967254f |
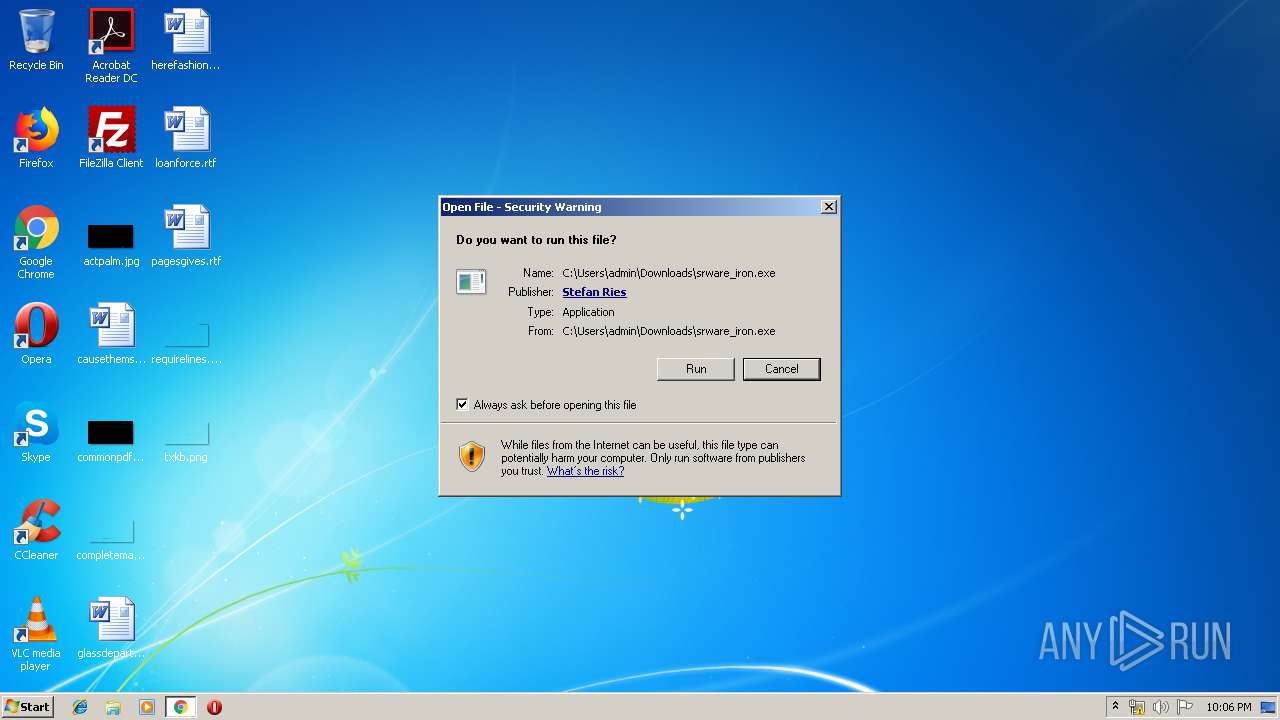
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2019, 21:04:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8703EE0C9DB0EF5E3BB8DB4038718802 |
| SHA1: | EE402ED2C557F941448FFD742D013B989980BB47 |
| SHA256: | 0240284D7A2BE62261F7FDD3620669B47190DEFF7284081CA825C12942F848B3 |
| SSDEEP: | 3:N8DSLHEeXyxhKVMGbVadSS:2OL2O7VWh |
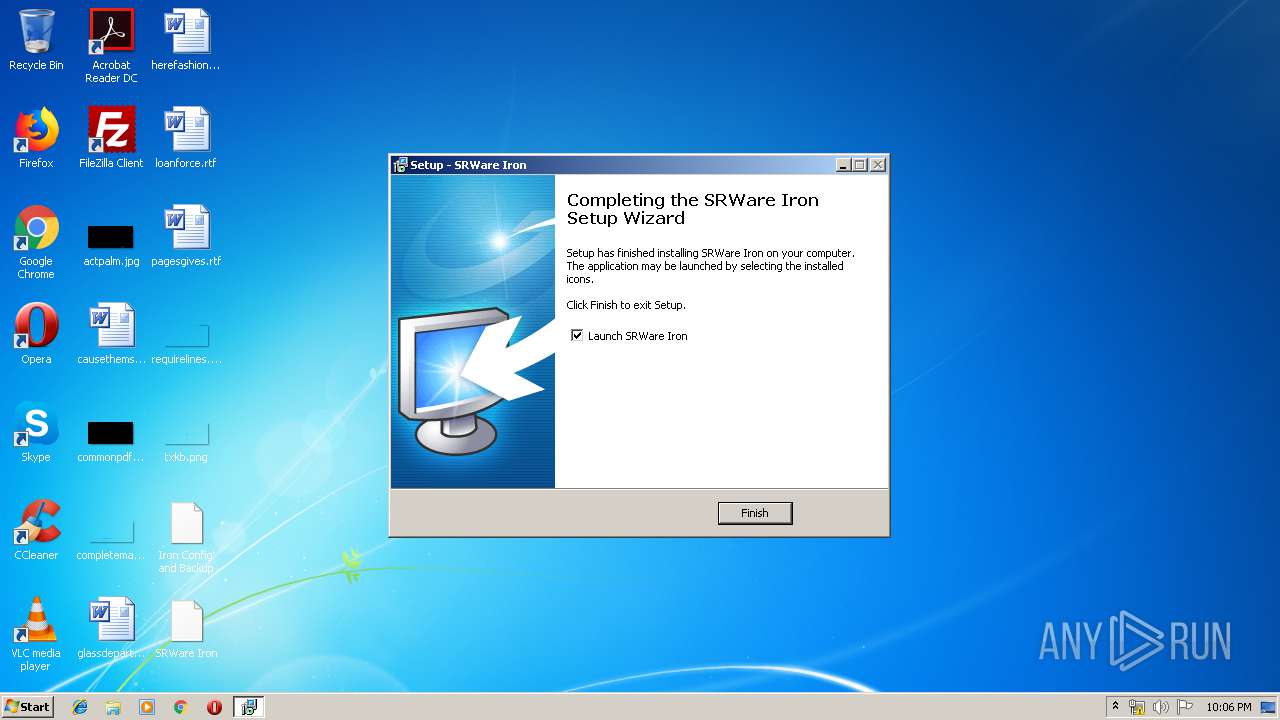
MALICIOUS
Application was dropped or rewritten from another process
- srware_iron.exe (PID: 2560)
- srware_iron.exe (PID: 3300)
- chrome.exe (PID: 1856)
- chrome.exe (PID: 2448)
- chrome.exe (PID: 2552)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 2576)
- chrome.exe (PID: 2224)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 3920)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 3032)
- chrome.exe (PID: 1476)
- chrome.exe (PID: 3272)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 2124)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 4036)
- chrome.exe (PID: 3276)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 2328)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 552)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3500)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 3936)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 3620)
- chrome.exe (PID: 456)
- chrome.exe (PID: 3284)
- chrome.exe (PID: 3688)
- chrome.exe (PID: 756)
- chrome.exe (PID: 3420)
- chrome.exe (PID: 3776)
Loads dropped or rewritten executable
- chrome.exe (PID: 1856)
- chrome.exe (PID: 2552)
- chrome.exe (PID: 2448)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 2576)
- chrome.exe (PID: 2224)
- chrome.exe (PID: 3920)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 3032)
- chrome.exe (PID: 1476)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 3272)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 2124)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 3276)
- chrome.exe (PID: 4036)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 3284)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 3500)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 2328)
- chrome.exe (PID: 552)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 3936)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 456)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 756)
- chrome.exe (PID: 3620)
- chrome.exe (PID: 3688)
Actions looks like stealing of personal data
- chrome.exe (PID: 1856)
SUSPICIOUS
Executable content was dropped or overwritten
- srware_iron.exe (PID: 2560)
- chrome.exe (PID: 2956)
- srware_iron.exe (PID: 3300)
- srware_iron.tmp (PID: 3960)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2956)
Reads Windows owner or organization settings
- srware_iron.tmp (PID: 3960)
Reads the Windows organization settings
- srware_iron.tmp (PID: 3960)
Modifies the open verb of a shell class
- srware_iron.tmp (PID: 3960)
Creates files in the user directory
- srware_iron.tmp (PID: 3960)
Application launched itself
- chrome.exe (PID: 1856)
INFO
Application launched itself
- chrome.exe (PID: 2956)
Application was dropped or rewritten from another process
- srware_iron.tmp (PID: 2376)
- srware_iron.tmp (PID: 3960)
Changes settings of System certificates
- chrome.exe (PID: 2956)
Loads dropped or rewritten executable
- srware_iron.tmp (PID: 3960)
Dropped object may contain Bitcoin addresses
- srware_iron.tmp (PID: 3960)
Creates a software uninstall entry
- srware_iron.tmp (PID: 3960)
Creates files in the program directory
- srware_iron.tmp (PID: 3960)
Reads settings of System Certificates
- chrome.exe (PID: 1856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
99
Monitored processes
65
Malicious processes
28
Suspicious processes
14
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files\SRWare Iron\chrome.exe" --type=renderer --field-trial-handle=964,5234299283323715363,11692966647256665724,131072 --disable-gpu-compositing --service-pipe-token=16803303664980909367 --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16803303664980909367 --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6008 /prefetch:1 | C:\Program Files\SRWare Iron\chrome.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: LOW Description: SRWare Iron Exit code: 0 Version: 73.0.3800.0 Modules
| |||||||||||||||
| 552 | "C:\Program Files\SRWare Iron\chrome.exe" --type=renderer --field-trial-handle=964,5234299283323715363,11692966647256665724,131072 --disable-gpu-compositing --service-pipe-token=448277796746698605 --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=448277796746698605 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=8372 /prefetch:1 | C:\Program Files\SRWare Iron\chrome.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: LOW Description: SRWare Iron Exit code: 0 Version: 73.0.3800.0 Modules
| |||||||||||||||
| 756 | "C:\Program Files\SRWare Iron\chrome.exe" --type=renderer --field-trial-handle=964,5234299283323715363,11692966647256665724,131072 --disable-gpu-compositing --service-pipe-token=8268447095661705600 --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8268447095661705600 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=8420 /prefetch:1 | C:\Program Files\SRWare Iron\chrome.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: LOW Description: SRWare Iron Exit code: 0 Version: 73.0.3800.0 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7519280040682335632 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7519280040682335632 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14656294939574056027 --mojo-platform-channel-handle=2636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\SRWare Iron\chrome.exe" --type=renderer --field-trial-handle=964,5234299283323715363,11692966647256665724,131072 --disable-gpu-compositing --service-pipe-token=12713931496605971316 --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12713931496605971316 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5048 /prefetch:1 | C:\Program Files\SRWare Iron\chrome.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: LOW Description: SRWare Iron Exit code: 0 Version: 73.0.3800.0 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\SRWare Iron\chrome.exe" | C:\Program Files\SRWare Iron\chrome.exe | srware_iron.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Description: SRWare Iron Exit code: 0 Version: 73.0.3800.0 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\SRWare Iron\chrome.exe" --type=renderer --field-trial-handle=964,5234299283323715363,11692966647256665724,131072 --disable-gpu-compositing --service-pipe-token=9939032356829877044 --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9939032356829877044 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4212 /prefetch:1 | C:\Program Files\SRWare Iron\chrome.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: LOW Description: SRWare Iron Exit code: 0 Version: 73.0.3800.0 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\SRWare Iron\chrome.exe" --type=renderer --field-trial-handle=964,5234299283323715363,11692966647256665724,131072 --disable-gpu-compositing --service-pipe-token=14485430689064302065 --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14485430689064302065 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=8388 /prefetch:1 | C:\Program Files\SRWare Iron\chrome.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: LOW Description: SRWare Iron Exit code: 0 Version: 73.0.3800.0 Modules
| |||||||||||||||
| 2224 | "C:\Program Files\SRWare Iron\chrome.exe" --type=renderer --field-trial-handle=964,5234299283323715363,11692966647256665724,131072 --service-pipe-token=7632620514297651597 --lang=en-US --extension-process --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7632620514297651597 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2164 /prefetch:1 | C:\Program Files\SRWare Iron\chrome.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: LOW Description: SRWare Iron Exit code: 0 Version: 73.0.3800.0 Modules
| |||||||||||||||
Total events
1 698
Read events
1 489
Write events
197
Delete events
12
Modification events
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2956-13199749508381125 |
Value: 259 | |||
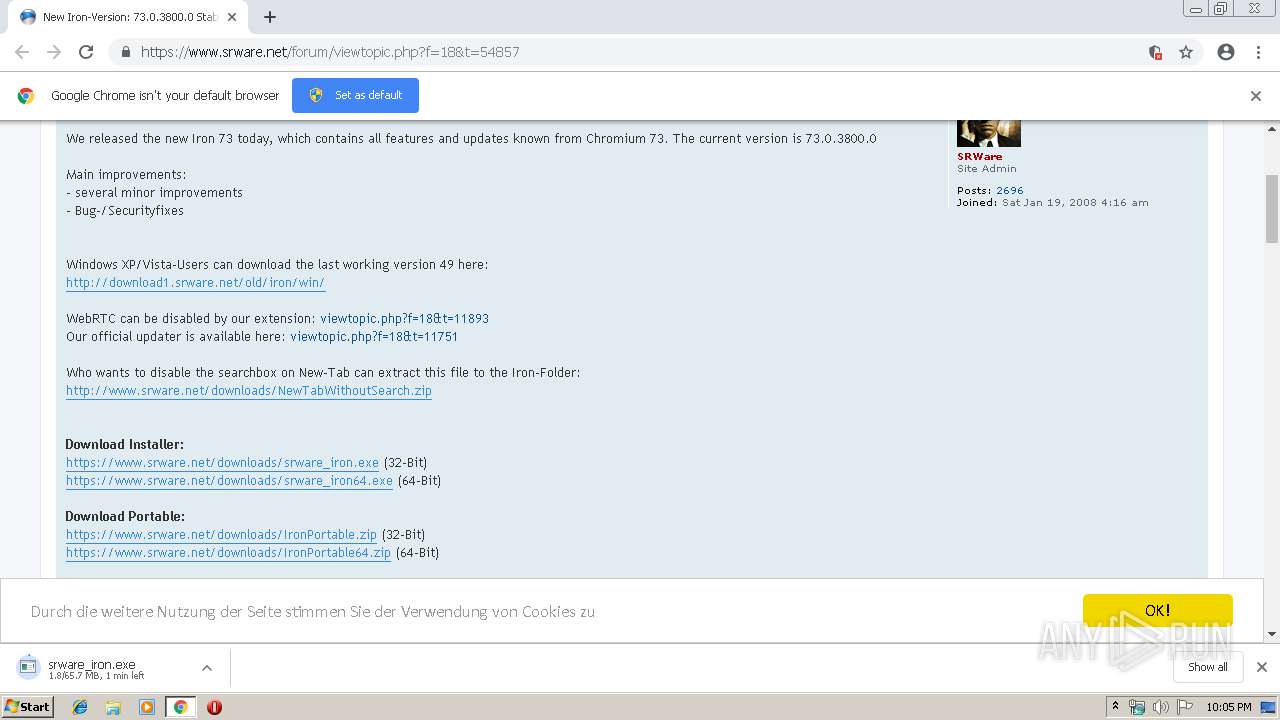
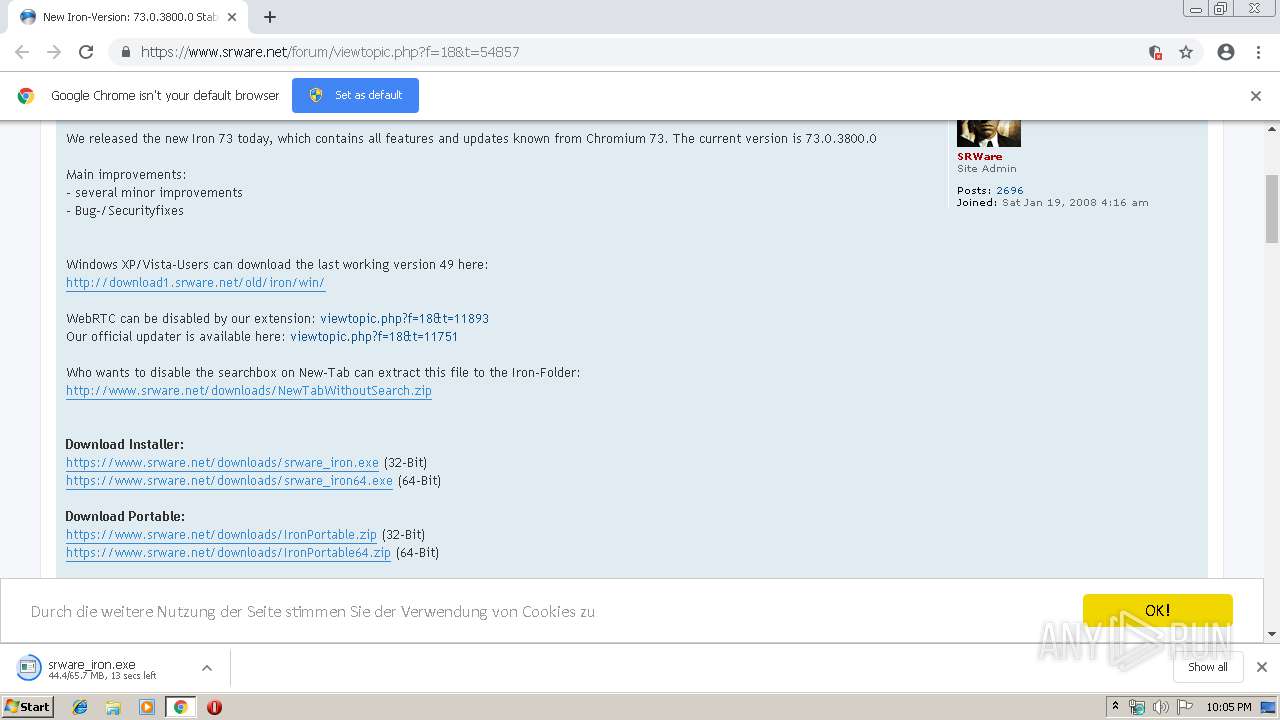
Executable files
19
Suspicious files
223
Text files
434
Unknown types
104
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\05e144ed-8856-4285-a5f6-714c88e4f1da.tmp | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
113
TCP/UDP connections
318
DNS requests
215
Threats
0
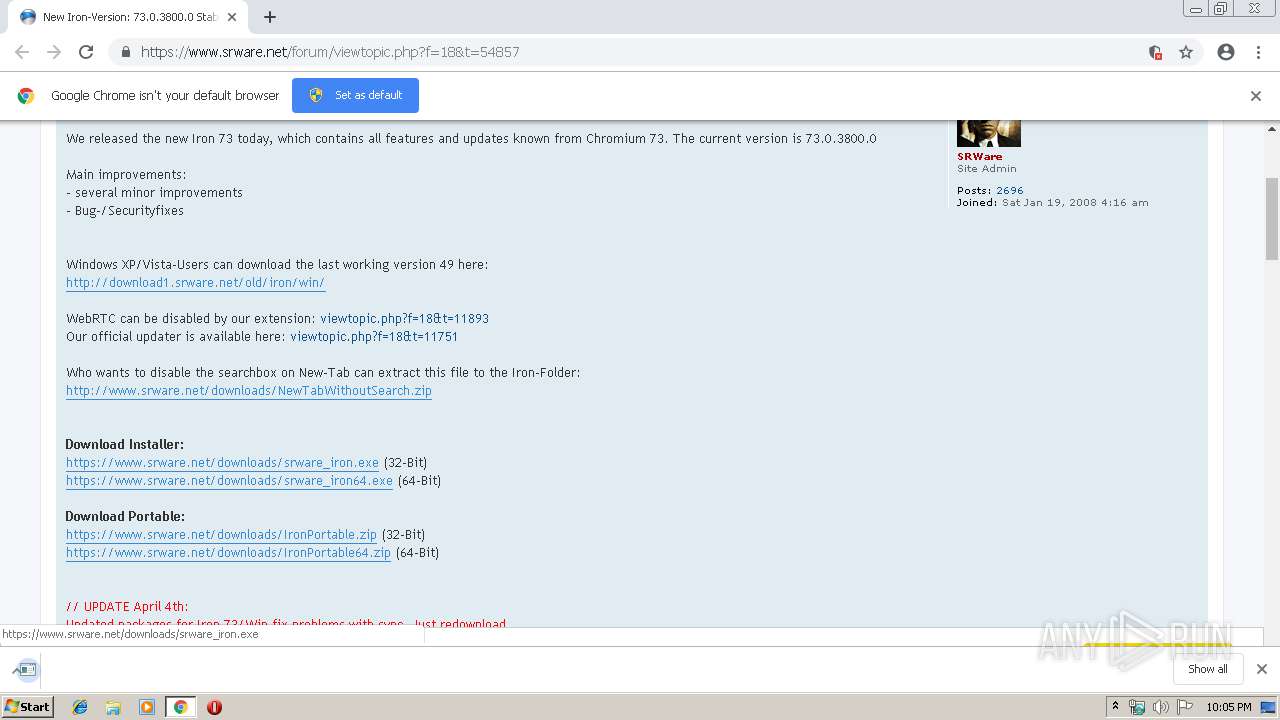
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1856 | chrome.exe | GET | — | 87.98.132.201:80 | http://www.srware.net/fr/fr.png | FR | — | — | unknown |
1856 | chrome.exe | GET | 301 | 87.98.132.201:80 | http://www.srware.net/es.png | FR | html | 247 b | unknown |
1856 | chrome.exe | GET | 301 | 87.98.132.201:80 | http://www.srware.net/en/iron | FR | html | 247 b | unknown |
4080 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 507 b | whitelisted |
1856 | chrome.exe | GET | 200 | 2.16.106.186:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 55.6 Kb | whitelisted |
4080 | chrome.exe | GET | 200 | 194.9.24.113:80 | http://r6---sn-5uh5o-f5fd.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.217.54&mm=28&mn=sn-5uh5o-f5fd&ms=nvh&mt=1555275666&mv=u&pl=21&shardbypass=yes | PL | crx | 842 Kb | whitelisted |
1856 | chrome.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEHiupDHBXOt1ew2KYQp0jmc%3D | NL | der | 1.71 Kb | shared |
1856 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
1856 | chrome.exe | GET | 301 | 87.98.132.201:80 | http://www.srware.net/en/software_srware_iron.php | FR | html | 258 b | unknown |
1856 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQu7Xbjq6rqggE7PFAsQRgy8Q8tzwQUkEeKG4TToN%2BkJNYZtBf1IaOym6gCEA7fr0YLsTZHJYxFeyuWNYA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4080 | chrome.exe | 104.19.197.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
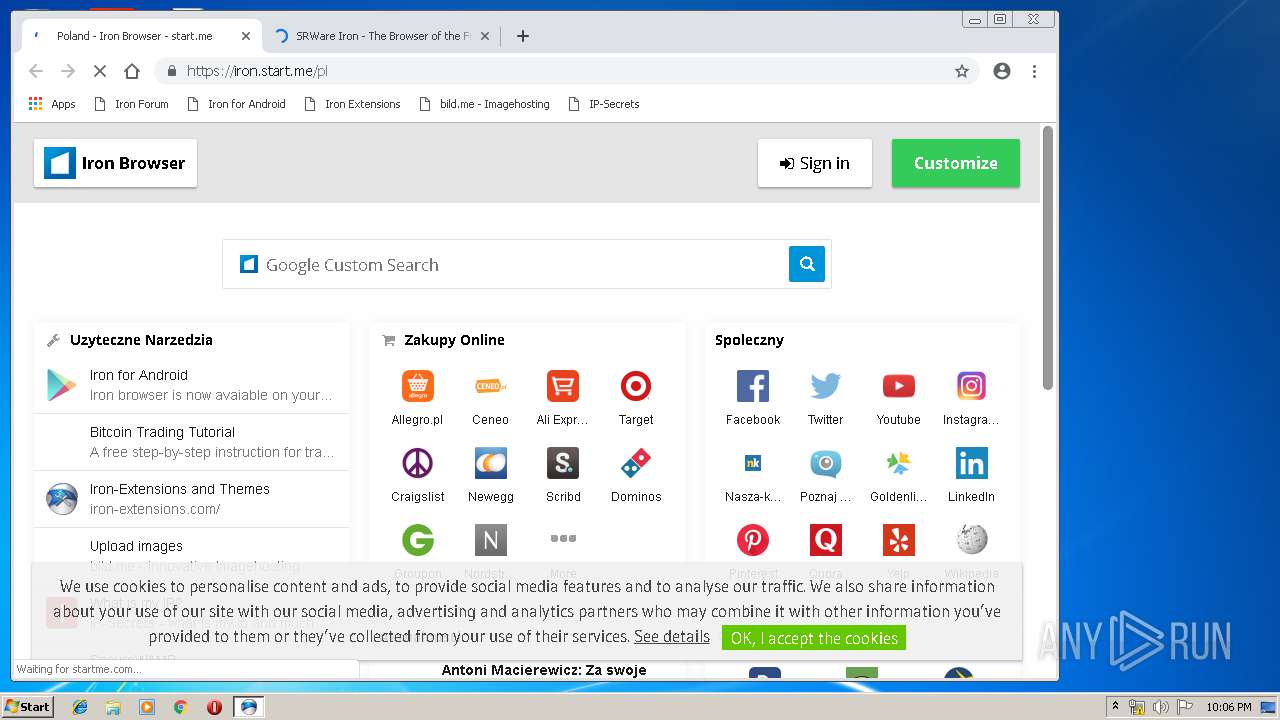
4080 | chrome.exe | 85.214.126.87:443 | www.browser-statistik.de | Strato AG | DE | unknown |
4080 | chrome.exe | 172.217.18.2:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 51.15.74.77:443 | i.ibb.co | Online S.a.s. | FR | unknown |
— | — | 87.98.132.201:443 | www.srware.net | OVH SAS | FR | unknown |
4080 | chrome.exe | 164.132.119.143:443 | myvisitorcounter.com | OVH SAS | FR | unknown |
4080 | chrome.exe | 216.58.207.65:443 | tpc.googlesyndication.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 172.217.16.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 194.9.24.113:80 | r6---sn-5uh5o-f5fd.gvt1.com | ATM S.A. | PL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.srware.net |
| unknown |
accounts.google.com |
| shared |
pagead2.googlesyndication.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
i.ibb.co |
| shared |
www.browser-statistik.de |
| malicious |
adservice.google.pl |
| whitelisted |
adservice.google.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |