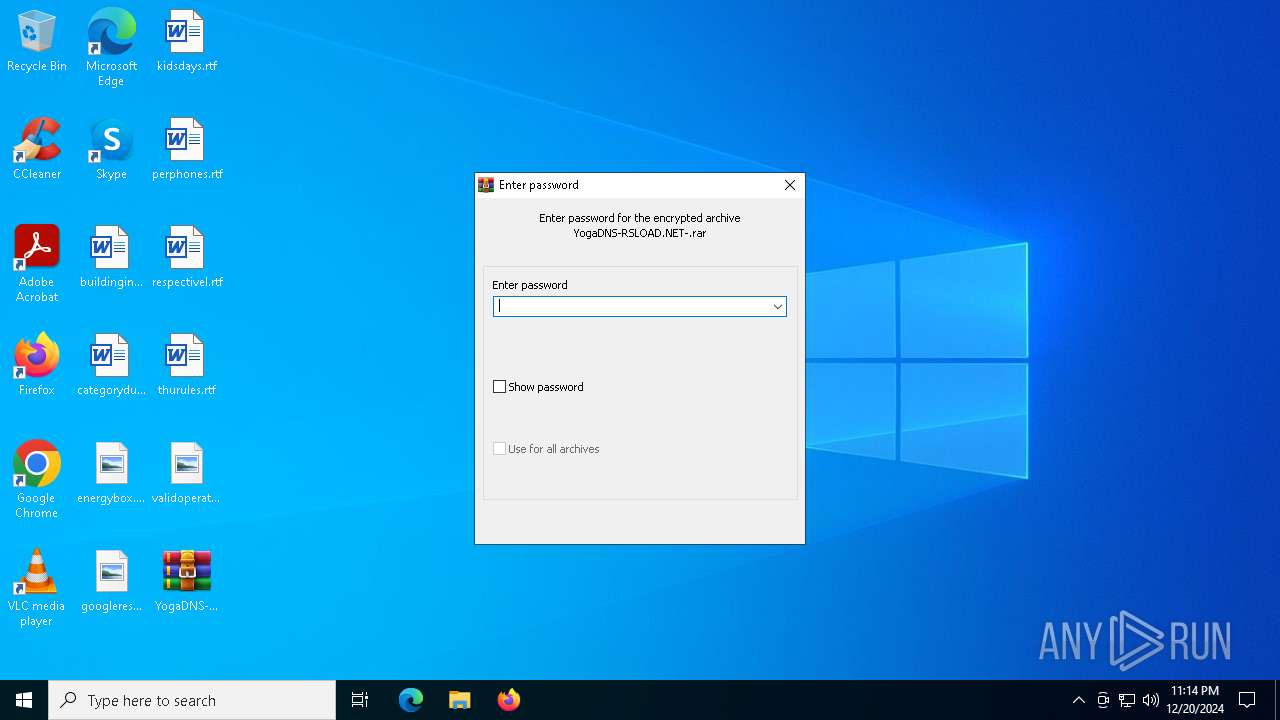
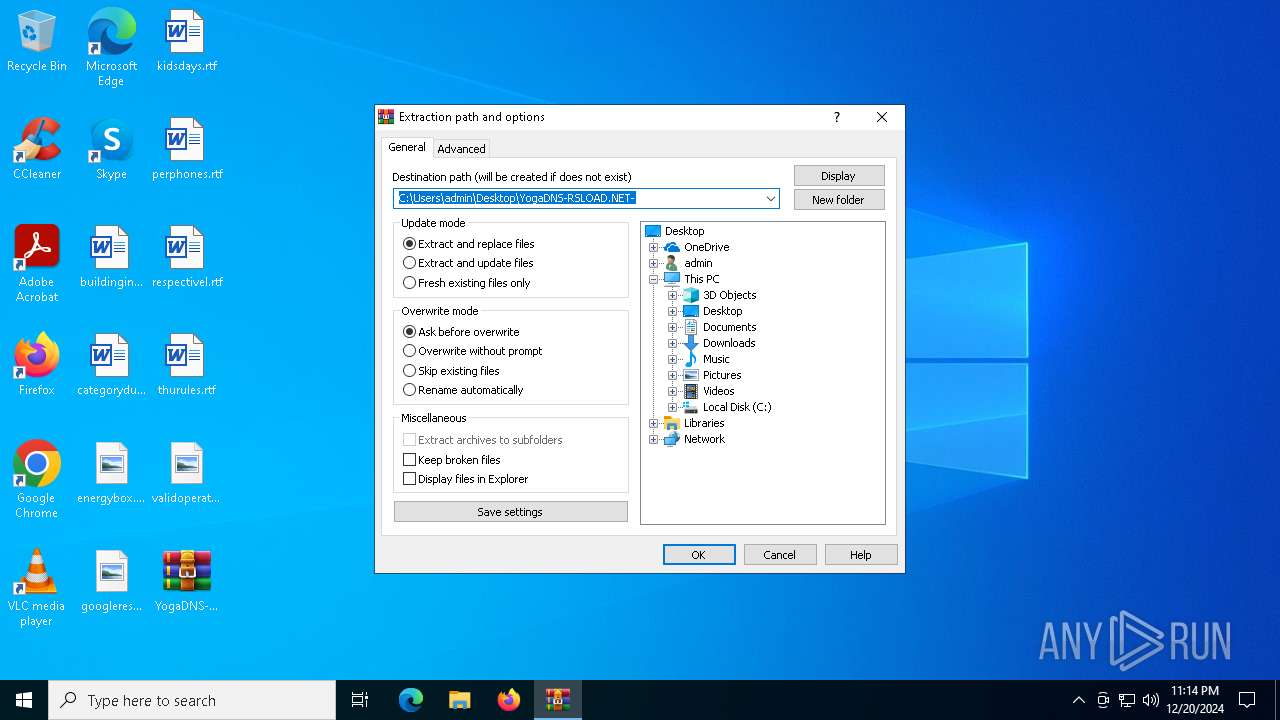
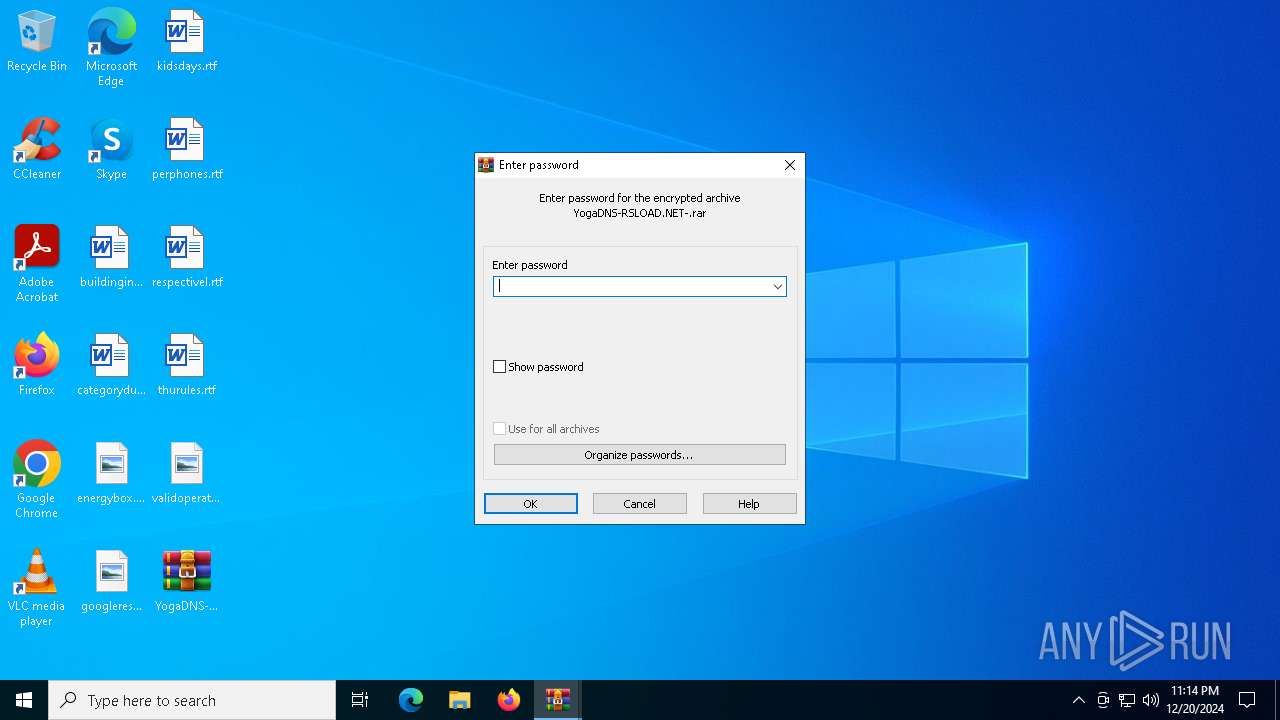
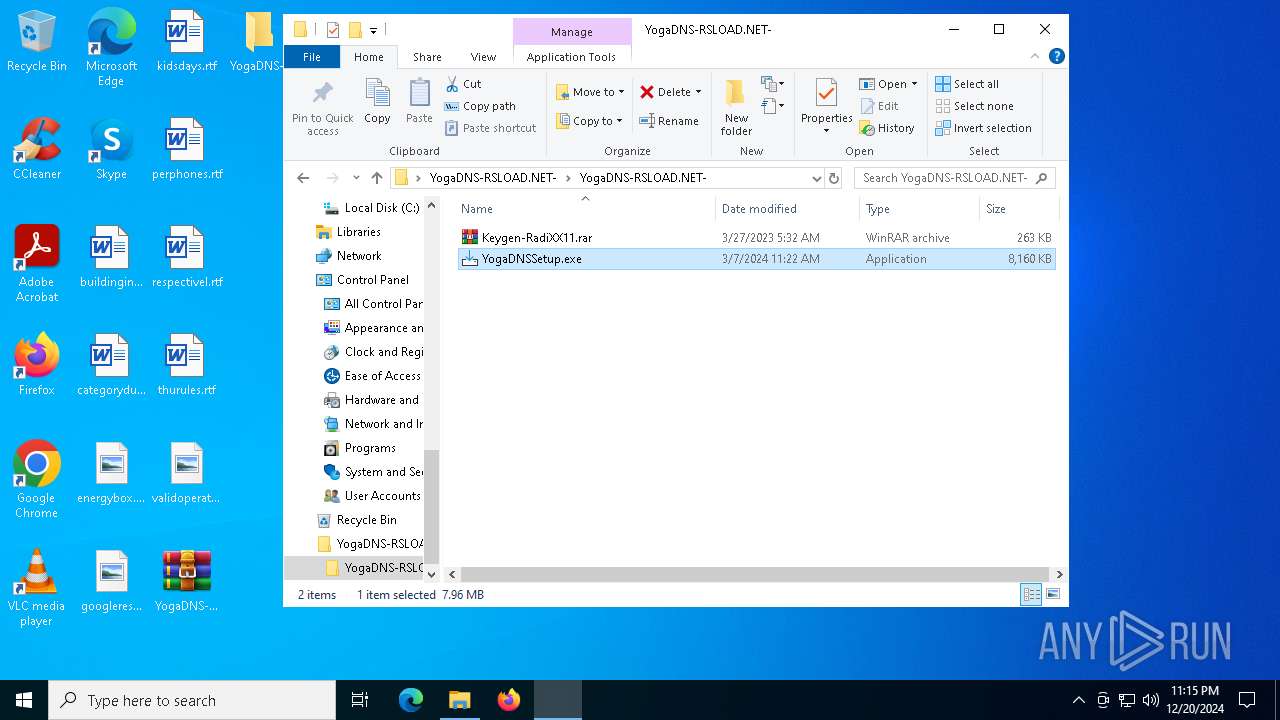
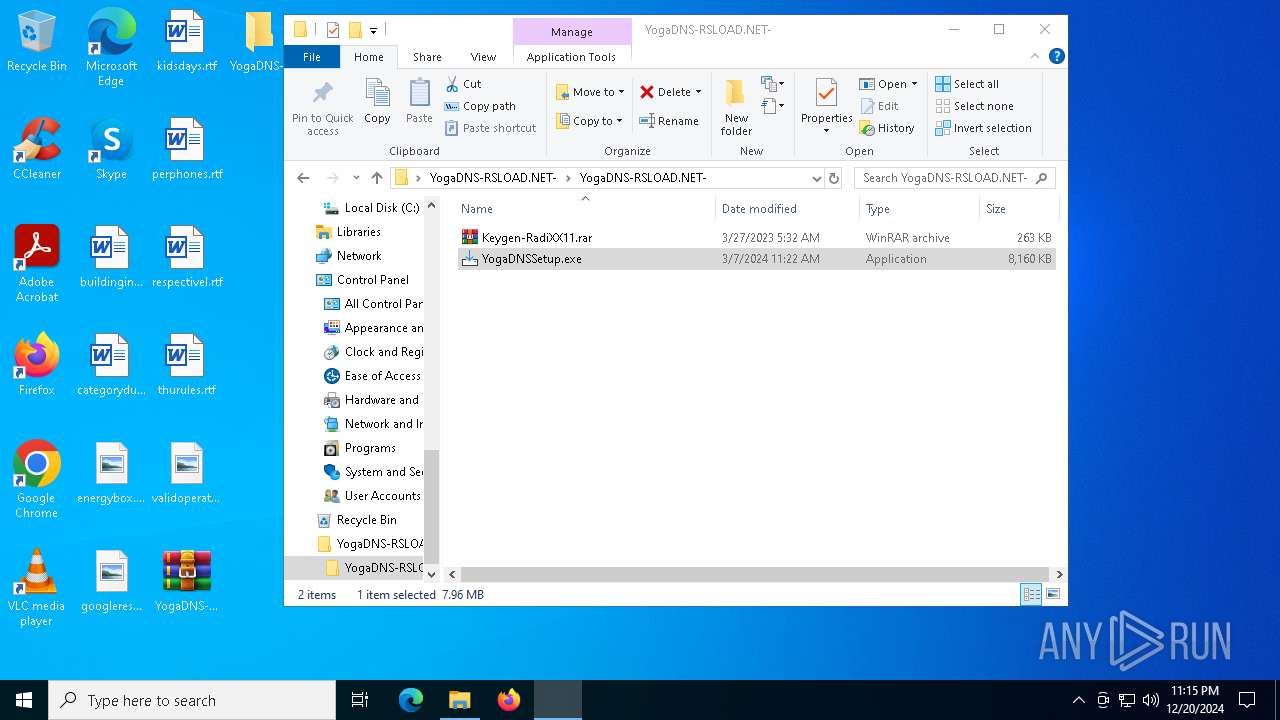
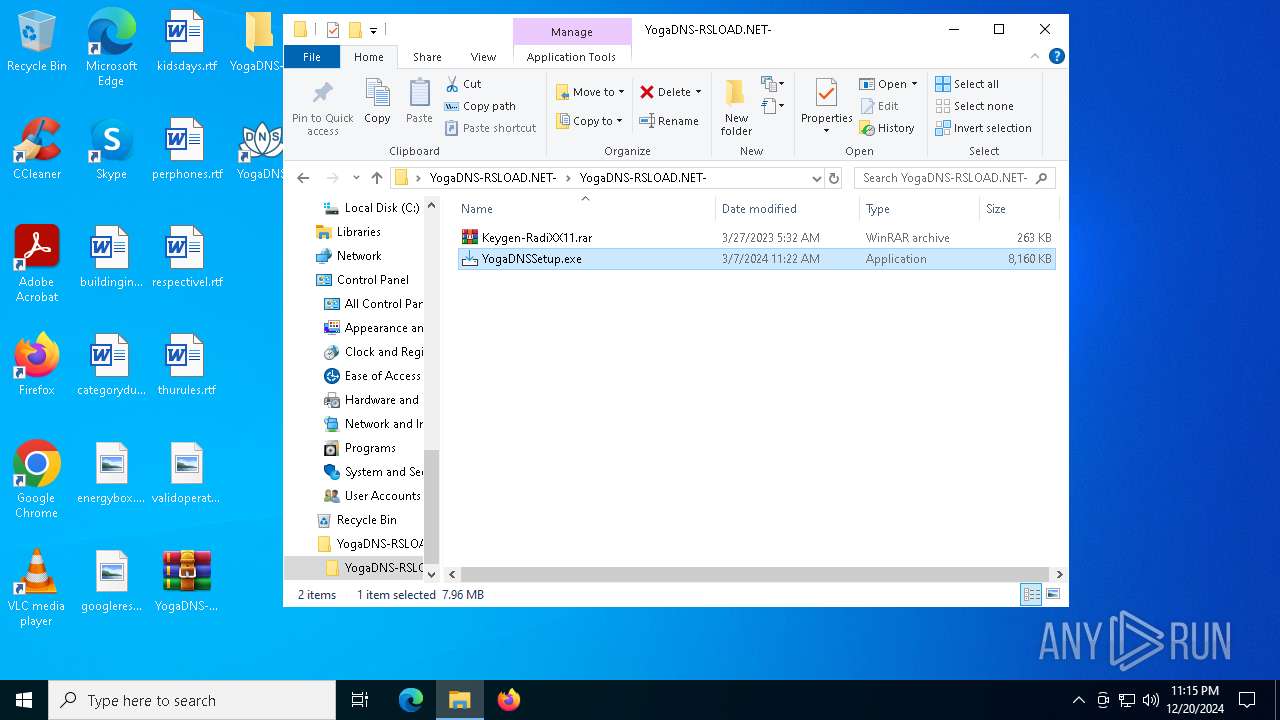
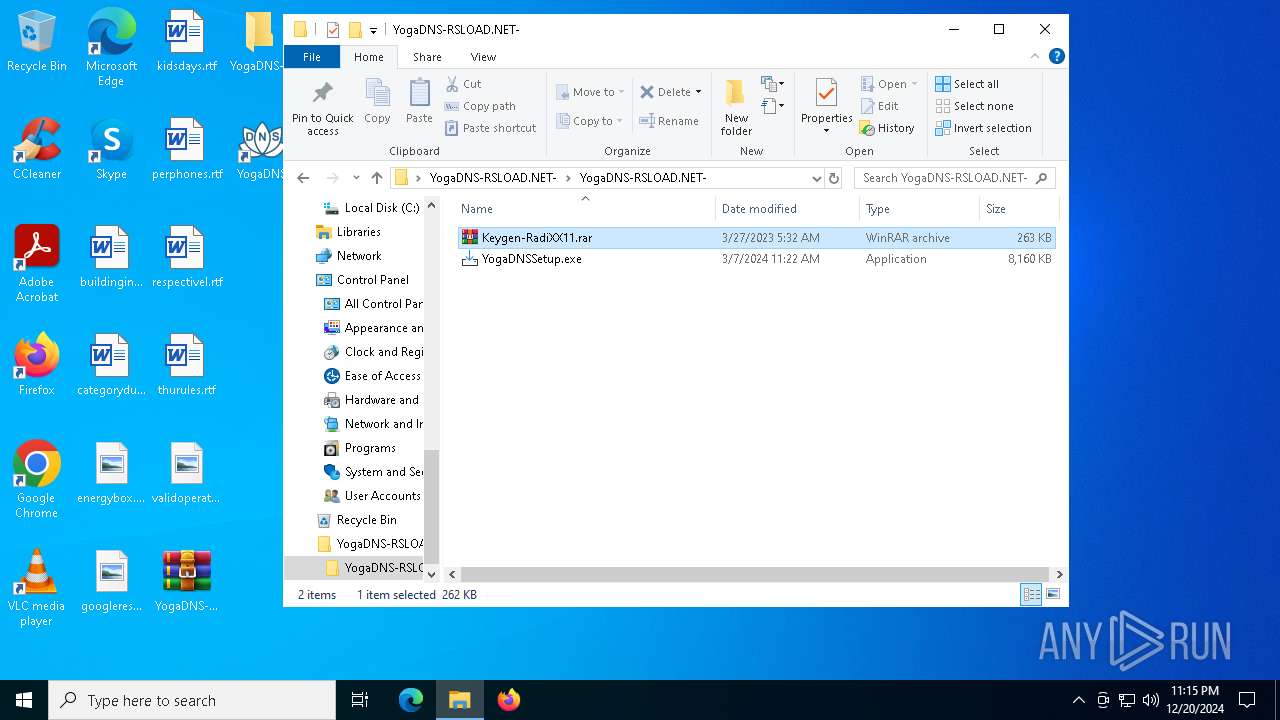
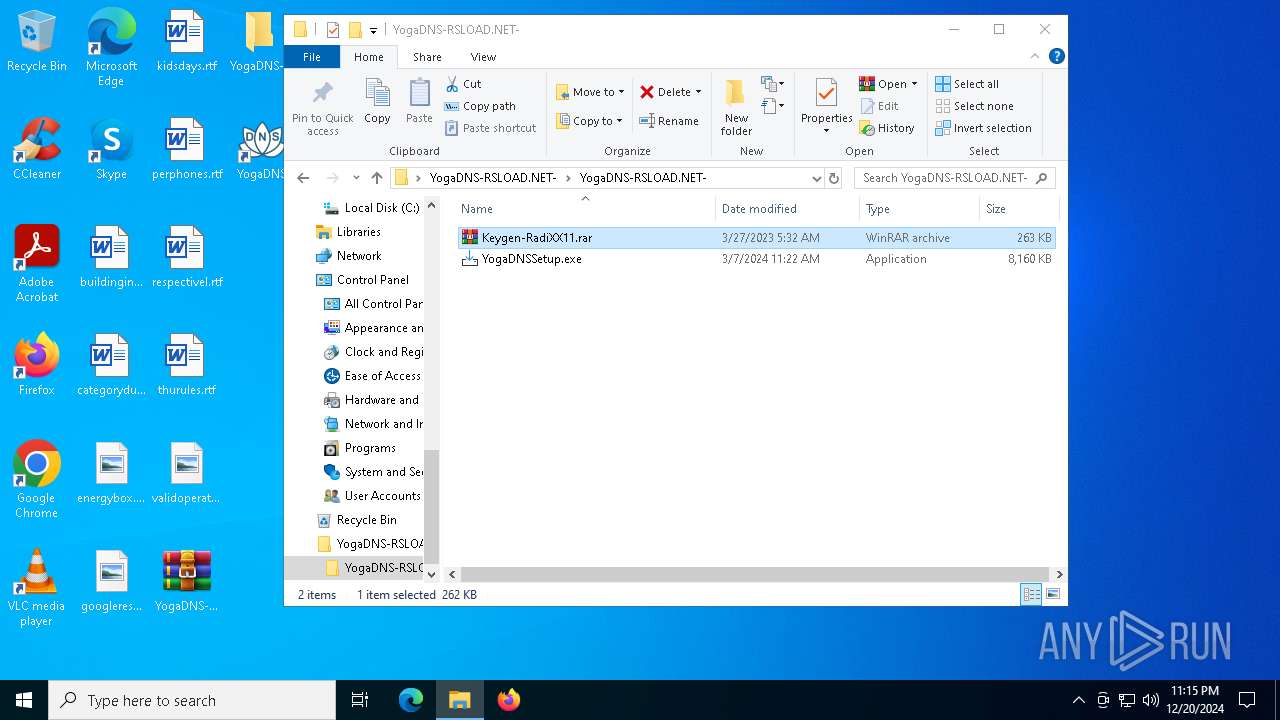
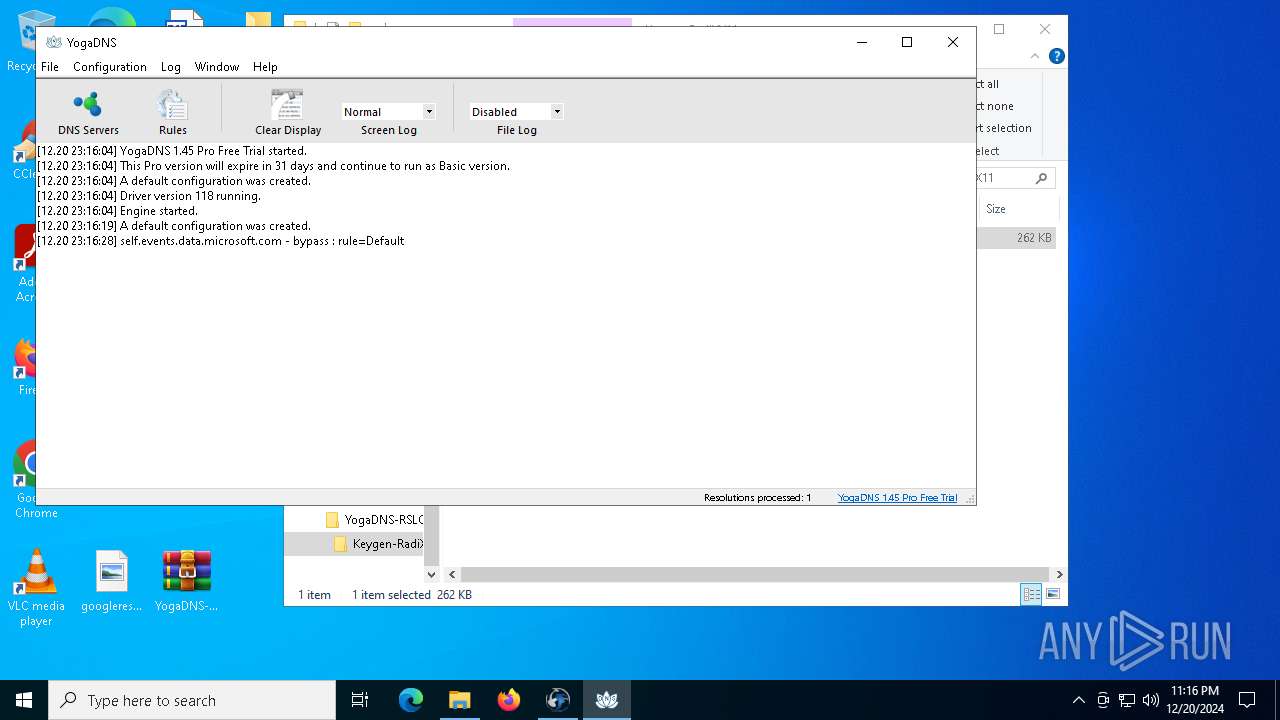
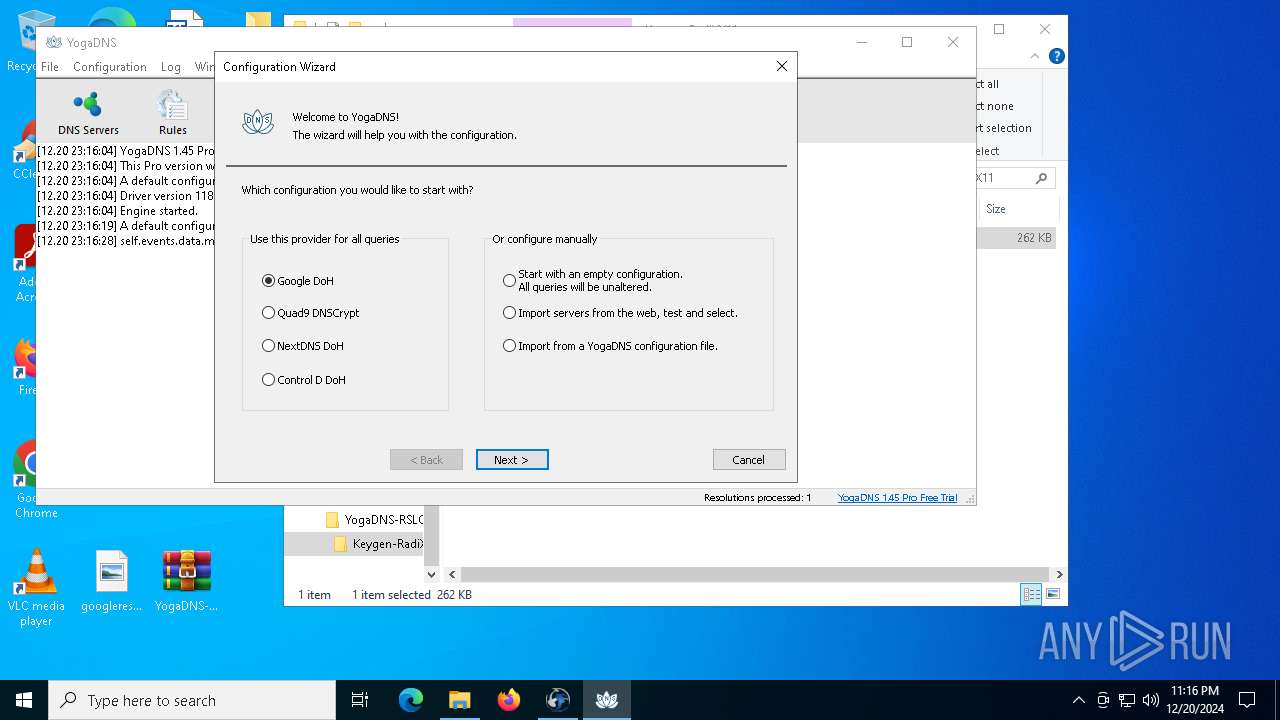
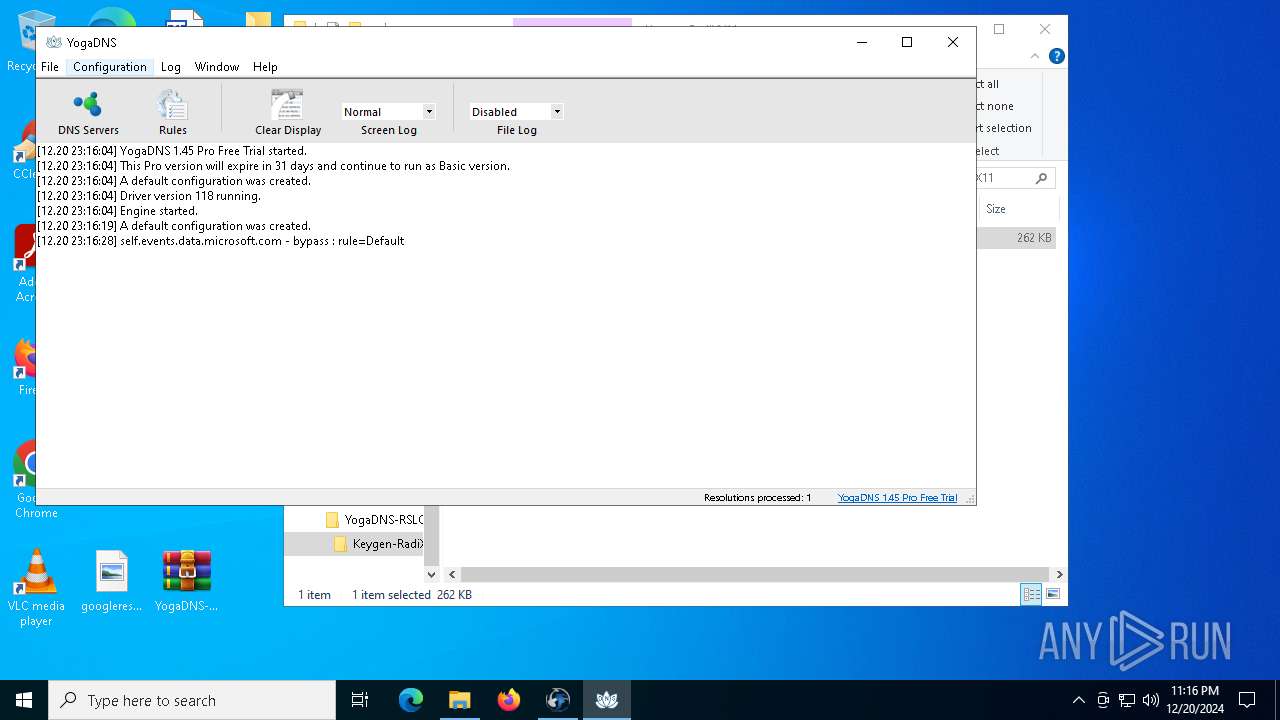
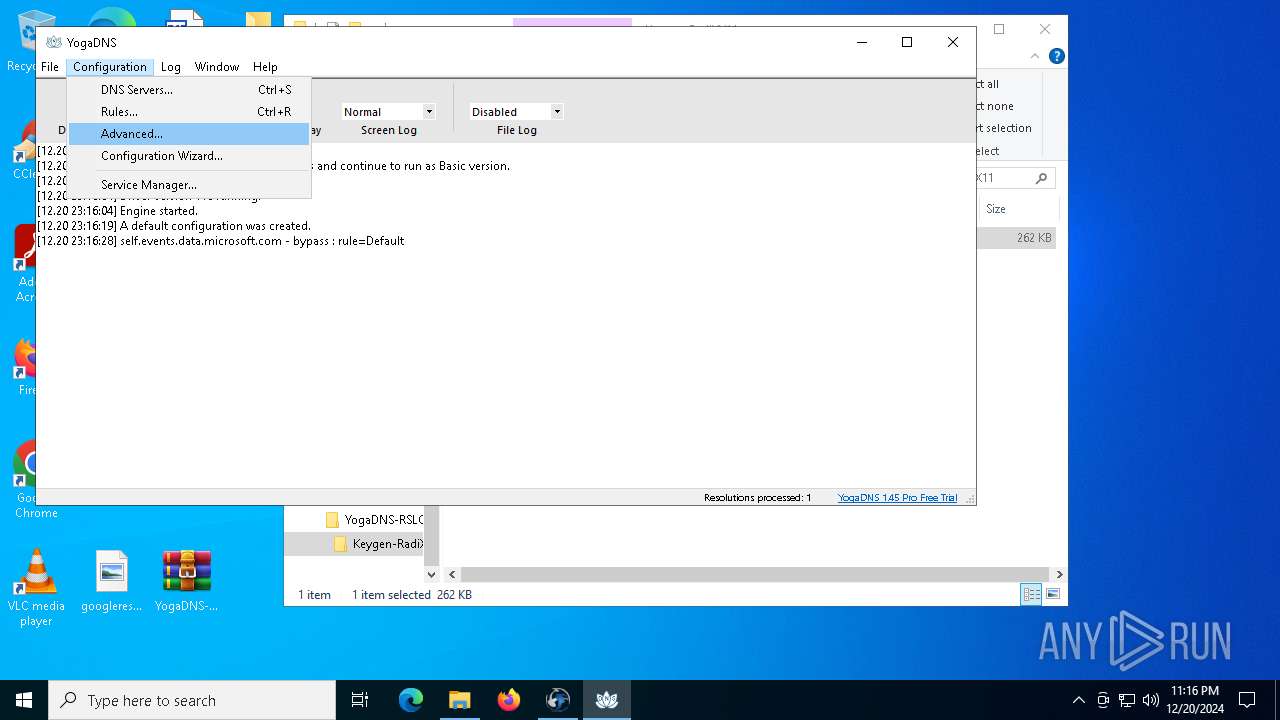
| File name: | YogaDNS-RSLOAD.NET-.rar |
| Full analysis: | https://app.any.run/tasks/a6188848-ee31-4928-94e1-e7e828c1d7ee |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2024, 23:14:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 6FDC2C57B29E157EC4FE26D250FEAEE3 |
| SHA1: | B04AEEBC8391D181131616918C1ECB935139B8B3 |
| SHA256: | 022F291788806C305502008B4305449854F4EB1CF6EAB5E61066BFE933E414C1 |
| SSDEEP: | 98304:iydRop5g8cwI9qY6fjVm8QlmLXzMirnyivWFqxx4AZQRsEKjEPd1DLoVyAx/duGr:ersqiQebaY3BEZJ1T |
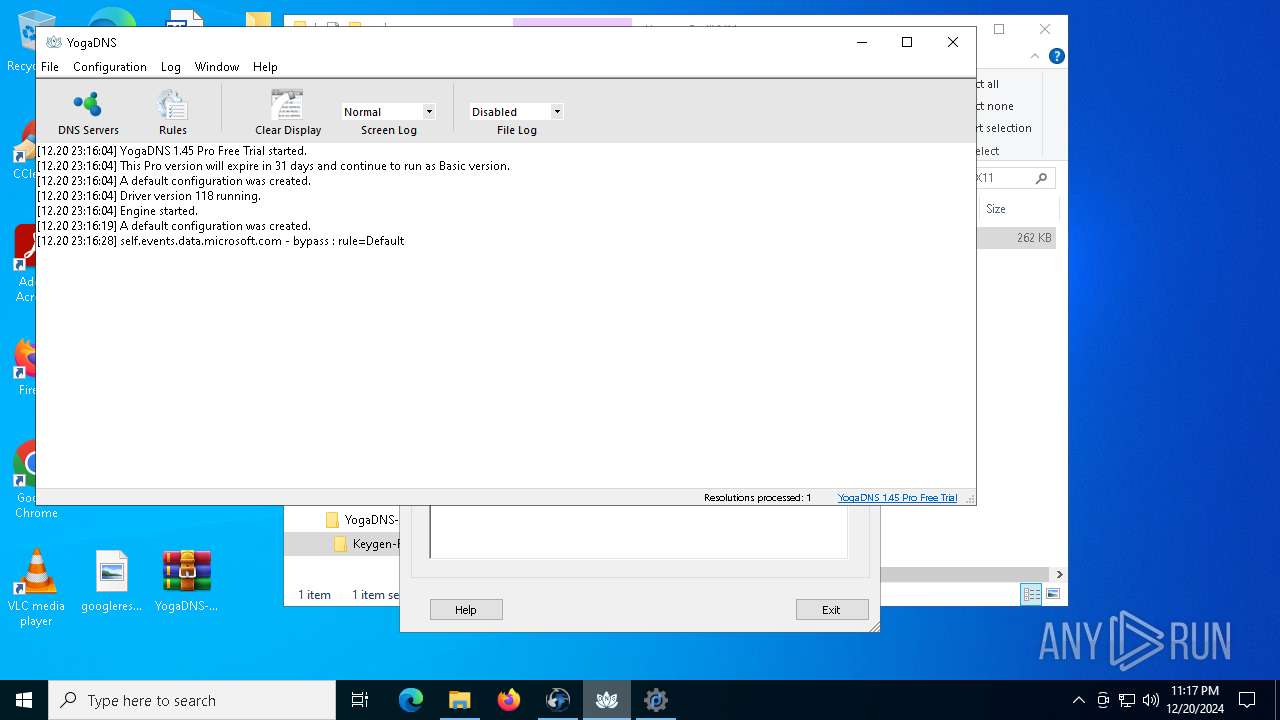
MALICIOUS
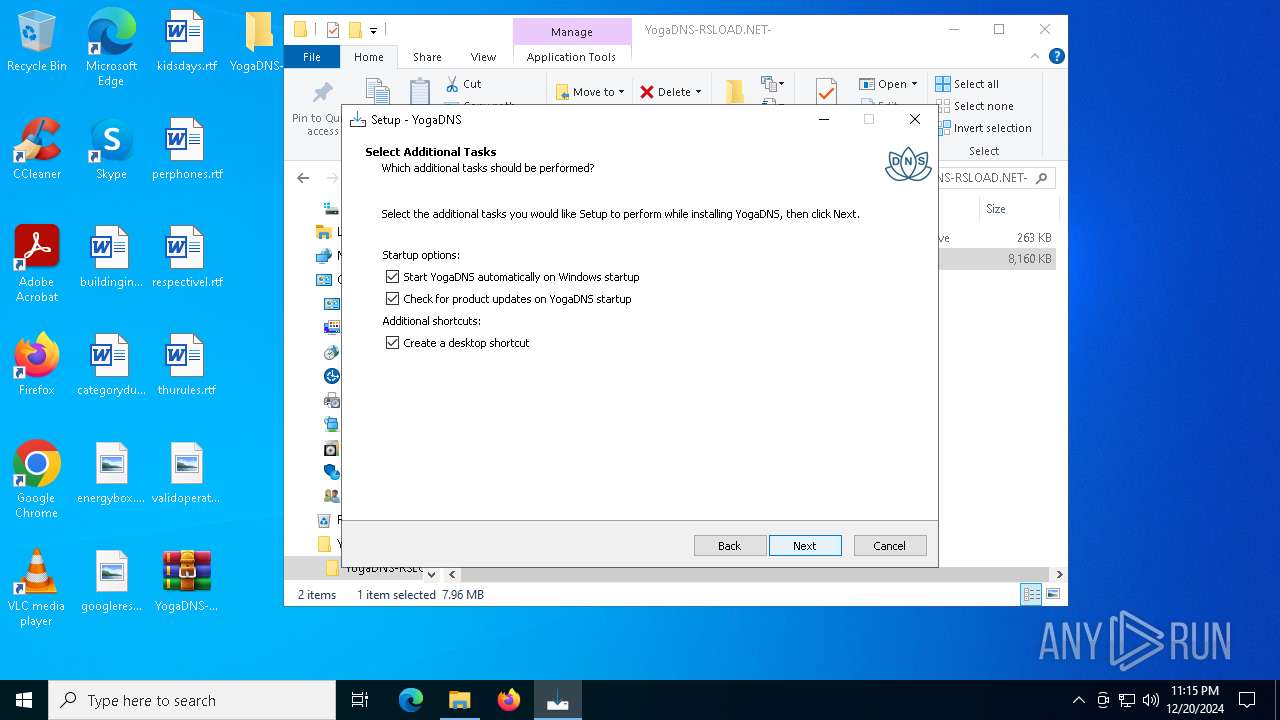
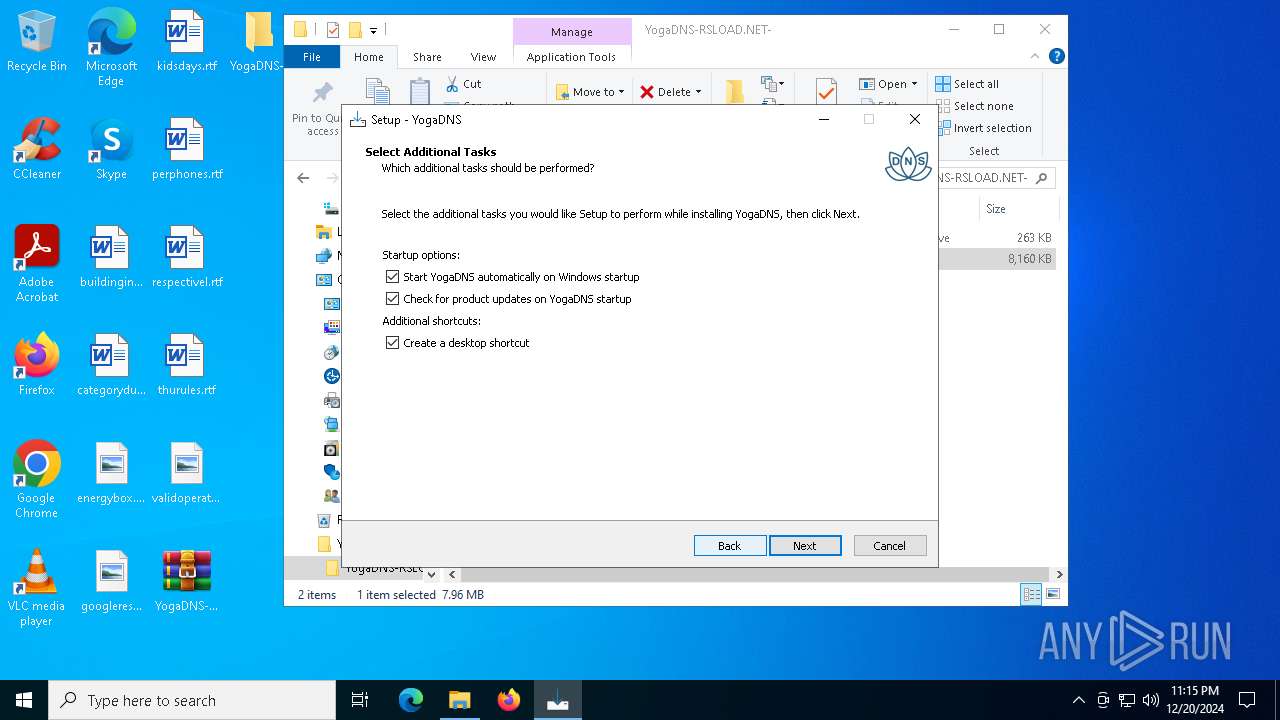
Changes the autorun value in the registry
- YogaDNSSetup.tmp (PID: 5308)
- rundll32.exe (PID: 5244)
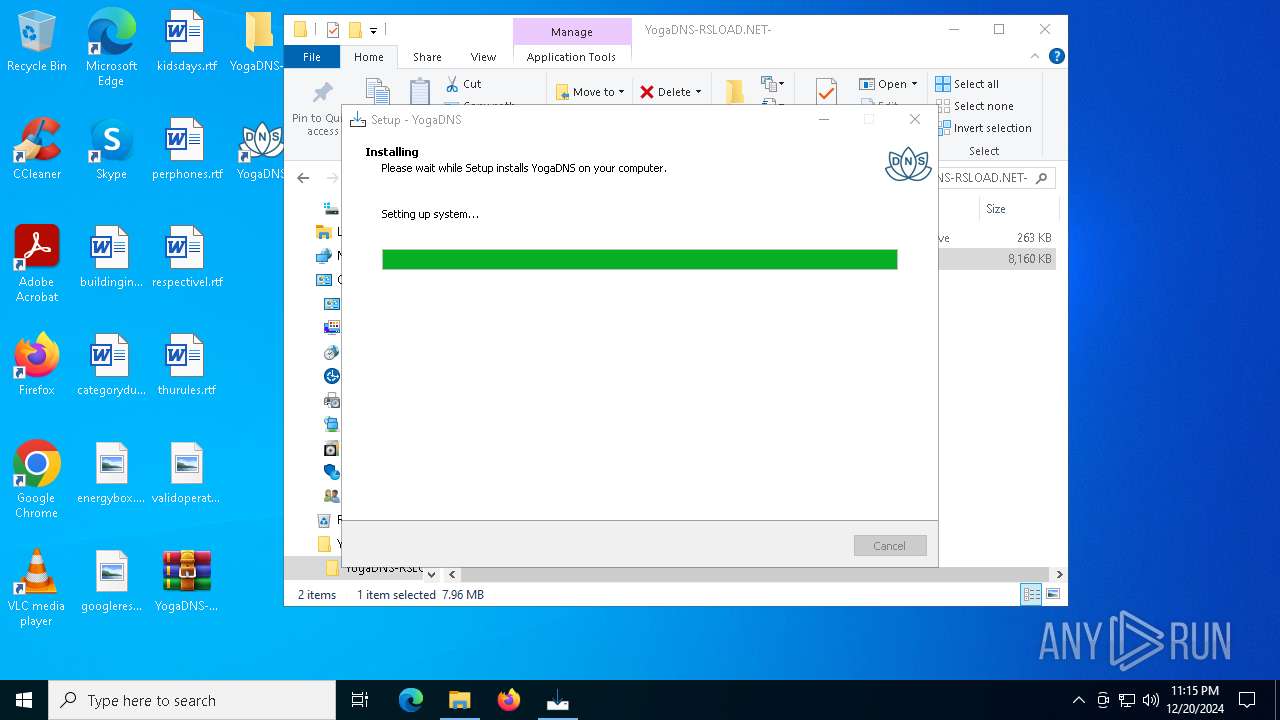
Starts NET.EXE for service management
- YogaDNSSetup.tmp (PID: 5308)
- net.exe (PID: 5000)
SUSPICIOUS
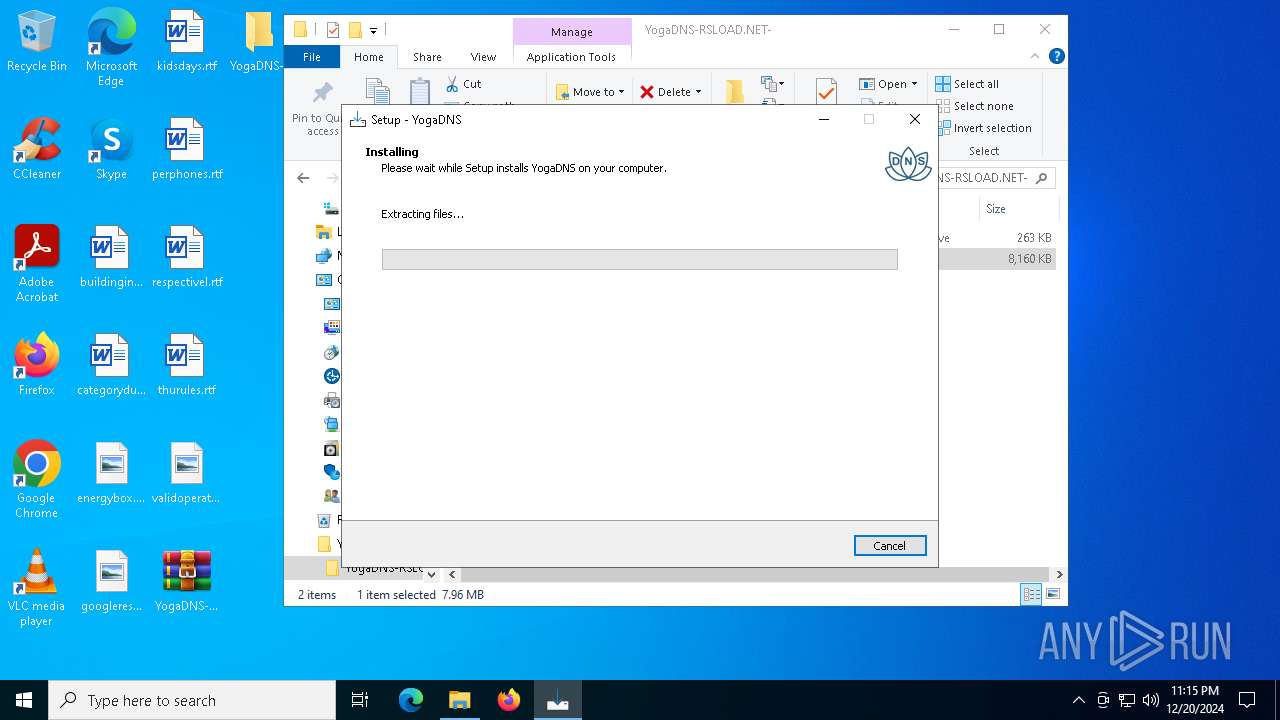
Executable content was dropped or overwritten
- YogaDNSSetup.exe (PID: 4428)
- YogaDNSSetup.exe (PID: 3620)
- YogaDNSSetup.tmp (PID: 5308)
- drvinst.exe (PID: 3952)
- rundll32.exe (PID: 5244)
- drvinst.exe (PID: 5252)
Reads security settings of Internet Explorer
- YogaDNSSetup.tmp (PID: 3544)
- YogaDNS.exe (PID: 6228)
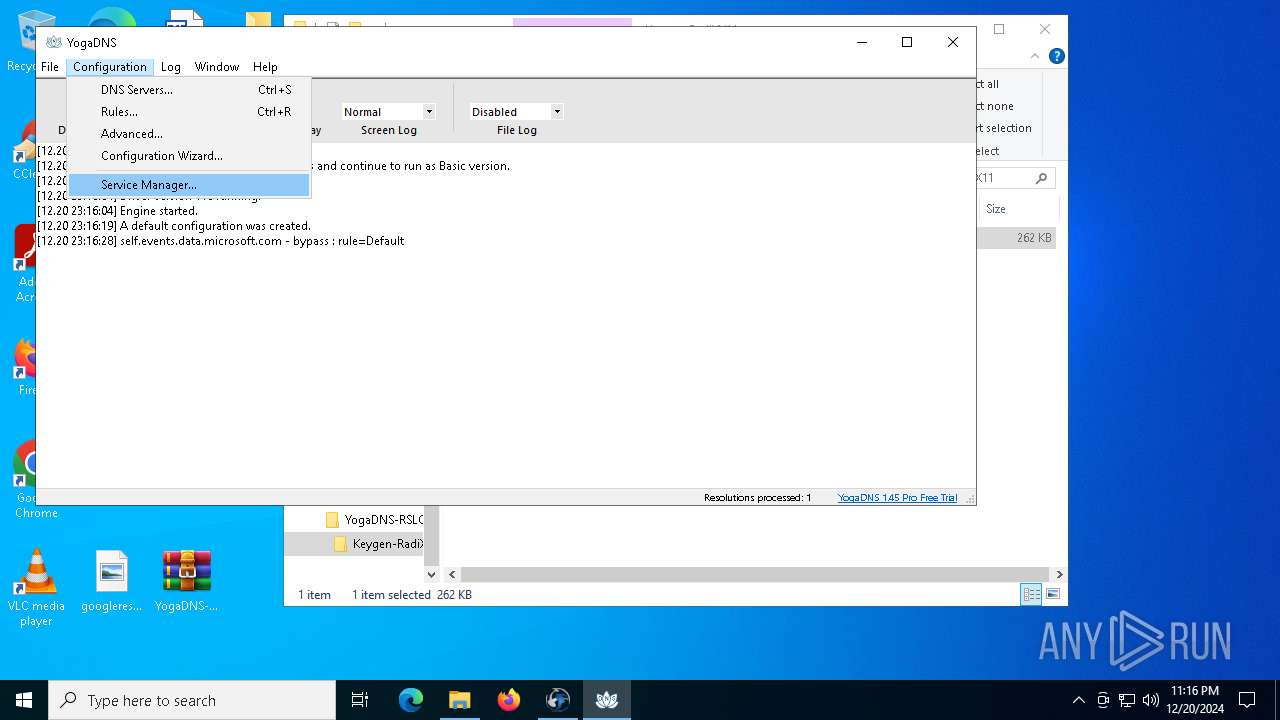
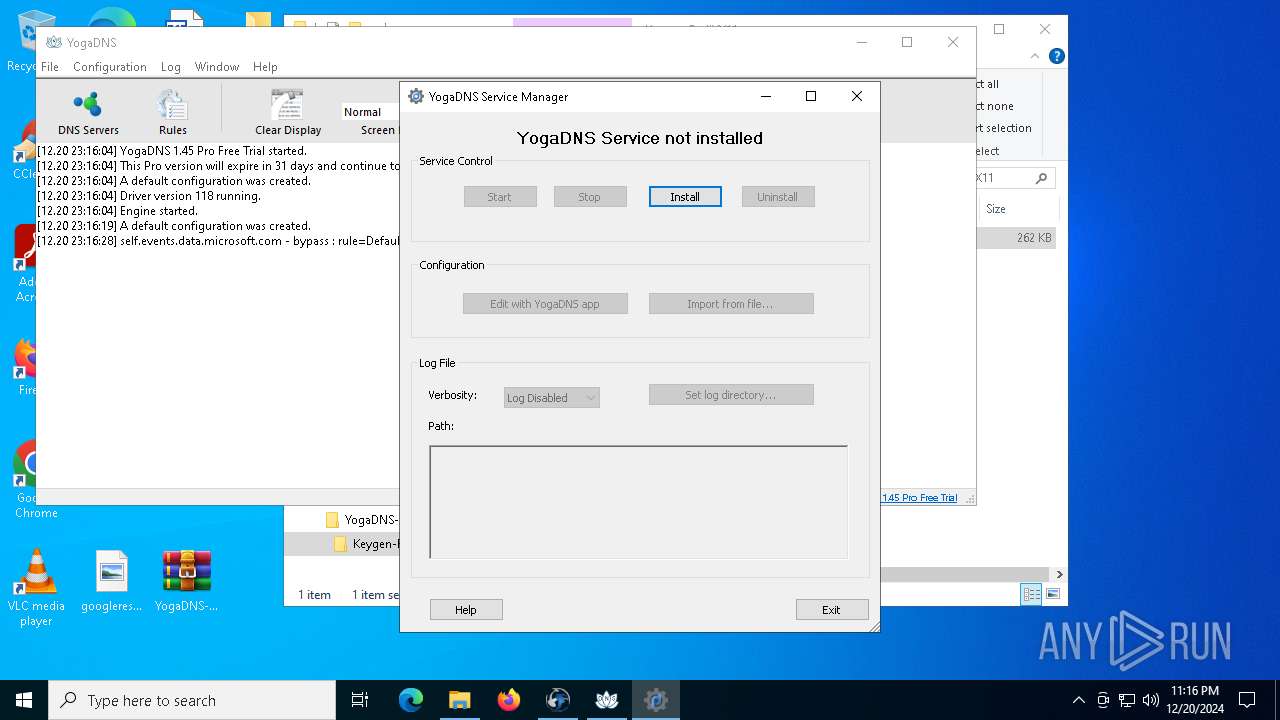
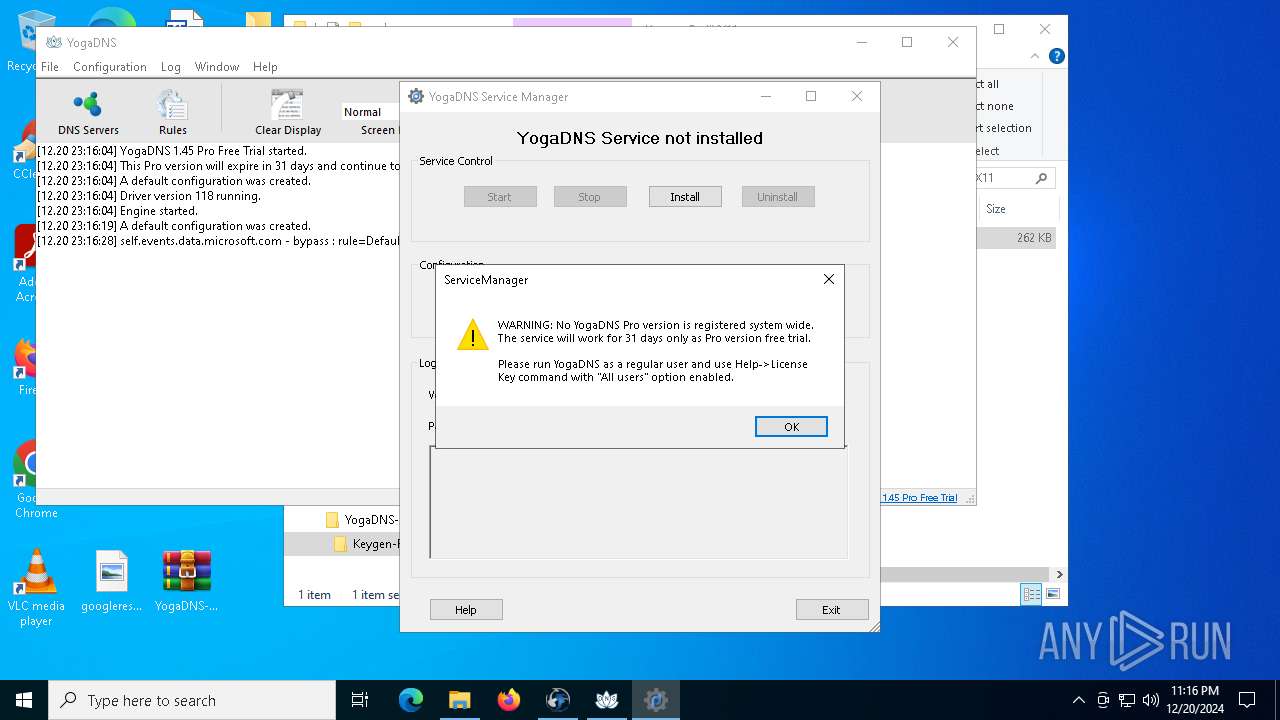
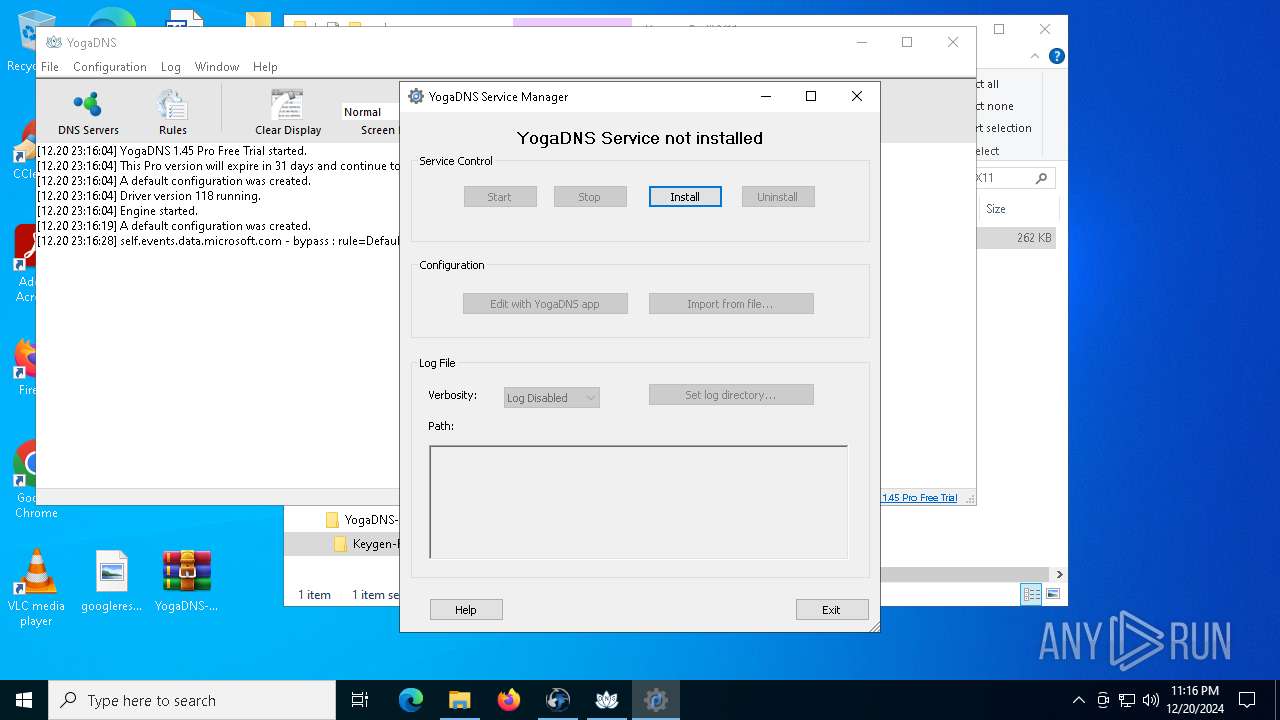
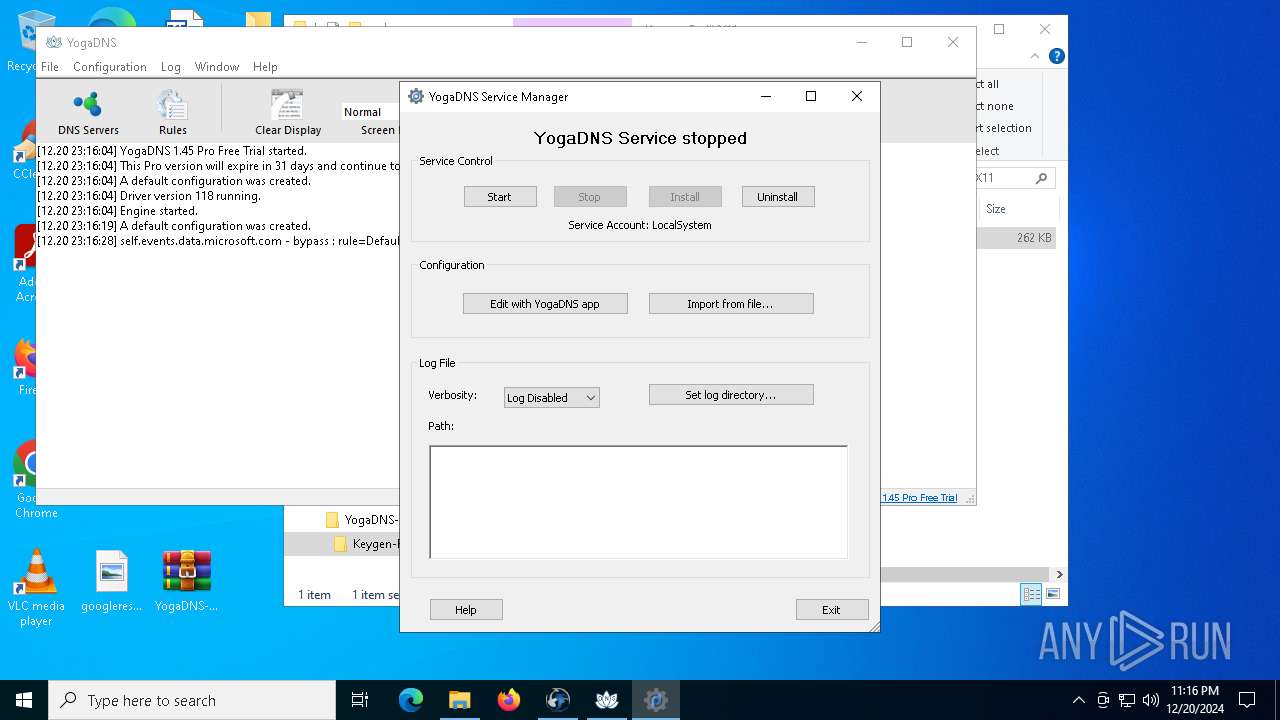
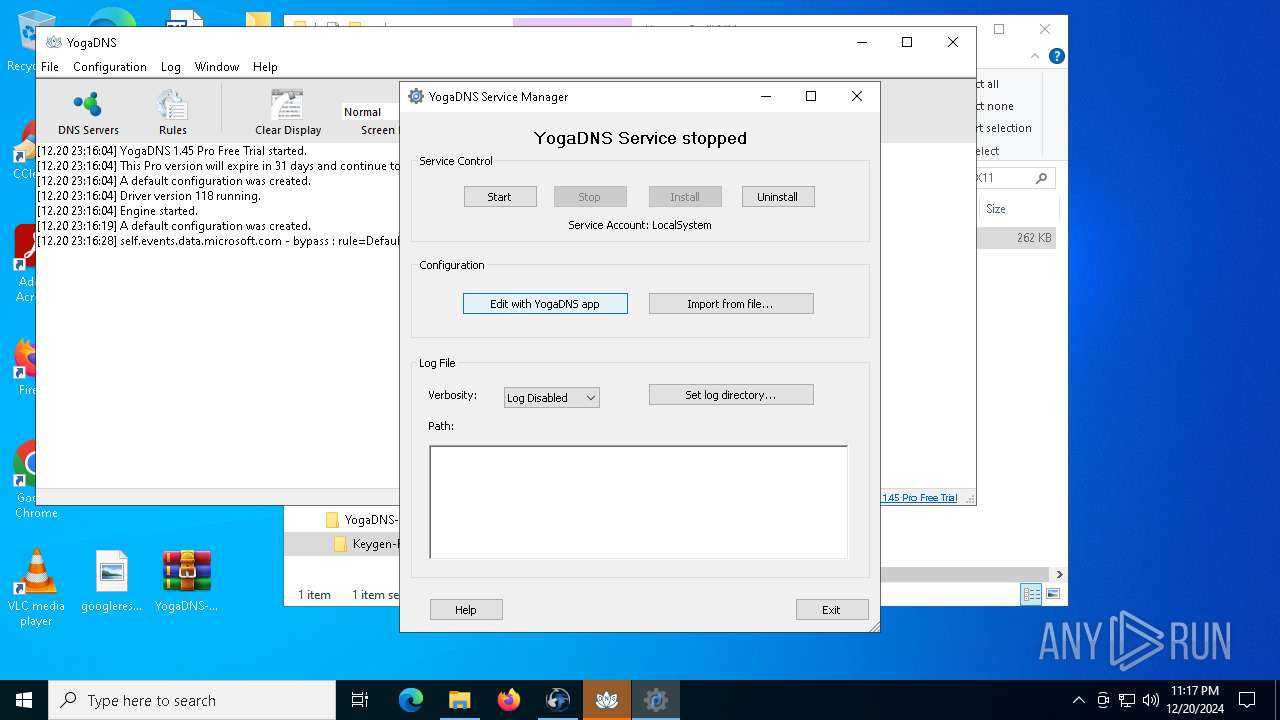
- ServiceManager.exe (PID: 6312)
Reads the Windows owner or organization settings
- YogaDNSSetup.tmp (PID: 5308)
Drops a system driver (possible attempt to evade defenses)
- YogaDNSSetup.tmp (PID: 5308)
- rundll32.exe (PID: 5244)
- drvinst.exe (PID: 3952)
- drvinst.exe (PID: 5252)
Uses RUNDLL32.EXE to load library
- YogaDNSSetup.tmp (PID: 5308)
Creates files in the driver directory
- drvinst.exe (PID: 3952)
- drvinst.exe (PID: 5252)
Checks Windows Trust Settings
- drvinst.exe (PID: 3952)
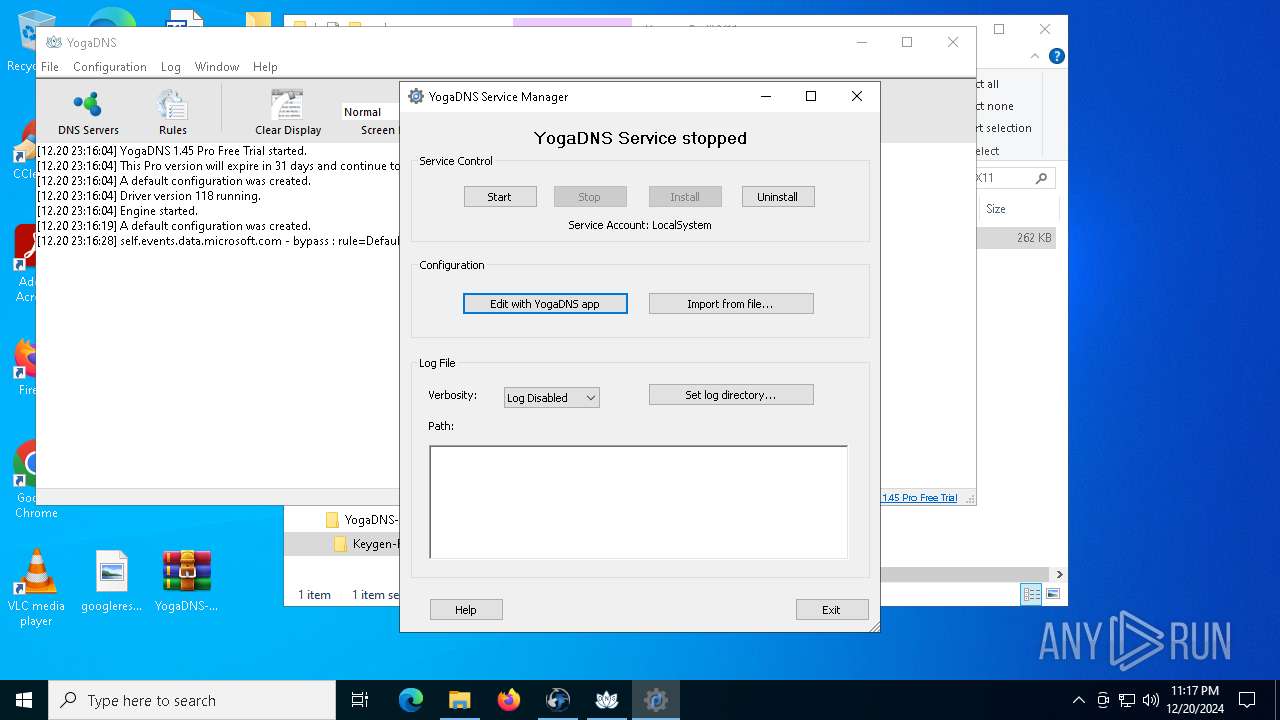
Creates or modifies Windows services
- drvinst.exe (PID: 5252)
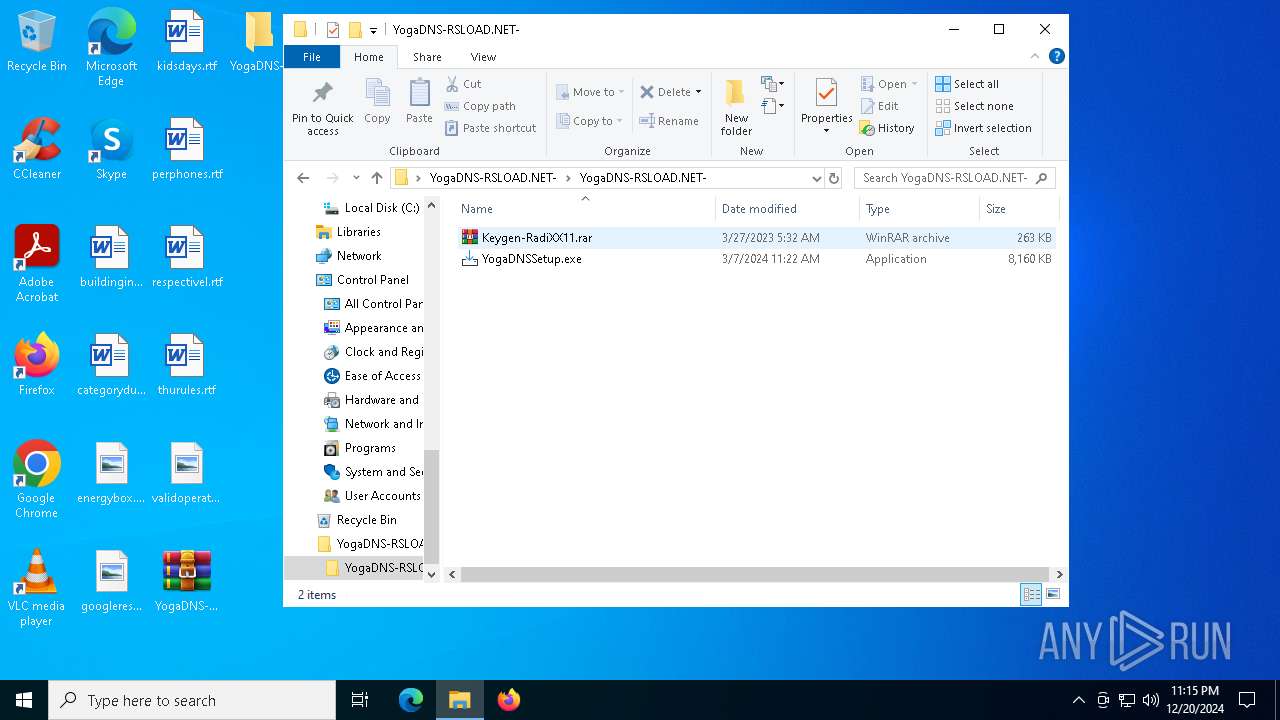
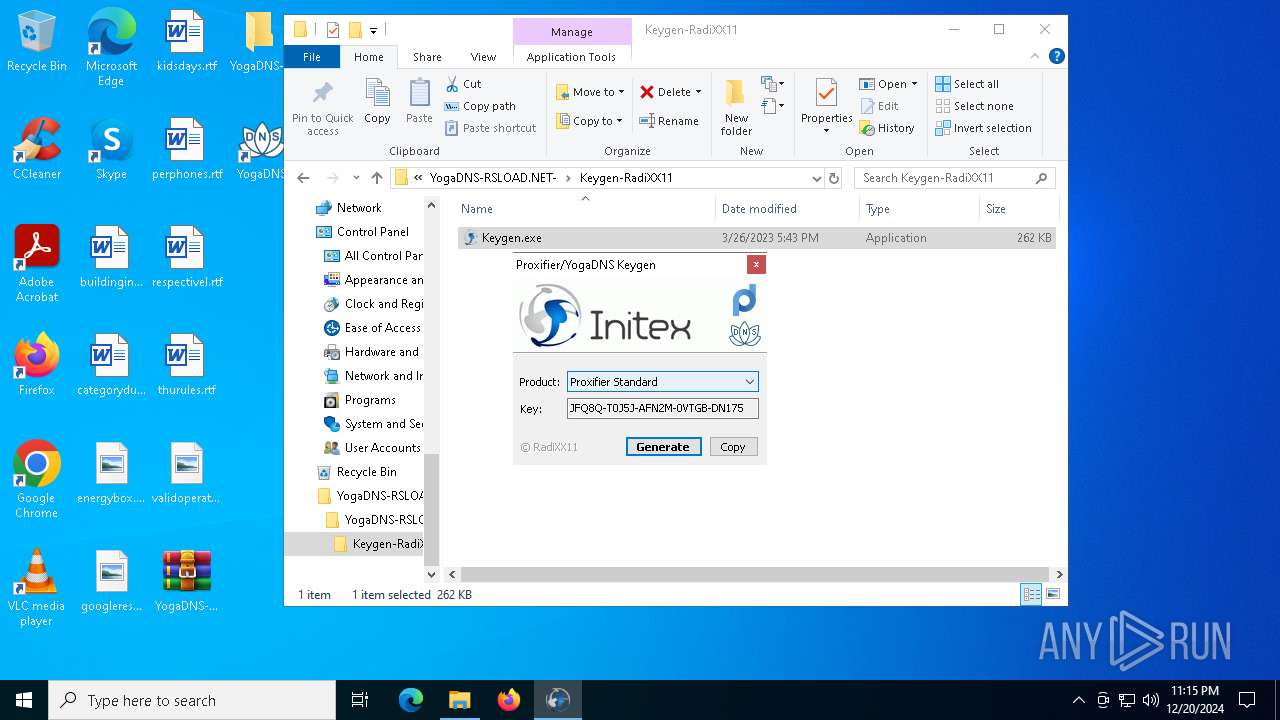
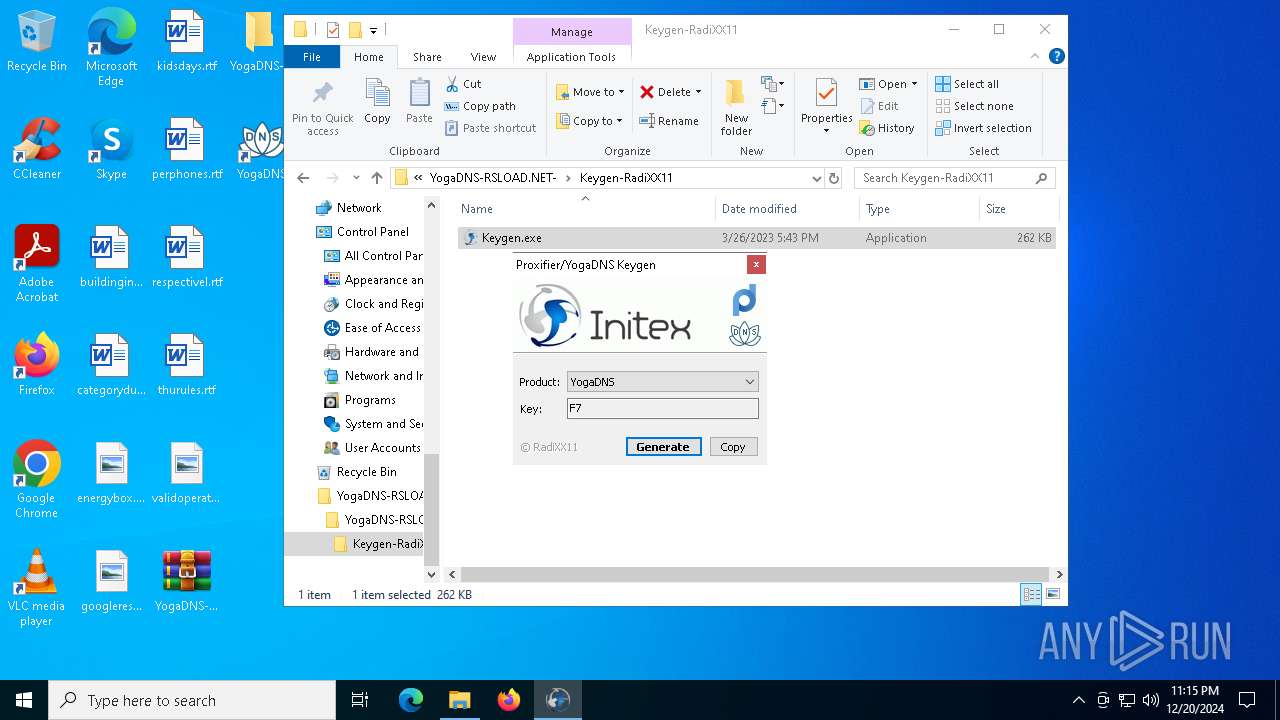
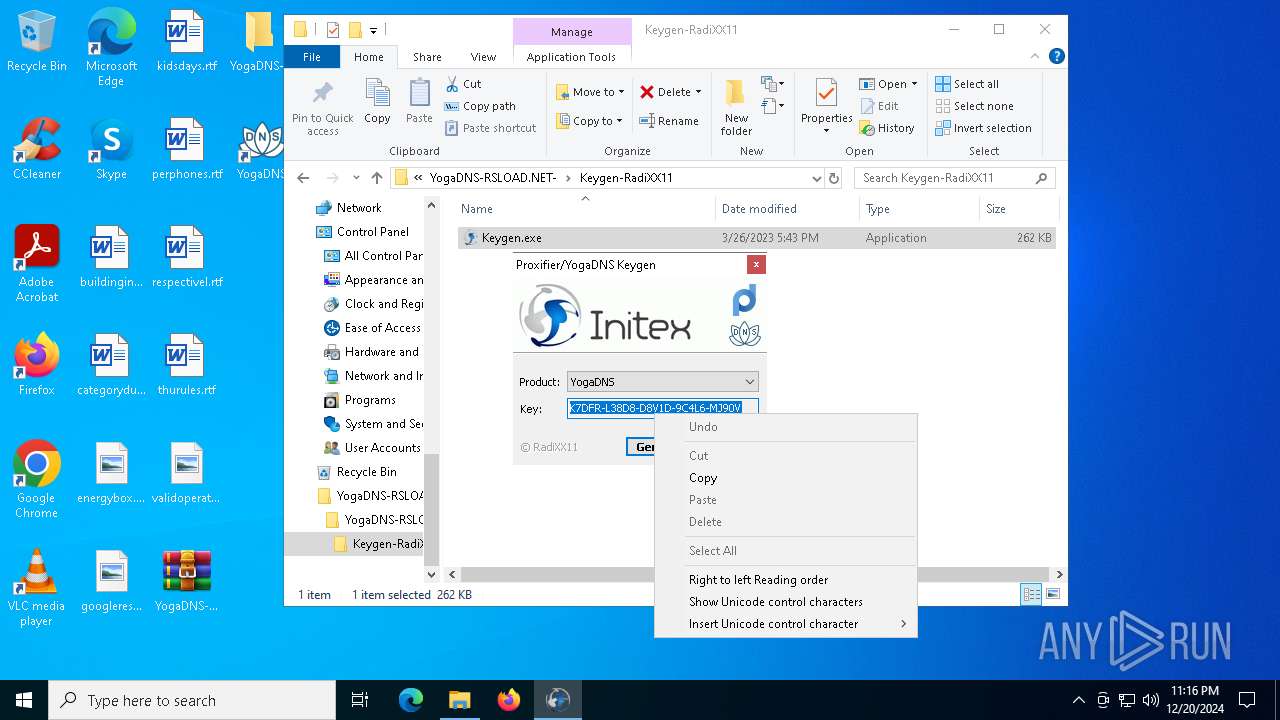
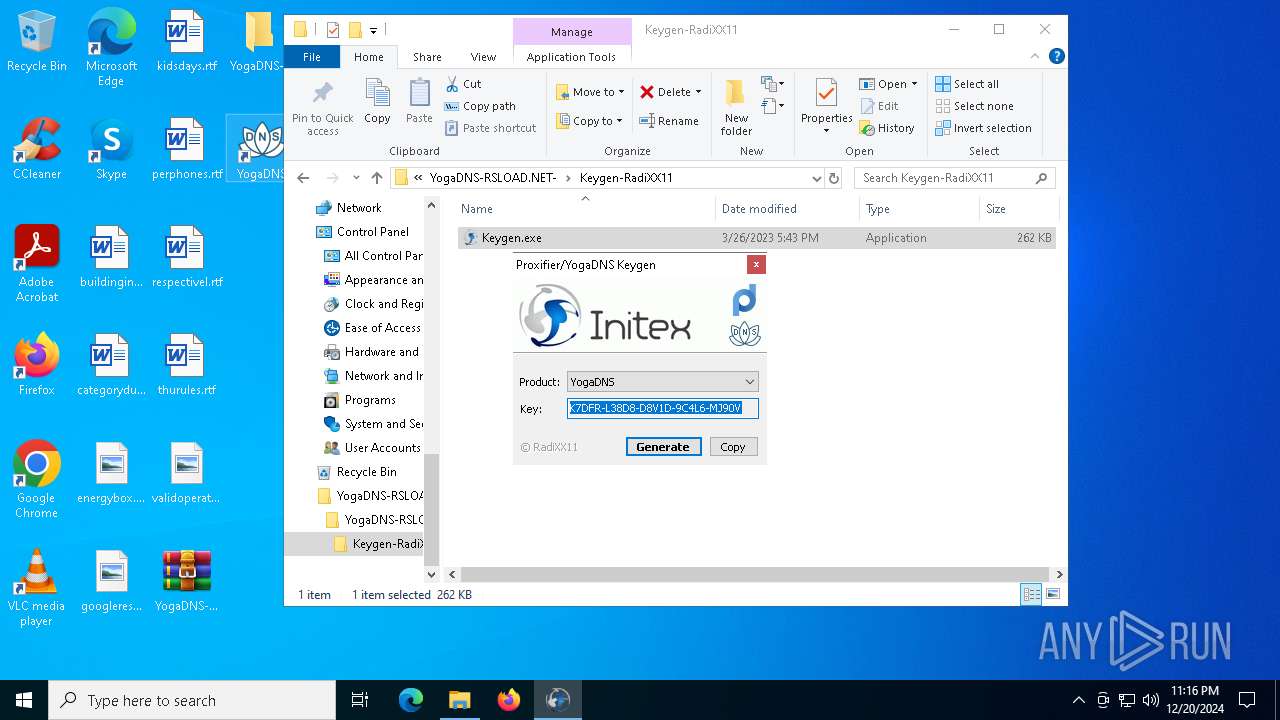
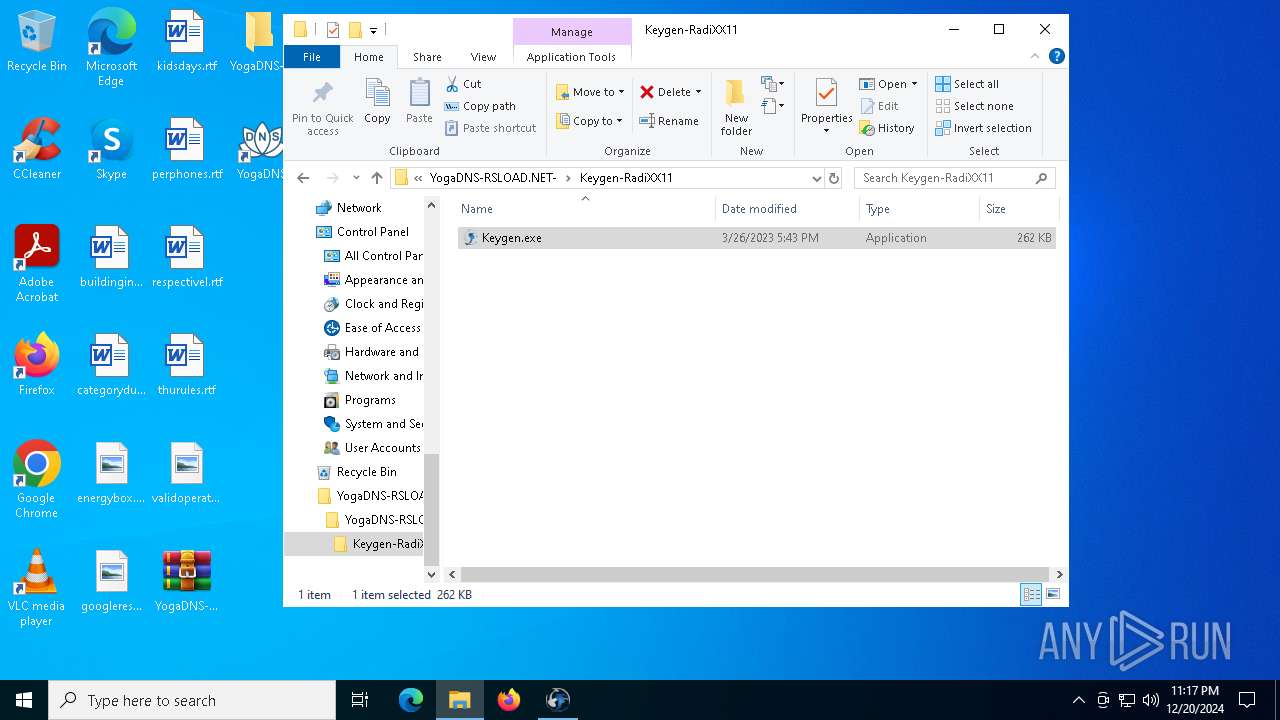
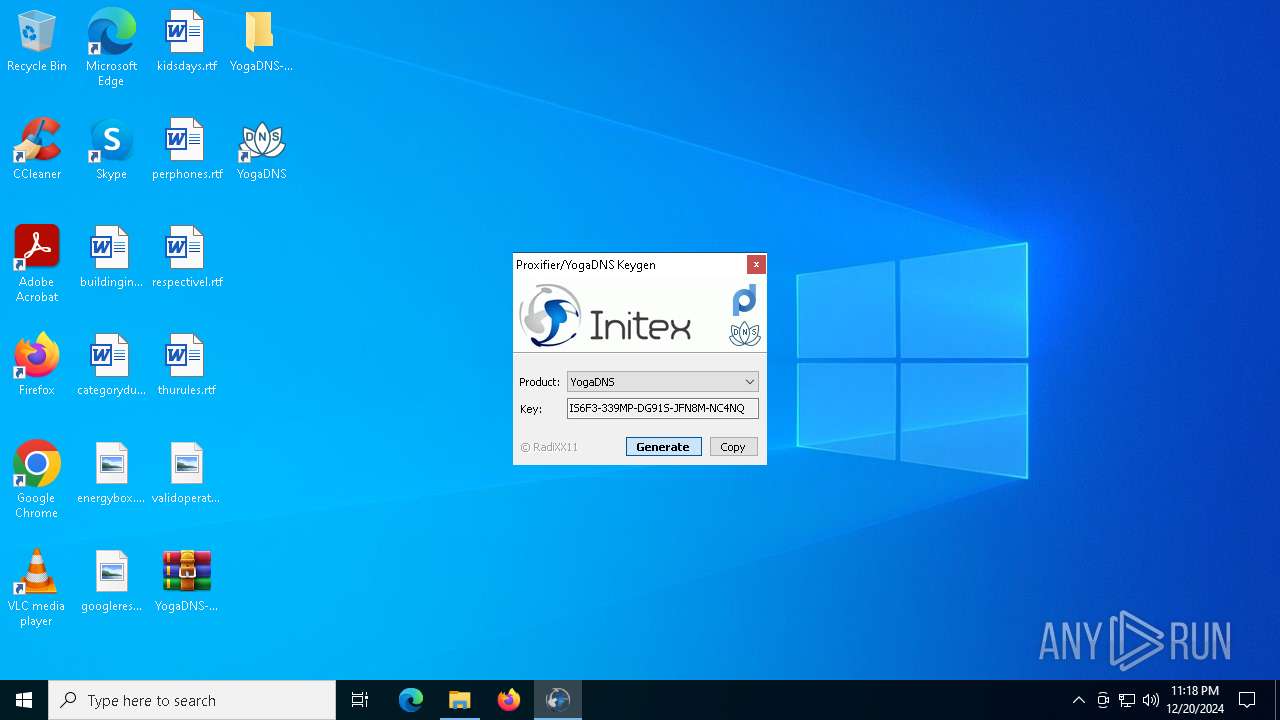
There is functionality for taking screenshot (YARA)
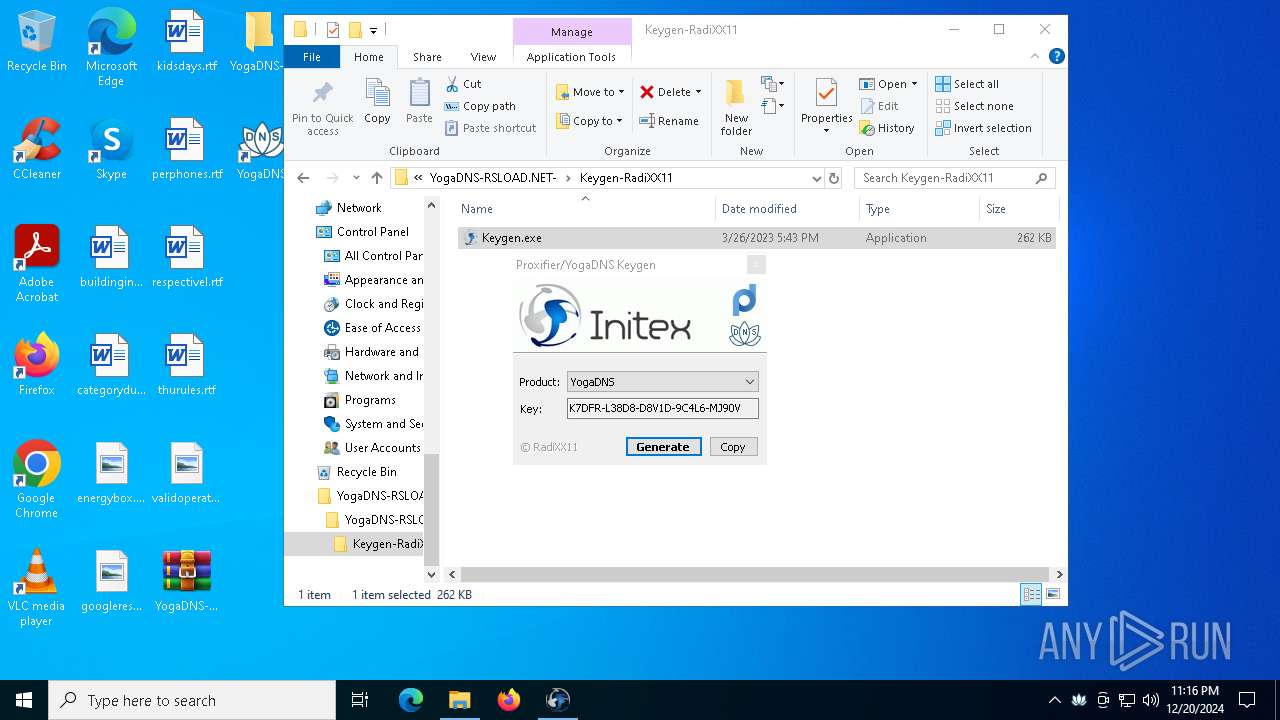
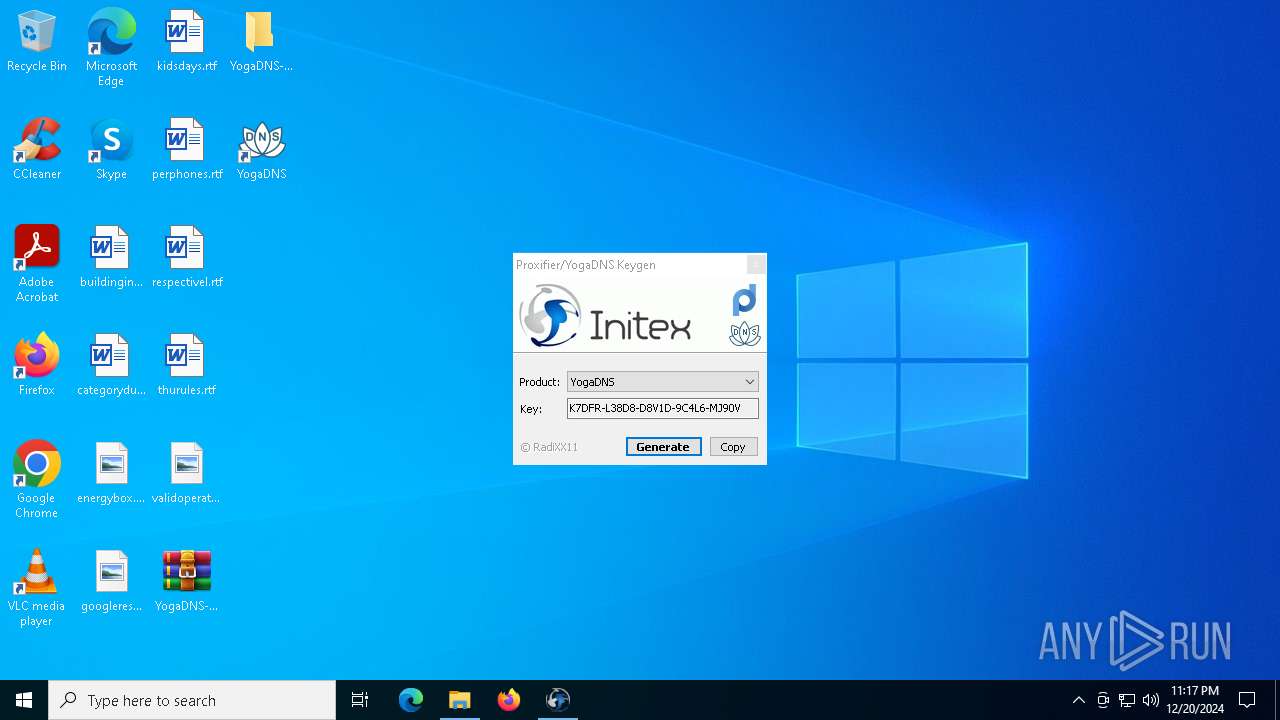
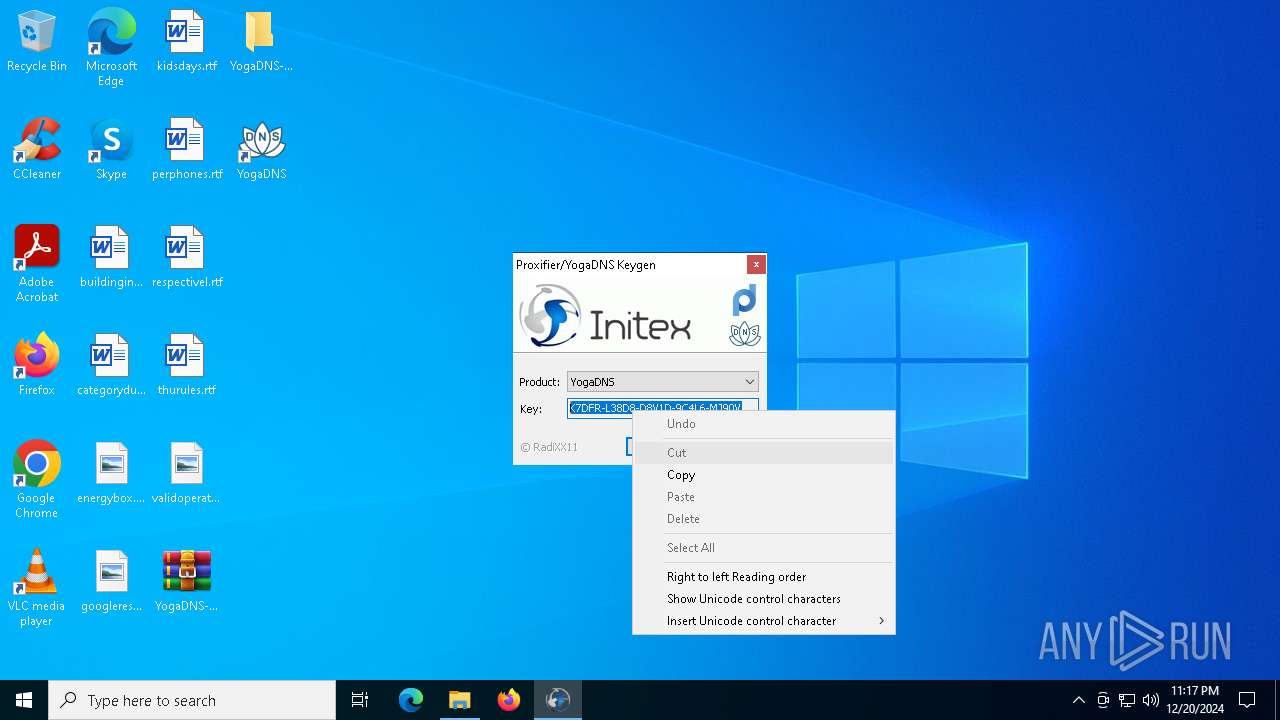
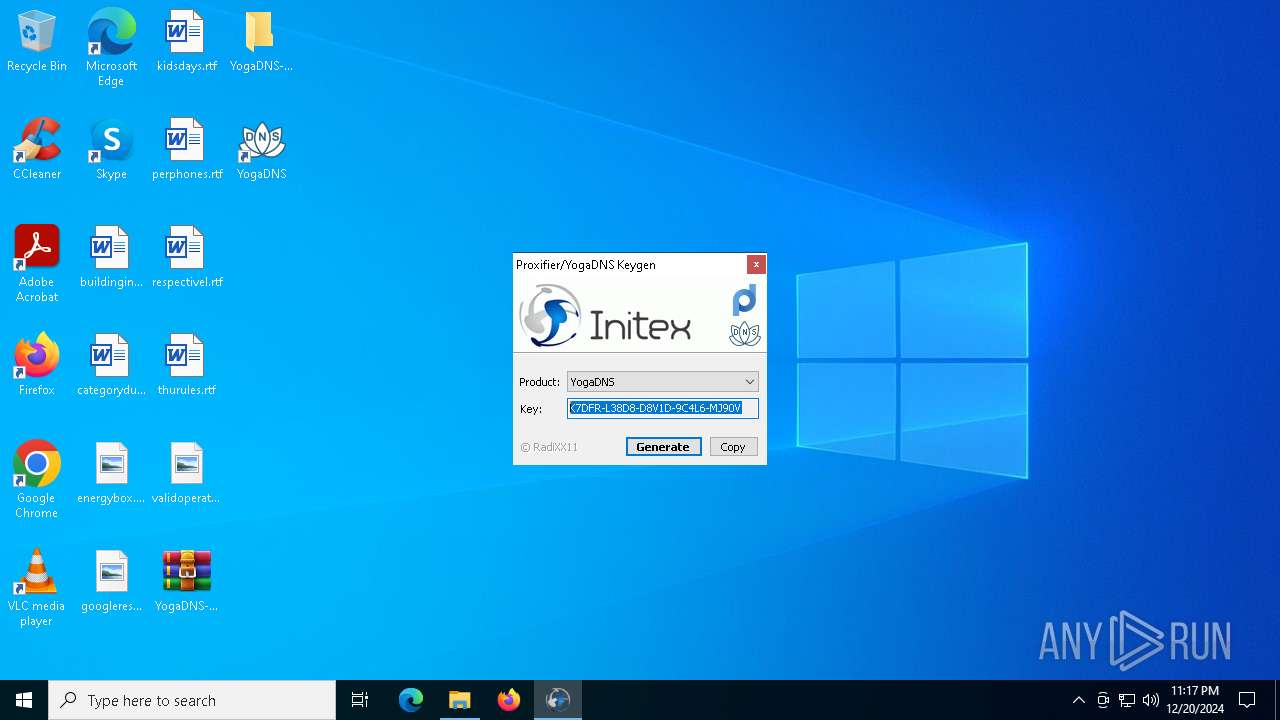
- Keygen.exe (PID: 4708)
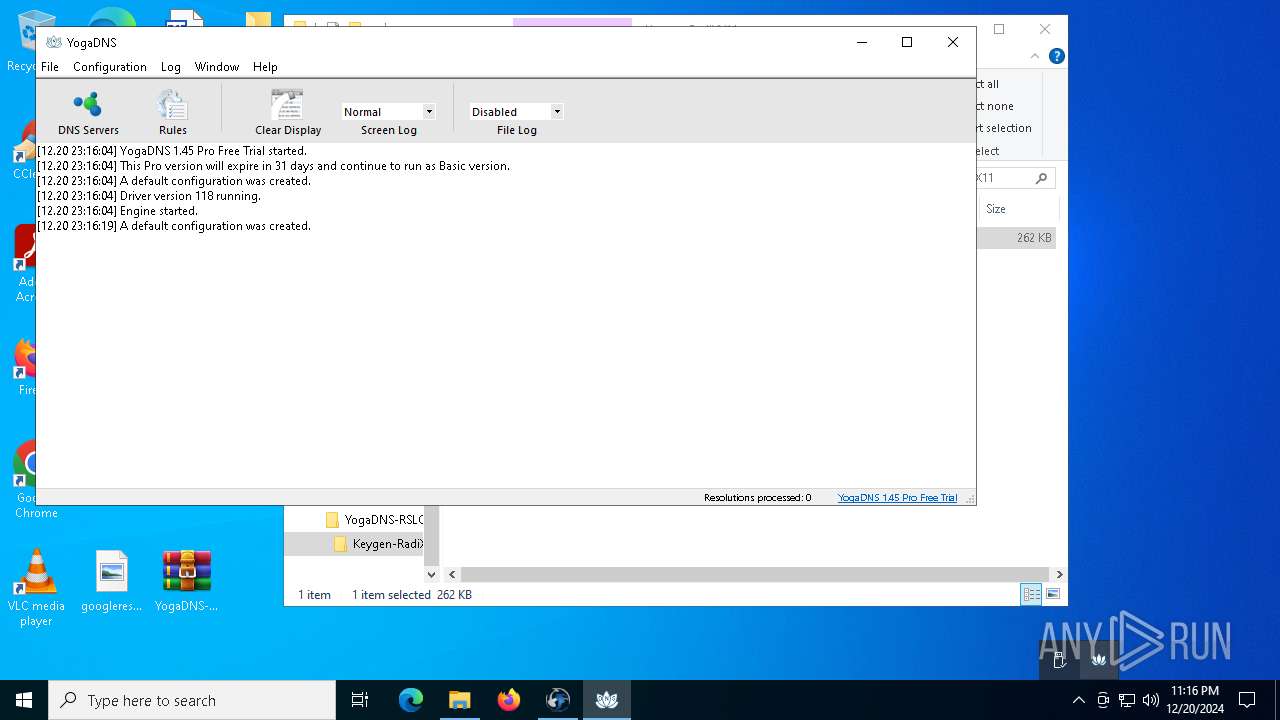
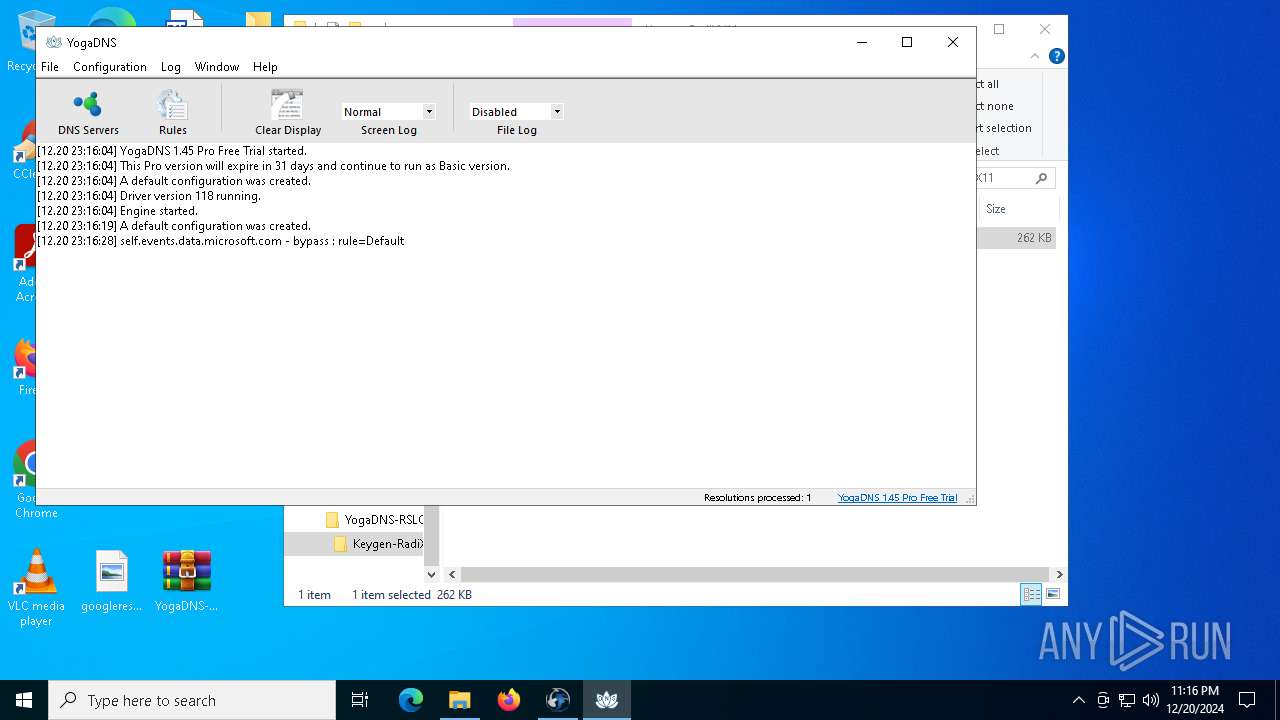
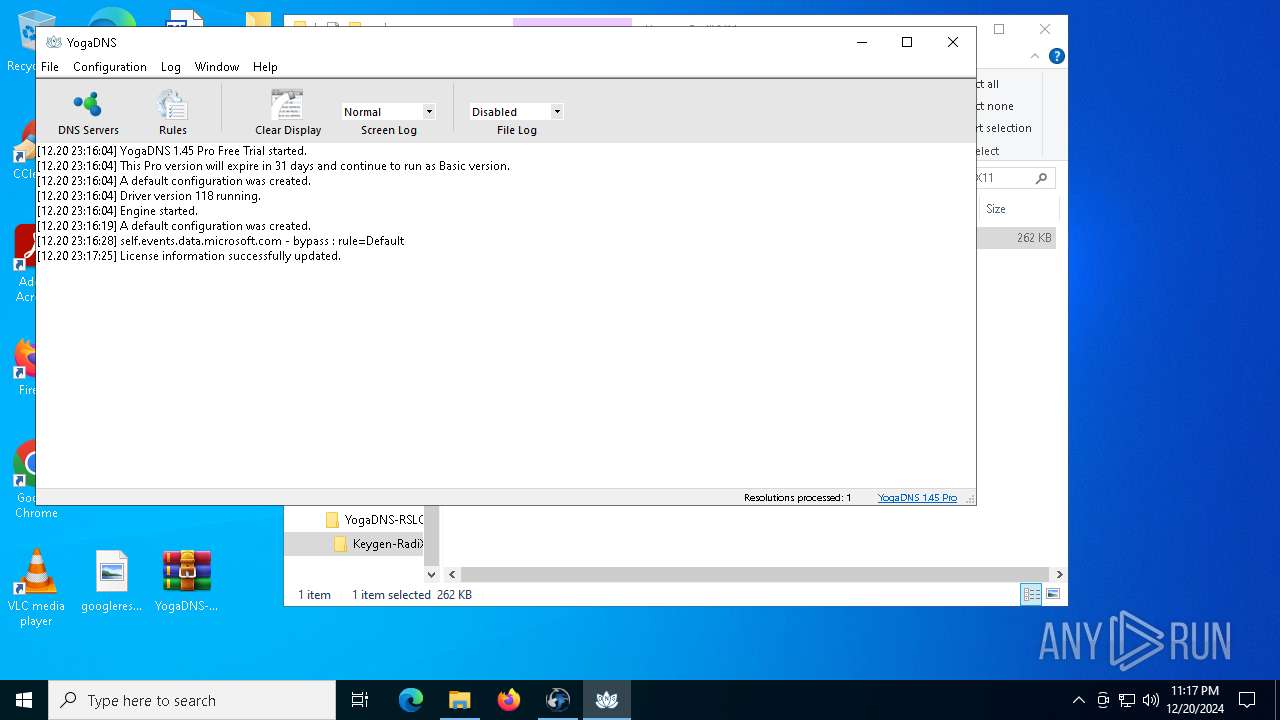
Process uses IPCONFIG to clear DNS cache
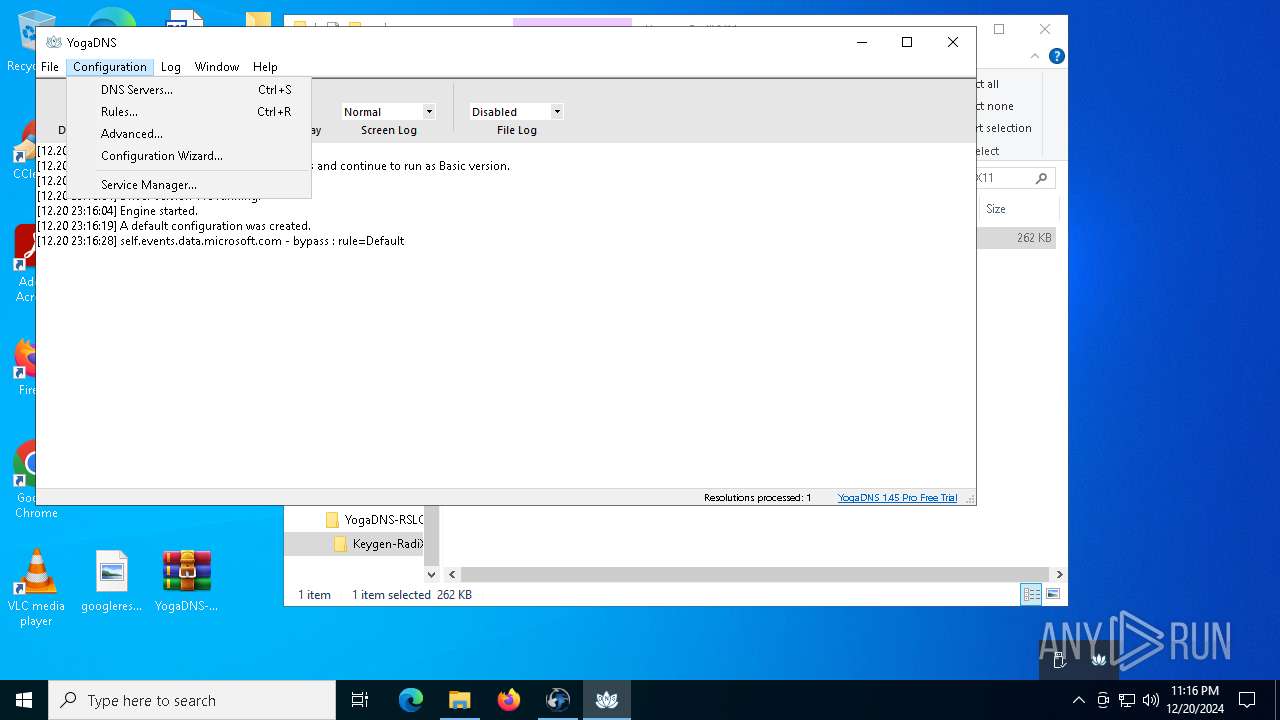
- YogaDNS.exe (PID: 6228)
Application launched itself
- YogaDNS.exe (PID: 6228)
INFO
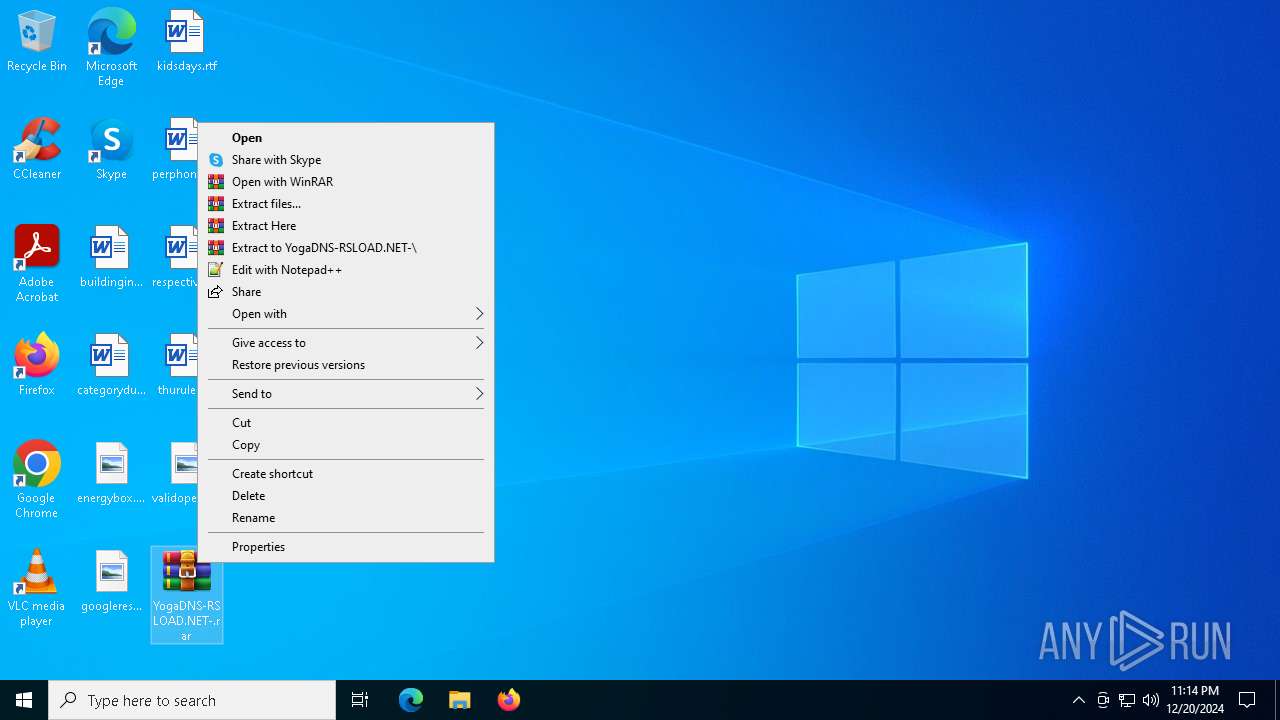
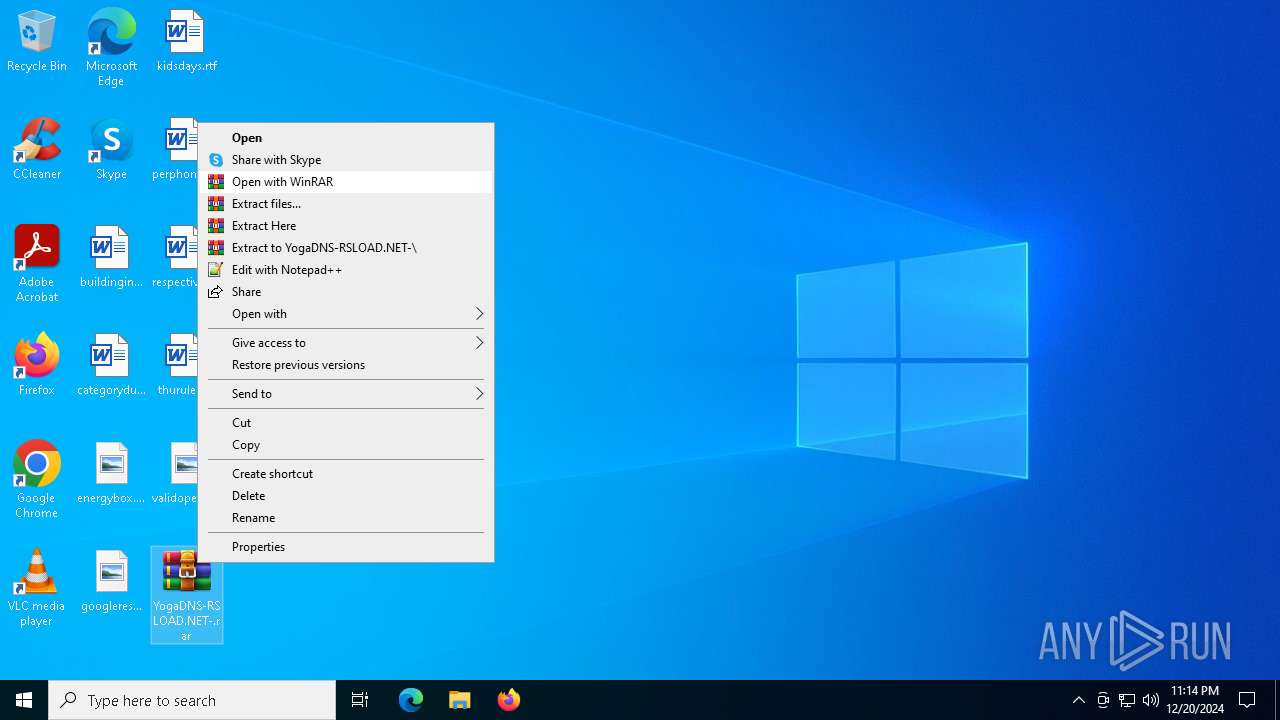
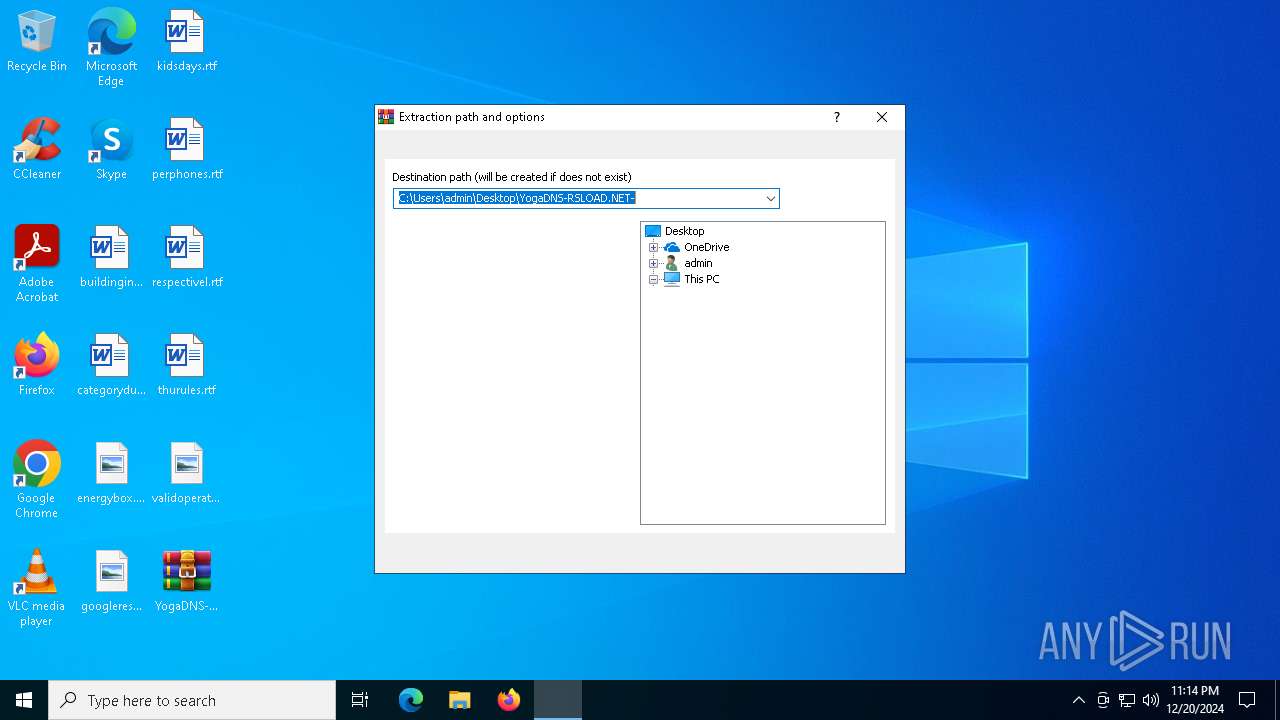
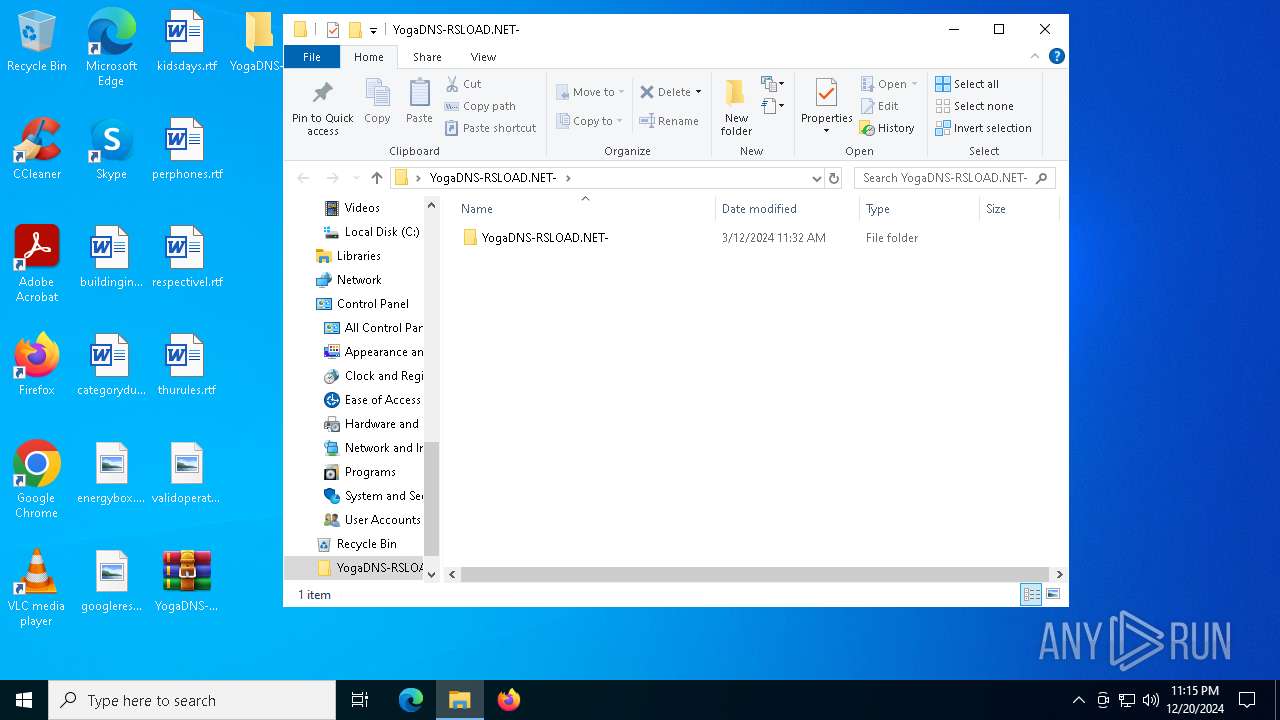
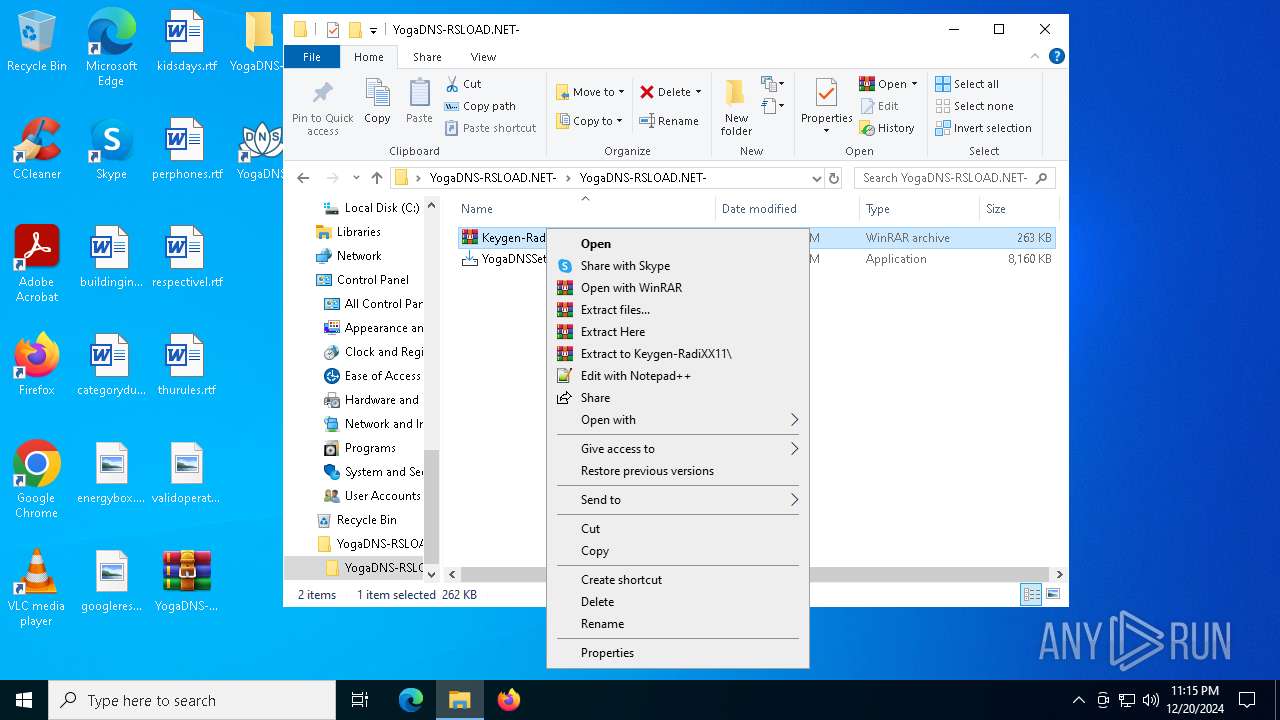
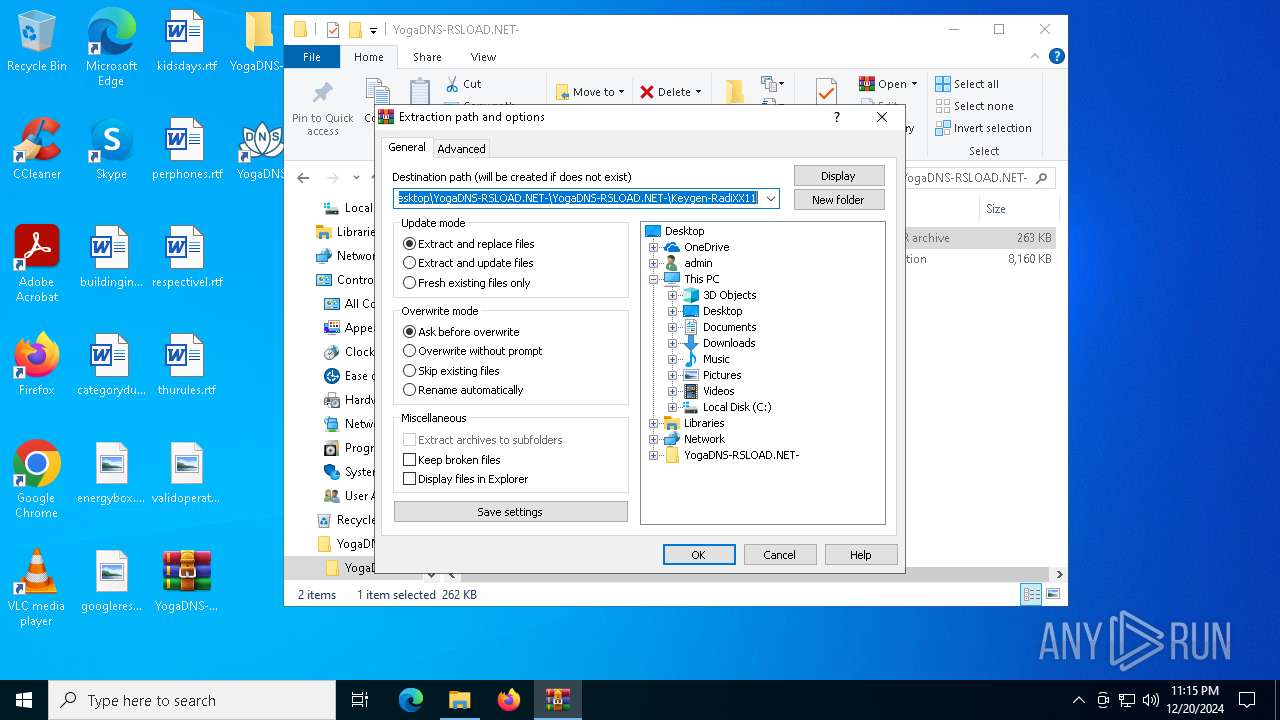
The process uses the downloaded file
- WinRAR.exe (PID: 6260)
- runonce.exe (PID: 6584)
- YogaDNS.exe (PID: 6228)
- ServiceManager.exe (PID: 6312)
- WinRAR.exe (PID: 3912)
The sample compiled with english language support
- WinRAR.exe (PID: 6260)
- YogaDNSSetup.tmp (PID: 5308)
- rundll32.exe (PID: 5244)
- drvinst.exe (PID: 3952)
- drvinst.exe (PID: 5252)
- WinRAR.exe (PID: 3912)
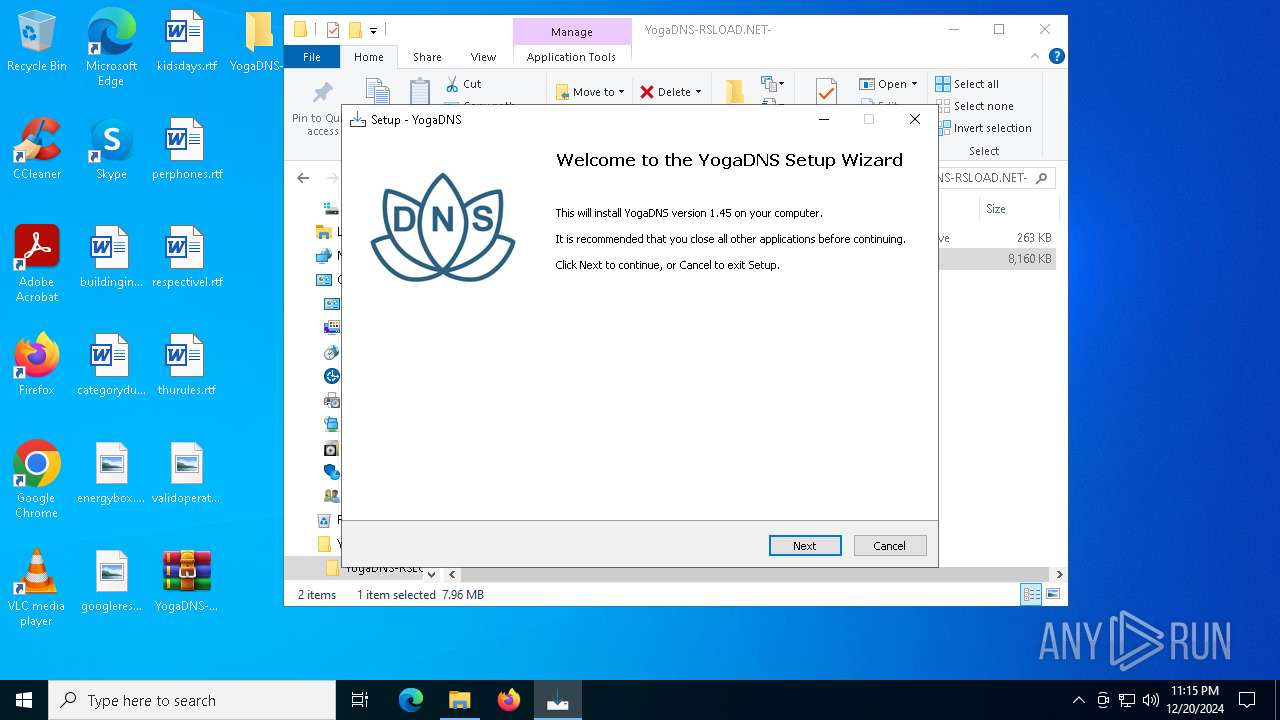
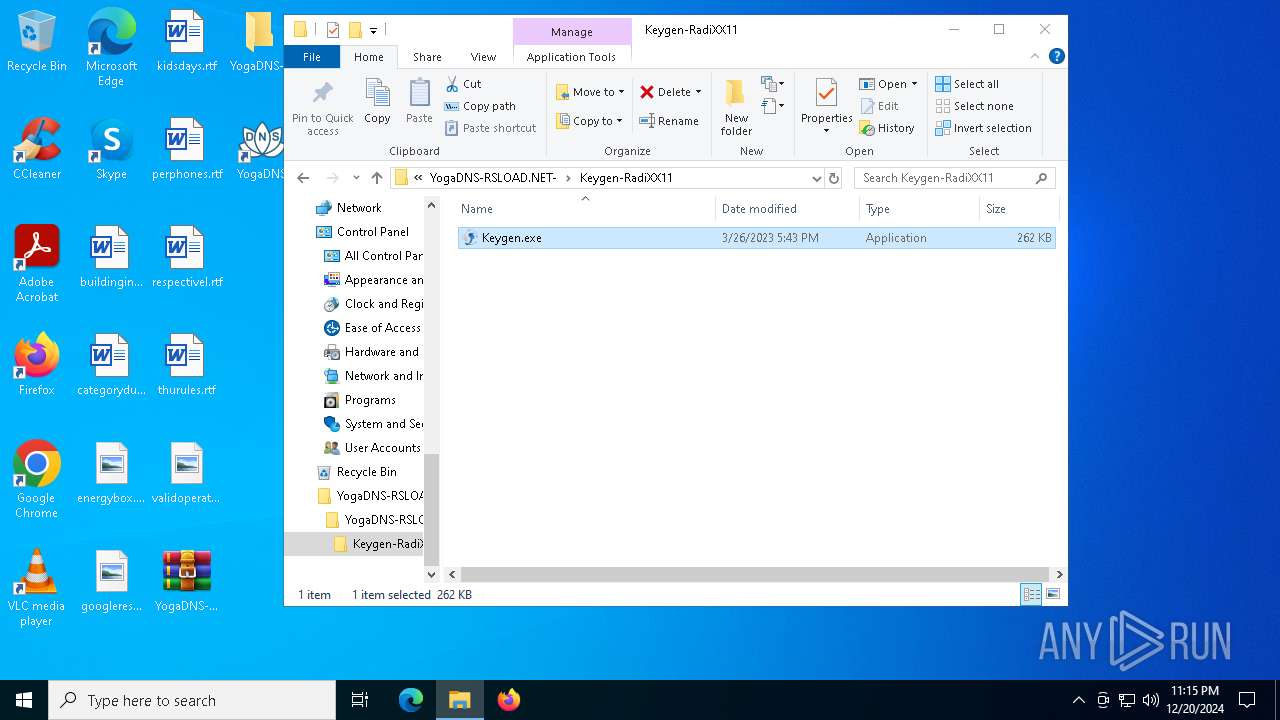
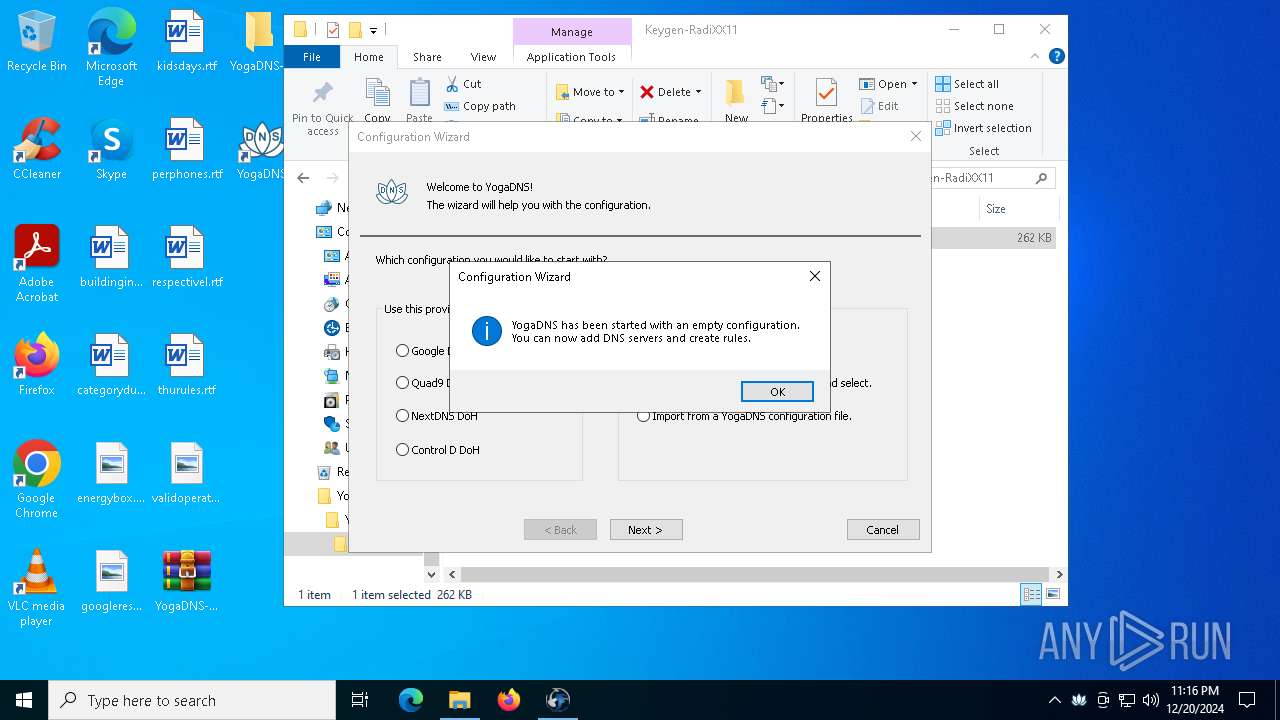
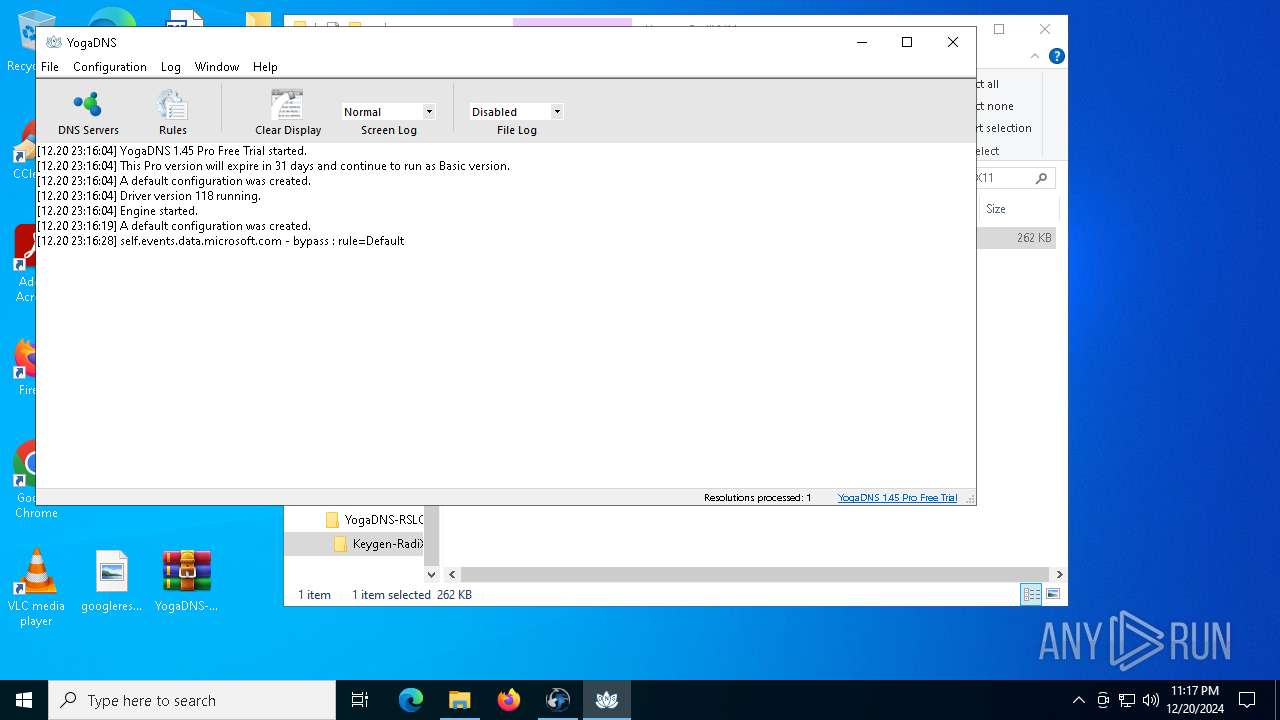
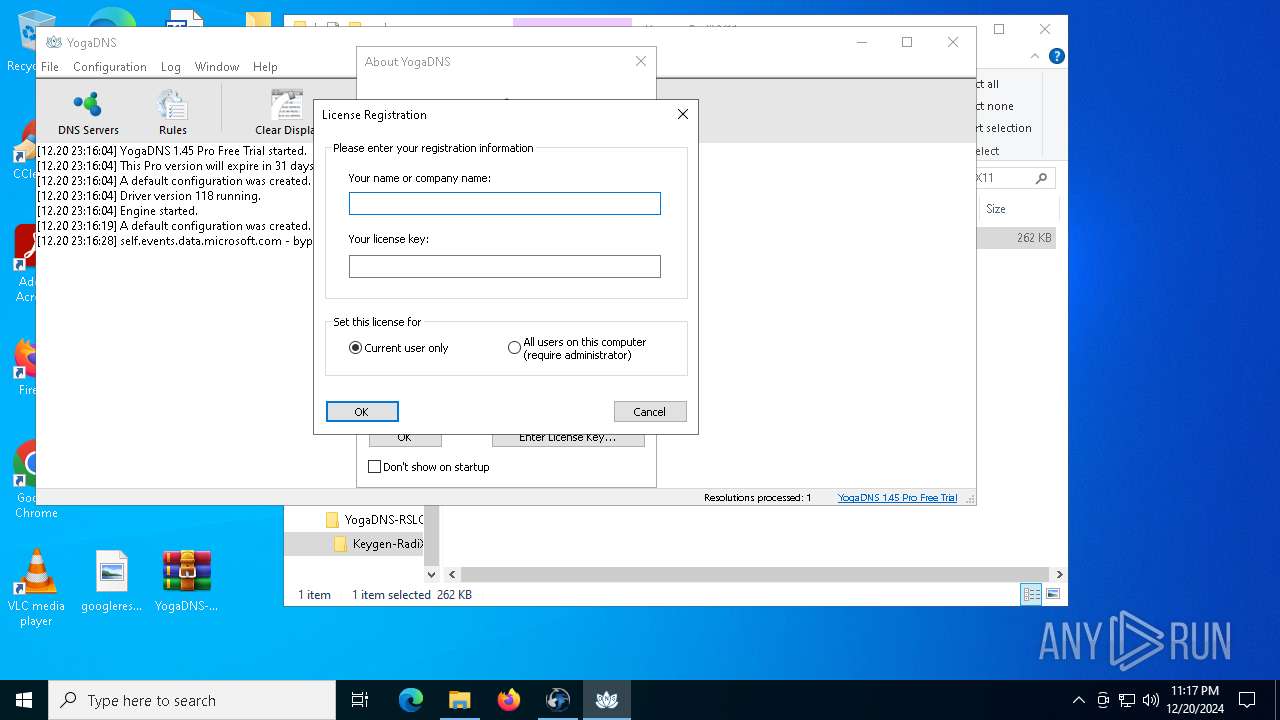
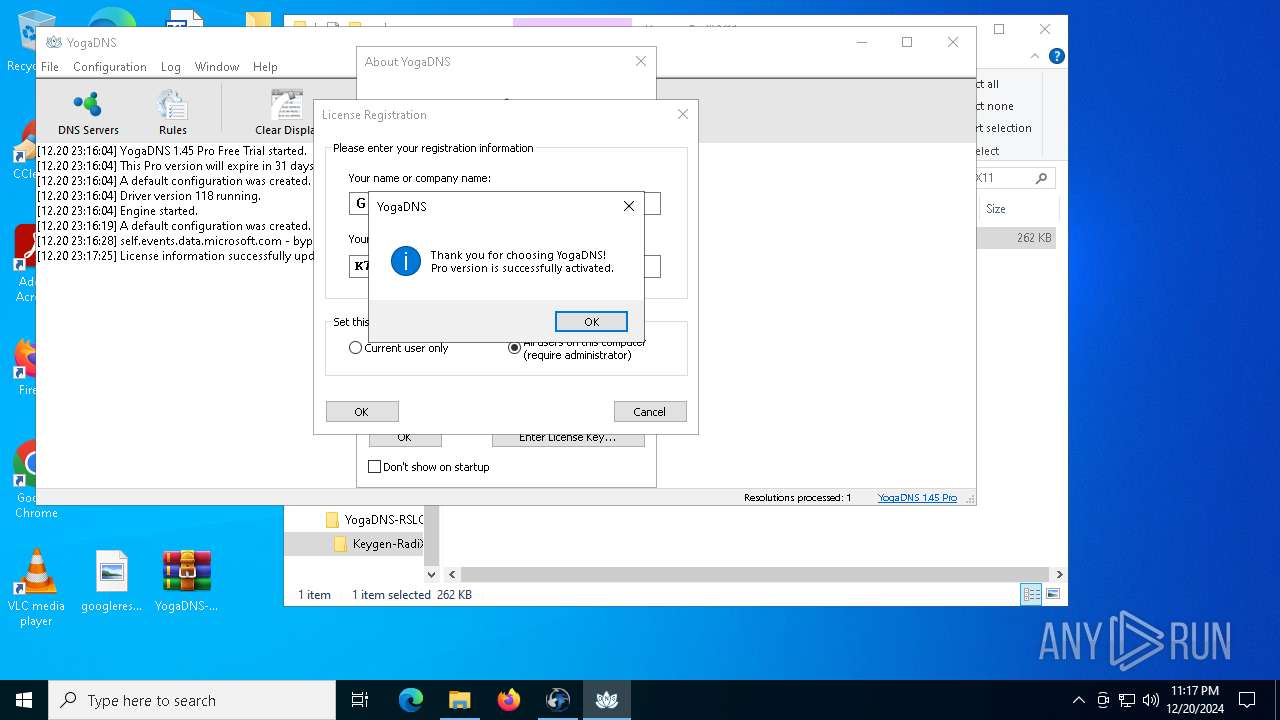
Manual execution by a user
- WinRAR.exe (PID: 6260)
- WinRAR.exe (PID: 3912)
- Keygen.exe (PID: 4708)
- YogaDNSSetup.exe (PID: 4428)
- YogaDNS.exe (PID: 6228)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6260)
- WinRAR.exe (PID: 3912)
Checks supported languages
- YogaDNSSetup.tmp (PID: 3544)
- YogaDNSSetup.exe (PID: 4428)
- YogaDNSSetup.exe (PID: 3620)
- YogaDNS.exe (PID: 5472)
- drvinst.exe (PID: 3952)
- drvinst.exe (PID: 5252)
- Keygen.exe (PID: 4708)
- YogaDNS.exe (PID: 6228)
- ServiceManager.exe (PID: 6312)
- YogaDNS.exe (PID: 6892)
- YogaDNS.exe (PID: 440)
- YogaDNSSetup.tmp (PID: 5308)
Create files in a temporary directory
- YogaDNSSetup.exe (PID: 4428)
- YogaDNSSetup.exe (PID: 3620)
- YogaDNSSetup.tmp (PID: 5308)
- rundll32.exe (PID: 5244)
Reads the computer name
- YogaDNSSetup.tmp (PID: 3544)
- YogaDNSSetup.tmp (PID: 5308)
- drvinst.exe (PID: 3952)
- drvinst.exe (PID: 5252)
- Keygen.exe (PID: 4708)
- YogaDNS.exe (PID: 6228)
- ServiceManager.exe (PID: 6312)
Process checks computer location settings
- YogaDNSSetup.tmp (PID: 3544)
- ServiceManager.exe (PID: 6312)
- YogaDNS.exe (PID: 6228)
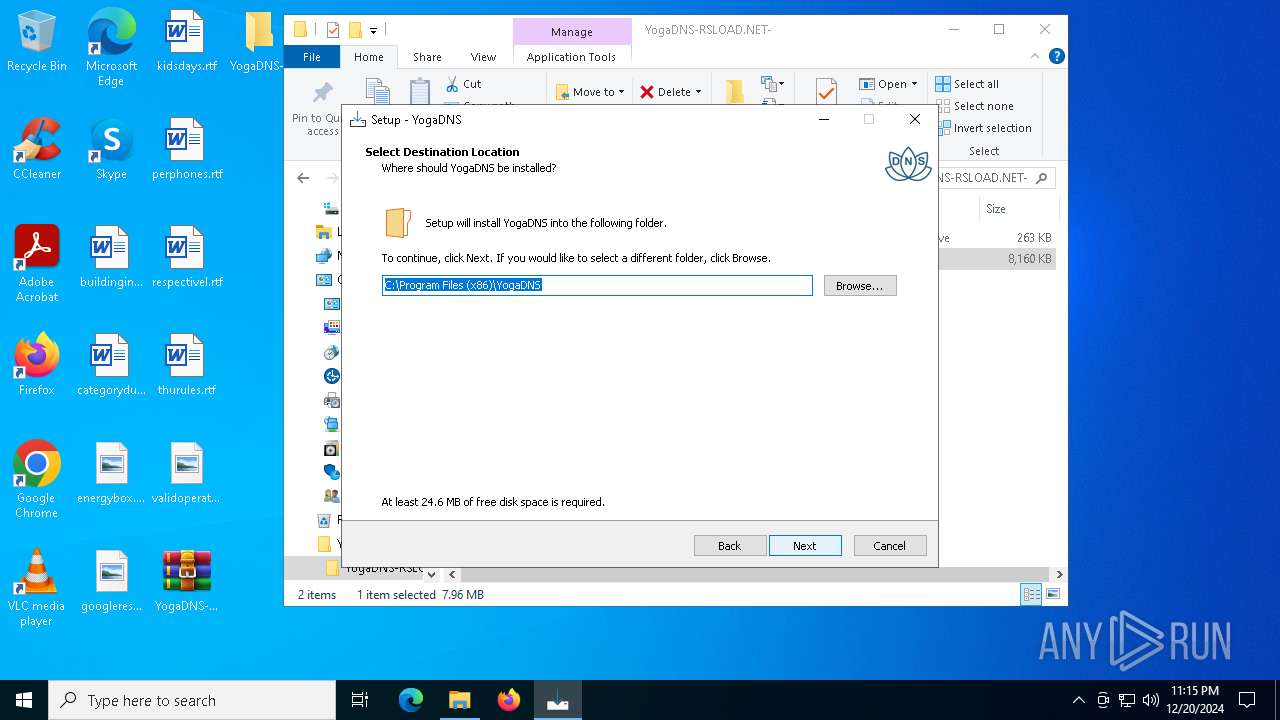
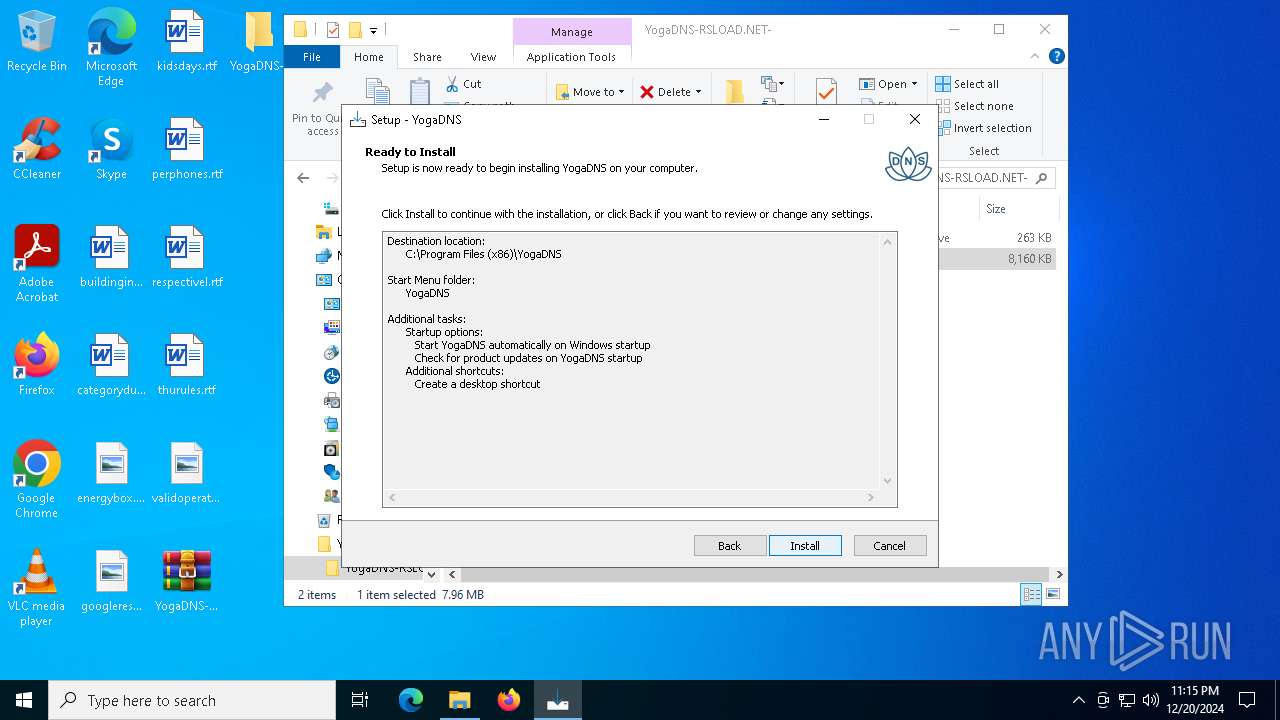
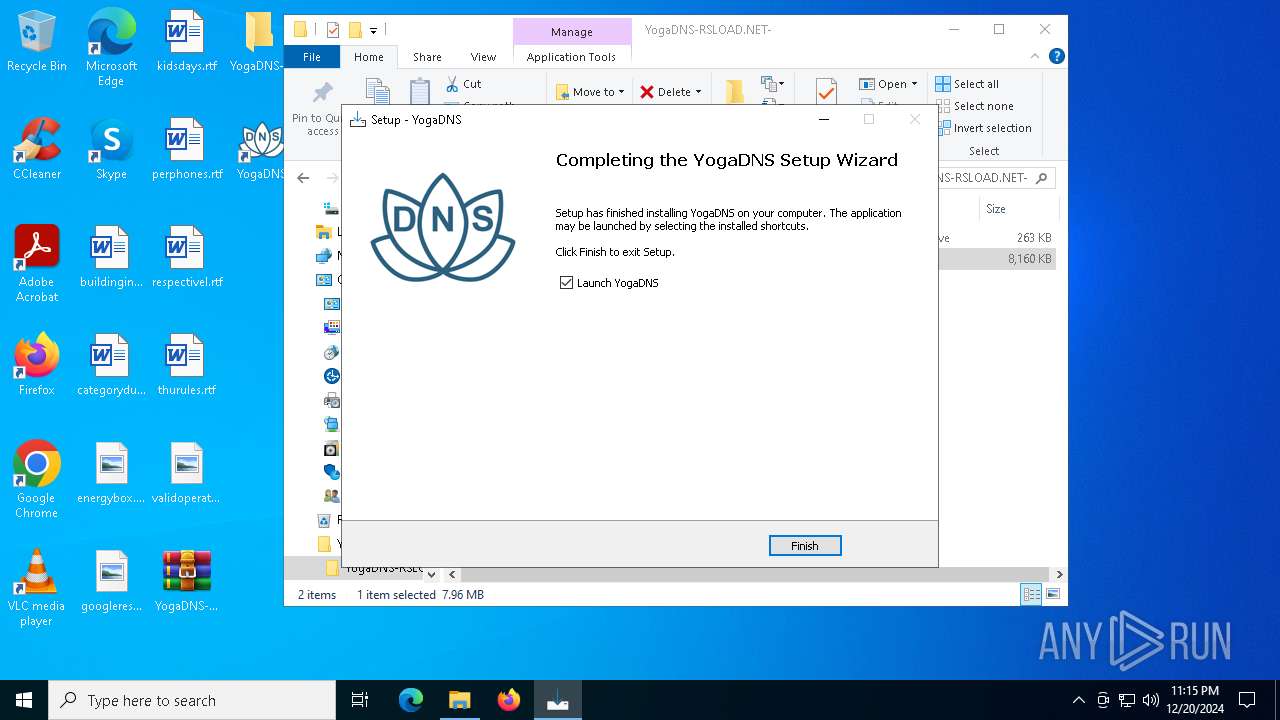
Creates a software uninstall entry
- YogaDNSSetup.tmp (PID: 5308)
Creates files in the program directory
- YogaDNSSetup.tmp (PID: 5308)
Reads the software policy settings
- drvinst.exe (PID: 3952)
Reads the machine GUID from the registry
- drvinst.exe (PID: 3952)
Reads the time zone
- runonce.exe (PID: 6584)
Reads security settings of Internet Explorer
- runonce.exe (PID: 6584)
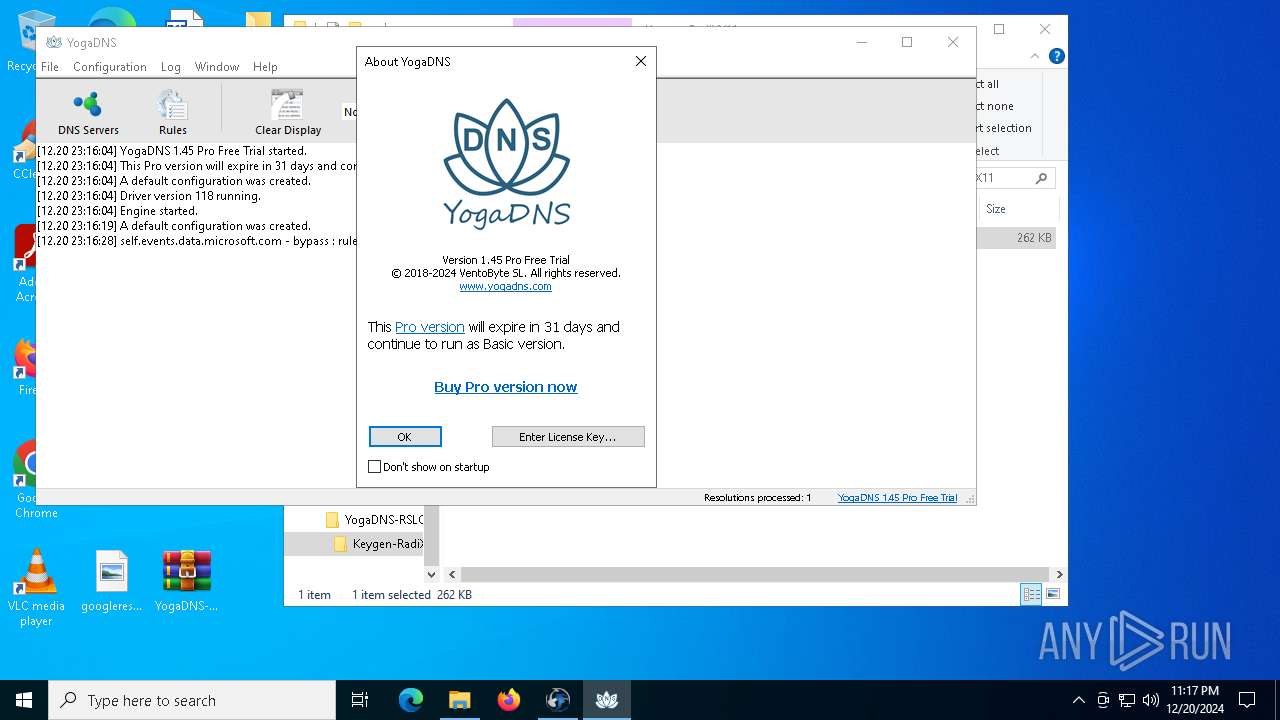
UPX packer has been detected
- Keygen.exe (PID: 4708)
Application based on Golang
- YogaDNS.exe (PID: 6228)
Creates files or folders in the user directory
- YogaDNS.exe (PID: 6228)
Disables trace logs
- YogaDNS.exe (PID: 6228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|
Total processes
156
Monitored processes
25
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files (x86)\YogaDNS\YogaDNS.exe" register K7DFR-L38D8-D8V1D-9C4L6-MJ90V G | C:\Program Files (x86)\YogaDNS\YogaDNS.exe | YogaDNS.exe | ||||||||||||
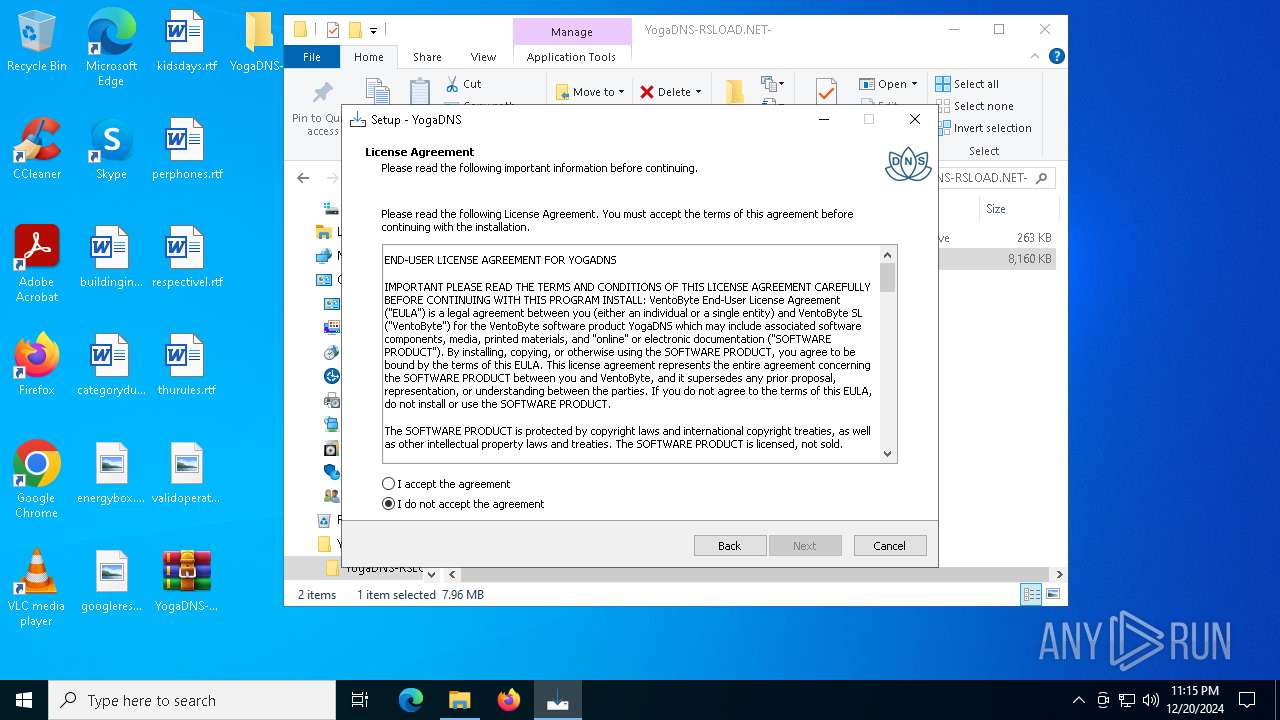
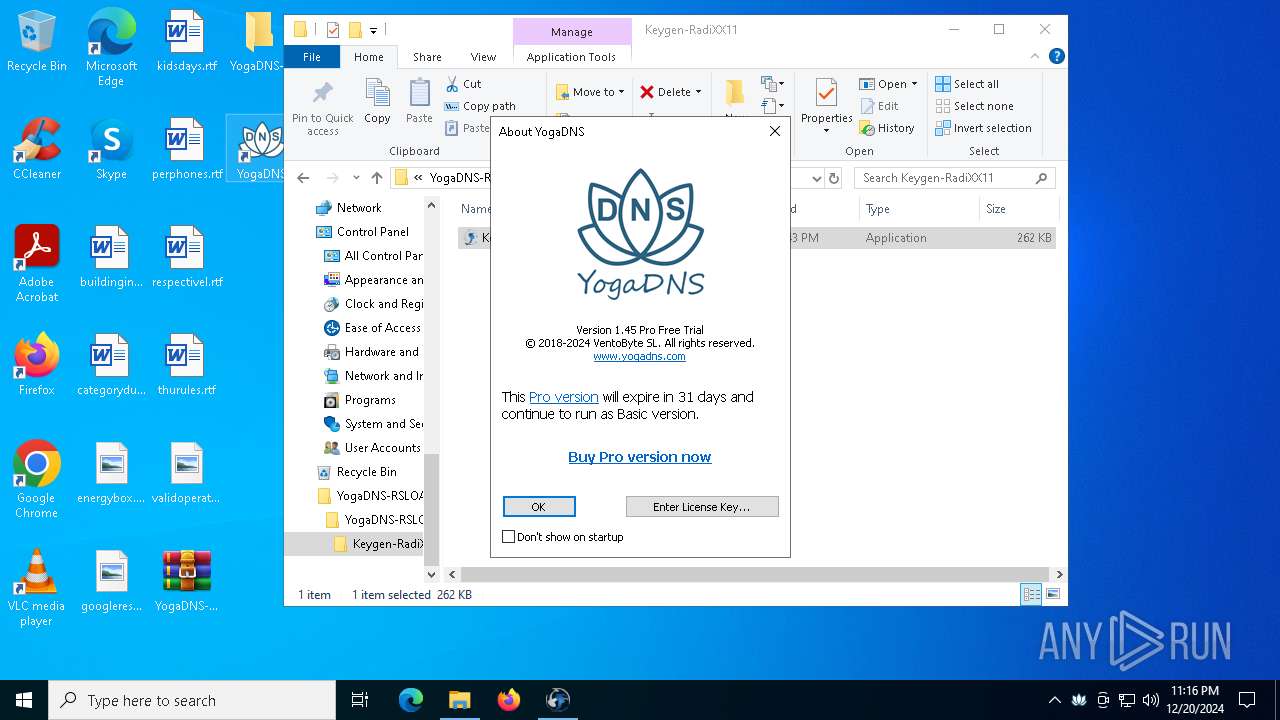
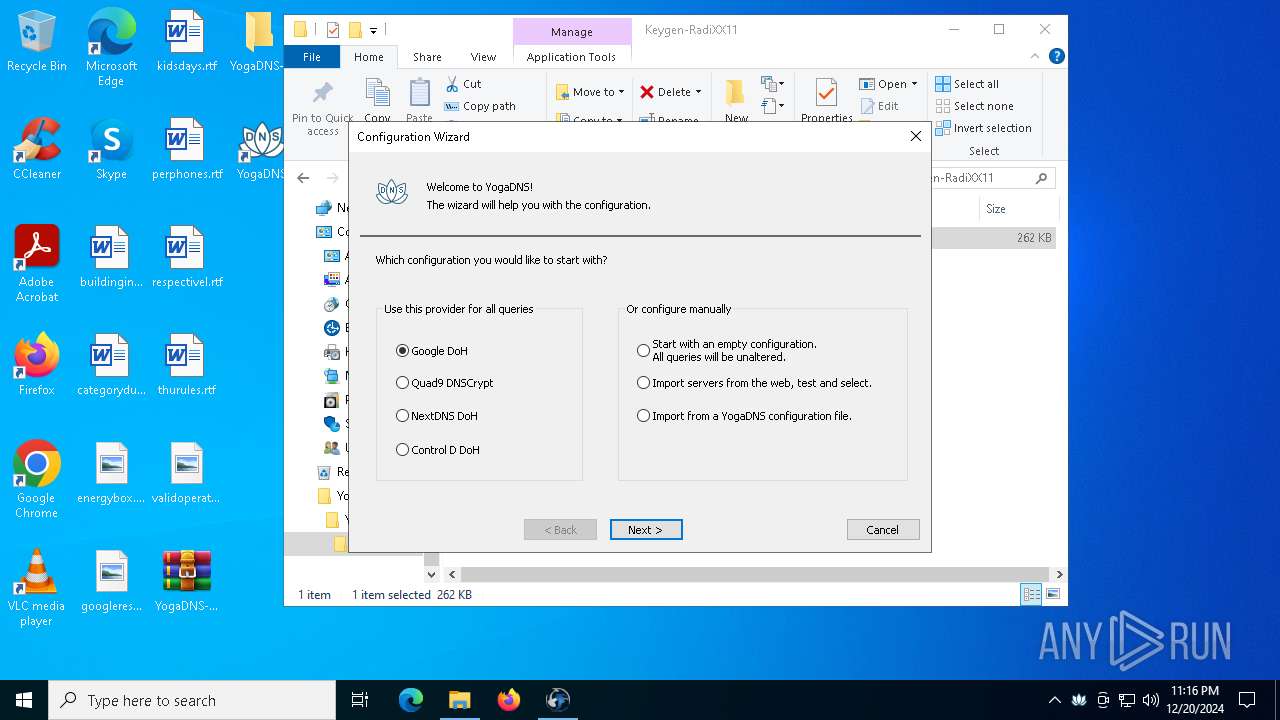
User: admin Company: VentoByte SL Integrity Level: HIGH Description: YogaDNS Exit code: 0 Version: 1.45.0.1 Modules
| |||||||||||||||
| 1544 | "C:\Program Files (x86)\YogaDNS\ServiceManager.exe" | C:\Program Files (x86)\YogaDNS\ServiceManager.exe | — | YogaDNS.exe | |||||||||||
User: admin Company: VentoByte SL Integrity Level: MEDIUM Description: YogaDNS Service Manager Exit code: 3221226540 Version: 1.2.0.1 Modules
| |||||||||||||||
| 1804 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3544 | "C:\Users\admin\AppData\Local\Temp\is-KTEAB.tmp\YogaDNSSetup.tmp" /SL5="$C02CC,7486188,831488,C:\Users\admin\Desktop\YogaDNS-RSLOAD.NET-\YogaDNS-RSLOAD.NET-\YogaDNSSetup.exe" | C:\Users\admin\AppData\Local\Temp\is-KTEAB.tmp\YogaDNSSetup.tmp | — | YogaDNSSetup.exe | |||||||||||
User: admin Company: VentoByte SL Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3564 | ipconfig /flushdns | C:\Windows\SysWOW64\ipconfig.exe | — | YogaDNS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3620 | "C:\Users\admin\Desktop\YogaDNS-RSLOAD.NET-\YogaDNS-RSLOAD.NET-\YogaDNSSetup.exe" /SPAWNWND=$20252 /NOTIFYWND=$C02CC | C:\Users\admin\Desktop\YogaDNS-RSLOAD.NET-\YogaDNS-RSLOAD.NET-\YogaDNSSetup.exe | YogaDNSSetup.tmp | ||||||||||||
User: admin Company: VentoByte SL Integrity Level: HIGH Description: YogaDNS Setup Exit code: 0 Version: 1.45.0.1 Modules
| |||||||||||||||
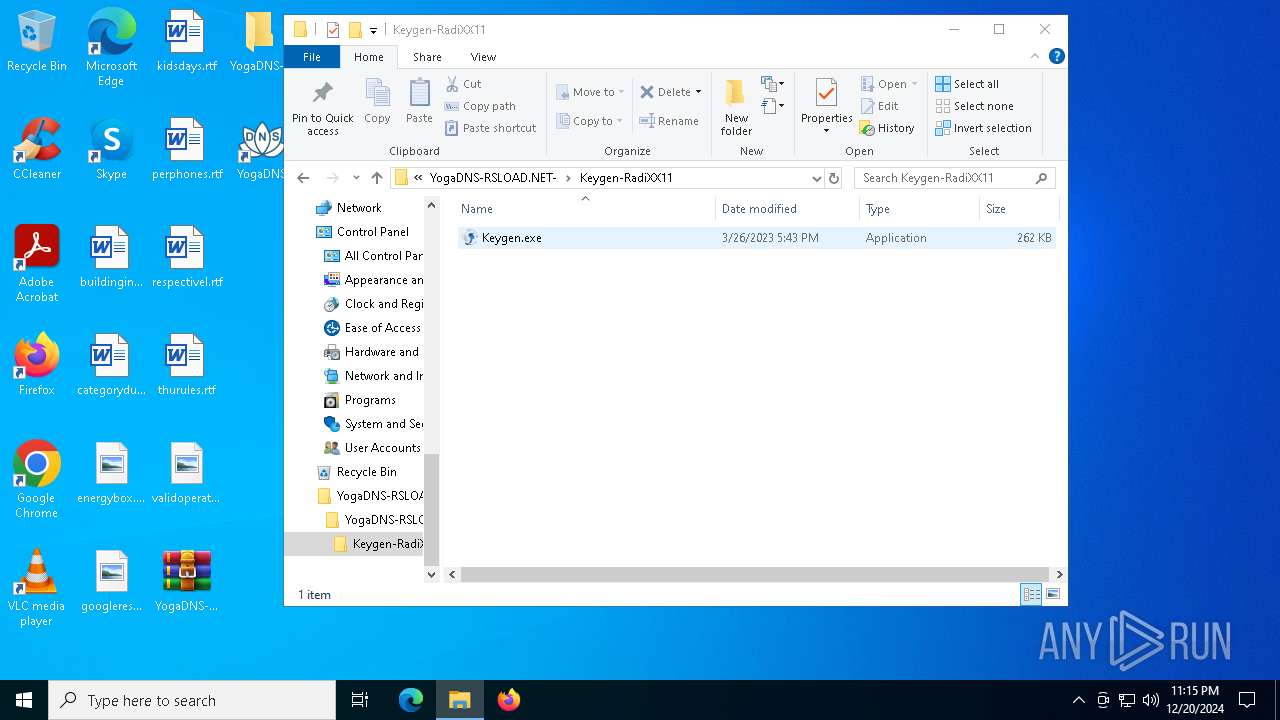
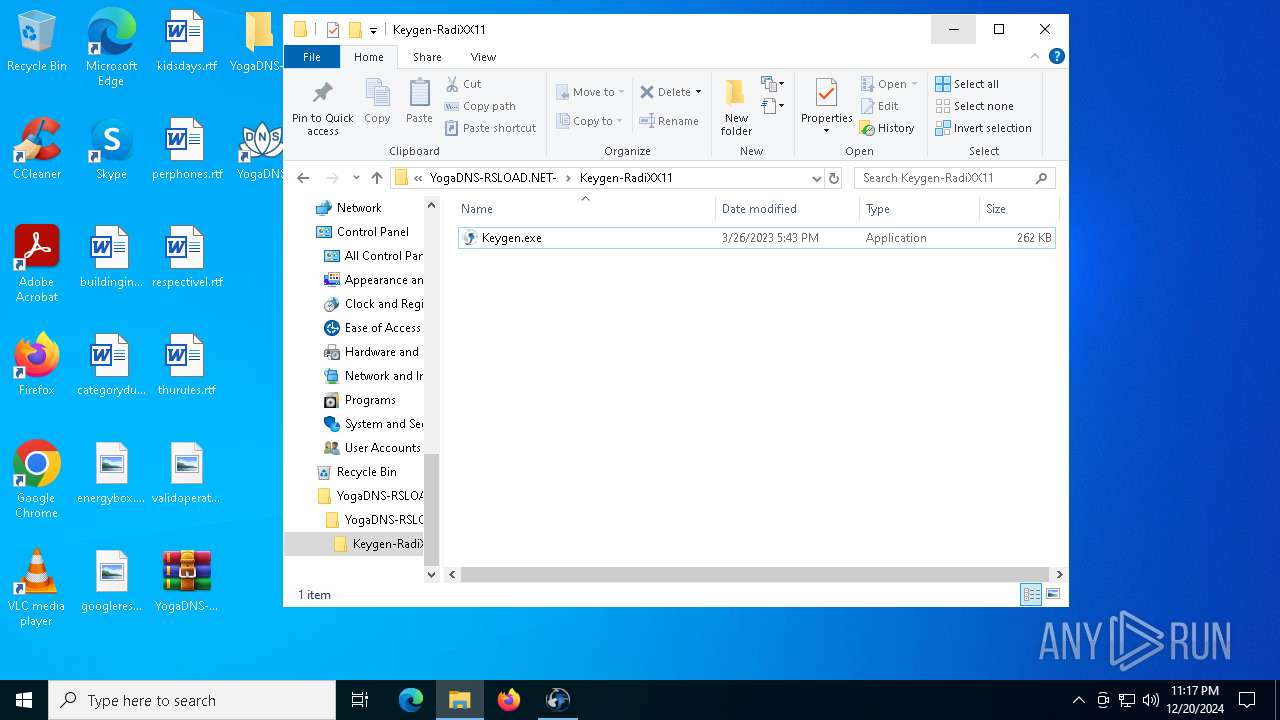
| 3912 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\YogaDNS-RSLOAD.NET-\YogaDNS-RSLOAD.NET-\Keygen-RadiXX11.rar" "?\" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3952 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{db040509-ad53-0543-bab1-e5f4531fbcad}\DnsFltEngineDrv.inf" "9" "48ceef827" "0000000000000174" "WinSta0\Default" "00000000000001DC" "208" "C:\Program Files (x86)\YogaDNS\Driver" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4400 | C:\WINDOWS\system32\net1 stop DnsFltEngineDrv | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4428 | "C:\Users\admin\Desktop\YogaDNS-RSLOAD.NET-\YogaDNS-RSLOAD.NET-\YogaDNSSetup.exe" | C:\Users\admin\Desktop\YogaDNS-RSLOAD.NET-\YogaDNS-RSLOAD.NET-\YogaDNSSetup.exe | explorer.exe | ||||||||||||
User: admin Company: VentoByte SL Integrity Level: MEDIUM Description: YogaDNS Setup Exit code: 0 Version: 1.45.0.1 Modules
| |||||||||||||||
Total events
9 940
Read events
9 840
Write events
73
Delete events
27
Modification events
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_0 |
Value: 4C000000730100000402000000000000F0F0F0000000000000000000000000000000000000000000EC02050000000000000000003B000000B402000000000000000000000000000001000000 | |||
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_1 |
Value: 4C000000730100000500000000000000F0F0F0000000000000000000000000000000000000000000EE0204000000000000000000180000002A00000000000000000000000000000002000000 | |||
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_2 |
Value: 4C000000730100000400000000000000F0F0F0000000000000000000000000000000000000000000E00105000000000000000000180000006400000000000000000000000000000003000000 | |||
| (PID) Process: | (6260) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6260) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (6260) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
Executable files
22
Suspicious files
21
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5308 | YogaDNSSetup.tmp | C:\Program Files (x86)\YogaDNS\dnscrypt.dll | executable | |
MD5:C5BB8D06E0C031F269D70150B946EE70 | SHA256:20E2E8084C111215D4AA5A0666CAFAF56431E15553267C5D018B26AD4EA8081D | |||
| 5308 | YogaDNSSetup.tmp | C:\Program Files (x86)\YogaDNS\is-8PNC5.tmp | executable | |
MD5:9A918EA79F21EDEA6046BB11EC0F94B9 | SHA256:78ACC8F6748ED579E0CBE4DE2EC748561363F49BB614587AFDDABDD4351FE843 | |||
| 5308 | YogaDNSSetup.tmp | C:\Program Files (x86)\YogaDNS\dnscrypt-proxy.toml | text | |
MD5:63425B993E903CA712124B3E4DF56B9F | SHA256:4849089C9D47D5240228C00FE5C8EE9C7FEF402780FBC442FE708F1C142E1C2D | |||
| 5308 | YogaDNSSetup.tmp | C:\Program Files (x86)\YogaDNS\unins000.exe | executable | |
MD5:9A918EA79F21EDEA6046BB11EC0F94B9 | SHA256:78ACC8F6748ED579E0CBE4DE2EC748561363F49BB614587AFDDABDD4351FE843 | |||
| 5308 | YogaDNSSetup.tmp | C:\Program Files (x86)\YogaDNS\Driver\DnsFltEngineDrv.inf | binary | |
MD5:71F188B094AEA862B928579EA3B5B8D3 | SHA256:CB0E4C116E30890DA4A9BC143826E65BF6C4F200237C8A0CBB12934C63A8954F | |||
| 5308 | YogaDNSSetup.tmp | C:\Program Files (x86)\YogaDNS\YogaDNS.exe | executable | |
MD5:C0C0B96046F27F7B549C42CD6B48B2D8 | SHA256:76409047EA4FC5785E9499CA5215E457DE446E08474FDF7C81EB83D3AF2B1AFE | |||
| 5308 | YogaDNSSetup.tmp | C:\Program Files (x86)\YogaDNS\is-K414U.tmp | text | |
MD5:240DF71B1A110C4DCEFFC1B77751B781 | SHA256:06C74EF5EF53344C78C9AF2B29DC458A2ABE93F1BFF429705955C033E7A0686F | |||
| 5308 | YogaDNSSetup.tmp | C:\Program Files (x86)\YogaDNS\is-MB3RO.tmp | text | |
MD5:87266FAFF9BEA0D9464D17AE6F99C742 | SHA256:692184F7D1272B8D1EC73A56C91D6C94C4E8F2C49FD1BE6DD3F6D75BFC48574F | |||
| 5308 | YogaDNSSetup.tmp | C:\Program Files (x86)\YogaDNS\is-EQ70L.tmp | executable | |
MD5:C5BB8D06E0C031F269D70150B946EE70 | SHA256:20E2E8084C111215D4AA5A0666CAFAF56431E15553267C5D018B26AD4EA8081D | |||
| 5308 | YogaDNSSetup.tmp | C:\Program Files (x86)\YogaDNS\Driver\is-7KN46.tmp | binary | |
MD5:71F188B094AEA862B928579EA3B5B8D3 | SHA256:CB0E4C116E30890DA4A9BC143826E65BF6C4F200237C8A0CBB12934C63A8954F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
33
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5200 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5200 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1468 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1468 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6476 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1468 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1468 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.19.96.66:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |