| URL: | https://bbvnews.com |
| Full analysis: | https://app.any.run/tasks/b3a9a96d-77b7-416e-bf18-6a0b46f48f73 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 11:43:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A90104D75289852E97629ADDA45229F9 |
| SHA1: | 2BBC6CEB83875D22300273887E49D6643AD8878F |
| SHA256: | 022524C22985383E2B00F8E31E0C1EB9A497CCA6BF7D9F732A7686147DA385F8 |
| SSDEEP: | 3:N89rW2:29n |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2852)
INFO
Application launched itself
- chrome.exe (PID: 2852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,6252004916191749631,15270776413018287283,131072 --enable-features=PasswordImport --service-pipe-token=14625635089896260212 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14625635089896260212 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,6252004916191749631,15270776413018287283,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3983289737734084607 --mojo-platform-channel-handle=1060 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,6252004916191749631,15270776413018287283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17433906588165804082 --mojo-platform-channel-handle=2628 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,6252004916191749631,15270776413018287283,131072 --enable-features=PasswordImport --service-pipe-token=4126131385282159727 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4126131385282159727 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1972 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2856 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://bbvnews.com | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,6252004916191749631,15270776413018287283,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14440828642209793449 --mojo-platform-channel-handle=2040 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,6252004916191749631,15270776413018287283,131072 --enable-features=PasswordImport --service-pipe-token=1668971295752836557 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1668971295752836557 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2140 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,6252004916191749631,15270776413018287283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5765040769386007478 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5765040769386007478 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,6252004916191749631,15270776413018287283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1538247455751339849 --mojo-platform-channel-handle=2768 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
529
Read events
459
Write events
66
Delete events
4
Modification events
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2736) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2852-13200666224360750 |
Value: 259 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
12
Text files
144
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a4ccd2ec-36cb-47d8-ac25-95e6007eef96.tmp | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
25
DNS requests
55
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
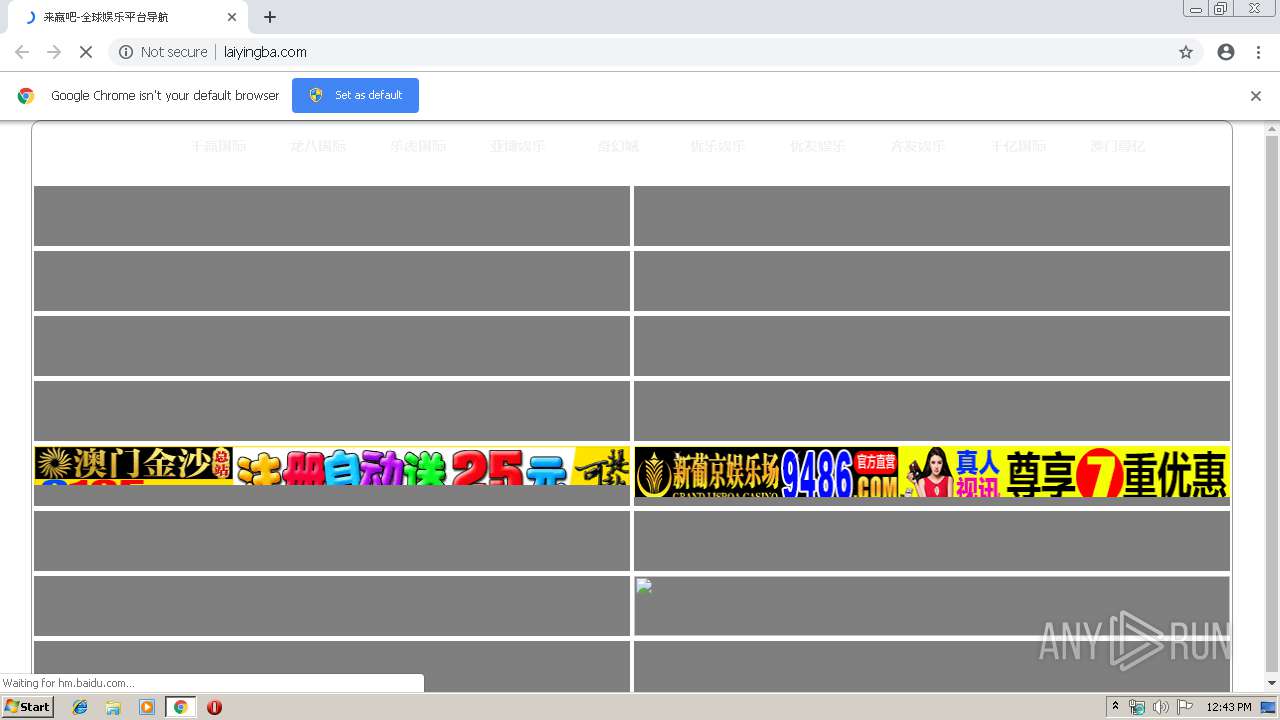
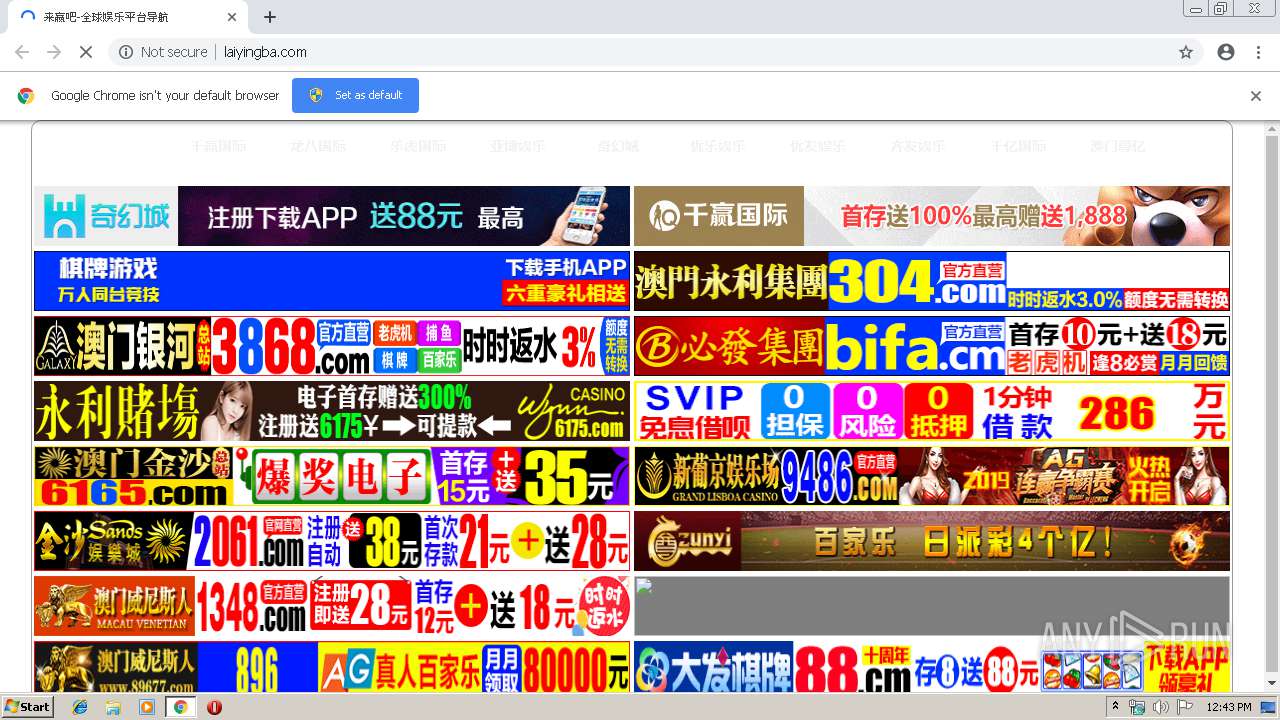
2852 | chrome.exe | GET | 200 | 183.131.207.78:80 | http://ia.51.la/go1?id=19305906&rt=1556192628799&rl=1280*720&lang=en-US&ct=unknow&pf=1&ins=1&vd=1&ce=1&cd=24&ds=%25E6%259D%25A5%25E8%25B5%25A2%25E5%2590%25A7&ing=1&ekc=&sid=1556192628799&tt=%25E6%259D%25A5%25E8%25B5%25A2%25E5%2590%25A7-%25E5%2585%25A8%25E7%2590%2583%25E5%25A8%25B1%25E4%25B9%2590%25E5%25B9%25B3%25E5%258F%25B0%25E5%25AF%25BC%25E8%2588%25AA&kw=%25E6%259D%25A5%25E8%25B5%25A2%25E5%2590%25A7&cu=http%253A%252F%252Flaiyingba.com%252F&pu= | CN | — | — | whitelisted |
2852 | chrome.exe | GET | 200 | 220.242.139.165:80 | http://js.users.51.la/19305906.js | CN | html | 2.48 Kb | whitelisted |
2852 | chrome.exe | GET | 200 | 183.60.187.58:80 | http://sinacloud.net/laiyingba/600x60%E6%B0%B8%E5%88%A920190425.gif | CN | image | 22.6 Kb | suspicious |
2852 | chrome.exe | GET | 200 | 103.42.178.61:80 | http://laiyingba.com/win.php?default | HK | html | 2.39 Kb | unknown |
2852 | chrome.exe | GET | 200 | 183.60.187.58:80 | http://sinacloud.net/sina555/laiyingba/ad_amwnsr.gif | CN | image | 184 Kb | suspicious |
2852 | chrome.exe | GET | 200 | 183.60.187.58:80 | http://sinacloud.net/sina555/quyingba/changtu/ad/ad_bifa600.gif | CN | image | 174 Kb | suspicious |
2852 | chrome.exe | GET | 200 | 103.42.178.61:80 | http://laiyingba.com/nav/css/style.css?20190425194349 | HK | text | 1.27 Kb | unknown |
2852 | chrome.exe | GET | 403 | 183.60.187.58:80 | http://sinacloud.net/laiyingba/600x60.gif | CN | xml | 271 b | suspicious |
2852 | chrome.exe | GET | 200 | 183.60.187.58:80 | http://sinacloud.net/sina555/laiyingba/ad_600_60_6165js.gif | CN | image | 239 Kb | suspicious |
2852 | chrome.exe | GET | 200 | 183.60.187.58:80 | http://sinacloud.net/laiyingba/xpj9486_600_60.gif | CN | image | 171 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2852 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2852 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
2852 | chrome.exe | 23.80.82.23:443 | bbvnews.com | Nobis Technology Group, LLC | US | unknown |
2852 | chrome.exe | 103.42.178.61:80 | laiyingba.com | Sun Network (Hong Kong) Limited - HongKong Backbone | HK | unknown |
2852 | chrome.exe | 220.242.139.165:80 | js.users.51.la | — | CN | unknown |
2852 | chrome.exe | 119.146.74.48:443 | timgsa.baidu.com | Guangdong | CN | unknown |
2852 | chrome.exe | 183.131.207.78:80 | ia.51.la | DaLi | CN | suspicious |
2852 | chrome.exe | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
2852 | chrome.exe | 103.235.46.191:443 | hm.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | suspicious |
2852 | chrome.exe | 183.60.187.58:80 | sinacloud.net | CHINANET Guangdong province network | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
bbvnews.com |
| unknown |
accounts.google.com |
| shared |
laiyingba.com |
| unknown |
js.users.51.la |
| whitelisted |
ia.51.la |
| whitelisted |
hm.baidu.com |
| whitelisted |
timgsa.baidu.com |
| suspicious |
www.51.la |
| suspicious |
sinacloud.net |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2852 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |