| URL: | client.c6gj-static.net |
| Full analysis: | https://app.any.run/tasks/a1cd25f7-9334-4c32-9af8-4b405f9e6dab |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2024, 08:39:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 7CEC41492A295682641C97651692CFB7 |
| SHA1: | ADA9AA54FEFB5F52CD48E5348F9BAD62D3F96461 |
| SHA256: | 0222AC8CC7C4DABDE99F7D4483B4FD11A1AACDC34E4954519A90C77F51A9C048 |
| SSDEEP: | 3:M1ripo:MApo |
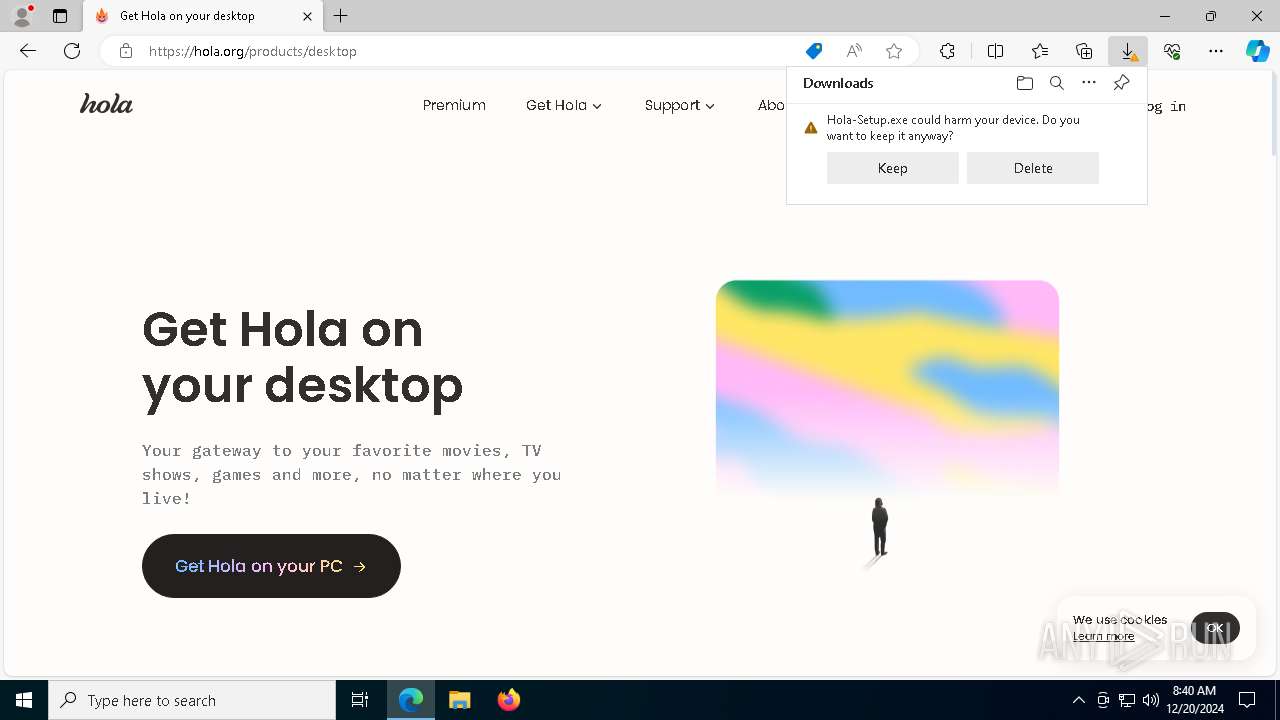
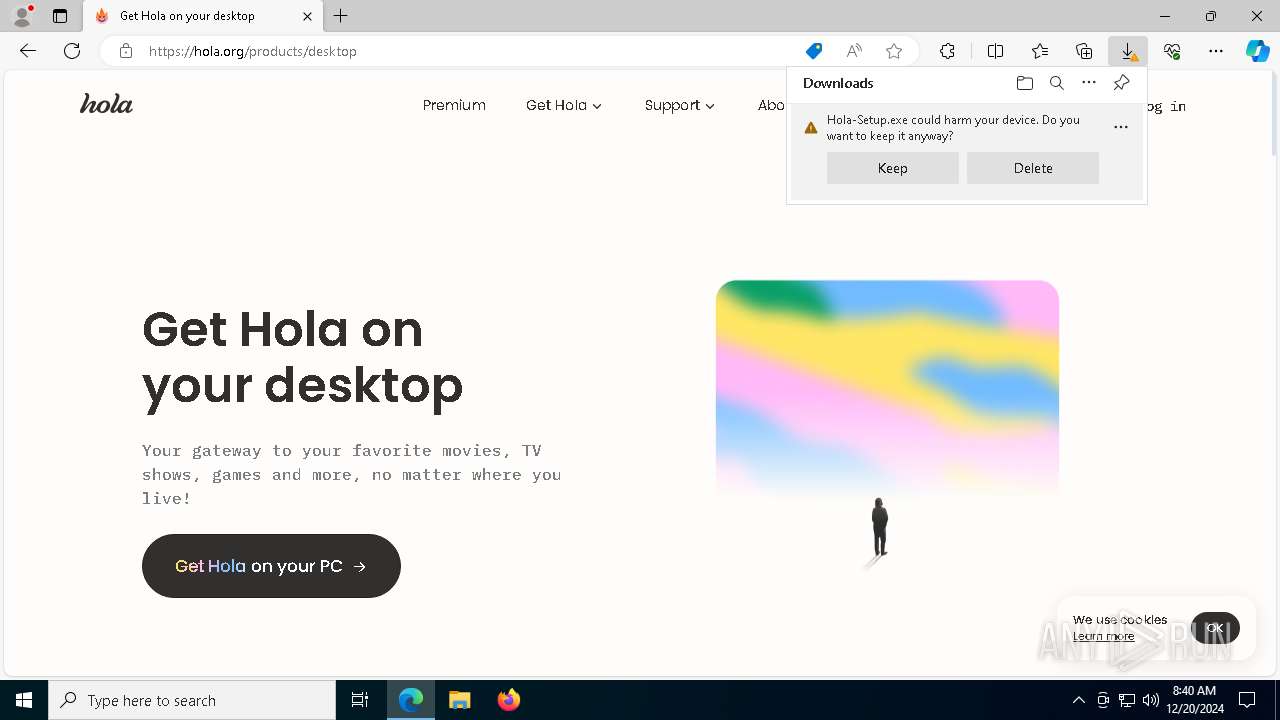
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- Hola-Setup.exe (PID: 5872)
Application launched itself
- Hola-Setup.exe (PID: 5872)
- hola_svc.exe (PID: 2600)
- Hola-Setup.exe (PID: 2624)
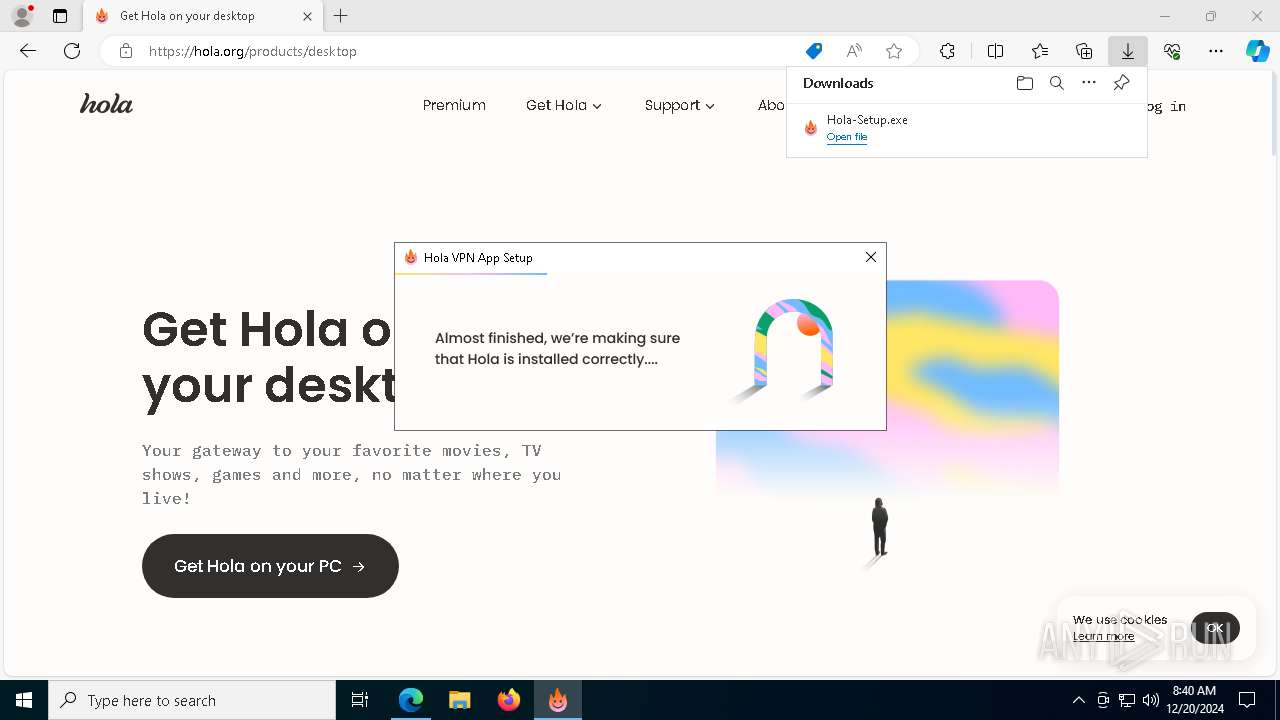
Executable content was dropped or overwritten
- Hola-Setup.exe (PID: 2624)
- Hola-Setup-x64-1.233.367.exe (PID: 3992)
- net_updater64.exe (PID: 2796)
- net_updater64.exe (PID: 3364)
- net_updater64.exe (PID: 4764)
Creates a software uninstall entry
- Hola-Setup-x64-1.233.367.exe (PID: 3992)
Drops a system driver (possible attempt to evade defenses)
- Hola-Setup-x64-1.233.367.exe (PID: 3992)
Drops 7-zip archiver for unpacking
- Hola-Setup-x64-1.233.367.exe (PID: 3992)
Executes as Windows Service
- net_updater64.exe (PID: 2796)
- hola_svc.exe (PID: 2600)
- WmiApSrv.exe (PID: 7572)
The process drops C-runtime libraries
- net_updater64.exe (PID: 2796)
Process drops legitimate windows executable
- net_updater64.exe (PID: 2796)
Detected use of alternative data streams (AltDS)
- net_updater64.exe (PID: 3364)
- net_updater64.exe (PID: 4764)
Checks Windows Trust Settings
- net_updater64.exe (PID: 4764)
The process checks if it is being run in the virtual environment
- net_updater64.exe (PID: 2796)
Checks for external IP
- net_updater64.exe (PID: 2796)
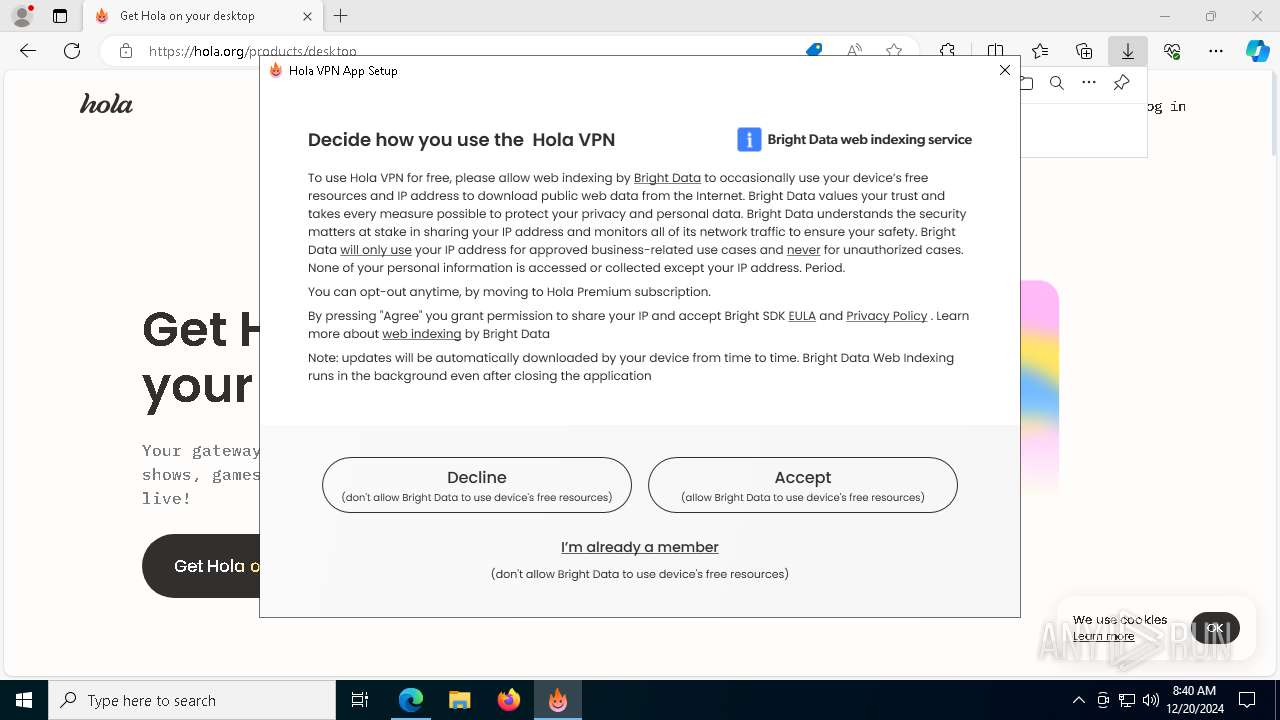
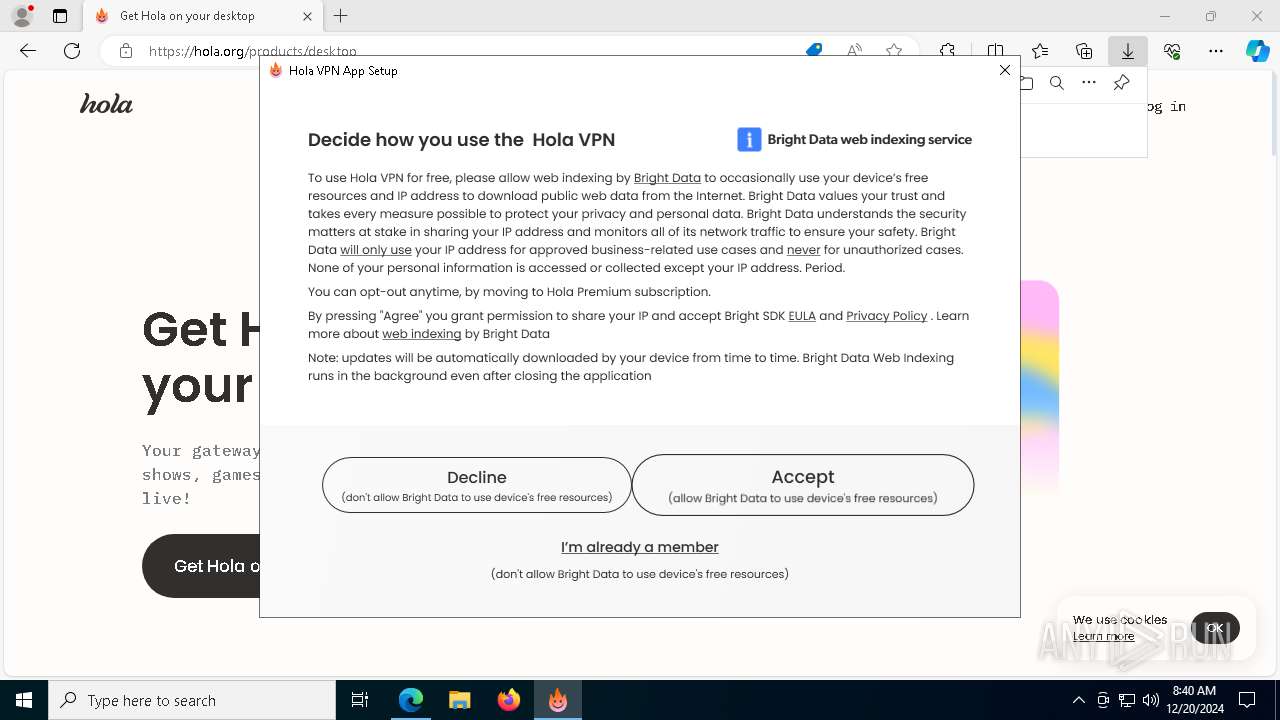
Potential Corporate Privacy Violation
- net_updater64.exe (PID: 2796)
Connects to unusual port
- hola_svc.exe (PID: 2600)
INFO
Application launched itself
- msedge.exe (PID: 1668)
Reads the machine GUID from the registry
- Hola-Setup.exe (PID: 6520)
- Hola-Setup.exe (PID: 5872)
- net_updater64.exe (PID: 2796)
- test_wpf.exe (PID: 5592)
- net_updater64.exe (PID: 3364)
- test_wpf.exe (PID: 2844)
- net_updater64.exe (PID: 4764)
- Hola-Setup.exe (PID: 2624)
Checks supported languages
- Hola-Setup.exe (PID: 6520)
- Hola-Setup.exe (PID: 5872)
- test_wpf.exe (PID: 5592)
- net_updater64.exe (PID: 3364)
- idle_report.exe (PID: 7424)
- net_updater64.exe (PID: 4764)
- hola_svc.exe (PID: 8148)
- Hola-Setup.exe (PID: 2624)
Reads Environment values
- identity_helper.exe (PID: 6844)
- net_updater64.exe (PID: 3364)
Executable content was dropped or overwritten
- msedge.exe (PID: 6464)
- msedge.exe (PID: 1668)
Reads the computer name
- identity_helper.exe (PID: 6844)
- Hola-Setup.exe (PID: 5872)
- Hola-Setup.exe (PID: 2624)
- test_wpf.exe (PID: 5592)
- Hola-Setup.exe (PID: 6520)
Disables trace logs
- Hola-Setup.exe (PID: 5872)
- Hola-Setup.exe (PID: 6520)
- net_updater64.exe (PID: 2796)
- hola_svc.exe (PID: 2600)
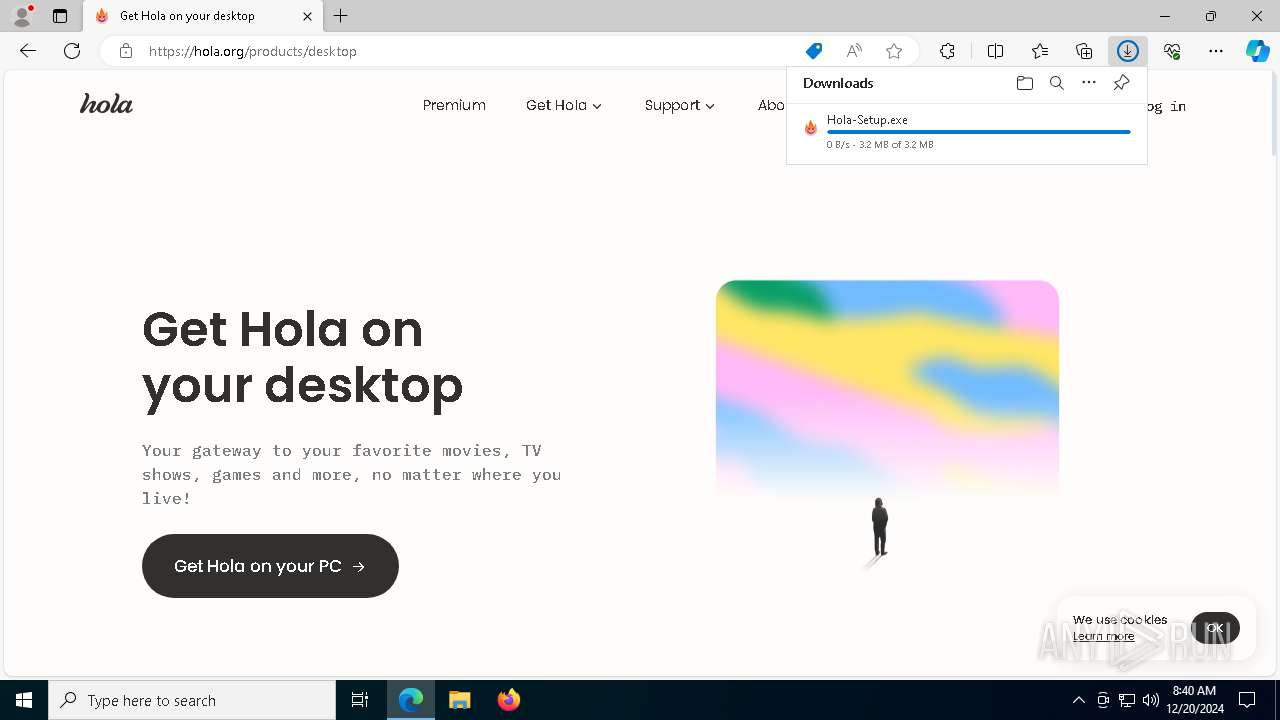
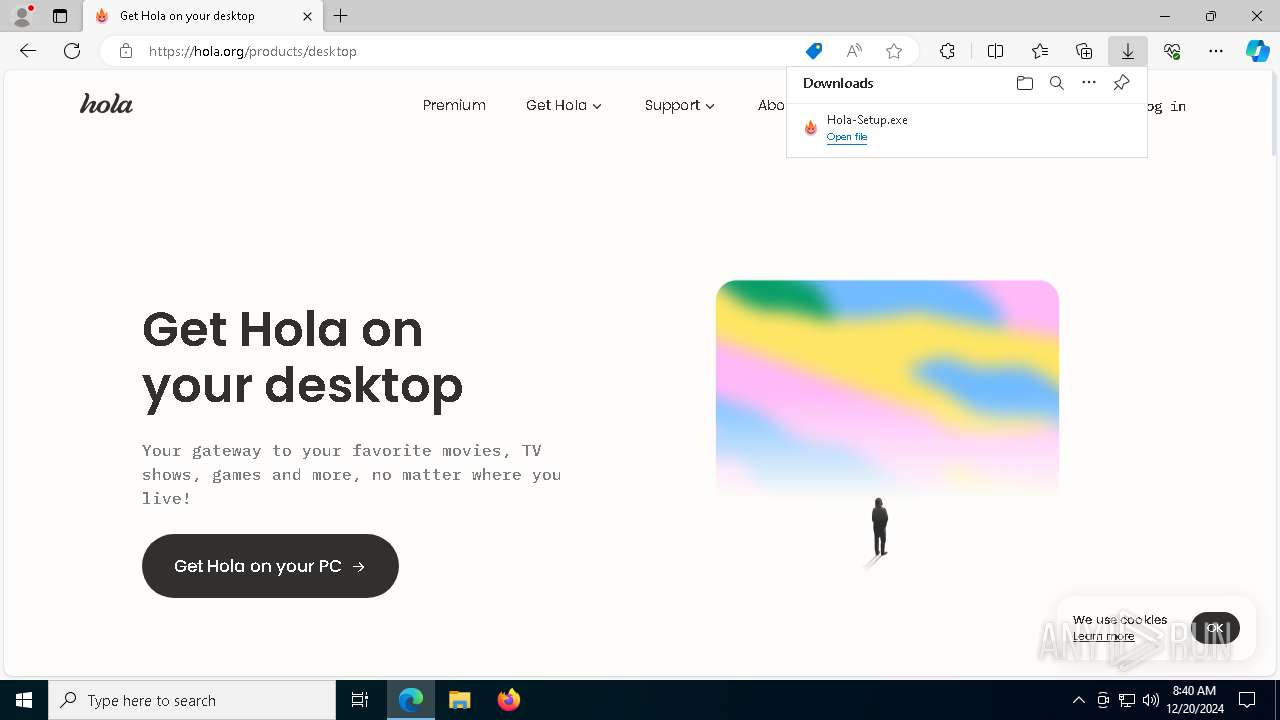
The process uses the downloaded file
- Hola-Setup.exe (PID: 5872)
Create files in a temporary directory
- Hola-Setup.exe (PID: 5872)
- Hola-Setup-x64-1.233.367.exe (PID: 3992)
Reads the software policy settings
- Hola-Setup.exe (PID: 6520)
- net_updater64.exe (PID: 2796)
- net_updater64.exe (PID: 3364)
Checks proxy server information
- Hola-Setup.exe (PID: 6520)
The sample compiled with english language support
- Hola-Setup.exe (PID: 2624)
- Hola-Setup-x64-1.233.367.exe (PID: 3992)
- net_updater64.exe (PID: 2796)
Creates files in the program directory
- Hola-Setup-x64-1.233.367.exe (PID: 3992)
- net_updater64.exe (PID: 7620)
- net_updater64.exe (PID: 3364)
- net_updater64.exe (PID: 2796)
- hola_svc.exe (PID: 2600)
Creates files or folders in the user directory
- net_updater64.exe (PID: 7620)
- net_updater64.exe (PID: 3364)
Reads CPU info
- net_updater64.exe (PID: 2796)
Reads the time zone
- net_updater64.exe (PID: 2796)
Process checks computer location settings
- net_updater64.exe (PID: 4764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
194
Monitored processes
62
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
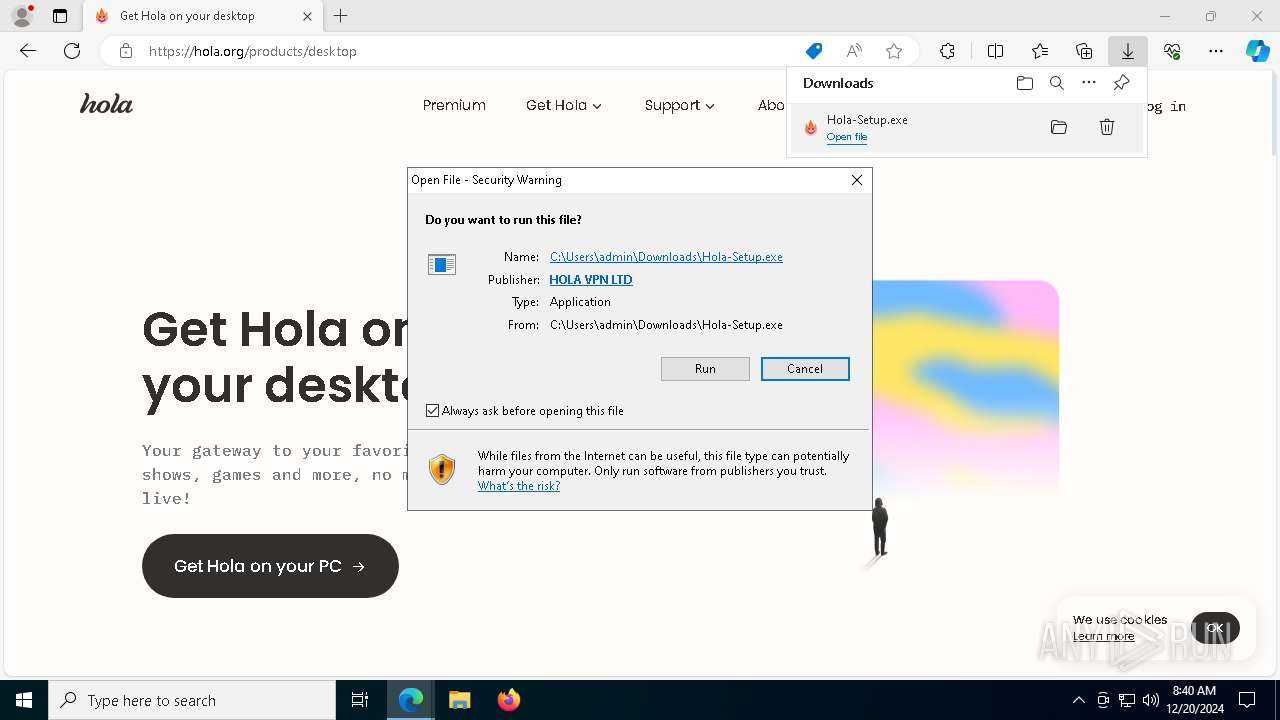
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | rasdial.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "client.c6gj-static.net" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1740 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6280 --field-trial-handle=2340,i,17942061815227527928,11678922239246440524,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net_updater64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Hola\app\hola_svc.exe" --service | C:\Program Files\Hola\app\hola_svc.exe | services.exe | ||||||||||||
User: SYSTEM Company: Hola Networks Ltd. Integrity Level: SYSTEM Description: Hola VPN Service Version: 1.233.367 | |||||||||||||||
| 2624 | "C:\Users\admin\Downloads\Hola-Setup.exe" | C:\Users\admin\Downloads\Hola-Setup.exe | Hola-Setup.exe | ||||||||||||
User: admin Company: Hola VPN Ltd. Integrity Level: HIGH Description: Hola VPN App Setup Version: 1.227.226.0 Modules
| |||||||||||||||
| 2796 | "C:/Program Files/Hola/app/net_updater64.exe" --updater win_hola.org | C:\Program Files\Hola\app\net_updater64.exe | services.exe | ||||||||||||
User: SYSTEM Company: BrightData Ltd. (certified) Integrity Level: SYSTEM Description: BrightData service allows free use of certain features in an app you installed Version: 1.489.750 Modules
| |||||||||||||||
| 2844 | C:\ProgramData\BrightData\108a47921d08860d64656218998ab66204caf497\test_wpf.exe | C:\ProgramData\BrightData\108a47921d08860d64656218998ab66204caf497\test_wpf.exe | — | net_updater64.exe | |||||||||||
User: admin Company: BrightData Ltd. (certified) Integrity Level: HIGH Description: test_wpf Exit code: 0 Version: 1.489.750 Modules
| |||||||||||||||
| 3364 | "C:\Program Files\Hola\app\net_updater64.exe" --uuid | C:\Program Files\Hola\app\net_updater64.exe | Hola-Setup-x64-1.233.367.exe | ||||||||||||
User: admin Company: BrightData Ltd. (certified) Integrity Level: HIGH Description: BrightData service allows free use of certain features in an app you installed Exit code: 0 Version: 1.489.750 Modules
| |||||||||||||||
| 3436 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7320 --field-trial-handle=2340,i,17942061815227527928,11678922239246440524,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
32 382
Read events
32 259
Write events
122
Delete events
1
Modification events
| (PID) Process: | (1668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1668) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2678D9DF45882F00 | |||
| (PID) Process: | (1668) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 11EFE3DF45882F00 | |||
| (PID) Process: | (1668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262916 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EBE3F536-9D98-41A8-A64B-F700AE1BCEF7} | |||
| (PID) Process: | (1668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262916 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {20956F9F-771B-43BE-B1EB-614E0E7D3CDF} | |||
| (PID) Process: | (1668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262916 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FEC70DF2-49B5-4D12-855B-53E437029812} | |||
| (PID) Process: | (1668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262916 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FE3B92DA-8E91-4FAB-A929-8794511AF00E} | |||
Executable files
32
Suspicious files
343
Text files
61
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135353.TMP | — | |
MD5:— | SHA256:— | |||
| 1668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135353.TMP | — | |
MD5:— | SHA256:— | |||
| 1668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135344.TMP | — | |
MD5:— | SHA256:— | |||
| 1668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135363.TMP | — | |
MD5:— | SHA256:— | |||
| 1668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135363.TMP | — | |
MD5:— | SHA256:— | |||
| 1668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
186
DNS requests
119
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7940 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2796 | net_updater64.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
1668 | msedge.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAXrhBDPOQ2gaSPA09Ycq3A%3D | unknown | — | — | whitelisted |
2796 | net_updater64.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAdTF0YC22Gdh8cnyPwWxE0%3D | unknown | — | — | whitelisted |
2796 | net_updater64.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
3364 | net_updater64.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAdTF0YC22Gdh8cnyPwWxE0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.158:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1668 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6464 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| unknown |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
client.c6gj-static.net |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
2796 | net_updater64.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2 ETPRO signatures available at the full report