| File name: | sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe |
| Full analysis: | https://app.any.run/tasks/960dc28d-5756-4eb9-8bcc-013da403dd23 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 16:41:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AD9FD1564DD1C6BE54747E84444B8F55 |
| SHA1: | 001495AF4AF443265200340A08B5E07DC2A32553 |
| SHA256: | 021D01FE3793879F57A2942664FC7C096710E94E87AD13DC21467C12EDF61546 |
| SSDEEP: | 96:bF2LOYFGrf4msMbe5r3NyTWrAZt7zd54fMVgYncY67AEA3dbwQNKSbuVmyVx9X:ALKf4my3ssAnktY67AN3BwQbqVx9X |
MALICIOUS
The process bypass UAC
- Dism.exe (PID: 2260)
SUSPICIOUS
Executable content was dropped or overwritten
- sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe (PID: 2368)
- dllhost.exe (PID: 3000)
Reads the Internet Settings
- sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe (PID: 2368)
INFO
Checks supported languages
- sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe (PID: 2368)
Reads the computer name
- sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe (PID: 2368)
Reads the machine GUID from the registry
- sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe (PID: 2368)
The process checks LSA protection
- dllhost.exe (PID: 3000)
- sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe (PID: 2368)
Checks transactions between databases Windows and Oracle
- sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe (PID: 2368)
Create files in a temporary directory
- sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe (PID: 2368)
- makecab.exe (PID: 1540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1450 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 11776 |
| CodeSize: | 2048 |
| LinkerVersion: | 14.14 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| TimeStamp: | 2018:08:04 23:55:45+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Aug-2018 23:55:45 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 04-Aug-2018 23:55:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000006BA | 0x00000800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.87714 |
.rdata | 0x00002000 | 0x00000994 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.79052 |
.data | 0x00003000 | 0x00000F78 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.16299 |
.rsrc | 0x00004000 | 0x00001270 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.30587 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
101 | 3.55552 | 4608 | UNKNOWN | UNKNOWN | WM_DISP |
Imports
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
46
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1392 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\System32\PkgMgr.exe | sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Package Manager Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
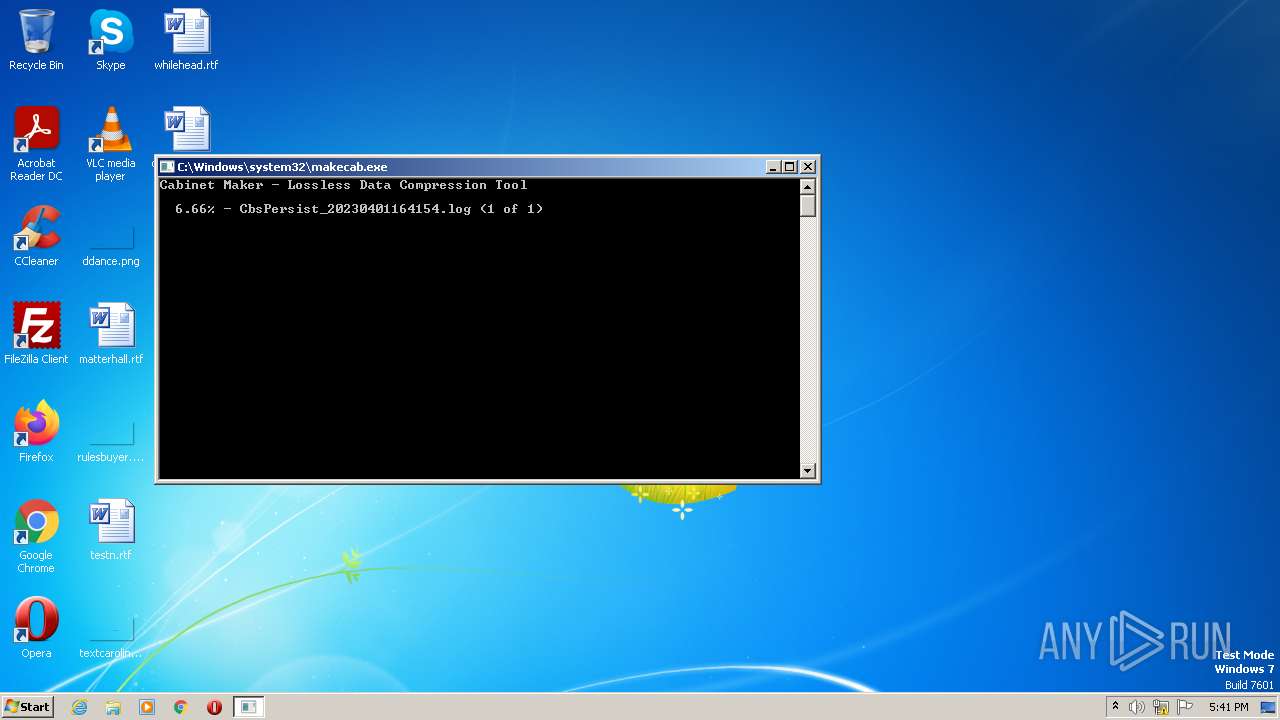
| 1540 | "C:\Windows\system32\makecab.exe" C:\Windows\Logs\CBS\CbsPersist_20230401164154.log C:\Windows\Logs\CBS\CbsPersist_20230401164154.cab | C:\Windows\System32\makecab.exe | — | PkgMgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2260 | "C:\Windows\system32\dism.exe" /online /norestart /apply-unattend:"C:\Users\admin\AppData\Local\Temp\ellocnak.xml" | C:\Windows\System32\Dism.exe | — | PkgMgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | "C:\Users\admin\AppData\Local\Temp\sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe" | C:\Users\admin\AppData\Local\Temp\sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3000 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3624 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\System32\PkgMgr.exe | — | sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Package Manager Exit code: 3221226540 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 768
Read events
1 744
Write events
24
Delete events
0
Modification events
| (PID) Process: | (2368) sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2368) sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2368) sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2368) sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
4
Suspicious files
12
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2368 | sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe | C:\Windows\System32\dismcore.dll | — | |
MD5:— | SHA256:— | |||
| 1392 | PkgMgr.exe | C:\Windows\Logs\CBS\CbsPersist_20230401164154.log | — | |
MD5:— | SHA256:— | |||
| 2368 | sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe | C:\Users\admin\AppData\Local\Temp\dismcore.dll | executable | |
MD5:6B906764A35508A7FD266CDD512E46B1 | SHA256:FC0C90044B94B080F307C16494369A0796AC1D4E74E7912BA79C15CCA241801C | |||
| 1392 | PkgMgr.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:— | SHA256:— | |||
| 1540 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_1540_3 | binary | |
MD5:— | SHA256:— | |||
| 1540 | makecab.exe | C:\Windows\Logs\CBS\CbsPersist_20230401164154.cab | compressed | |
MD5:— | SHA256:— | |||
| 1540 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_1540_5 | binary | |
MD5:— | SHA256:— | |||
| 3000 | dllhost.exe | C:\Windows\System32\dismcore.dll | executable | |
MD5:6B906764A35508A7FD266CDD512E46B1 | SHA256:FC0C90044B94B080F307C16494369A0796AC1D4E74E7912BA79C15CCA241801C | |||
| 1540 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_1540_2 | binary | |
MD5:F7BB56E52701D76FCE4941B41C44DB3F | SHA256:A35F5A8709EC880025656ADA2F4AFE1EC6207C4FAE69CD654632016F61A9AFFD | |||
| 2368 | sasub.exe.0ae0_00021000.exe.0001cc70_2c00.exe | C:\Users\admin\AppData\Local\Temp\ellocnak.xml | xml | |
MD5:427EB7374887305B72F5C552837C9036 | SHA256:B3F421780A49CBE680A317259D4DF9CE1D0CDACA3020B4DF0DC18CC01D68CCBB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report