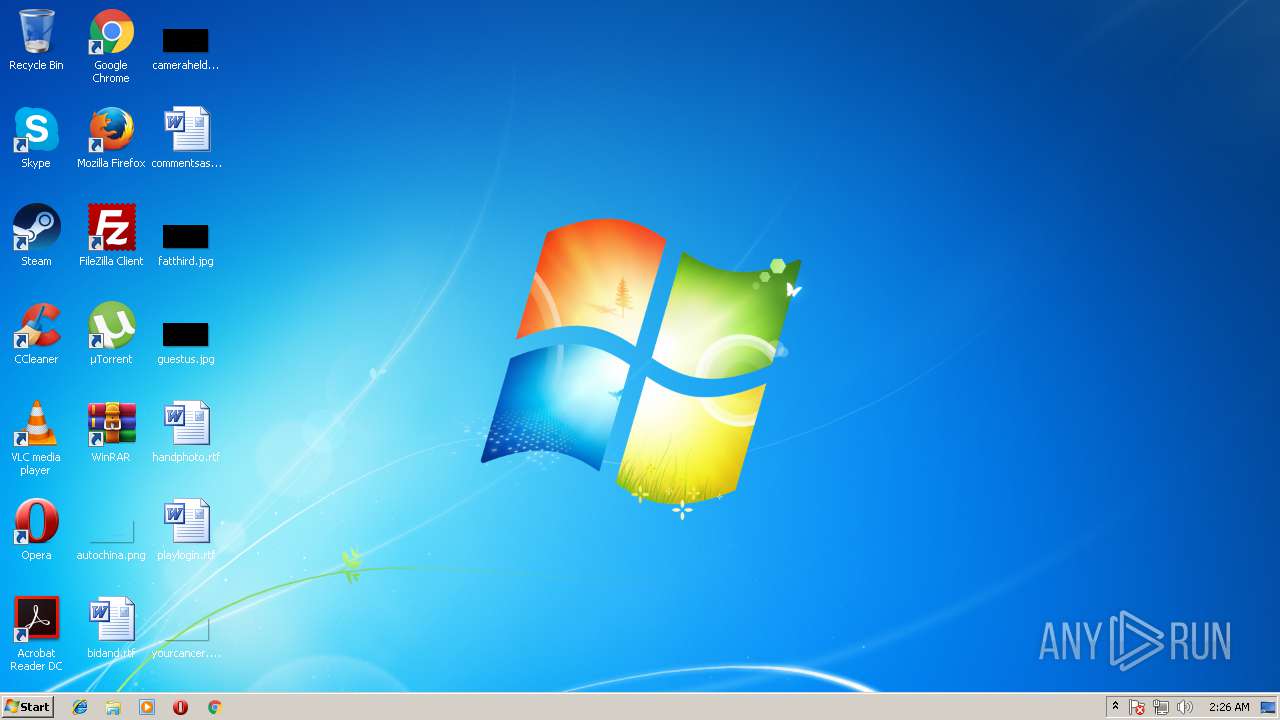
| File name: | Termite.exe |
| Full analysis: | https://app.any.run/tasks/21563964-c30e-47e0-aa4c-1b4709afc928 |
| Verdict: | Malicious activity |
| Analysis date: | August 24, 2018, 01:25:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 48E4A8C42A7E84C8279D1B489DC51023 |
| SHA1: | 64621781550058676EF56BC445F208C831D37879 |
| SHA256: | 021CA4692D3A721AF510F294326A31780D6F8FCD9BE2046D1C2A0902A7D58133 |
| SSDEEP: | 24576:tnxLSUXY7WSIGgjQvYaxKMiZA+yH6uw1ECvGX6H7O3YpPNaG:txOUpSIZMv1xim+y6HLOO3 |
MALICIOUS
Changes the autorun value in the registry
- Termite.exe (PID: 584)
SUSPICIOUS
Uses ICACLS.EXE to modify access control list
- Termite.exe (PID: 584)
Creates files in the program directory
- Termite.exe (PID: 584)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:08:23 07:04:10+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 524288 |
| InitializedDataSize: | 1572864 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x616a4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Aug-2018 05:04:10 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 23-Aug-2018 05:04:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0007F246 | 0x00080000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56637 |
.rdata | 0x00081000 | 0x00133434 | 0x00134000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.16607 |
.data | 0x001B5000 | 0x0003604A | 0x00014000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.93051 |
.rsrc | 0x001EC000 | 0x00014E60 | 0x00015000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.1932 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07695 | 461 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 2.18858 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 1.17674 | 66040 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.74274 | 180 | UNKNOWN | Chinese - PRC | RT_CURSOR |
127 | 1.4183 | 12 | UNKNOWN | Chinese - PRC | RT_MENU |
150 | 3.06278 | 152 | UNKNOWN | Chinese - PRC | RT_DIALOG |
286 | 3.5561 | 378 | UNKNOWN | Chinese - PRC | RT_DIALOG |
554 | 3.78697 | 250 | UNKNOWN | Chinese - PRC | RT_DIALOG |
1031 | 3.67246 | 584 | UNKNOWN | Chinese - PRC | RT_BITMAP |
1032 | 1.91924 | 20 | UNKNOWN | Chinese - PRC | RT_GROUP_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
WINMM.dll |
WINSPOOL.DRV |
WS2_32.dll |
Total processes
43
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Windows\Termite.exe" | C:\Windows\Termite.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1712 | takeown /f "C:\Windows\SysNative\mswsock.dll" | C:\Windows\system32\takeown.exe | — | Termite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Takes ownership of a file Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
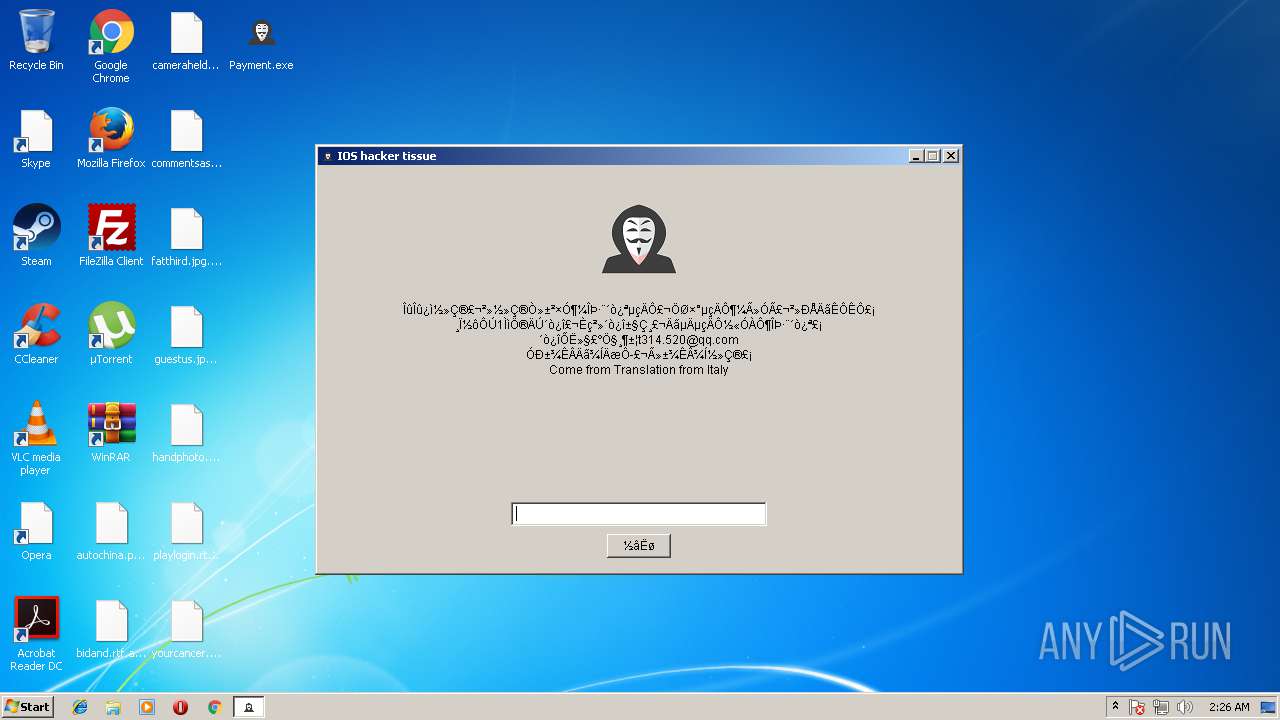
| 2172 | C:\Users\admin\Desktop\Payment.exe | C:\Users\admin\Desktop\Payment.exe | — | Termite.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2228 | icacls "C:\Windows\SysNative\mswsock.dll" /grant administrators:F | C:\Windows\system32\icacls.exe | — | Termite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3868 | icacls "C:\Windows\SysWOW64\mswsock.dll" /grant administrators:F | C:\Windows\system32\icacls.exe | — | Termite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4056 | takeown /f "C:\Windows\SysWOW64\mswsock.dll" | C:\Windows\system32\takeown.exe | — | Termite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Takes ownership of a file Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
20
Read events
12
Write events
8
Delete events
0
Modification events
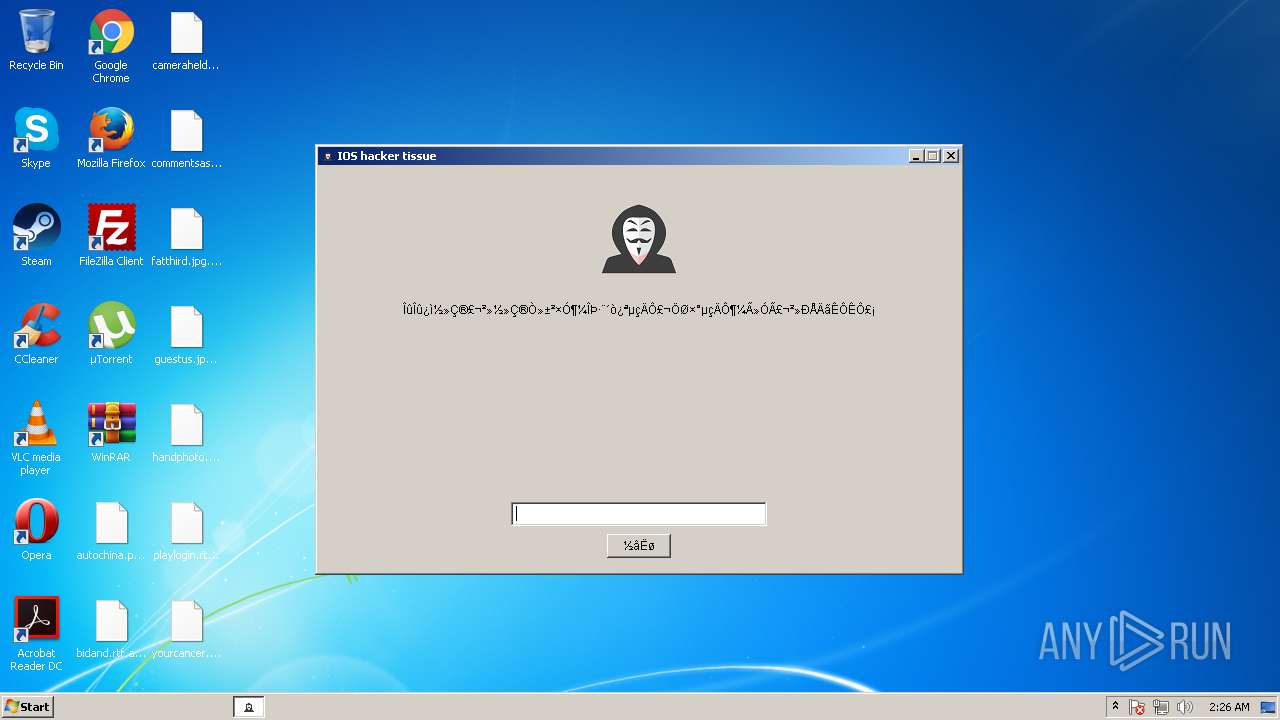
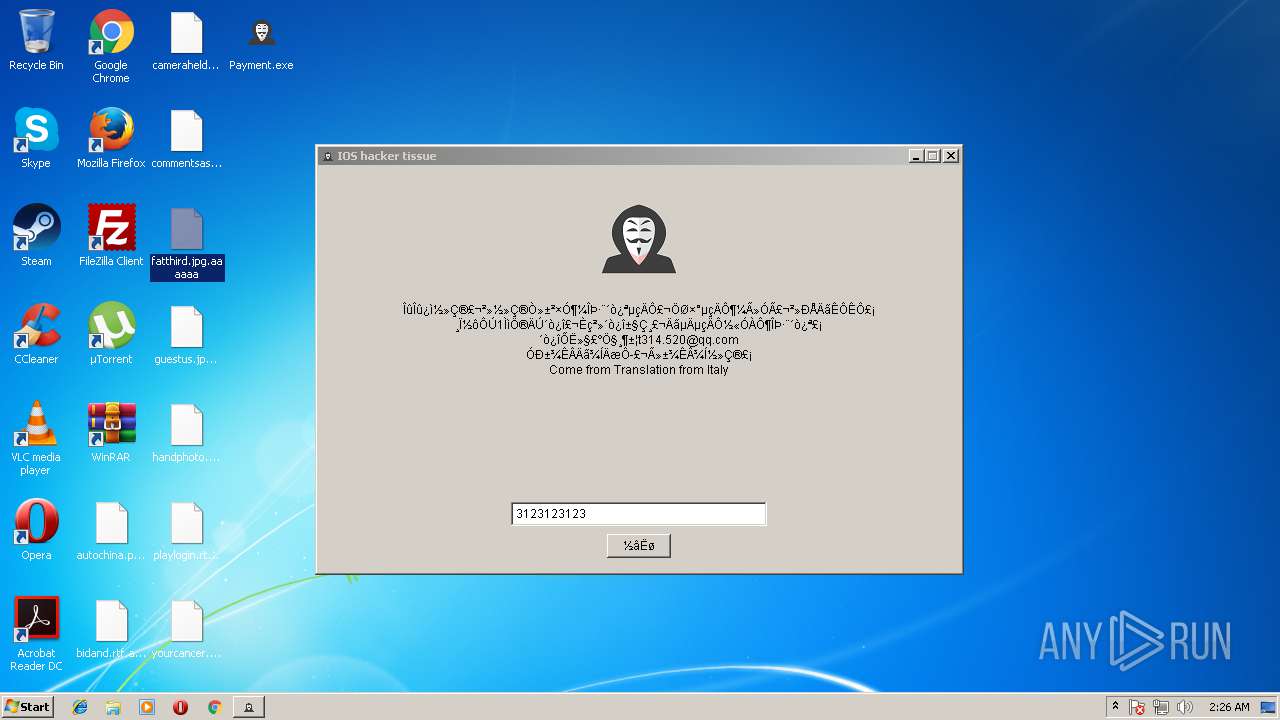
| (PID) Process: | (584) Termite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft |
| Operation: | write | Name: | Title |
Value: IOS hacker tissue | |||
| (PID) Process: | (584) Termite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft |
| Operation: | write | Name: | Content |
Value: ÎûÎû¿ì½»Ç®£¬²»½»Ç®Ò»±²×Ó¶¼ÎÞ·¨´ò¿ªµçÄÔ£¬ÖØ×°µçÄÔ¶¼Ã»Ó㬲»ÐÅÄãÊÔÊÔ£¡
¸Ï½ôÔÚ1ÌìÖ®ÄÚ´ò¿î£¬Èç²»´ò¿î±§Ç¸£¬ÄãµÄµçÄÔ½«ÓÀÔ¶ÎÞ·¨´ò¿ª£¡
´ò¿îÕË»§£ºÖ§¸¶±¦t314.520@qq.com
Óб¾ÊÂÄã¾ÍÄæÔ£¬Ã»±¾Ê¾ͽ»Ç®£¡
Come from Translation from Italy | |||
| (PID) Process: | (584) Termite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft |
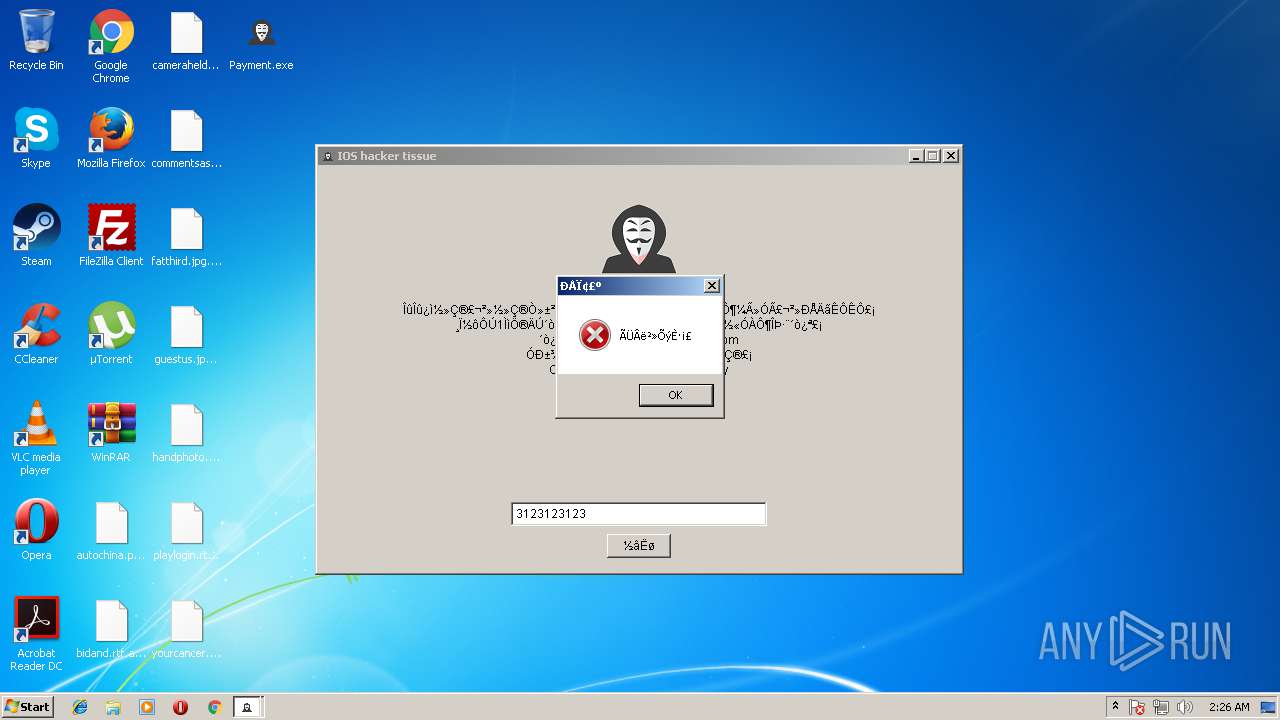
| Operation: | write | Name: | PassWord |
Value: a330326 | |||
| (PID) Process: | (584) Termite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft |
| Operation: | write | Name: | Tail |
Value: aaaaaa | |||
| (PID) Process: | (584) Termite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft |
| Operation: | write | Name: | savetime |
Value: 20180823144443 | |||
| (PID) Process: | (2172) Payment.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 46 | |||
| (PID) Process: | (584) Termite.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Termite.exe |
Value: C:\Windows\Termite.exe | |||
| (PID) Process: | (584) Termite.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Payment.exe |
Value: C:\Users\admin\Desktop\Payment.exe | |||
Executable files
0
Suspicious files
817
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 584 | Termite.exe | C:\Users\admin\AppData\Local\Temp\5006375\TemporaryFile | — | |
MD5:— | SHA256:— | |||
| 584 | Termite.exe | C:\Users\admin\AppData\Local\Temp\5006609\TemporaryFile | — | |
MD5:— | SHA256:— | |||
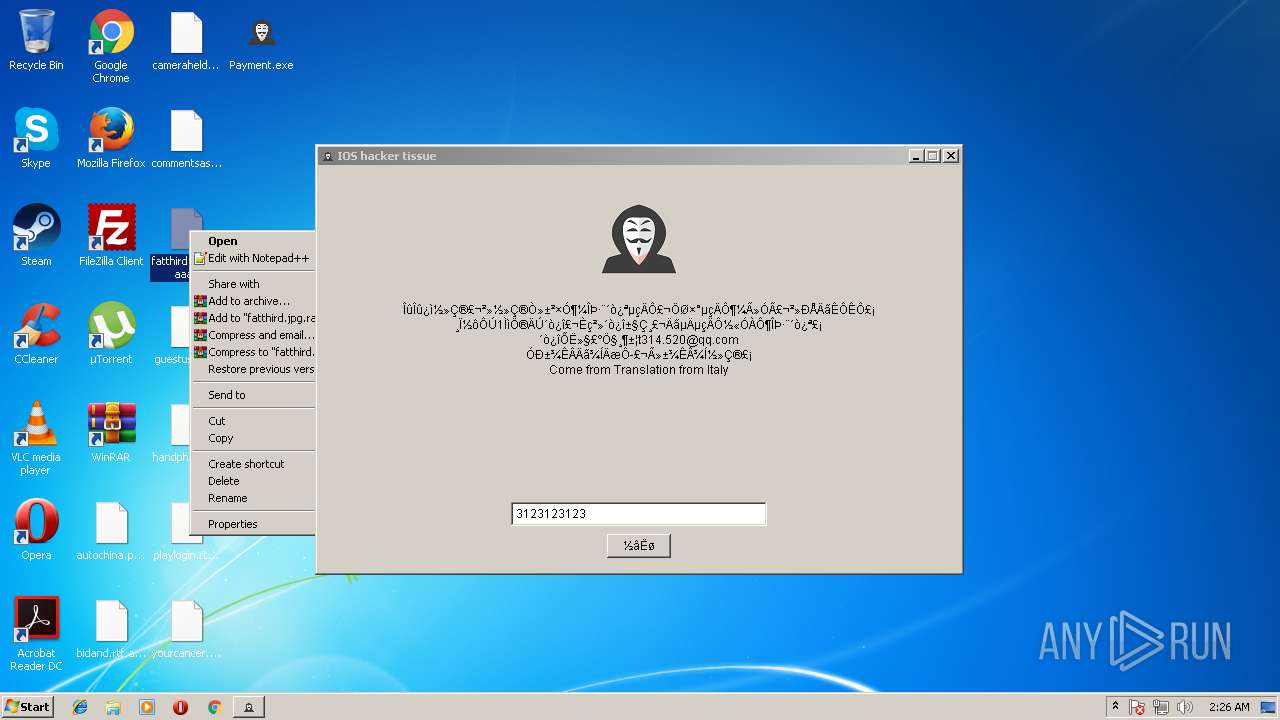
| 584 | Termite.exe | C:\Users\admin\Desktop\autochina.png.aaaaaa | binary | |
MD5:— | SHA256:— | |||
| 584 | Termite.exe | C:\Users\admin\Desktop\cameraheld.jpg.aaaaaa | binary | |
MD5:— | SHA256:— | |||
| 584 | Termite.exe | C:\Users\admin\Desktop\bidand.rtf.aaaaaa | binary | |
MD5:— | SHA256:— | |||
| 584 | Termite.exe | C:\Users\admin\Desktop\commentsas.rtf.aaaaaa | binary | |
MD5:— | SHA256:— | |||
| 584 | Termite.exe | C:\Users\admin\Desktop\guestus.jpg.aaaaaa | binary | |
MD5:— | SHA256:— | |||
| 584 | Termite.exe | C:\Users\admin\AppData\Local\VirtualStore\hiberfil.sys.aaaaaa | text | |
MD5:— | SHA256:— | |||
| 584 | Termite.exe | C:\Users\admin\AppData\Local\VirtualStore\pagefile.sys.aaaaaa | text | |
MD5:— | SHA256:— | |||
| 584 | Termite.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\IrakHau.htm.aaaaaa | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report