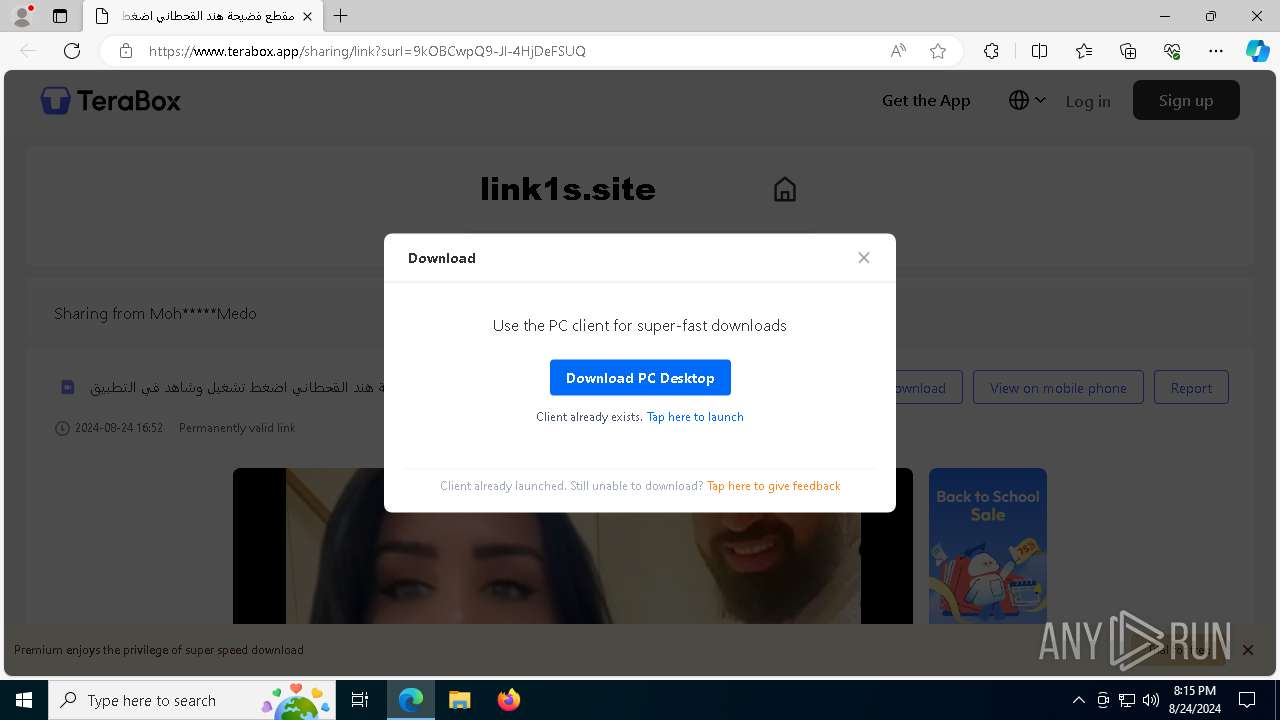
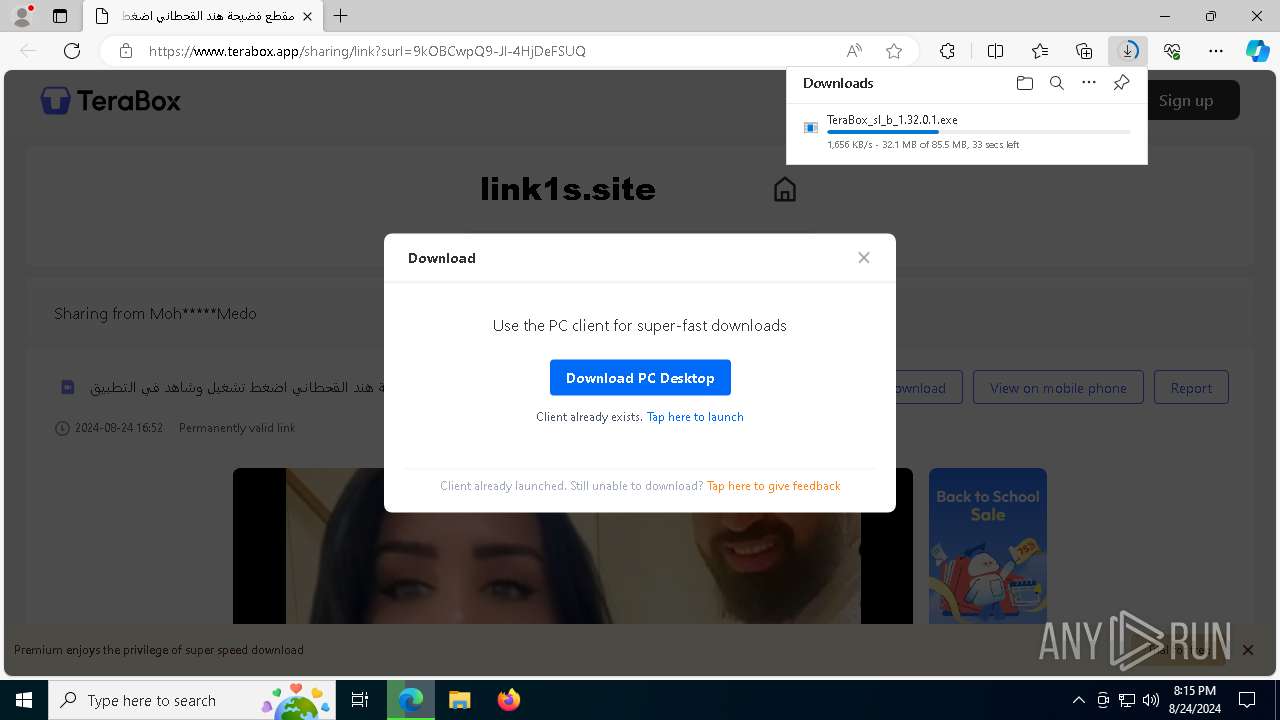
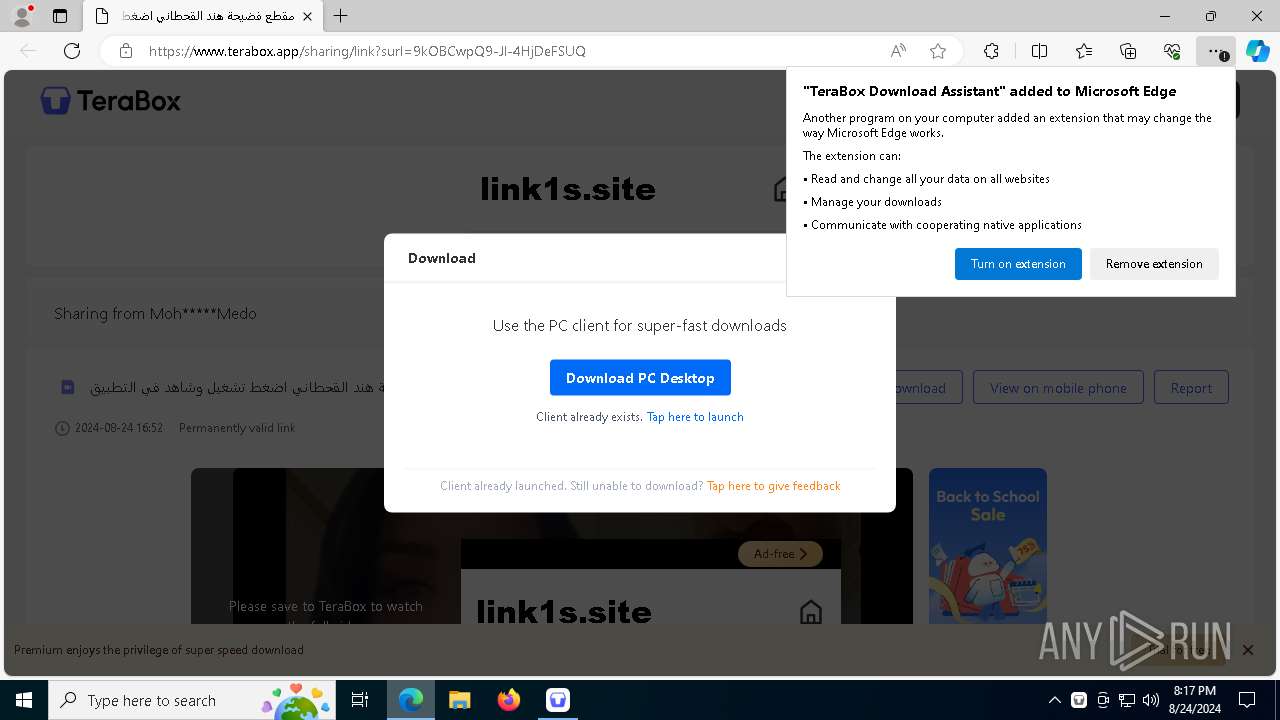
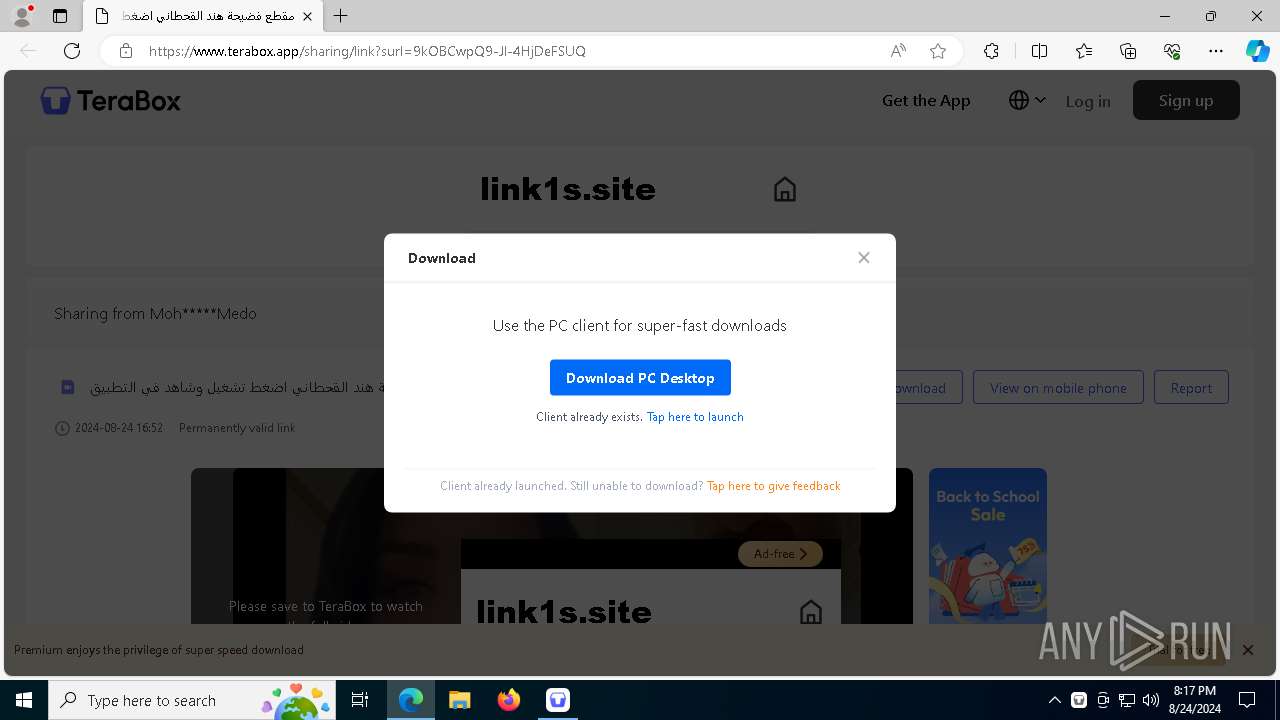
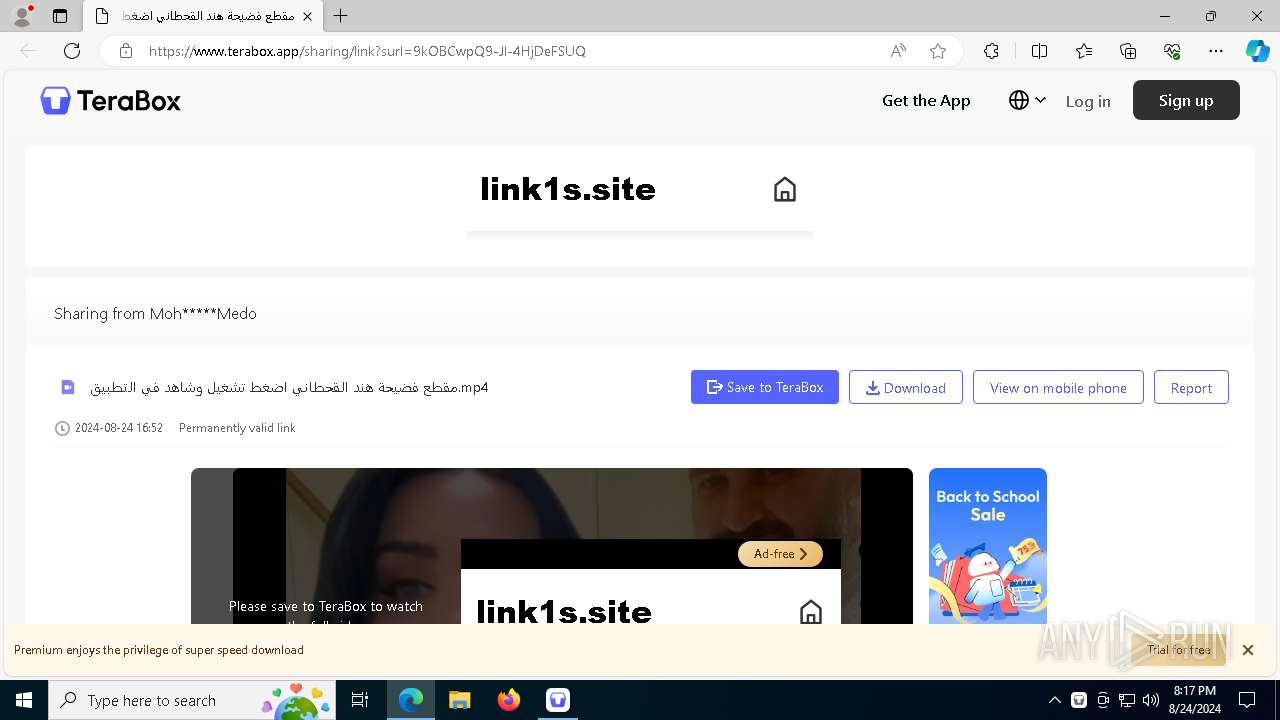
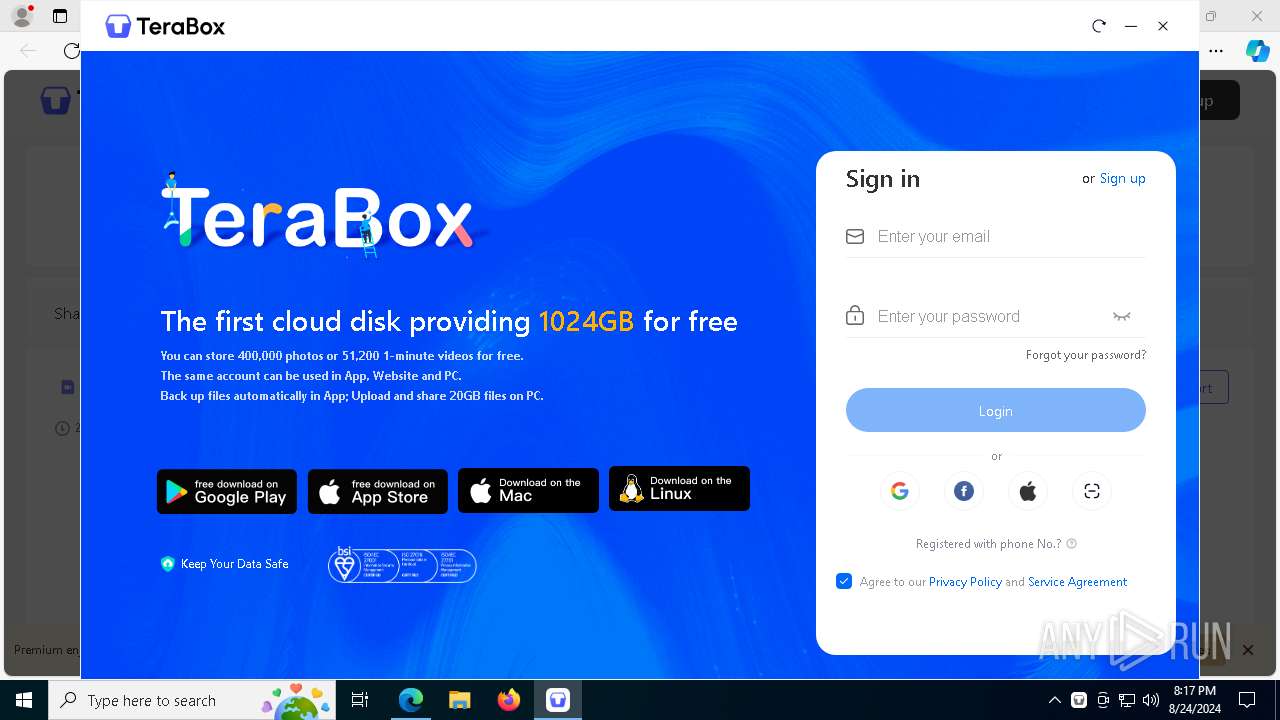
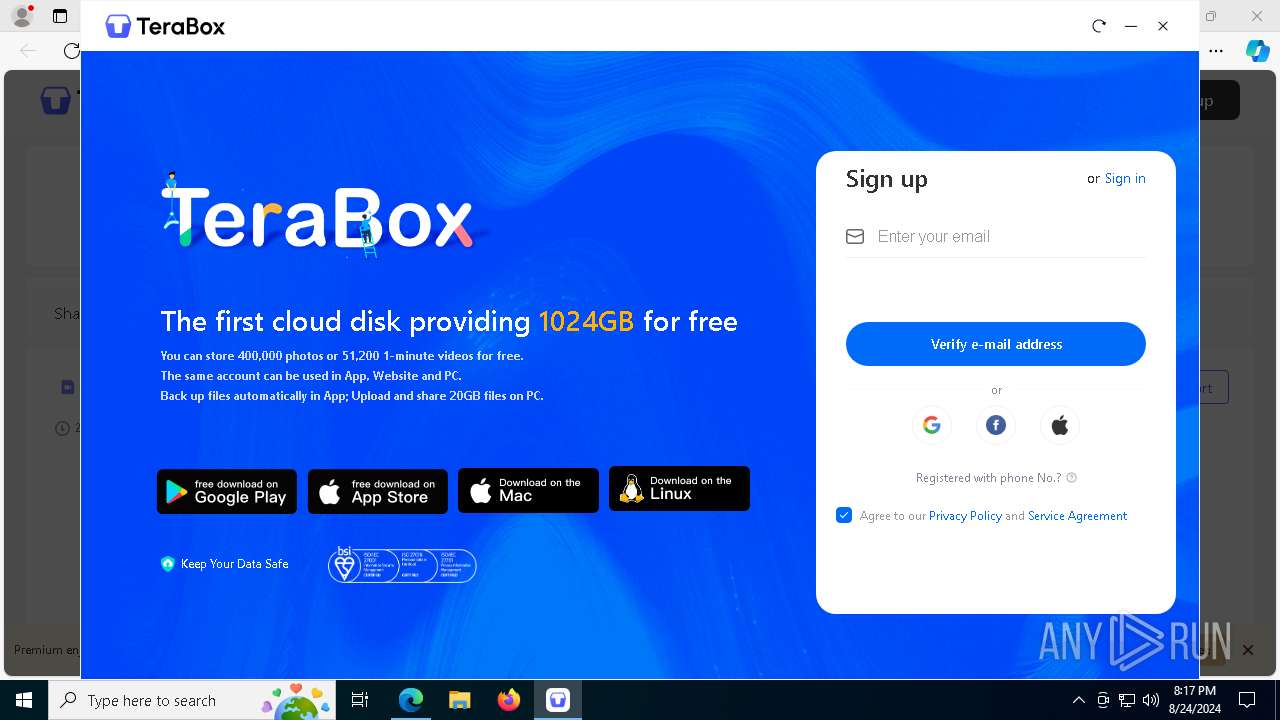
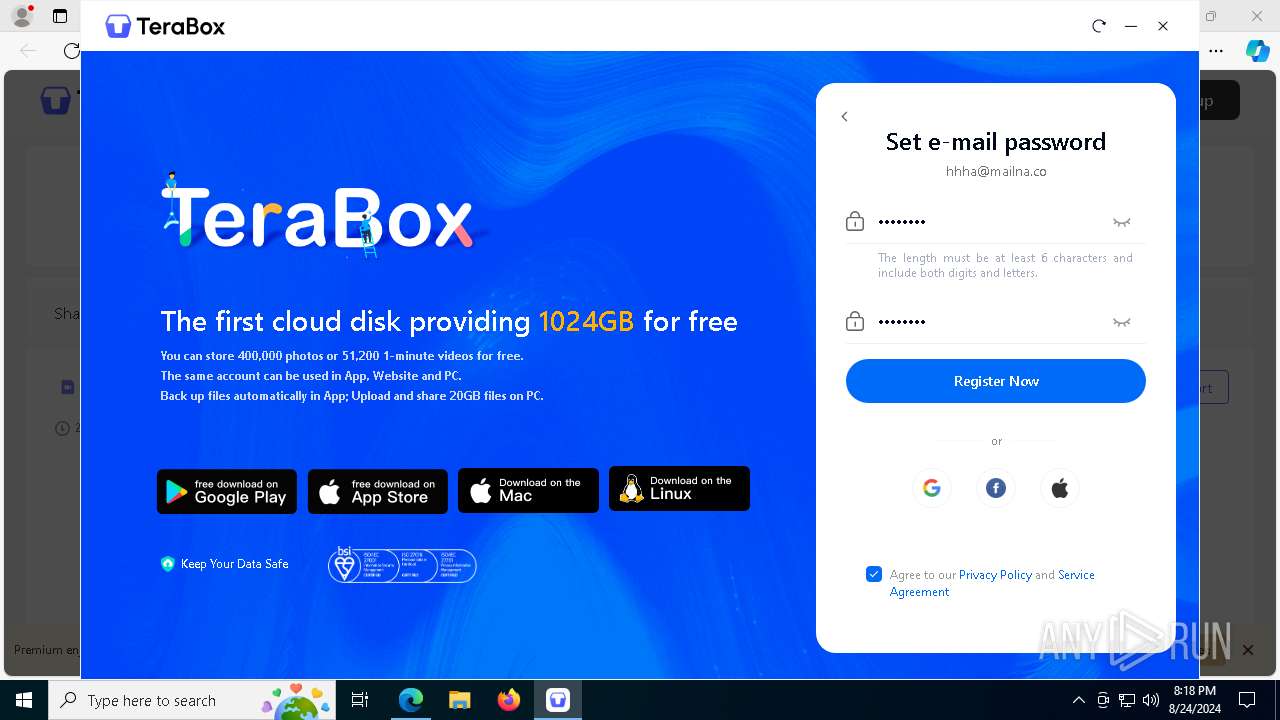
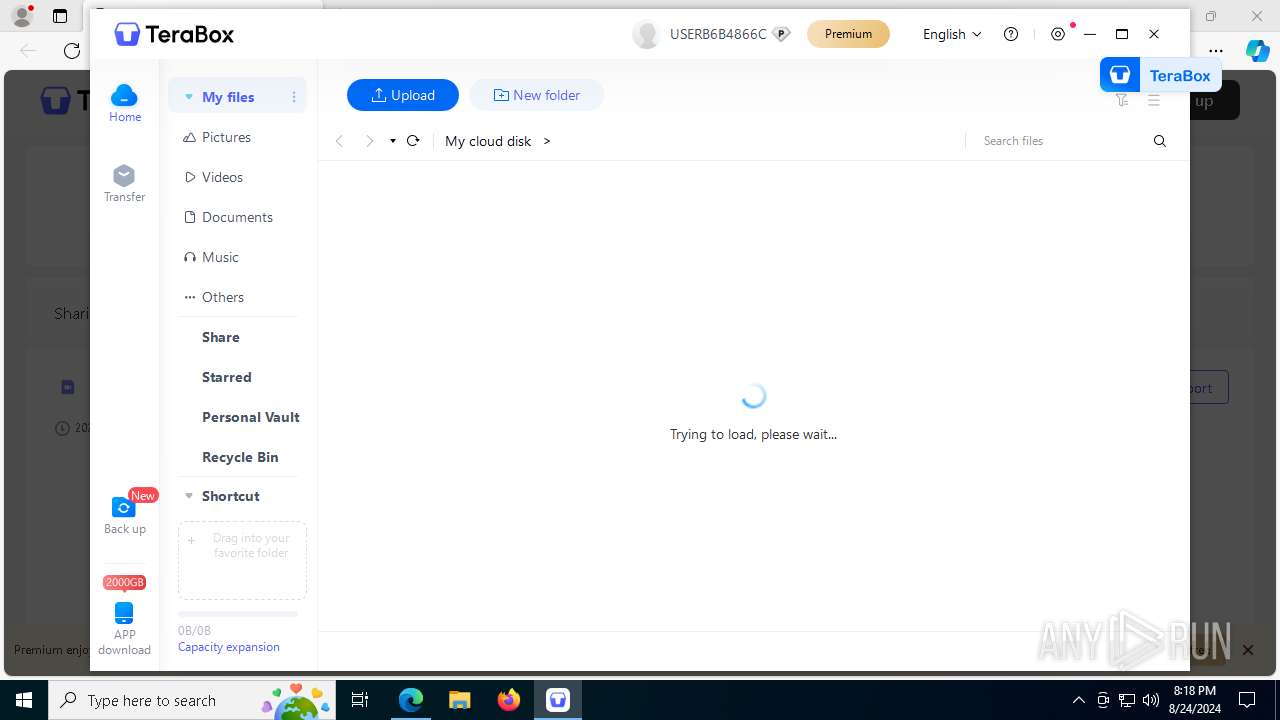
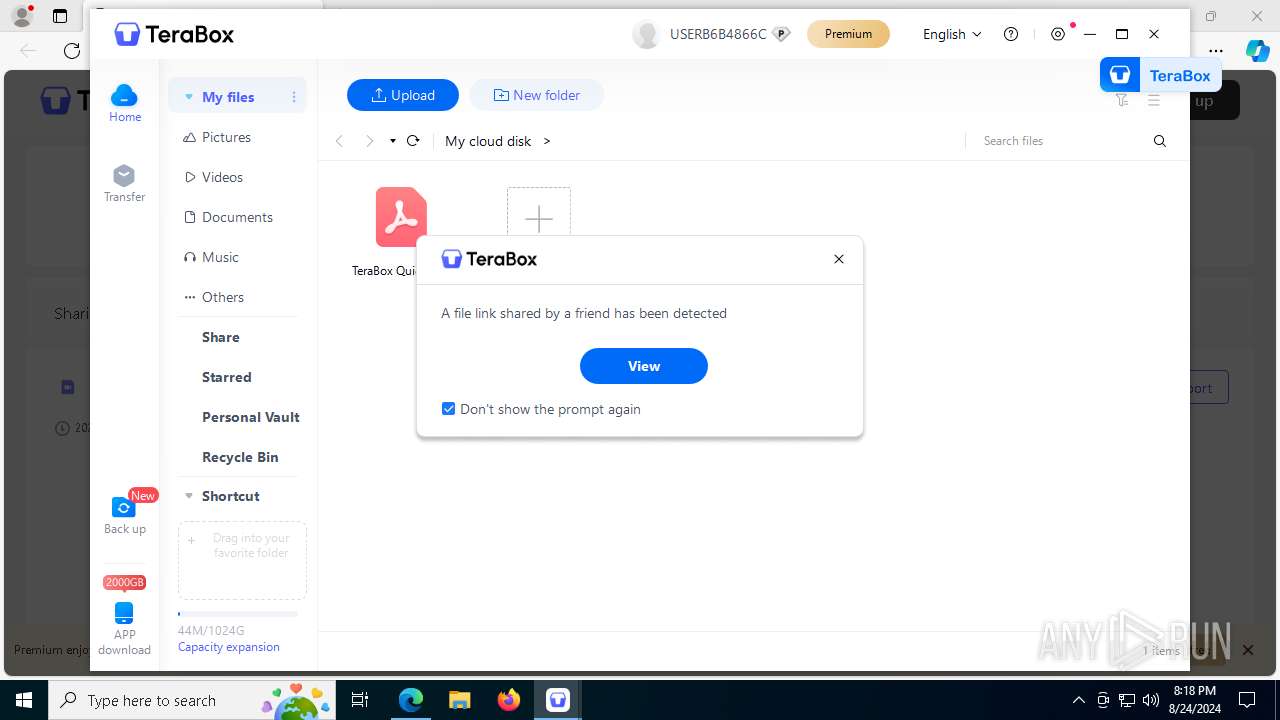
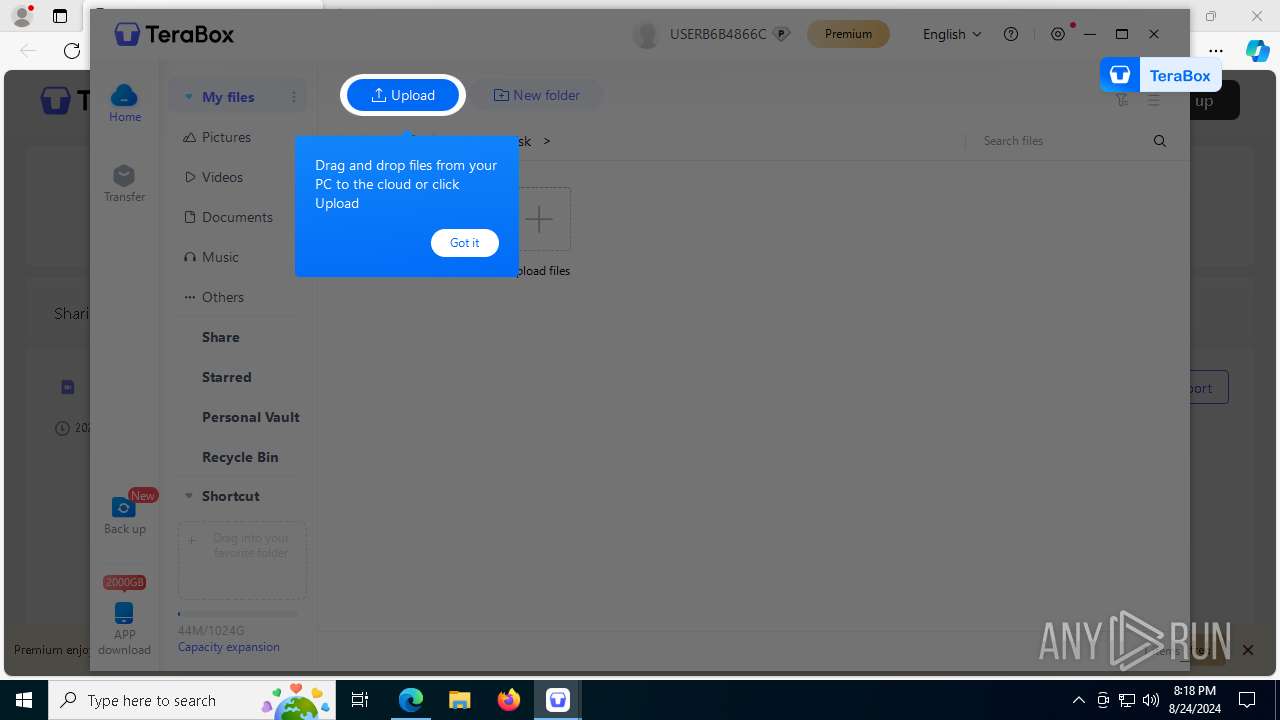
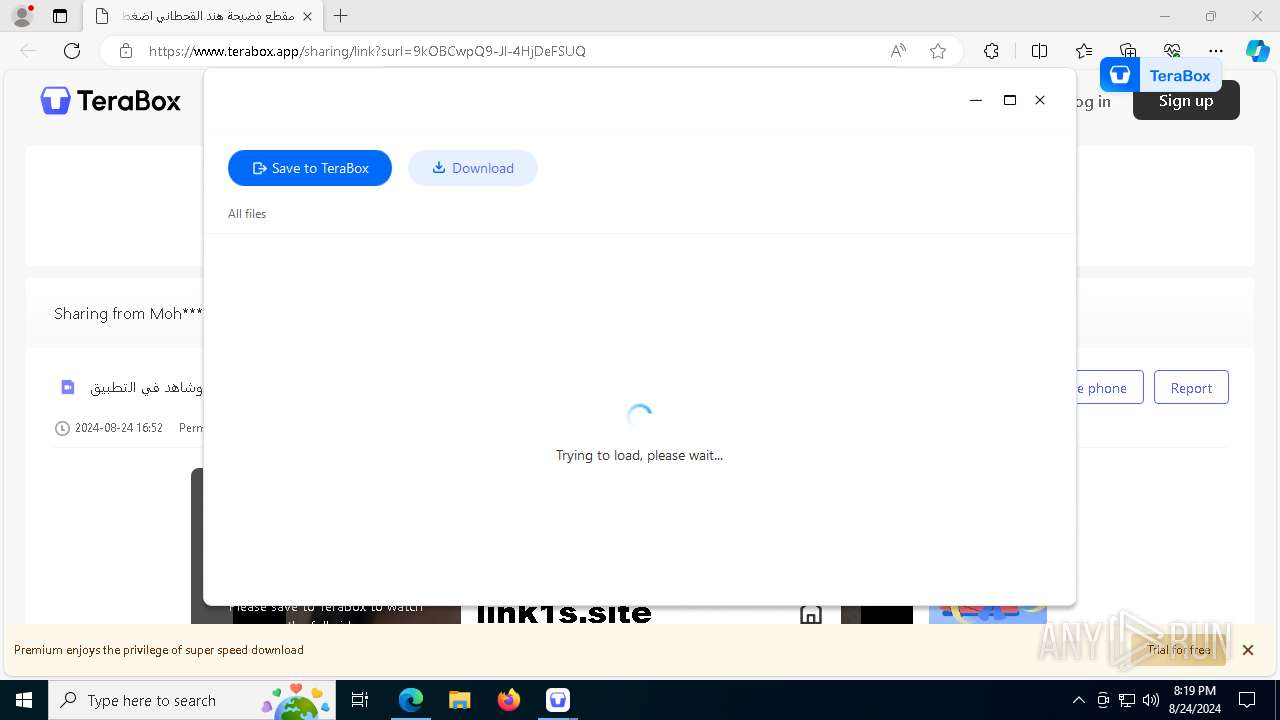
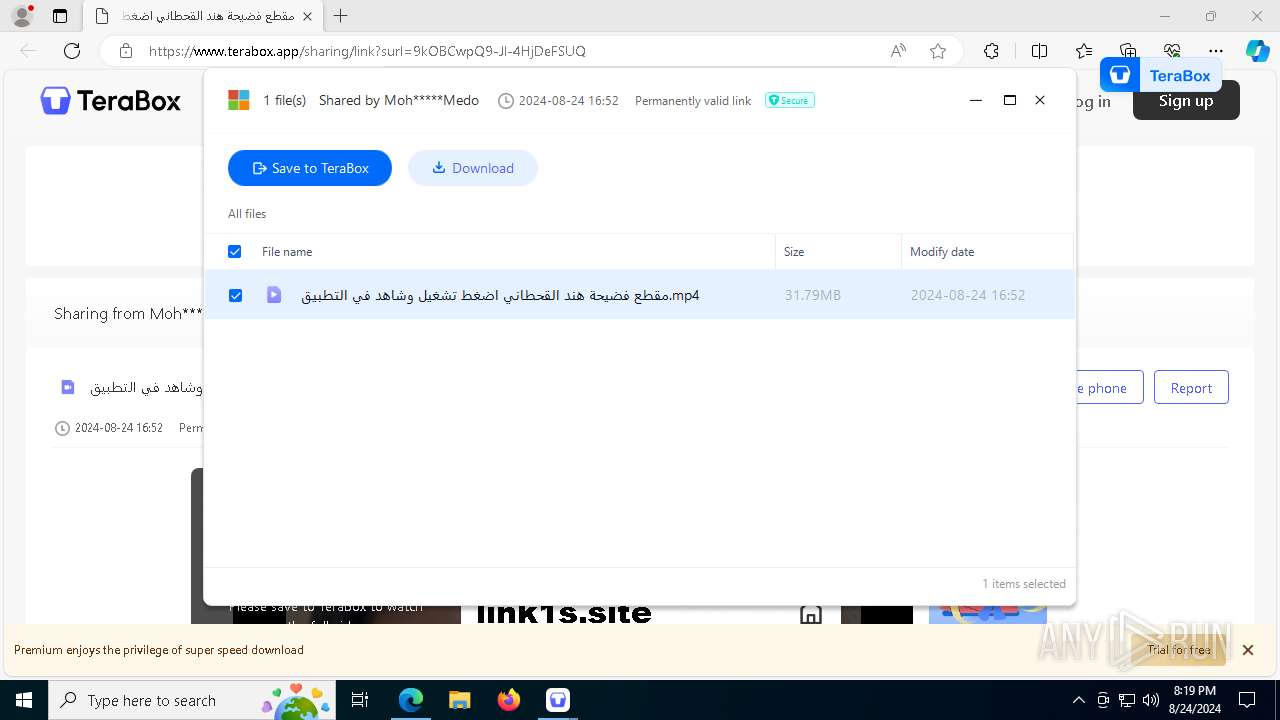
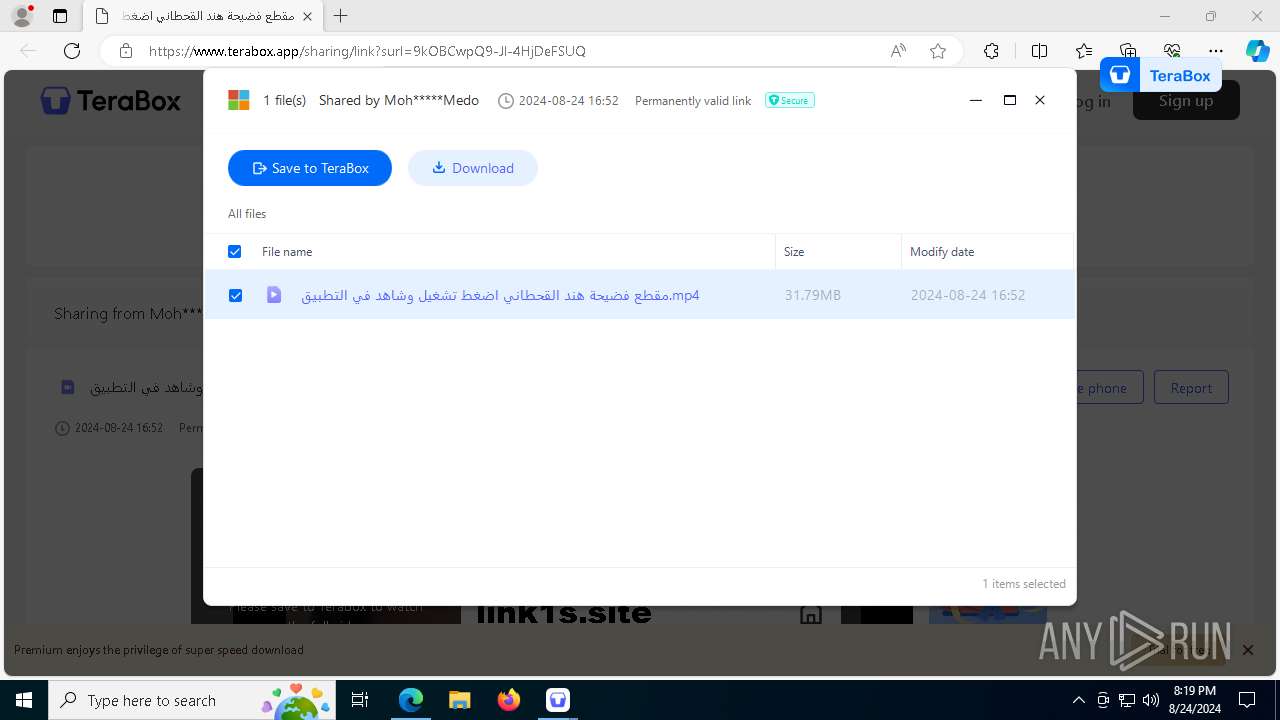
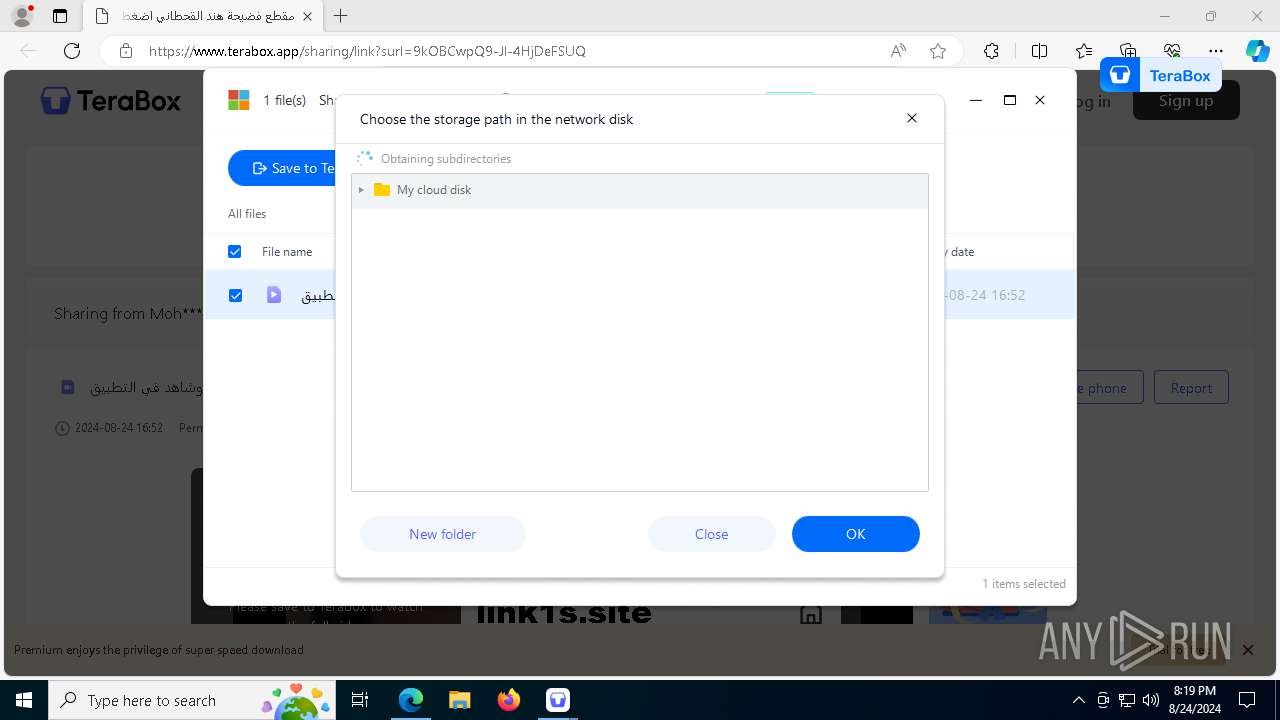
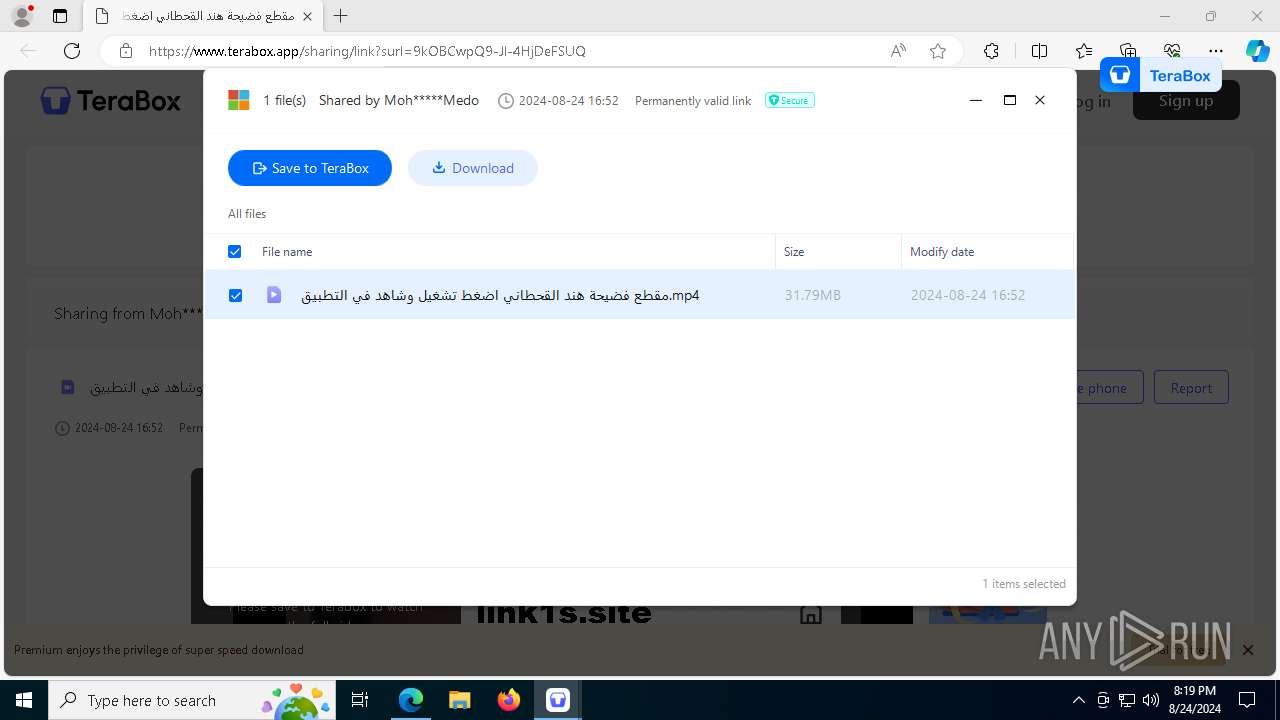
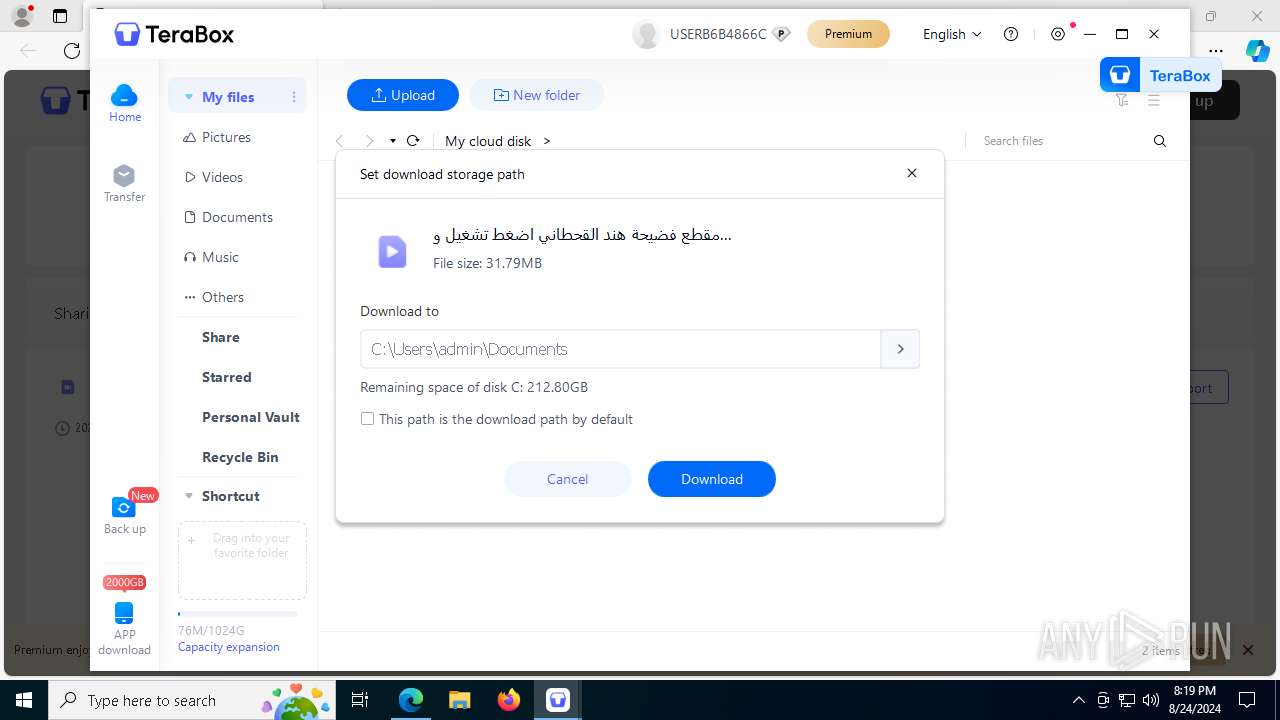
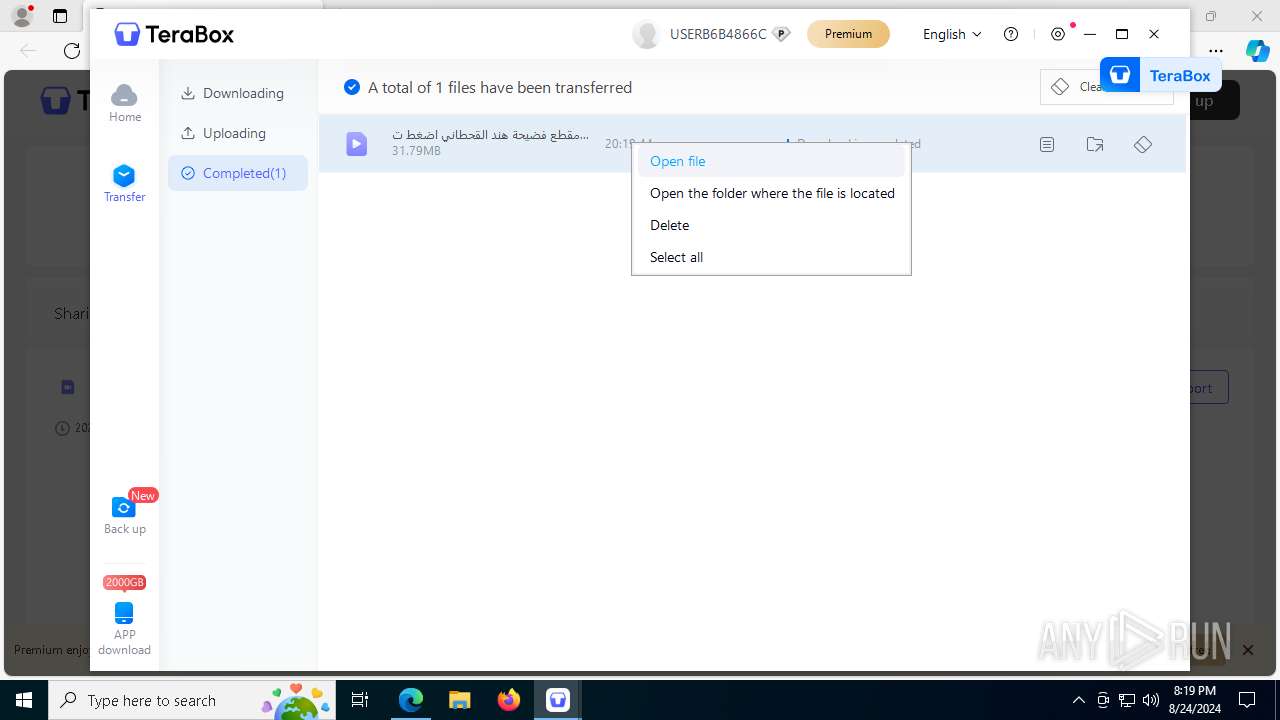
| URL: | https://1024terabox.com/s/19kOBCwpQ9-Jl-4HjDeFSUQ |
| Full analysis: | https://app.any.run/tasks/2b0d90d9-5989-4dd8-9bd7-9daddae84471 |
| Verdict: | Malicious activity |
| Analysis date: | August 24, 2024, 20:14:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C951B42A6C3CDE93F5FCFC1D80B5B36D |
| SHA1: | 84C43B56DAC21CC606C104E83002C6A5ED03CA14 |
| SHA256: | 021AD3E68CD1F9FED9EE5266F3C4F37E4716E72A9CAF529552DFF0B1343E3D01 |
| SSDEEP: | 3:N8+Xx3D5voG2Bn:2+h3D5vh2B |
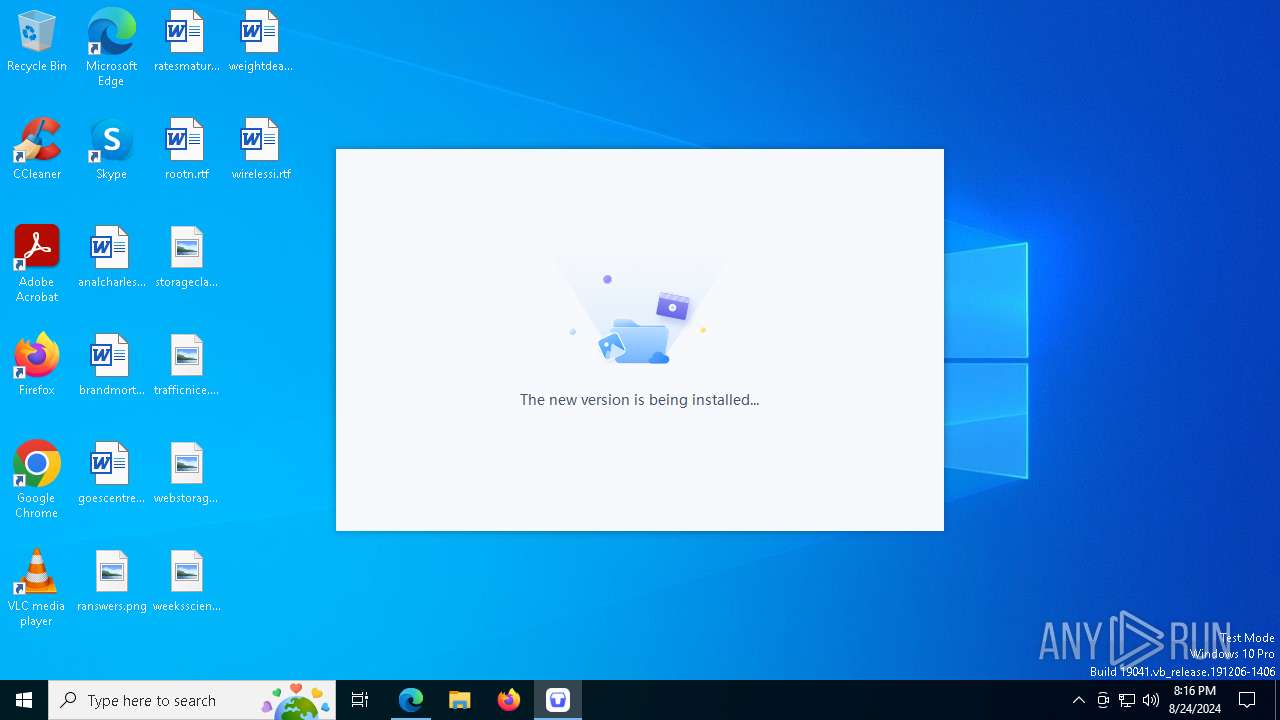
MALICIOUS
Changes the autorun value in the registry
- TeraBox.exe (PID: 1124)
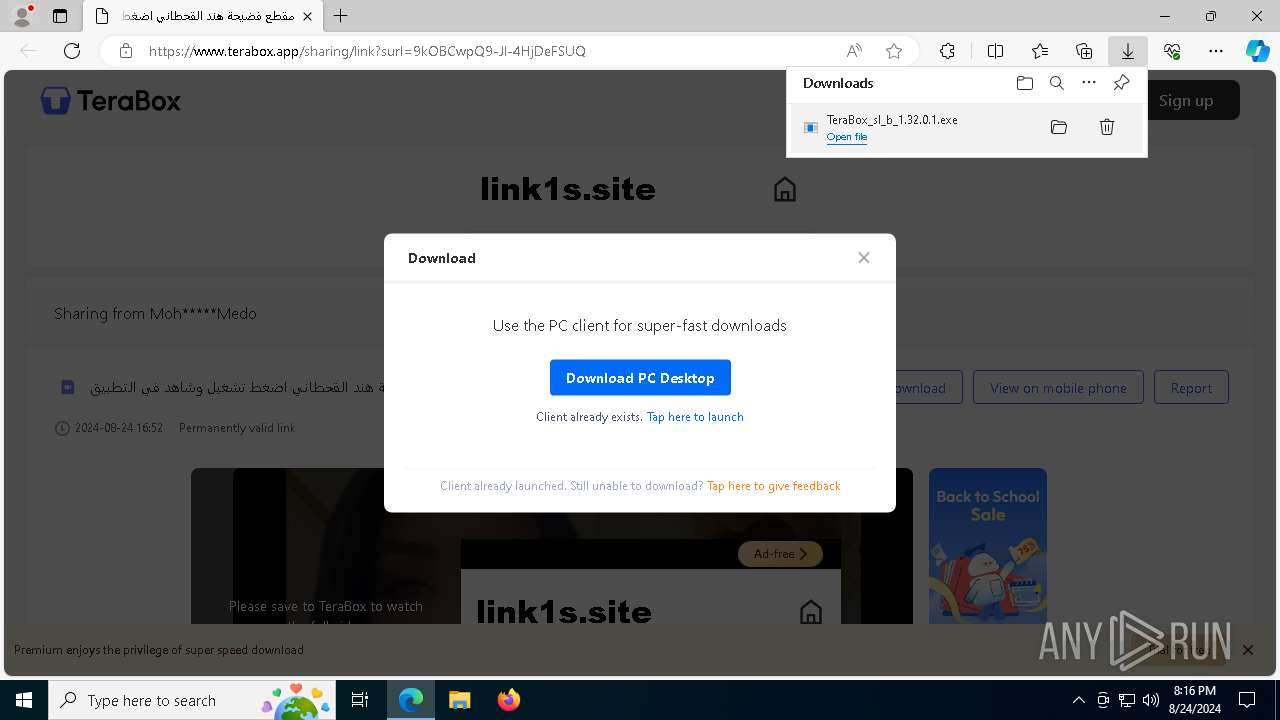
Registers / Runs the DLL via REGSVR32.EXE
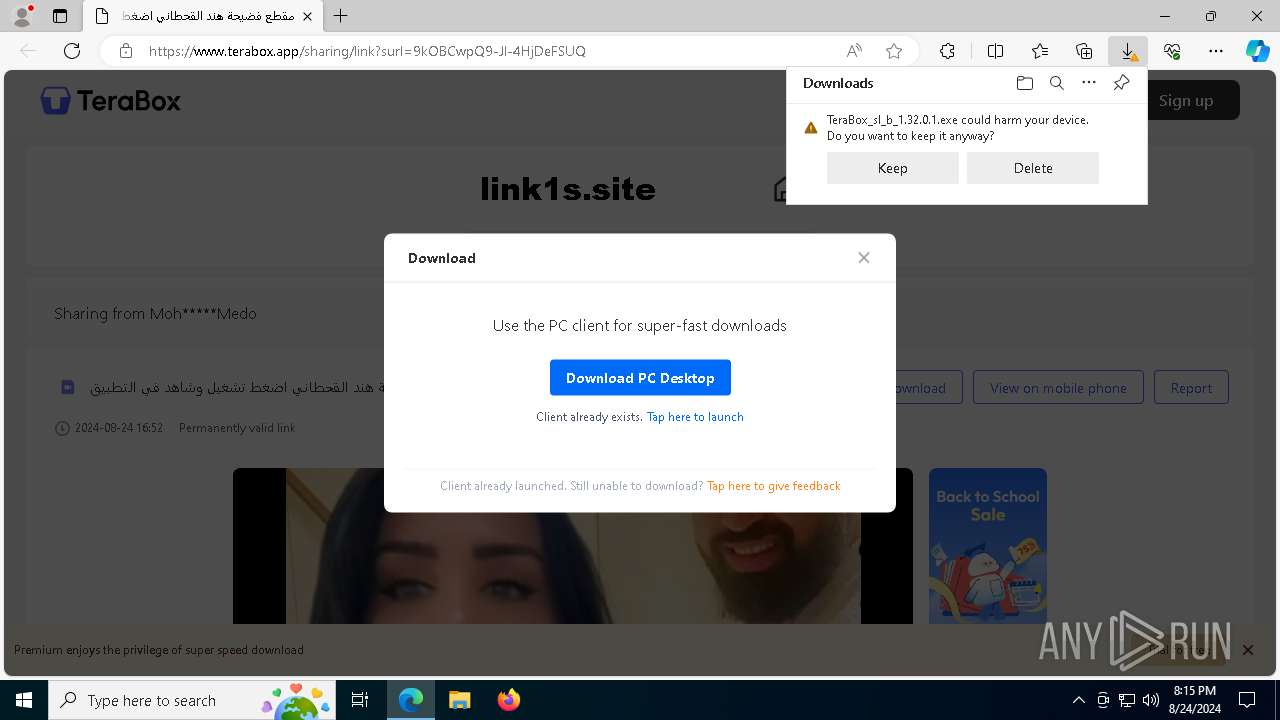
- TeraBox_sl_b_1.32.0.1.exe (PID: 3832)
XORed URL has been found (YARA)
- TeraBoxHost.exe (PID: 4436)
SUSPICIOUS
The process creates files with name similar to system file names
- TeraBox_sl_b_1.32.0.1.exe (PID: 3832)
- TeraBoxRender.exe (PID: 7552)
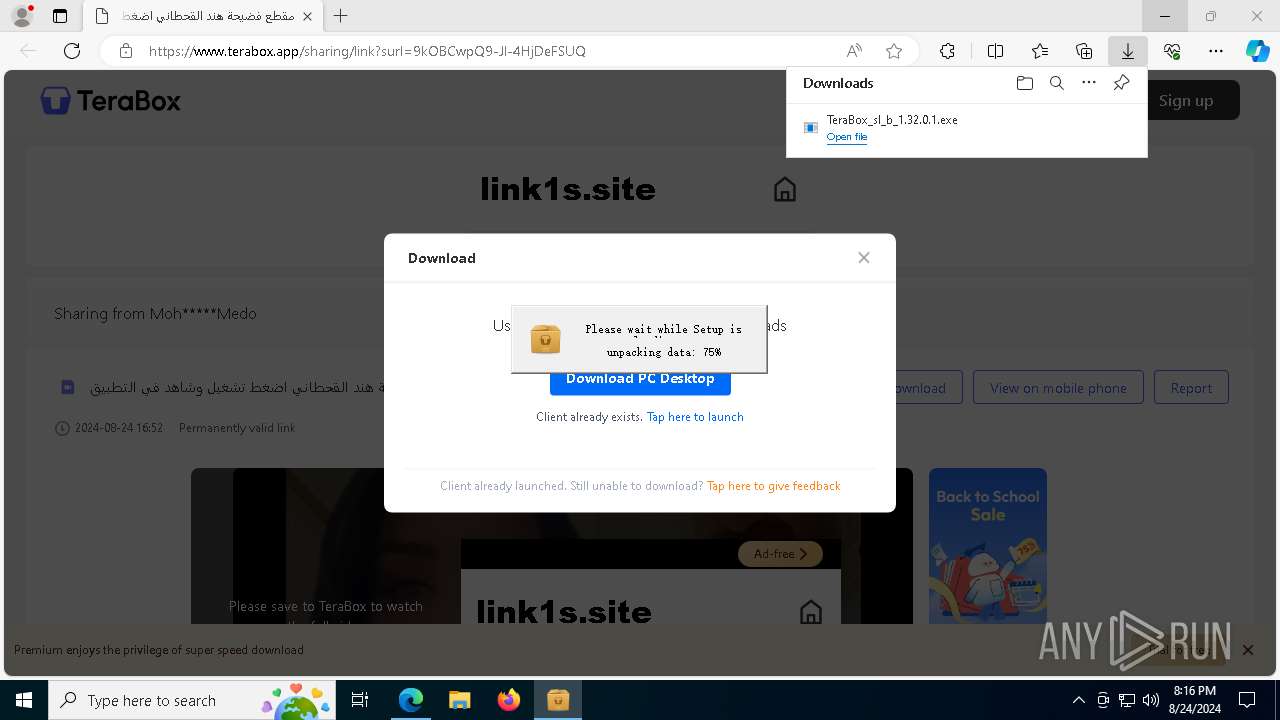
Drops the executable file immediately after the start
- TeraBox_sl_b_1.32.0.1.exe (PID: 3832)
Executable content was dropped or overwritten
- TeraBox_sl_b_1.32.0.1.exe (PID: 3832)
The process drops C-runtime libraries
- TeraBox_sl_b_1.32.0.1.exe (PID: 3832)
Malware-specific behavior (creating "System.dll" in Temp)
- TeraBox_sl_b_1.32.0.1.exe (PID: 3832)
Process drops legitimate windows executable
- TeraBox_sl_b_1.32.0.1.exe (PID: 3832)
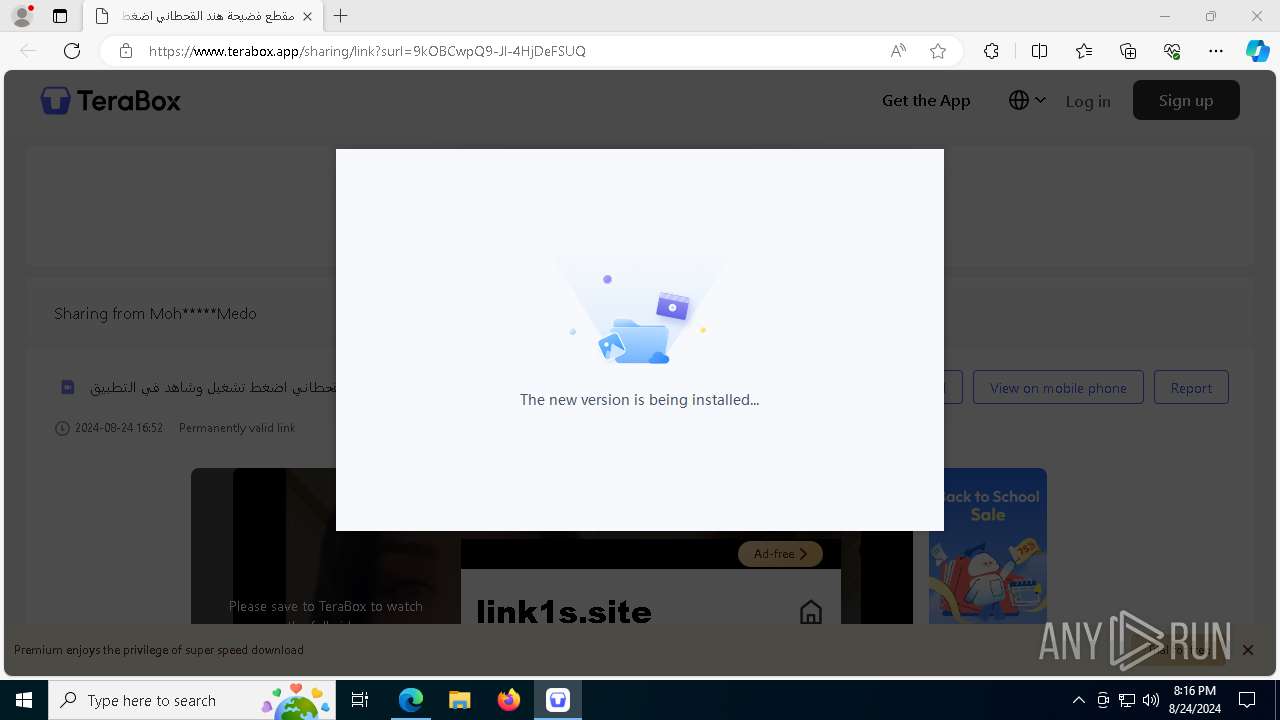
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 5284)
- regsvr32.exe (PID: 5344)
- regsvr32.exe (PID: 6624)
- TeraBox.exe (PID: 7620)
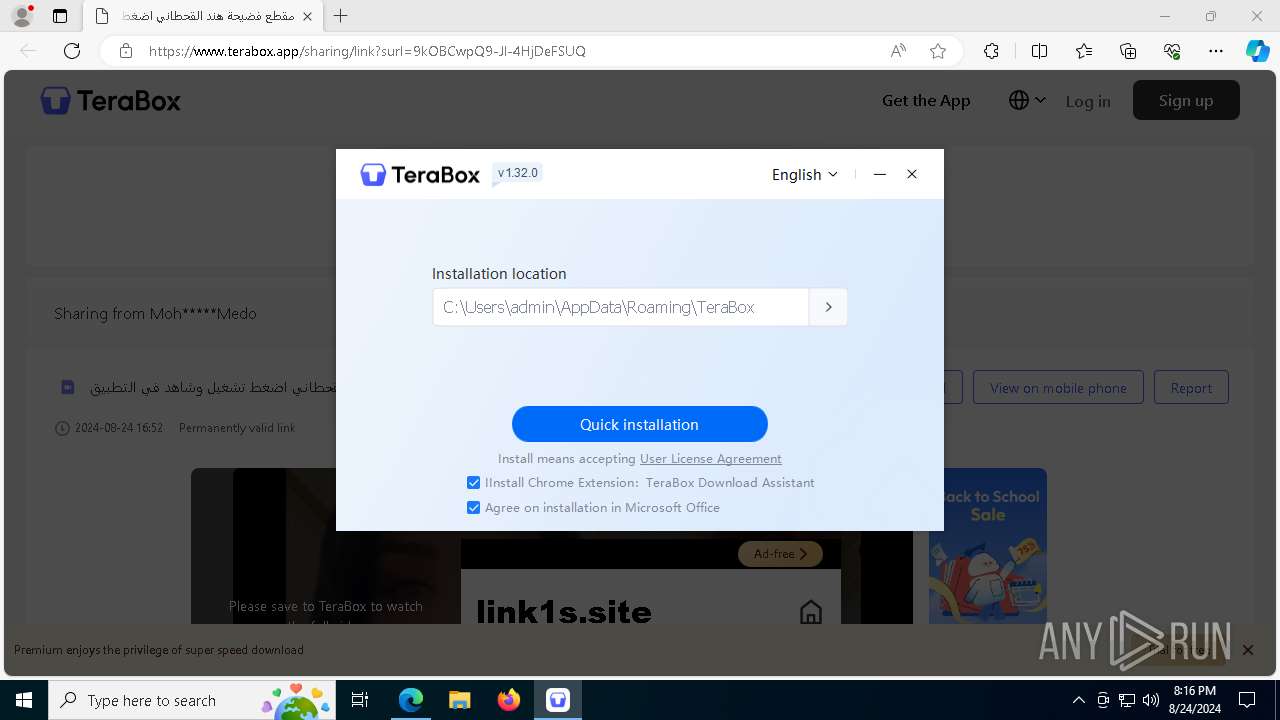
Creates a software uninstall entry
- TeraBox_sl_b_1.32.0.1.exe (PID: 3832)
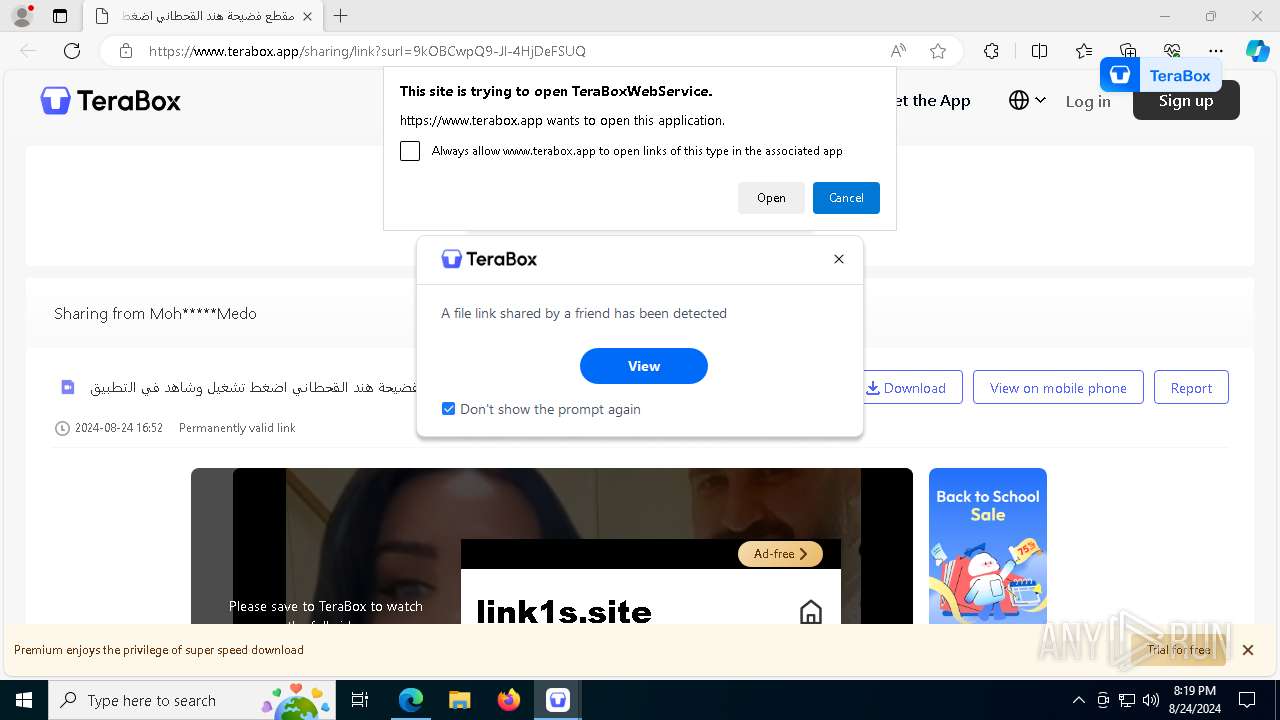
Reads security settings of Internet Explorer
- TeraBoxWebService.exe (PID: 7600)
- TeraBox.exe (PID: 7620)
- Autoupdate.exe (PID: 7696)
The process checks if it is being run in the virtual environment
- TeraBox.exe (PID: 7620)
Checks Windows Trust Settings
- TeraBox.exe (PID: 7620)
- YunUtilityService.exe (PID: 7984)
- Autoupdate.exe (PID: 7696)
Executes as Windows Service
- YunUtilityService.exe (PID: 7984)
Reads the date of Windows installation
- TeraBox.exe (PID: 7620)
Adds/modifies Windows certificates
- YunUtilityService.exe (PID: 7984)
INFO
Checks supported languages
- identity_helper.exe (PID: 7732)
- TeraBox.exe (PID: 1124)
- TeraBox_sl_b_1.32.0.1.exe (PID: 3832)
- TeraBoxWebService.exe (PID: 3916)
- YunUtilityService.exe (PID: 3384)
- TeraBox.exe (PID: 7620)
- TeraBoxWebService.exe (PID: 7600)
- TeraBoxRender.exe (PID: 2360)
- TeraBoxRender.exe (PID: 2192)
- TeraBoxRender.exe (PID: 7552)
- TeraBoxRender.exe (PID: 7412)
- TeraBoxRender.exe (PID: 6016)
- YunUtilityService.exe (PID: 7984)
- TeraBoxHost.exe (PID: 4436)
- TeraBoxRender.exe (PID: 5704)
- identity_helper.exe (PID: 2660)
- TeraBoxHost.exe (PID: 5532)
- Autoupdate.exe (PID: 7696)
- TeraBoxWebService.exe (PID: 1356)
- TeraBoxRender.exe (PID: 6312)
- vlc.exe (PID: 4732)
Reads Environment values
- identity_helper.exe (PID: 7732)
- TeraBox_sl_b_1.32.0.1.exe (PID: 3832)
- identity_helper.exe (PID: 2660)
Reads the computer name
- identity_helper.exe (PID: 7732)
- TeraBox_sl_b_1.32.0.1.exe (PID: 3832)
- TeraBox.exe (PID: 1124)
- YunUtilityService.exe (PID: 3384)
- TeraBoxWebService.exe (PID: 7600)
- TeraBox.exe (PID: 7620)
- TeraBoxRender.exe (PID: 7552)
- TeraBoxRender.exe (PID: 2360)
- TeraBoxRender.exe (PID: 7412)
- YunUtilityService.exe (PID: 7984)
- TeraBoxHost.exe (PID: 4436)
- TeraBoxHost.exe (PID: 5532)
- identity_helper.exe (PID: 2660)
- vlc.exe (PID: 4732)
- Autoupdate.exe (PID: 7696)
Application launched itself
- msedge.exe (PID: 6632)
Create files in a temporary directory
- TeraBox_sl_b_1.32.0.1.exe (PID: 3832)
- TeraBox.exe (PID: 7620)
- TeraBoxRender.exe (PID: 2360)
Creates files or folders in the user directory
- TeraBox_sl_b_1.32.0.1.exe (PID: 3832)
- TeraBox.exe (PID: 7620)
- TeraBoxWebService.exe (PID: 7600)
- TeraBox.exe (PID: 1124)
- TeraBoxHost.exe (PID: 4436)
- TeraBoxHost.exe (PID: 5532)
- Autoupdate.exe (PID: 7696)
Executable content was dropped or overwritten
- msedge.exe (PID: 6632)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6632)
Reads the machine GUID from the registry
- TeraBox.exe (PID: 7620)
- TeraBoxRender.exe (PID: 2360)
- YunUtilityService.exe (PID: 7984)
- TeraBoxHost.exe (PID: 4436)
- Autoupdate.exe (PID: 7696)
Checks proxy server information
- TeraBoxWebService.exe (PID: 7600)
- TeraBox.exe (PID: 7620)
- Autoupdate.exe (PID: 7696)
Process checks computer location settings
- TeraBox.exe (PID: 7620)
- TeraBoxRender.exe (PID: 2192)
- TeraBoxRender.exe (PID: 6016)
- TeraBoxRender.exe (PID: 5704)
- TeraBoxRender.exe (PID: 6312)
Reads the software policy settings
- TeraBox.exe (PID: 7620)
- YunUtilityService.exe (PID: 7984)
- TeraBoxRender.exe (PID: 2360)
- Autoupdate.exe (PID: 7696)
Creates files in the program directory
- TeraBoxHost.exe (PID: 4436)
VMProtect protector has been detected
- TeraBoxHost.exe (PID: 4436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(4436) TeraBoxHost.exe
Decrypted-URLs (1)https://terabox.com/statistics?clienttype=9&version=1.0.0.7
Total processes
232
Monitored processes
93
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1340 --field-trial-handle=2416,i,8019724943362928241,9326193409064312173,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 752 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5612 --field-trial-handle=2416,i,8019724943362928241,9326193409064312173,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 936 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=36 --mojo-platform-channel-handle=7372 --field-trial-handle=2416,i,8019724943362928241,9326193409064312173,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1084 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=6176 --field-trial-handle=2416,i,8019724943362928241,9326193409064312173,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5188 --field-trial-handle=2416,i,8019724943362928241,9326193409064312173,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
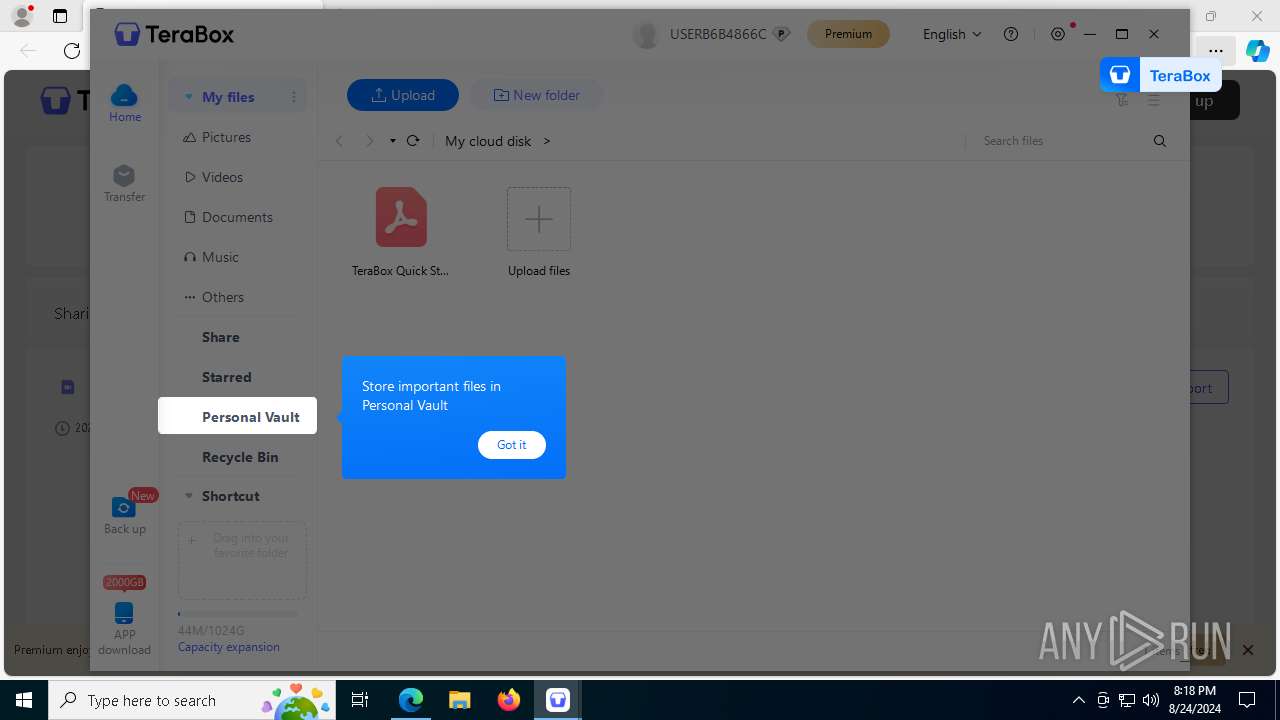
| 1124 | "C:\Users\admin\AppData\Roaming\TeraBox\TeraBox.exe" -install "createdetectstartup" -install "btassociation" -install "createshortcut" "0" -install "createstartup" | C:\Users\admin\AppData\Roaming\TeraBox\TeraBox.exe | TeraBox_sl_b_1.32.0.1.exe | ||||||||||||
User: admin Company: Flextech Inc. Integrity Level: HIGH Description: TeraBox Exit code: 1 Version: 1.32.0.1 Modules
| |||||||||||||||
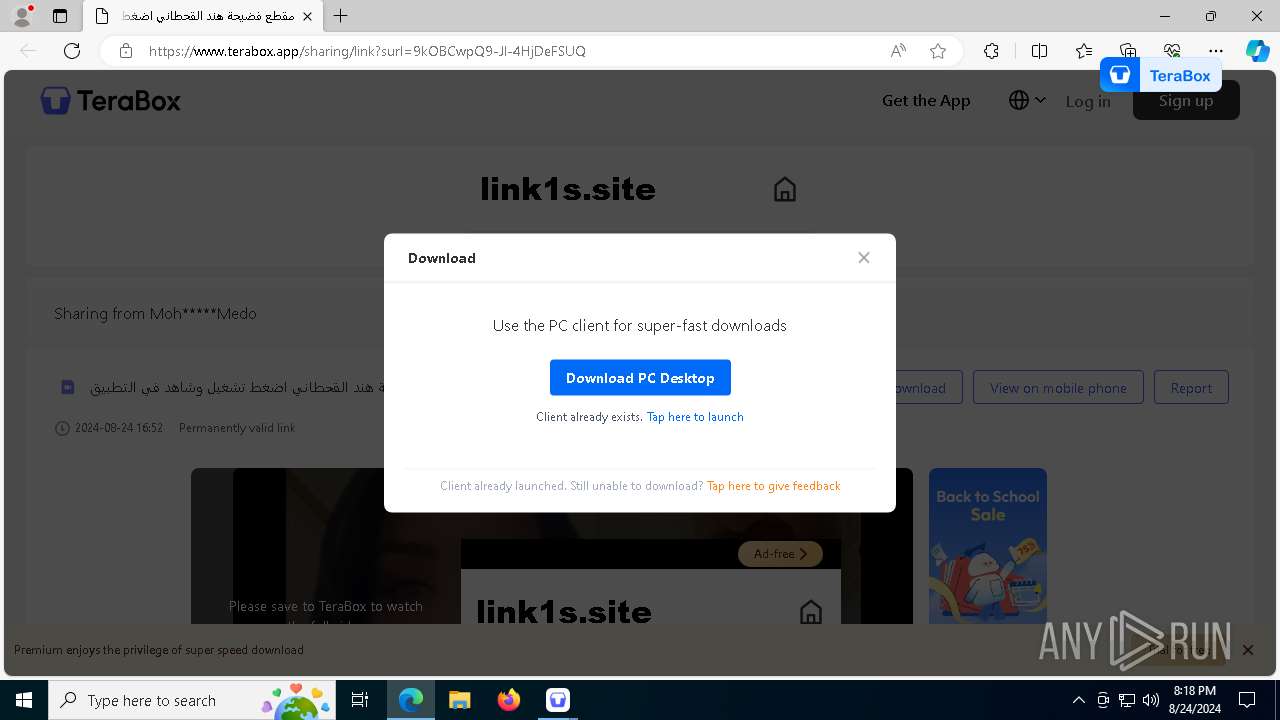
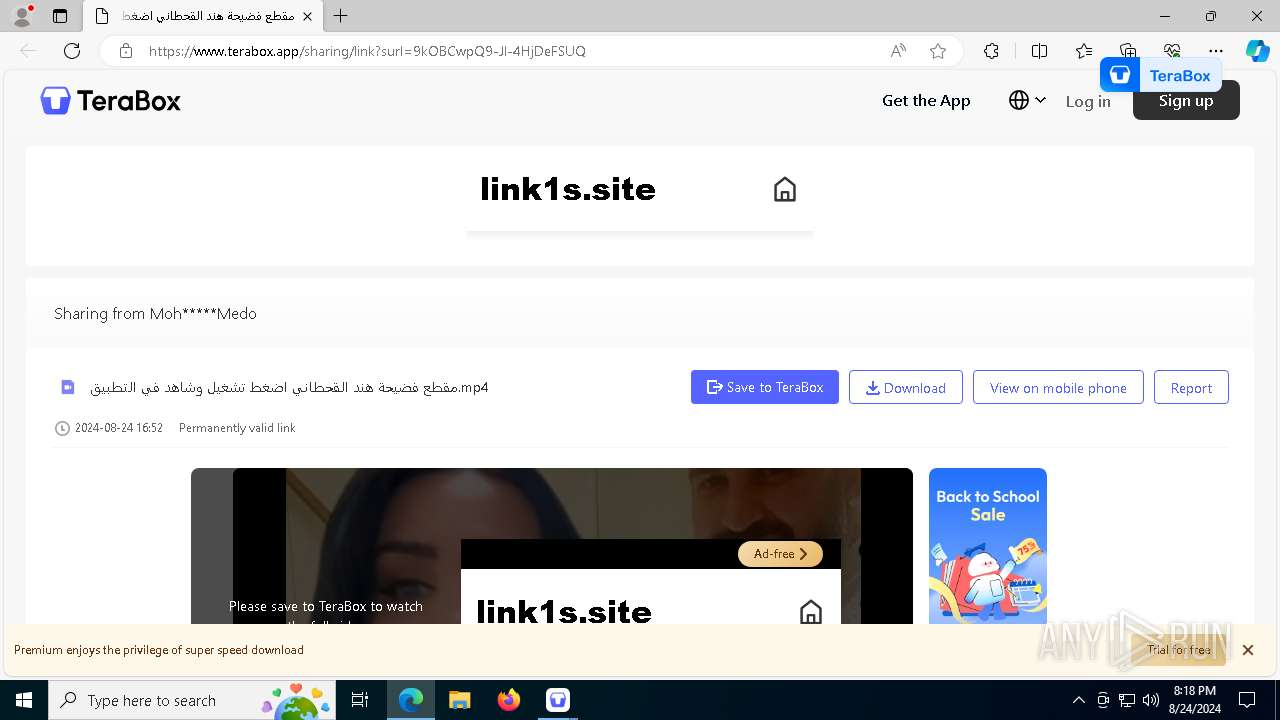
| 1356 | "C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxWebService.exe" "terabox://launch-app/" | C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxWebService.exe | — | msedge.exe | |||||||||||
User: admin Company: Flextech Inc. Integrity Level: MEDIUM Description: TeraBoxWebService Exit code: 0 Version: 1.32.0.1 Modules
| |||||||||||||||
| 2032 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6848 --field-trial-handle=2416,i,8019724943362928241,9326193409064312173,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2192 | "C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxRender.exe" --type=renderer --no-sandbox --log-file="C:\Users\admin\AppData\Roaming\TeraBox\debug.log" --field-trial-handle=2612,9792675490102933245,9597618965772408857,131072 --enable-features=CastMediaRouteProvider --disable-gpu-compositing --lang=en-US --locales-dir-path="C:\Users\admin\AppData\Roaming\TeraBox\browserres\locales" --log-file="C:\Users\admin\AppData\Roaming\TeraBox\debug.log" --log-severity=disable --resources-dir-path="C:\Users\admin\AppData\Roaming\TeraBox\browserres" --user-agent="Mozilla/5.0; (Windows NT 10.0; WOW64); AppleWebKit/537.36; (KHTML, like Gecko); Chrome/86.0.4240.198; Safari/537.36; terabox;1.32.0.1;PC;PC-Windows;10.0.19045;WindowsTeraBox" --disable-extensions --ppapi-flash-path="C:\Users\admin\AppData\Roaming\TeraBox\pepflashplayer.dll" --ppapi-flash-version=20.0.0.306 --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4248 /prefetch:1 | C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxRender.exe | — | TeraBox.exe | |||||||||||
User: admin Company: Flextech Inc. Integrity Level: MEDIUM Description: TeraBoxRender Version: 2.0.1.1 Modules
| |||||||||||||||
| 2360 | "C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxRender.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=2612,9792675490102933245,9597618965772408857,131072 --enable-features=CastMediaRouteProvider --lang=en-US --service-sandbox-type=network --no-sandbox --locales-dir-path="C:\Users\admin\AppData\Roaming\TeraBox\browserres\locales" --log-file="C:\Users\admin\AppData\Roaming\TeraBox\debug.log" --log-severity=disable --resources-dir-path="C:\Users\admin\AppData\Roaming\TeraBox\browserres" --user-agent="Mozilla/5.0; (Windows NT 10.0; WOW64); AppleWebKit/537.36; (KHTML, like Gecko); Chrome/86.0.4240.198; Safari/537.36; terabox;1.32.0.1;PC;PC-Windows;10.0.19045;WindowsTeraBox" --lang=en-US --log-file="C:\Users\admin\AppData\Roaming\TeraBox\debug.log" --mojo-platform-channel-handle=2736 /prefetch:8 | C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxRender.exe | TeraBox.exe | ||||||||||||
User: admin Company: Flextech Inc. Integrity Level: MEDIUM Description: TeraBoxRender Version: 2.0.1.1 Modules
| |||||||||||||||
Total events
52 635
Read events
52 245
Write events
375
Delete events
15
Modification events
| (PID) Process: | (6632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6632) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6632) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
88
Suspicious files
751
Text files
295
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF11d9f2.TMP | — | |
MD5:— | SHA256:— | |||
| 6632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11d9f2.TMP | — | |
MD5:— | SHA256:— | |||
| 6632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11d9f2.TMP | — | |
MD5:— | SHA256:— | |||
| 6632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11d9f2.TMP | — | |
MD5:— | SHA256:— | |||
| 6632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF11da40.TMP | — | |
MD5:— | SHA256:— | |||
| 6632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
276
DNS requests
225
Threats
67
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5244 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7896 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9826d128-542d-4289-a6ad-0c4056553914?P1=1725090369&P2=404&P3=2&P4=UekqkKjb0a0%2fey4ixGiVuqPxwRcoGNJqOK%2fXIrOdmWImlwFonUvXiyvpn0b8EVA98WORhkb7OYUXuUIYaAkKhQ%3d%3d | unknown | — | — | whitelisted |
460 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7896 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9826d128-542d-4289-a6ad-0c4056553914?P1=1725090369&P2=404&P3=2&P4=UekqkKjb0a0%2fey4ixGiVuqPxwRcoGNJqOK%2fXIrOdmWImlwFonUvXiyvpn0b8EVA98WORhkb7OYUXuUIYaAkKhQ%3d%3d | unknown | — | — | whitelisted |
7896 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9826d128-542d-4289-a6ad-0c4056553914?P1=1725090369&P2=404&P3=2&P4=UekqkKjb0a0%2fey4ixGiVuqPxwRcoGNJqOK%2fXIrOdmWImlwFonUvXiyvpn0b8EVA98WORhkb7OYUXuUIYaAkKhQ%3d%3d | unknown | — | — | whitelisted |
7896 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9826d128-542d-4289-a6ad-0c4056553914?P1=1725090369&P2=404&P3=2&P4=UekqkKjb0a0%2fey4ixGiVuqPxwRcoGNJqOK%2fXIrOdmWImlwFonUvXiyvpn0b8EVA98WORhkb7OYUXuUIYaAkKhQ%3d%3d | unknown | — | — | whitelisted |
7896 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9826d128-542d-4289-a6ad-0c4056553914?P1=1725090369&P2=404&P3=2&P4=UekqkKjb0a0%2fey4ixGiVuqPxwRcoGNJqOK%2fXIrOdmWImlwFonUvXiyvpn0b8EVA98WORhkb7OYUXuUIYaAkKhQ%3d%3d | unknown | — | — | whitelisted |
7896 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9826d128-542d-4289-a6ad-0c4056553914?P1=1725090369&P2=404&P3=2&P4=UekqkKjb0a0%2fey4ixGiVuqPxwRcoGNJqOK%2fXIrOdmWImlwFonUvXiyvpn0b8EVA98WORhkb7OYUXuUIYaAkKhQ%3d%3d | unknown | — | — | whitelisted |
7896 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7b9cac0d-9ca2-42ef-9c46-ce975d51335a?P1=1724991979&P2=404&P3=2&P4=fMvgVDDEpLp%2fiX03GPqYchMZRP6dO8InlJa51ES6gt6rE4OpNWt7sxueuxAkmtWvJ%2bS%2boaQUBiQ58qDj81hWlA%3d%3d | unknown | — | — | whitelisted |
7896 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/062b65bc-b6a4-4f5a-8413-7218292237fe?P1=1724901148&P2=404&P3=2&P4=Vy4QQY06DX8kg01gTvUSgeN1XgdEqJ3t%2bH%2bSCodM7fbxAlAE534L7i9tyMuIEL5CQ4gHntV0QEfupf4Y6PwyKA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3376 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3308 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6960 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6960 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6632 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6960 | msedge.exe | 210.148.85.38:443 | 1024terabox.com | Internet Initiative Japan Inc. | JP | unknown |
6960 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6960 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
1024terabox.com |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.terabox.app |
| unknown |
www.staticcc.com |
| unknown |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6960 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
6960 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
6960 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
6960 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
6960 | msedge.exe | Misc activity | ET INFO Observed File Sharing Domain (terabox .com in TLS SNI) |
6960 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
6960 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
6960 | msedge.exe | Misc activity | ET INFO Observed File Sharing Domain (terabox .com in TLS SNI) |
6960 | msedge.exe | Misc activity | ET INFO Observed File Sharing Domain (terabox .com in TLS SNI) |
6960 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
Process | Message |
|---|---|
TeraBoxHost.exe | vast_media--[2024-08-24 20:17:07:360] Initialized sdl_video_render_driver=software
|
TeraBoxHost.exe | vast_media--[2024-08-24 20:17:07:360] Initialized sdl_audio_play_driver=directsound
|
TeraBoxHost.exe | vast_media--[2024-08-24 20:17:07:360] Initialized hardware_type=3001
|
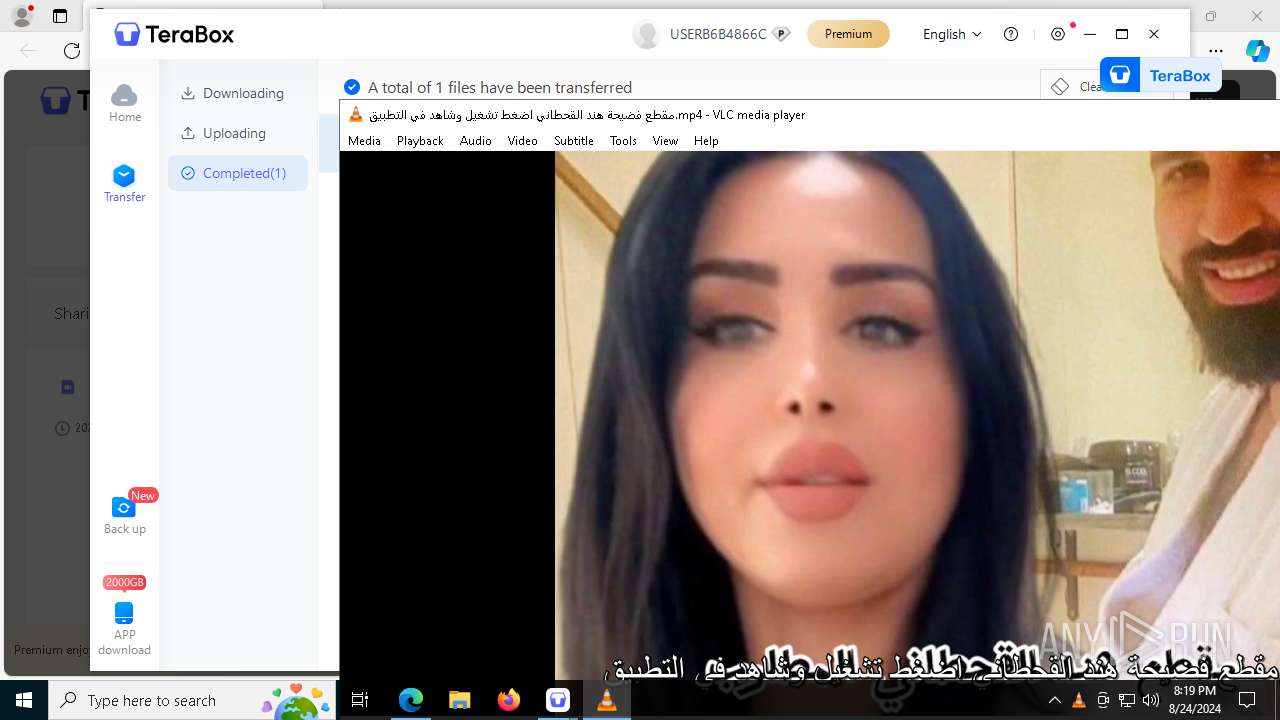
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=x86_64-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=x86_64-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x64/contrib/x86_64-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: searching plug-in modules
|