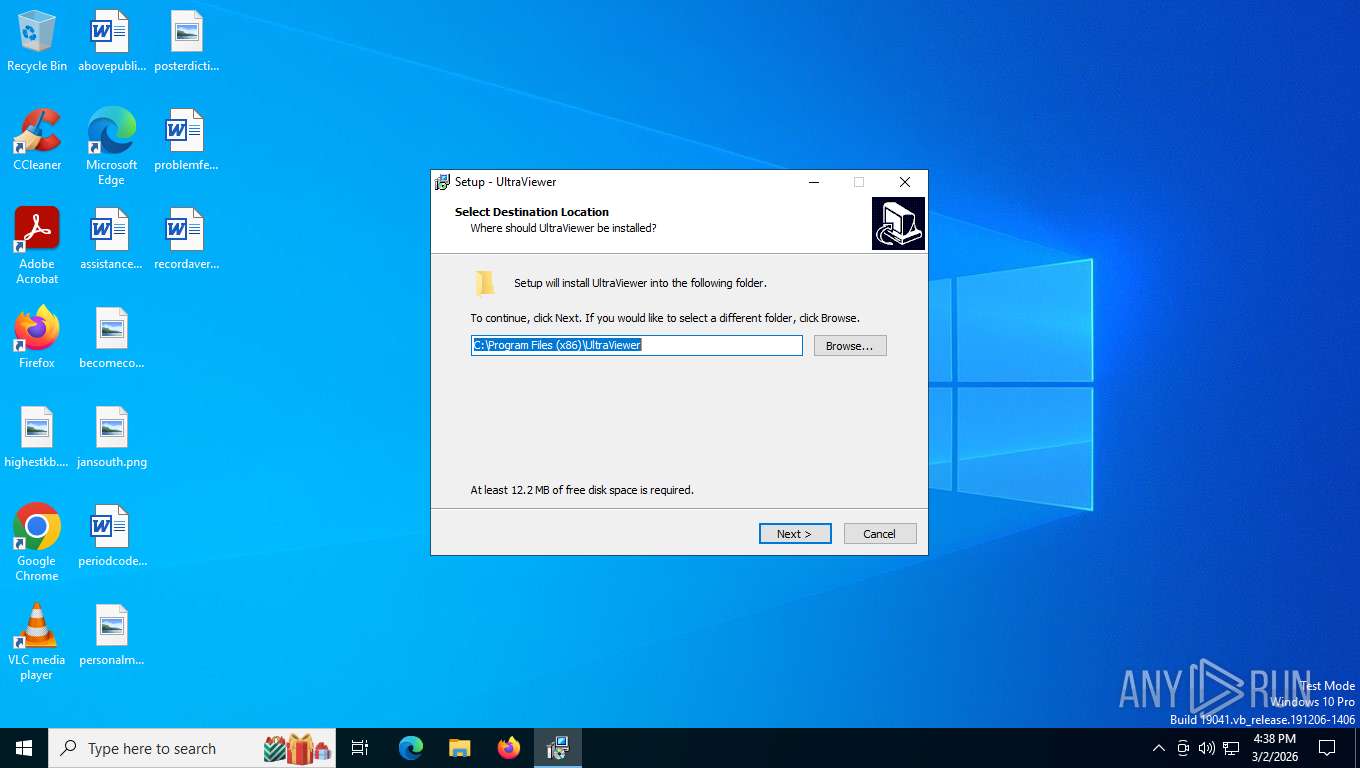
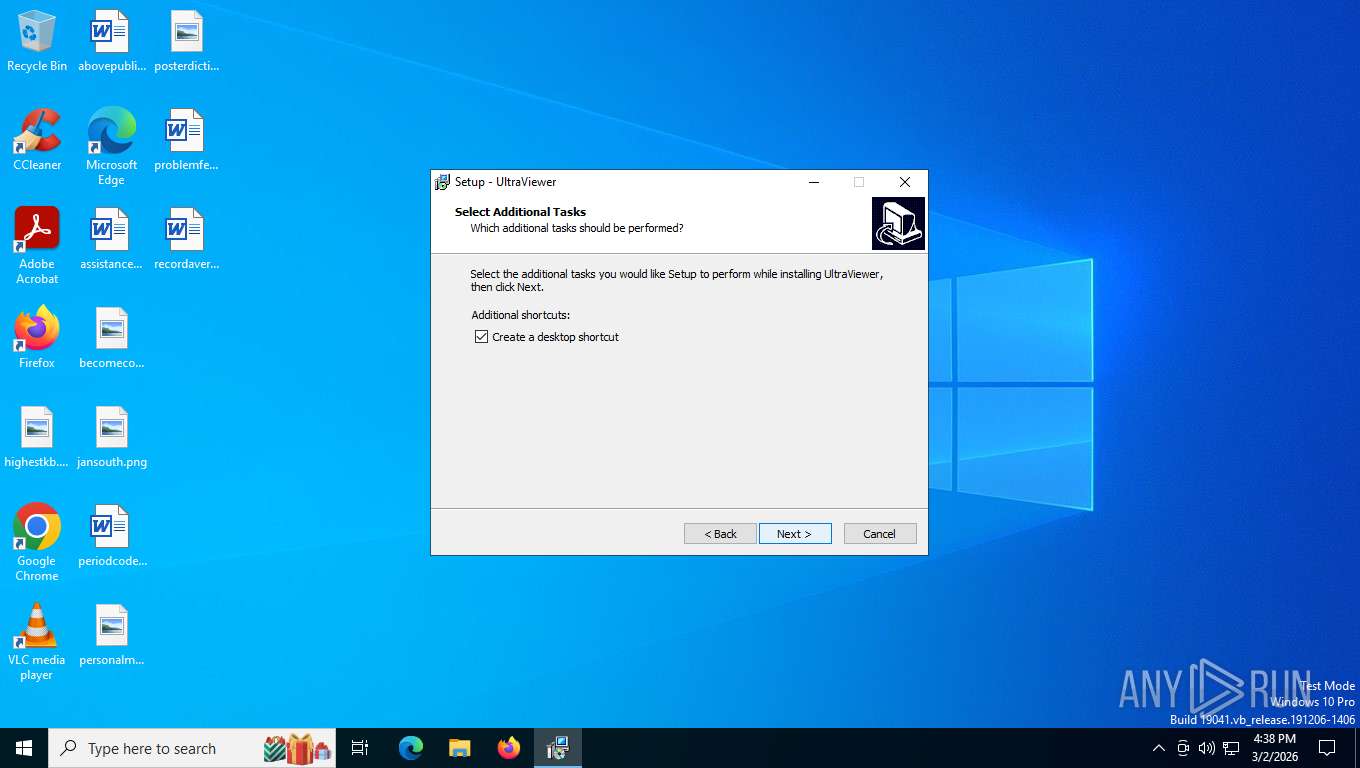
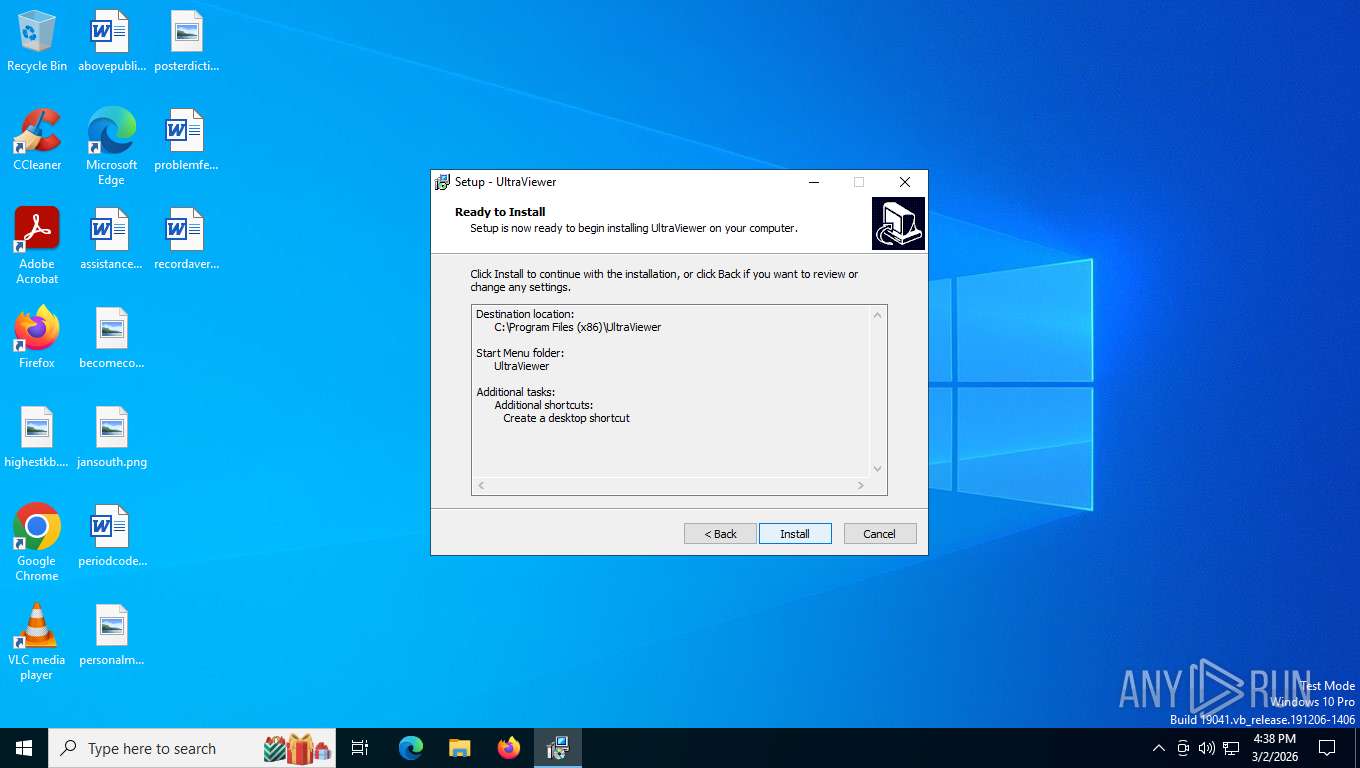
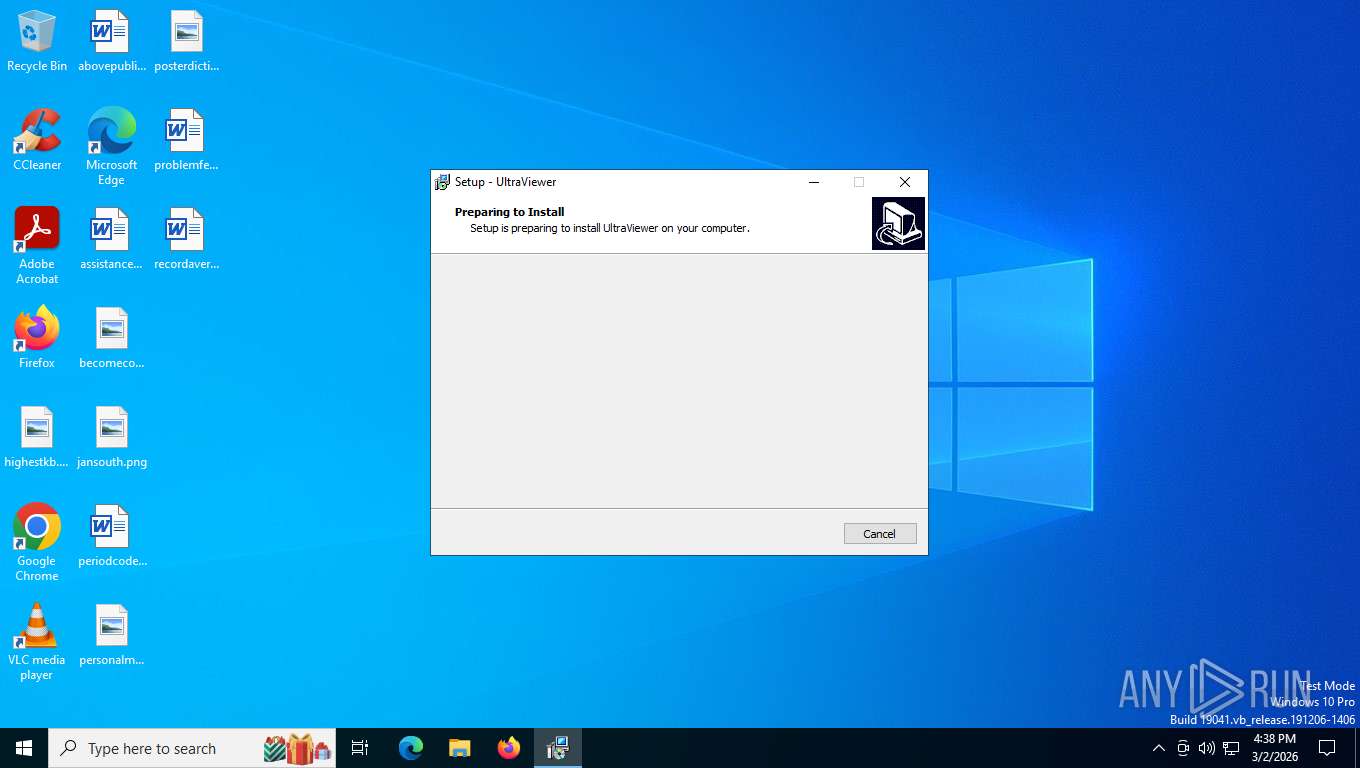
| File name: | UltraViewer_setup_6.6.124_en.exe |
| Full analysis: | https://app.any.run/tasks/3a53f149-d2ff-400c-86ca-5e88733c6b0b |
| Verdict: | Malicious activity |
| Analysis date: | March 02, 2026, 21:38:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | AB0DF05E39BD73F4ADADE8FDC21A1F25 |
| SHA1: | B12C2771C040F6175902EC5941FFD09748F87ED3 |
| SHA256: | 020AAC79A14717E316A593155CA778DD3E253B888BF62633B174838D35DF7F41 |
| SSDEEP: | 98304:NgjAtDi7PImpRp7TCCI/Skb5FQTXN2MY0bqOsTiWgrKeCBWGP+zblXJcV4Y6gWwu:wwIuy |
MALICIOUS
Executing a file with an untrusted certificate
- UltraViewer_setup_6.6.124_en.exe (PID: 7392)
- UltraViewer_setup_6.6.124_en.exe (PID: 6488)
- UltraViewer_Desktop.exe (PID: 6108)
- UltraViewer_Desktop.exe (PID: 8316)
- UltraViewer_Service.exe (PID: 8196)
- UltraViewer_Desktop.exe (PID: 1352)
- UltraViewer_Desktop.exe (PID: 1956)
- UltraViewer_Desktop.exe (PID: 2016)
Starts NET.EXE for service management
- net.exe (PID: 7664)
- net.exe (PID: 8572)
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
SUSPICIOUS
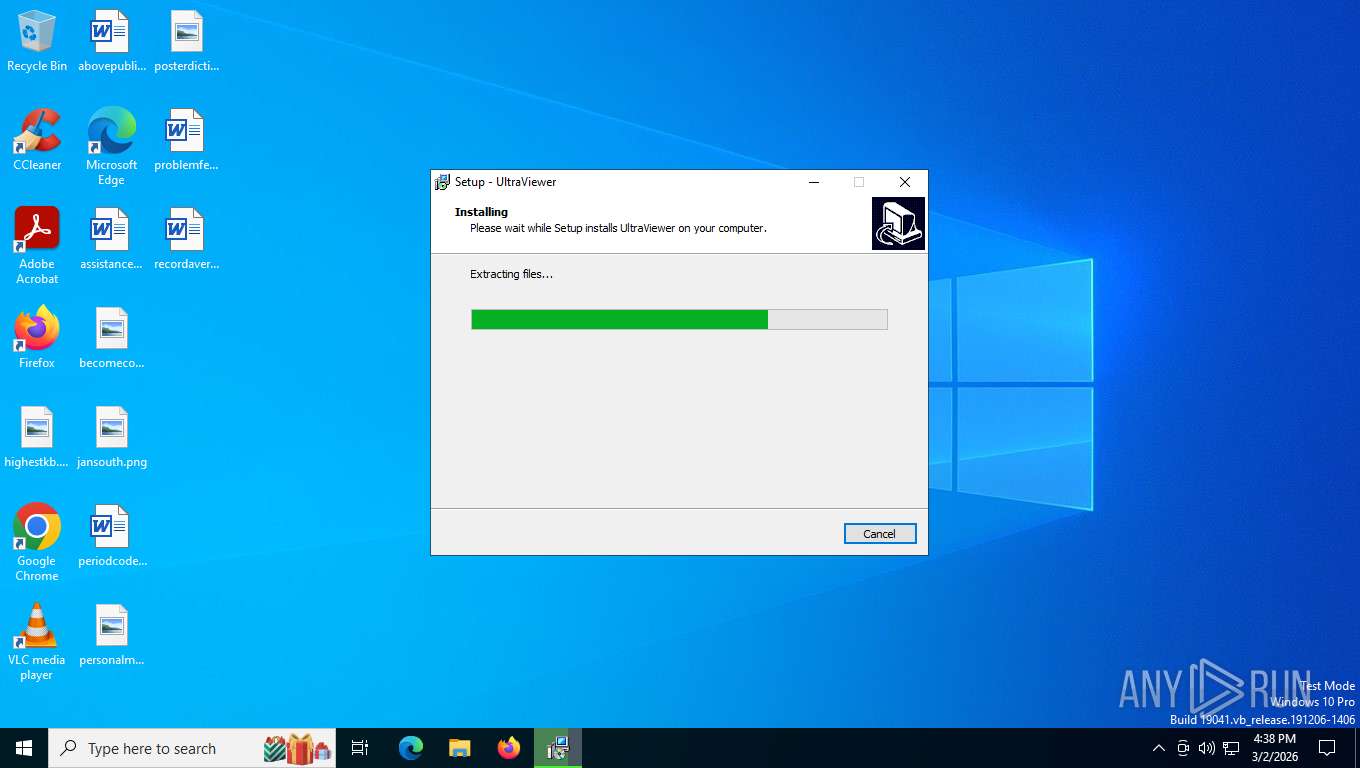
Executable content was dropped or overwritten
- UltraViewer_setup_6.6.124_en.exe (PID: 7392)
- UltraViewer_setup_6.6.124_en.exe (PID: 6488)
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
Reads the Windows owner or organization settings
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
Windows service management via SC.EXE
- sc.exe (PID: 8228)
Uses TASKKILL.EXE to kill process
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
Creates/Modifies COM task schedule object
- RegAsm.exe (PID: 2288)
- RegAsm.exe (PID: 3636)
Reads Microsoft Outlook installation path
- UltraViewer_Desktop.exe (PID: 6108)
- UltraViewer_Desktop.exe (PID: 1956)
Reads Internet Explorer settings
- UltraViewer_Desktop.exe (PID: 6108)
- UltraViewer_Desktop.exe (PID: 1956)
Executes as Windows Service
- UltraViewer_Service.exe (PID: 8196)
Restarts service on failure
- sc.exe (PID: 756)
INFO
Process checks computer location settings
- UltraViewer_setup_6.6.124_en.tmp (PID: 7832)
Create files in a temporary directory
- UltraViewer_setup_6.6.124_en.exe (PID: 7392)
- UltraViewer_setup_6.6.124_en.exe (PID: 6488)
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
- UltraViewer_Desktop.exe (PID: 6108)
- UltraViewer_Desktop.exe (PID: 1956)
Reads security settings of Internet Explorer
- UltraViewer_setup_6.6.124_en.tmp (PID: 7832)
- RegAsm.exe (PID: 2288)
- UltraViewer_Desktop.exe (PID: 6108)
- RegAsm.exe (PID: 3636)
- UltraViewer_Service.exe (PID: 8196)
- UltraViewer_Desktop.exe (PID: 1956)
Checks supported languages
- UltraViewer_setup_6.6.124_en.tmp (PID: 7832)
- UltraViewer_setup_6.6.124_en.exe (PID: 7392)
- UltraViewer_setup_6.6.124_en.exe (PID: 6488)
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
- UVUninstallHelper.exe (PID: 7424)
- RegAsm.exe (PID: 2288)
- UltraViewer_Desktop.exe (PID: 6108)
- RegAsm.exe (PID: 3636)
- UltraViewer_Desktop.exe (PID: 8316)
- UltraViewer_Service.exe (PID: 8196)
- RegAsm.exe (PID: 8348)
- UltraViewer_Desktop.exe (PID: 1352)
- RegAsm.exe (PID: 3388)
- UltraViewer_Desktop.exe (PID: 1956)
- RegAsm.exe (PID: 7460)
- UltraViewer_Desktop.exe (PID: 2016)
- uv_x64.exe (PID: 5392)
Reads the computer name
- UltraViewer_setup_6.6.124_en.tmp (PID: 7832)
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
- UVUninstallHelper.exe (PID: 7424)
- RegAsm.exe (PID: 2288)
- UltraViewer_Desktop.exe (PID: 6108)
- RegAsm.exe (PID: 3636)
- UltraViewer_Service.exe (PID: 8196)
- UltraViewer_Desktop.exe (PID: 1352)
- RegAsm.exe (PID: 8348)
- UltraViewer_Desktop.exe (PID: 8316)
- RegAsm.exe (PID: 3388)
- RegAsm.exe (PID: 7460)
- UltraViewer_Desktop.exe (PID: 1956)
- UltraViewer_Desktop.exe (PID: 2016)
- uv_x64.exe (PID: 5392)
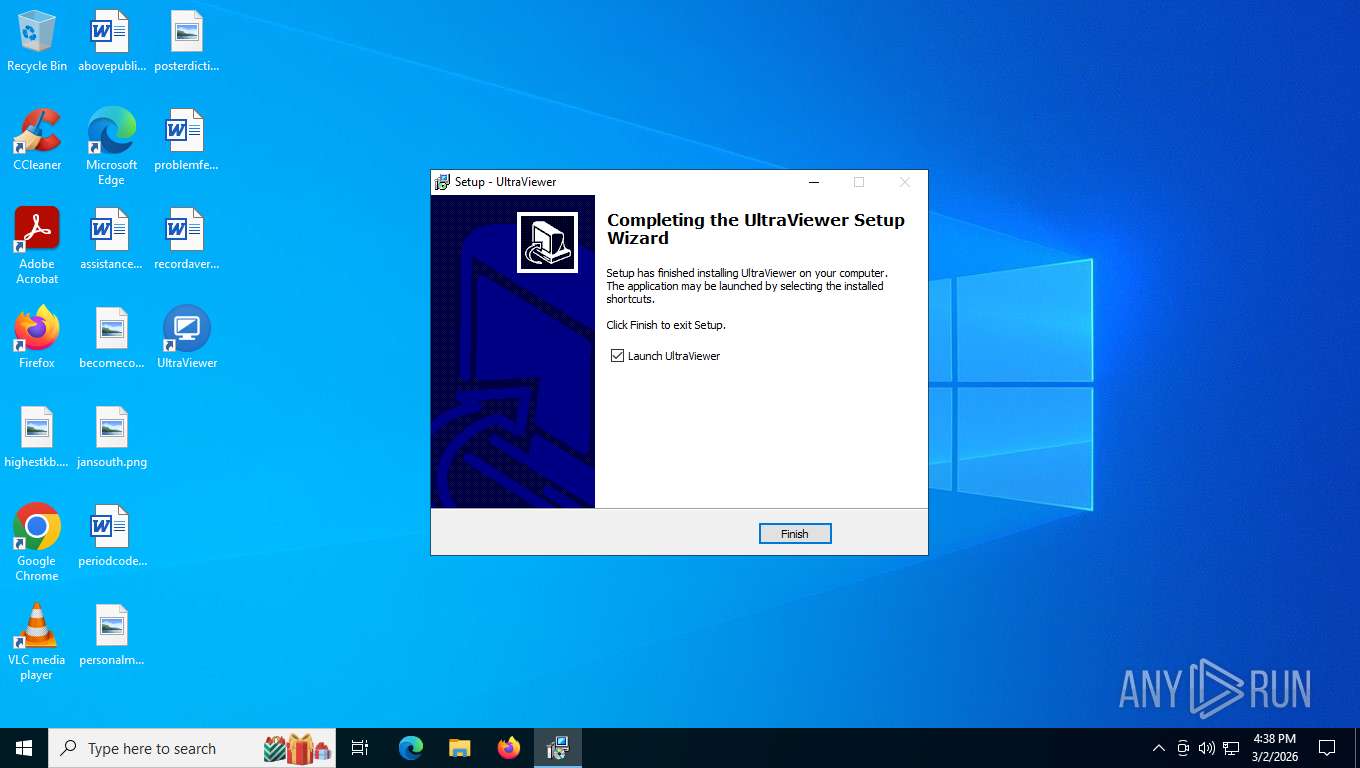
Creates files in the program directory
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
- RegAsm.exe (PID: 2288)
- RegAsm.exe (PID: 3636)
- UltraViewer_Service.exe (PID: 8196)
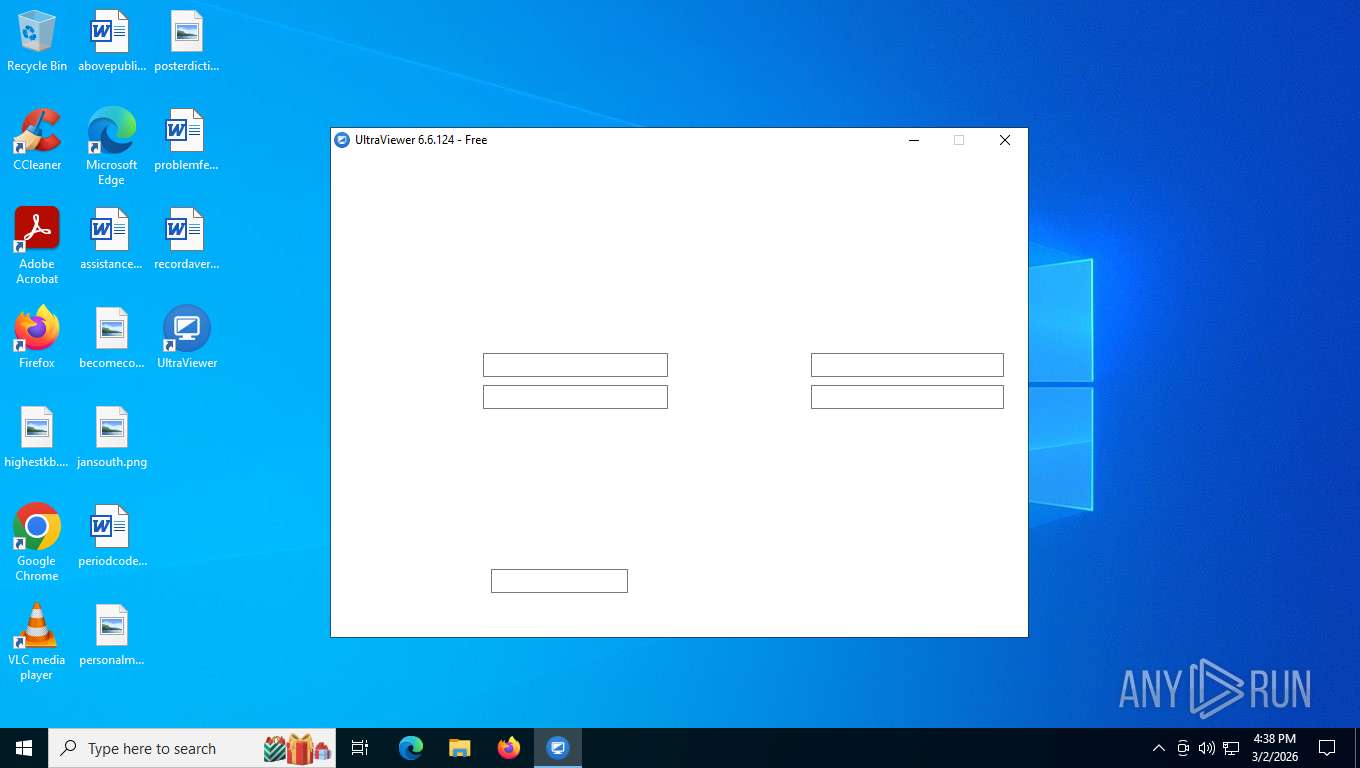
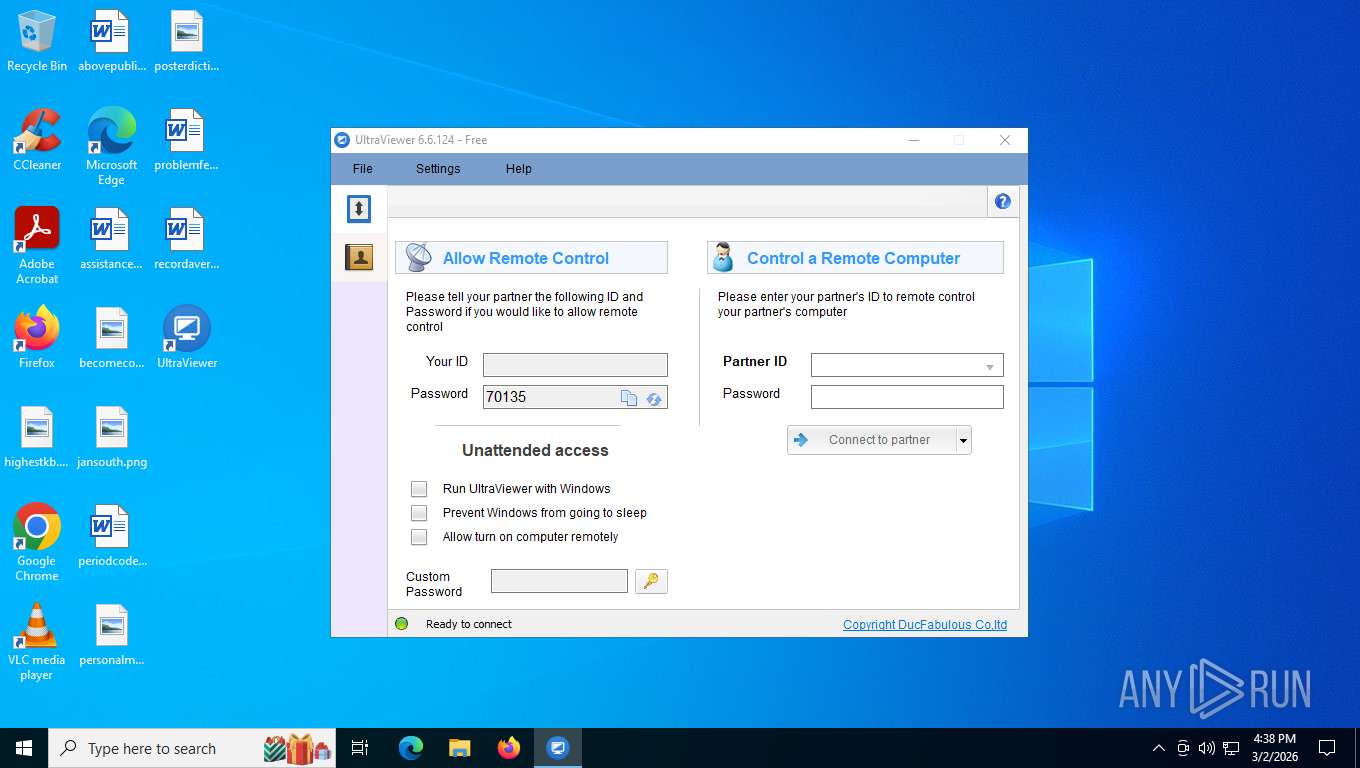
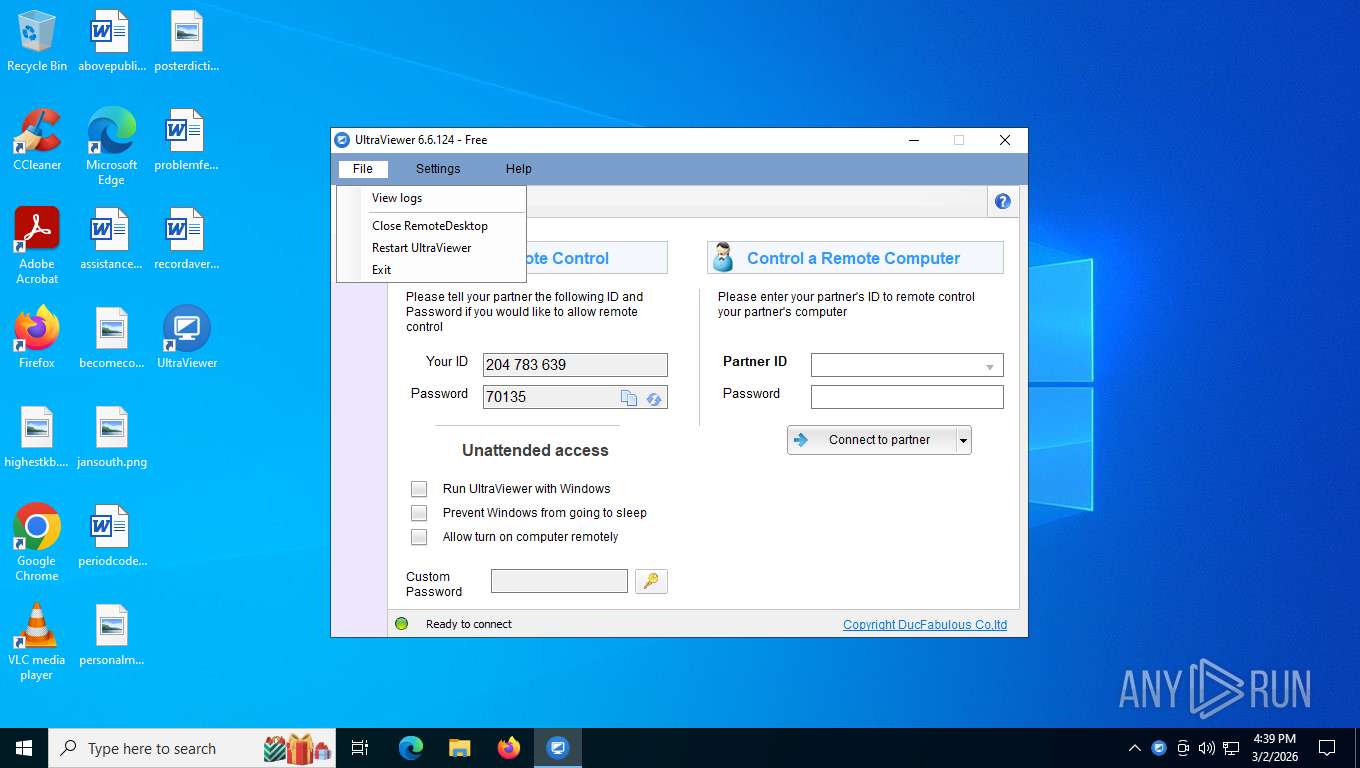
ULTRAVIEWER has been detected
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
- RegAsm.exe (PID: 2288)
- UltraViewer_Desktop.exe (PID: 6108)
- RegAsm.exe (PID: 3636)
- conhost.exe (PID: 6828)
- UltraViewer_Desktop.exe (PID: 1352)
- UltraViewer_Service.exe (PID: 8196)
- RegAsm.exe (PID: 8348)
- UltraViewer_Desktop.exe (PID: 8316)
- RegAsm.exe (PID: 3388)
- RegAsm.exe (PID: 7460)
- UltraViewer_setup_6.6.124_en.tmp (PID: 7832)
- UltraViewer_Desktop.exe (PID: 1956)
- UltraViewer_Desktop.exe (PID: 2016)
- conhost.exe (PID: 5888)
- uv_x64.exe (PID: 5392)
The sample compiled with english language support
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
Drops script file
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
- UltraViewer_Desktop.exe (PID: 1956)
Compiled with Borland Delphi (YARA)
- UltraViewer_setup_6.6.124_en.exe (PID: 7392)
- UltraViewer_setup_6.6.124_en.tmp (PID: 7832)
- UltraViewer_setup_6.6.124_en.exe (PID: 6488)
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
Detects InnoSetup installer (YARA)
- UltraViewer_setup_6.6.124_en.exe (PID: 7392)
- UltraViewer_setup_6.6.124_en.tmp (PID: 7832)
- UltraViewer_setup_6.6.124_en.exe (PID: 6488)
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
UPX packer has been detected
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
There is functionality for taking screenshot (YARA)
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 2288)
- RegAsm.exe (PID: 3636)
- UltraViewer_Desktop.exe (PID: 6108)
- UltraViewer_Desktop.exe (PID: 8316)
- UltraViewer_Service.exe (PID: 8196)
- UltraViewer_Desktop.exe (PID: 1956)
- UltraViewer_Desktop.exe (PID: 2016)
- uv_x64.exe (PID: 5392)
Confuser has been detected (YARA)
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
Checks proxy server information
- UltraViewer_Desktop.exe (PID: 6108)
- UltraViewer_Desktop.exe (PID: 1956)
Creates a software uninstall entry
- UltraViewer_setup_6.6.124_en.tmp (PID: 2564)
Disables trace logs
- UltraViewer_Service.exe (PID: 8196)
- UltraViewer_Desktop.exe (PID: 1956)
Creates files or folders in the user directory
- UltraViewer_Desktop.exe (PID: 1956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 14:39:04+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | DucFabulous |
| FileDescription: | UltraViewer Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | UltraViewer |
| ProductVersion: | 6.6.124 |
Total processes
578
Monitored processes
430
Malicious processes
6
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 416 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 416 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 416 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 476 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 508 | "taskkill.exe" /f /im "UltraViewer_Service.exe" | C:\Windows\SysWOW64\taskkill.exe | — | UltraViewer_setup_6.6.124_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 508 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "taskkill.exe" /f /im "UltraViewer_Desktop.exe" | C:\Windows\SysWOW64\taskkill.exe | — | UltraViewer_setup_6.6.124_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
35 433
Read events
33 910
Write events
1 523
Delete events
0
Modification events
| (PID) Process: | (2288) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{1CA5DE22-F295-3F03-8D69-018007836F60}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2288) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{1CA5DE22-F295-3F03-8D69-018007836F60}\InprocServer32 |
| Operation: | write | Name: | Class |
Value: RemoteControl.ComRegistrationException | |||
| (PID) Process: | (2288) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{1CA5DE22-F295-3F03-8D69-018007836F60}\InprocServer32 |
| Operation: | write | Name: | Assembly |
Value: RemoteControl, Version=1.0.0.0, Culture=neutral, PublicKeyToken=null | |||
| (PID) Process: | (2288) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{1CA5DE22-F295-3F03-8D69-018007836F60}\InprocServer32 |
| Operation: | write | Name: | RuntimeVersion |
Value: v4.0.30319 | |||
| (PID) Process: | (2288) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{1CA5DE22-F295-3F03-8D69-018007836F60}\InprocServer32\1.0.0.0 |
| Operation: | write | Name: | Class |
Value: RemoteControl.ComRegistrationException | |||
| (PID) Process: | (2288) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{1CA5DE22-F295-3F03-8D69-018007836F60}\InprocServer32\1.0.0.0 |
| Operation: | write | Name: | Assembly |
Value: RemoteControl, Version=1.0.0.0, Culture=neutral, PublicKeyToken=null | |||
| (PID) Process: | (2288) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{1CA5DE22-F295-3F03-8D69-018007836F60}\InprocServer32\1.0.0.0 |
| Operation: | write | Name: | RuntimeVersion |
Value: v4.0.30319 | |||
| (PID) Process: | (2288) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Component Categories\{62C8FE65-4EBB-45E7-B440-6E39B2CDBF29} |
| Operation: | write | Name: | 0 |
Value: .NET Category | |||
| (PID) Process: | (2288) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{315D07B8-9F8F-3885-AB17-1C3D460CEE4E}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2288) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{315D07B8-9F8F-3885-AB17-1C3D460CEE4E}\InprocServer32 |
| Operation: | write | Name: | Class |
Value: RemoteControl.ExtendTreeView | |||
Executable files
39
Suspicious files
16
Text files
171
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6488 | UltraViewer_setup_6.6.124_en.exe | C:\Users\admin\AppData\Local\Temp\is-ISI92.tmp\UltraViewer_setup_6.6.124_en.tmp | executable | |
MD5:E845838D99D29C4BBA4AD35EE996DEA3 | SHA256:B727418174AD4F929AD9206E4DF51865DEF55C0D2874BDA487CBAE6F2946938D | |||
| 2564 | UltraViewer_setup_6.6.124_en.tmp | C:\Program Files (x86)\UltraViewer\unins000.exe | executable | |
MD5:74FFBE801489485E95D1AADEAD574CC0 | SHA256:8901B12FE6EF4BD14DC9AF0C7EFAEF050F036800FA919614DAF4A59FED50391D | |||
| 2564 | UltraViewer_setup_6.6.124_en.tmp | C:\Program Files (x86)\UltraViewer\is-ILMRE.tmp | executable | |
MD5:74FFBE801489485E95D1AADEAD574CC0 | SHA256:8901B12FE6EF4BD14DC9AF0C7EFAEF050F036800FA919614DAF4A59FED50391D | |||
| 2564 | UltraViewer_setup_6.6.124_en.tmp | C:\Users\admin\AppData\Local\Temp\is-30IK8.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 2564 | UltraViewer_setup_6.6.124_en.tmp | C:\Users\admin\AppData\Local\Temp\is-30IK8.tmp\idp.dll | executable | |
MD5:55C310C0319260D798757557AB3BF636 | SHA256:54E7E0AD32A22B775131A6288F083ED3286A9A436941377FC20F85DD9AD983ED | |||
| 2564 | UltraViewer_setup_6.6.124_en.tmp | C:\Program Files (x86)\UltraViewer\CopyRights.txt | text | |
MD5:1545270D0FF548C77A57D008223DB83E | SHA256:3E40C331E56BC35DF9C6341E05FAA41165F4E25718914248886295B7553A734C | |||
| 2564 | UltraViewer_setup_6.6.124_en.tmp | C:\Program Files (x86)\UltraViewer\emotion.fan | text | |
MD5:5E28EF7C6FB2D23E9DF42B3355BDCEB7 | SHA256:F899D1C4F1B55BDFA9F4237CFC593BF8AEDE52AF4D5EB3CC2AAEF8B77CF5C519 | |||
| 2564 | UltraViewer_setup_6.6.124_en.tmp | C:\Program Files (x86)\UltraViewer\is-L2F0J.tmp | text | |
MD5:AB6894E112614829CDDB91290EB8A045 | SHA256:C46517EE870DAD84C8D778AC1F39CC96394BAF4DB59535F4D64C5B070C7F751E | |||
| 2564 | UltraViewer_setup_6.6.124_en.tmp | C:\Program Files (x86)\UltraViewer\is-MEAVV.tmp | text | |
MD5:1545270D0FF548C77A57D008223DB83E | SHA256:3E40C331E56BC35DF9C6341E05FAA41165F4E25718914248886295B7553A734C | |||
| 2564 | UltraViewer_setup_6.6.124_en.tmp | C:\Program Files (x86)\UltraViewer\is-VEQP1.tmp | text | |
MD5:5E28EF7C6FB2D23E9DF42B3355BDCEB7 | SHA256:F899D1C4F1B55BDFA9F4237CFC593BF8AEDE52AF4D5EB3CC2AAEF8B77CF5C519 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
29
DNS requests
22
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
4948 | svchost.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | — | — | whitelisted |
7916 | SIHClient.exe | GET | 304 | 135.233.95.144:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
7916 | SIHClient.exe | GET | 200 | 135.233.95.135:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
7916 | SIHClient.exe | GET | 200 | 135.233.95.144:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
7916 | SIHClient.exe | GET | 304 | 135.233.95.144:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
1956 | UltraViewer_Desktop.exe | POST | — | 103.74.123.129:443 | https://functions3.ultraviewer.net/UVService/ | unknown | — | — | unknown |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
356 | svchost.exe | POST | 200 | 40.126.31.2:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4948 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
148 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.241.205:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
356 | svchost.exe | 40.126.31.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4948 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
1956 | UltraViewer_Desktop.exe | Generic Protocol Command Decode | SURICATA HTTP request field missing colon |
1956 | UltraViewer_Desktop.exe | Generic Protocol Command Decode | SURICATA HTTP URI terminated by non-compliant character |
1956 | UltraViewer_Desktop.exe | Generic Protocol Command Decode | SURICATA HTTP METHOD terminated by non-compliant character |
Process | Message |
|---|---|
UltraViewer_Desktop.exe | uvh - 1956 - 525274
|