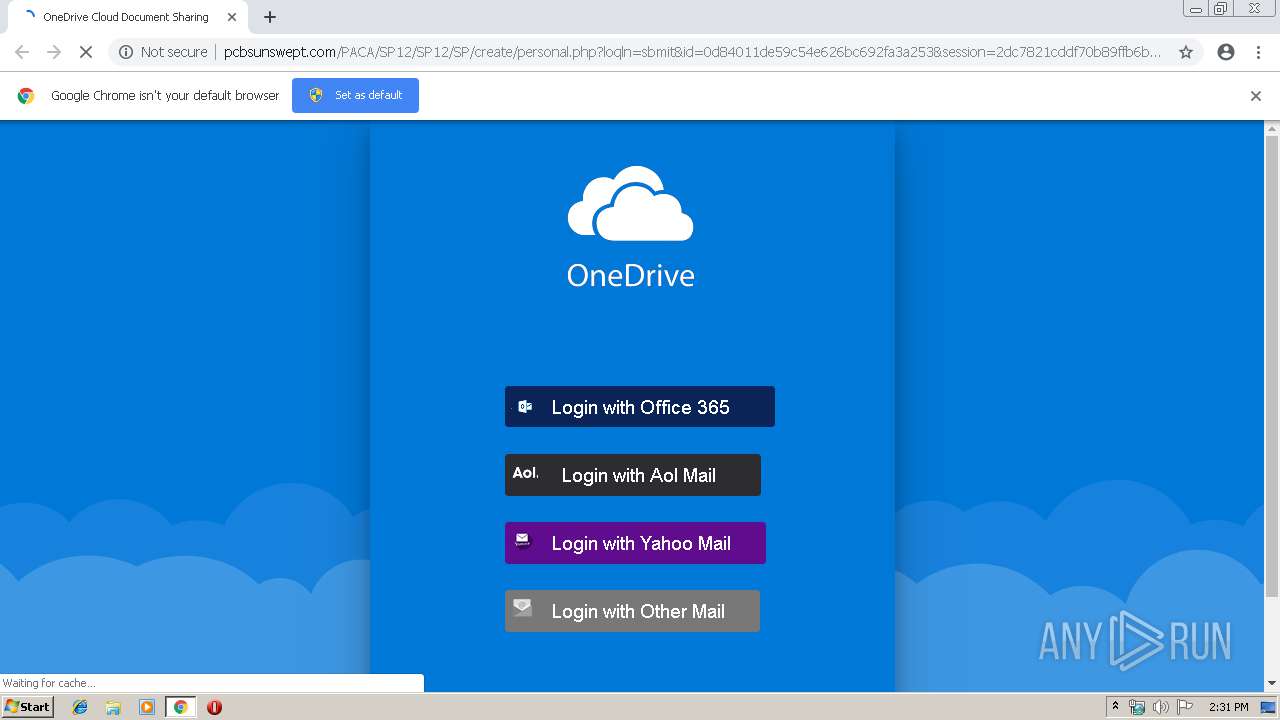
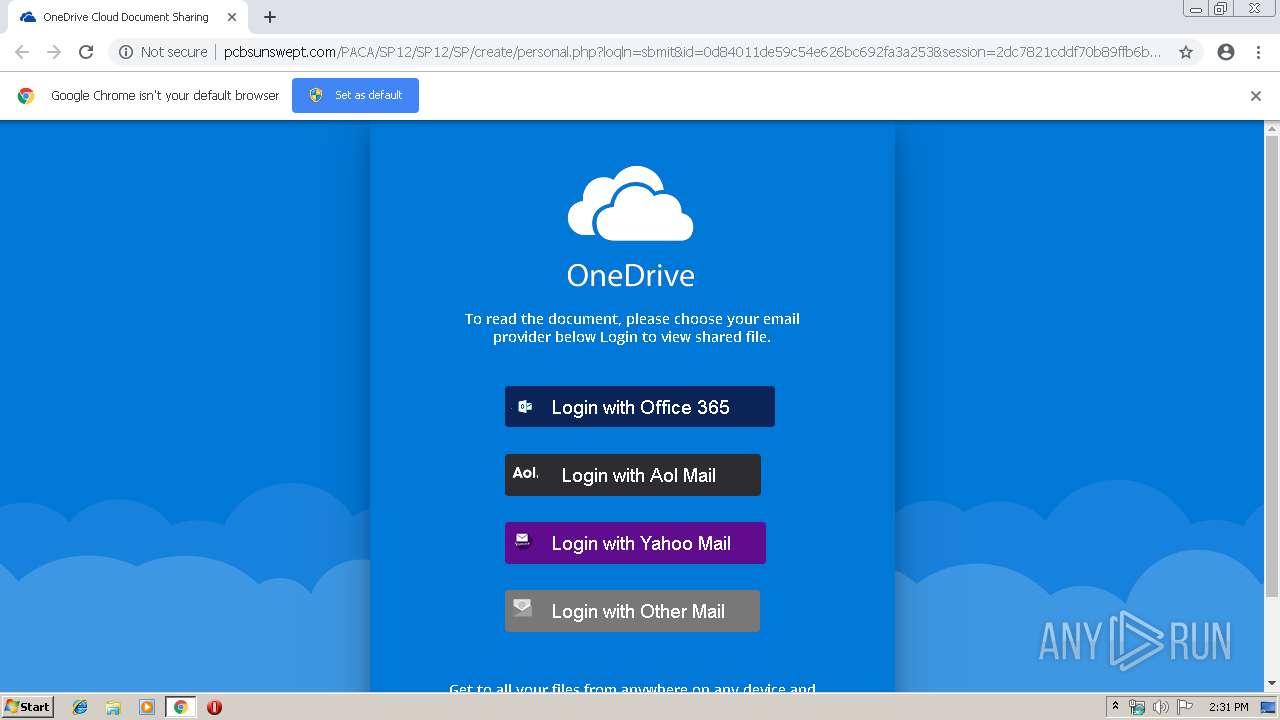
| URL: | http://pcbsunswept.com/PACA/SP12/SP12/SP/create/index.php |
| Full analysis: | https://app.any.run/tasks/706748cc-a8a1-4740-88e2-b8df82f23991 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 14:30:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D8F295075D97F4149ED3428615CCAFC0 |
| SHA1: | 7C96DE1293D8325EFB025A963AE6174BA1CA026E |
| SHA256: | 020879AF8671278387595DAC33E1261568607B58F0DAD052F710A69ED4AD0595 |
| SSDEEP: | 3:N1KOGSPZIyD2eXHUZyAdhHn:CONPZgeXHUwAbHn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2244)
INFO
Application launched itself
- chrome.exe (PID: 2244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
15
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --service-pipe-token=1802740631834519846 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1802740631834519846 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --service-pipe-token=4844518070069619783 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4844518070069619783 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9931523076505383417 --mojo-platform-channel-handle=3328 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17511907933671878153 --mojo-platform-channel-handle=1516 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8314476830673488658 --mojo-platform-channel-handle=3220 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8224111986360863366 --mojo-platform-channel-handle=3232 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://pcbsunswept.com/PACA/SP12/SP12/SP/create/index.php | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2248 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --service-pipe-token=14996147638628409404 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14996147638628409404 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1515958885878299576 --mojo-platform-channel-handle=3068 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
175
Read events
90
Write events
80
Delete events
5
Modification events
| (PID) Process: | (2244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2244) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2244-13197652263265250 |
Value: 259 | |||
Executable files
0
Suspicious files
5
Text files
119
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5174b9f0-0c39-45f0-83ff-f066fa145b89.tmp | — | |
MD5:— | SHA256:— | |||
| 2244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
15
DNS requests
8
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1472 | chrome.exe | GET | 302 | 107.180.41.227:80 | http://pcbsunswept.com/PACA/SP12/SP12/SP/create/index.php | US | — | — | suspicious |
1472 | chrome.exe | GET | 200 | 107.180.41.227:80 | http://pcbsunswept.com/PACA/SP12/SP12/SP/create/personal.php?loqln=sbmit&id=0d84011de59c54e626bc692fa3a253&session=2dc7821cddf70b89ffb6b5cdbaa2a53b | US | html | 1.01 Kb | suspicious |
1472 | chrome.exe | GET | 200 | 107.180.41.227:80 | http://pcbsunswept.com/PACA/SP12/SP12/SP/create/images_files/o.png | US | image | 844 b | suspicious |
1472 | chrome.exe | GET | 200 | 107.180.41.227:80 | http://pcbsunswept.com/PACA/SP12/SP12/SP/create/images_files/style.css | US | text | 1.77 Kb | suspicious |
1472 | chrome.exe | GET | 200 | 107.180.41.227:80 | http://pcbsunswept.com/PACA/SP12/SP12/SP/create/images_files/css.css | US | text | 521 b | suspicious |
1472 | chrome.exe | GET | 200 | 107.180.41.227:80 | http://pcbsunswept.com/PACA/SP12/SP12/SP/create/images_files/wback.png | US | image | 19.0 Kb | suspicious |
1472 | chrome.exe | GET | 200 | 107.180.41.227:80 | http://pcbsunswept.com/PACA/SP12/SP12/SP/create/images_files/bright.png | US | image | 4.16 Kb | suspicious |
1472 | chrome.exe | GET | 200 | 107.180.41.227:80 | http://pcbsunswept.com/PACA/SP12/SP12/SP/create/images_files/a.png | US | image | 430 b | suspicious |
1472 | chrome.exe | GET | 200 | 107.180.41.227:80 | http://pcbsunswept.com/PACA/SP12/SP12/SP/create/images_files/y.png | US | image | 1.95 Kb | suspicious |
1472 | chrome.exe | GET | 200 | 107.180.41.227:80 | http://pcbsunswept.com/PACA/SP12/SP12/SP/create/images_files/m.png | US | image | 1.65 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1472 | chrome.exe | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1472 | chrome.exe | 216.58.207.78:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1472 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
1472 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1472 | chrome.exe | 173.194.150.219:80 | r5---sn-5goeen7r.gvt1.com | Google Inc. | US | whitelisted |
1472 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1472 | chrome.exe | 107.180.41.227:80 | pcbsunswept.com | GoDaddy.com, LLC | US | suspicious |
1472 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
pcbsunswept.com |
| suspicious |
accounts.google.com |
| shared |
fonts.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r5---sn-5goeen7r.gvt1.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1472 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Generic Multi-Email Popupwnd Phishing Landing 2018-01-25 |
1472 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Generic Multi-Email Phishing Landing 2018-08-30 |