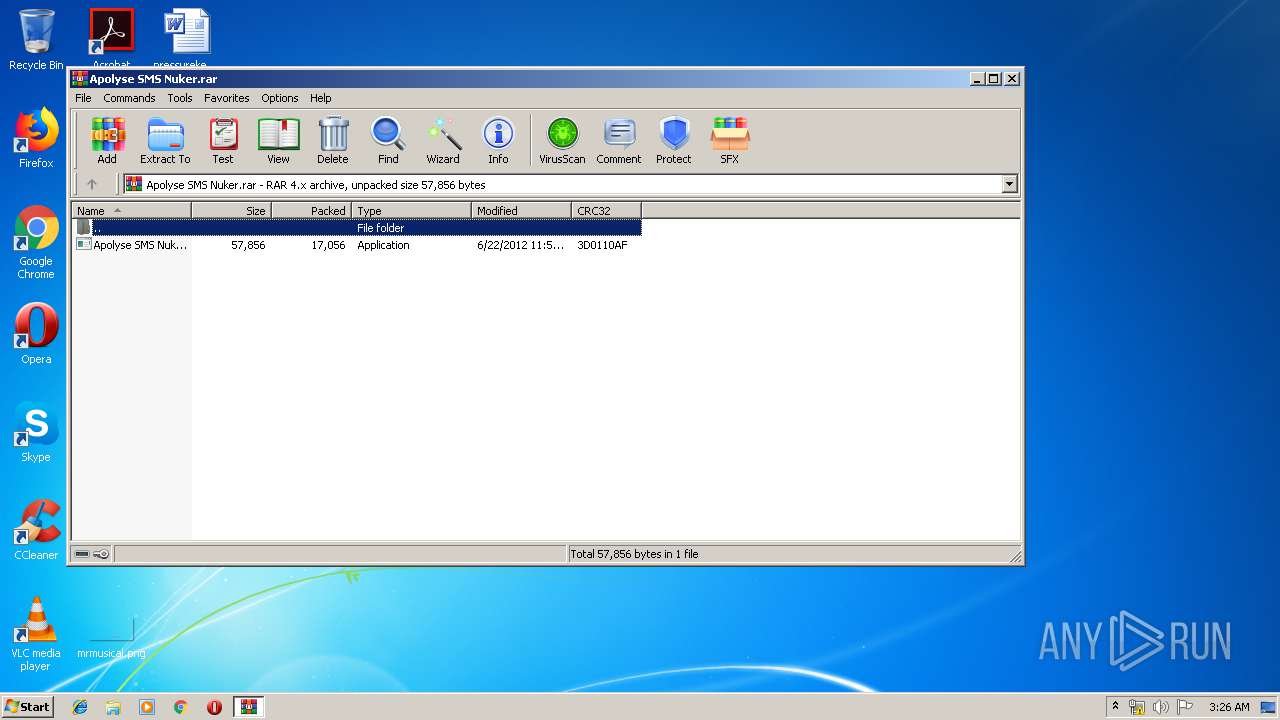
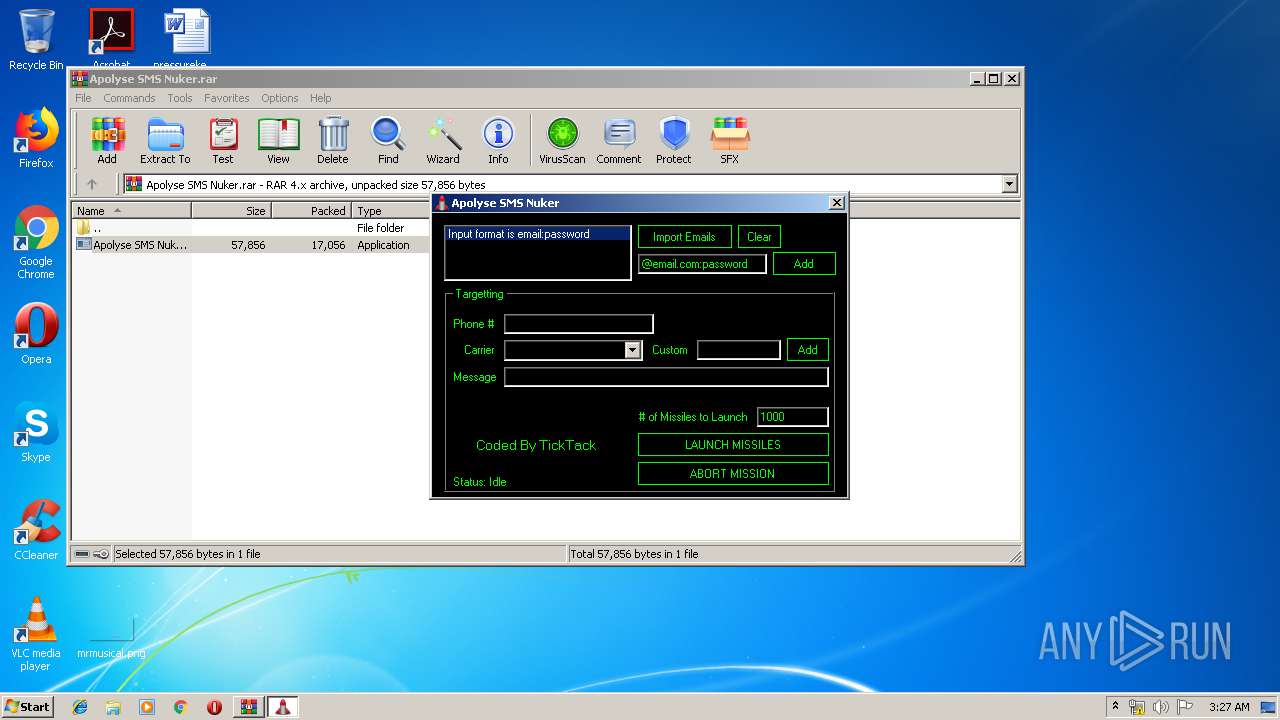
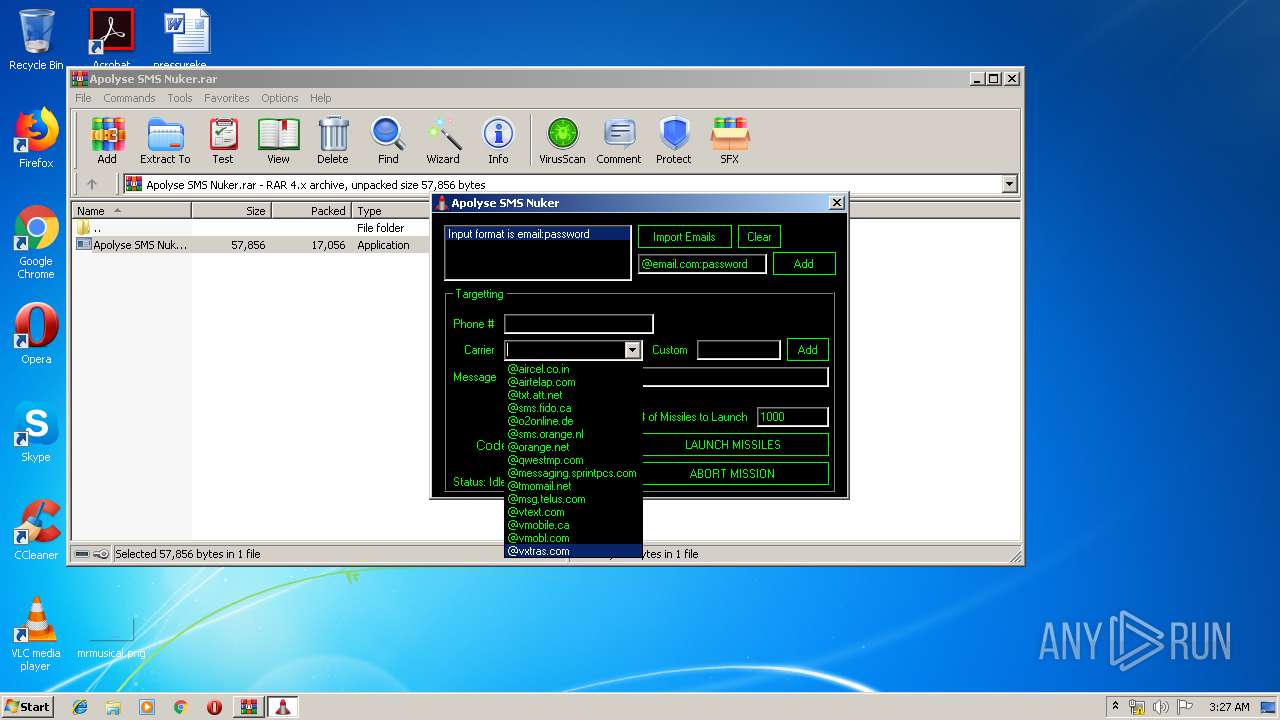
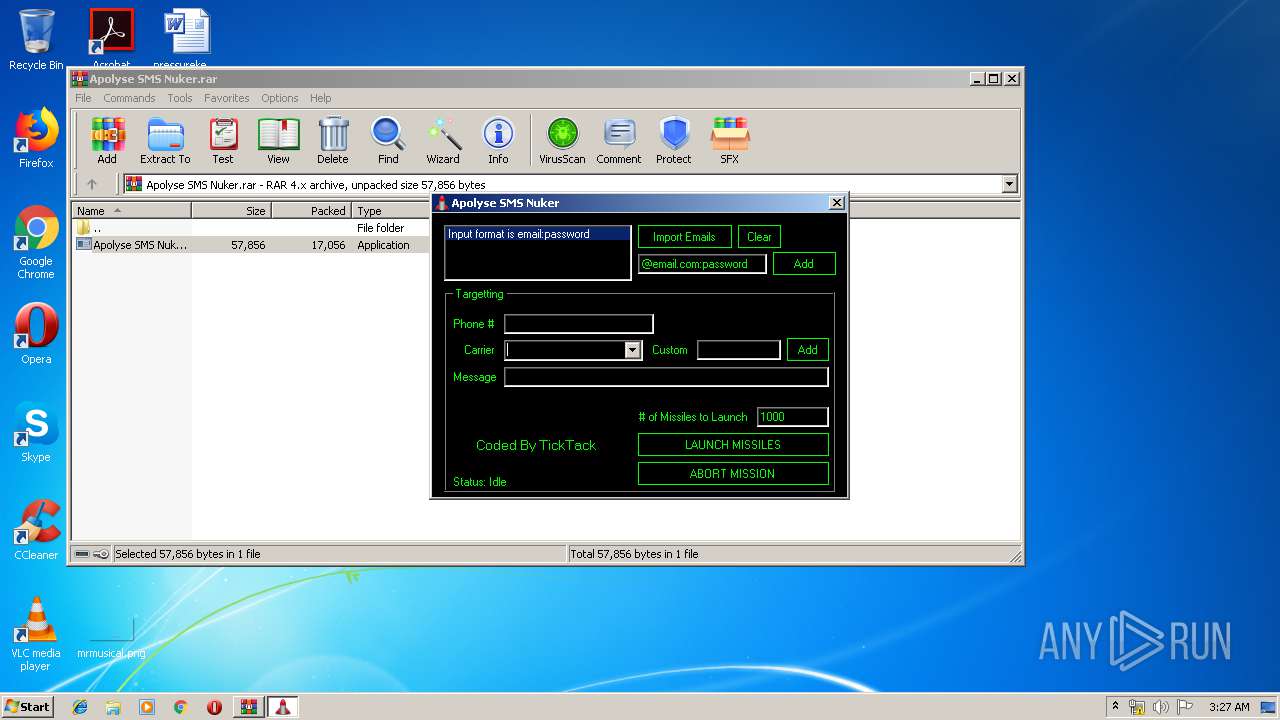
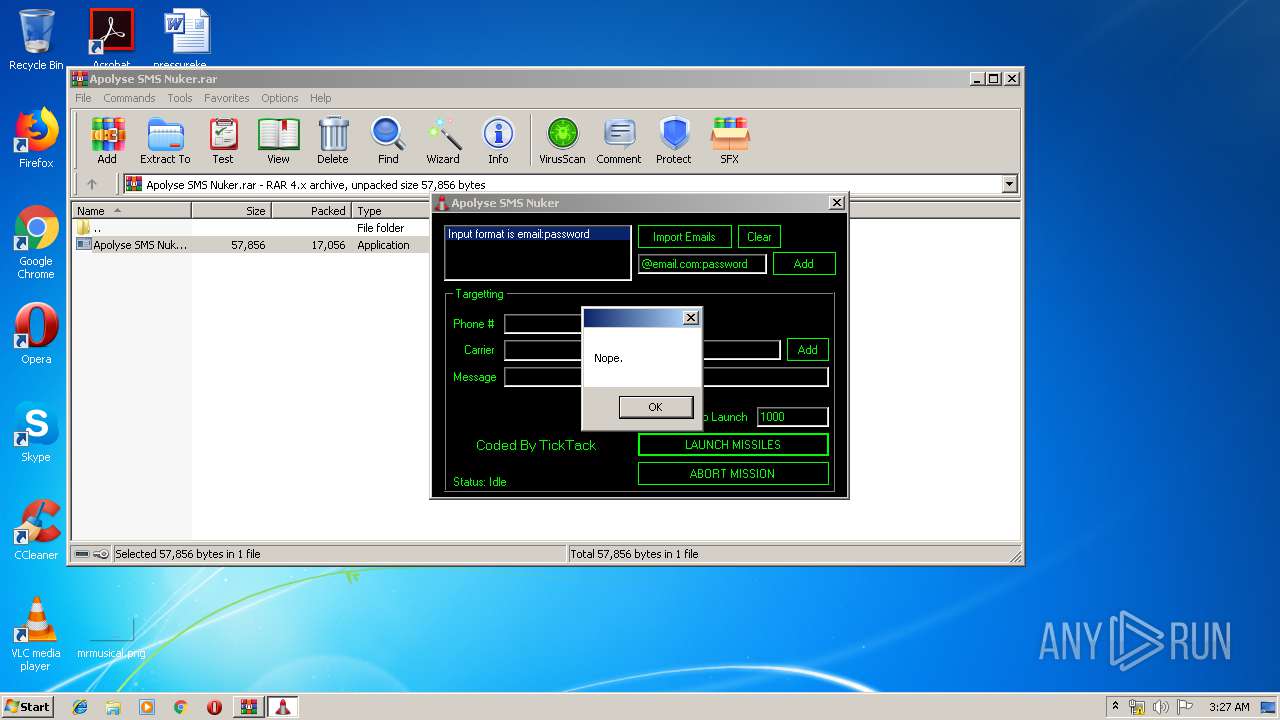
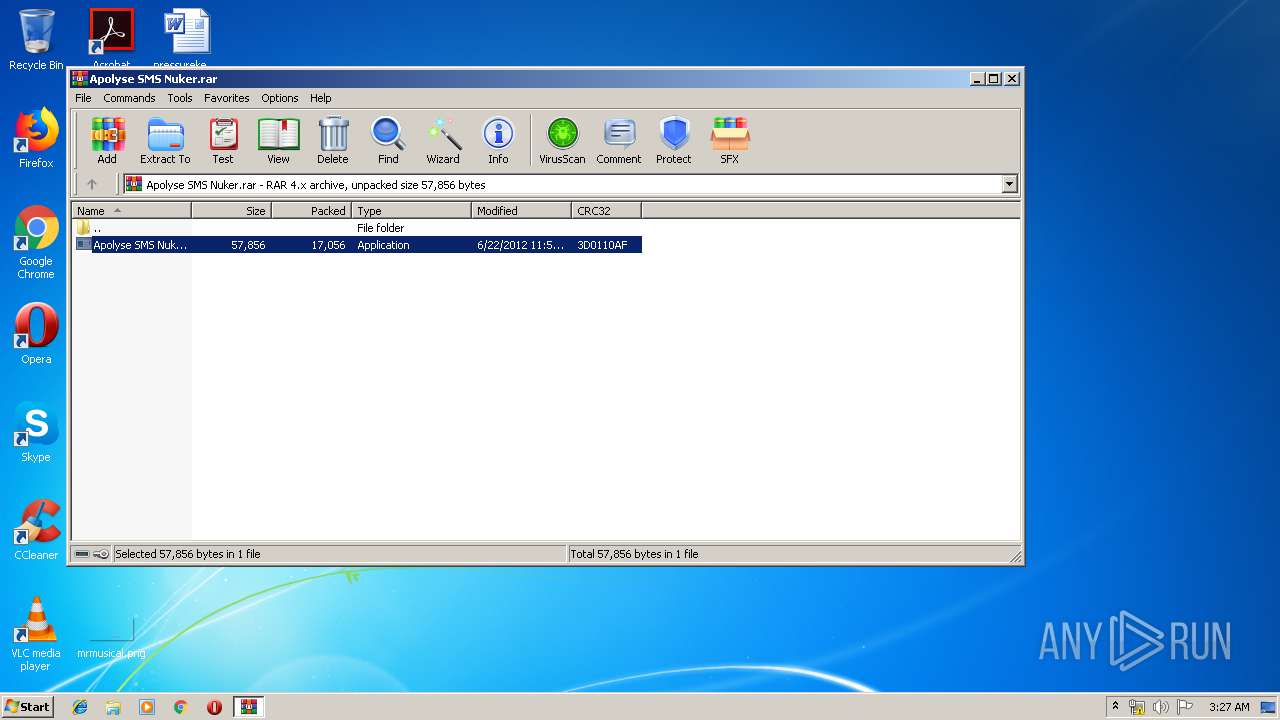
| File name: | Apolyse SMS Nuker.rar |
| Full analysis: | https://app.any.run/tasks/8419e260-4885-4c03-b6af-e294364608d3 |
| Verdict: | No threats detected |
| Analysis date: | July 24, 2019, 02:26:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | EB8A698D3793FD8C373A312B81192714 |
| SHA1: | 710AD9B153D243321A016B259995A1FC5C75BCC0 |
| SHA256: | 0203D5719D6F6622AAF582B2472C732A5E90824B2B5C1884CC0A6E8BC17C4E73 |
| SSDEEP: | 384:uuTz1sA5fbNJgFoCPVroj0H4d5UvkJKmFtxAi/AUJ9/+Z7:bTW+vUte0oJKU3Jv+Z7 |
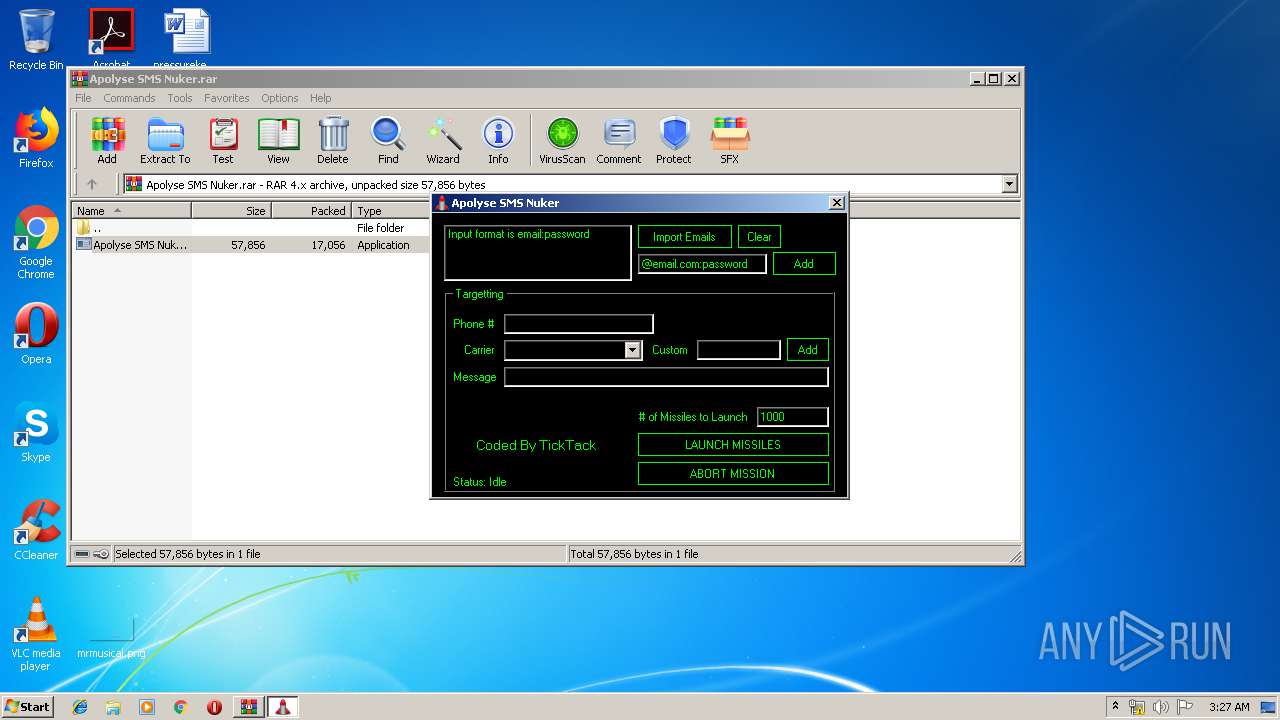
MALICIOUS
Application was dropped or rewritten from another process
- Apolyse SMS Nuker.exe (PID: 2480)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3880)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 17098 |
|---|---|
| UncompressedSize: | 57856 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2012:06:22 11:55:04 |
| PackingMethod: | Normal |
| ArchivedFileName: | Apolyse SMS Nuker.exe |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
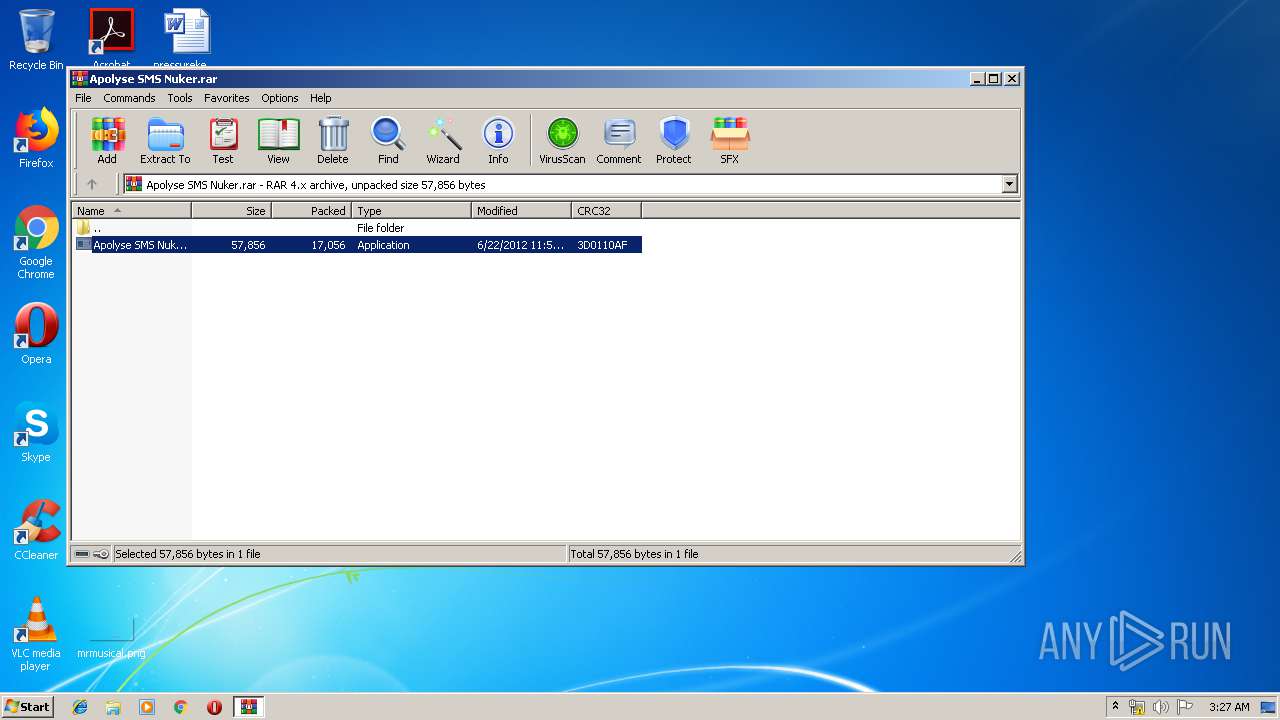
| 2480 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3880.23156\Apolyse SMS Nuker.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3880.23156\Apolyse SMS Nuker.exe | — | WinRAR.exe | |||||||||||
User: admin Company: TickTack Integrity Level: MEDIUM Description: Apolyse SMS Nuker Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3880 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Apolyse SMS Nuker.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
453
Read events
430
Write events
23
Delete events
0
Modification events
| (PID) Process: | (3880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3880) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Apolyse SMS Nuker.rar | |||
| (PID) Process: | (3880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3880.23156\Apolyse SMS Nuker.exe | executable | |
MD5:D3516FED15D2430A0CC97A5600281BFD | SHA256:992C384ED5C1EE51261DFE0BB6BE8FE28703C4893BC189BC794706F68851F276 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report