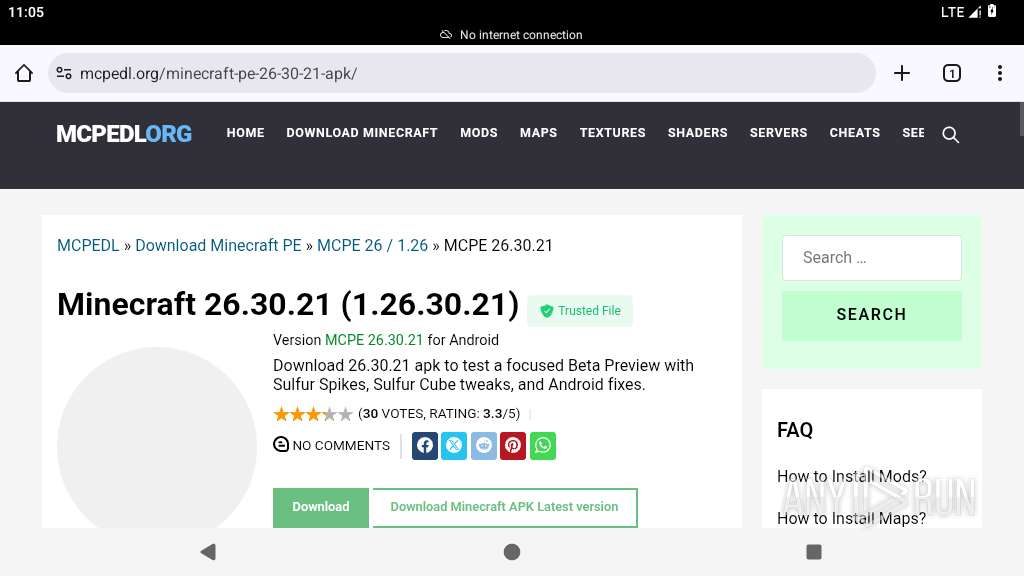
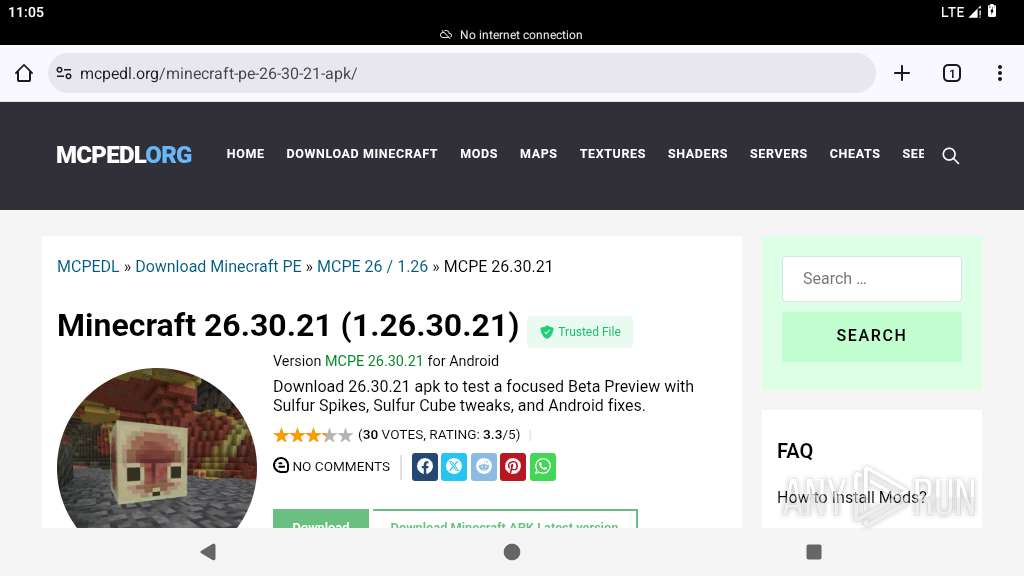
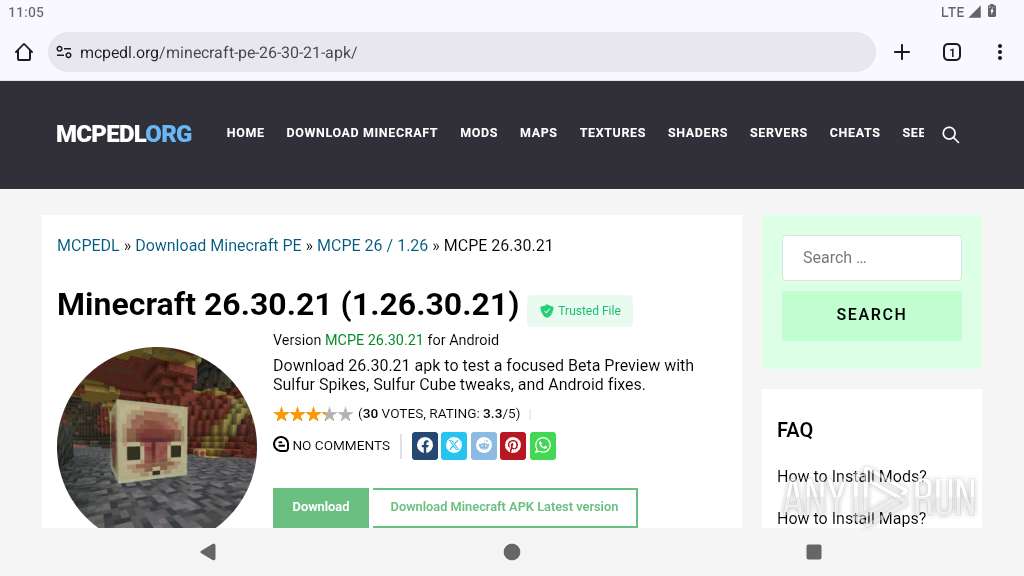
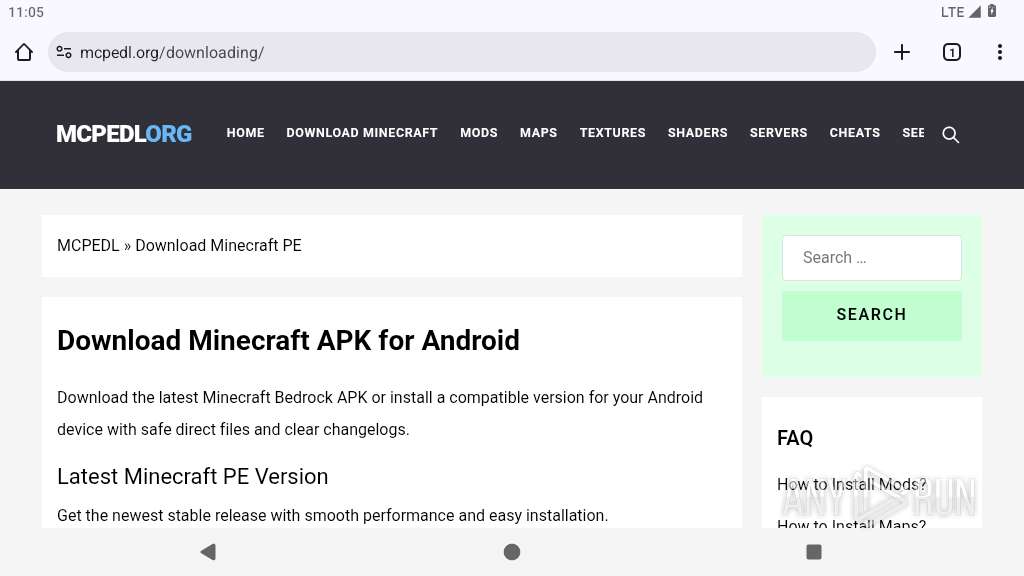
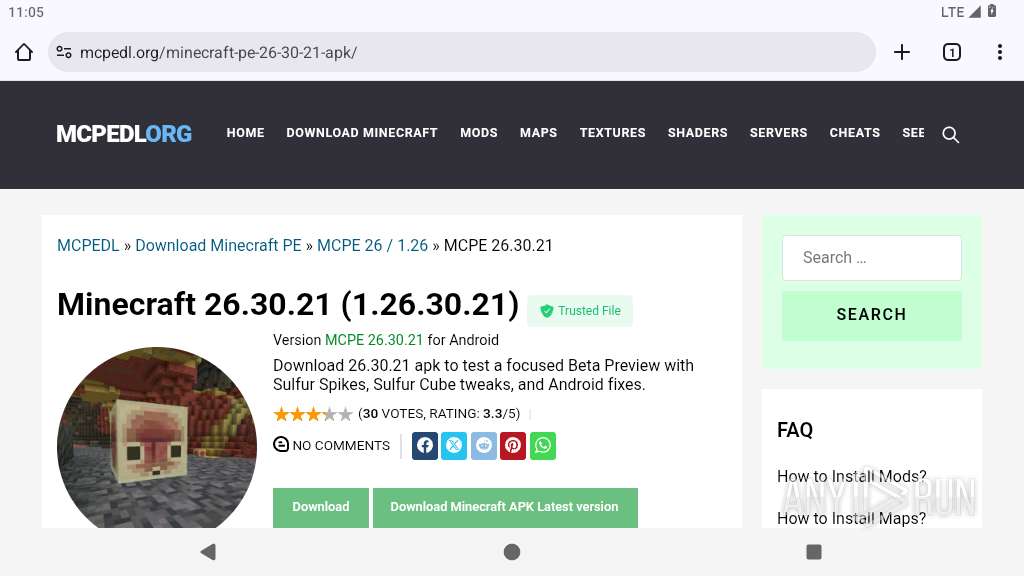
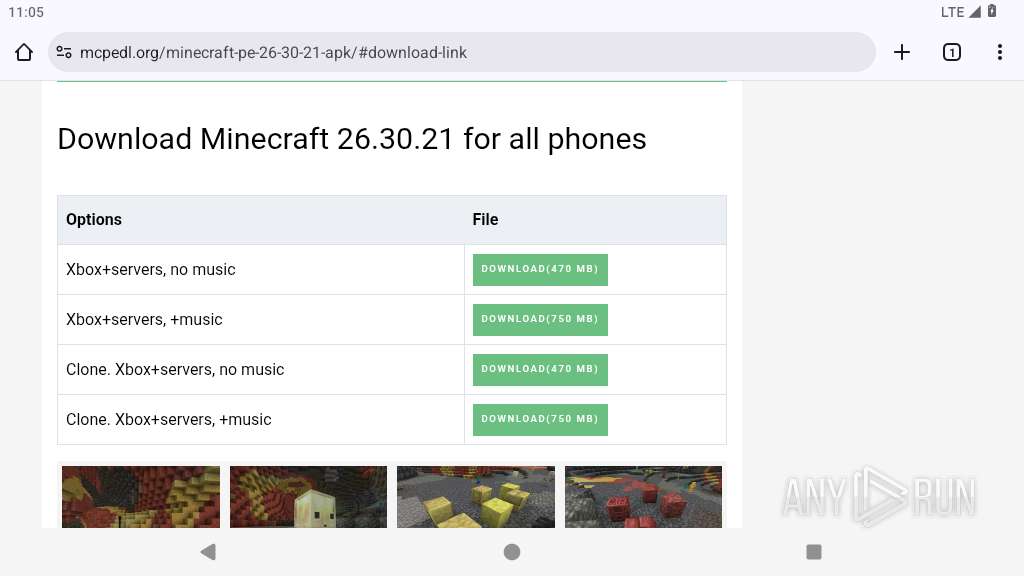
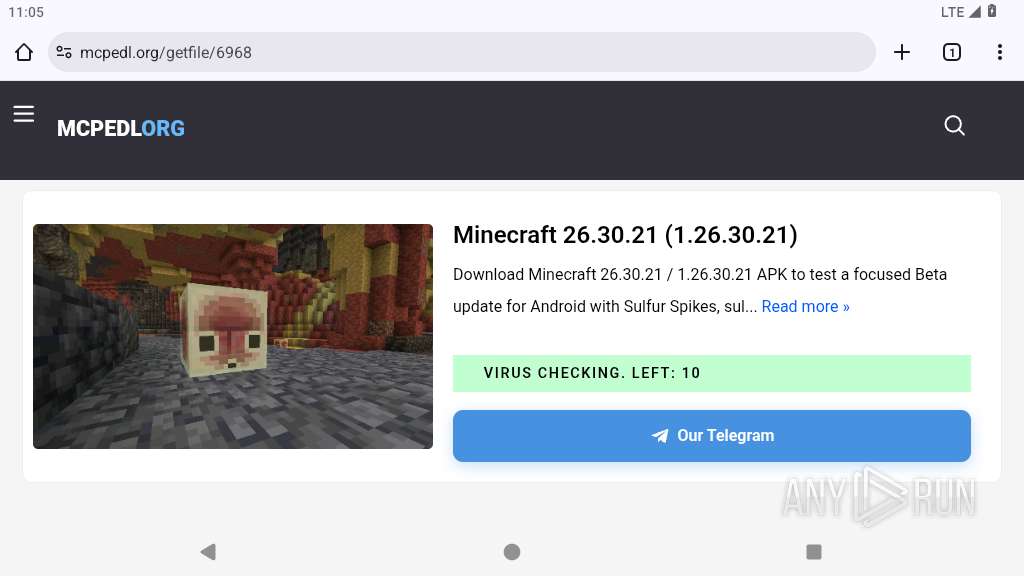
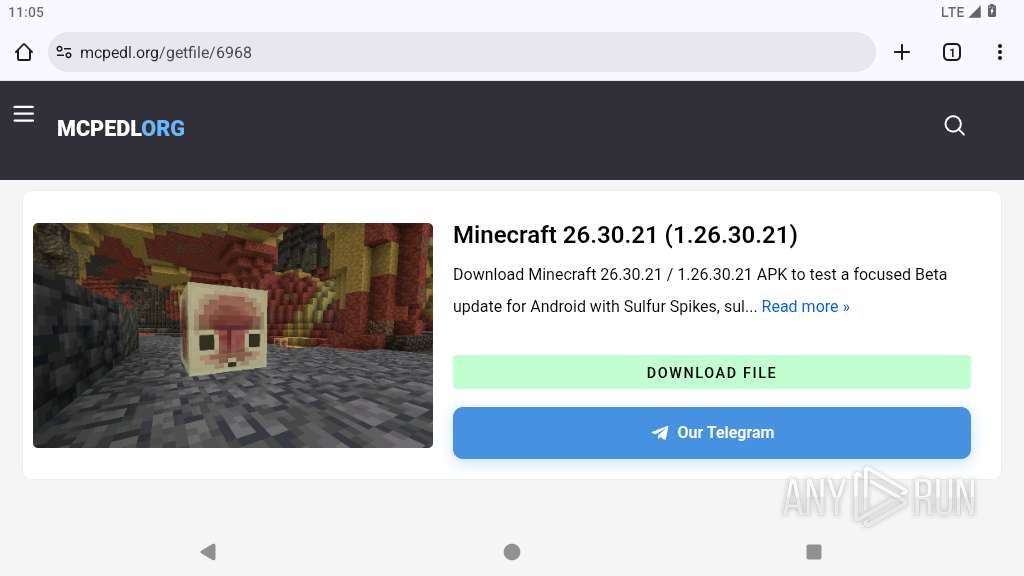
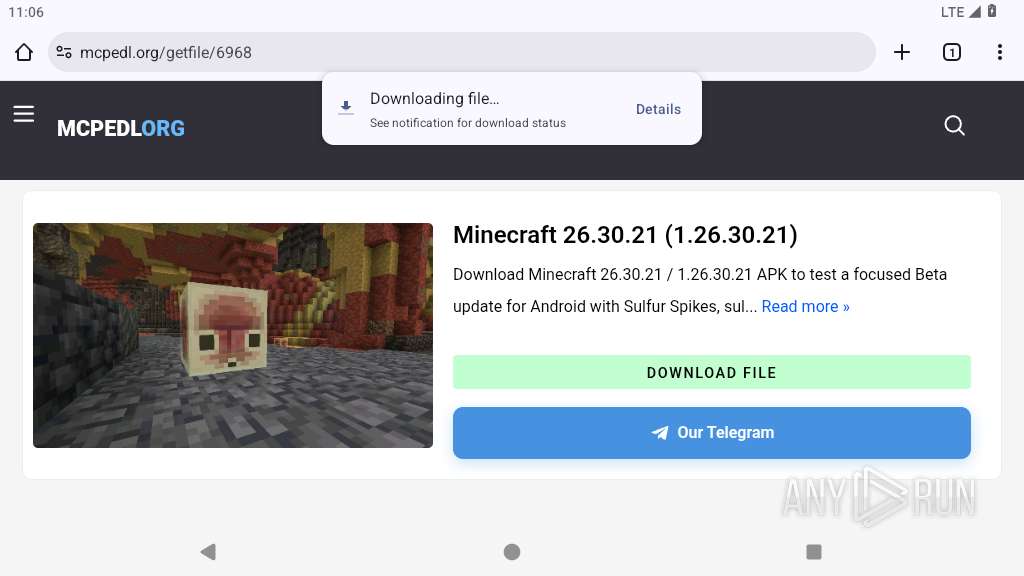
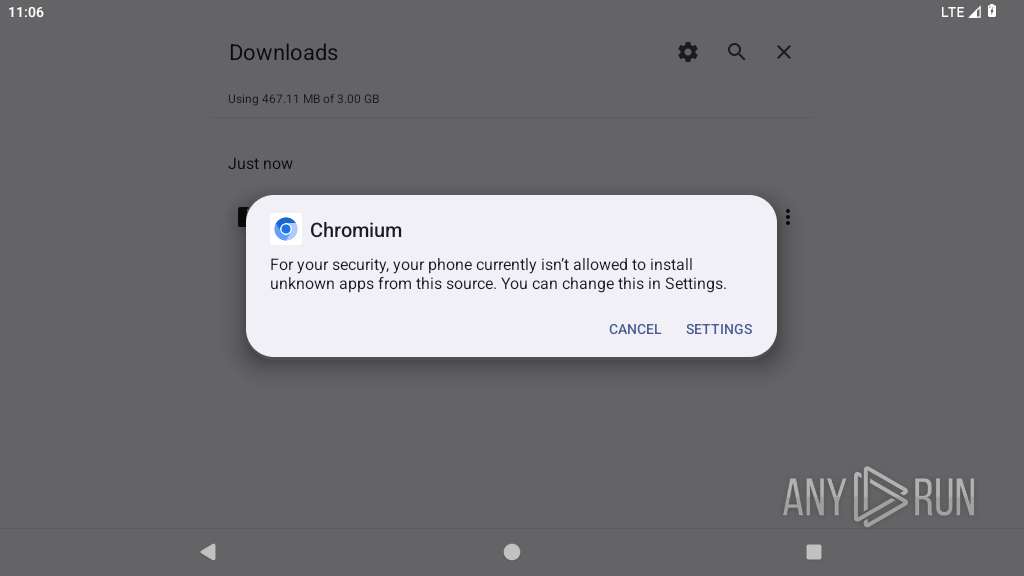
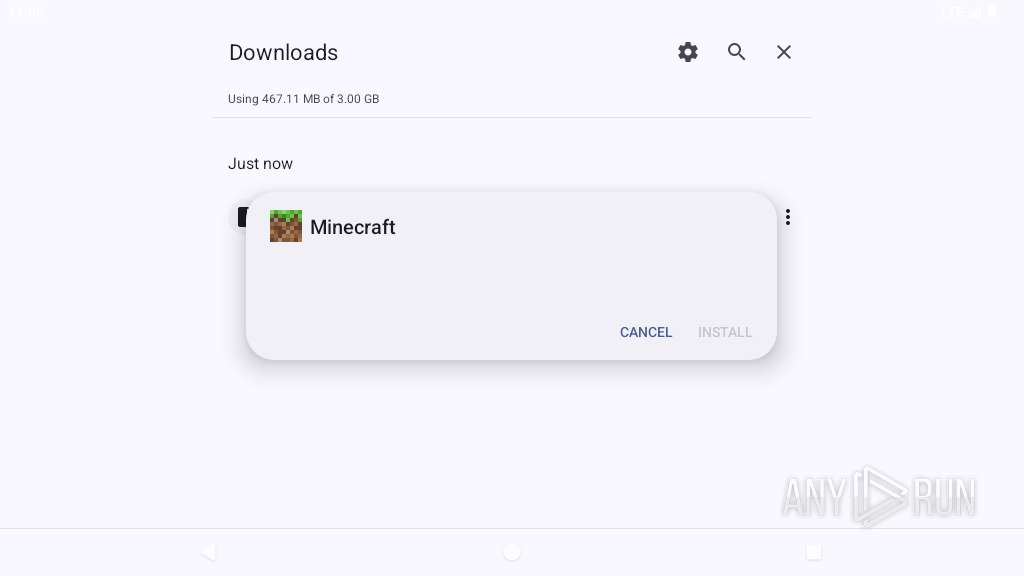
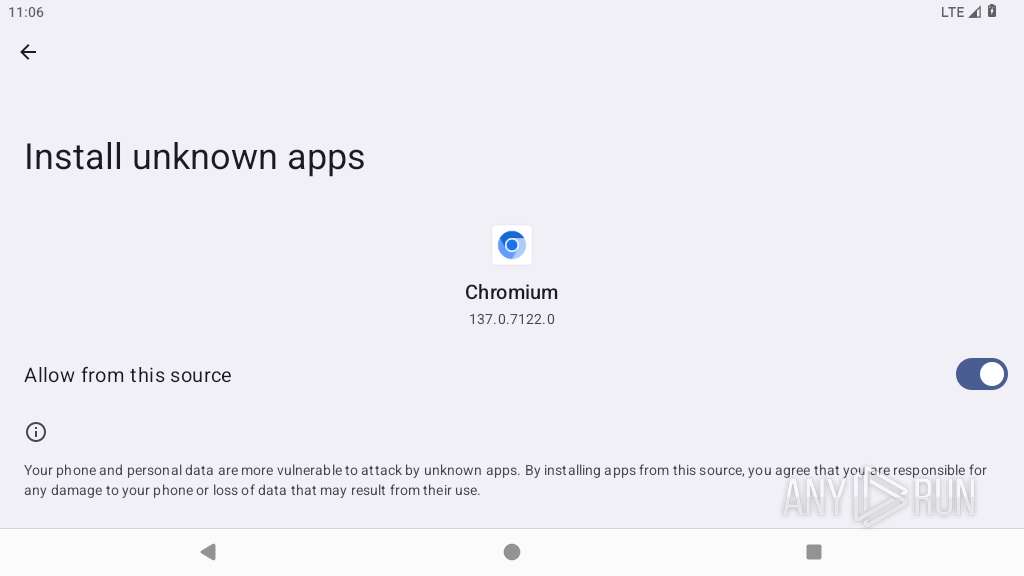
| URL: | https://mcpedl.org/minecraft-pe-26-30-21-apk/ |
| Full analysis: | https://app.any.run/tasks/bc60c215-a74a-4bb5-b64d-b8c48976c329 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2026, 23:04:52 |
| OS: | Android 14 |
| Indicators: | |
| MD5: | 3F566C37BAC537748329B3B1885C0753 |
| SHA1: | 4FE06BB2FE4EE079A870C062F22592E39507F0A6 |
| SHA256: | 01FFBD4FED440B7F00A96B46A8064CFAF4DC5D39021DBCBC208465E4ED4AA16A |
| SSDEEP: | 3:N8TADDPhg8iDn:2MXPhgz |
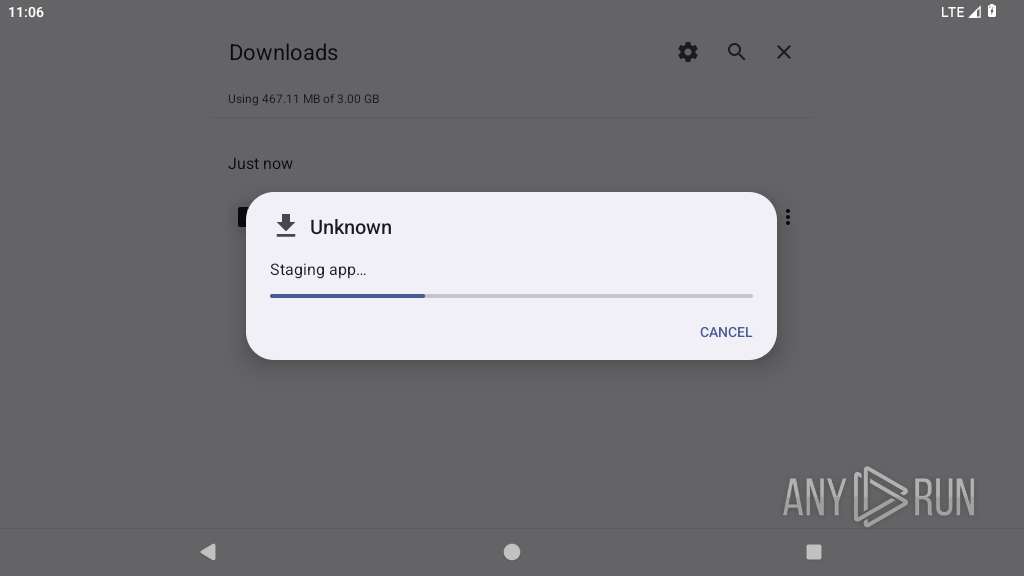
MALICIOUS
Executes system commands or scripts
- app_process64 (PID: 4920)
SUSPICIOUS
Cpu information query suggesting anti-analysis behavior
- app_process64 (PID: 4920)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 4920)
Accesses memory information
- app_process64 (PID: 4920)
Accesses external device storage files
- app_process64 (PID: 4920)
Accesses system-level resources
- app_process64 (PID: 4920)
Establishing a connection
- app_process64 (PID: 4920)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 4920)
Checks Bluetooth audio routing status
- app_process64 (PID: 4920)
Uses encryption API functions
- app_process64 (PID: 4920)
Returns the name of the current network operator
- app_process64 (PID: 4920)
INFO
Loads a native library into the application
- app_process64 (PID: 4920)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 4920)
Retrieves CPU core information
- app_process64 (PID: 4920)
Dynamically registers broadcast event listeners
- app_process64 (PID: 4920)
Retrieves the value of a secure system setting
- app_process64 (PID: 4920)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 4920)
Detects device power status
- app_process64 (PID: 4920)
Verifies whether the device is connected to the internet
- app_process64 (PID: 4920)
Returns elapsed time since boot
- app_process64 (PID: 4920)
Dynamically loads a class in Java
- app_process64 (PID: 4920)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 4920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
169
Monitored processes
41
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
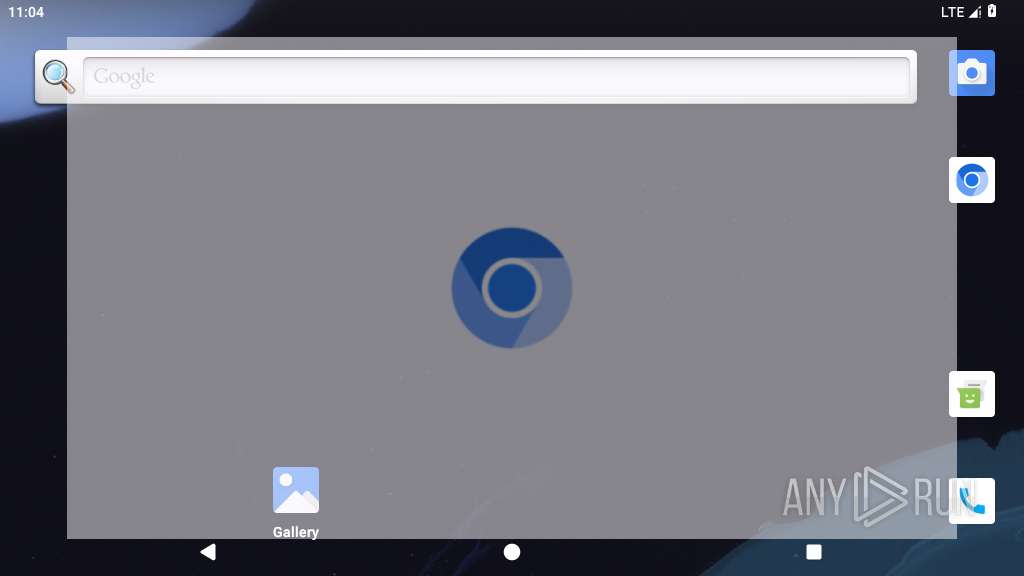
| 3970 | org.chromium.chrome | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4025 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4036 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4049 | com.android.traceur | /system/bin/app_process64 | — | app_process64 |
User: u0_a54 Integrity Level: UNKNOWN Exit code: 512 | ||||
| 4068 | org.chromium.chrome:privileged_process0 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4091 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4151 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4173 | com.android.providers.partnerbookmarks | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4242 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4262 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
307
Text files
377
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4242 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.WlCxIk/list.pb | binary | |
MD5:— | SHA256:— | |||
| 4242 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.WlCxIk/manifest.json | text | |
MD5:— | SHA256:— | |||
| 4242 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.WlCxIk/LICENSE | text | |
MD5:— | SHA256:— | |||
| 4242 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.WlCxIk/_metadata/verified_contents.json | text | |
MD5:— | SHA256:— | |||
| 4242 | app_process64 | /data/data/org.chromium.chrome/app_chrome/component_crx_cache/cab4d1f0a6a2a1afecae808a520f6690dd2b9d58bf54762877f2dc9715d55461 | binary | |
MD5:— | SHA256:— | |||
| 4262 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.Lq5DiE/privacy-sandbox-attestations.dat | binary | |
MD5:— | SHA256:— | |||
| 4262 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.Lq5DiE/manifest.json | text | |
MD5:— | SHA256:— | |||
| 4262 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.Lq5DiE/_metadata/verified_contents.json | text | |
MD5:— | SHA256:— | |||
| 4262 | app_process64 | /data/data/org.chromium.chrome/app_chrome/component_crx_cache/38c89b12bb20a8f2751c9c7cd2e31c173a47af08c115e1ecccc2f5151a2cf2c6 | binary | |
MD5:— | SHA256:— | |||
| 4281 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.Qii2hL/decoded_xz | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
120
TCP/UDP connections
85
DNS requests
75
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1921 | app_process64 | GET | 204 | 142.251.153.119:443 | https://www.google.com/generate_204 | US | — | — | whitelisted |
3970 | app_process64 | GET | 200 | 142.250.154.138:80 | http://clients2.google.com/time/1/current?cup2key=9:cFoDjcD1RD8lUXQxD2fTLG81C7WZ_0jD_Dgf4a-llvw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 105 b | whitelisted |
2931 | app_process64 | POST | 200 | 142.251.127.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:fetchEekChain | US | binary | 778 b | whitelisted |
2931 | app_process64 | POST | 200 | 142.251.127.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:signCertificates?challenge=AAABndt9OIQBILStY9XdjVB0DkMVl7CrxAe9TLI=&request_id=482a5192-f70f-4086-8c84-9651ade7c880 | US | binary | 11.8 Kb | whitelisted |
3970 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acmmwq7dser4xm5sepzjv74g65vq_2023.7.28.10/cffplpkejcbdpfnfabnjikeicbedmifn_2023.07.28.10_all_acgbwixmcanakp2bkoppyszsbkrq.crx3 | US | compressed | 6.04 Kb | whitelisted |
3970 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | US | compressed | 6.41 Kb | whitelisted |
3970 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/gcmjkmgdlgnkkcocmoeiminaijmmjnii/b809333d493ae614f8a7c0f09385e344aad6c0188126095c0c61362c478435eb | US | binary | 56.1 Kb | whitelisted |
3970 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/obedbbhbpmojnkanicioggnmelmoomoc/e40bb820d29fb9a9bf8935fa5fbe77b363cf9c553cd0c1993bf0a9bec48686e4 | US | binary | 4.41 Mb | whitelisted |
3970 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/pg4njza7nbdid7jkzqa63dqjqy_662/lmelglejhemejginpboagddgdfbepgmp_662_all_ZZ_ac6u6ze7sm7u2dv6kzbnczrhotmq.crx3 | US | compressed | 390 Kb | whitelisted |
3970 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lkptbildbpqiy52krytlomh6za_2026.3.23.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2026.03.23.01_all_lij76gb6h65kut3ntuqwmflaom.crx3 | US | compressed | 8.98 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 142.251.150.119:80 | www.google.com | GOOGLE | US | whitelisted |
— | — | 192.178.183.94:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 142.251.154.119:443 | www.google.com | GOOGLE | US | whitelisted |
452 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
3970 | app_process64 | 142.250.154.138:80 | google.com | GOOGLE | US | whitelisted |
3970 | app_process64 | 104.21.19.193:443 | mcpedl.org | CLOUDFLARENET | US | whitelisted |
3970 | app_process64 | 142.251.155.119:443 | www.google.com | GOOGLE | US | whitelisted |
3970 | app_process64 | 142.251.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3970 | app_process64 | 88.212.202.52:443 | counter.yadro.ru | UNITEDNET | RU | whitelisted |
3970 | app_process64 | 142.251.20.95:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
mcpedl.org |
| unknown |
accounts.google.com |
| whitelisted |
counter.yadro.ru |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
region1.google-analytics.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3970 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3970 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1921 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
3970 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3970 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
3970 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |