| File name: | 01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f |
| Full analysis: | https://app.any.run/tasks/d90dedb7-0dd6-4f49-8234-46a74c5e5773 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 17:09:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 12 sections |
| MD5: | 8817C6F8ECFE67FD50FEF745A882DABB |
| SHA1: | 5746632AF055D79489A402C47DEEEFD76C851F8F |
| SHA256: | 01FF59346C9B37097DF7C1B8EEAA1A2B2B8639D1CD987A71ED976DAE21C13E0F |
| SSDEEP: | 98304:0iXqxrMsCChROSZVx4FVIksTSw7l66xT8cG2gRCHxcVIUypuz4S2pS5Vv/Fykjgk:bzyR3oROeP |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the BIOS version
- 01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f.exe (PID: 1228)
Starts CMD.EXE for commands execution
- 01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f.exe (PID: 1228)
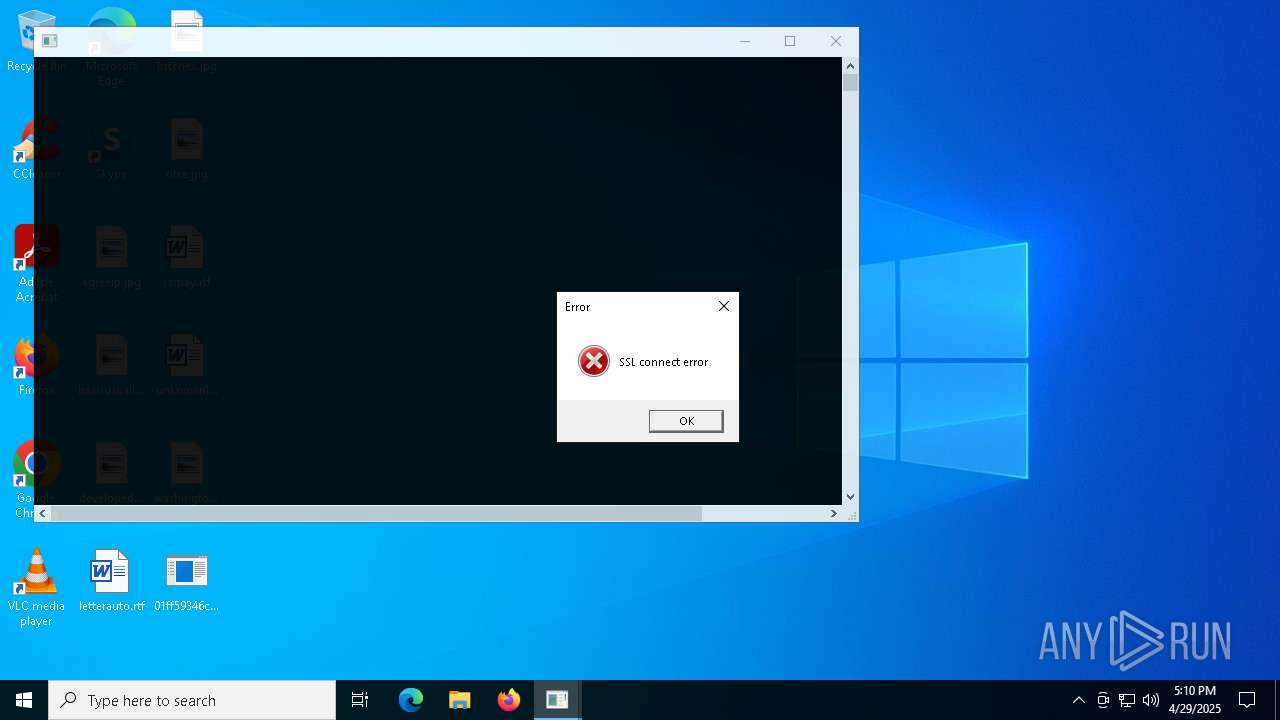
Executes application which crashes
- 01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f.exe (PID: 1228)
INFO
Reads the computer name
- 01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f.exe (PID: 1228)
Checks supported languages
- 01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f.exe (PID: 1228)
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 7036)
Creates files or folders in the user directory
- WerFault.exe (PID: 4812)
Checks proxy server information
- slui.exe (PID: 516)
Reads the software policy settings
- slui.exe (PID: 516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:19 05:48:42+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 461312 |
| InitializedDataSize: | 198656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6b6058 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
135
Monitored processes
9
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | "C:\Users\admin\Desktop\01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f.exe" | C:\Users\admin\Desktop\01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226505 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4336 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4812 | C:\WINDOWS\system32\WerFault.exe -u -p 1228 -s 1004 | C:\Windows\System32\WerFault.exe | — | 01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5124 | C:\WINDOWS\system32\cmd.exe /c certutil -hashfile "C:\Users\admin\Desktop\01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f.exe" MD5 | find /i /v "md5" | find /i /v "certutil" | C:\Windows\System32\cmd.exe | — | 01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6272 | find /i /v "certutil" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6712 | find /i /v "md5" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7036 | certutil -hashfile "C:\Users\admin\Desktop\01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f.exe" MD5 | C:\Windows\System32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 530
Read events
5 530
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4812 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_01ff59346c9b3709_3174ffaeb1117ce4d4233799b08e808d48f04e_28d1151c_26581946-a7a7-49e7-92b7-fb32bc8729ba\Report.wer | — | |
MD5:— | SHA256:— | |||
| 4812 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f.exe.1228.dmp | — | |
MD5:— | SHA256:— | |||
| 4812 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERCB14.tmp.xml | xml | |
MD5:A0DD7F65CF4779883E1C5C7D149C17A0 | SHA256:CCC4346A8D24C0459BC0F71598C593E118F11B9E3025138CC1BBE438316D0389 | |||
| 4812 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERCAF4.tmp.WERInternalMetadata.xml | binary | |
MD5:16ECA0D09E48F3205AE9074068B79501 | SHA256:DA39006DD601810484CAFFDA1C8341D43DA8AB845C8BC9E198750DC6E6AFCD6D | |||
| 4812 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERC9DA.tmp.dmp | binary | |
MD5:B8A50DDE53CC6A5A610378A241224273 | SHA256:A25D9DB13A69EA196BD0894E54DB8ECCE989ECA6A843B40807C6AD6949FC4274 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
43
DNS requests
15
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 20.109.210.53:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 304 | 20.109.210.53:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
3240 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
3240 | SIHClient.exe | GET | 200 | 2.19.126.226:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
3240 | SIHClient.exe | GET | 200 | 2.19.126.226:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
3240 | SIHClient.exe | GET | 200 | 2.19.126.226:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 40.69.42.241:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
3240 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
3240 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3240 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1228 | 01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f.exe | 104.26.0.5:443 | keyauth.win | CLOUDFLARENET | US | malicious |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3240 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3240 | SIHClient.exe | 2.19.126.226:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3240 | SIHClient.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
keyauth.win |
| malicious |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |
1228 | 01ff59346c9b37097df7c1b8eeaa1a2b2b8639d1cd987a71ed976dae21c13e0f.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |