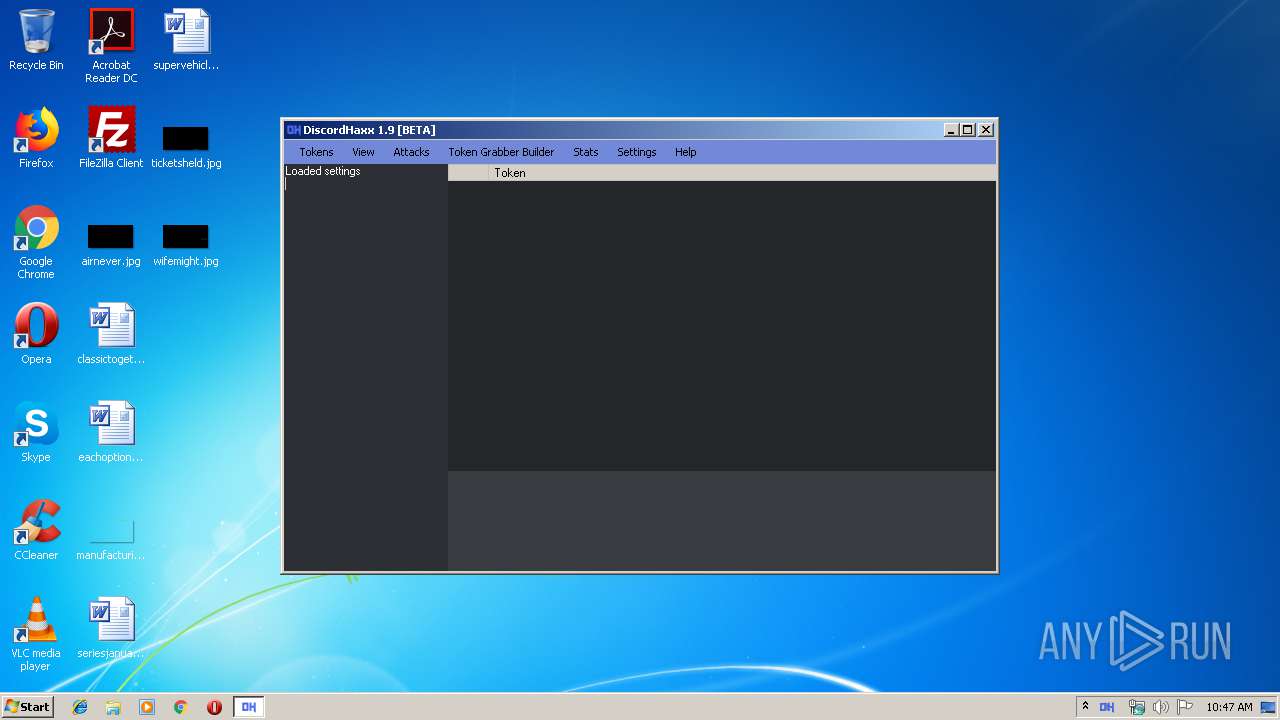
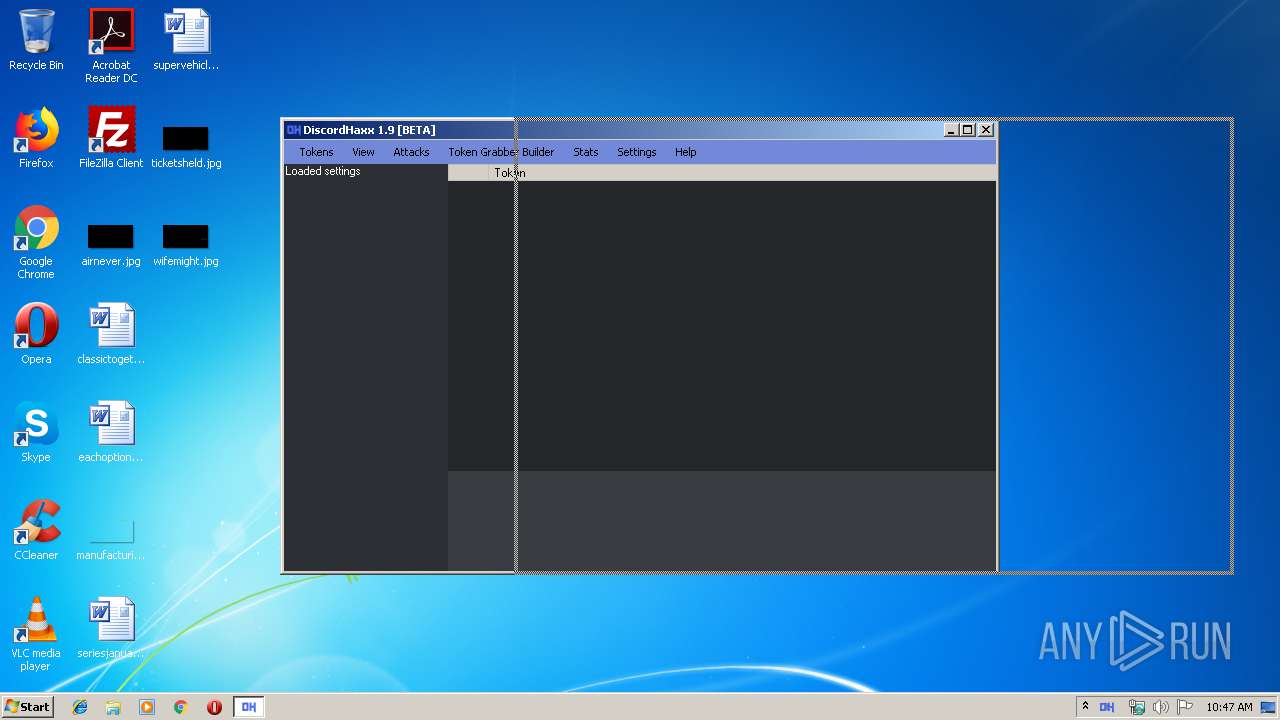
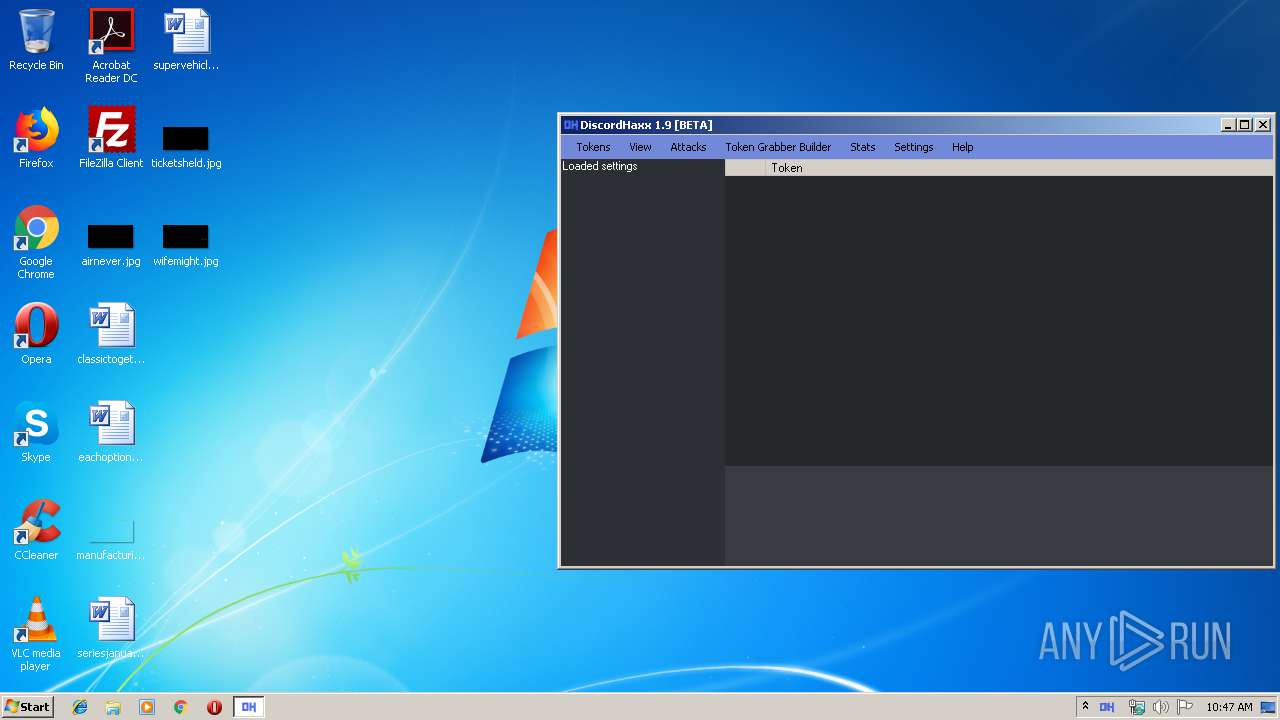
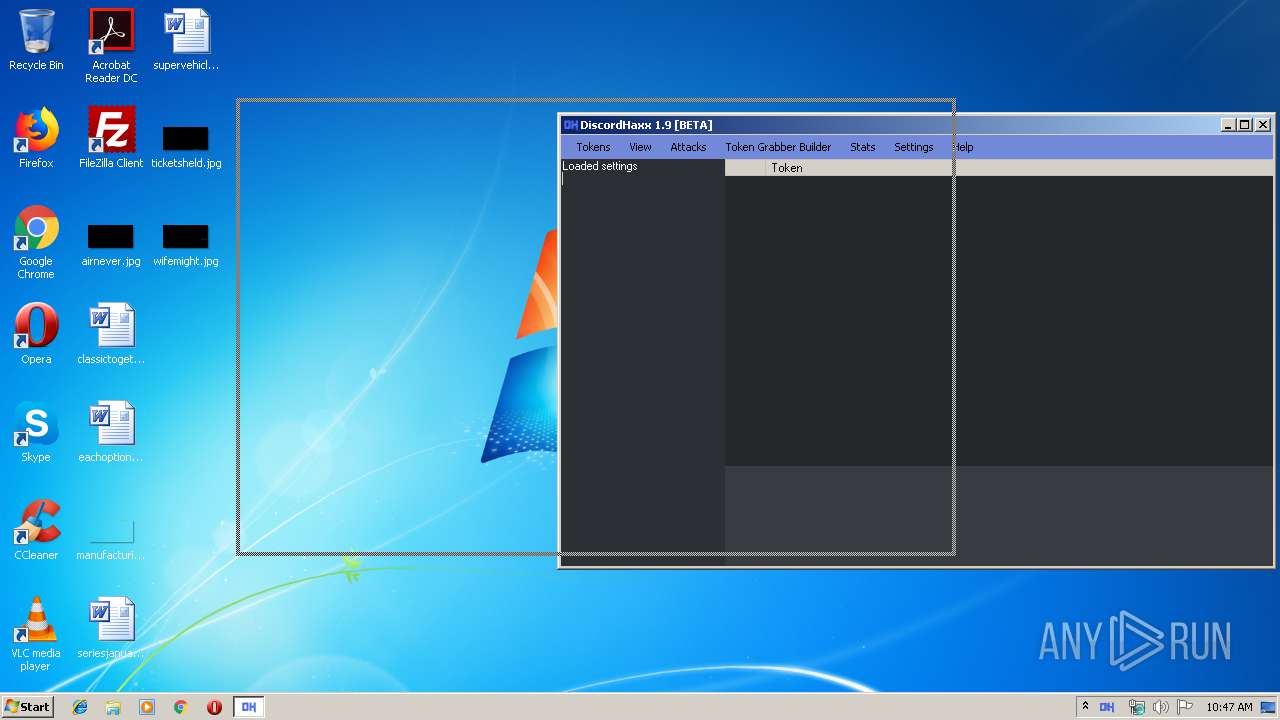
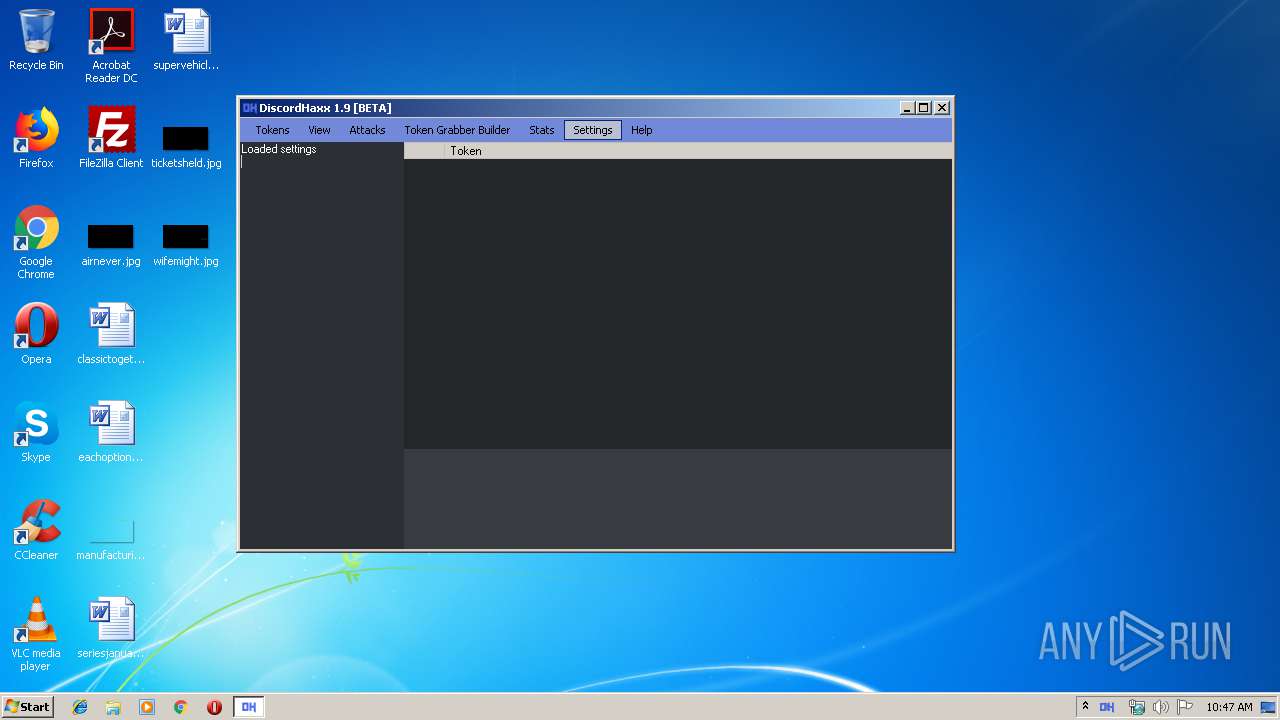
| File name: | DiscordHaxx 1.9 [BETA].exe |
| Full analysis: | https://app.any.run/tasks/acb1f53d-3742-4226-bc2e-bd20fbeffa74 |
| Verdict: | Malicious activity |
| Analysis date: | September 02, 2019, 09:46:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A2D44456C20101332B6D222906CDDDEE |
| SHA1: | A6AB4F8BAC66FCA726EB477658A336DD22E2AC74 |
| SHA256: | 01EB57FD4B25142BA43680E0849E2466A272B1D39F5ECFA58761A7DC594FE1BA |
| SSDEEP: | 49152:55jLVfwBVlxguHzkQgOipOqHHkHeGmUQ5320i7KHf:55hwXguT1MlHk+GVQk0im/ |
MALICIOUS
Application was dropped or rewritten from another process
- SPAMBOT.exe (PID: 3032)
- DiscordHaxx.exe (PID: 3608)
Loads dropped or rewritten executable
- DiscordHaxx.exe (PID: 3608)
SUSPICIOUS
Executes scripts
- DiscordHaxx 1.9 [BETA].exe (PID: 3728)
Executable content was dropped or overwritten
- DiscordHaxx 1.9 [BETA].exe (PID: 3728)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:27 22:03:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 190976 |
| InitializedDataSize: | 242176 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d759 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Apr-2019 20:03:27 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 27-Apr-2019 20:03:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E854 | 0x0002EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69231 |
.rdata | 0x00030000 | 0x00009A9C | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13286 |
.data | 0x0003A000 | 0x000213D0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.25381 |
.gfids | 0x0005C000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.11154 |
.rsrc | 0x0005D000 | 0x0000DFD0 | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.63679 |
.reloc | 0x0006B000 | 0x00001FCC | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64554 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.10026 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 5.25868 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.02609 | 1128 | UNKNOWN | English - United States | RT_ICON |
5 | 5.18109 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.04307 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.15447 | 494 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
35
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3032 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\SPAMBOT.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\SPAMBOT.exe | — | WScript.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: AnarchyGrabber Exit code: 0 Version: 0.0.2.0 Modules
| |||||||||||||||
| 3608 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\DiscordHaxx.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\DiscordHaxx.exe | WScript.exe | ||||||||||||
User: admin Company: iLinked Software Integrity Level: MEDIUM Description: DiscordHaxx Exit code: 0 Version: 1.8.5.0 Modules
| |||||||||||||||
| 3728 | "C:\Users\admin\AppData\Local\Temp\DiscordHaxx 1.9 [BETA].exe" | C:\Users\admin\AppData\Local\Temp\DiscordHaxx 1.9 [BETA].exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3964 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\RarSFX0\run.vbs" | C:\Windows\System32\WScript.exe | — | DiscordHaxx 1.9 [BETA].exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
811
Read events
789
Write events
22
Delete events
0
Modification events
| (PID) Process: | (3728) DiscordHaxx 1.9 [BETA].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3728) DiscordHaxx 1.9 [BETA].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3964) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3964) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3608) DiscordHaxx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3608) DiscordHaxx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3608) DiscordHaxx.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
8
Suspicious files
0
Text files
10
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3728 | DiscordHaxx 1.9 [BETA].exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Information\Changelog.txt | text | |
MD5:8DBA3C2D34AB8BA3201FEFC777FF17E2 | SHA256:E386D5964EEC4296F723463F739EB6DC368C64843AA3FAC45360BE285A8E0F62 | |||
| 3728 | DiscordHaxx 1.9 [BETA].exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Themes\Icons\AppleTheme.ico | image | |
MD5:4EDE8EFF1669E9F4B8889B4DF77F8A0C | SHA256:755CBD5E30832A4AD32CCB211794BD9AD2900909CF2075F6F262C65F3FF7E893 | |||
| 3728 | DiscordHaxx 1.9 [BETA].exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Settings\Settings.json | text | |
MD5:5FD55357E3C9307C94638E2ECD9F694A | SHA256:FDF555CDAB77A9921972673917B014A1198DCCD7E37056B2214E7C0FAF4D18DB | |||
| 3728 | DiscordHaxx 1.9 [BETA].exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\TokenGrabber.bin | executable | |
MD5:FAB9ED6DE6C7579B5C3D3798042A9FDB | SHA256:C14CB0E81F3584BEA99E33610F369EE8DEE89BFDAED34C12A331891B93CB8B2D | |||
| 3728 | DiscordHaxx 1.9 [BETA].exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Information\README.txt | text | |
MD5:F6CD338F09657291879605F44F78A7A3 | SHA256:B6505D14BE249D624BB044EE2563F284D77C52B56FFE00BE5167CB1FFDE25479 | |||
| 3728 | DiscordHaxx 1.9 [BETA].exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Themes\DiscordHaxx.dht | text | |
MD5:DA8E70C47F6581691403CBBC007215A8 | SHA256:D67602BE736BCF6ECB076CA54181C3B638D397E19180513A09BED2CC9EF0B71C | |||
| 3728 | DiscordHaxx 1.9 [BETA].exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\run.vbs | text | |
MD5:195955D7520E841C1C806019E1284400 | SHA256:A7EF3A57CEE47CC3745CC730AEA8FAF2A4E86DC5E04A6FD81F57DE0D5FE314BE | |||
| 3728 | DiscordHaxx 1.9 [BETA].exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\DiscordHaxx.exe | executable | |
MD5:26F173E94F1FA44A405AF7A94BD8C49A | SHA256:B53AE81D91C10E6045033C814788BB537B6E5DB5DAA554FA6C4B5B75699B30F0 | |||
| 3728 | DiscordHaxx 1.9 [BETA].exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\SPAMBOT.pdb | pdb | |
MD5:9169E4C3C01AF9660D739E9EBCED4517 | SHA256:D1CCA5C954C5290E07F722BA4D989AEF1C6C6F71BB8A48253711DF065B5E971E | |||
| 3728 | DiscordHaxx 1.9 [BETA].exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\SPAMBOT.exe.config | xml | |
MD5:7B32E1417D368F9361A2DEDA7F0BCFAB | SHA256:D4D800C424B0E226D35F3595CBB0FA470EB44228780E7DFB2AF1A11B93AB6BFB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3608 | DiscordHaxx.exe | 104.20.208.21:443 | pastebin.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |