| download: | /IrisV3rm/Roblox-Asset-Scraper/releases/download/4.0.5/MassRobloxAssetStealer.exe |
| Full analysis: | https://app.any.run/tasks/39b7f3d1-29a6-40de-b108-3123de6d1030 |
| Verdict: | Malicious activity |
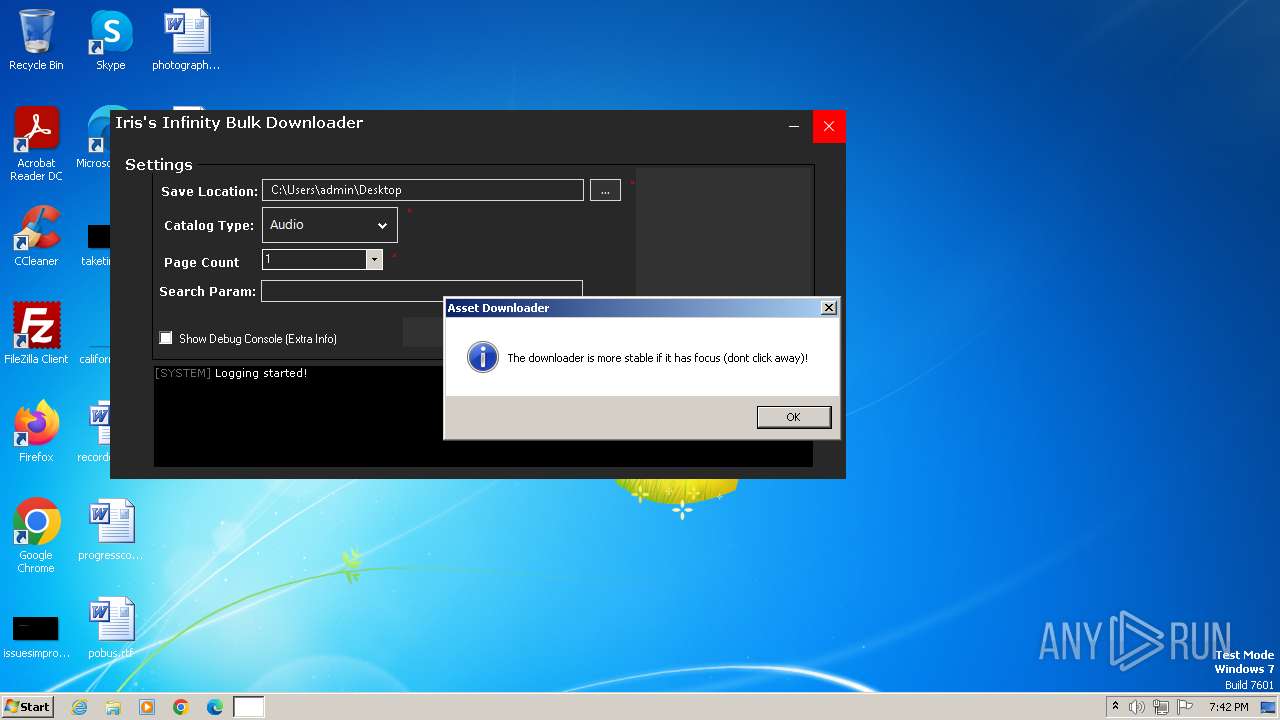
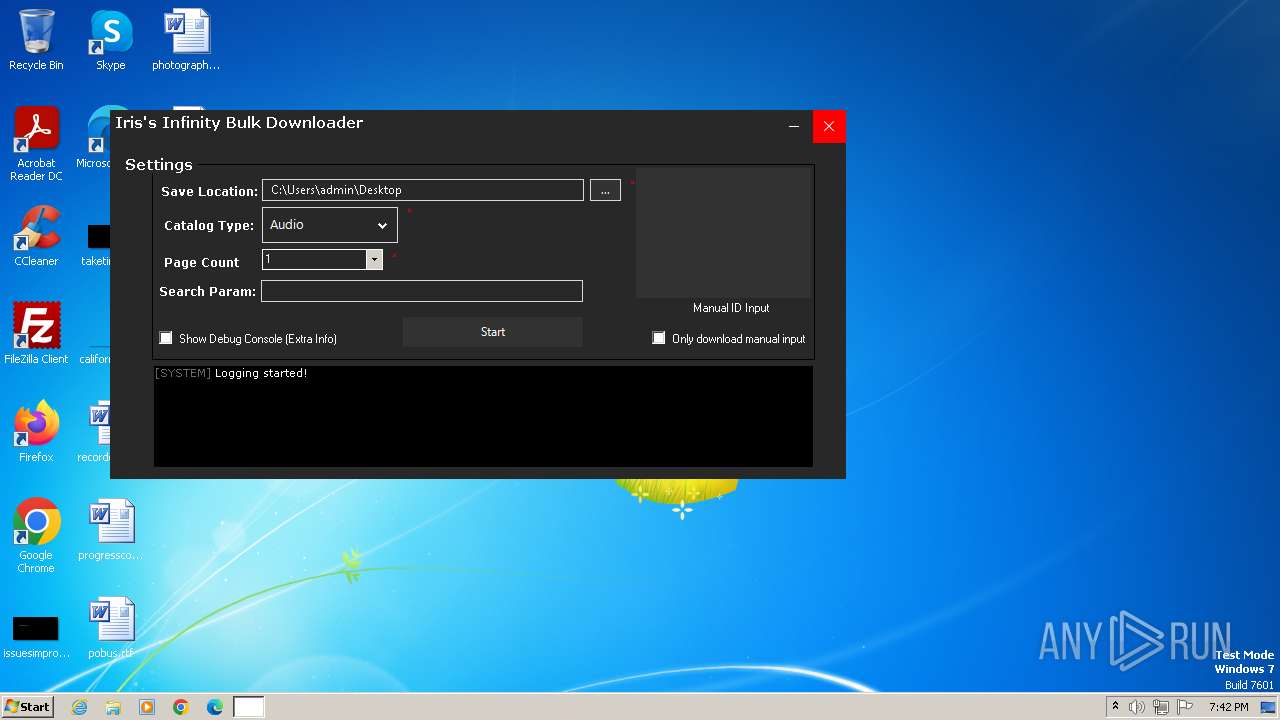
| Analysis date: | November 03, 2023, 19:42:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 65D55C589932CA85D4D07795C63C6E12 |
| SHA1: | 3332AF273F98C7B3F390C520D3E76DEB499B721B |
| SHA256: | 01E872E959381DFDB6A4CEB3E92DB29DAD7D767D2FA6A4DDC8F2109B0DAEAA21 |
| SSDEEP: | 98304:G8Svfx9vEqwYnDWNpK65DBoIBajEHyVy9YBPUHexnMO93WGY:wY |
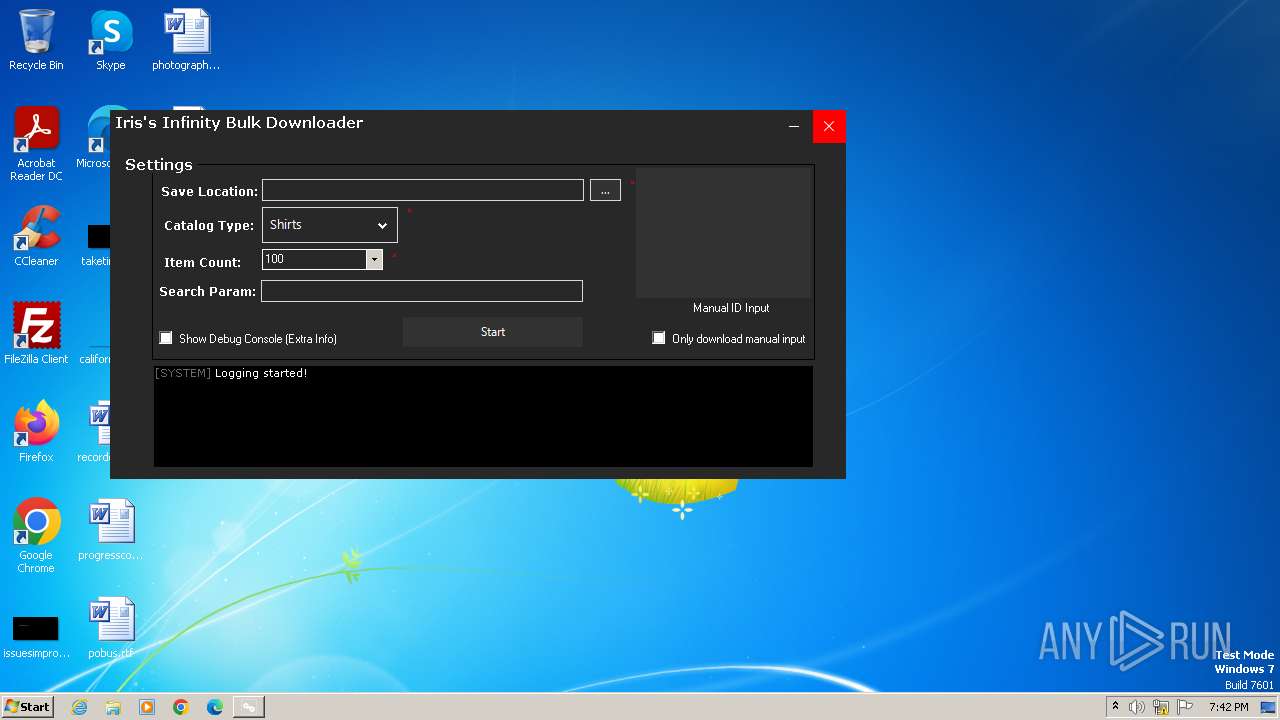
MALICIOUS
Drops the executable file immediately after the start
- MassRobloxAssetStealer.exe (PID: 3308)
SUSPICIOUS
Reads settings of System Certificates
- MassRobloxAssetStealer.exe (PID: 3308)
Reads the Internet Settings
- MassRobloxAssetStealer.exe (PID: 3308)
INFO
Reads the computer name
- MassRobloxAssetStealer.exe (PID: 3308)
- wmpnscfg.exe (PID: 3512)
Checks supported languages
- MassRobloxAssetStealer.exe (PID: 3308)
- wmpnscfg.exe (PID: 3512)
Manual execution by a user
- wmpnscfg.exe (PID: 3512)
Reads the machine GUID from the registry
- MassRobloxAssetStealer.exe (PID: 3308)
- wmpnscfg.exe (PID: 3512)
Create files in a temporary directory
- MassRobloxAssetStealer.exe (PID: 3308)
Reads Environment values
- MassRobloxAssetStealer.exe (PID: 3308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2084:07:10 22:59:49+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 1522688 |
| InitializedDataSize: | 272896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x175bee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | MassRobloxAssetStealer |
| FileVersion: | 1.0.0.0 |
| InternalName: | MassRobloxAssetStealer.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | MassRobloxAssetStealer.exe |
| ProductName: | MassRobloxAssetStealer |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
37
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3308 | "C:\Users\admin\AppData\Local\Temp\MassRobloxAssetStealer.exe" | C:\Users\admin\AppData\Local\Temp\MassRobloxAssetStealer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MassRobloxAssetStealer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3512 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 283
Read events
3 265
Write events
15
Delete events
3
Modification events
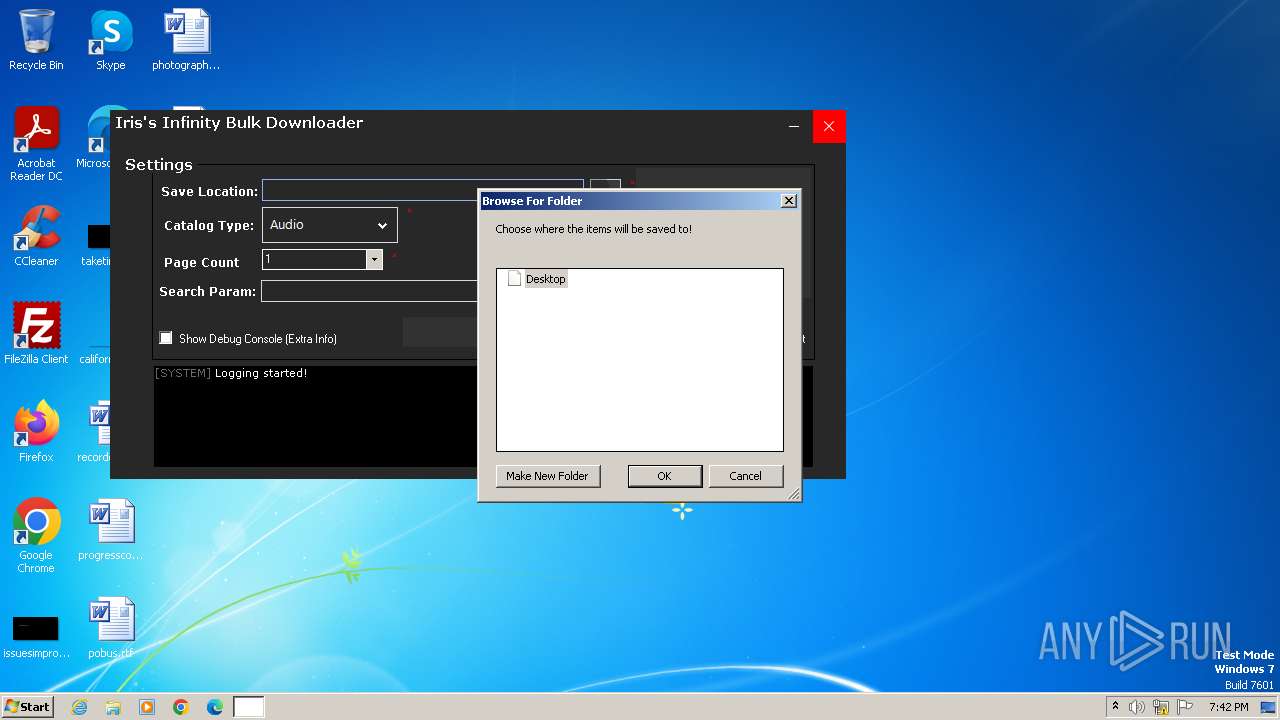
| (PID) Process: | (3308) MassRobloxAssetStealer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3308) MassRobloxAssetStealer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (3308) MassRobloxAssetStealer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
| (PID) Process: | (3512) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{80312084-547A-42F1-AD60-98B17B700032}\{0096301B-622E-43BE-AFC4-0BA08DE5BDCD} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3512) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{80312084-547A-42F1-AD60-98B17B700032} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3512) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{4C66A10C-7ED5-455B-8A1E-8865147F1F98} |
| Operation: | delete key | Name: | (default) |
Value: | |||
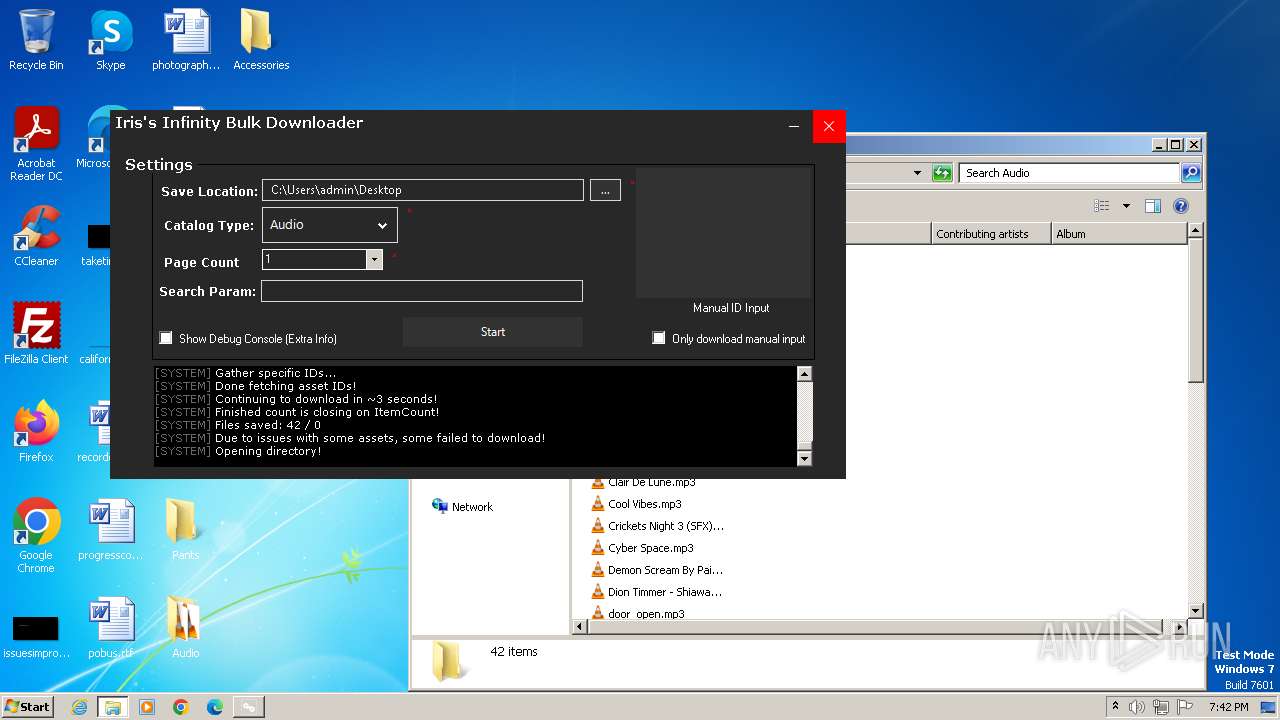
Executable files
1
Suspicious files
28
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
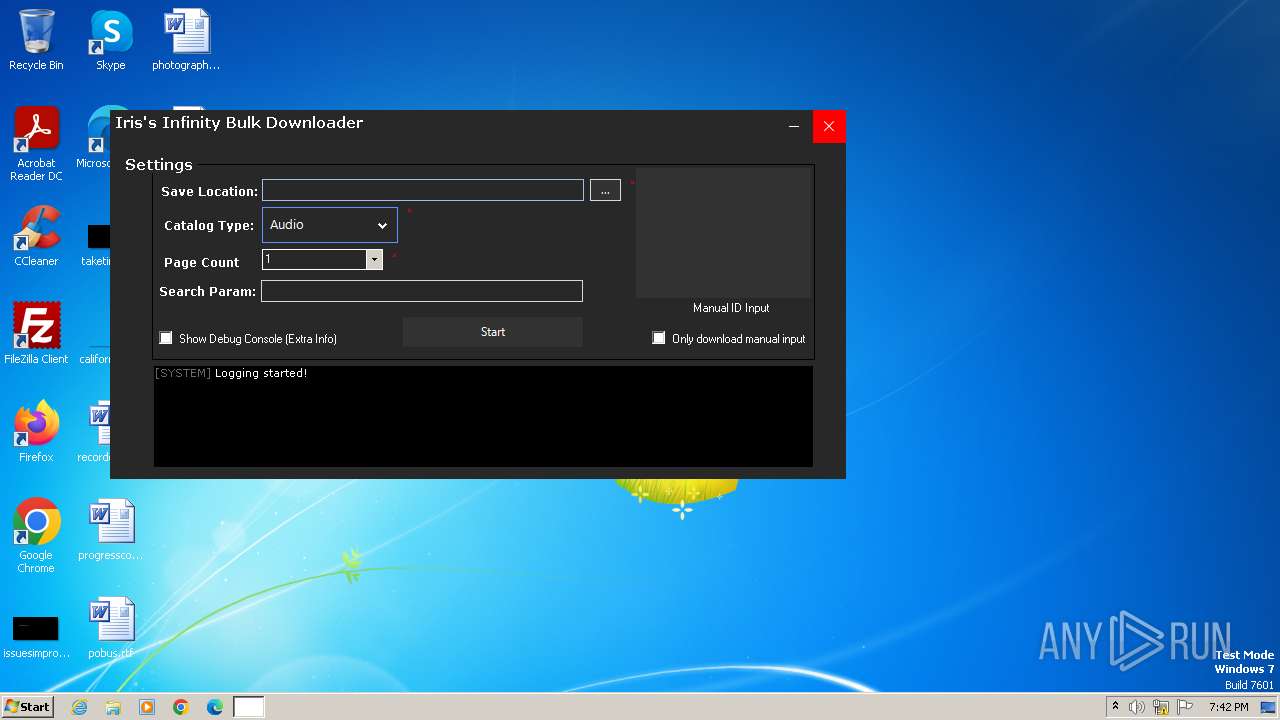
| 3308 | MassRobloxAssetStealer.exe | C:\Users\admin\Desktop\Audio\Demon Scream By Pained Screeches Wheezing 4 (SFX).mp3 | binary | |
MD5:70561E5194B425D1E8A0A85FE4F433E6 | SHA256:B719BEE739BA860D15E8EC885DD357C34D36CD7584EB5FFE4BEAC89C3E7C14BD | |||
| 3308 | MassRobloxAssetStealer.exe | C:\Users\admin\Desktop\Audio\Gun Shot.mp3 | binary | |
MD5:2A0D8A469ED04649A944666DDA99DFE3 | SHA256:5D0638C85CDA049C0879EBC529226E80E4B7D16CE95641C45842945E1EB12BE8 | |||
| 3308 | MassRobloxAssetStealer.exe | C:\Users\admin\Desktop\Audio\Paradise Falls.mp3 | binary | |
MD5:DBA1251FE38C313F38AD10587B4AEBC4 | SHA256:1DDEB739B65F863BEACAEDD30D0C08DCCBC51F4DFB9399947034747E4E22B25C | |||
| 3308 | MassRobloxAssetStealer.exe | C:\Users\admin\Desktop\Audio\Rain On Leaves 2 (SFX).mp3 | binary | |
MD5:8BF261DA3D94222A3F8227A1375397B1 | SHA256:58EFA0F519A50FB2F3A2F1308927B0FD61C1C907553A541DF25B6FBDF01B169D | |||
| 3308 | MassRobloxAssetStealer.exe | C:\Users\admin\Desktop\Audio\Life in an Elevator.mp3 | binary | |
MD5:E3F2423EF4D9DFA0CB2EDC17B80A722C | SHA256:B562251831AD3ED9EC760FEF418A1F7F4B86845D953036D48FB423A8E7749470 | |||
| 3308 | MassRobloxAssetStealer.exe | C:\Users\admin\Desktop\Audio\Hospital Horror Roars Booms 2 (SFX).mp3 | binary | |
MD5:33F6910FB55B1F3AF8F304BB1BBF556F | SHA256:787D8339971DAA27E374770D485F7774CDD2B4C040AA93DC8BDE07F4F5BF203F | |||
| 3308 | MassRobloxAssetStealer.exe | C:\Users\admin\Desktop\Audio\Neighborhood Birds 2 (SFX).mp3 | binary | |
MD5:11BC9179DB4BDDB79A0D4DC729FA4C90 | SHA256:9249D4A5F7ABC27BC25399673CA5FC53FB53D3167979669AEDFBF6912B9C4F14 | |||
| 3308 | MassRobloxAssetStealer.exe | C:\Users\admin\Desktop\Audio\Afterworld Ambience Weird Rumbling Ambience (SFX).mp3 | binary | |
MD5:8C38BDFC8E58674E7B695BA6824681E3 | SHA256:DBA5B0418369211C1EF98FDF7A8D05ADA900C194057053BCFE5112F1C7A9275C | |||
| 3308 | MassRobloxAssetStealer.exe | C:\Users\admin\Desktop\Audio\Clair De Lune.mp3 | — | |
MD5:— | SHA256:— | |||
| 3308 | MassRobloxAssetStealer.exe | C:\Users\admin\Desktop\Audio\8 Bitty Kitty - Underscore.mp3 | binary | |
MD5:7C195E931F79561278ED8D76FF976858 | SHA256:4C91E48BD802C61CD73326BCA4CFECEC1BCF3993201C9EA7DA9FDC69F3A5061D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
22
DNS requests
16
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
868 | svchost.exe | 95.101.148.135:80 | — | Akamai International B.V. | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
868 | svchost.exe | 88.221.124.138:80 | armmf.adobe.com | AKAMAI-AS | DE | unknown |
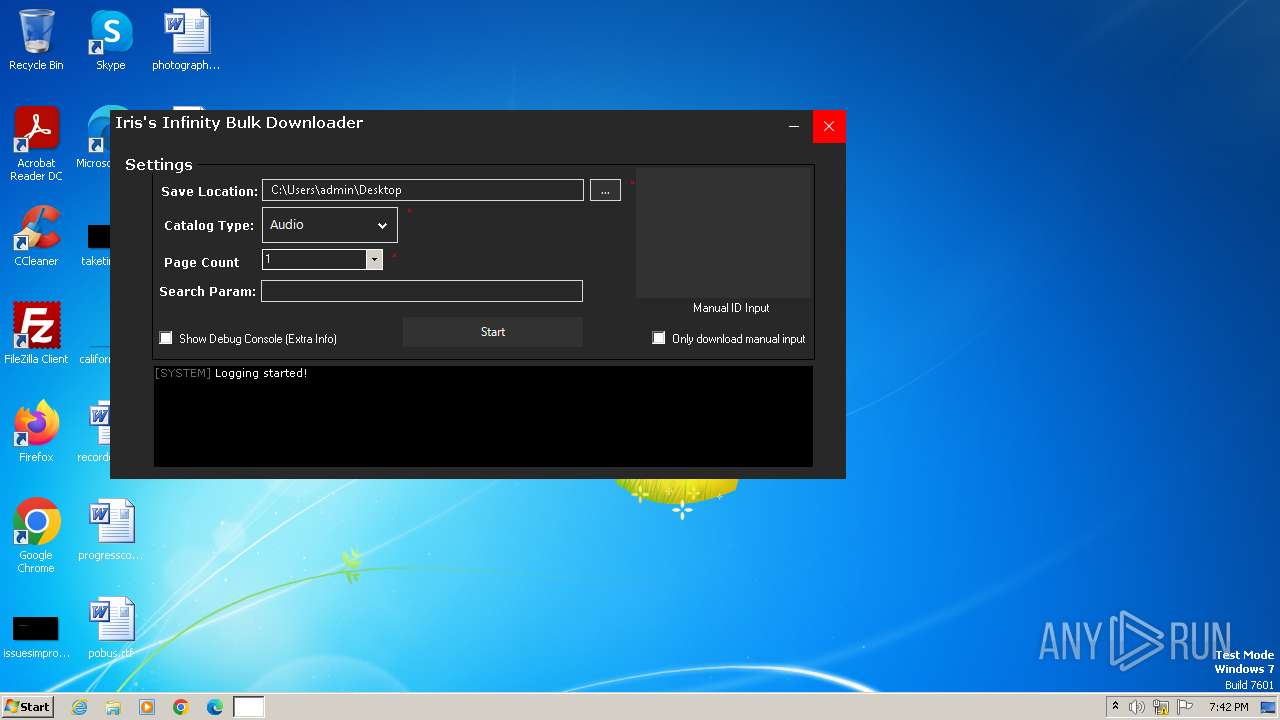
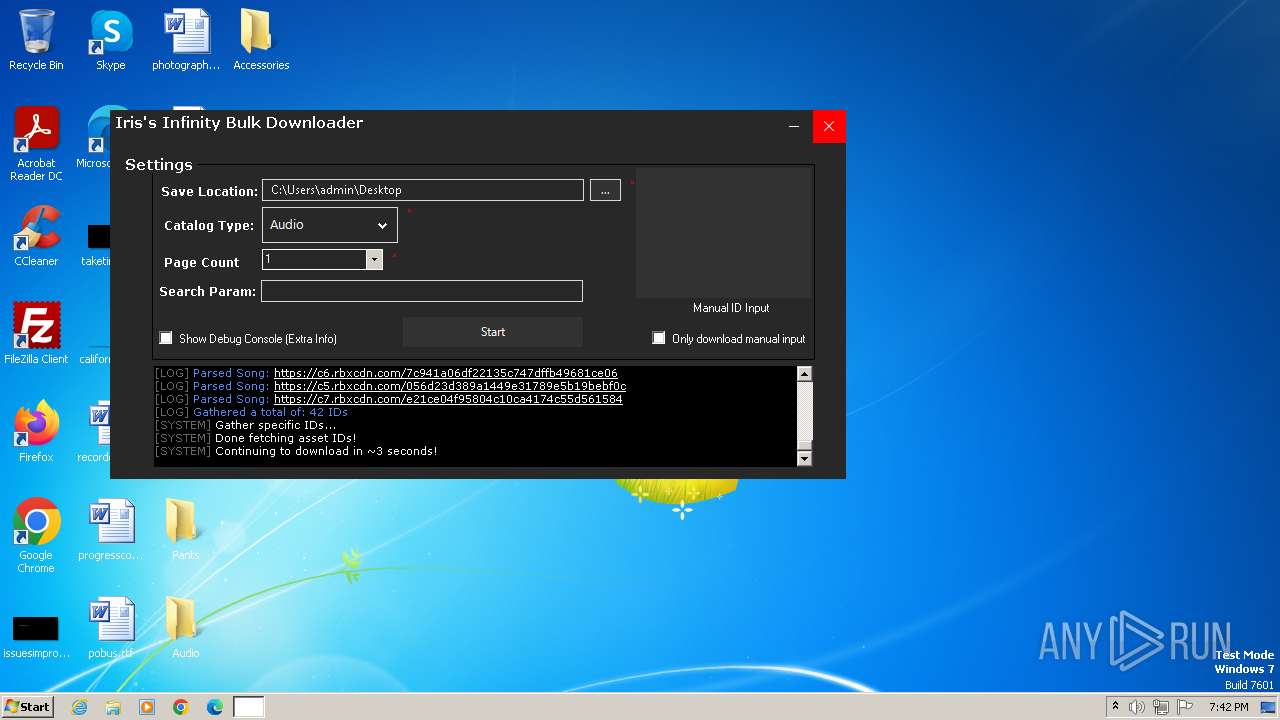
3308 | MassRobloxAssetStealer.exe | 104.21.16.76:443 | api.irisapp.ca | CLOUDFLARENET | — | unknown |
3308 | MassRobloxAssetStealer.exe | 205.185.216.42:443 | c7.rbxcdn.com | STACKPATH-CDN | US | whitelisted |
3308 | MassRobloxAssetStealer.exe | 205.185.216.10:443 | c7.rbxcdn.com | STACKPATH-CDN | US | whitelisted |
3308 | MassRobloxAssetStealer.exe | 2.16.164.115:443 | c1.rbxcdn.com | Akamai International B.V. | NL | unknown |
3308 | MassRobloxAssetStealer.exe | 2.16.164.104:443 | c5.rbxcdn.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
armmf.adobe.com |
| whitelisted |
api.irisapp.ca |
| unknown |
c7.rbxcdn.com |
| whitelisted |
c3.rbxcdn.com |
| whitelisted |
c6.rbxcdn.com |
| whitelisted |
c1.rbxcdn.com |
| whitelisted |
c5.rbxcdn.com |
| whitelisted |
c2.rbxcdn.com |
| whitelisted |
c4.rbxcdn.com |
| whitelisted |
c0.rbxcdn.com |
| whitelisted |