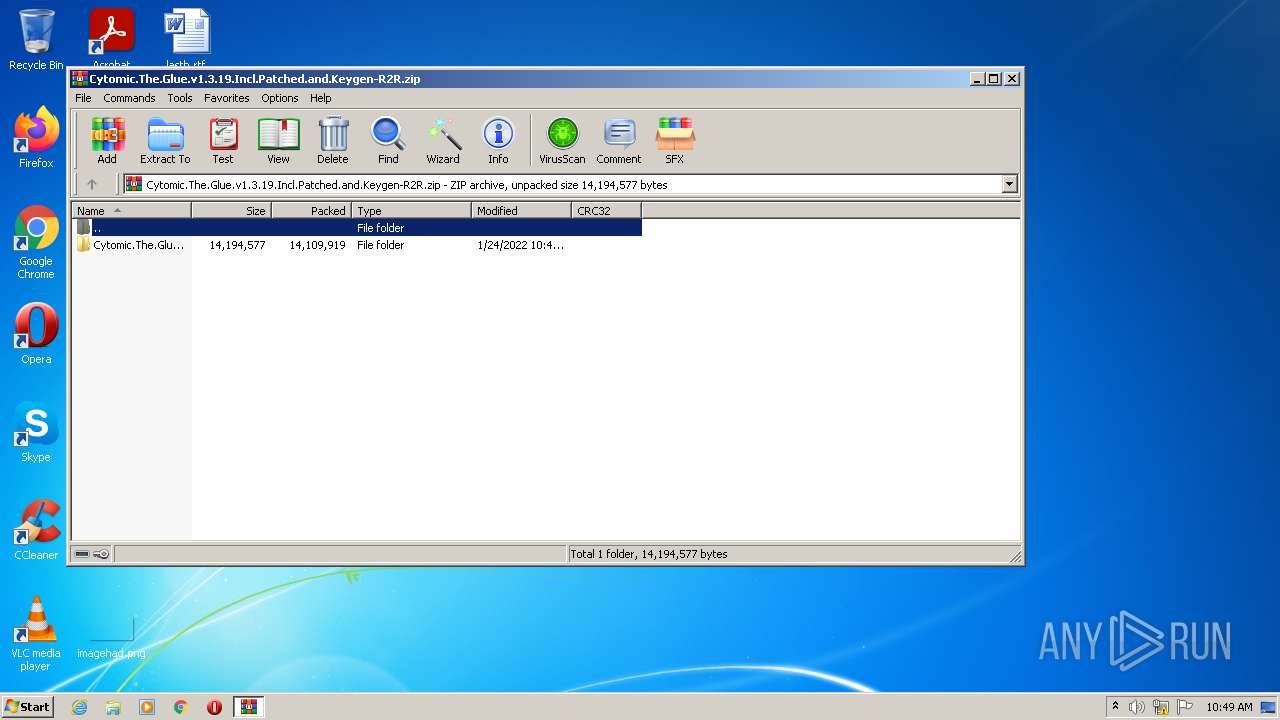
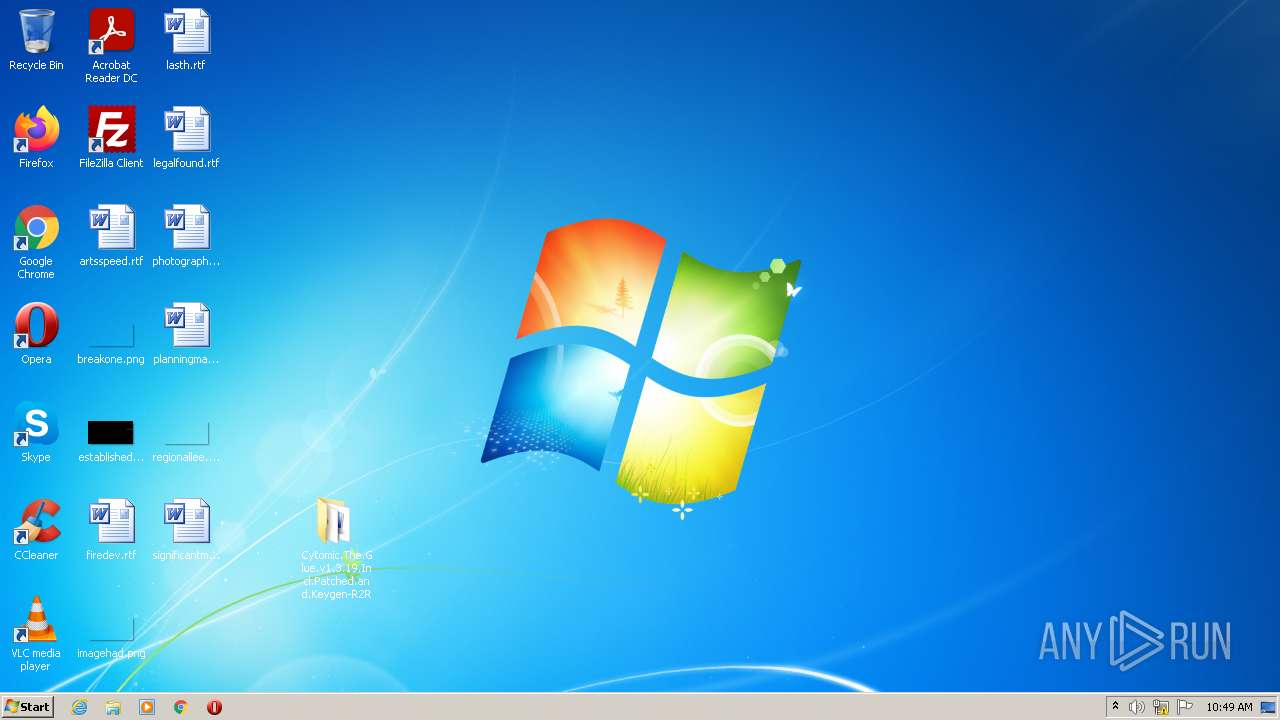
| File name: | Cytomic.The.Glue.v1.3.19.Incl.Patched.and.Keygen-R2R.zip |
| Full analysis: | https://app.any.run/tasks/48d259a8-e525-412a-940e-fd43f8e3e9d5 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 10:49:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | BC650B58E3BEE808B22AC214C64F6325 |
| SHA1: | 31425D0AD59214E496B6F9370859F0B4430A49CF |
| SHA256: | 01E0DFE0E0C4372B96AB529497370CC76A0E5FB71F6FB58E6E5347FF1A3943E1 |
| SSDEEP: | 393216:BsPmEXBWCbu+nDDhGXigniPktBkbapuPE:B4cCbRoigaykbyH |
MALICIOUS
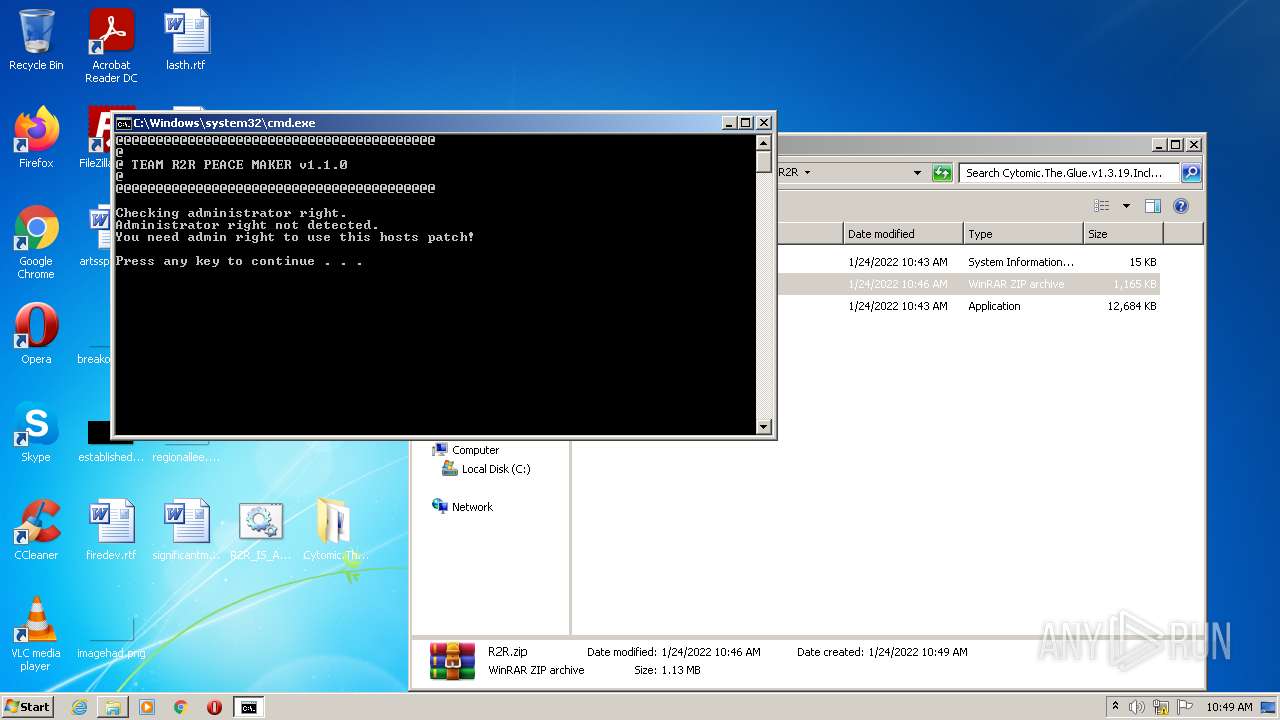
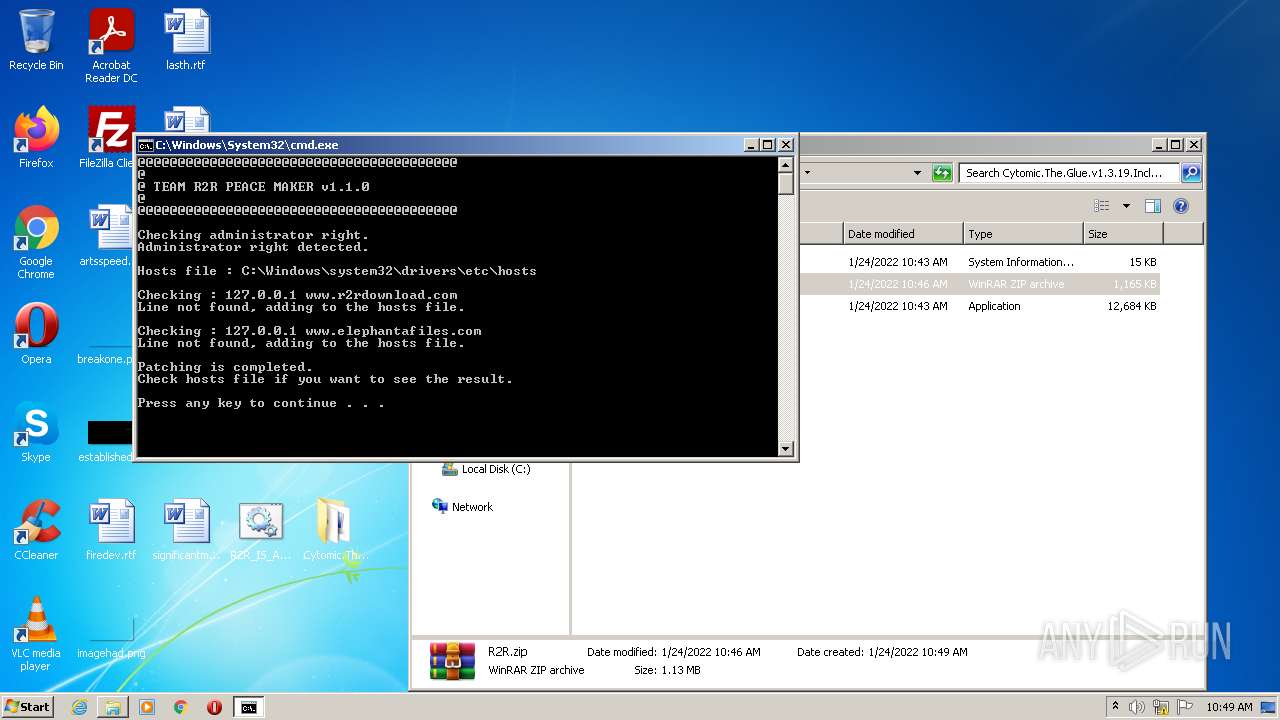
Writes to the hosts file
- cmd.exe (PID: 3276)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 576)
- WinRAR.exe (PID: 3768)
Checks supported languages
- WinRAR.exe (PID: 576)
- WinRAR.exe (PID: 3768)
- cmd.exe (PID: 2328)
- cmd.exe (PID: 3276)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 576)
INFO
Checks supported languages
- openfiles.exe (PID: 1088)
- openfiles.exe (PID: 3204)
- find.exe (PID: 4040)
- find.exe (PID: 3924)
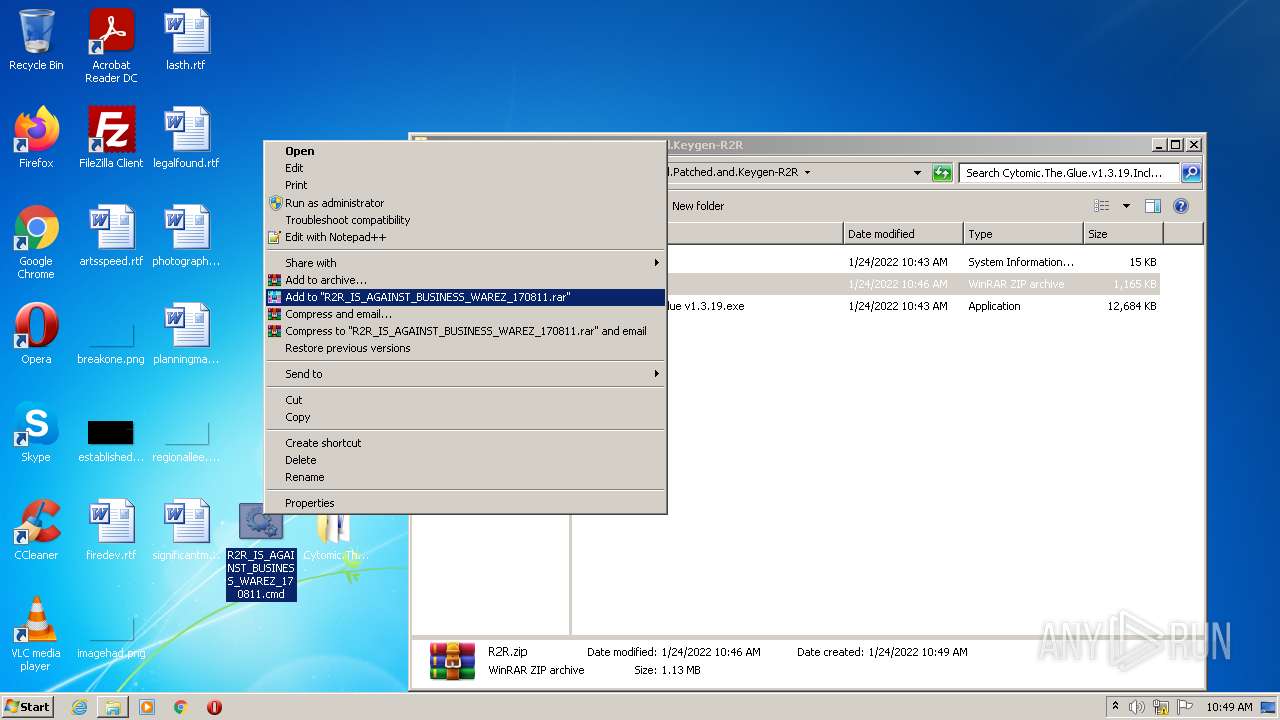
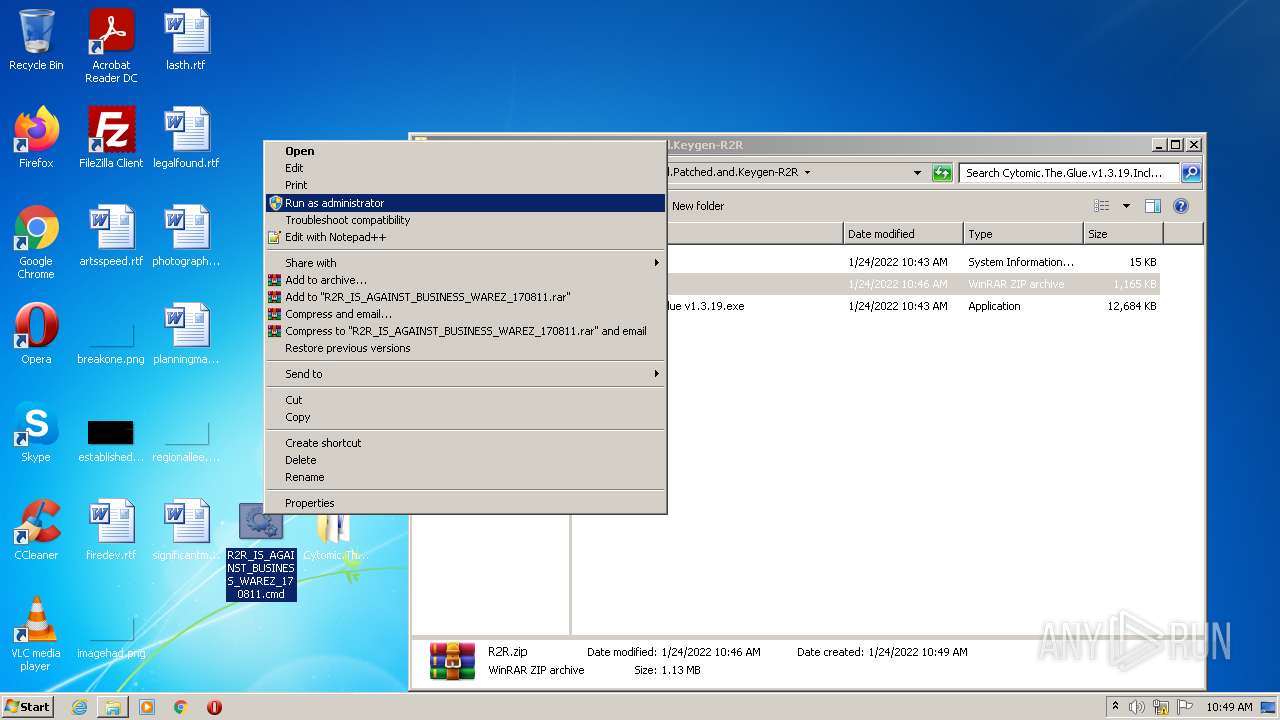
Manual execution by user
- cmd.exe (PID: 2328)
- WinRAR.exe (PID: 3768)
- cmd.exe (PID: 3276)
Reads CPU info
- openfiles.exe (PID: 1088)
- openfiles.exe (PID: 3204)
Reads the computer name
- openfiles.exe (PID: 3204)
Reads the hosts file
- cmd.exe (PID: 3276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
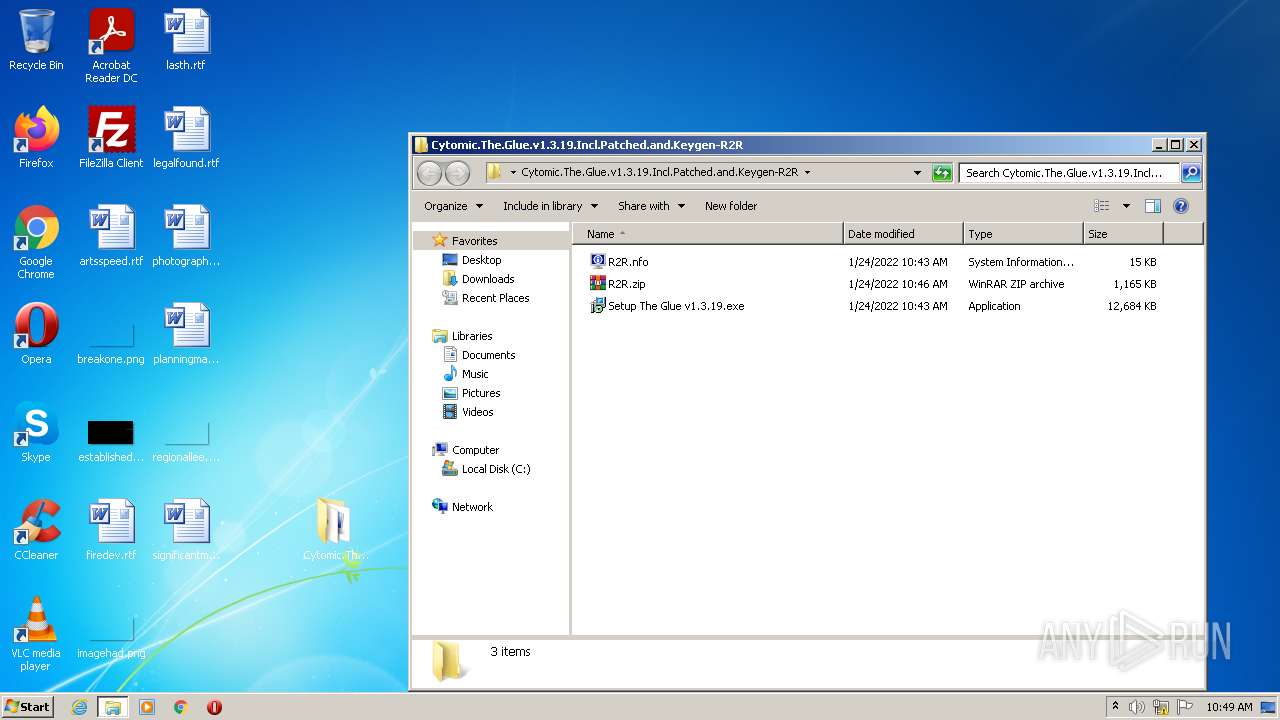
| ZipFileName: | Cytomic.The.Glue.v1.3.19.Incl.Patched.and.Keygen-R2R/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2022:01:24 07:46:28 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
48
Monitored processes
8
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
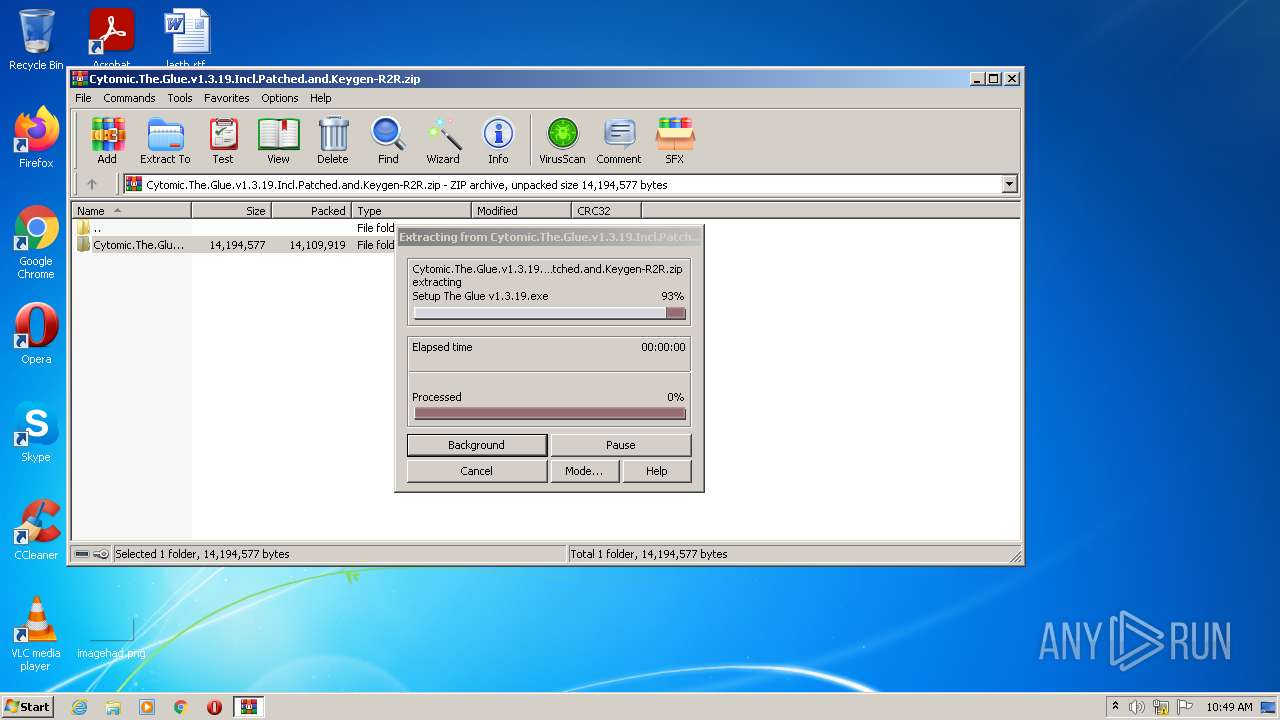
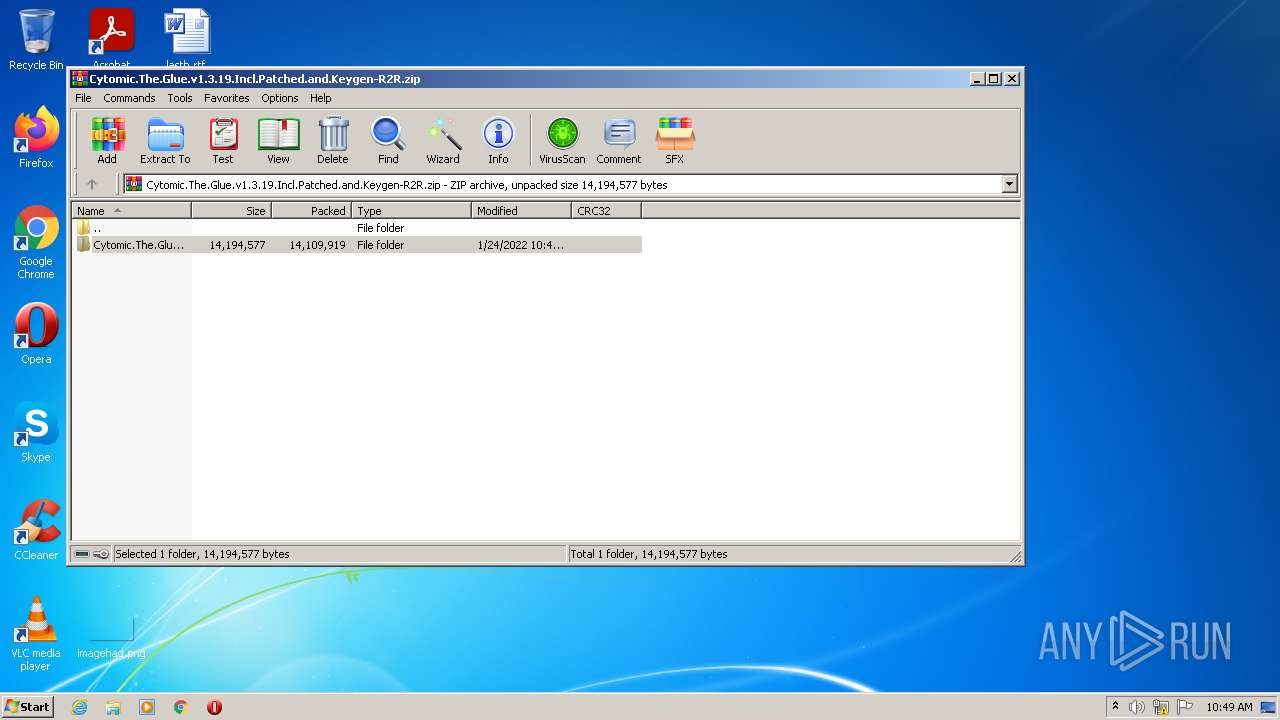
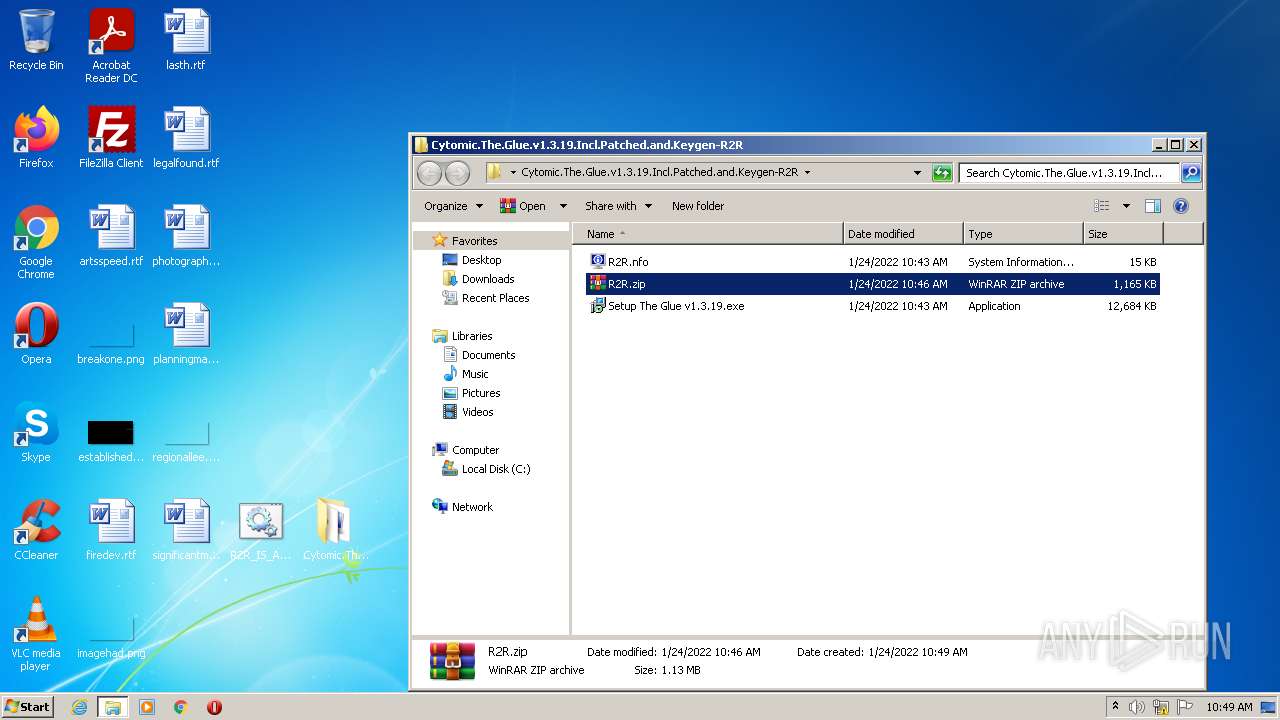
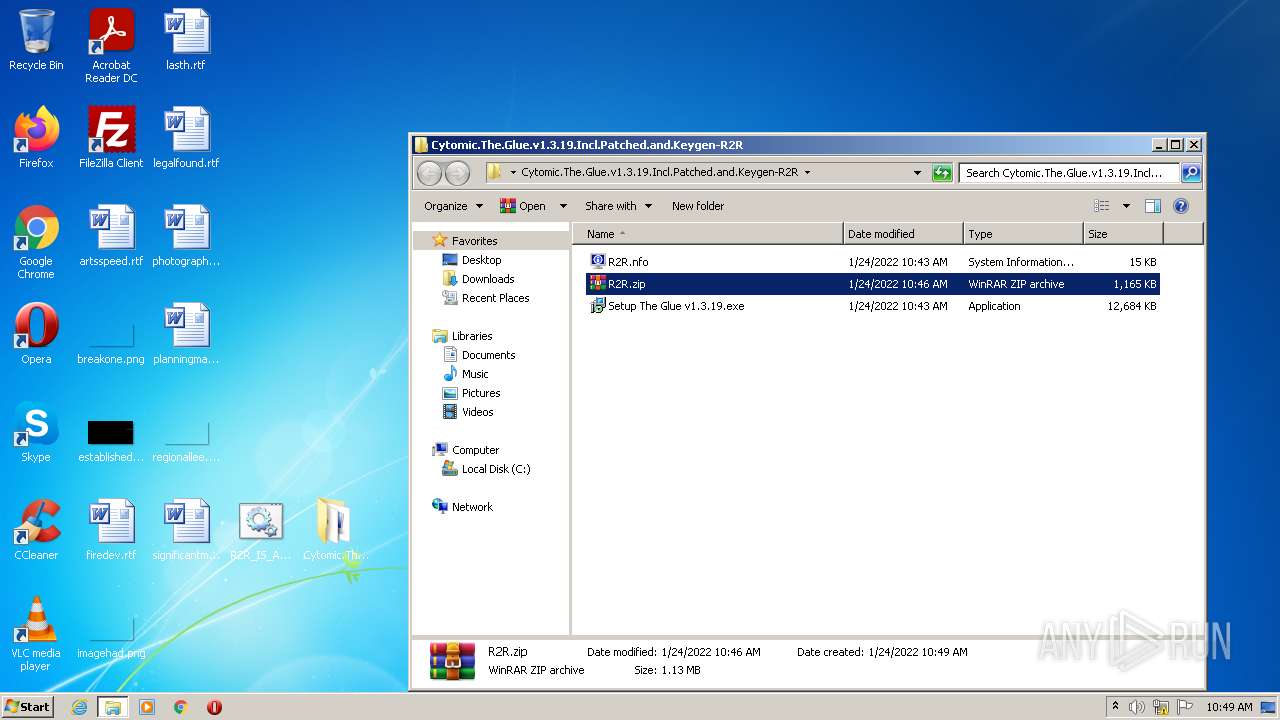
| 576 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Cytomic.The.Glue.v1.3.19.Incl.Patched.and.Keygen-R2R.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1088 | OPENFILES | C:\Windows\system32\openfiles.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Displays the current open files list Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
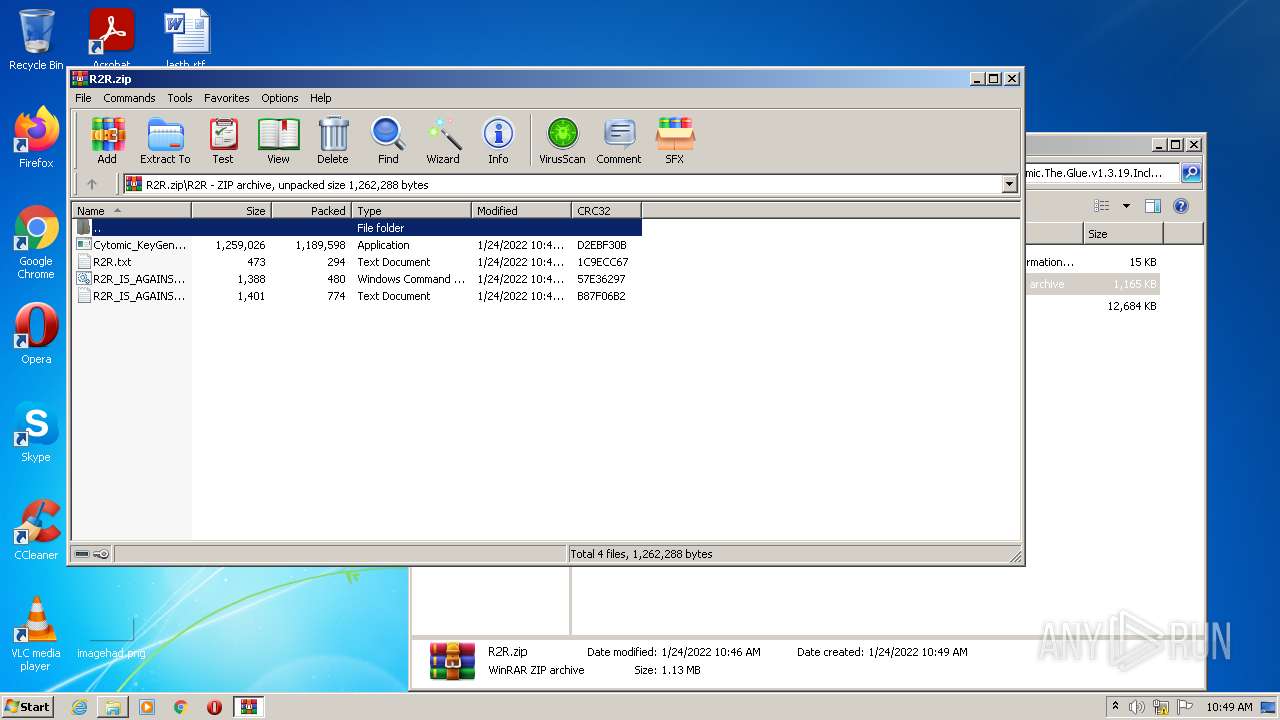
| 2328 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\R2R_IS_AGAINST_BUSINESS_WAREZ_170811.cmd" " | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3204 | OPENFILES | C:\Windows\system32\openfiles.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Displays the current open files list Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3276 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\Desktop\R2R_IS_AGAINST_BUSINESS_WAREZ_170811.cmd" | C:\Windows\System32\cmd.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
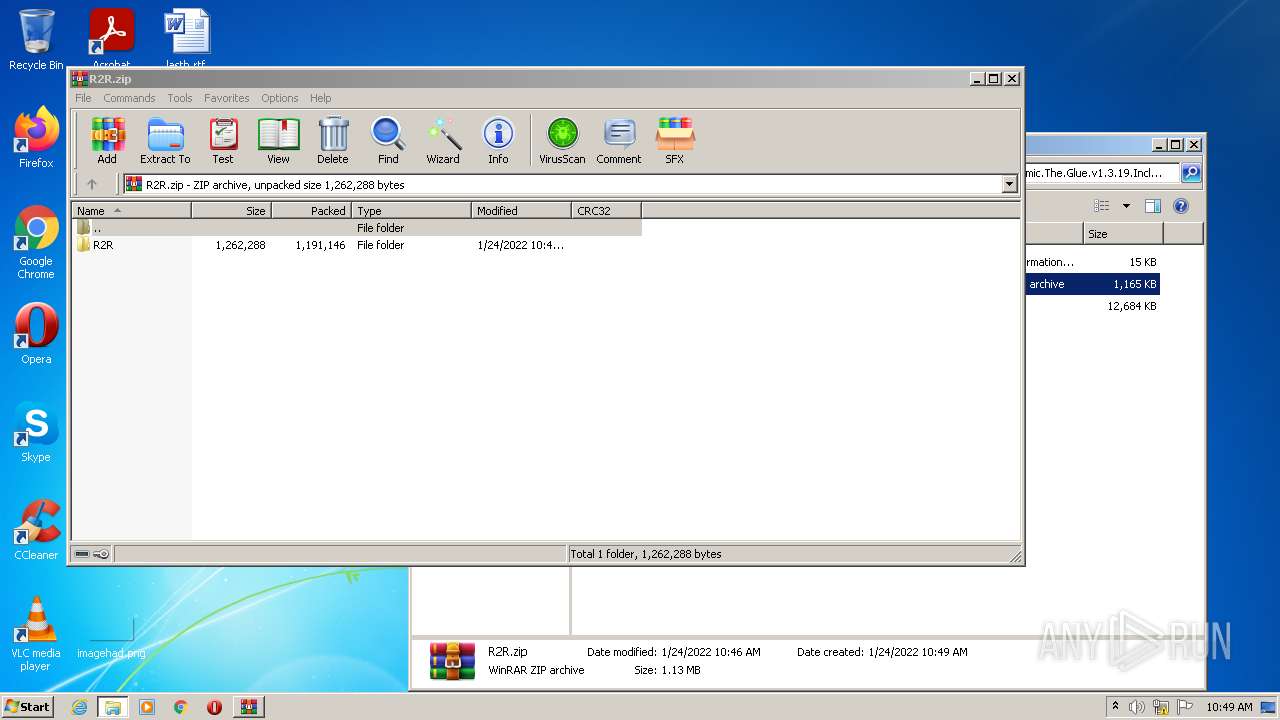
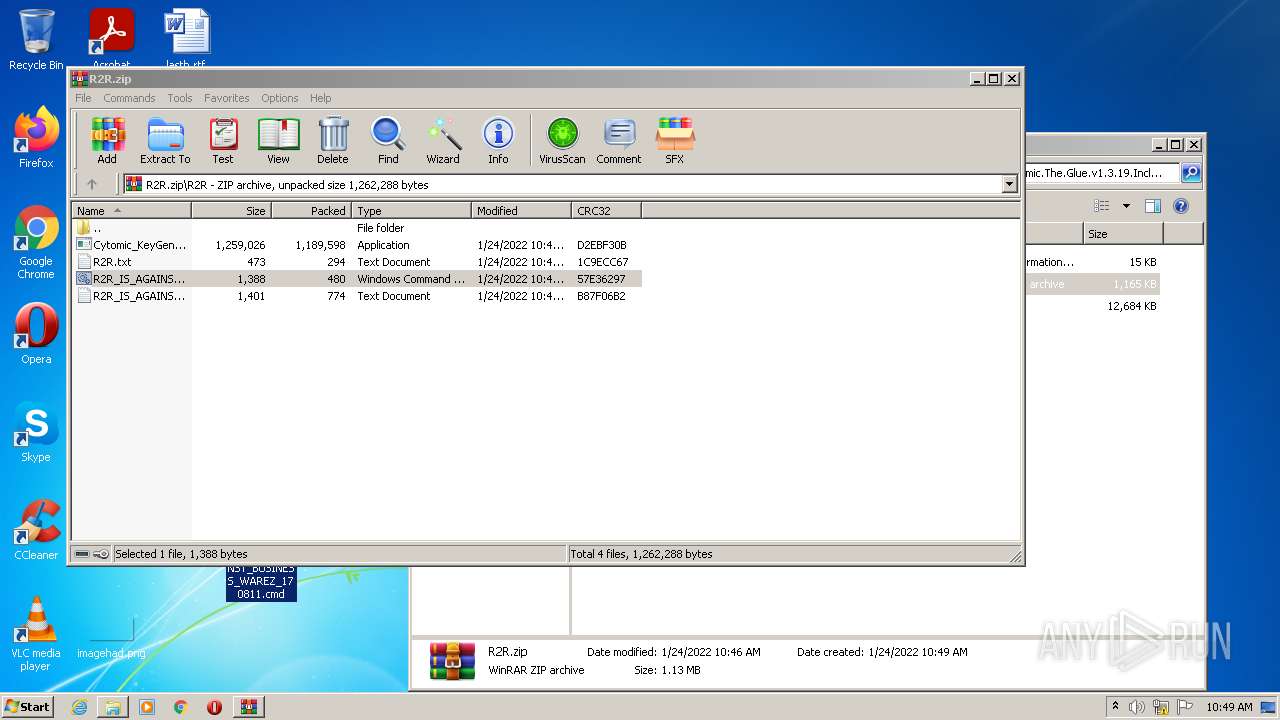
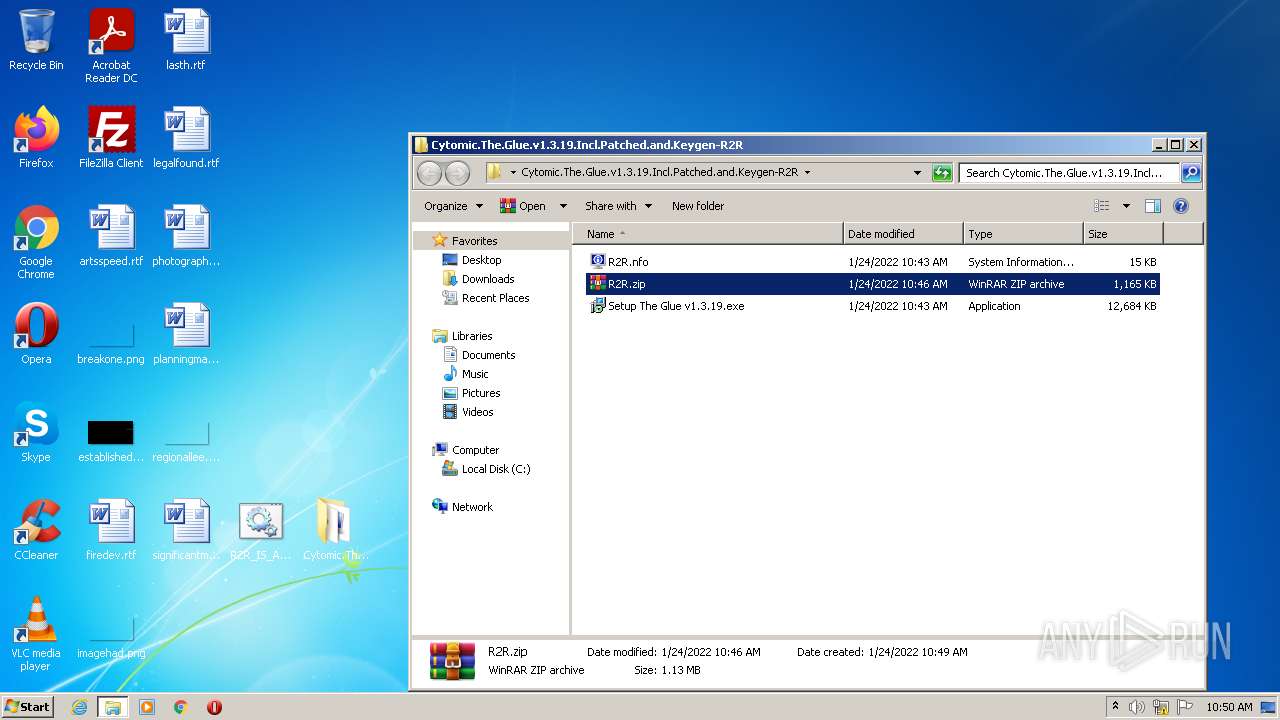
| 3768 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Cytomic.The.Glue.v1.3.19.Incl.Patched.and.Keygen-R2R\R2R.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3924 | FIND /C /I "127.0.0.1 www.elephantafiles.com" "C:\Windows\system32\drivers\etc\hosts" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4040 | FIND /C /I "127.0.0.1 www.r2rdownload.com" "C:\Windows\system32\drivers\etc\hosts" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 864
Read events
1 818
Write events
46
Delete events
0
Modification events
| (PID) Process: | (576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (576) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Cytomic.The.Glue.v1.3.19.Incl.Patched.and.Keygen-R2R.zip | |||
| (PID) Process: | (576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa576.3898\Cytomic.The.Glue.v1.3.19.Incl.Patched.and.Keygen-R2R\Setup The Glue v1.3.19.exe | executable | |
MD5:— | SHA256:— | |||
| 576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa576.3898\Cytomic.The.Glue.v1.3.19.Incl.Patched.and.Keygen-R2R\R2R.nfo | text | |
MD5:— | SHA256:— | |||
| 3276 | cmd.exe | C:\Windows\system32\drivers\etc\hosts | text | |
MD5:— | SHA256:— | |||
| 3768 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3768.4824\R2R\R2R_IS_AGAINST_BUSINESS_WAREZ_170811.cmd | text | |
MD5:3DB6F1C259A0AA6971FF535B67385794 | SHA256:CDAED74DE125FC29FD3BDD7F550DF7DAB6121494C905D827D1432A6D7855426D | |||
| 576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa576.3898\Cytomic.The.Glue.v1.3.19.Incl.Patched.and.Keygen-R2R\R2R.zip | compressed | |
MD5:37F19B918B86AA704A391D0C1A9F2125 | SHA256:24FD8F01E8B38CB2746EDCED17D3BF5C5309DDBE0EFB675631093ECEEEEE22B6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report