| File name: | Xeno.exe |
| Full analysis: | https://app.any.run/tasks/729111b8-ecfd-40ea-8ee2-e32570ed38fb |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | May 25, 2025, 02:23:21 |
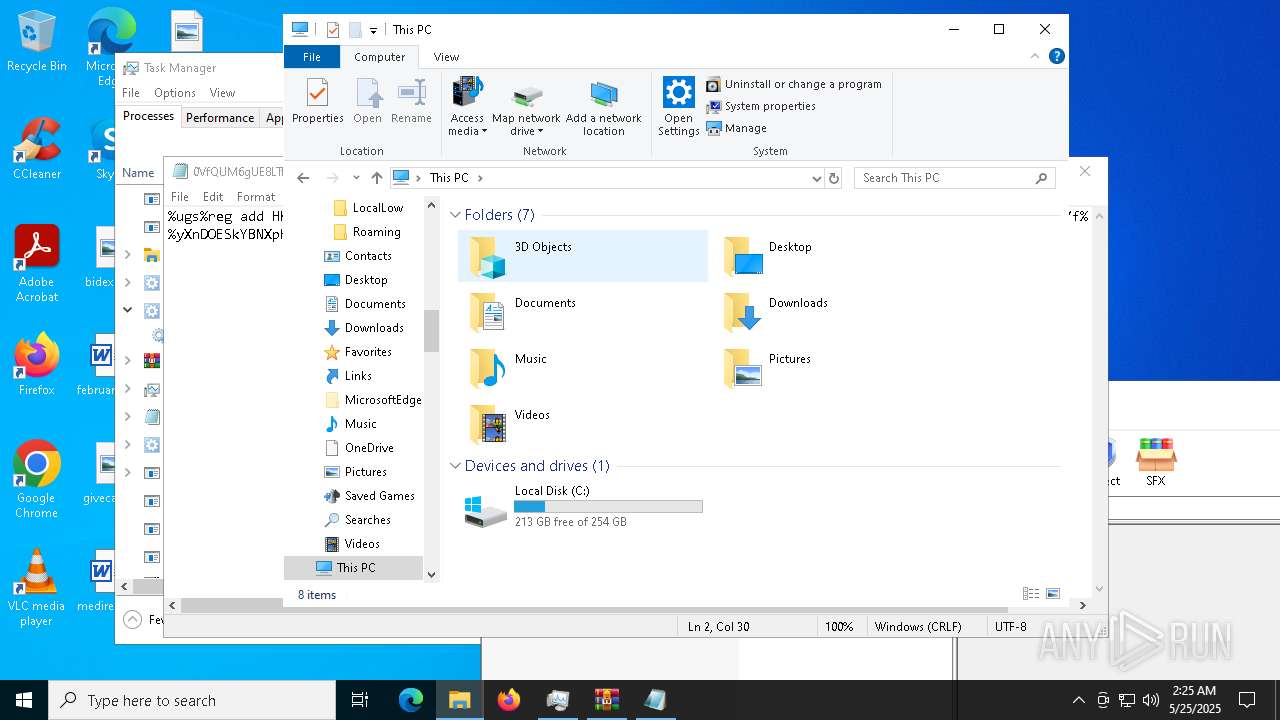
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 6F2C998C60A662361C52B5AAC308DBCF |
| SHA1: | 2EA662E7306F5DADC507F7E70BB0017AEA904A0E |
| SHA256: | 01D051294C52CEEE92BC40026C9F8C8D076F3B128BD7DA809BD8ED257FEF0EEA |
| SSDEEP: | 98304:MmgwMyDhnqxL/xYxpPMonmt2qzPOPsxbwp1n/DtMEWQXUykaSLw2BRyjUipTMEjz:/hrzdjRV8wo2s7U7deG/cUpPTRcd4 |
MALICIOUS
Executing a file with an untrusted certificate
- SetTimerResolutionService.exe (PID: 6816)
- SetTimerResolutionService.exe (PID: 2892)
- updater.exe (PID: 10168)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 2740)
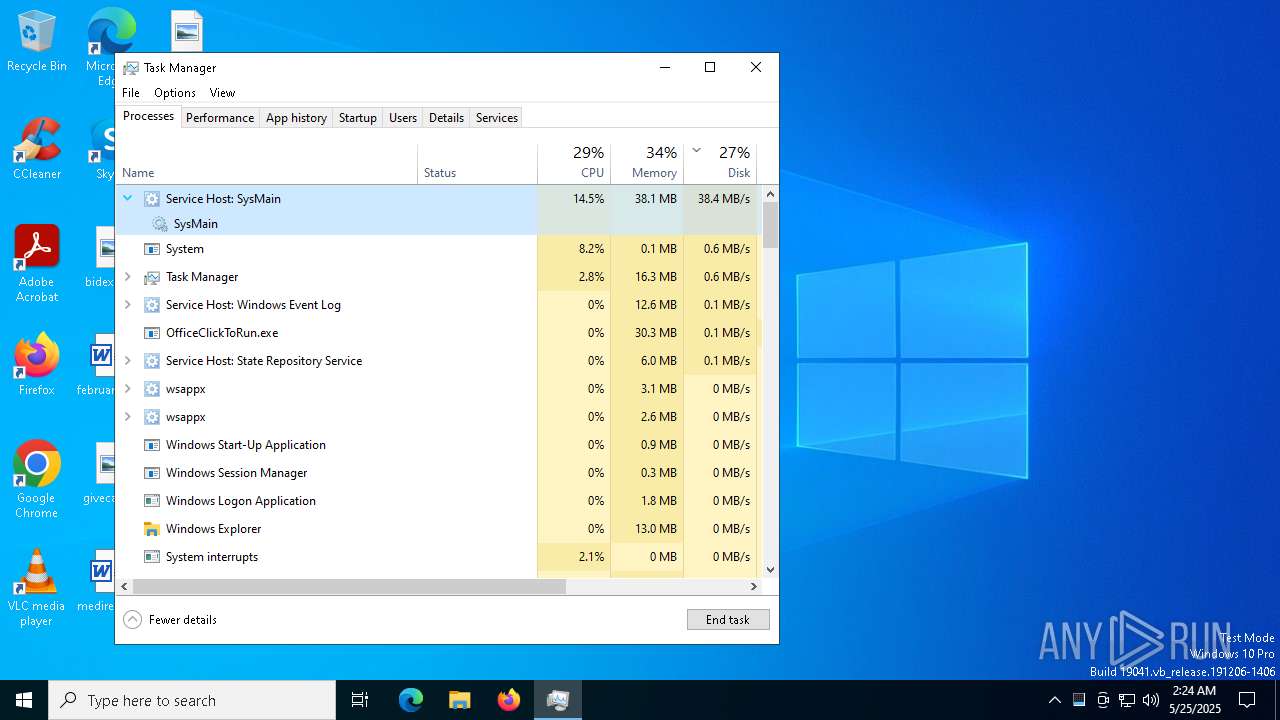
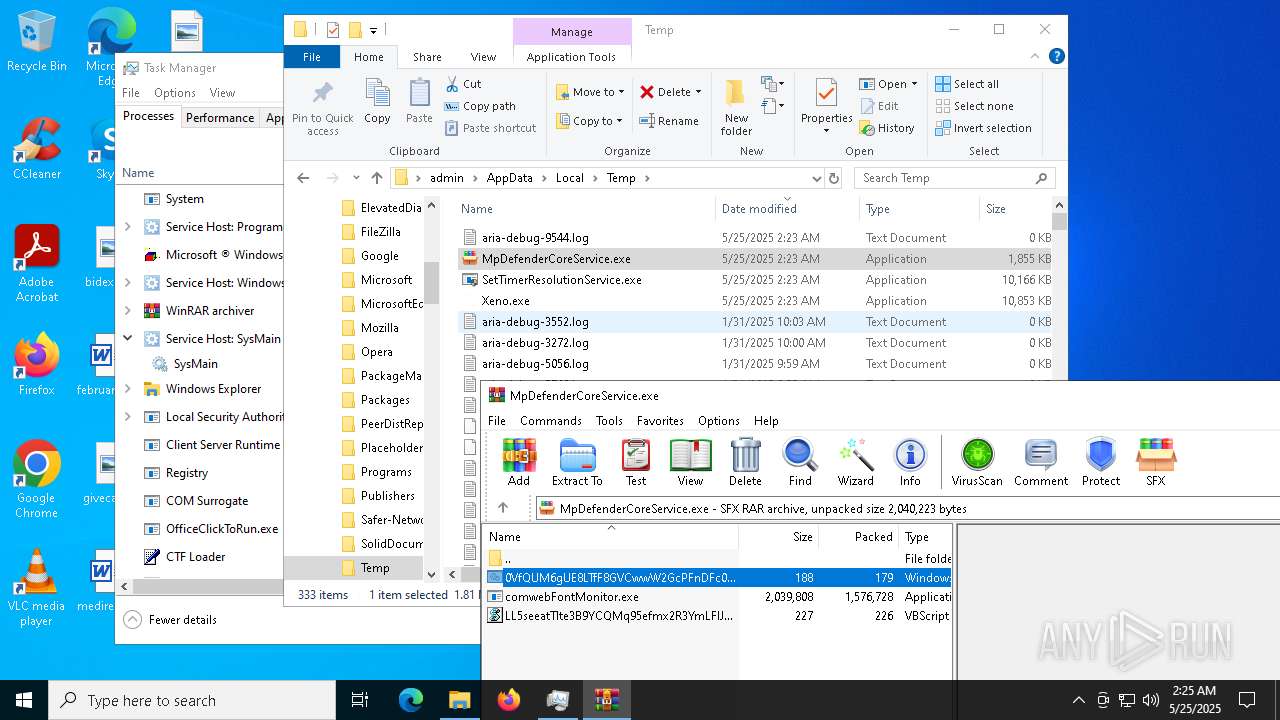
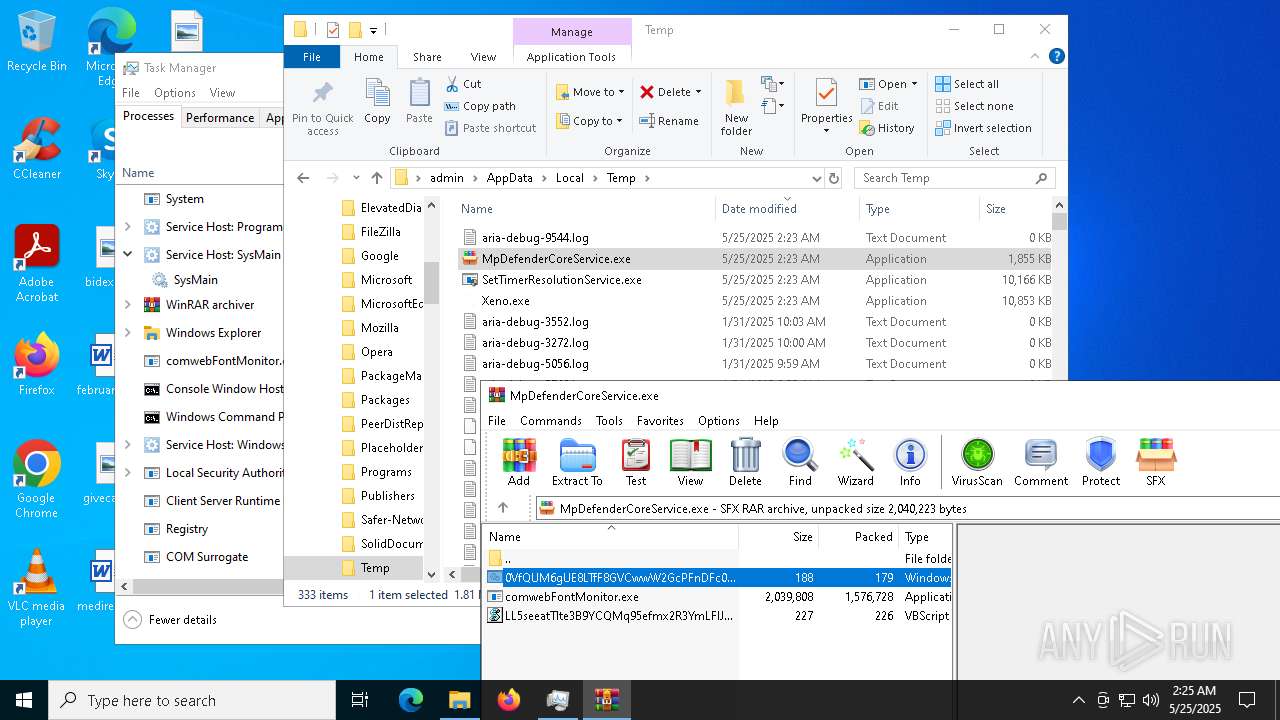
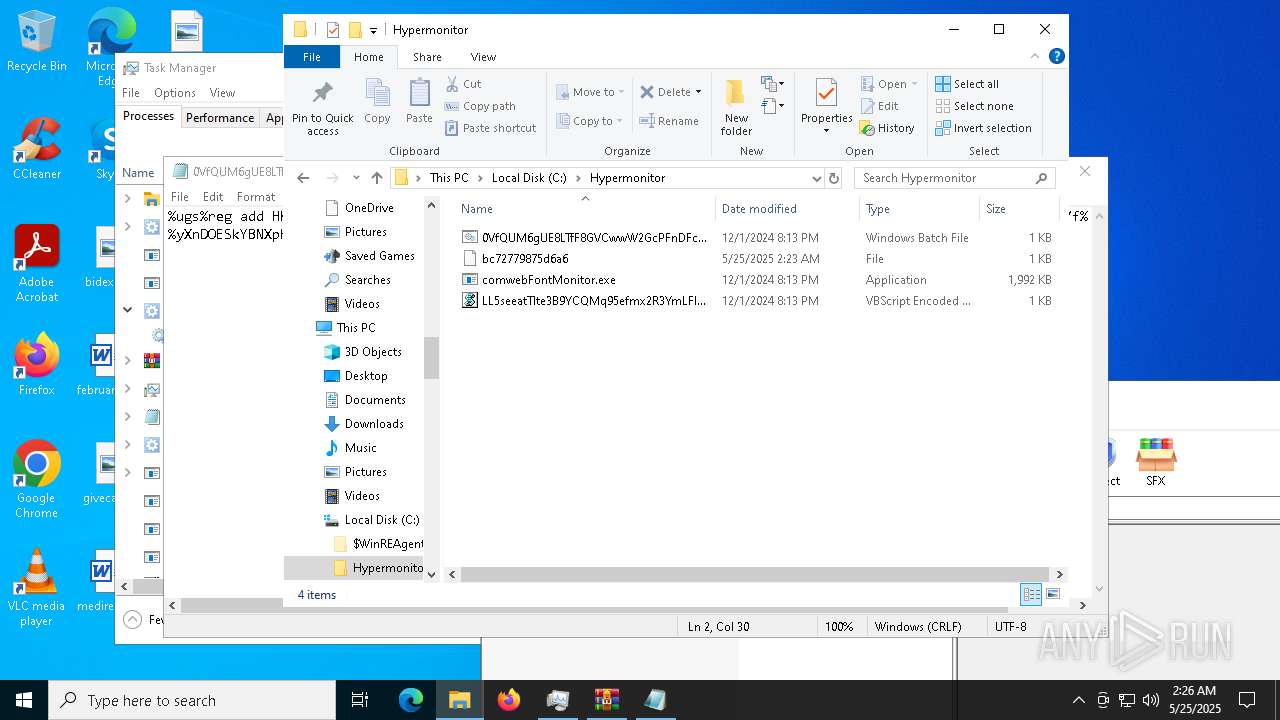
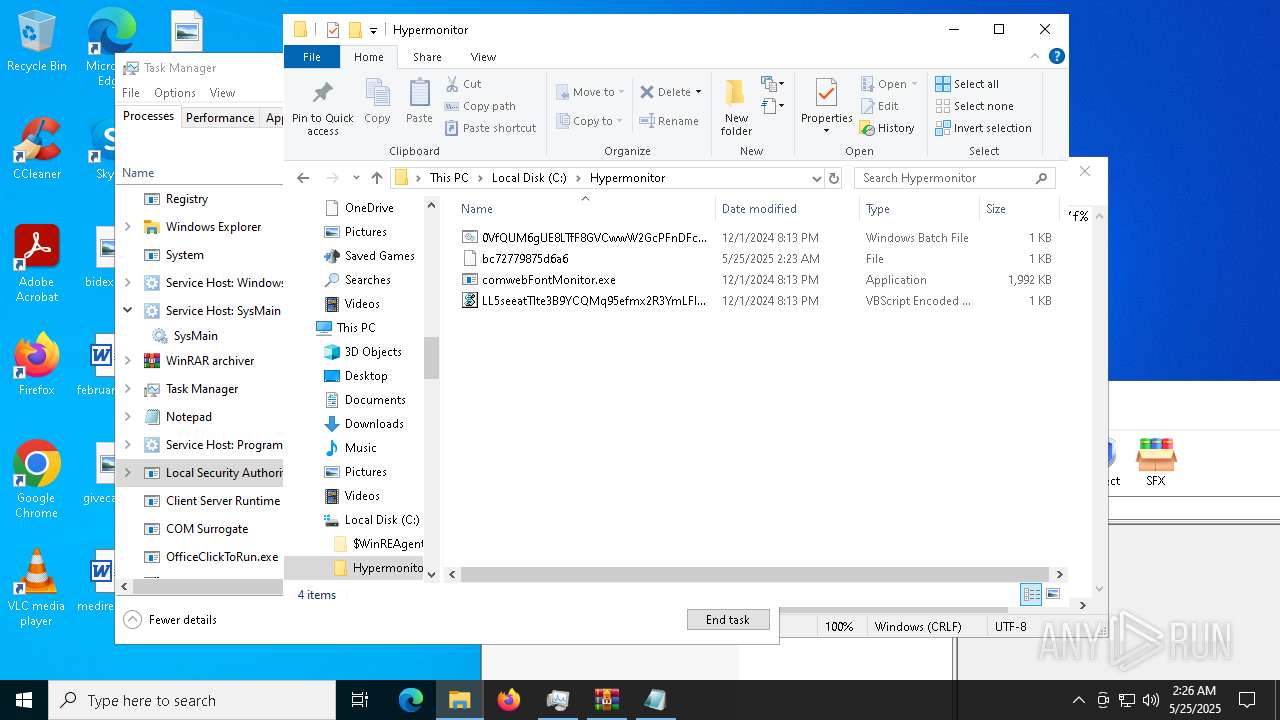
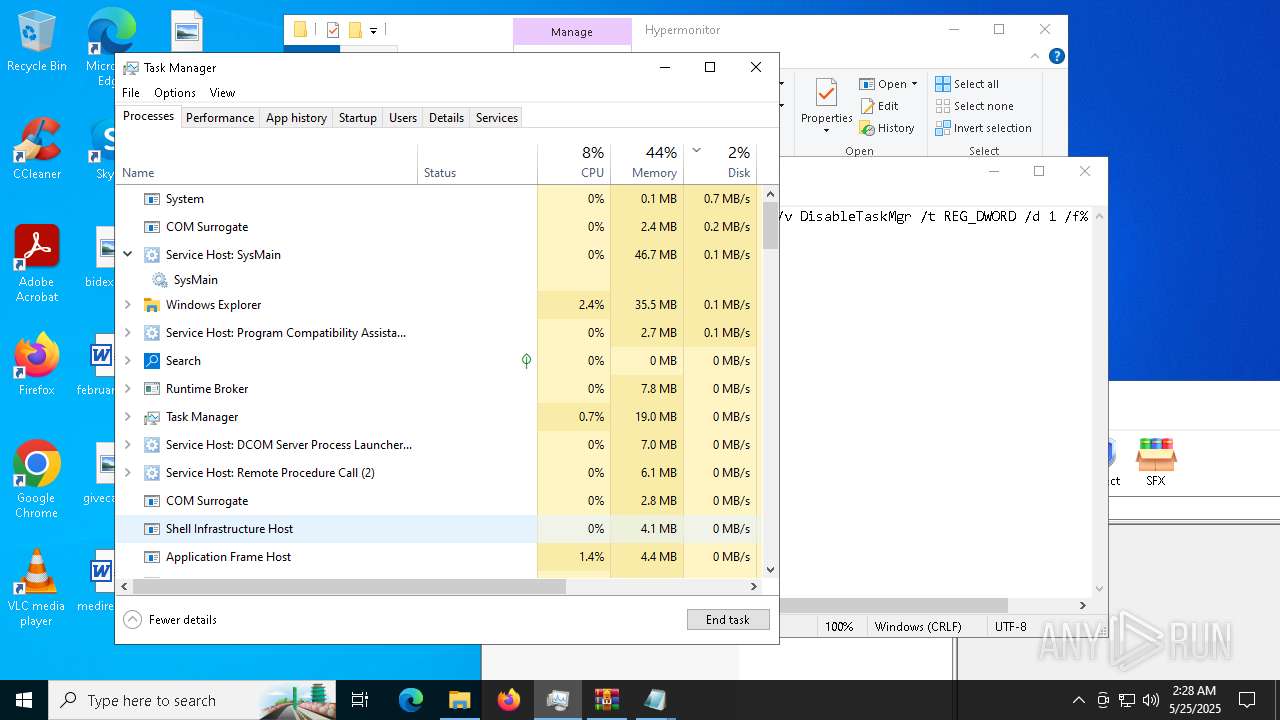
DCRAT mutex has been found
- comwebFontMonitor.exe (PID: 1696)
- comwebFontMonitor.exe (PID: 5416)
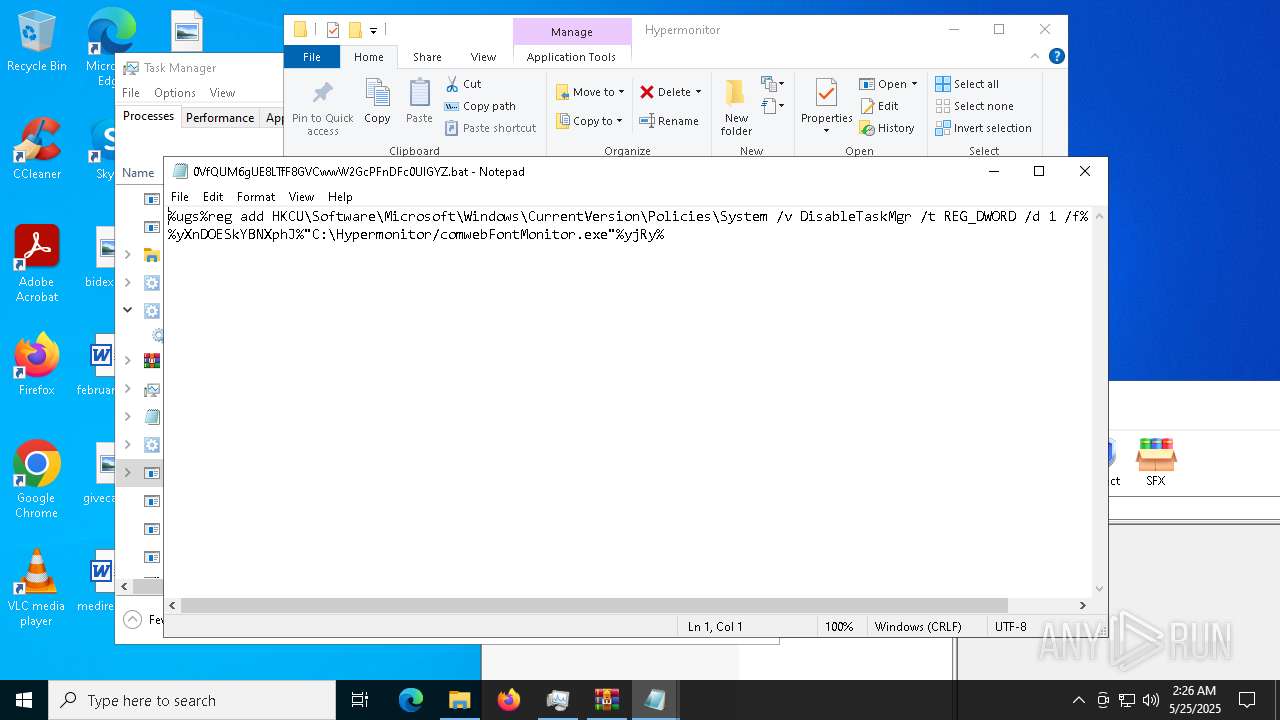
Changes the autorun value in the registry
- comwebFontMonitor.exe (PID: 5416)
Changes the login/logoff helper path in the registry
- comwebFontMonitor.exe (PID: 5416)
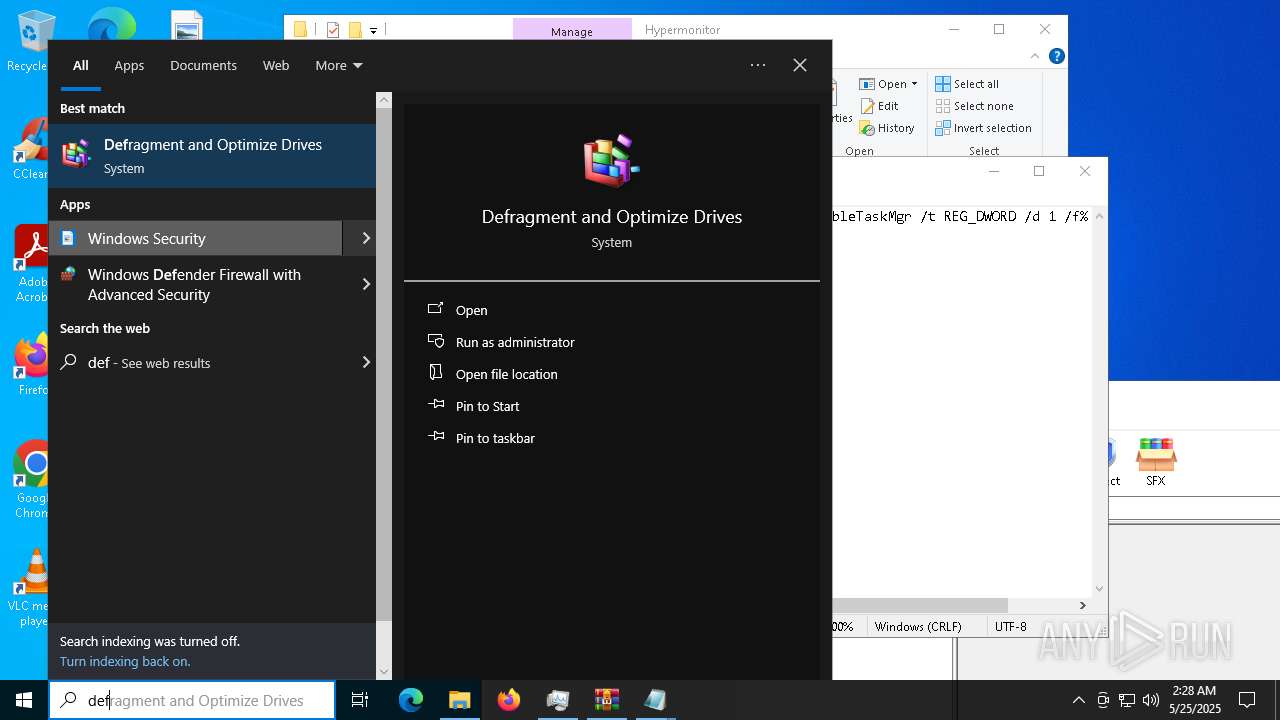
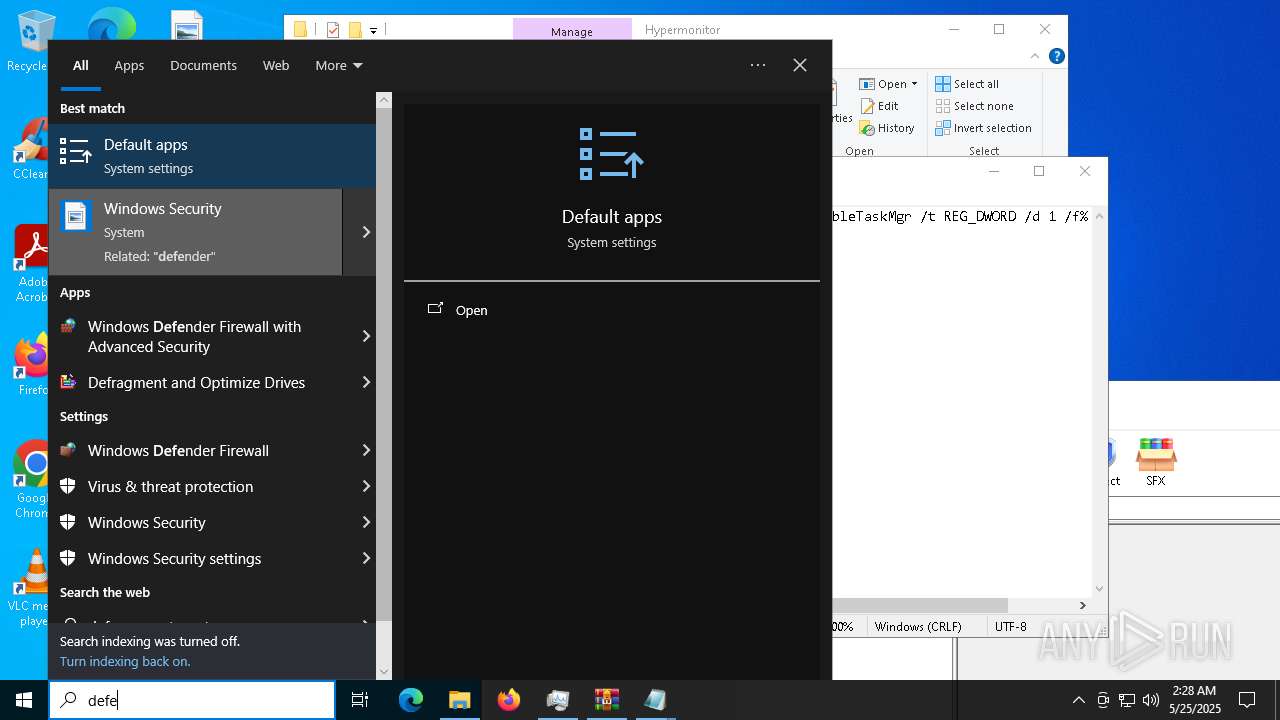
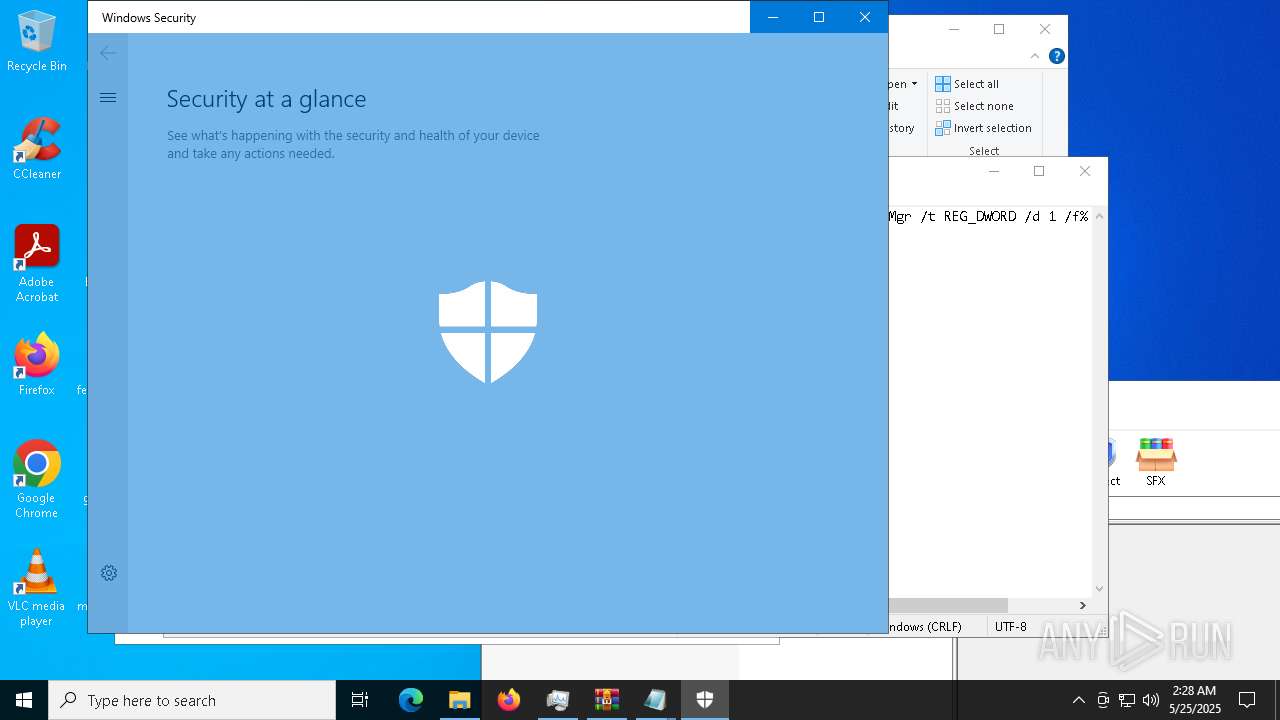
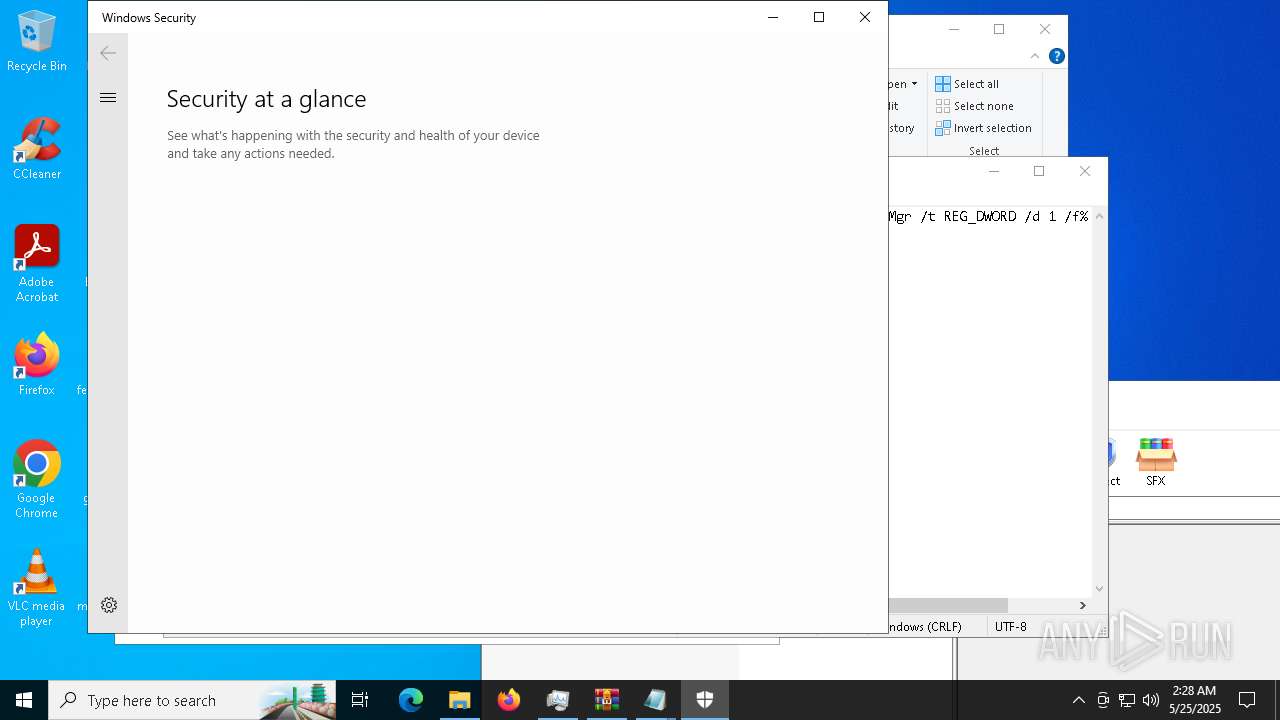
Changes Windows Defender settings
- comwebFontMonitor.exe (PID: 5416)
Adds path to the Windows Defender exclusion list
- comwebFontMonitor.exe (PID: 5416)
Vulnerable driver has been detected
- updater.exe (PID: 10168)
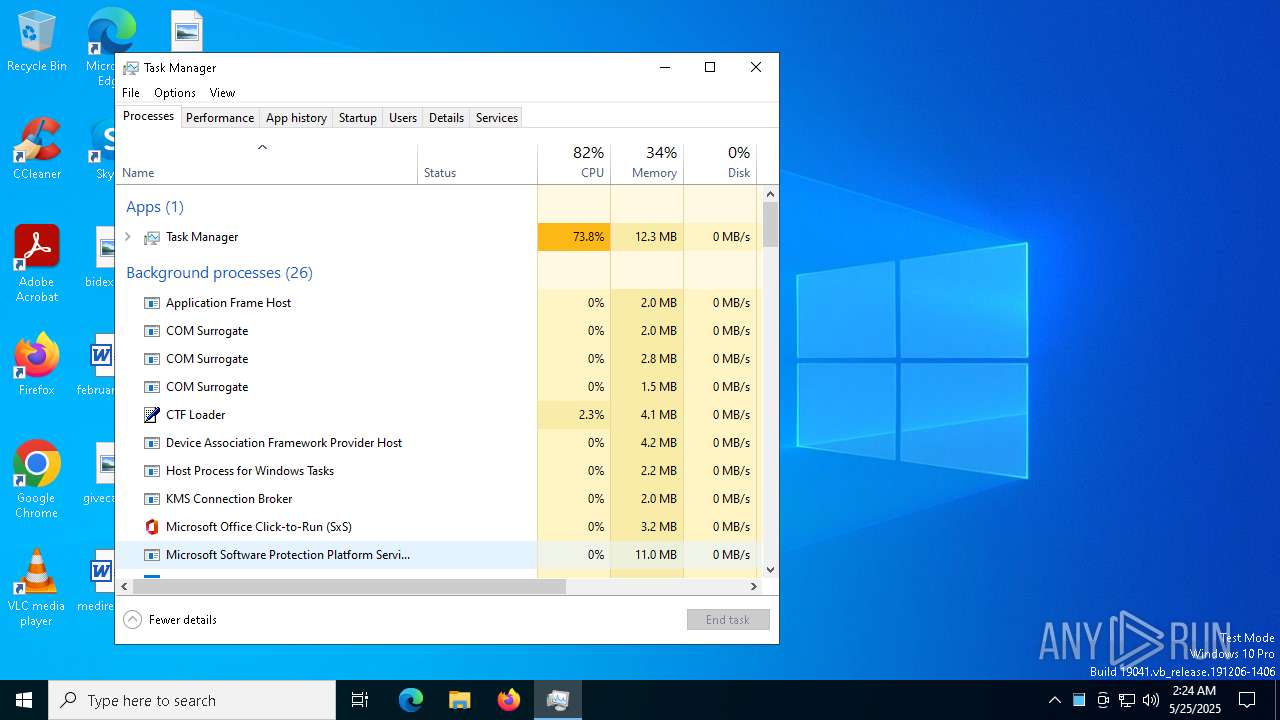
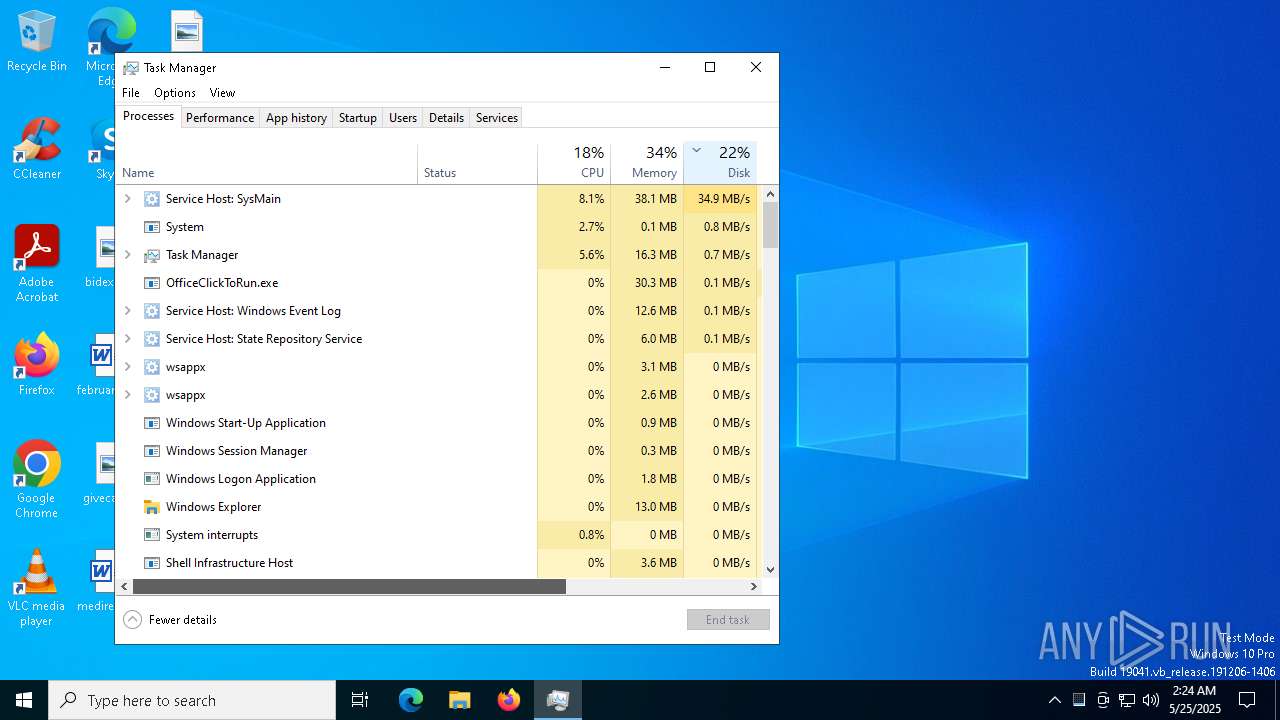
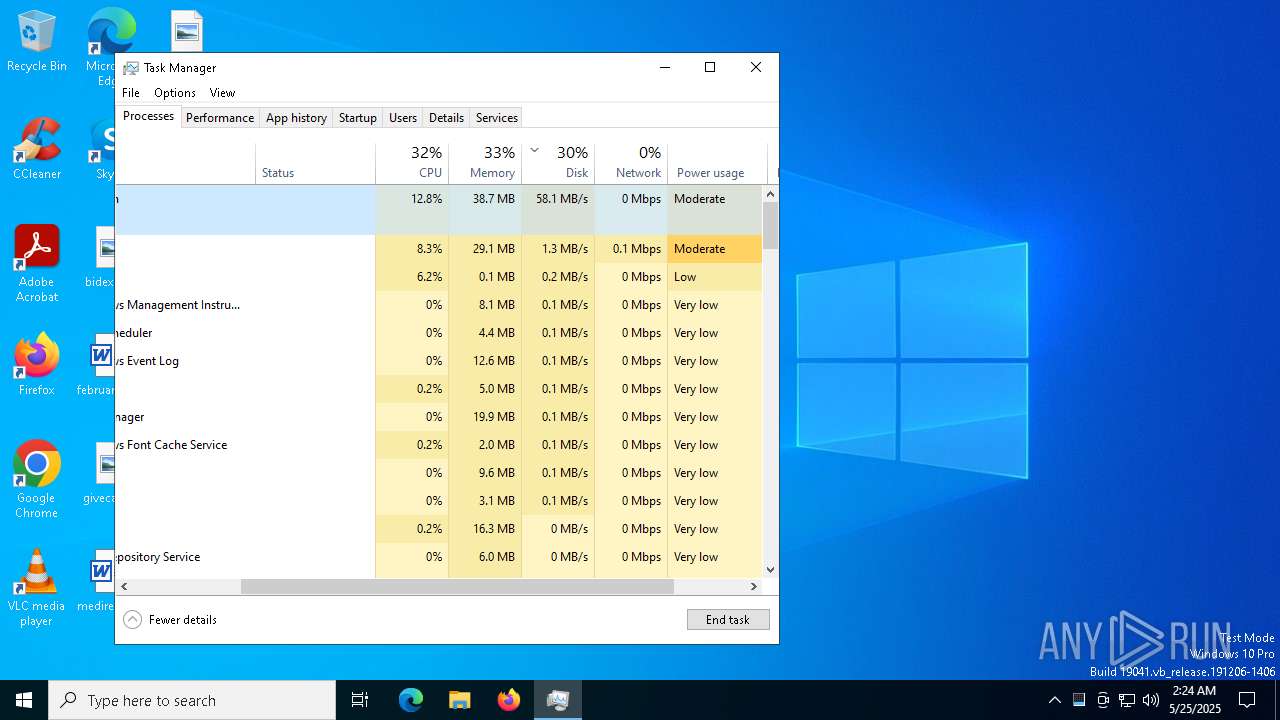
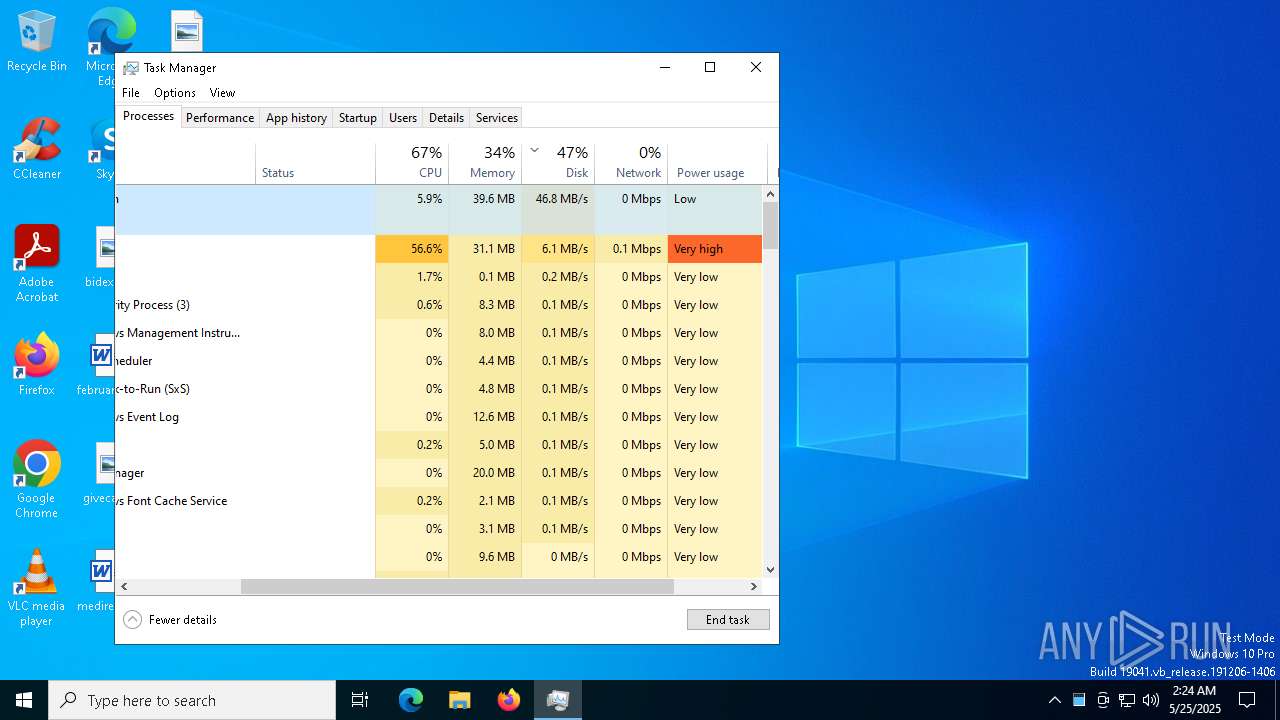
MINER has been detected (SURICATA)
- svchost.exe (PID: 2196)
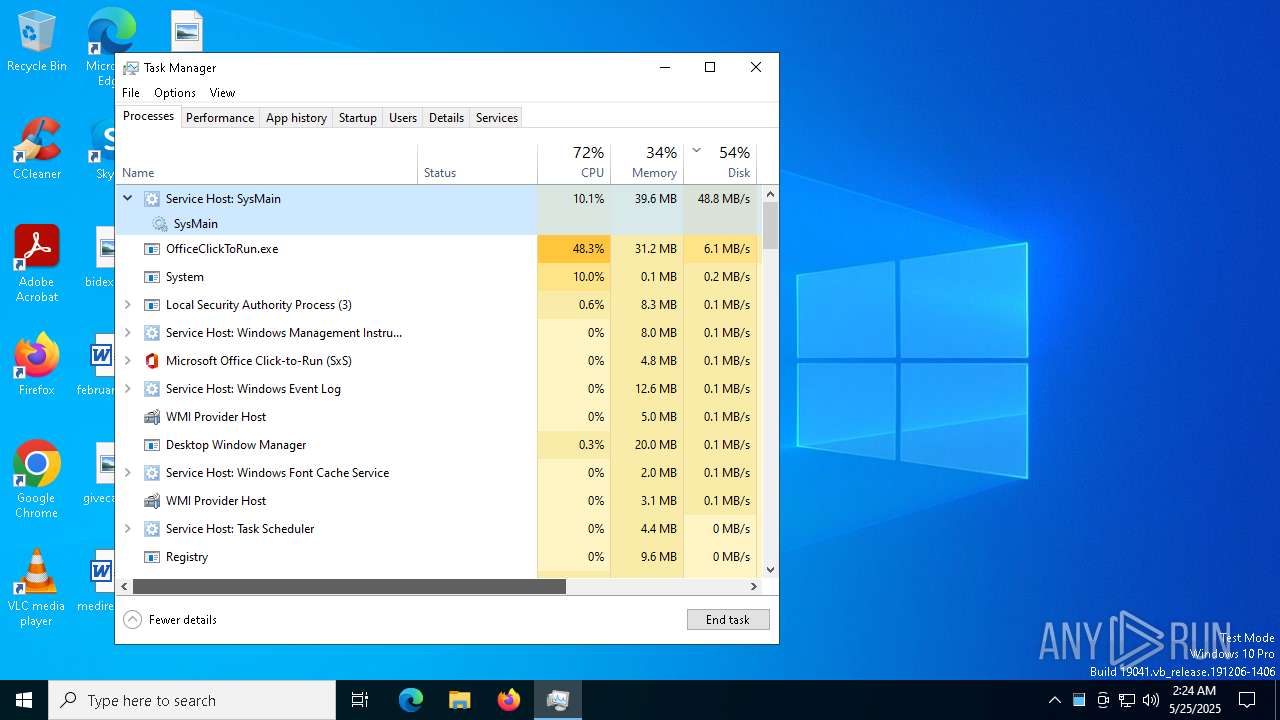
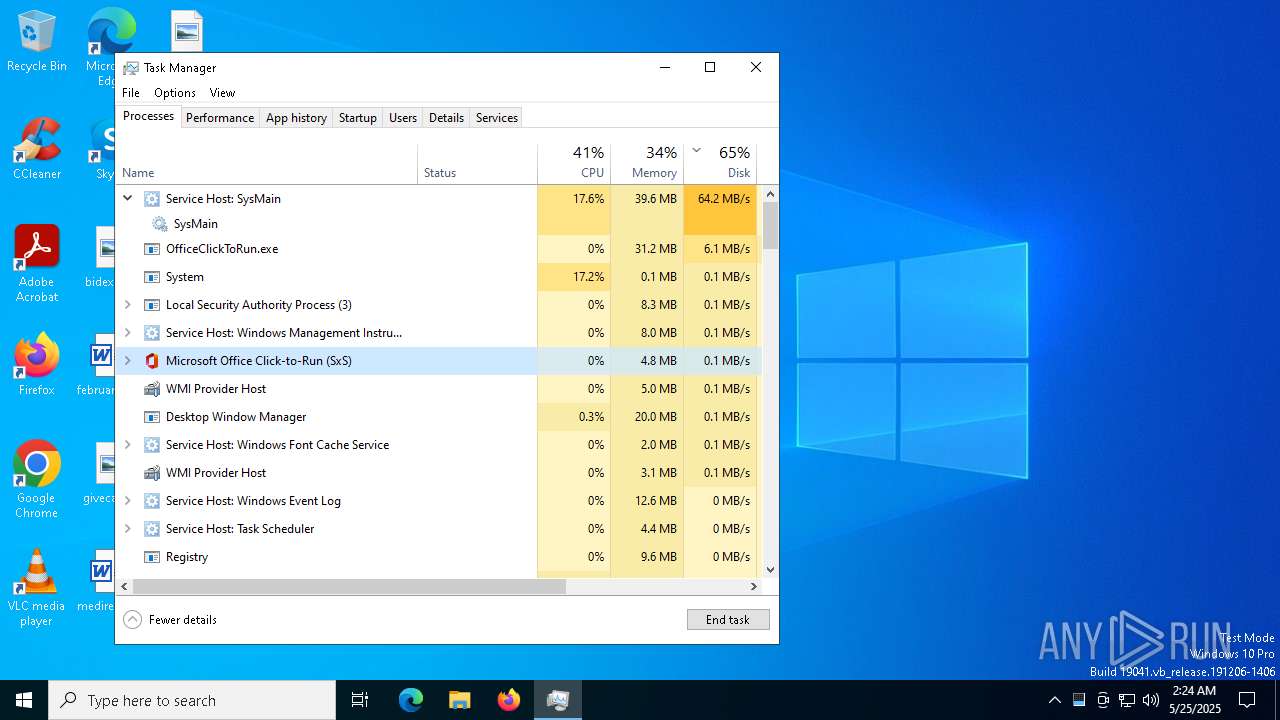
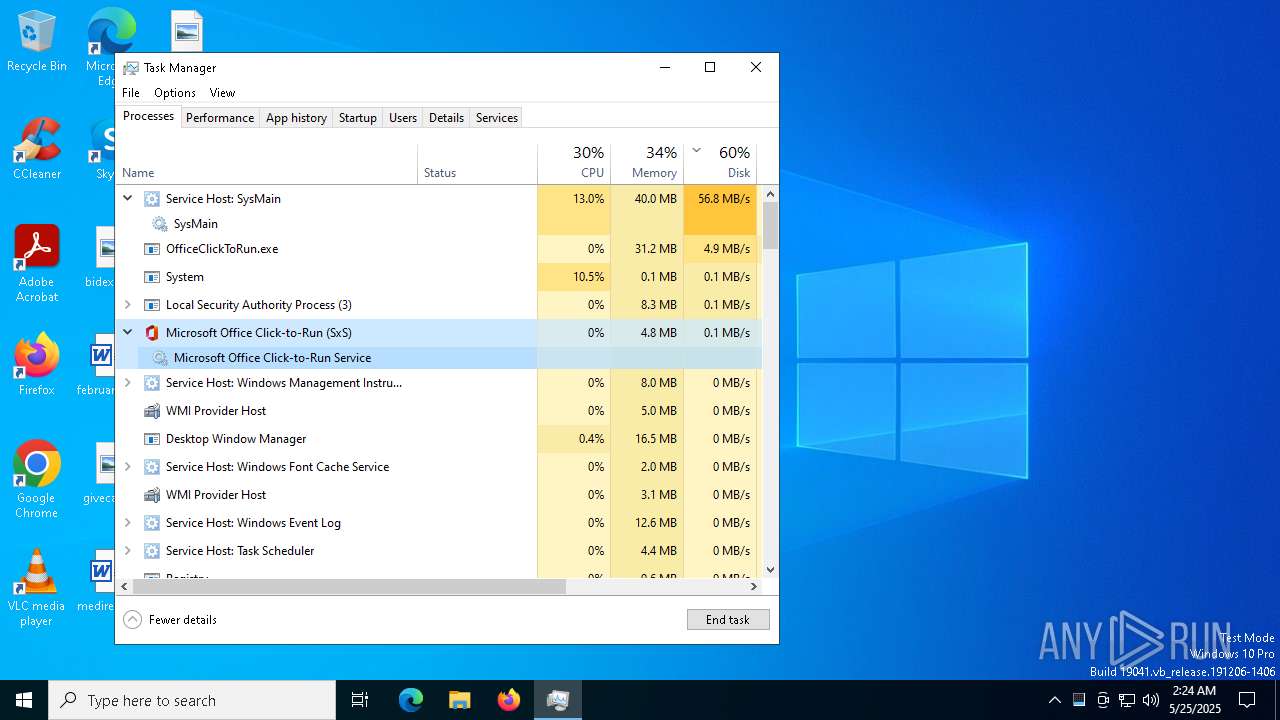
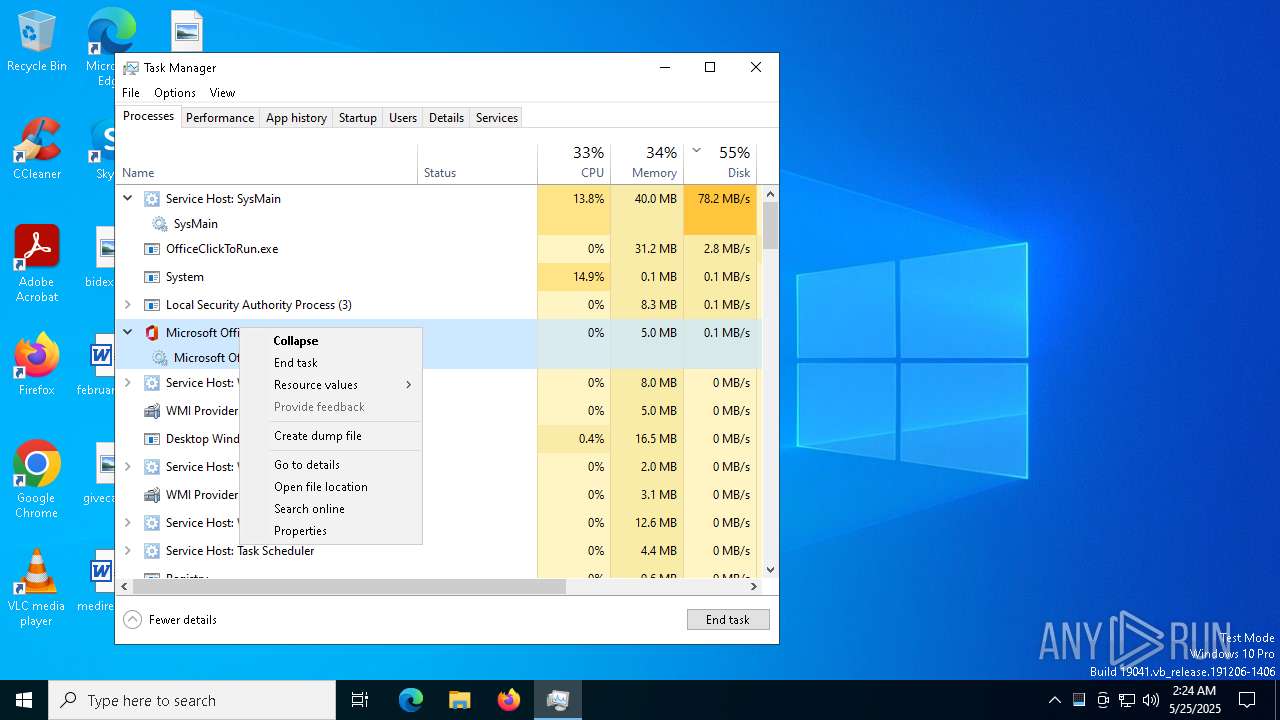
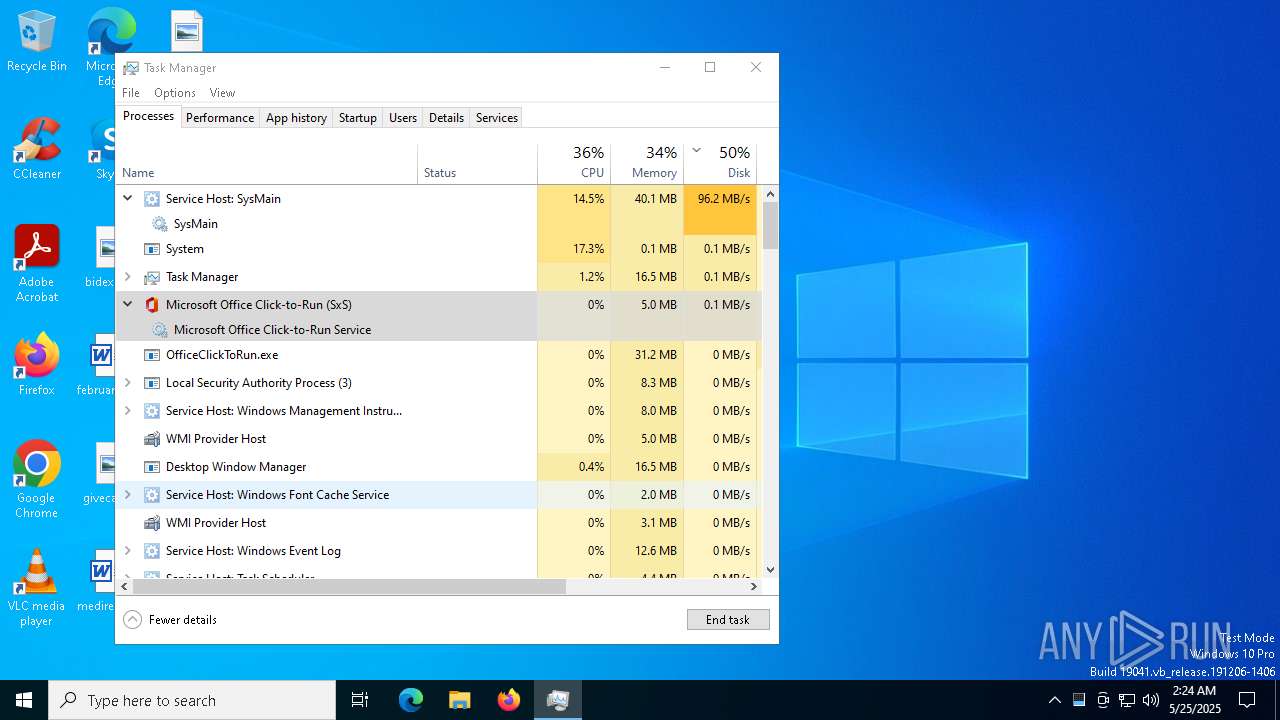
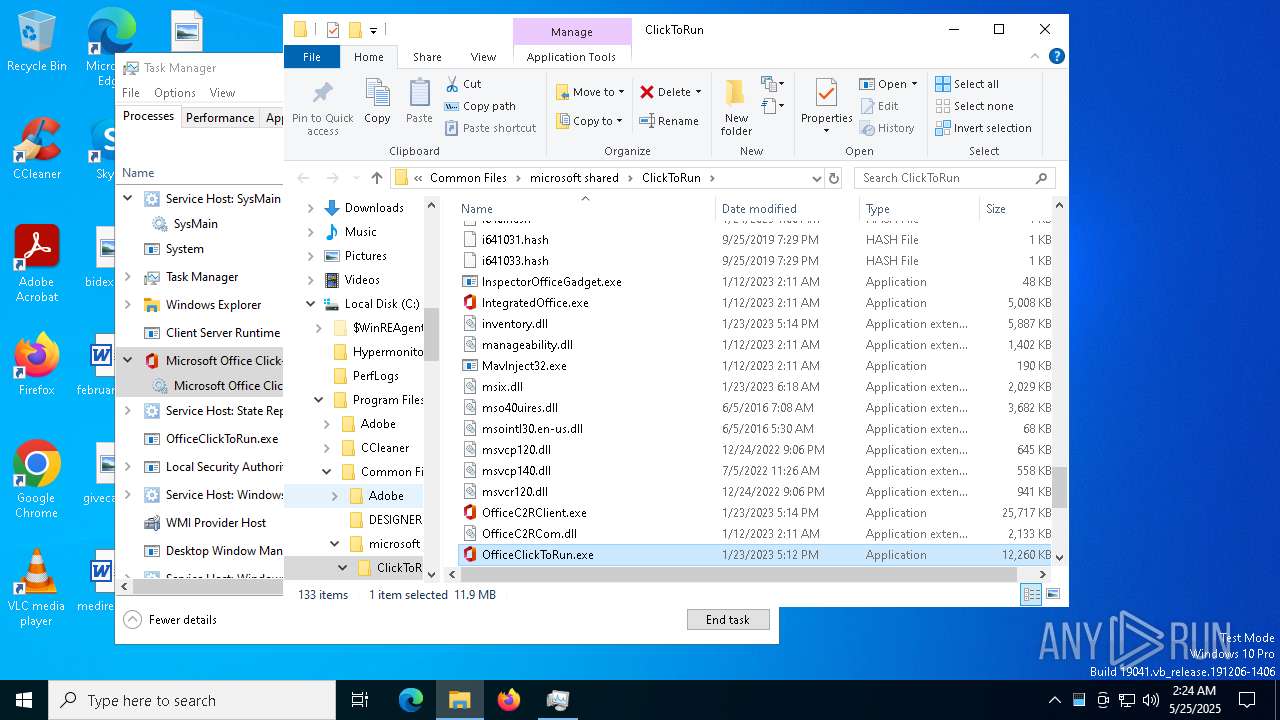
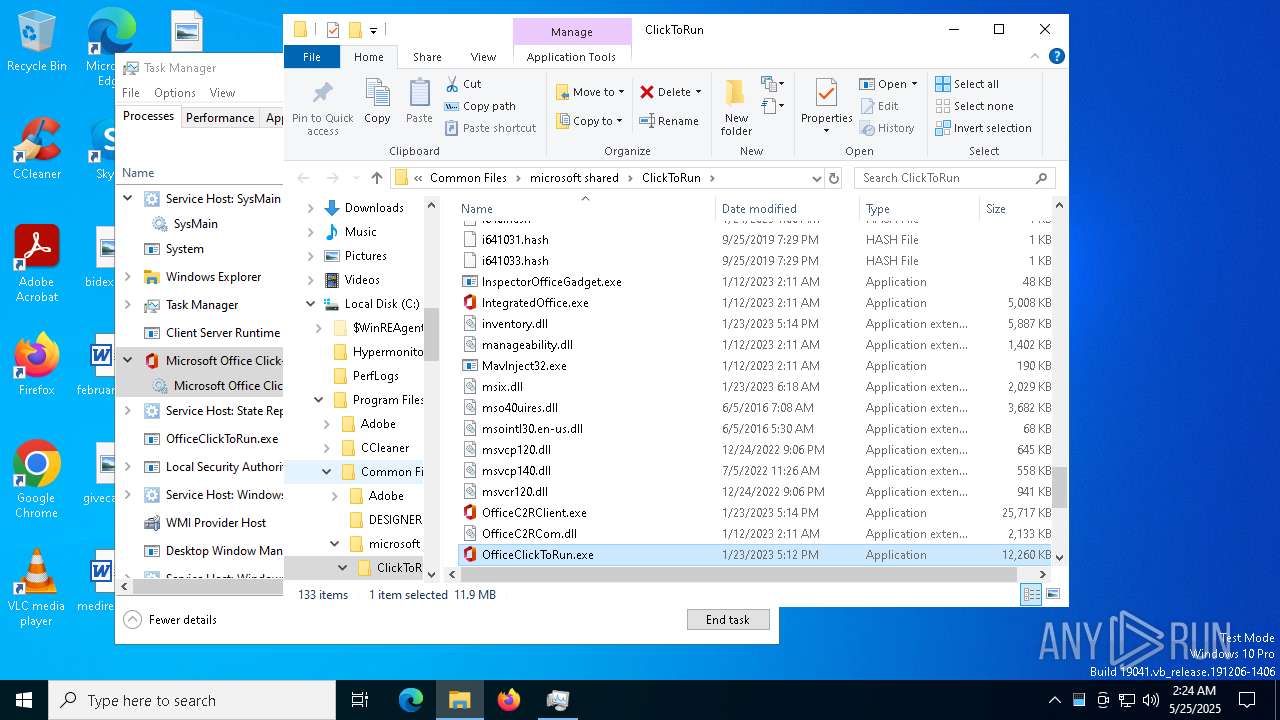
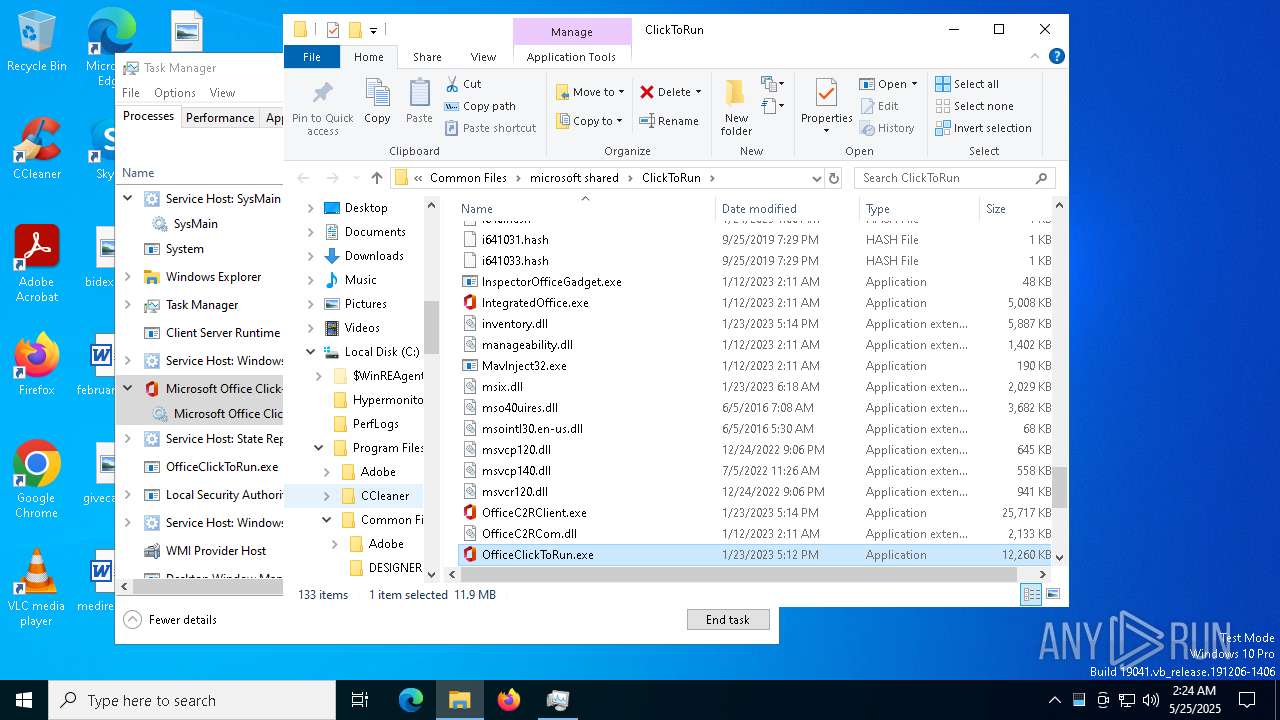
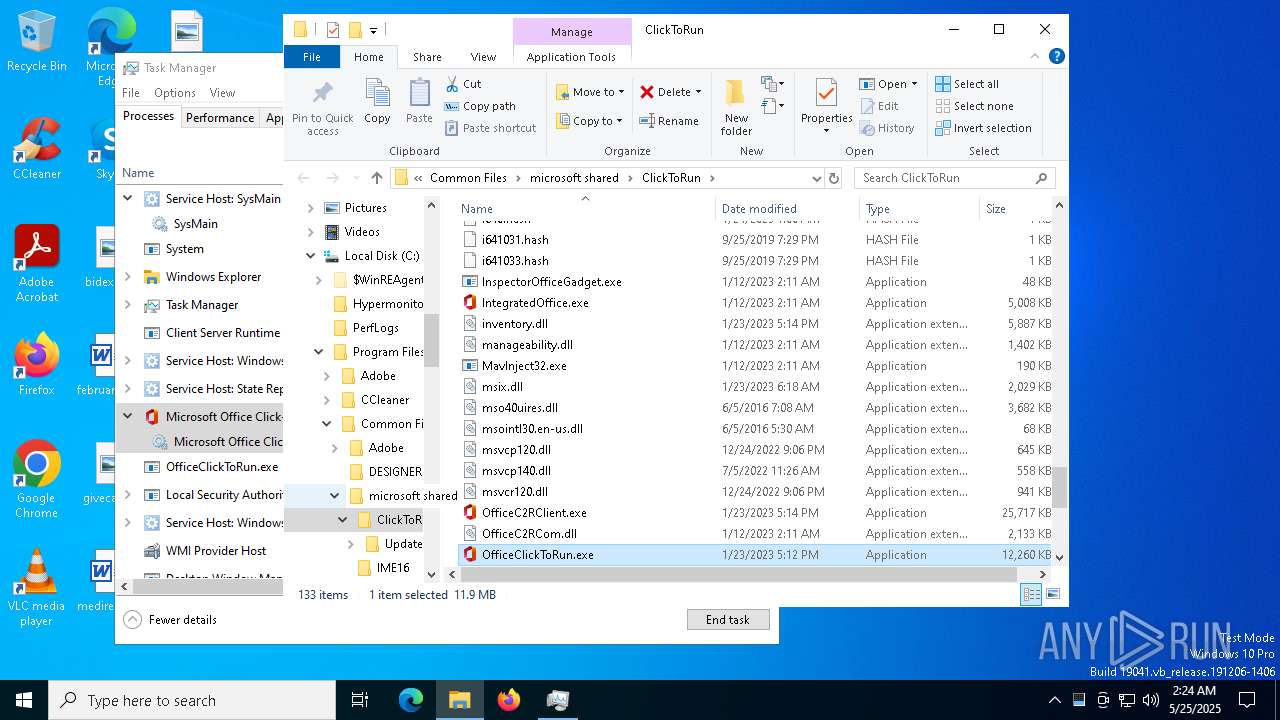
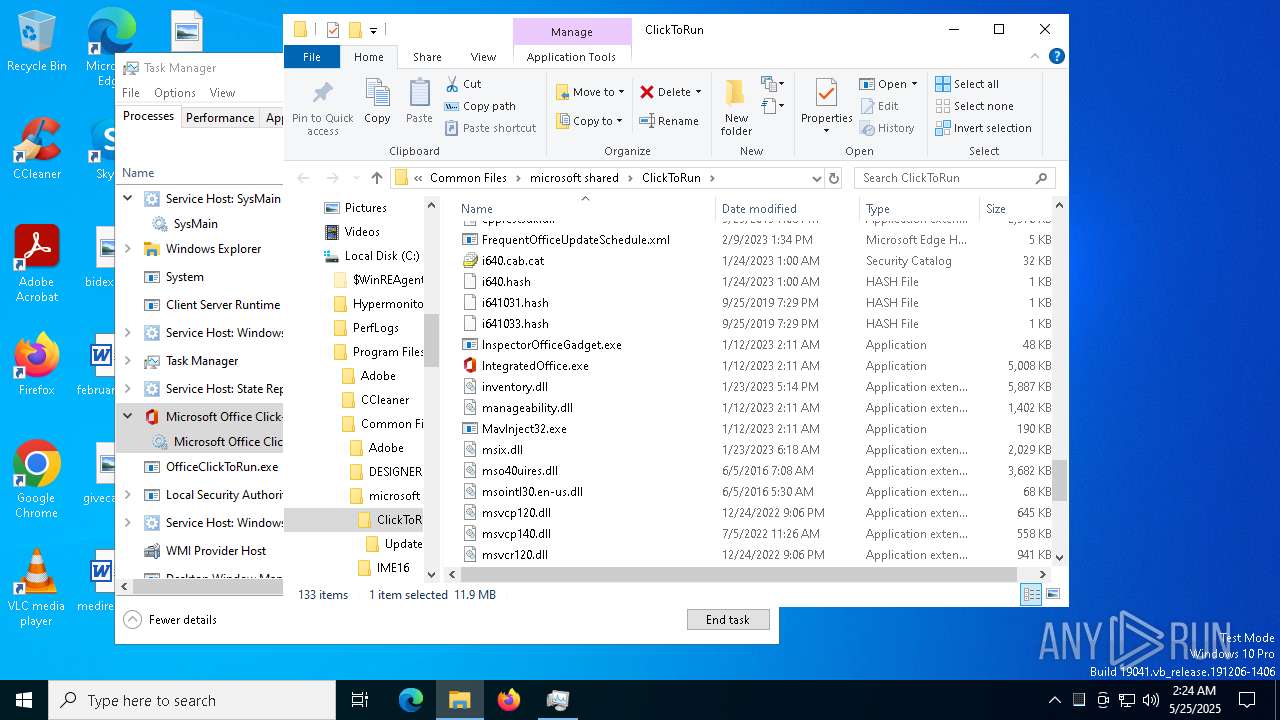
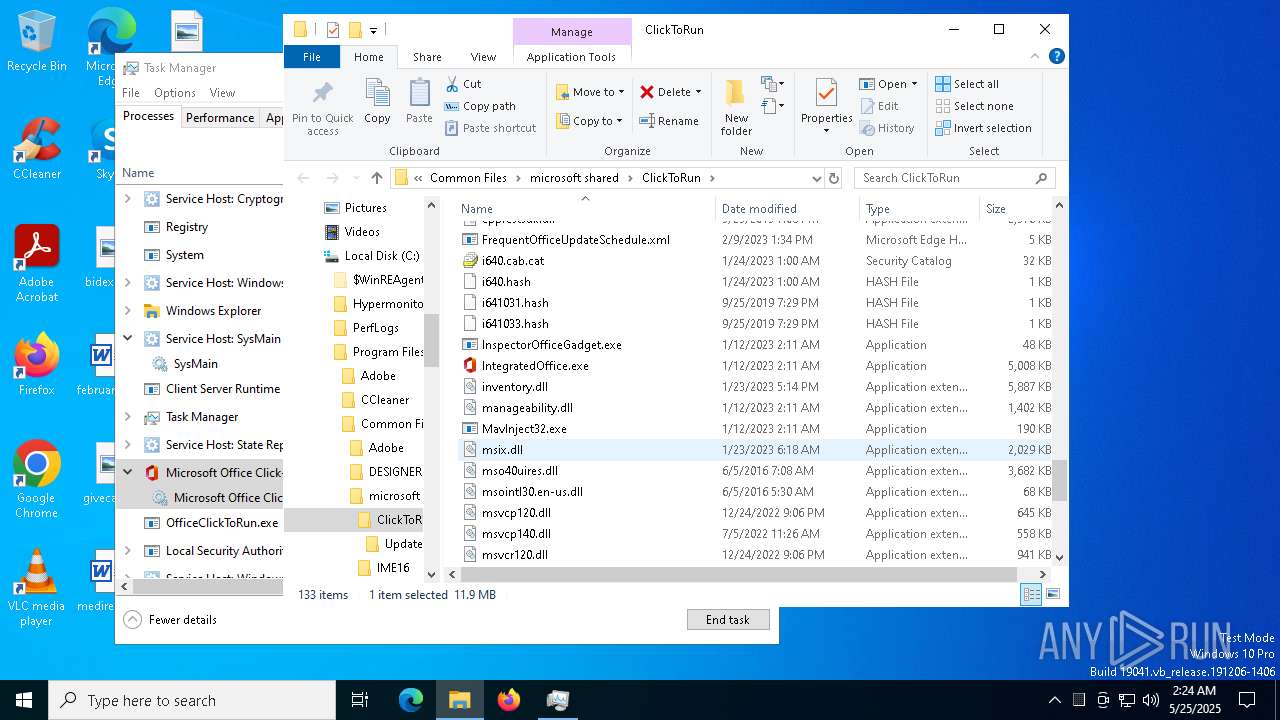
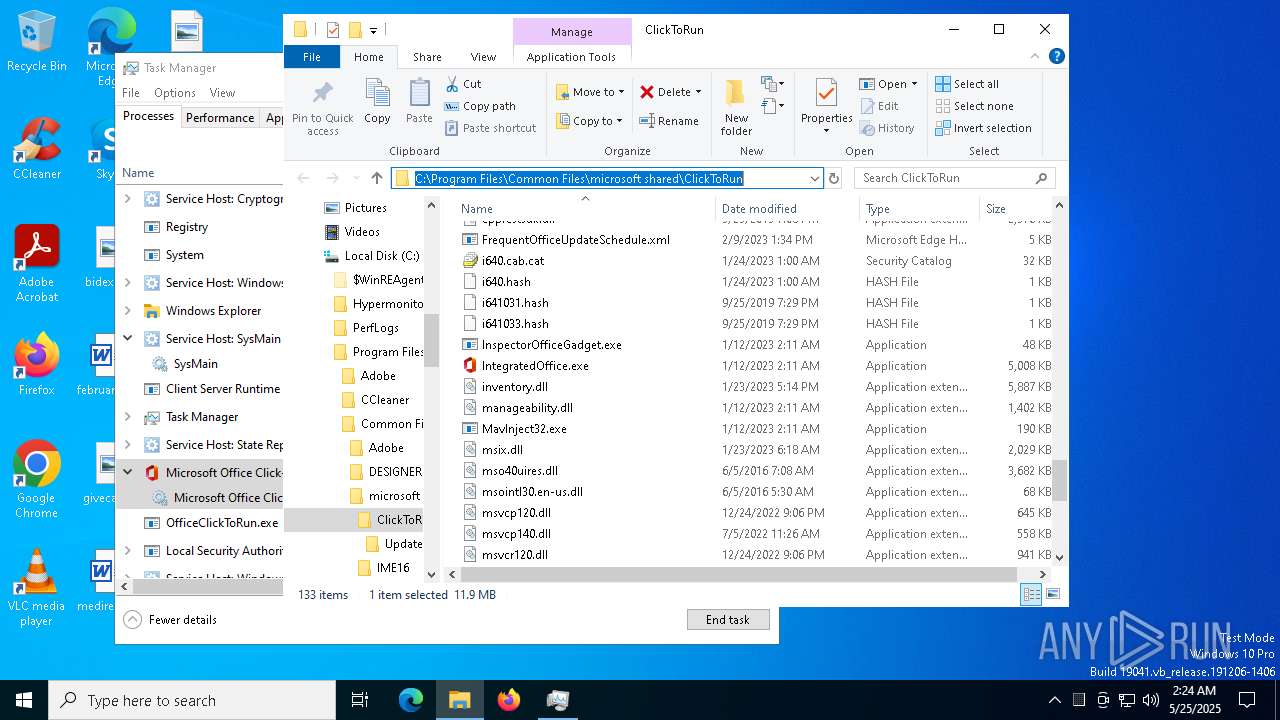
DARKCRYSTAL has been detected (SURICATA)
- OfficeClickToRun.exe (PID: 8472)
Connects to the CnC server
- OfficeClickToRun.exe (PID: 8472)
SUSPICIOUS
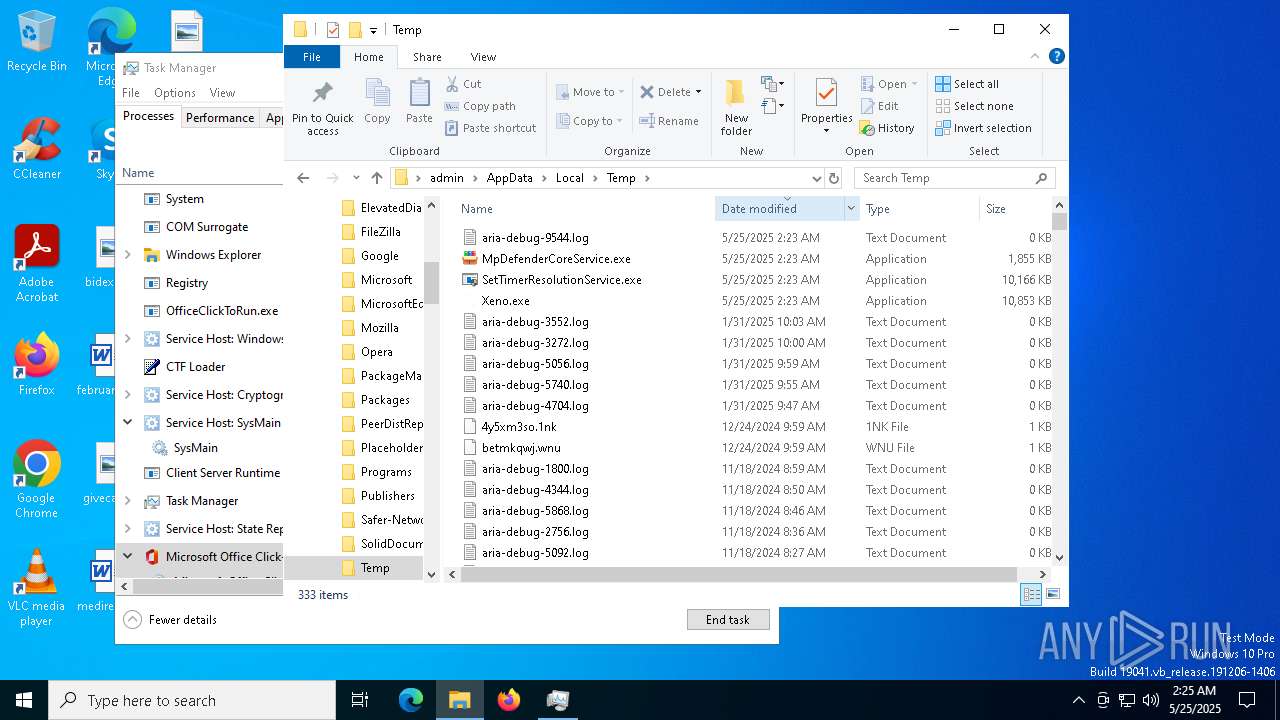
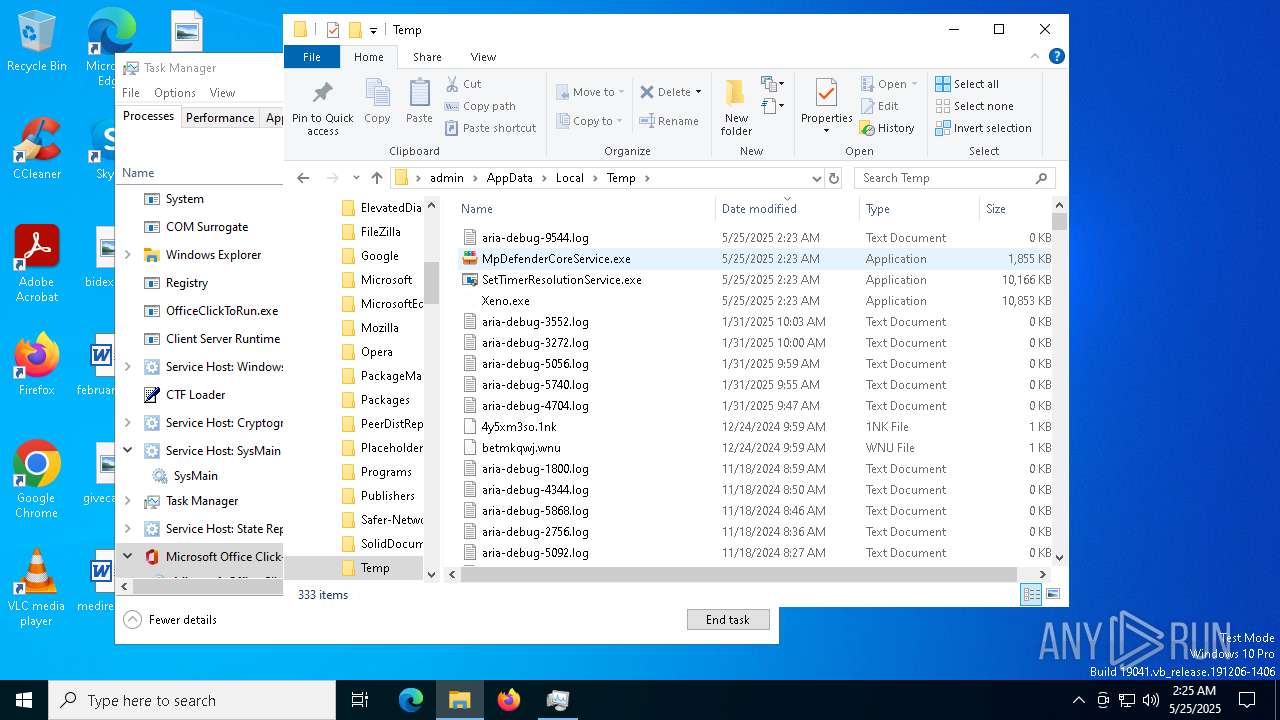
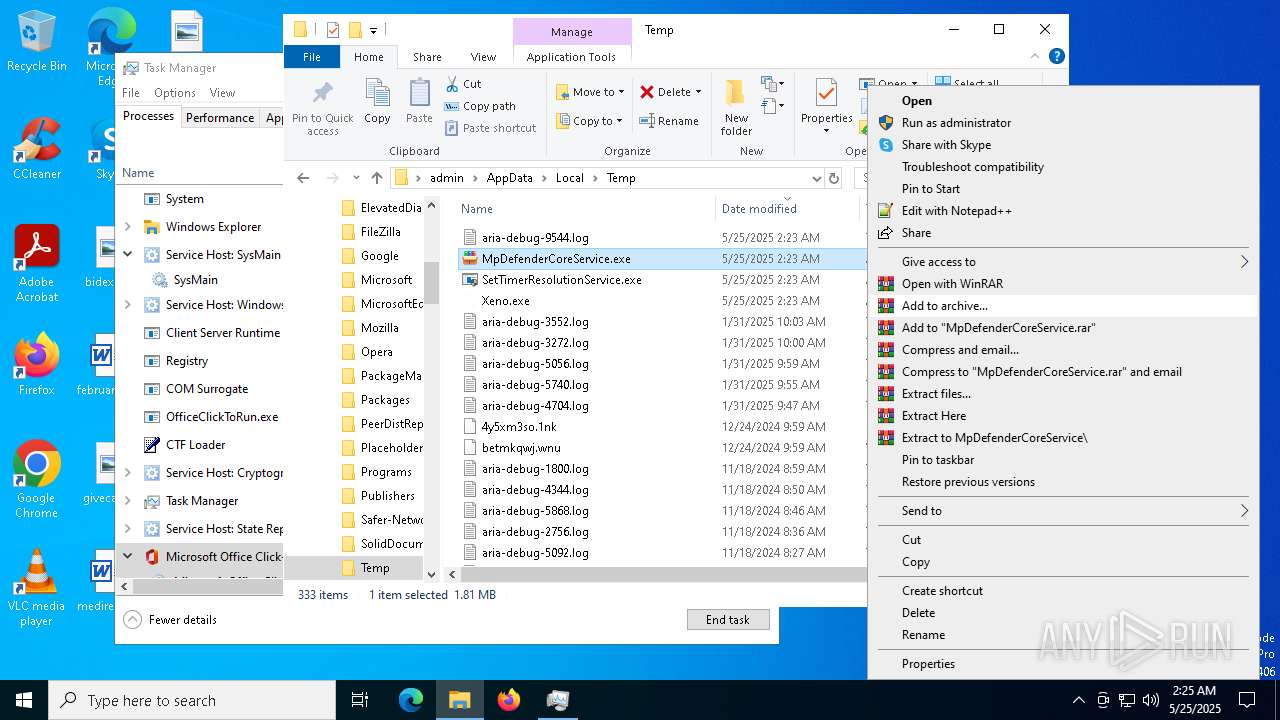
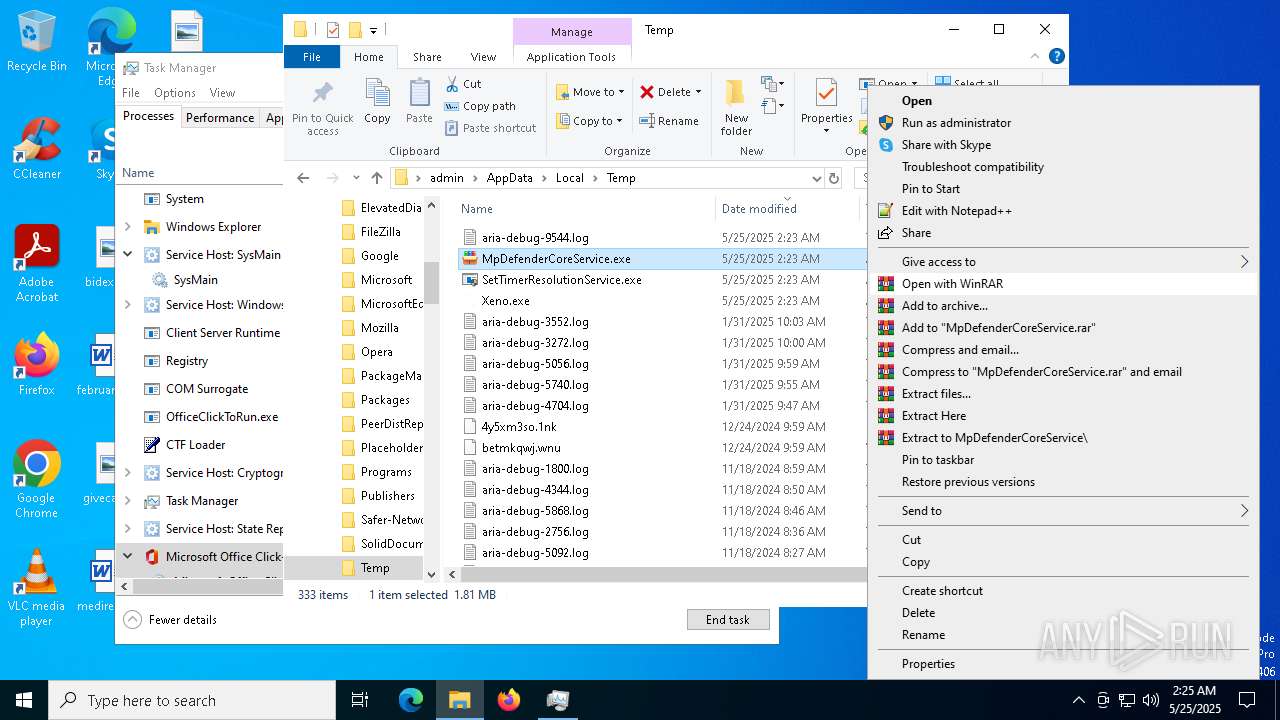
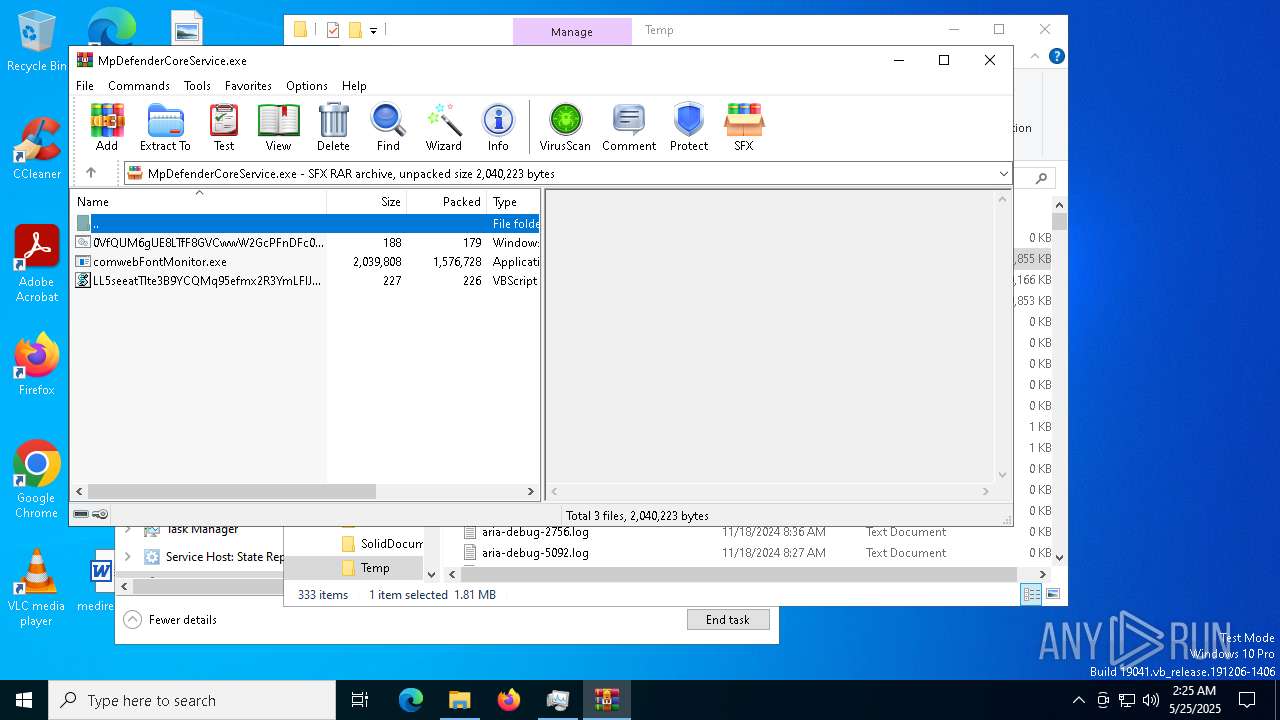
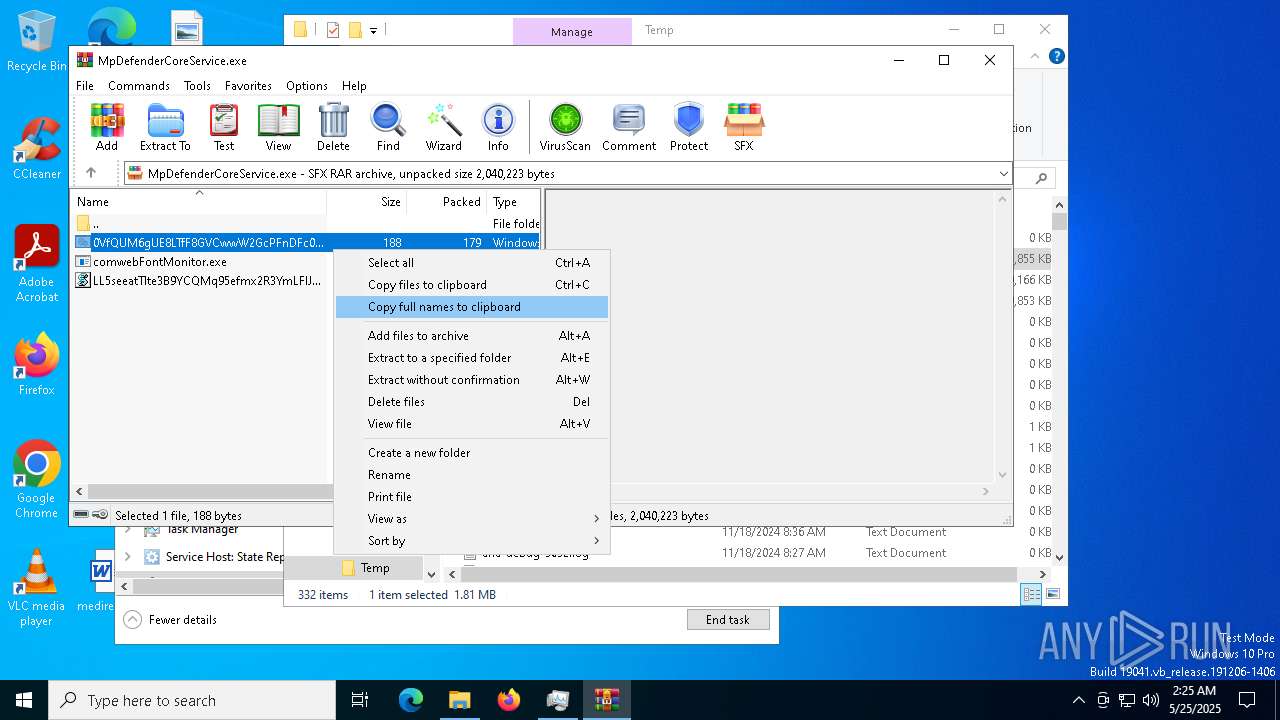
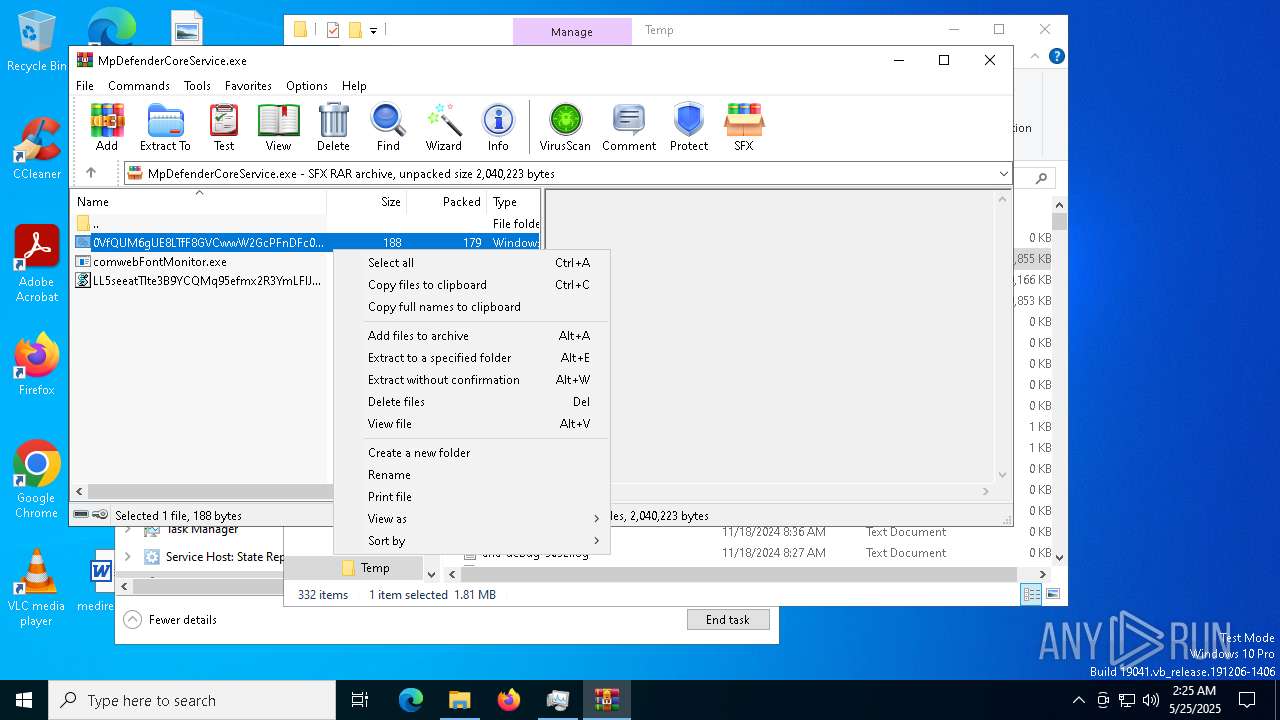
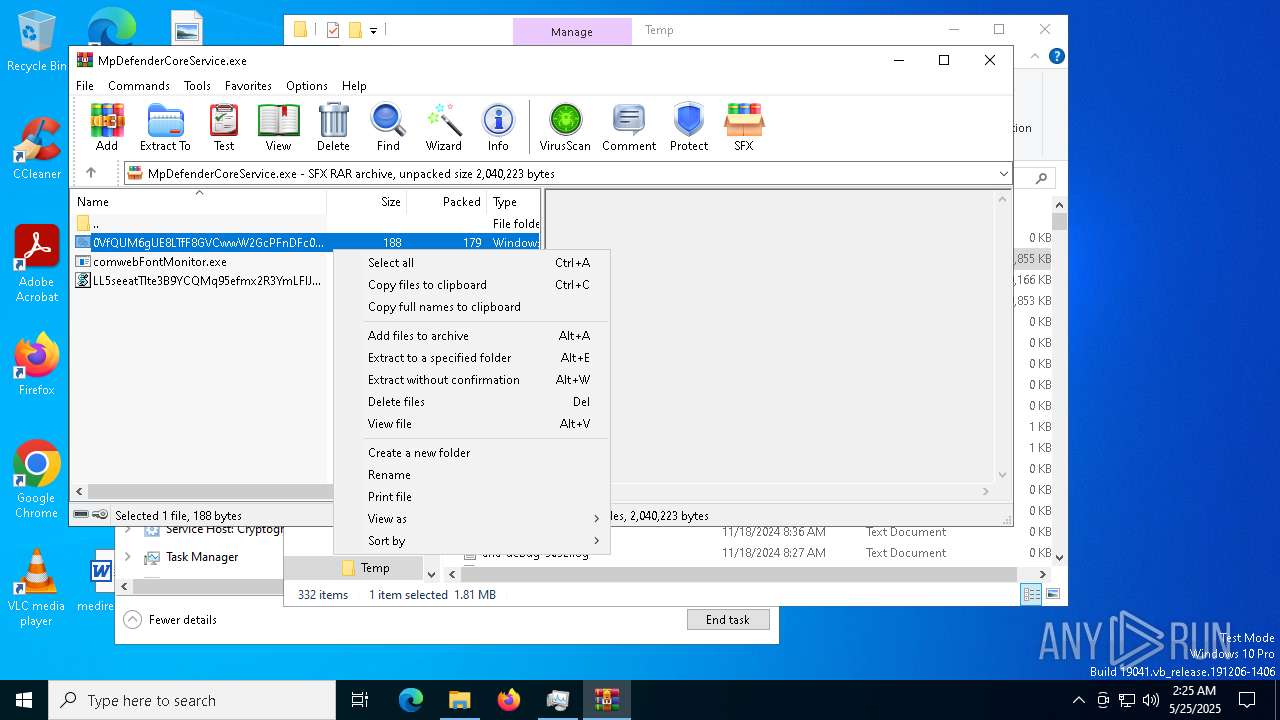
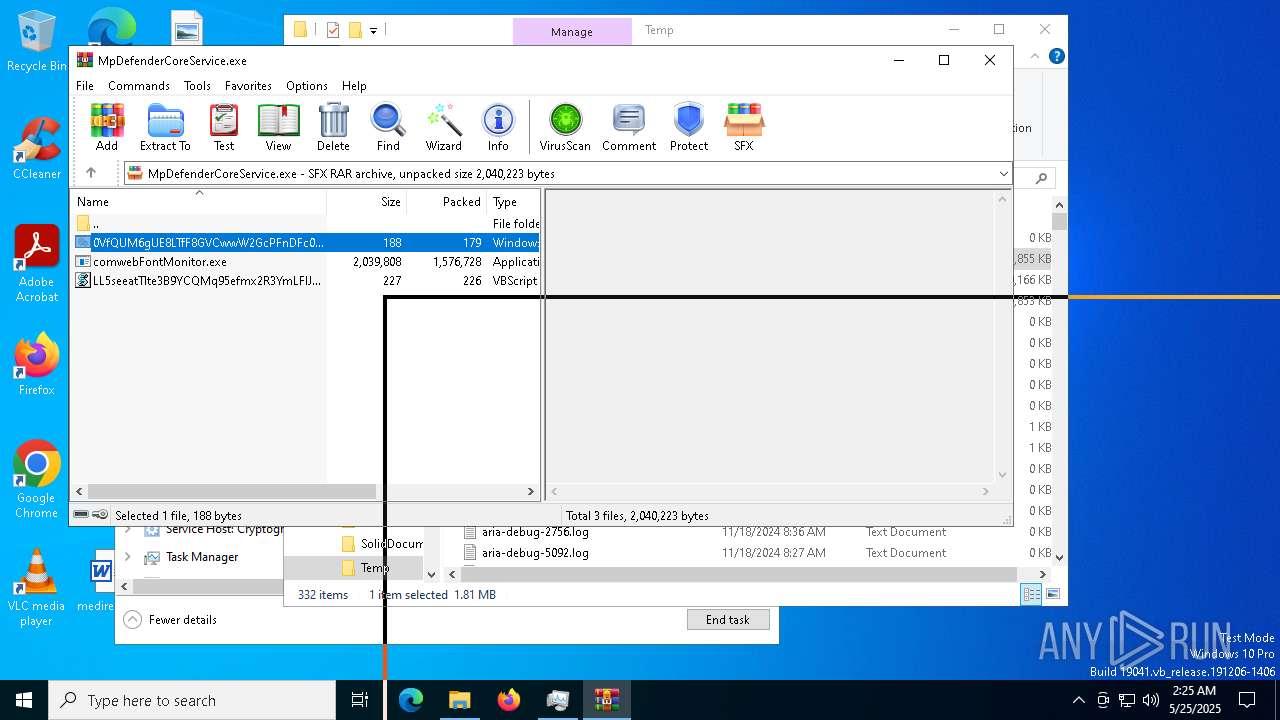
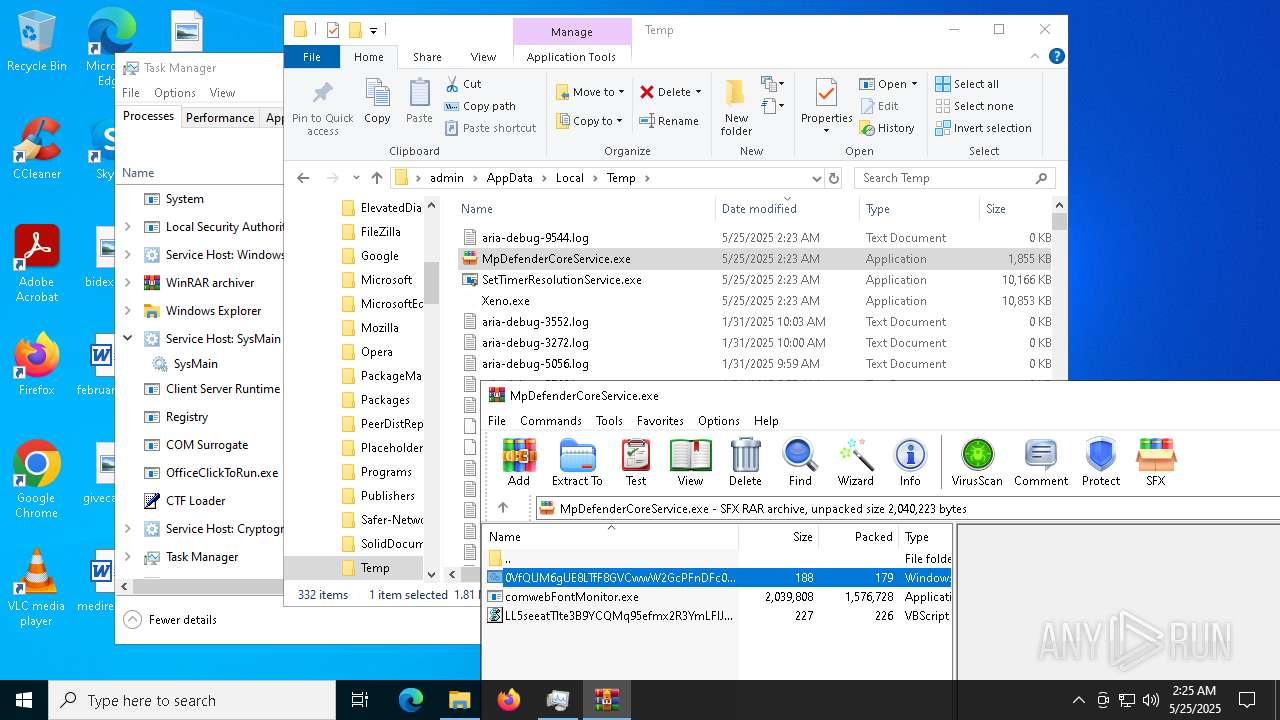
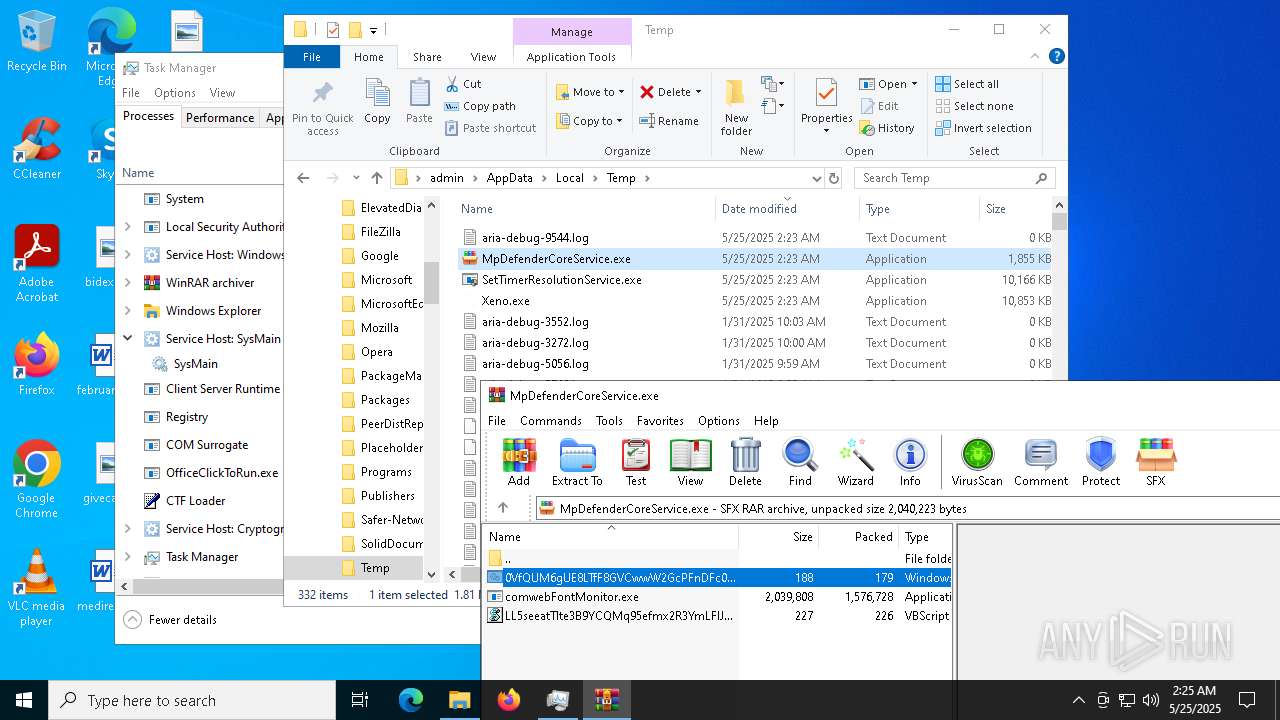
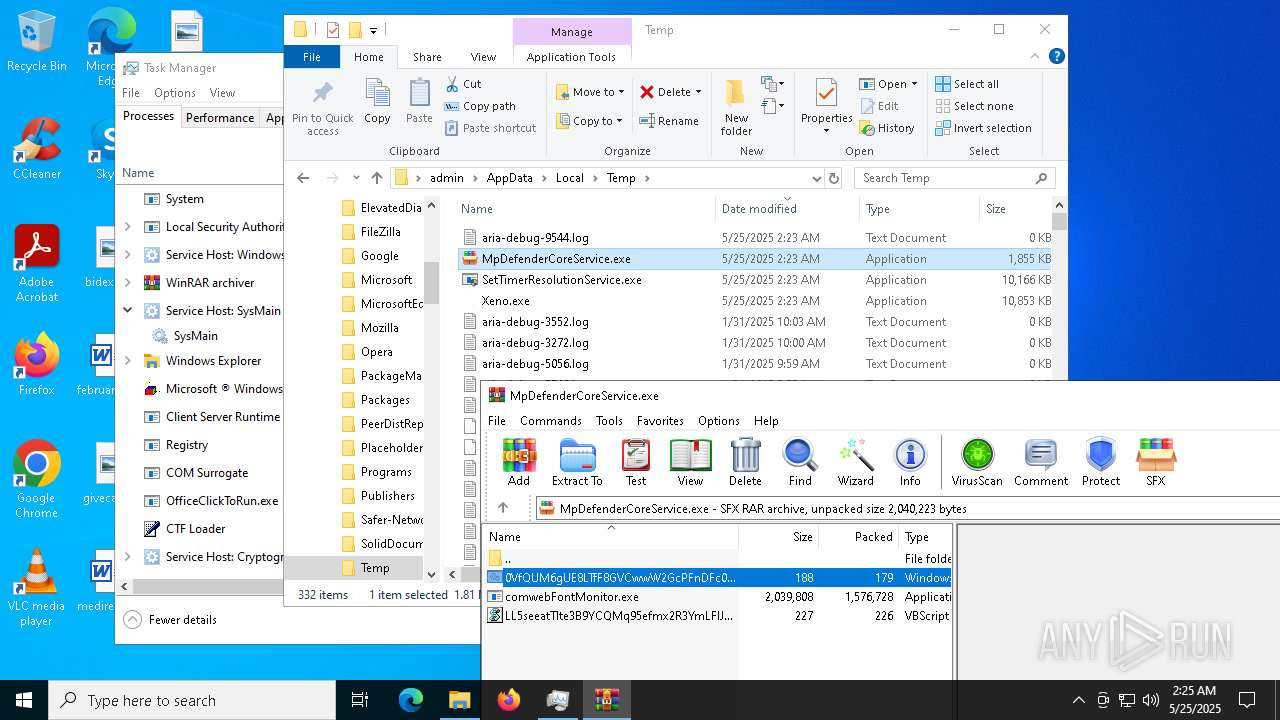
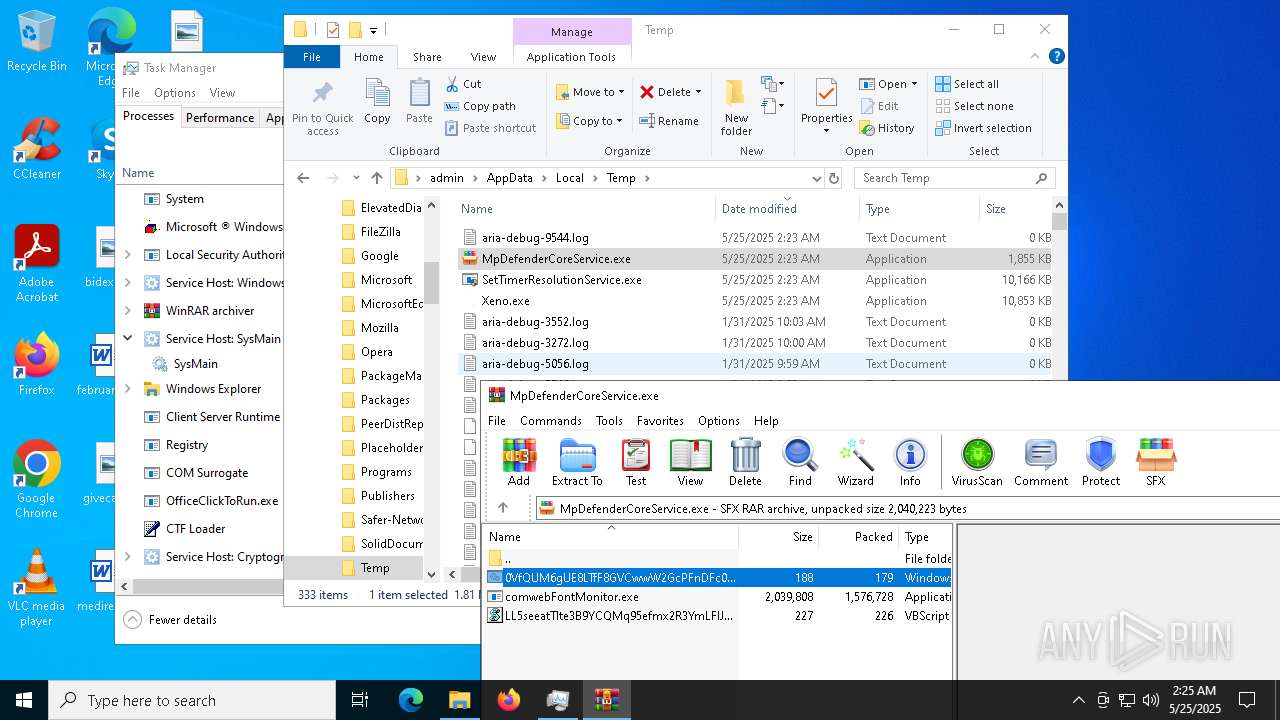
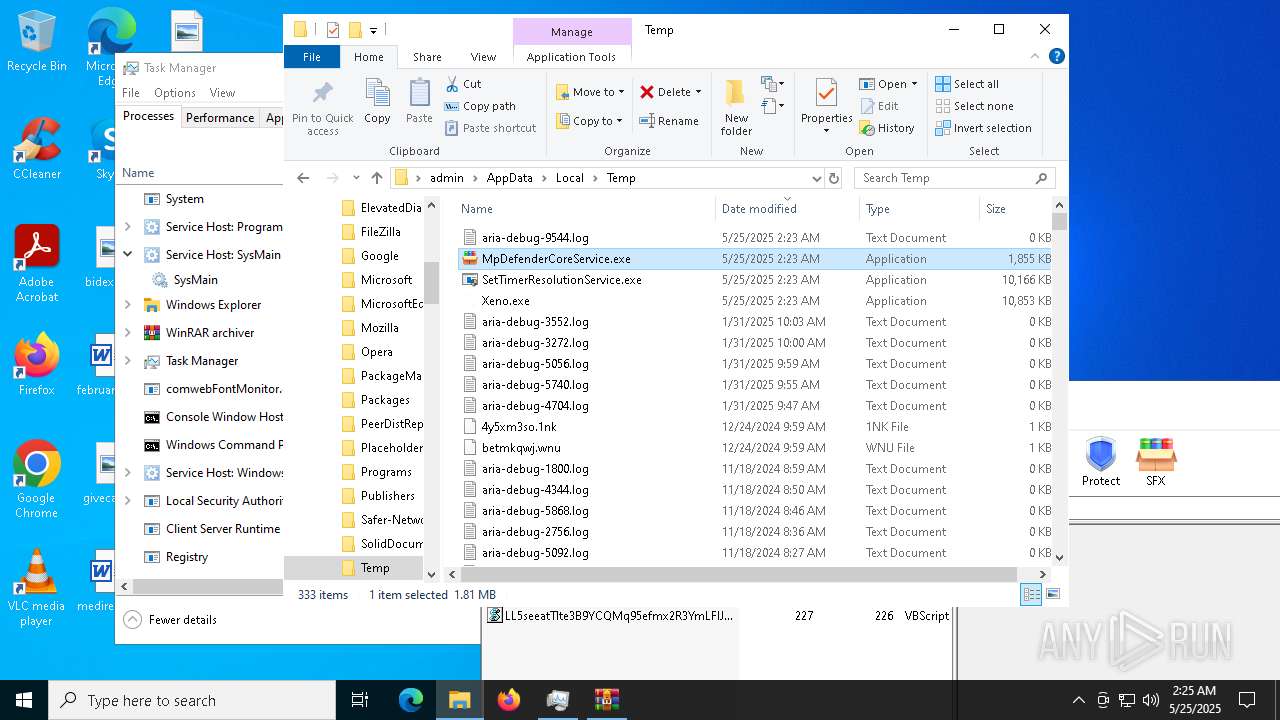
Executable content was dropped or overwritten
- Xeno.exe (PID: 5024)
- MpDefenderCoreService.exe (PID: 5968)
- comwebFontMonitor.exe (PID: 1696)
- comwebFontMonitor.exe (PID: 5416)
- csc.exe (PID: 7188)
- csc.exe (PID: 7308)
- csc.exe (PID: 7472)
- csc.exe (PID: 7384)
- SetTimerResolutionService.exe (PID: 2892)
- updater.exe (PID: 10168)
- OfficeClickToRun.exe (PID: 8472)
Reads security settings of Internet Explorer
- Xeno.exe (PID: 5024)
- MpDefenderCoreService.exe (PID: 5968)
- comwebFontMonitor.exe (PID: 1696)
- comwebFontMonitor.exe (PID: 5416)
Manipulates environment variables
- powershell.exe (PID: 680)
- powershell.exe (PID: 6560)
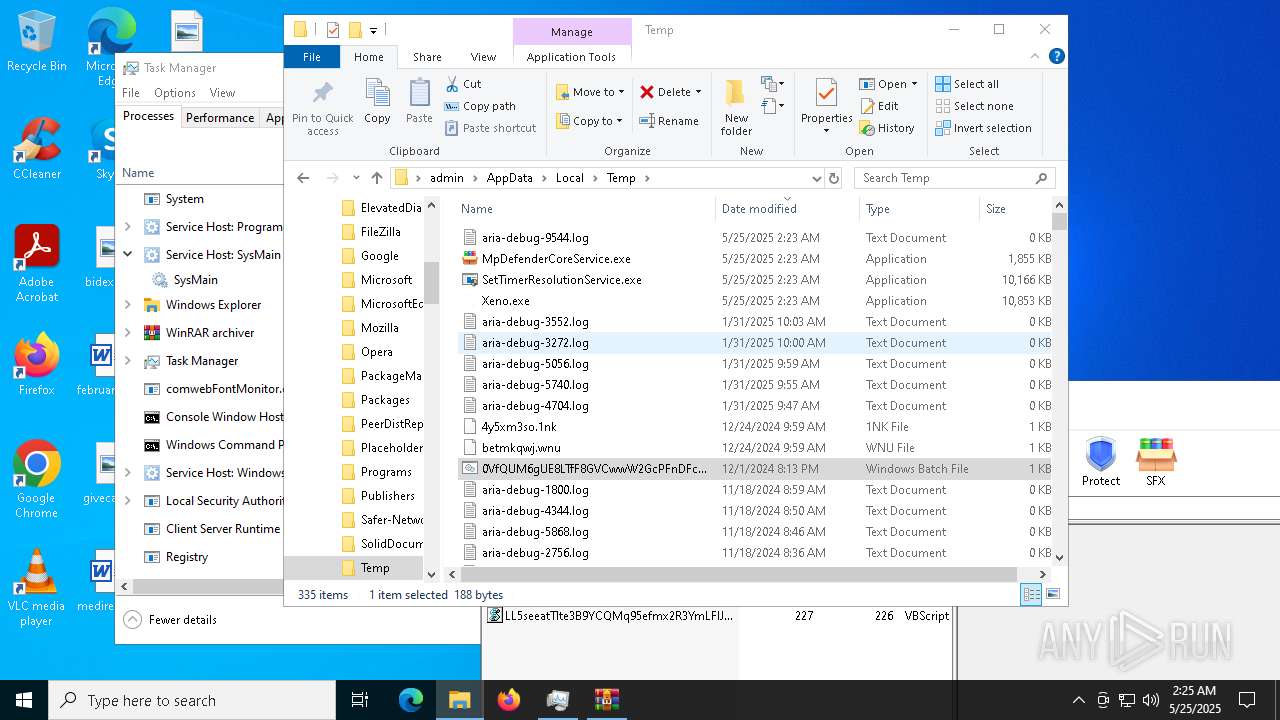
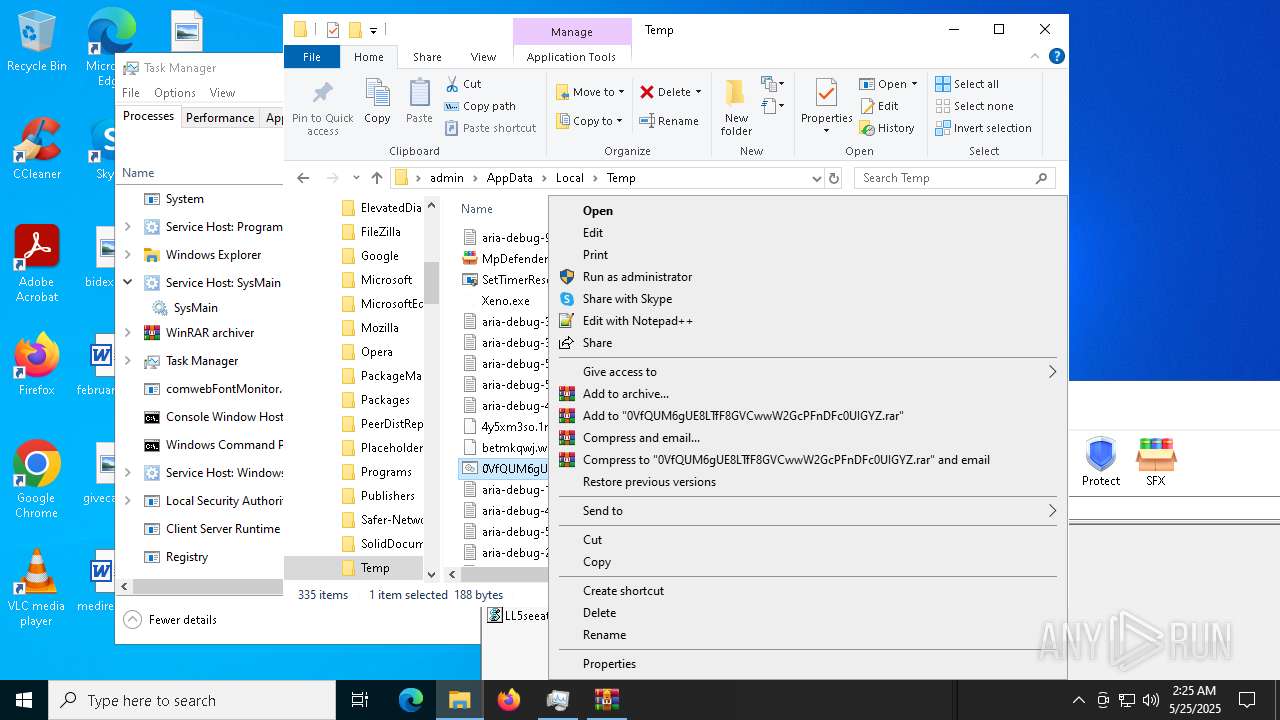
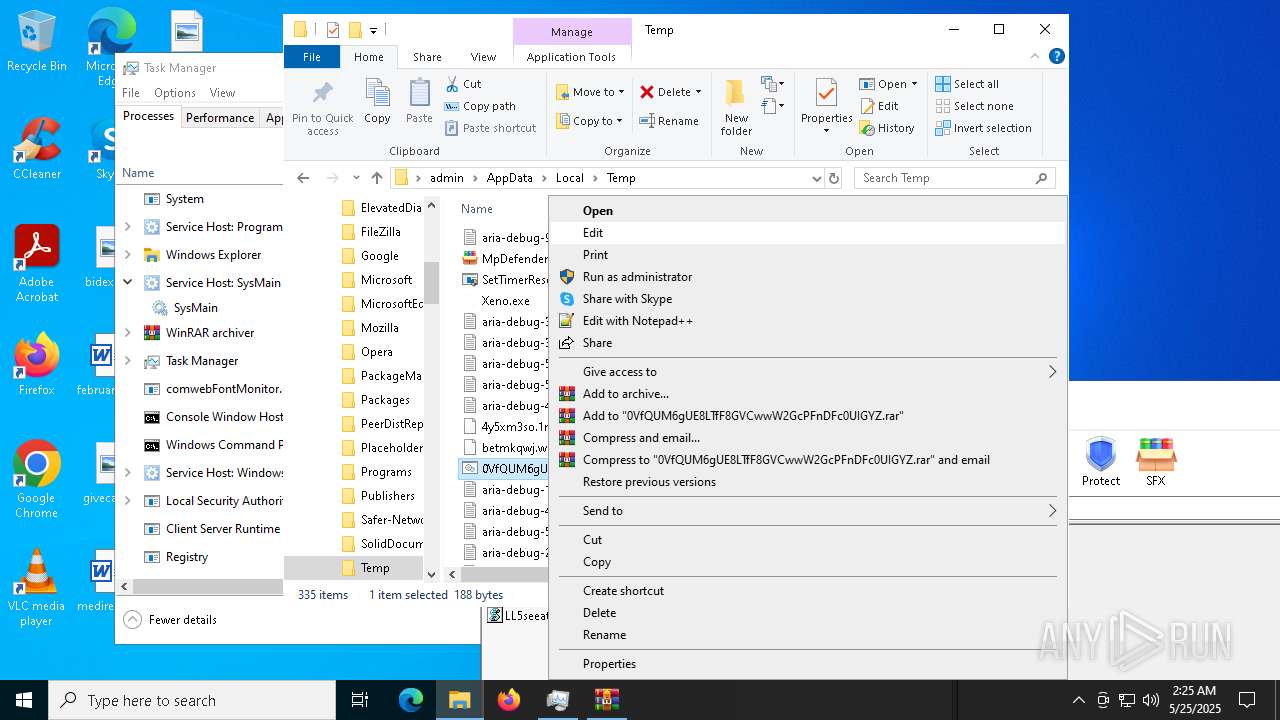
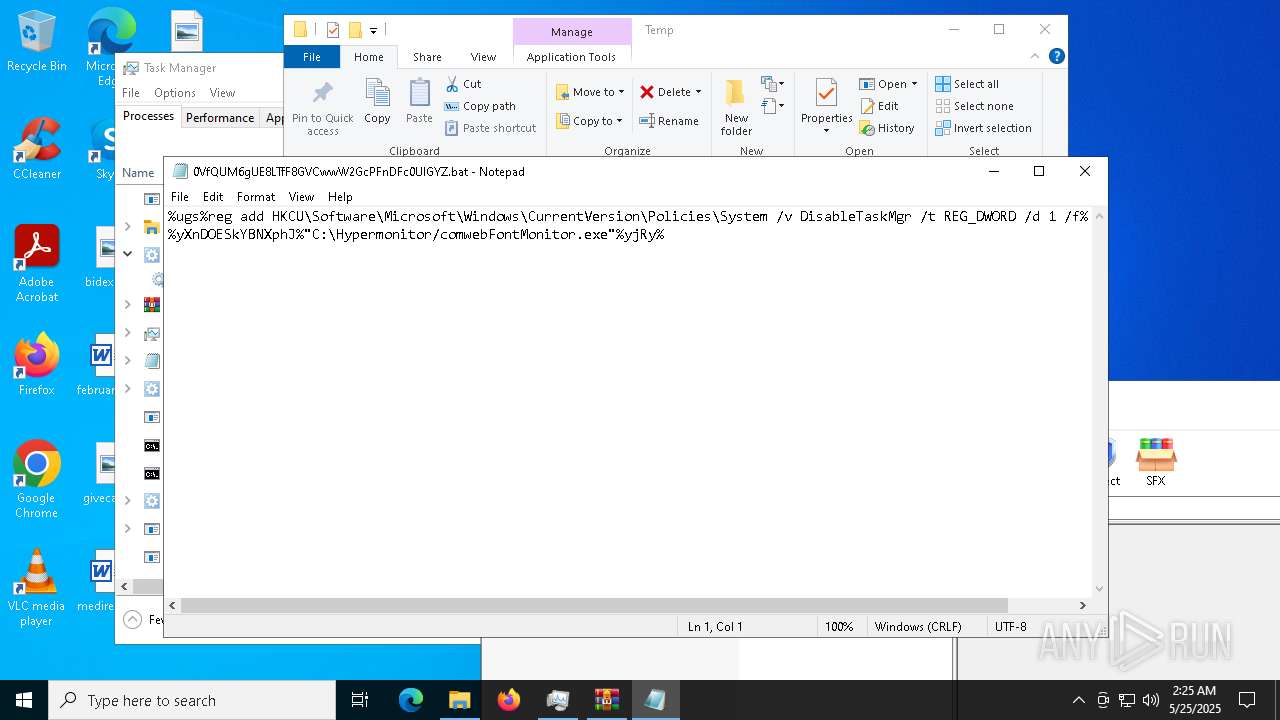
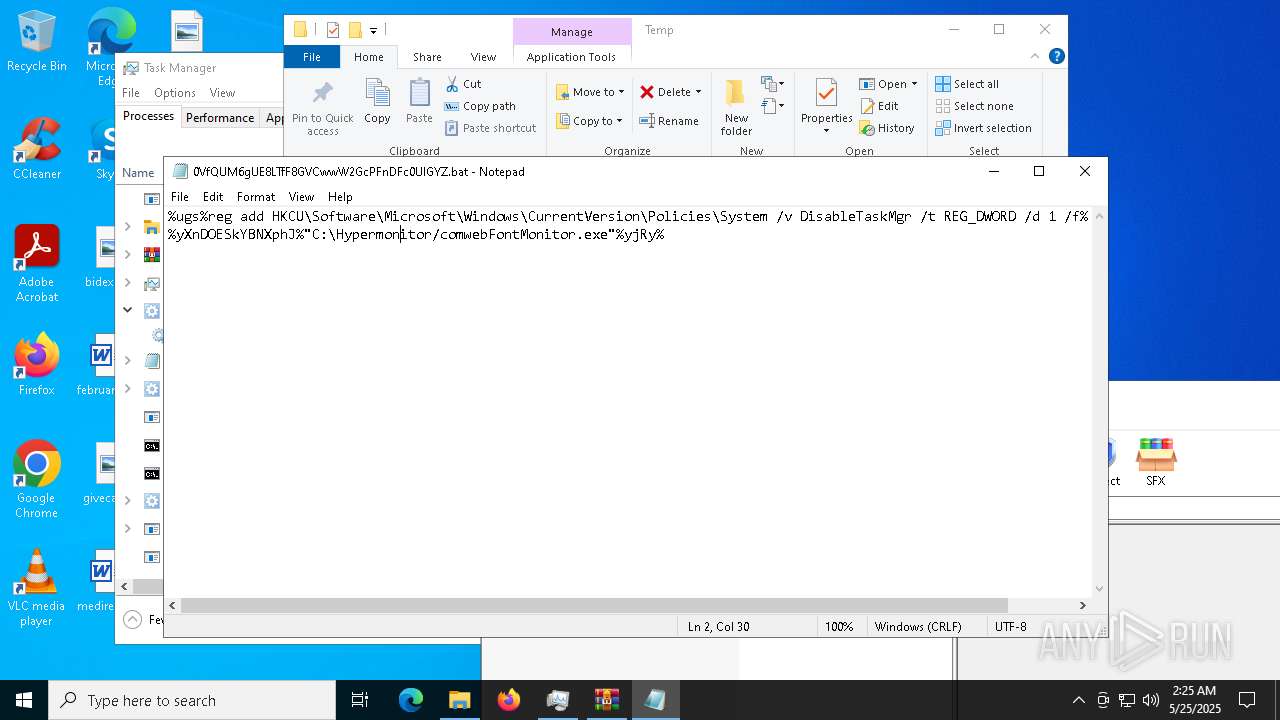
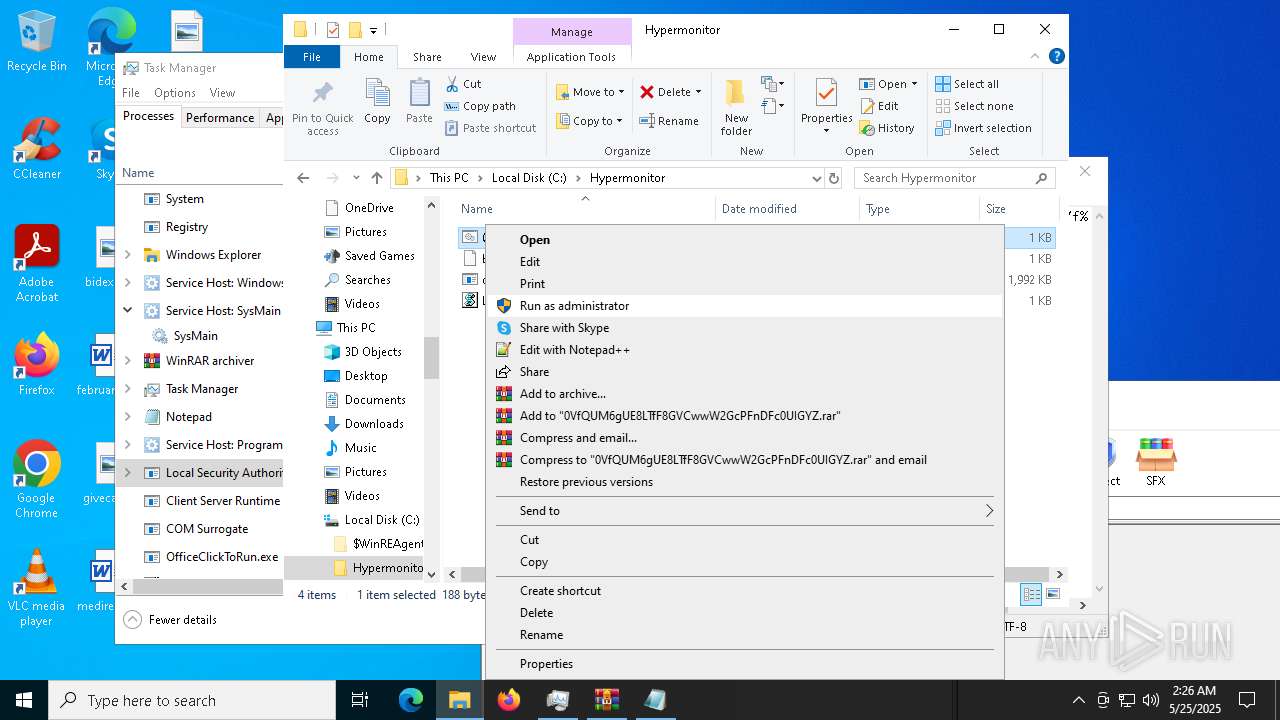
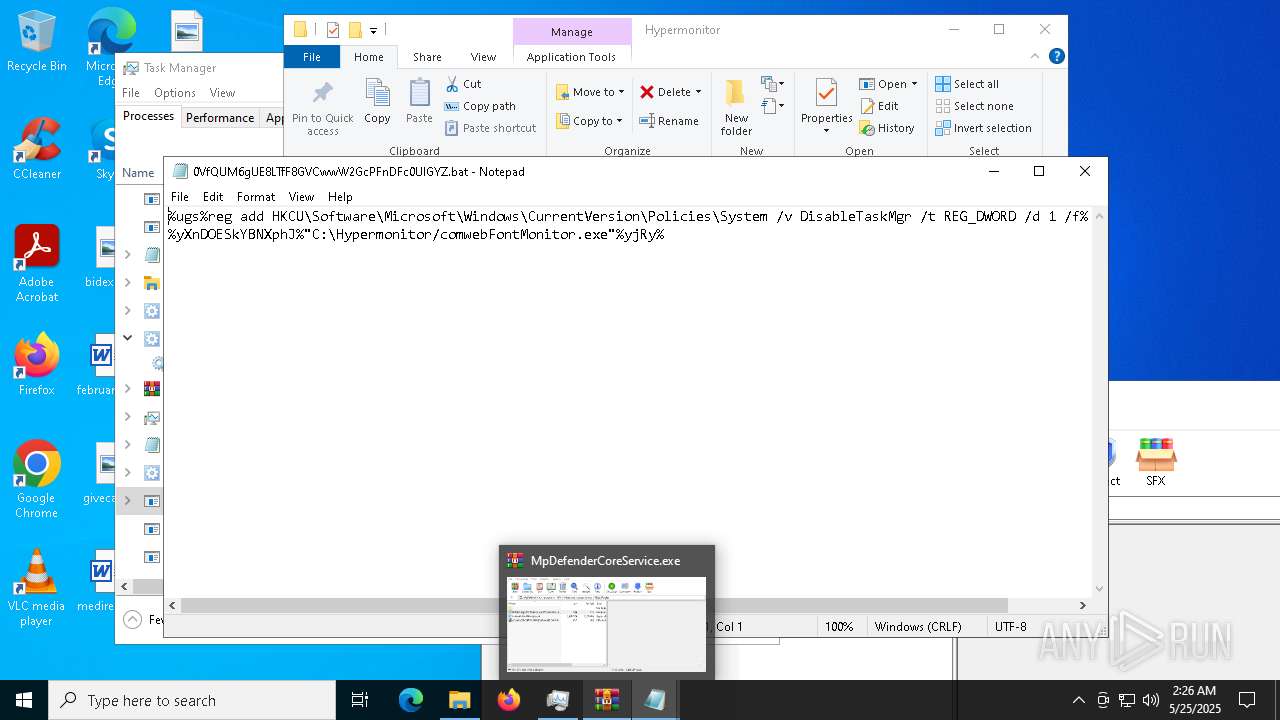
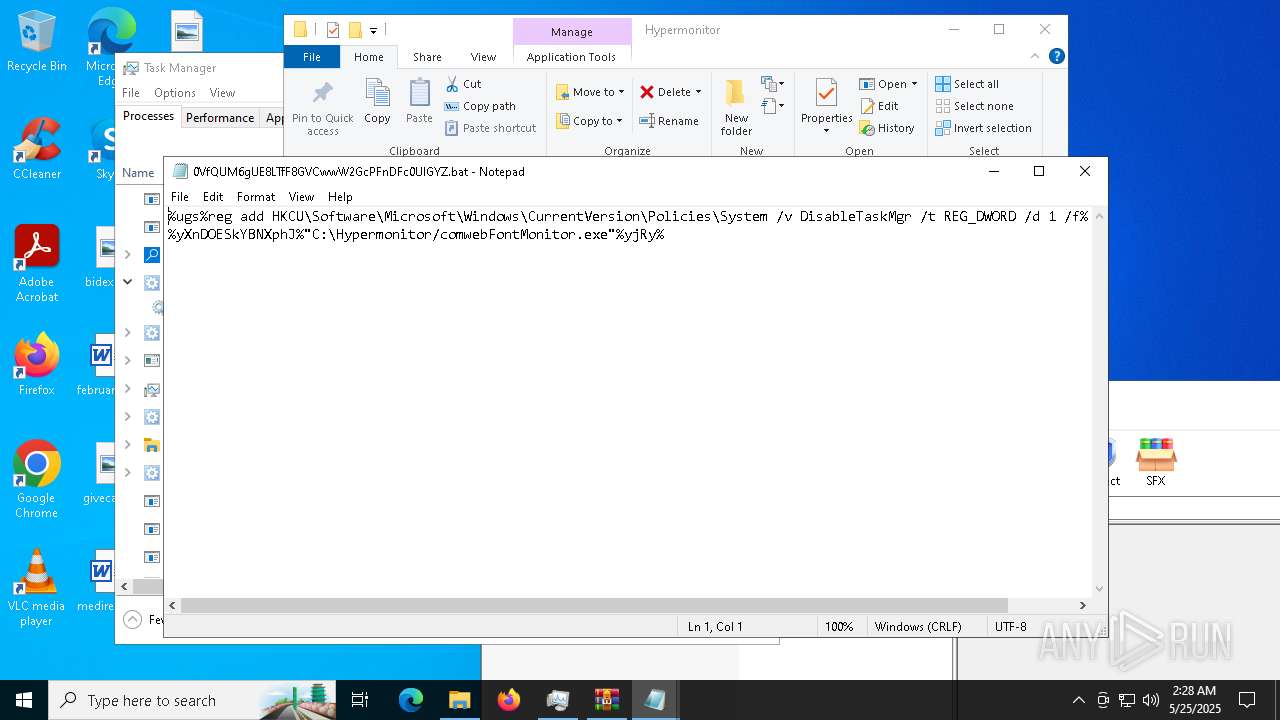
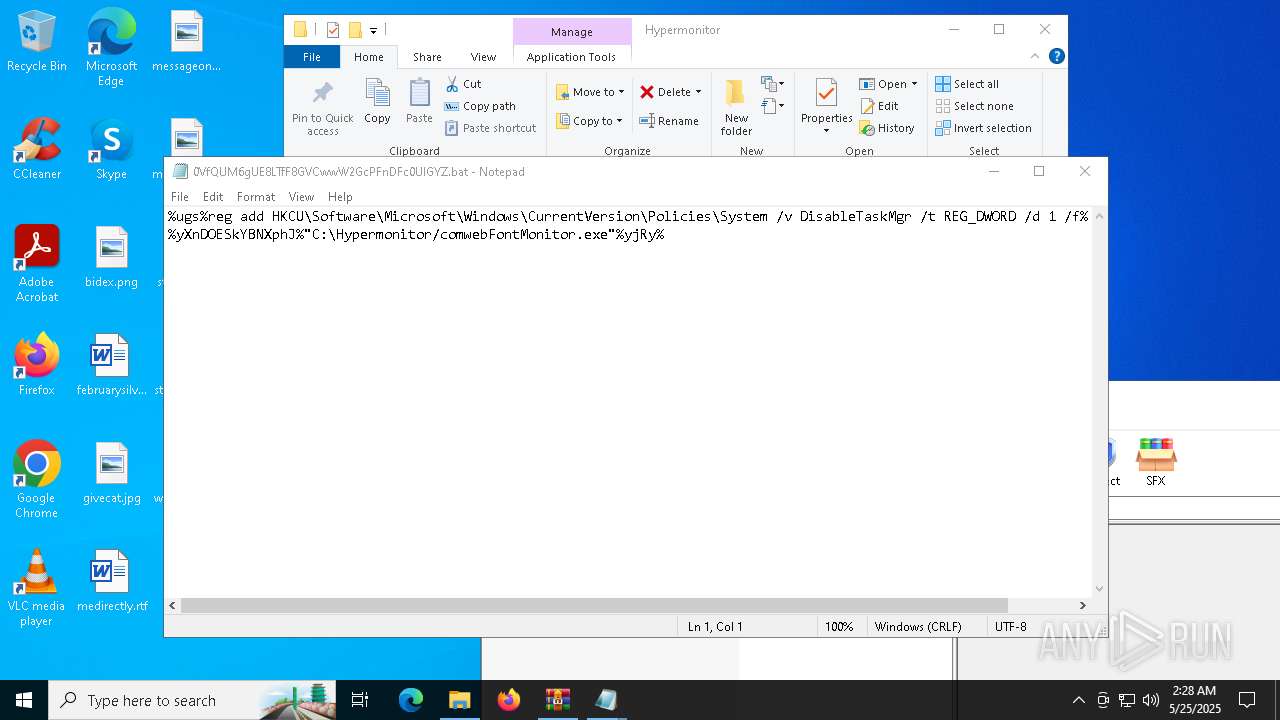
Executing commands from a ".bat" file
- wscript.exe (PID: 2740)
- comwebFontMonitor.exe (PID: 5416)
- wscript.exe (PID: 9112)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2740)
- comwebFontMonitor.exe (PID: 1696)
- comwebFontMonitor.exe (PID: 5416)
- wscript.exe (PID: 9112)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2740)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4572)
- cmd.exe (PID: 10204)
Reads the date of Windows installation
- comwebFontMonitor.exe (PID: 1696)
- comwebFontMonitor.exe (PID: 5416)
The process creates files with name similar to system file names
- comwebFontMonitor.exe (PID: 5416)
Executed via WMI
- schtasks.exe (PID: 2236)
- schtasks.exe (PID: 2136)
- schtasks.exe (PID: 6668)
- schtasks.exe (PID: 7672)
- schtasks.exe (PID: 7764)
- schtasks.exe (PID: 7720)
- schtasks.exe (PID: 7952)
- schtasks.exe (PID: 7896)
- schtasks.exe (PID: 8036)
- schtasks.exe (PID: 8096)
- schtasks.exe (PID: 8176)
- schtasks.exe (PID: 8140)
- schtasks.exe (PID: 7208)
- schtasks.exe (PID: 7288)
- schtasks.exe (PID: 4652)
- schtasks.exe (PID: 7240)
- schtasks.exe (PID: 7356)
- schtasks.exe (PID: 7304)
Process drops legitimate windows executable
- comwebFontMonitor.exe (PID: 5416)
Starts SC.EXE for service management
- cmd.exe (PID: 7524)
- cmd.exe (PID: 8388)
Stops a currently running service
- sc.exe (PID: 7604)
- sc.exe (PID: 7564)
- sc.exe (PID: 7636)
- sc.exe (PID: 7664)
- sc.exe (PID: 7712)
- sc.exe (PID: 7188)
- sc.exe (PID: 5140)
- sc.exe (PID: 7624)
- sc.exe (PID: 672)
- sc.exe (PID: 8412)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 7772)
- cmd.exe (PID: 8836)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7896)
The process executes via Task Scheduler
- updater.exe (PID: 10168)
- taskhostw.exe (PID: 928)
Starts application with an unusual extension
- cmd.exe (PID: 7896)
Starts POWERSHELL.EXE for commands execution
- comwebFontMonitor.exe (PID: 5416)
Script adds exclusion path to Windows Defender
- comwebFontMonitor.exe (PID: 5416)
Drops a system driver (possible attempt to evade defenses)
- updater.exe (PID: 10168)
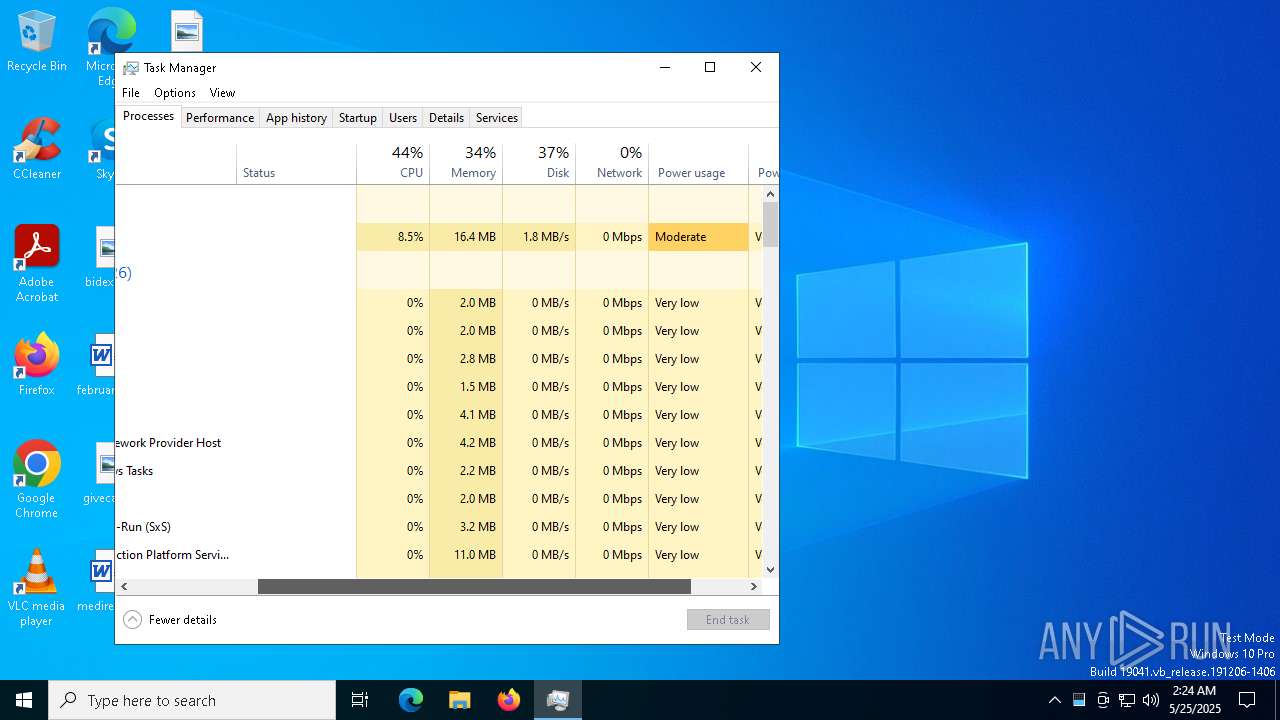
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2196)
Application launched itself
- msedge.exe.exe (PID: 4448)
INFO
Checks supported languages
- Xeno.exe (PID: 5024)
- MpDefenderCoreService.exe (PID: 5968)
- SetTimerResolutionService.exe (PID: 2892)
- comwebFontMonitor.exe (PID: 1696)
- comwebFontMonitor.exe (PID: 5416)
- cvtres.exe (PID: 7276)
- csc.exe (PID: 7308)
- csc.exe (PID: 7188)
- cvtres.exe (PID: 7352)
- csc.exe (PID: 7384)
- csc.exe (PID: 7472)
- cvtres.exe (PID: 7572)
- cvtres.exe (PID: 7440)
- chcp.com (PID: 9208)
Reads the computer name
- Xeno.exe (PID: 5024)
- MpDefenderCoreService.exe (PID: 5968)
- comwebFontMonitor.exe (PID: 1696)
- comwebFontMonitor.exe (PID: 5416)
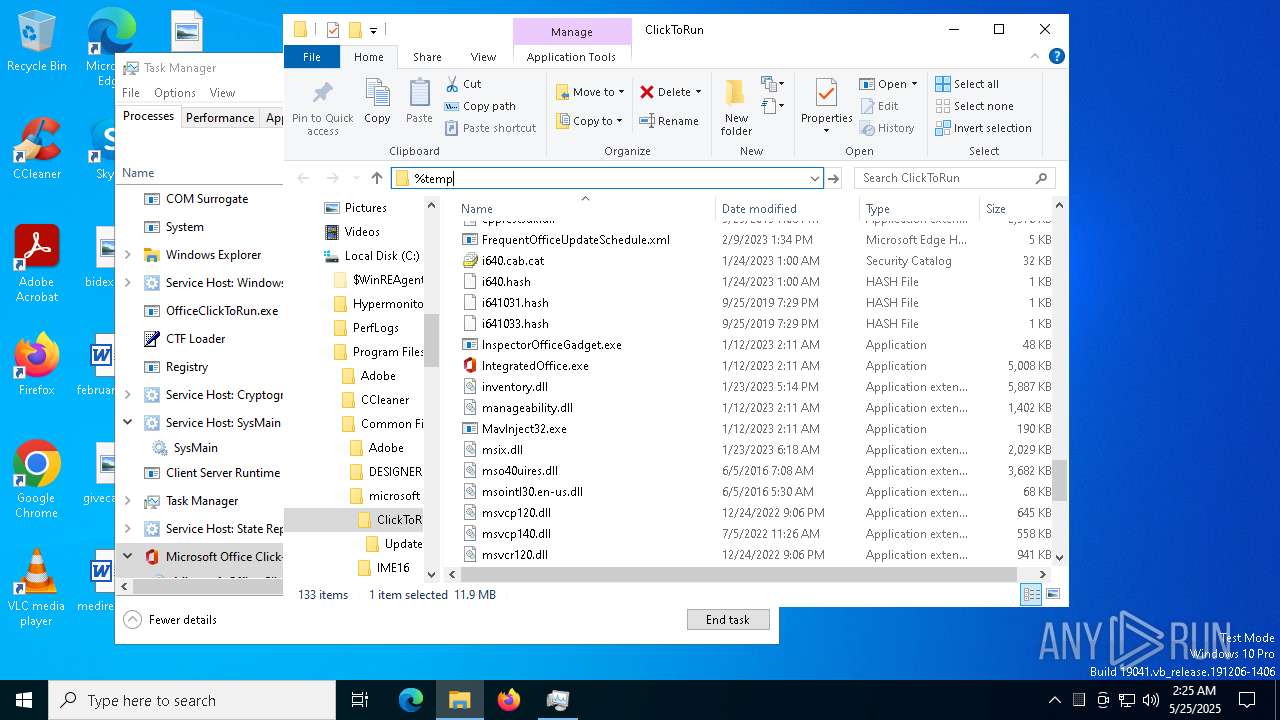
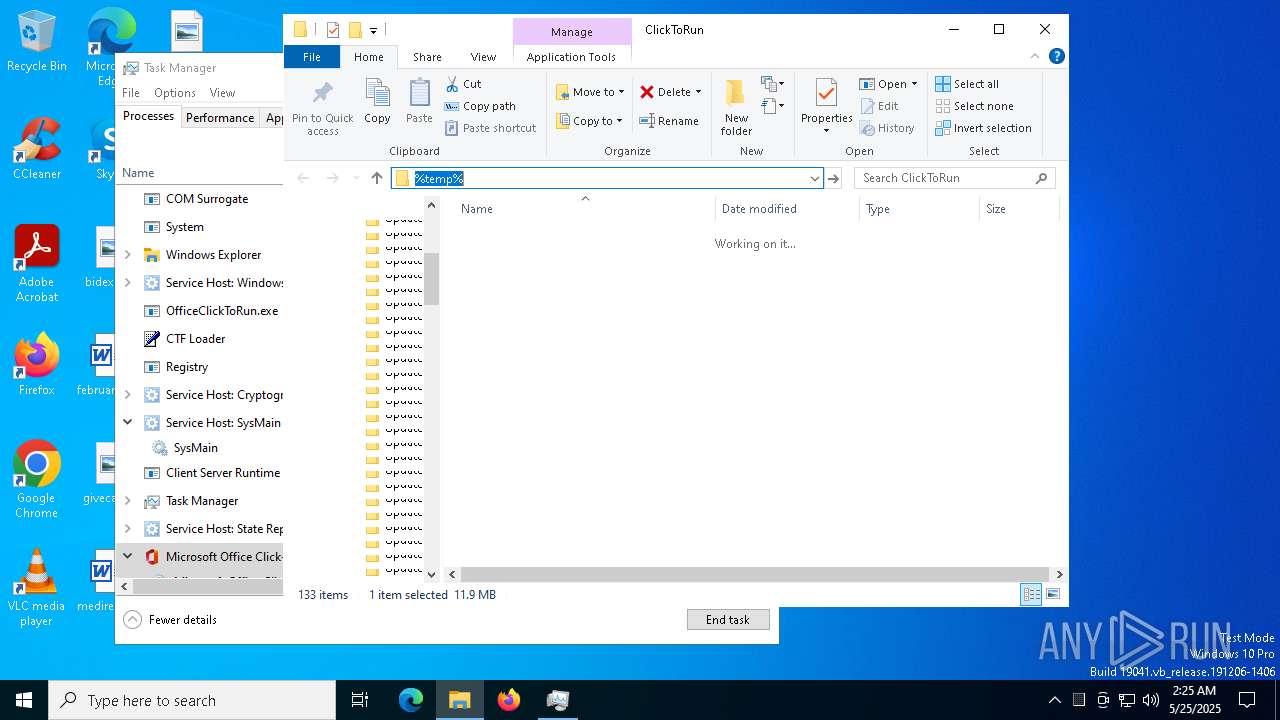
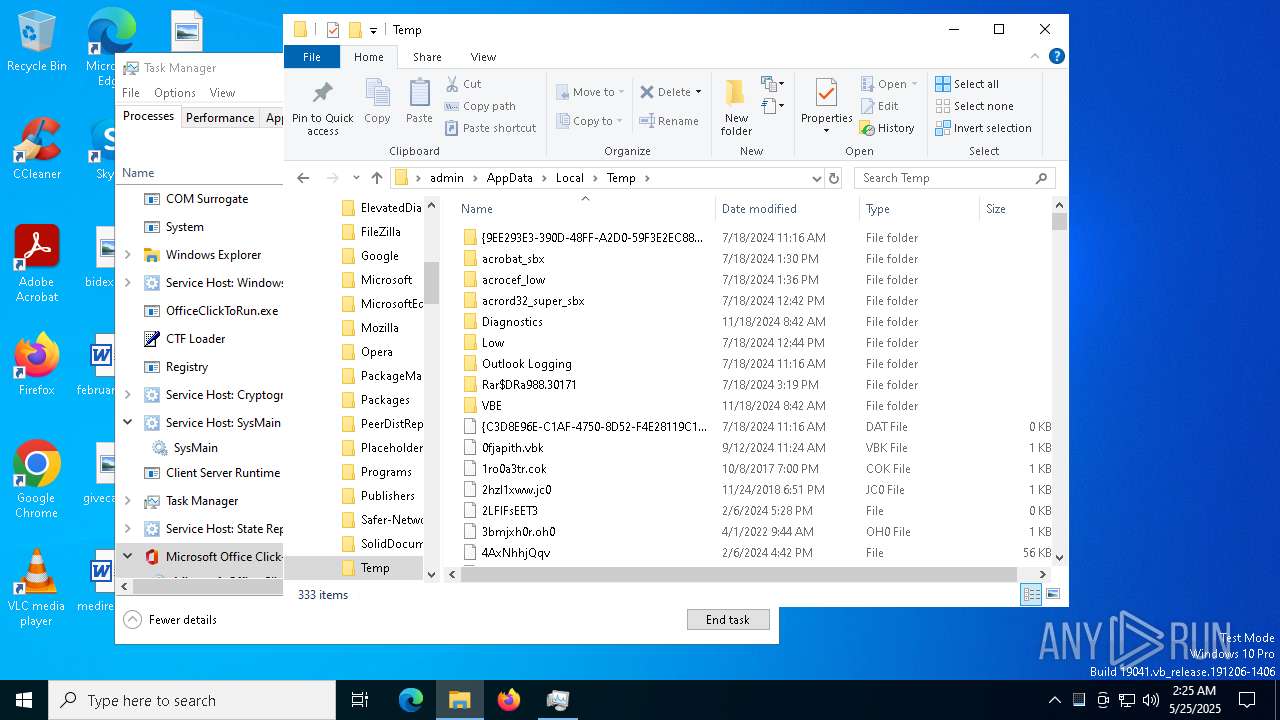
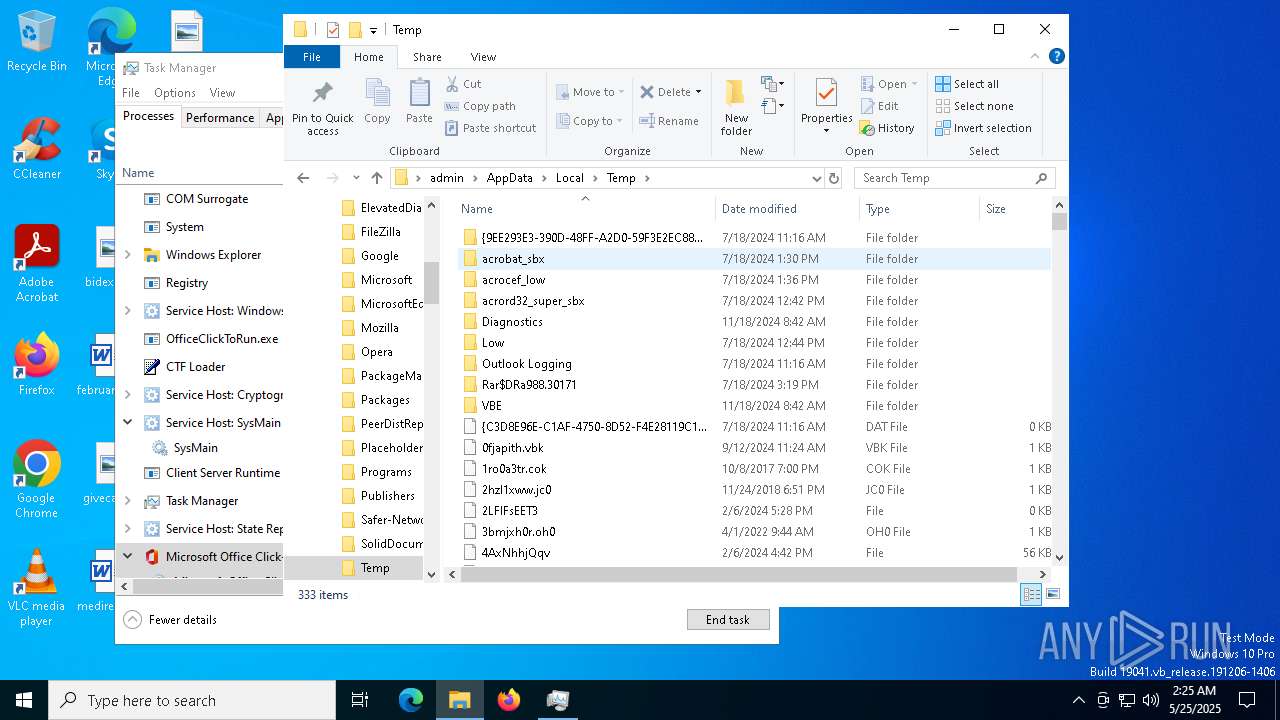
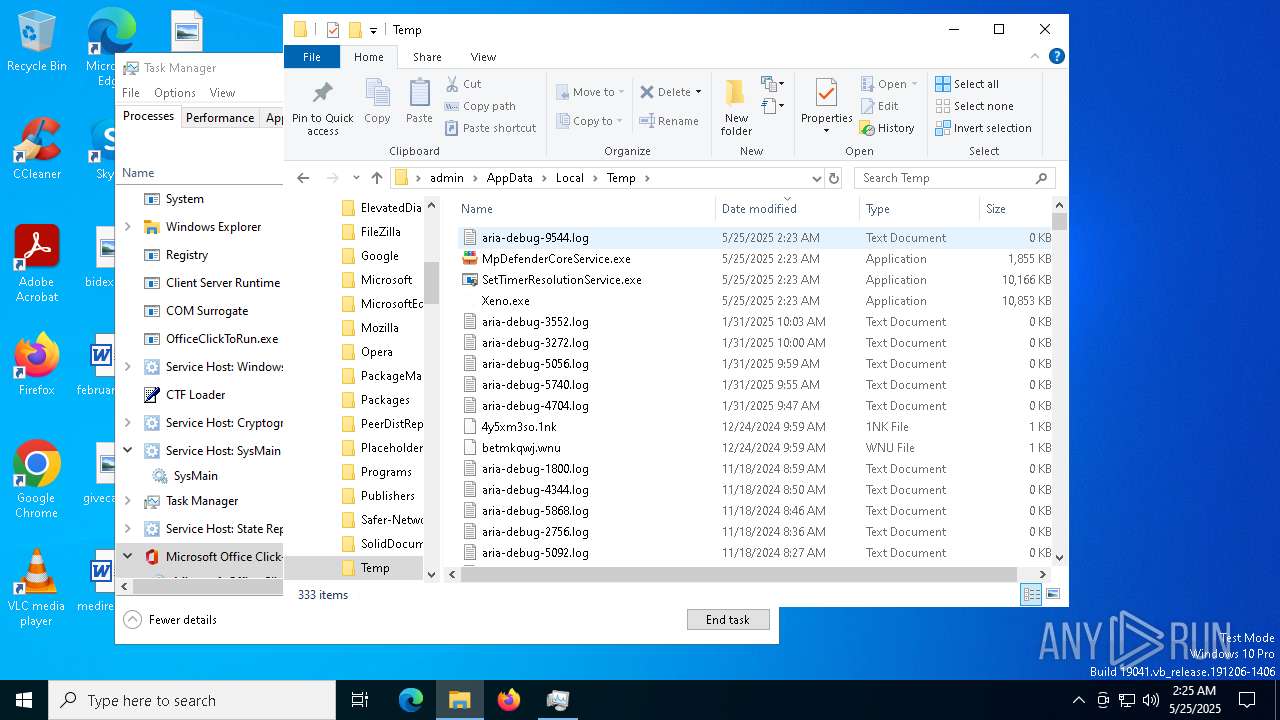
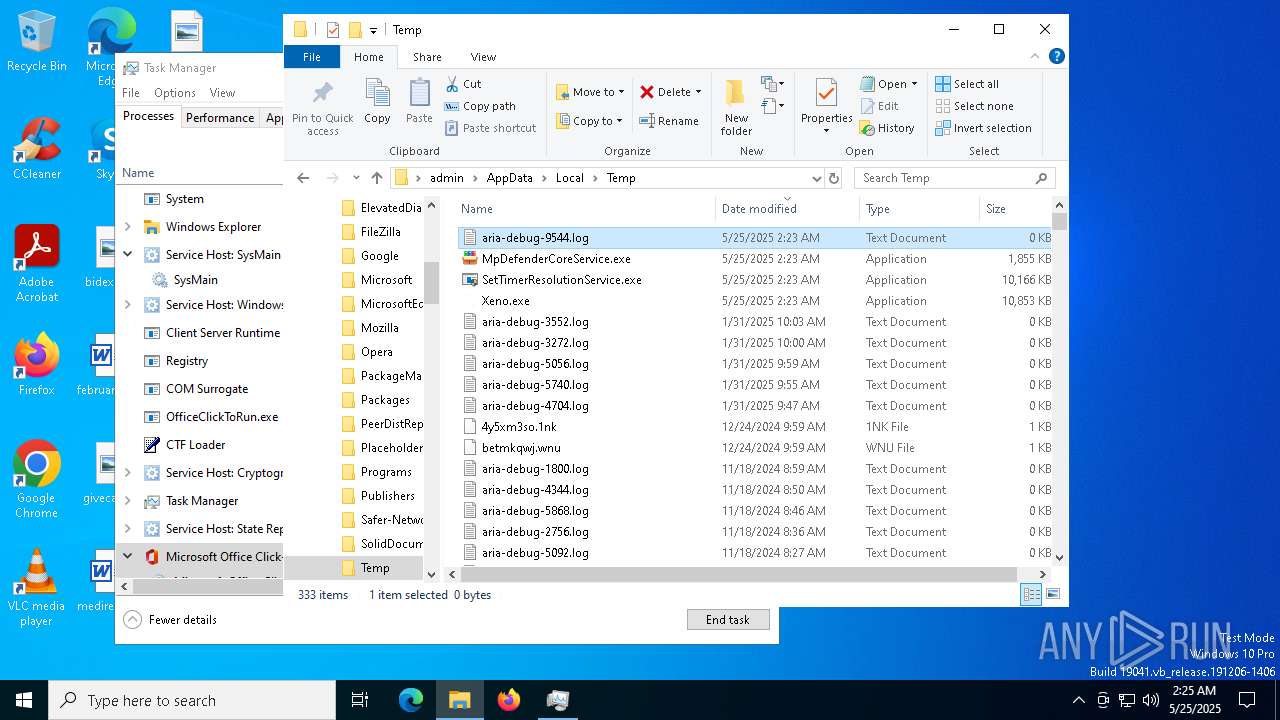
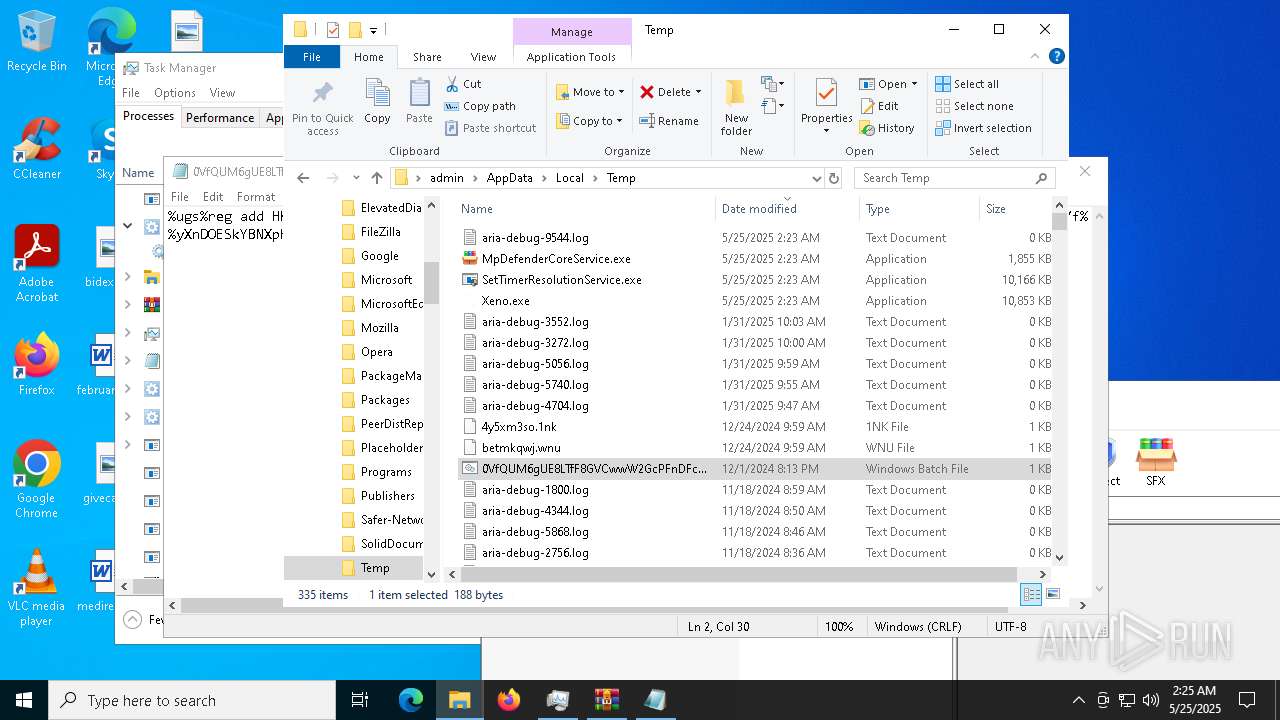
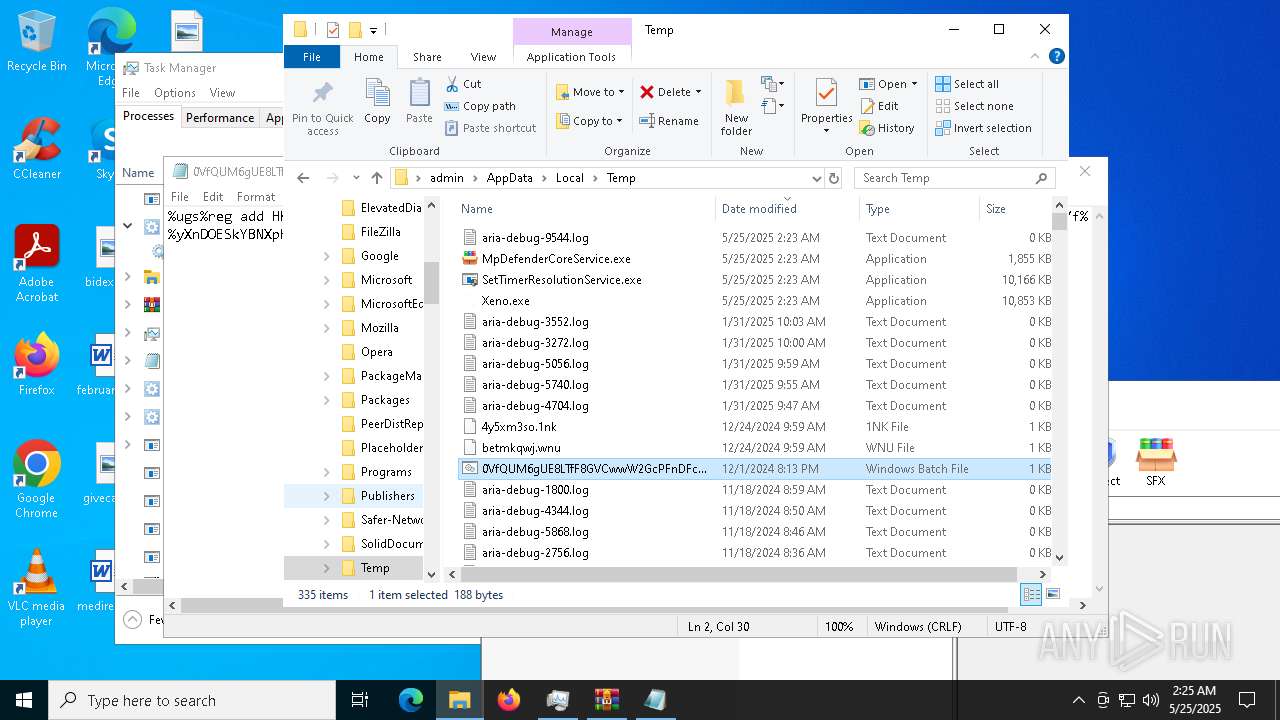
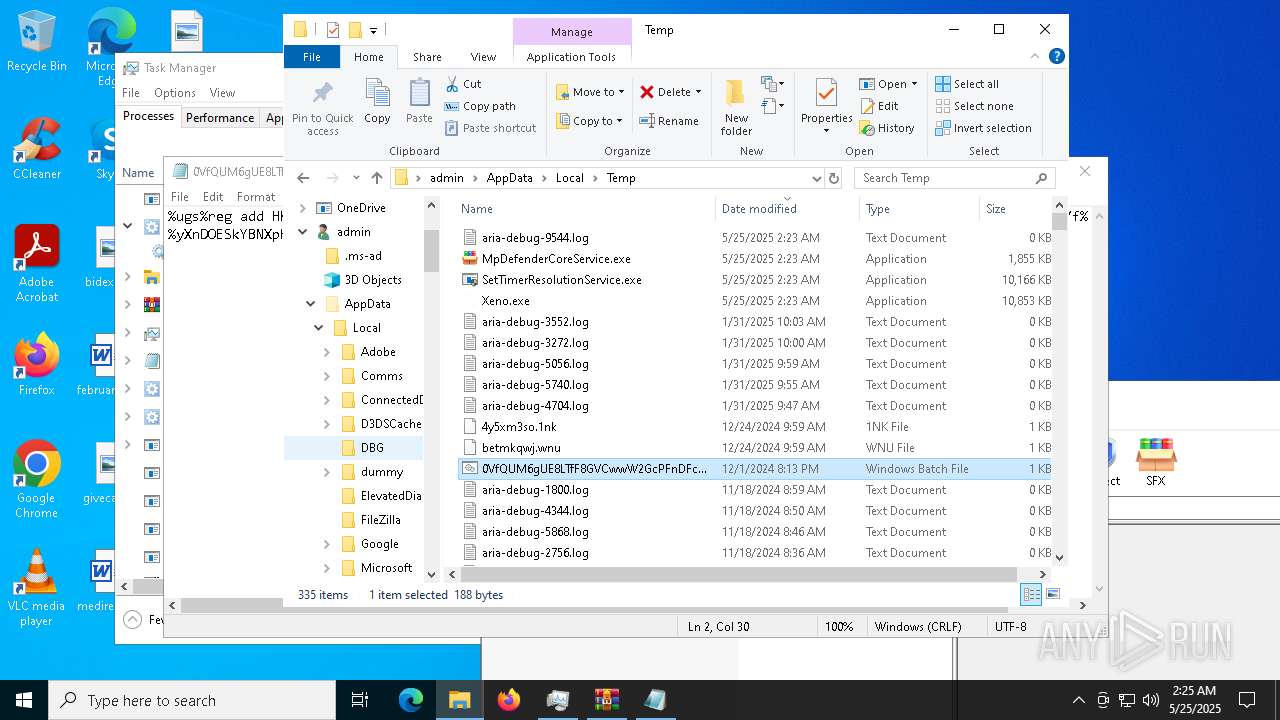
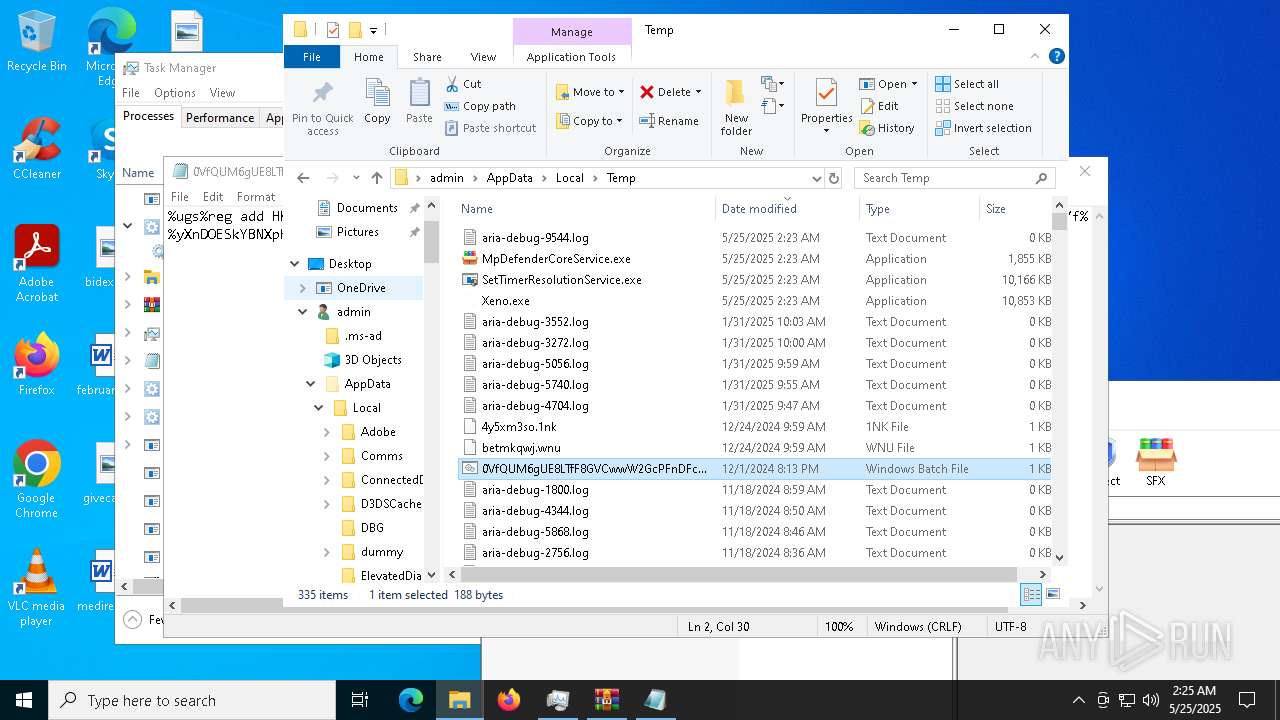
Create files in a temporary directory
- Xeno.exe (PID: 5024)
- cvtres.exe (PID: 7276)
- comwebFontMonitor.exe (PID: 5416)
- cvtres.exe (PID: 7352)
- cvtres.exe (PID: 7572)
- cvtres.exe (PID: 7440)
- SetTimerResolutionService.exe (PID: 2892)
Process checks computer location settings
- Xeno.exe (PID: 5024)
- MpDefenderCoreService.exe (PID: 5968)
- comwebFontMonitor.exe (PID: 1696)
- comwebFontMonitor.exe (PID: 5416)
Drops encrypted VBS script (Microsoft Script Encoder)
- MpDefenderCoreService.exe (PID: 5968)
The sample compiled with english language support
- Xeno.exe (PID: 5024)
- comwebFontMonitor.exe (PID: 5416)
- SetTimerResolutionService.exe (PID: 2892)
Reads the machine GUID from the registry
- comwebFontMonitor.exe (PID: 1696)
- comwebFontMonitor.exe (PID: 5416)
- csc.exe (PID: 7188)
- csc.exe (PID: 7308)
- csc.exe (PID: 7384)
- csc.exe (PID: 7472)
Reads Environment values
- comwebFontMonitor.exe (PID: 1696)
- comwebFontMonitor.exe (PID: 5416)
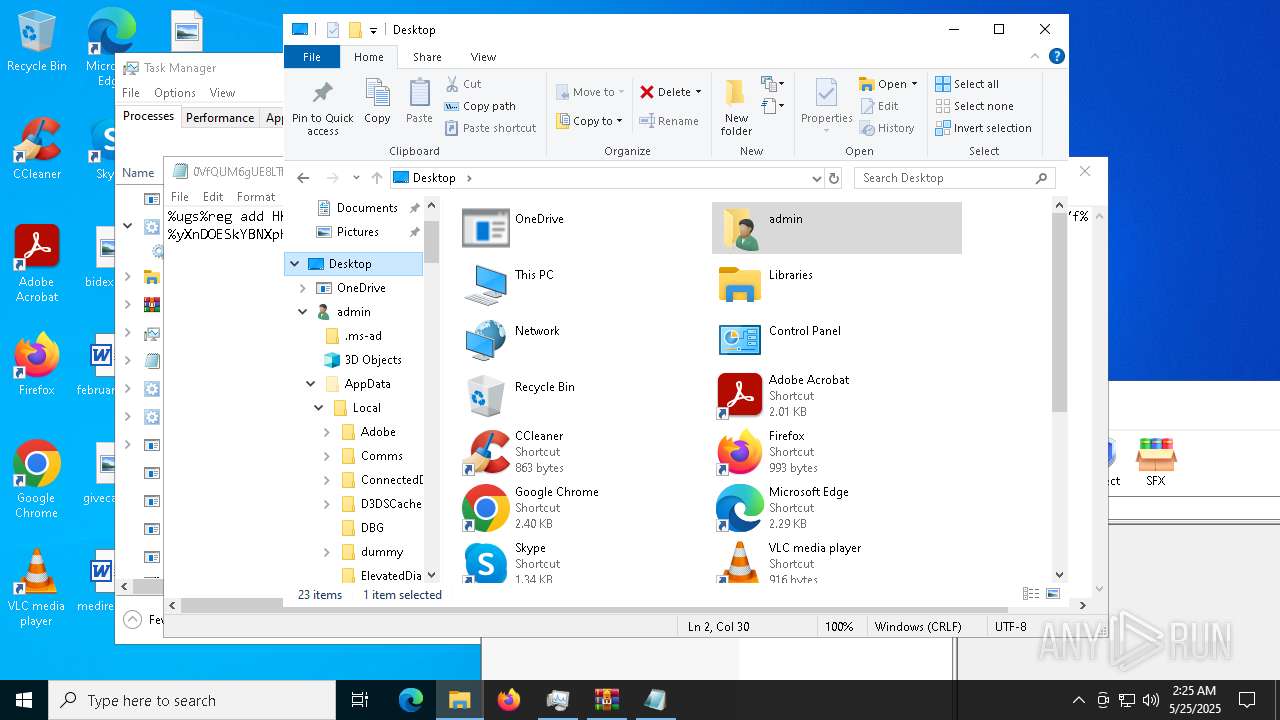
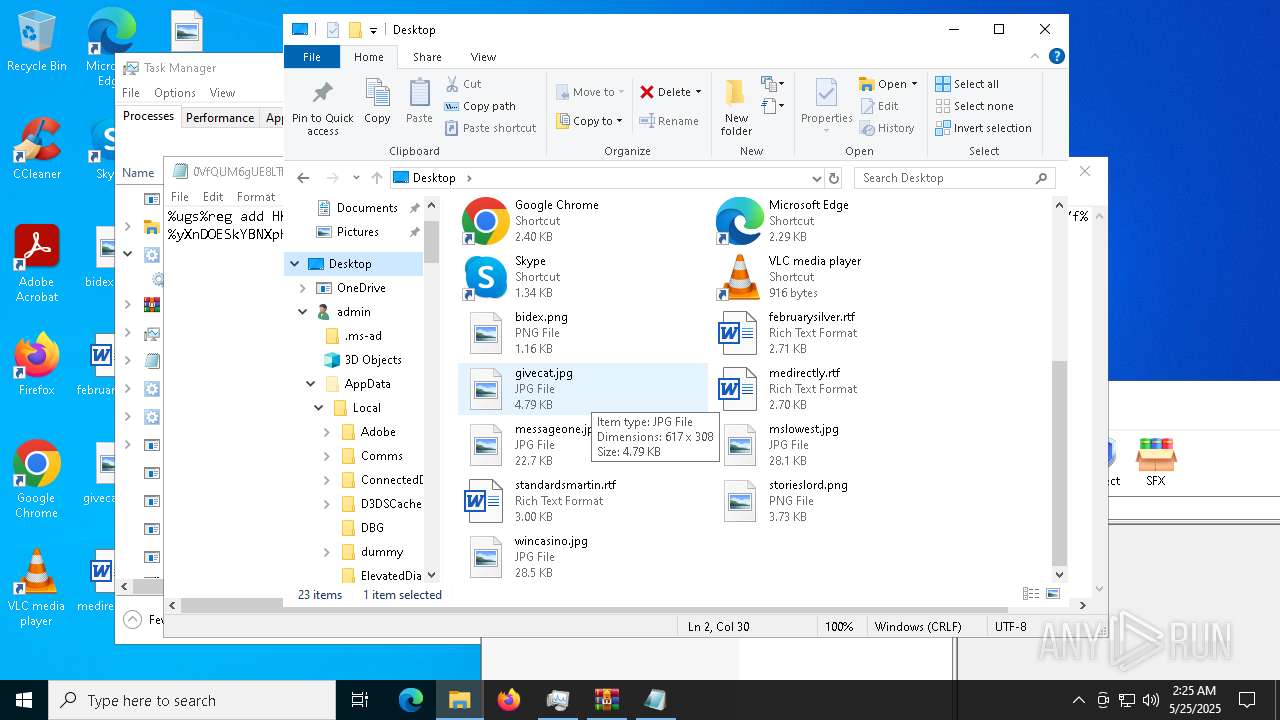
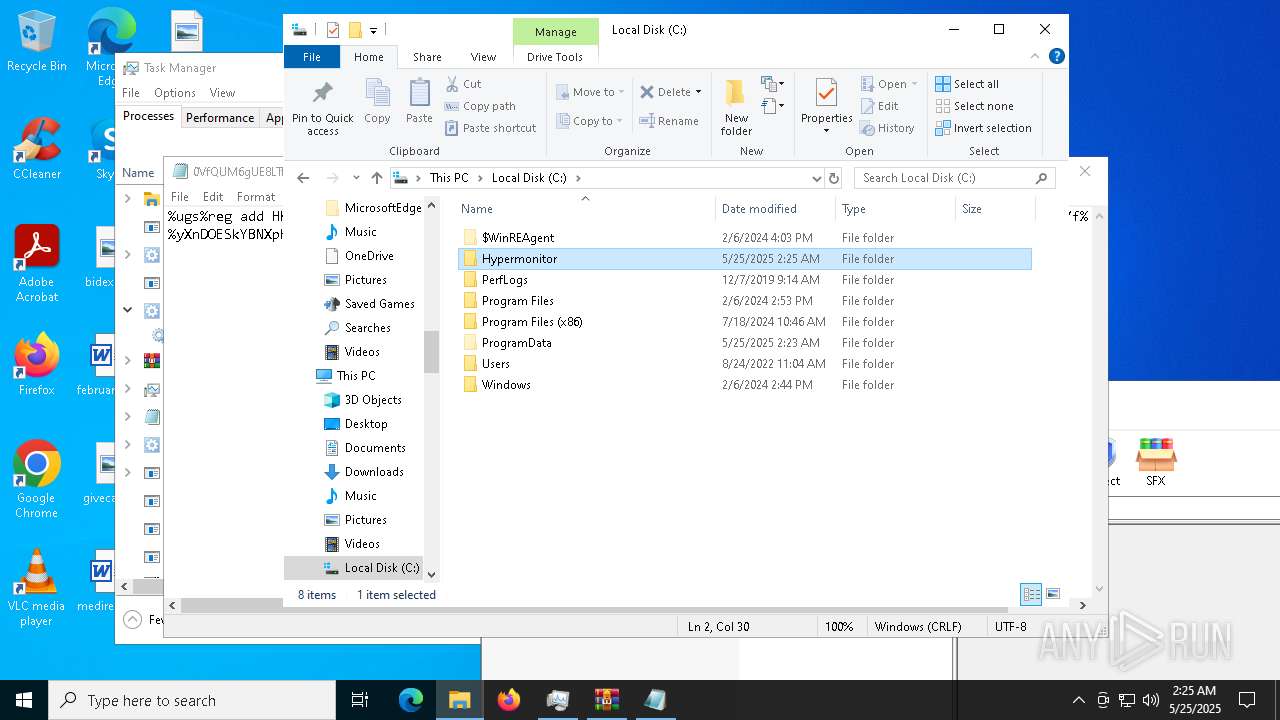
Creates files in the program directory
- comwebFontMonitor.exe (PID: 5416)
- csc.exe (PID: 7308)
- csc.exe (PID: 7384)
- csc.exe (PID: 7472)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 680)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 680)
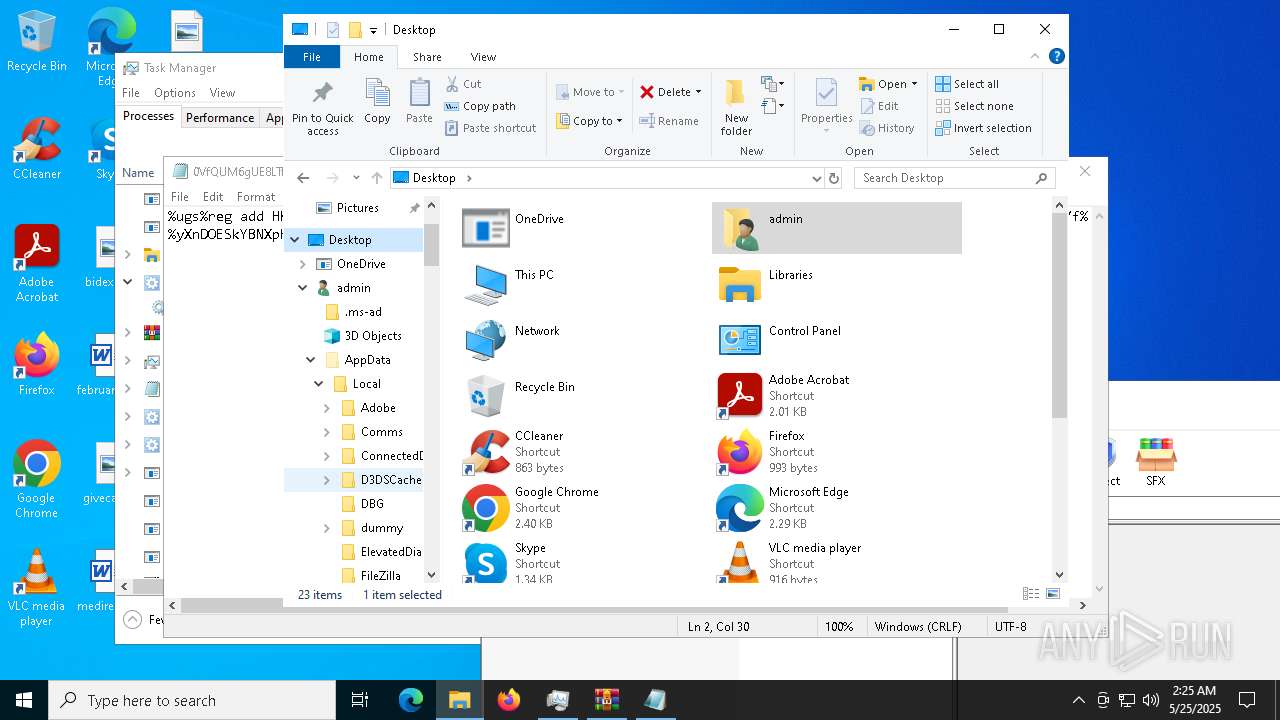
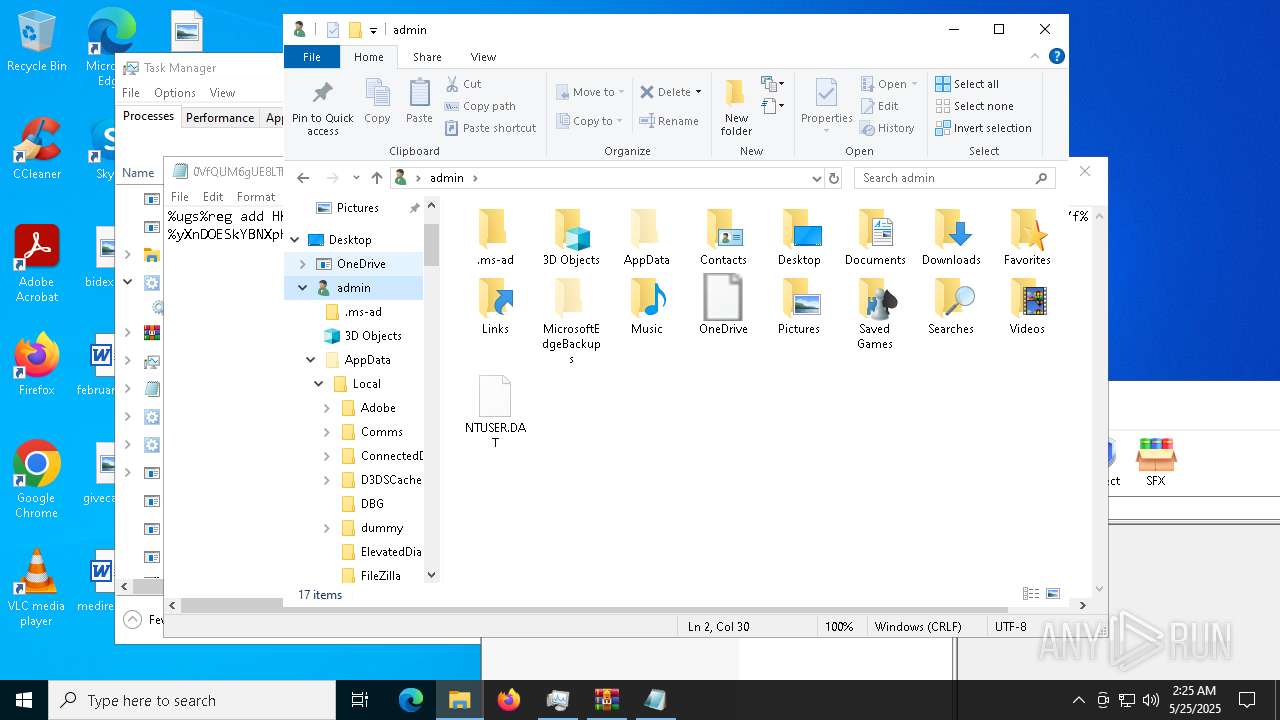
Creates files or folders in the user directory
- csc.exe (PID: 7188)
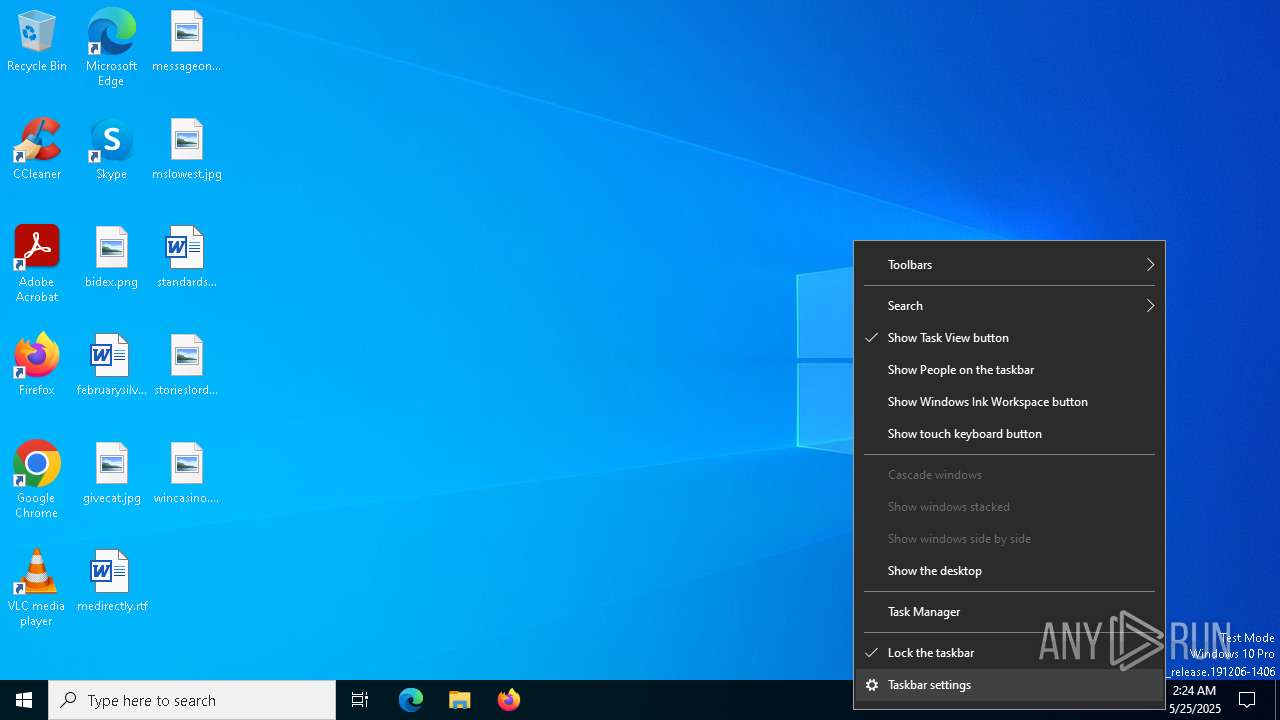
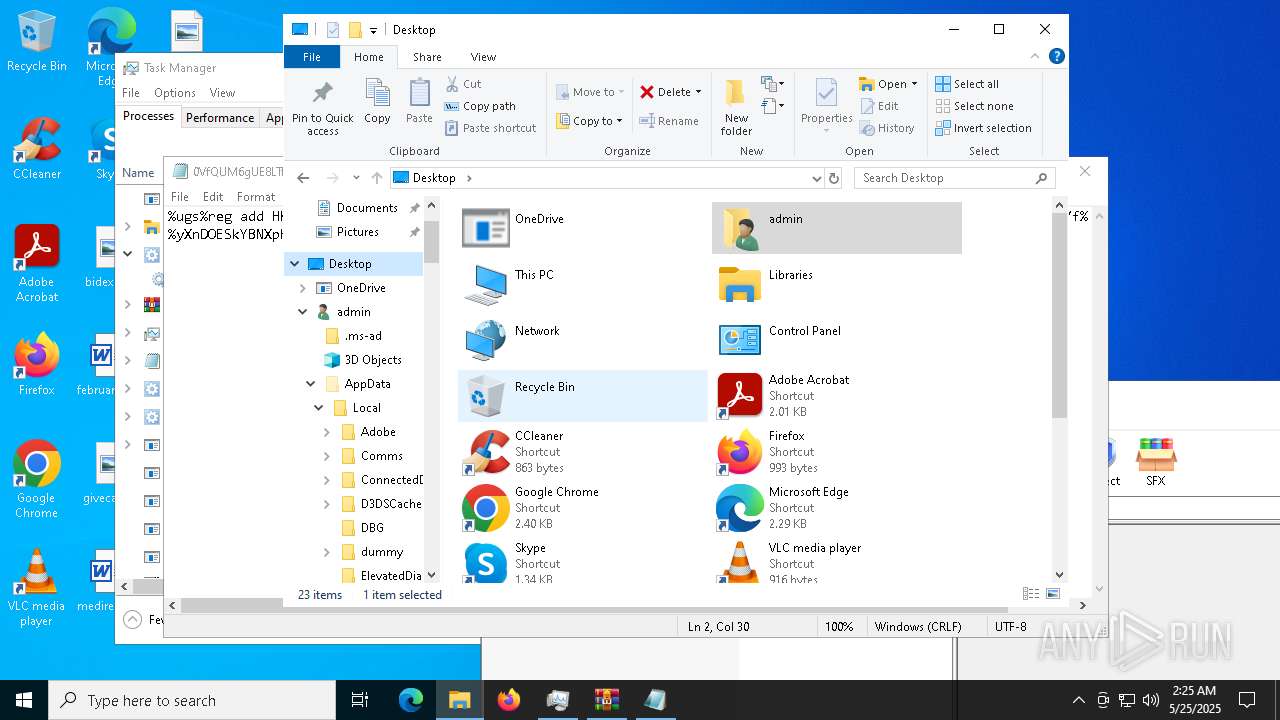
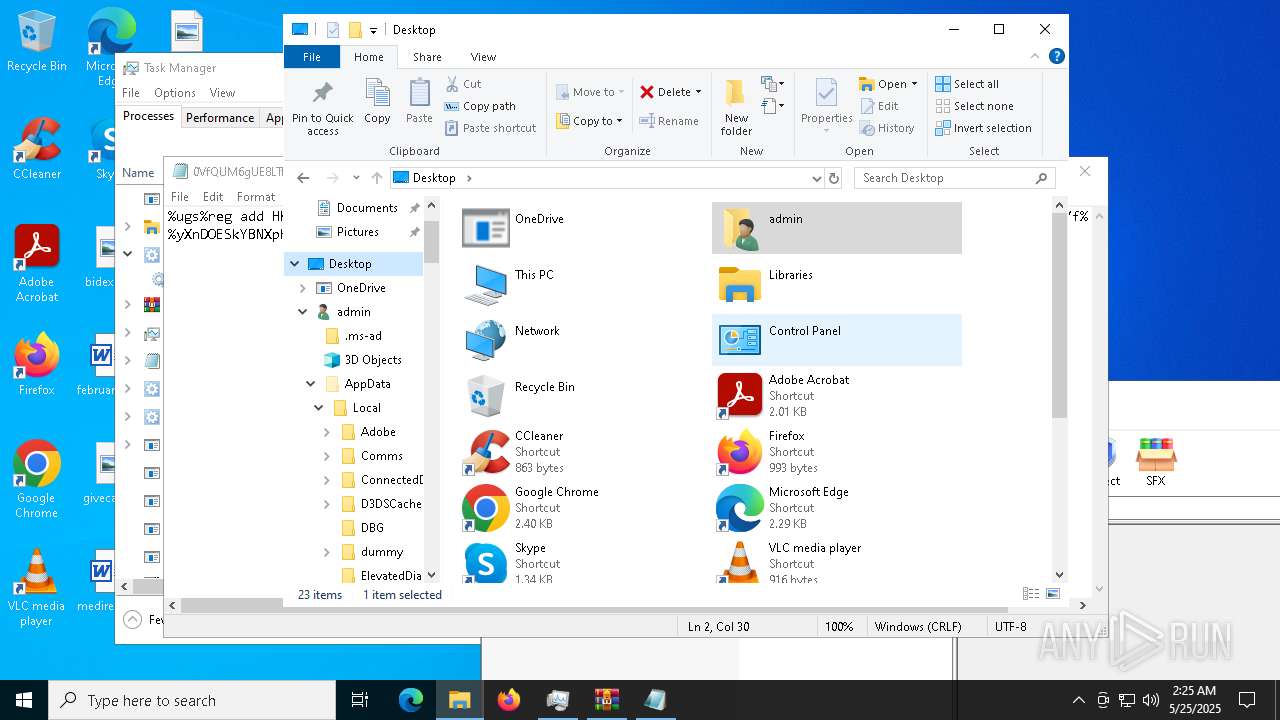
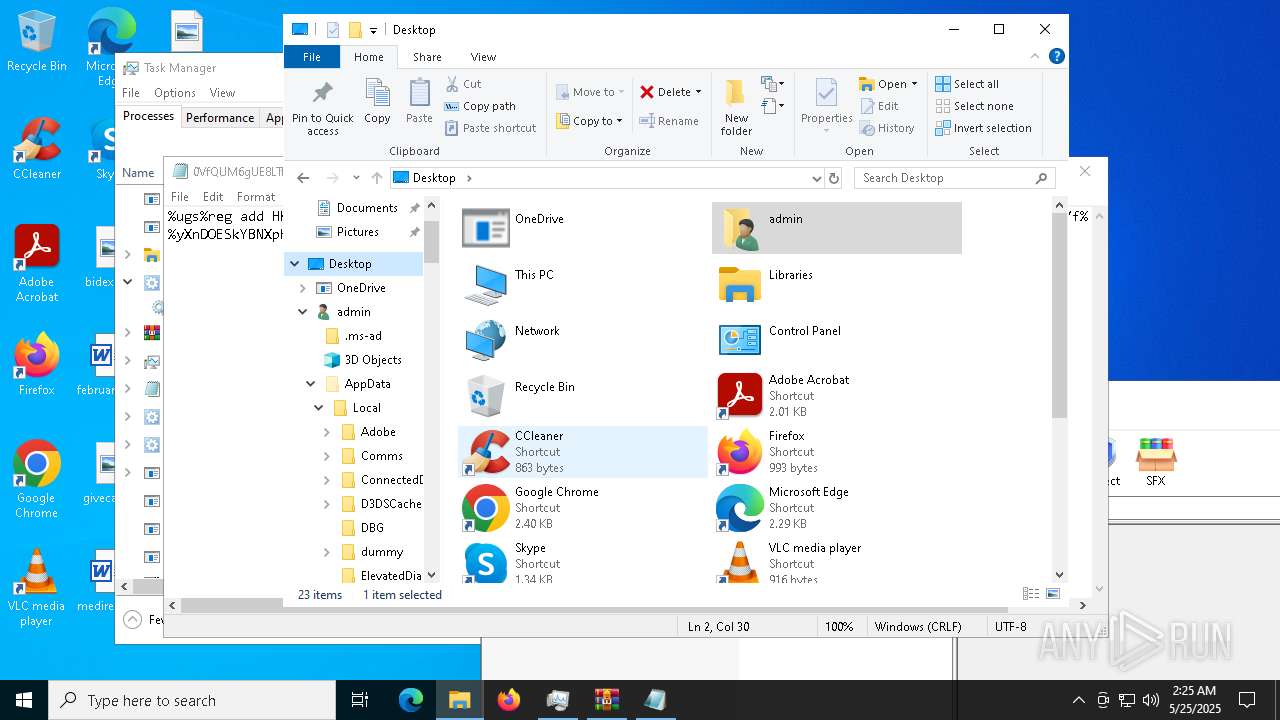
Manual execution by a user
- cmd.exe (PID: 7524)
- powershell.exe (PID: 680)
- cmd.exe (PID: 7772)
- powershell.exe (PID: 7816)
- dialer.exe (PID: 7796)
- schtasks.exe (PID: 8468)
- powershell.exe (PID: 6560)
- cmd.exe (PID: 8388)
- cmd.exe (PID: 8836)
- dialer.exe (PID: 2320)
- powershell.exe (PID: 9700)
- dialer.exe (PID: 7668)
- dialer.exe (PID: 4424)
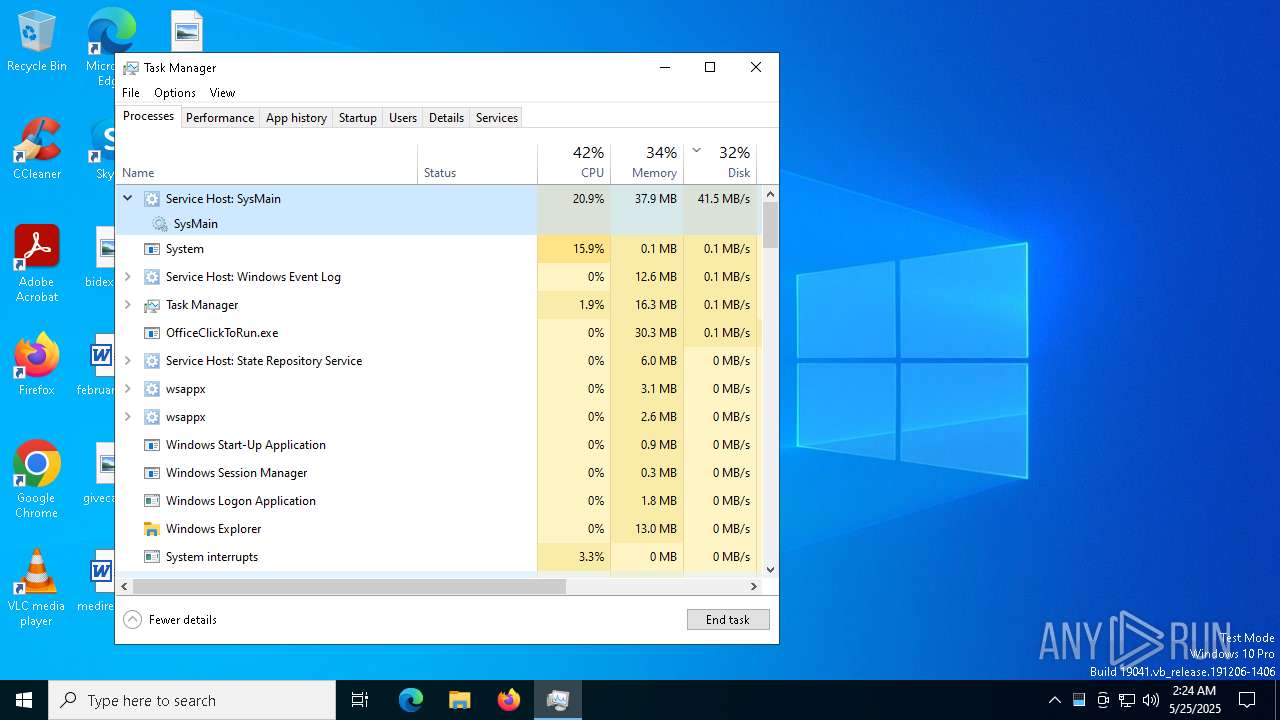
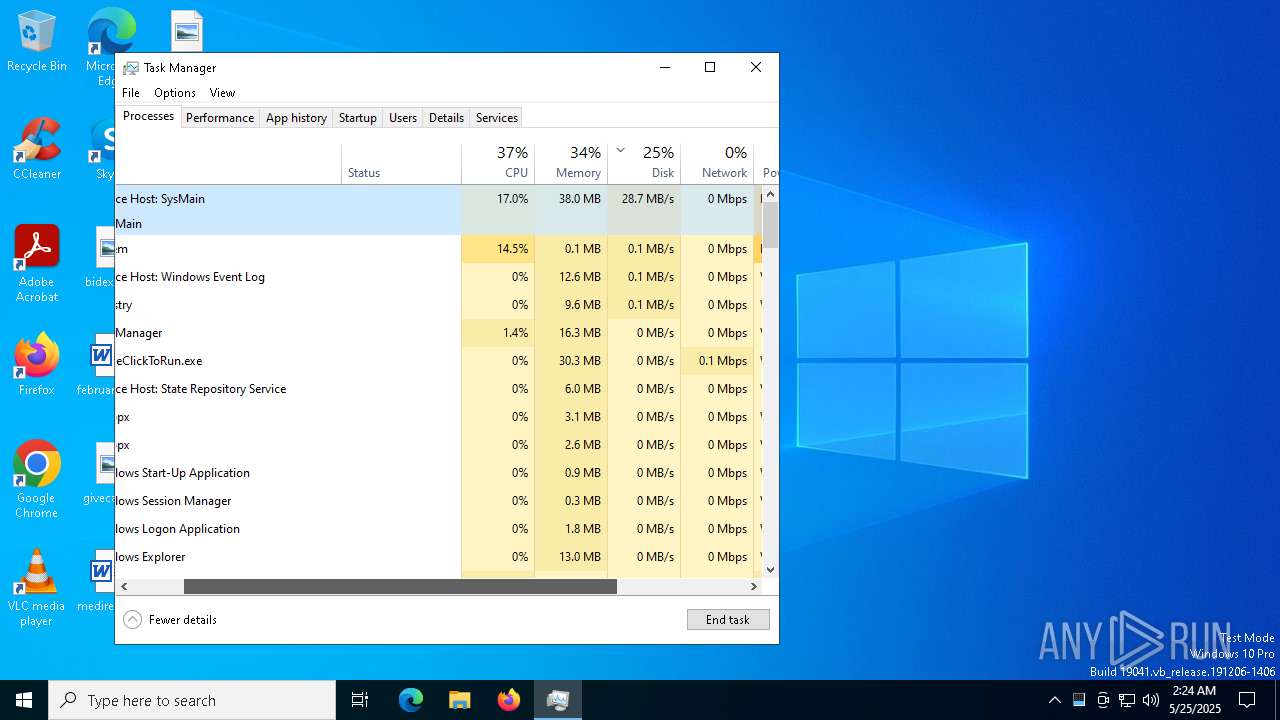
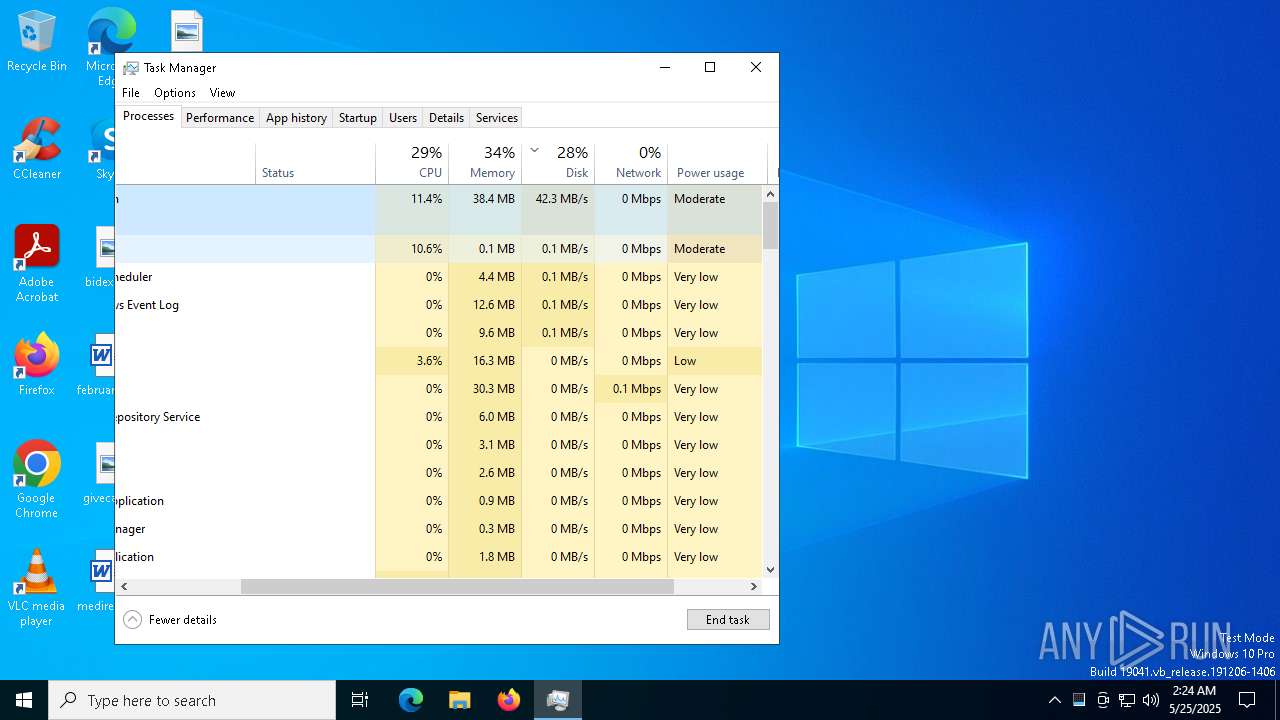
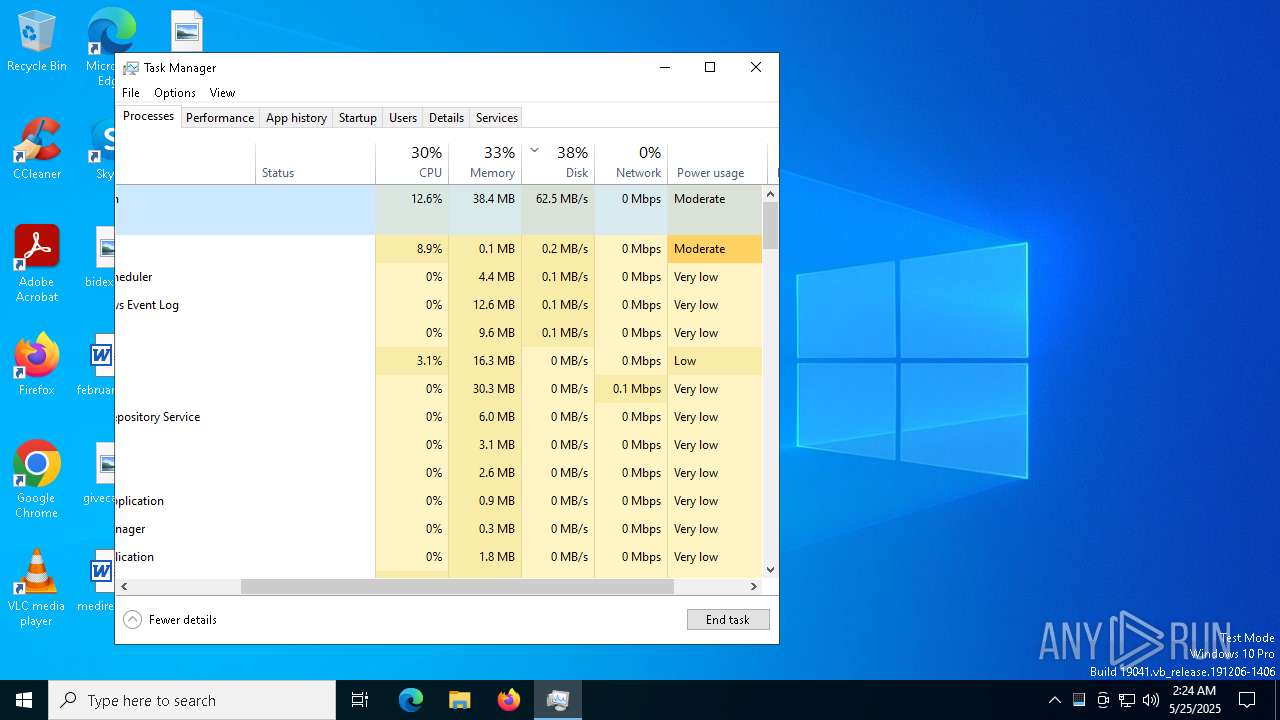
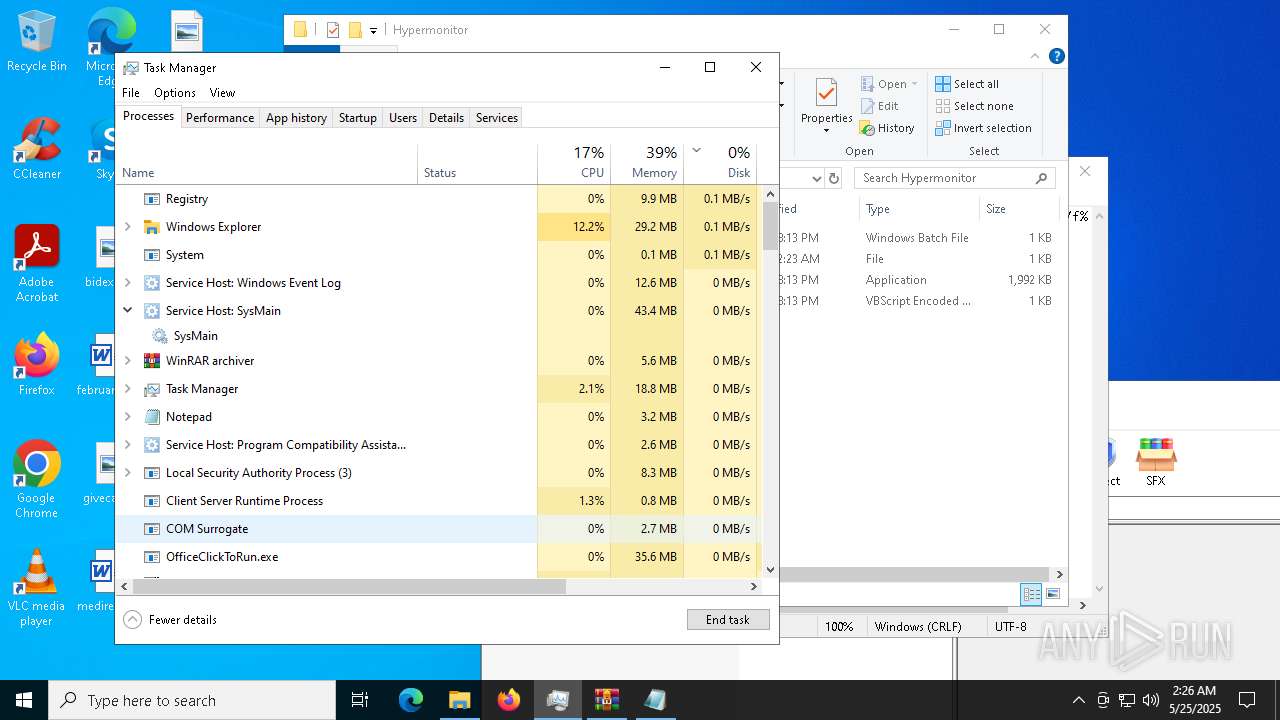
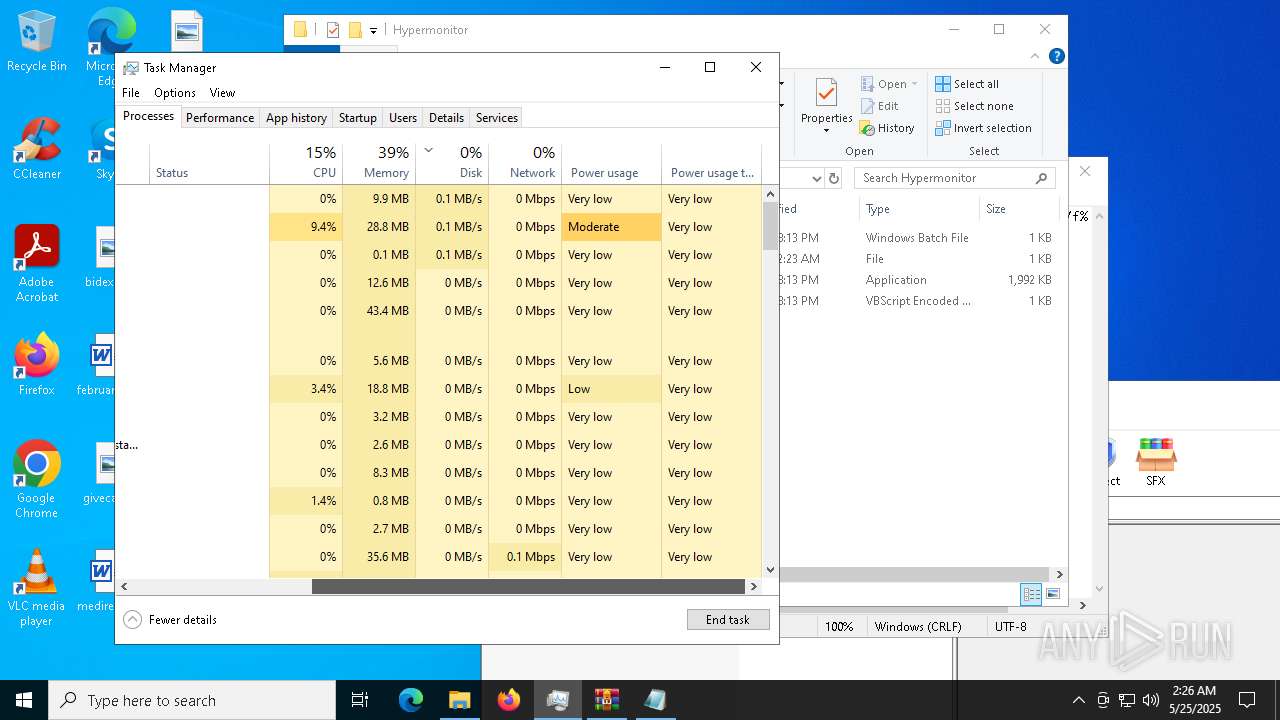
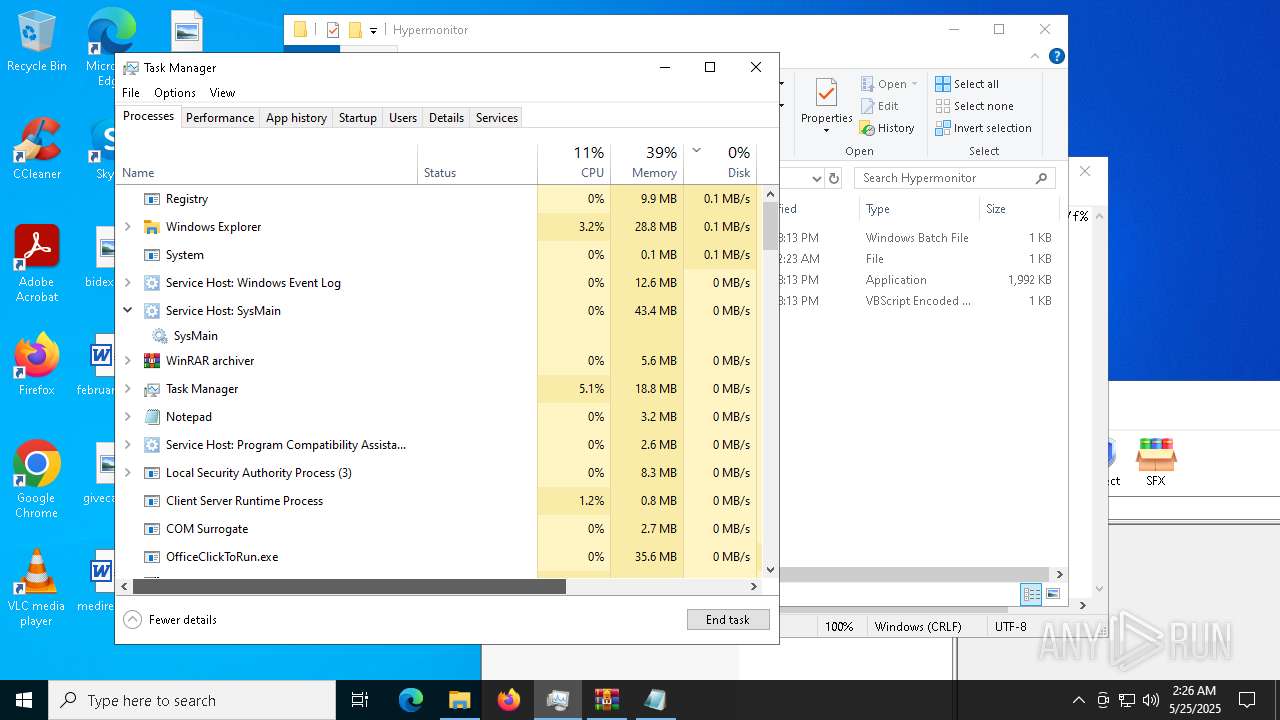
- Taskmgr.exe (PID: 8768)
- Taskmgr.exe (PID: 8584)
- notepad.exe (PID: 6060)
- WinRAR.exe (PID: 8784)
- notepad.exe (PID: 10156)
- MpDefenderCoreService.exe (PID: 7568)
- notepad.exe (PID: 6572)
Changes the display of characters in the console
- cmd.exe (PID: 7896)
The sample compiled with japanese language support
- updater.exe (PID: 10168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ 4.x (69.9) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (14.3) |
| .scr | | | Windows screen saver (6.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.4) |
| .exe | | | Win32 Executable (generic) (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:06:15 16:44:28+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 5.12 |
| CodeSize: | 3584 |
| InitializedDataSize: | 11108864 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ae1 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.9.0 |
| ProductVersionNumber: | 1.0.9.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Xeno - Executor UI https://github.com/Riz-ve/Xeno |
| CompanyName: | XenoUI |
| FileDescription: | XenoUI |
| FileVersion: | 1.0.9 |
| InternalName: | XenoUI.dll |
| LegalCopyright: | Rizve |
| OriginalFileName: | XenoUI.dll |
| ProductName: | Xeno |
| ProductVersion: | 1.0.9+87ae4f96f8a0927052c1120167982fb069afd1b4 |
| AssemblyVersion: | 1.0.9.0 |
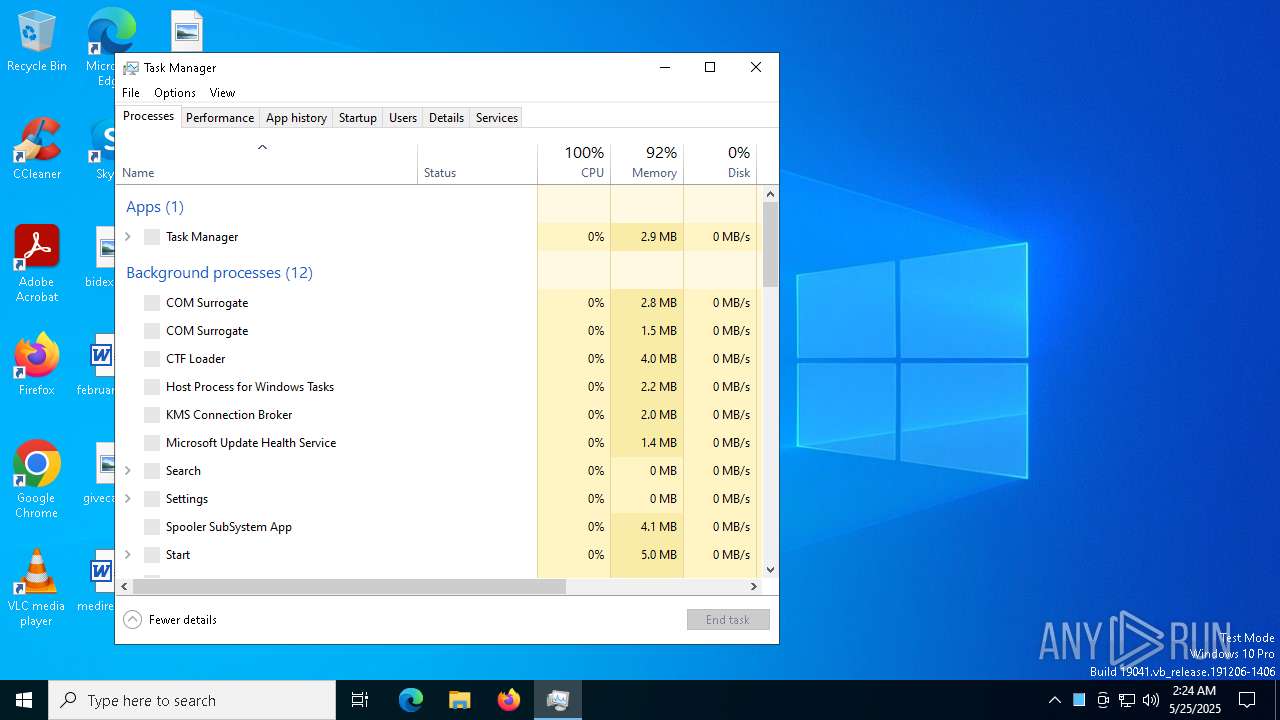
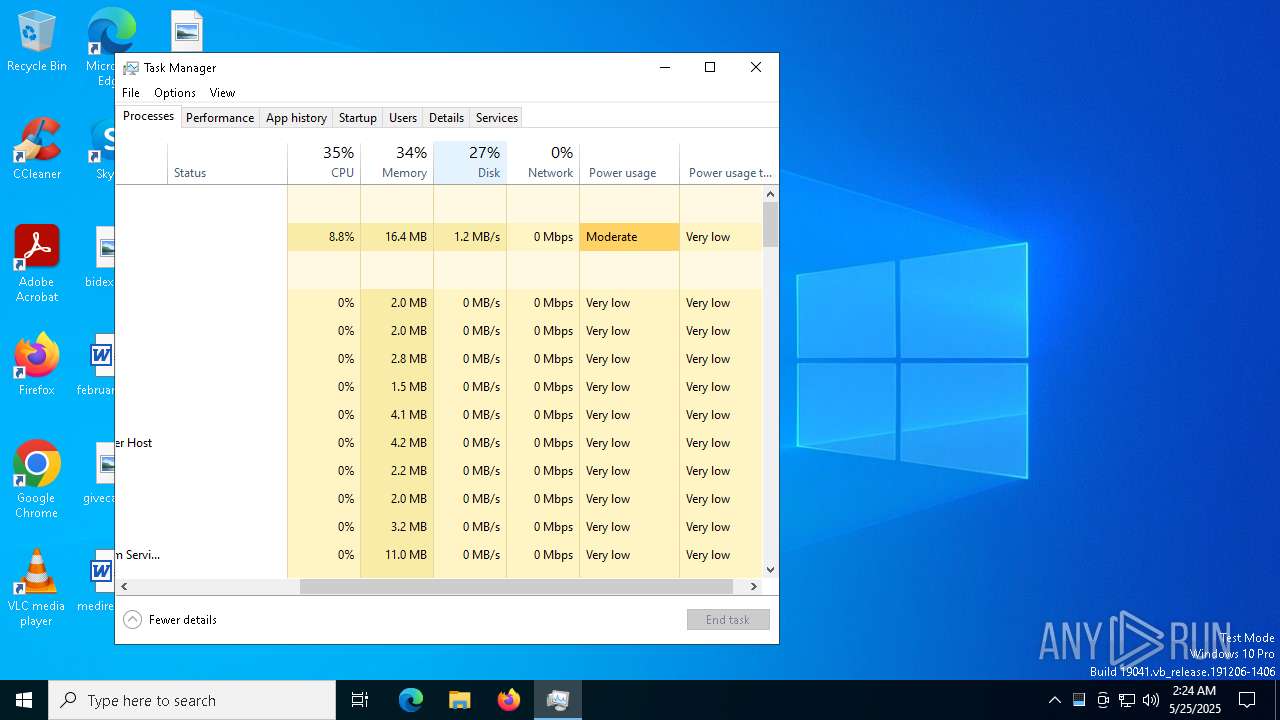
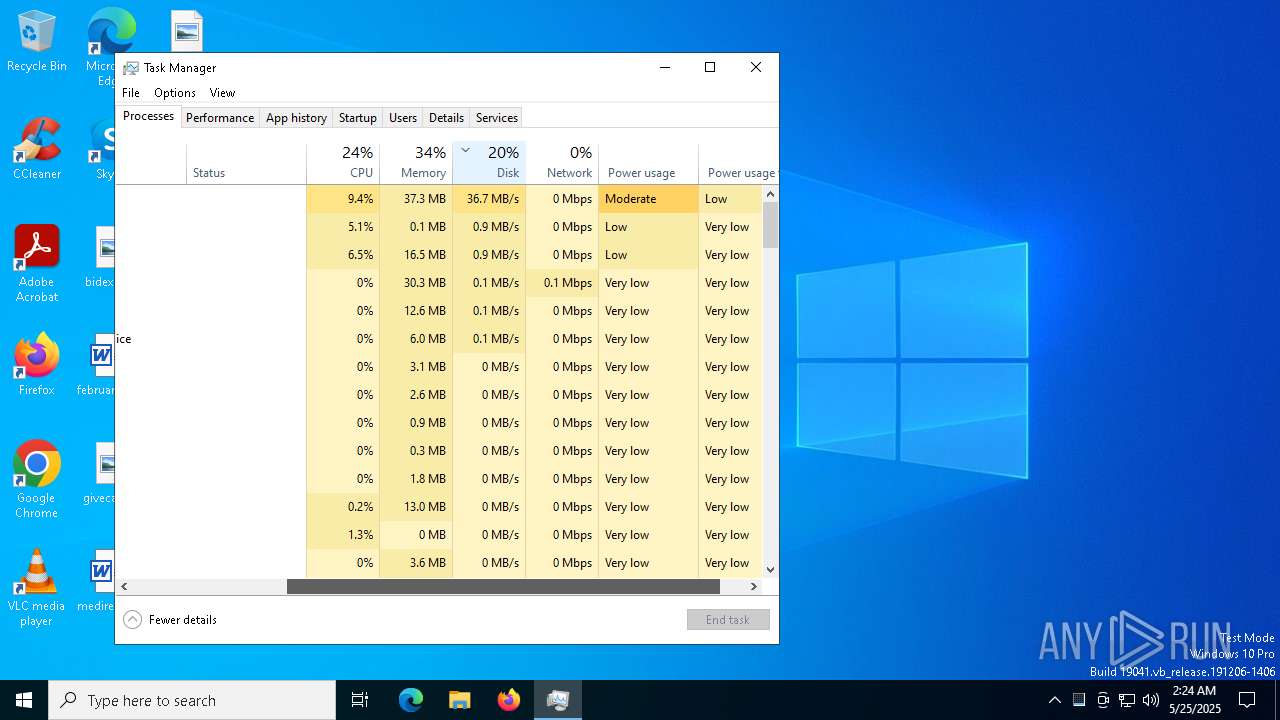
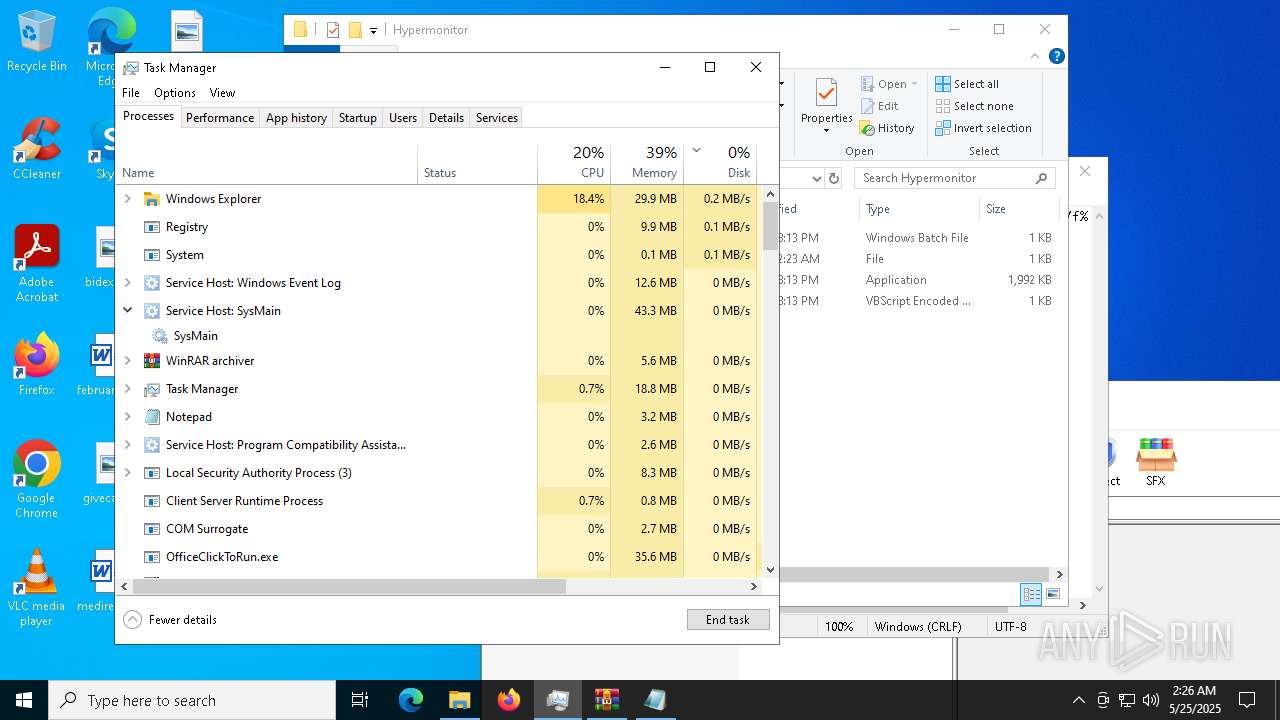
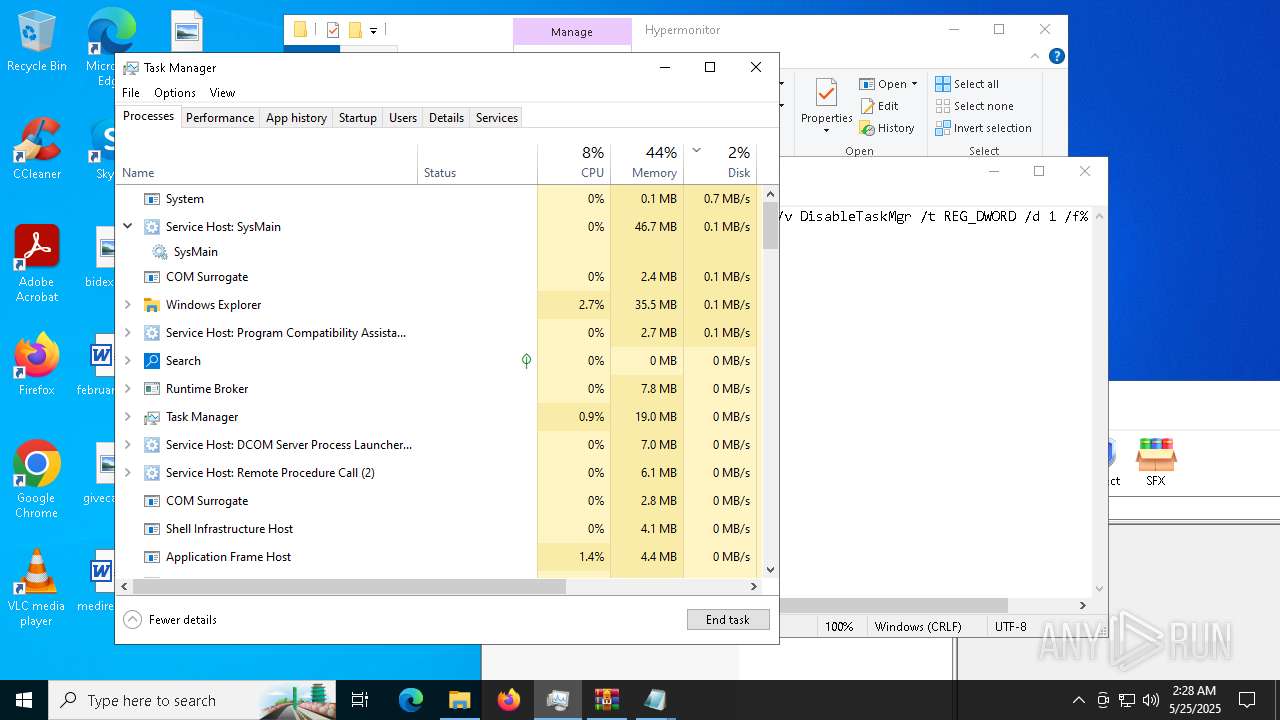
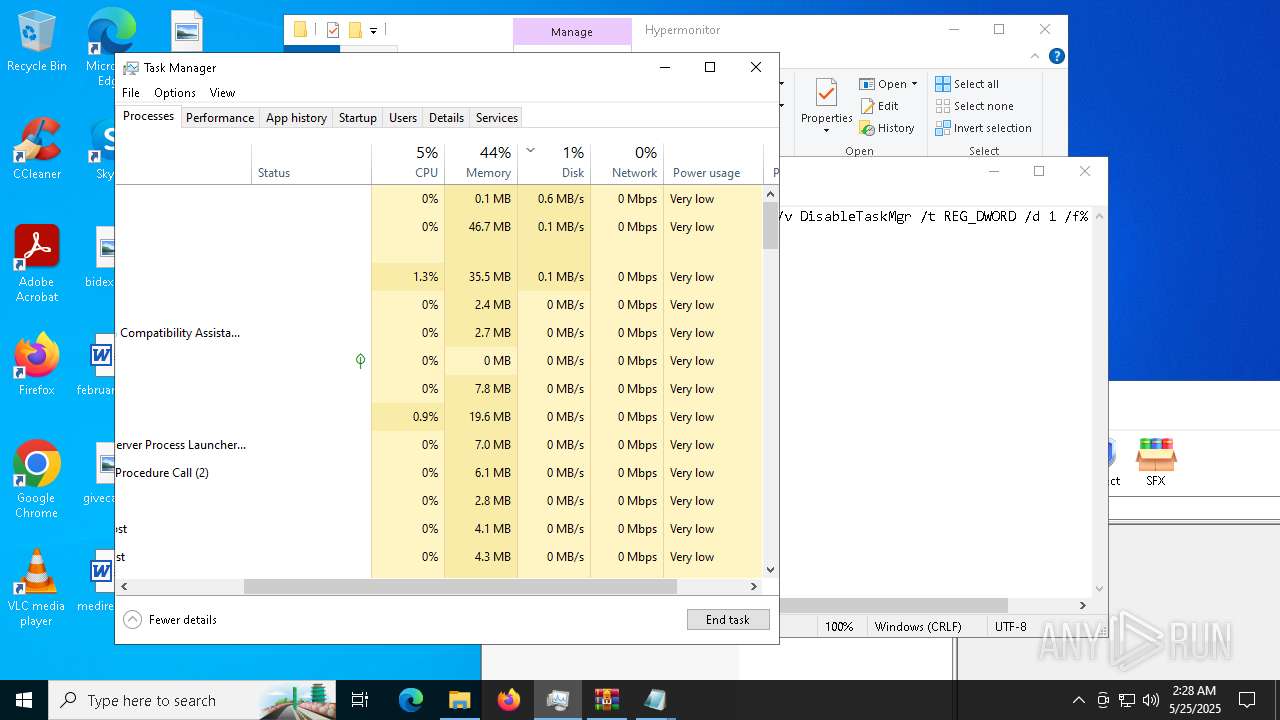
Total processes
283
Monitored processes
151
Malicious processes
14
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 672 | sc stop dosvc | C:\Windows\System32\sc.exe | — | cmd.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 680 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe Add-MpPreference -ExclusionPath @($env:UserProfile, $env:ProgramFiles) -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 896 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 928 | "C:\Windows\System32\sppui\taskhostw.exe" | C:\Windows\System32\sppui\taskhostw.exe | — | svchost.exe |
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.2.7.1277 | ||||
| 1188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 1696 | "C:\Hypermonitor/comwebFontMonitor.exe" | C:\Hypermonitor\comwebFontMonitor.exe | cmd.exe | |
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.2.7.1277 | ||||
| 2136 | schtasks.exe /create /tn "taskhostw" /sc ONLOGON /tr "'C:\Windows\System32\sppui\taskhostw.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | |
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 2236 | schtasks.exe /create /tn "taskhostwt" /sc MINUTE /mo 10 /tr "'C:\Windows\System32\sppui\taskhostw.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 2244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
40
Suspicious files
37
Text files
77
Unknown types
1
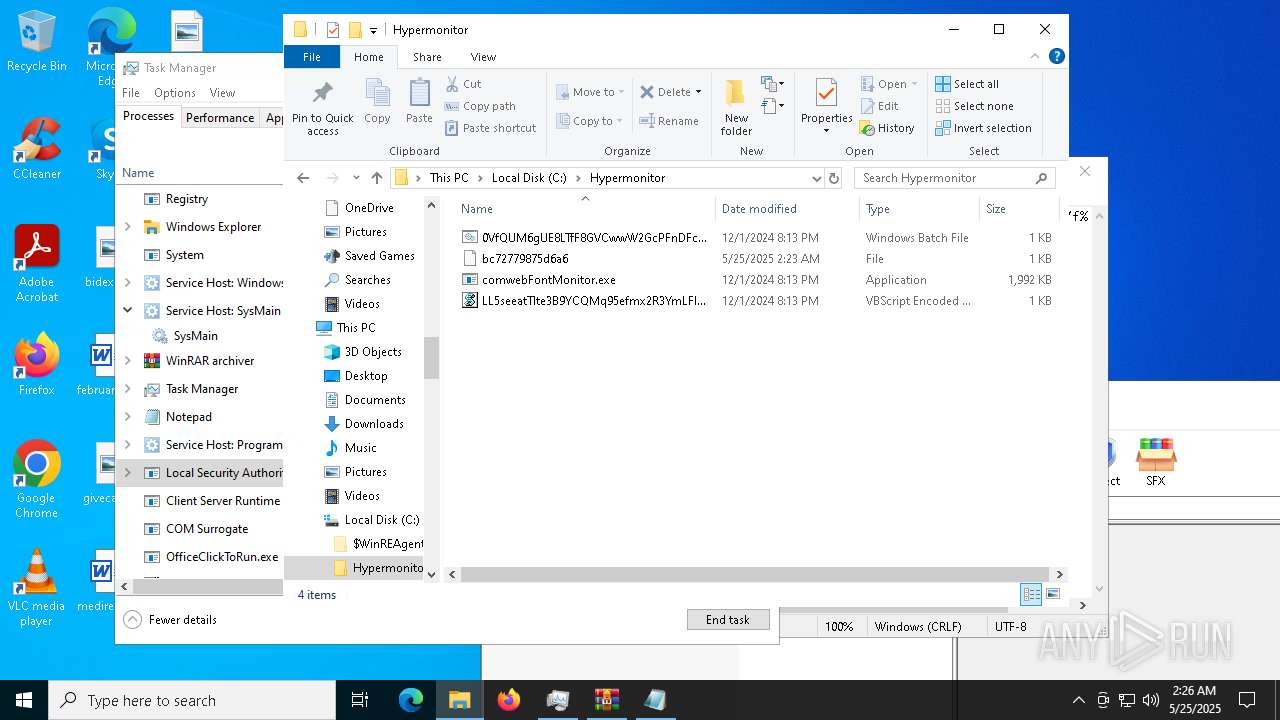
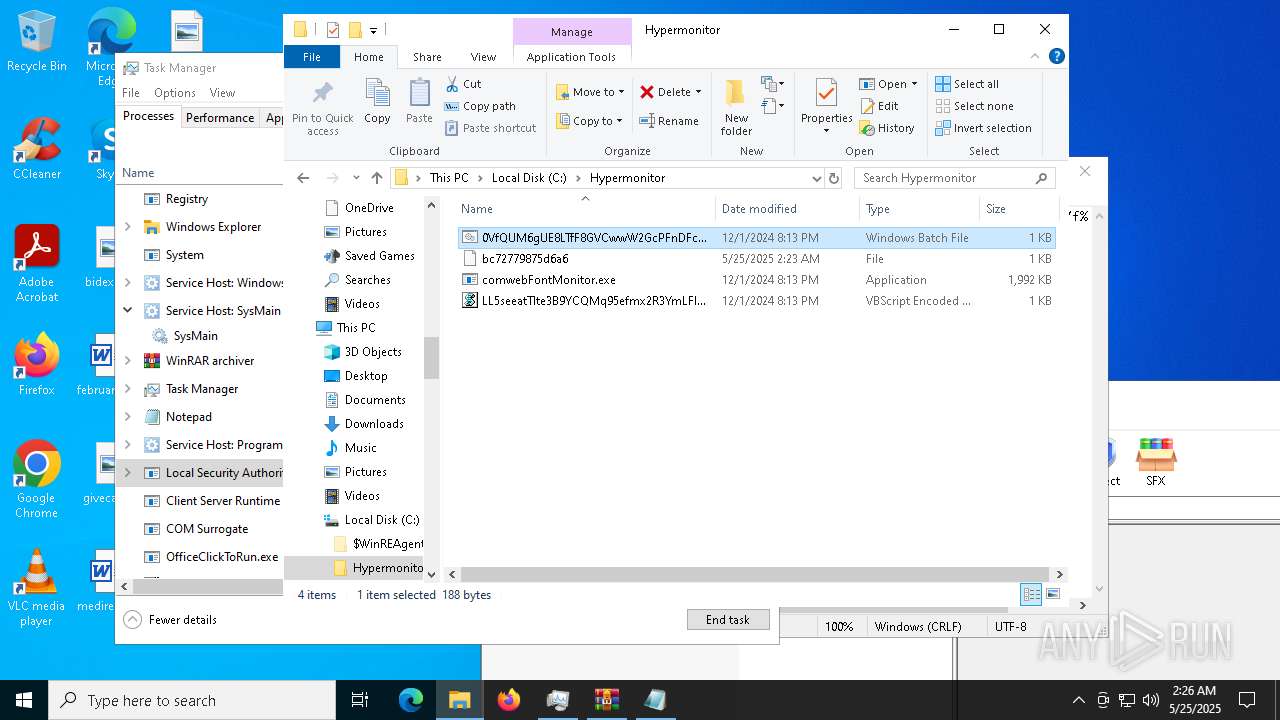
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5024 | Xeno.exe | C:\Users\admin\AppData\Local\Temp\MpDefenderCoreService.exe | executable | |
MD5:0461FFE7BD459338E588A58C7603308F | SHA256:9E91E2EE79C04872C4F235EAA085BFBA87DBFB68D1D047D086B08F277CA0F274 | |||
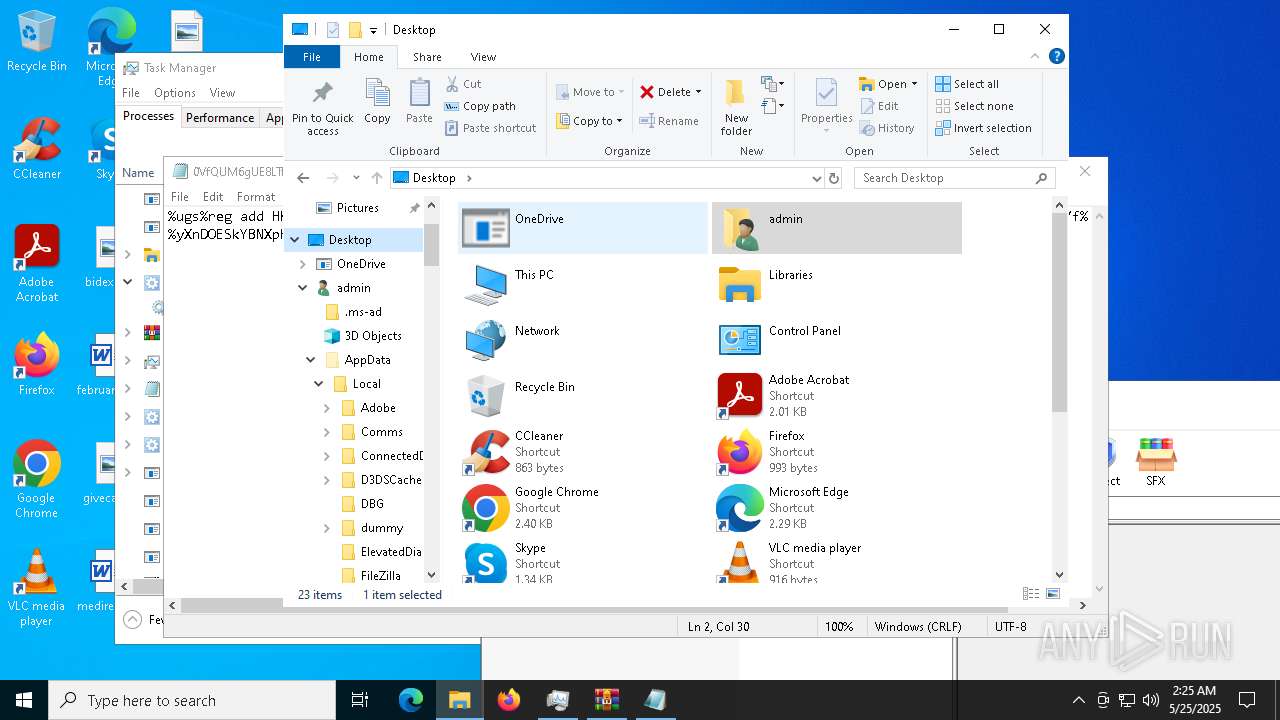
| 1696 | comwebFontMonitor.exe | C:\Users\admin\Desktop\bkHIFifo.log | executable | |
MD5:E84DCD8370FAC91DE71DEF8DCF09BFEC | SHA256:DD7AC164E789CAD96D30930EFE9BBA99698473EDEA38252C2C0EA44043FB1DB5 | |||
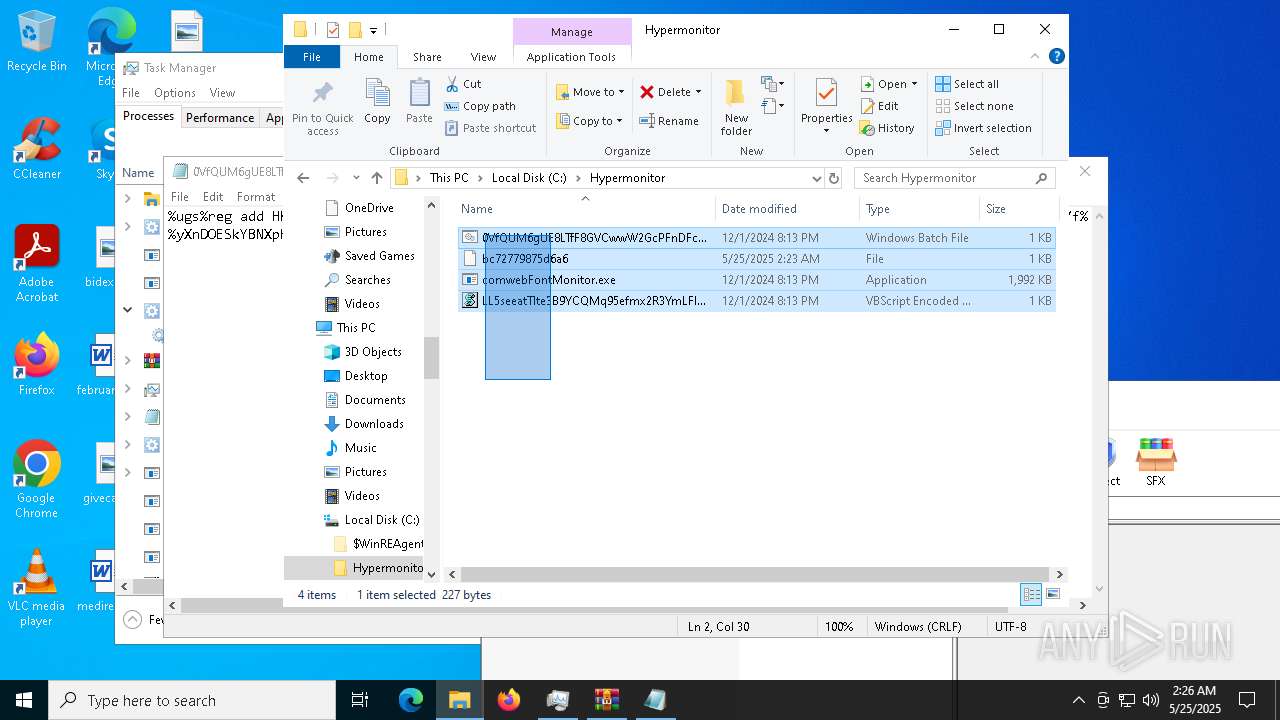
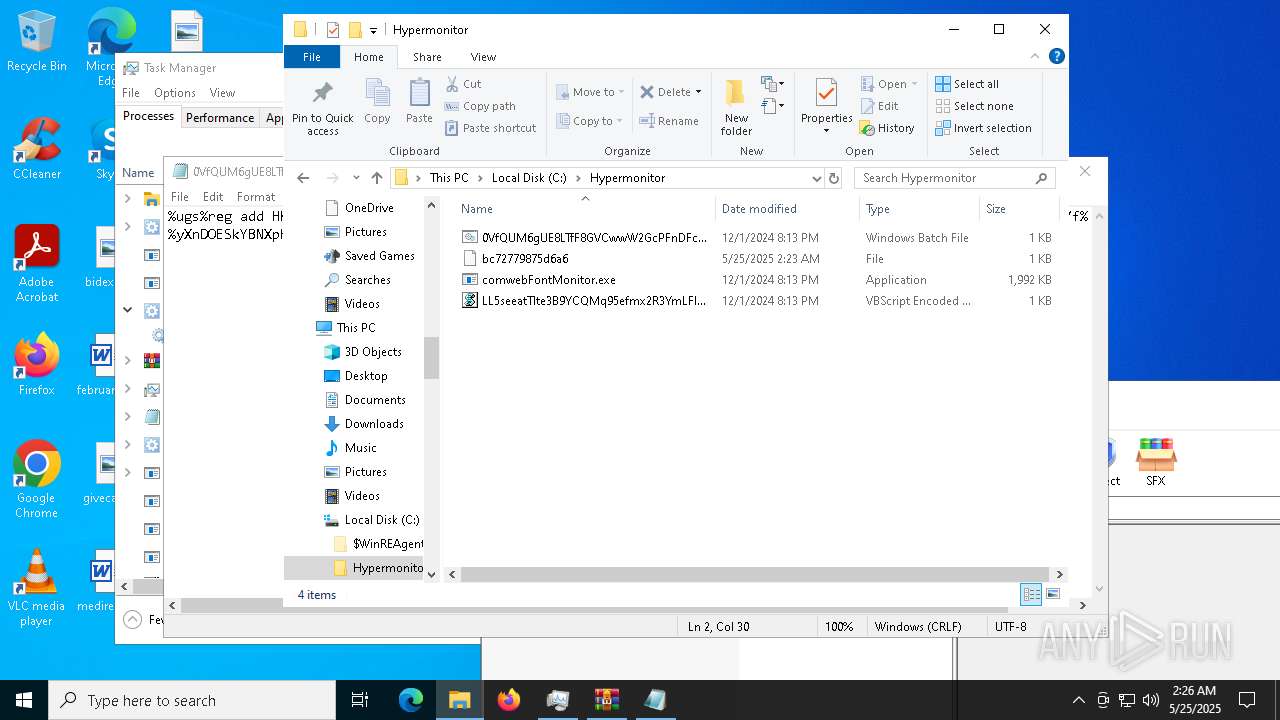
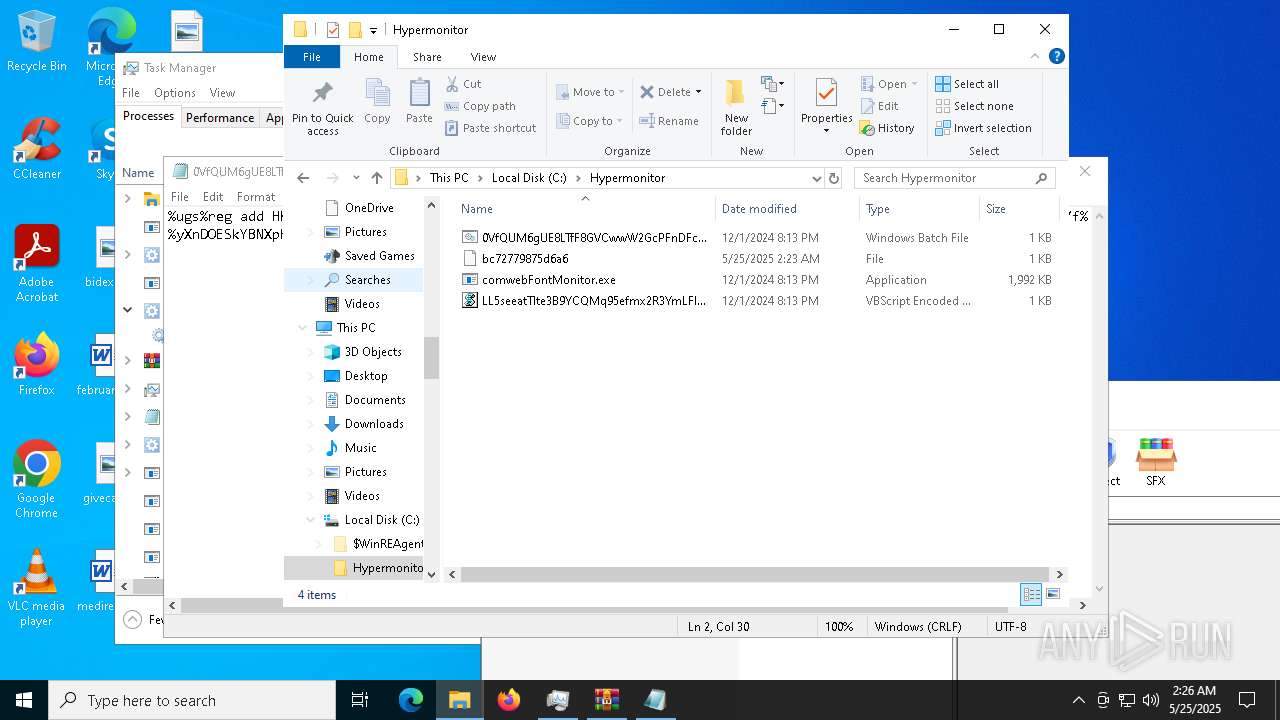
| 5968 | MpDefenderCoreService.exe | C:\Hypermonitor\LL5seeatTlte3B9YCQMq95efmx2R3YmLFIJLWG6vqF8oW.vbe | binary | |
MD5:7F5E8D0B1160ECE312F4B2C21FB997BD | SHA256:9FB10A883054DAE561E5ADEFE1AE01ED1990964C07E06673CEB69ED848ADF319 | |||
| 680 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_u5cpik5b.l5i.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1696 | comwebFontMonitor.exe | C:\Users\admin\Desktop\kTaYpKkW.log | executable | |
MD5:E9CE850DB4350471A62CC24ACB83E859 | SHA256:7C95D3B38114E7E4126CB63AADAF80085ED5461AB0868D2365DD6A18C946EA3A | |||
| 680 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0j4mbuto.5tf.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1696 | comwebFontMonitor.exe | C:\Users\admin\Desktop\SGySVoPH.log | executable | |
MD5:2D6975FD1CC3774916D8FF75C449EE7B | SHA256:75CE6EB6CDDD67D47FB7C5782F45FDC497232F87A883650BA98679F92708A986 | |||
| 1696 | comwebFontMonitor.exe | C:\Users\admin\Desktop\SOilzYqM.log | executable | |
MD5:D8BF2A0481C0A17A634D066A711C12E9 | SHA256:2B93377EA087225820A9F8E4F331005A0C600D557242366F06E0C1EAE003D669 | |||
| 1696 | comwebFontMonitor.exe | C:\Users\admin\Desktop\TLJtVYFH.log | executable | |
MD5:BBDE7073BAAC996447F749992D65FFBA | SHA256:1FAE639DF1C497A54C9F42A8366EDAE3C0A6FEB4EB917ECAD9323EF8D87393E8 | |||
| 5416 | comwebFontMonitor.exe | C:\Users\admin\Desktop\vQcOJIyB.log | executable | |
MD5:E9CE850DB4350471A62CC24ACB83E859 | SHA256:7C95D3B38114E7E4126CB63AADAF80085ED5461AB0868D2365DD6A18C946EA3A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
138
TCP/UDP connections
47
DNS requests
24
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8472 | OfficeClickToRun.exe | POST | 200 | 104.21.64.1:80 | http://uffyaa.ru/Phpjavascript_Test.php | unknown | — | — | malicious |
8472 | OfficeClickToRun.exe | POST | 200 | 104.21.64.1:80 | http://uffyaa.ru/Phpjavascript_Test.php | unknown | — | — | malicious |
8472 | OfficeClickToRun.exe | POST | 200 | 104.21.64.1:80 | http://uffyaa.ru/Phpjavascript_Test.php | unknown | — | — | malicious |
8472 | OfficeClickToRun.exe | POST | 200 | 104.21.64.1:80 | http://uffyaa.ru/Phpjavascript_Test.php | unknown | — | — | malicious |
8472 | OfficeClickToRun.exe | POST | 200 | 104.21.64.1:80 | http://uffyaa.ru/Phpjavascript_Test.php | unknown | — | — | malicious |
8472 | OfficeClickToRun.exe | POST | 200 | 104.21.64.1:80 | http://uffyaa.ru/Phpjavascript_Test.php | unknown | — | — | malicious |
8472 | OfficeClickToRun.exe | POST | 200 | 104.21.64.1:80 | http://uffyaa.ru/Phpjavascript_Test.php | unknown | — | — | malicious |
8472 | OfficeClickToRun.exe | POST | 200 | 104.21.64.1:80 | http://uffyaa.ru/Phpjavascript_Test.php | unknown | — | — | malicious |
8472 | OfficeClickToRun.exe | POST | 200 | 104.21.64.1:80 | http://uffyaa.ru/Phpjavascript_Test.php | unknown | — | — | malicious |
8472 | OfficeClickToRun.exe | POST | 200 | 104.21.64.1:80 | http://uffyaa.ru/Phpjavascript_Test.php | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5796 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6540 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
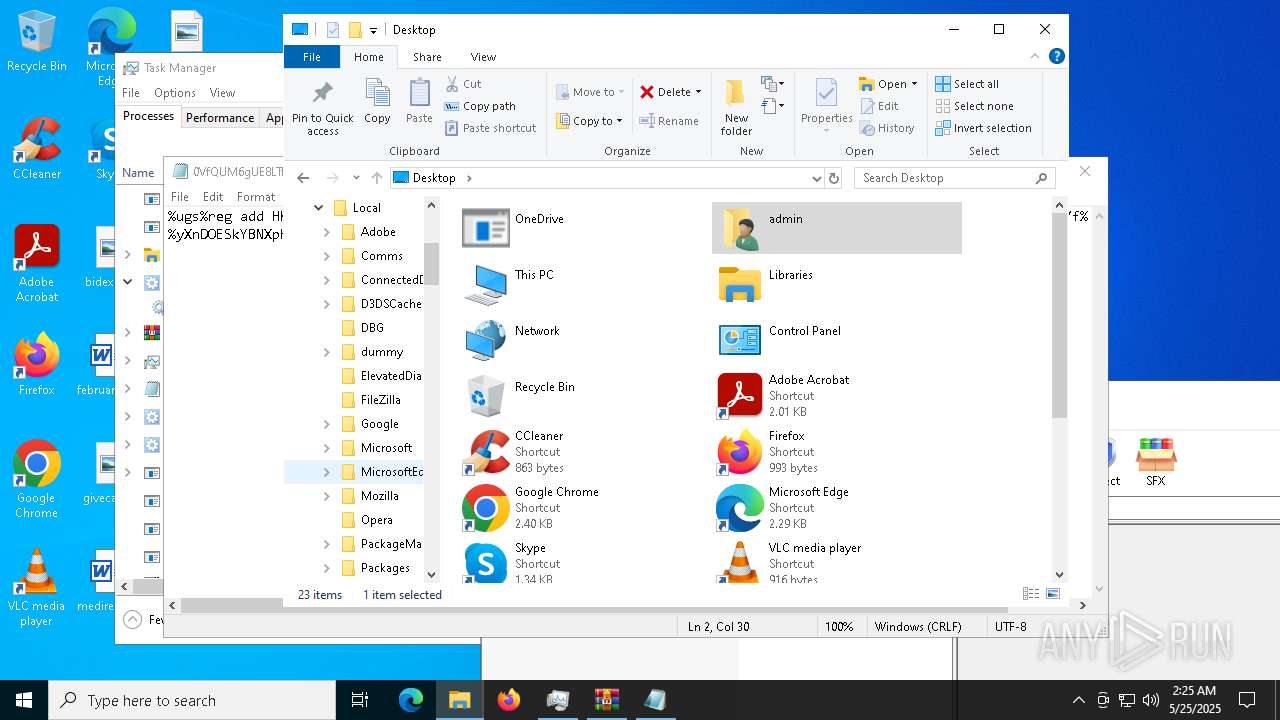
5496 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
9244 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
9244 | SIHClient.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
licensing.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER CoinMiner Domain in DNS Lookup (pool .hashvault .pro) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
8472 | OfficeClickToRun.exe | A Network Trojan was detected | REMOTE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
8472 | OfficeClickToRun.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] DarkCrystal Rat Check-in (POST) |