| download: | terms |
| Full analysis: | https://app.any.run/tasks/96688481-39a2-4ef1-bdac-5a2256d93f7a |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 11:32:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | 7351C840F81D03E7285B410D77AC7758 |
| SHA1: | A3A24466A9007669C8649CB925C1F42073295929 |
| SHA256: | 01CBBDC977ECAD02933BE8F15B57C81ECE36F5E7136EFF989616CD5D46B913A5 |
| SSDEEP: | 1536:reE4eynvDYTa2W7flXB4eL2fCzbr2UdiUz70jD9H:reE4eynvyax7daQ2crxgD9H |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
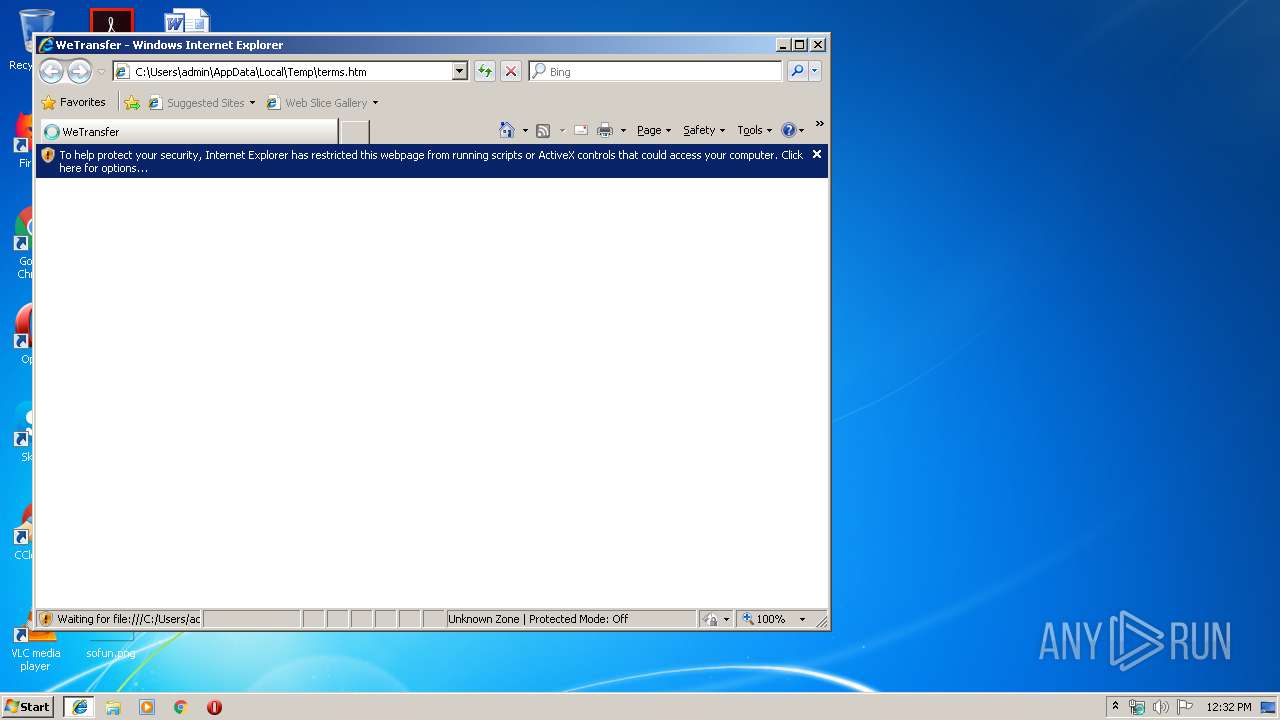
Changes internet zones settings
- iexplore.exe (PID: 2932)
Changes settings of System certificates
- iexplore.exe (PID: 3324)
Reads Internet Cache Settings
- iexplore.exe (PID: 2932)
- iexplore.exe (PID: 3324)
Reads internet explorer settings
- iexplore.exe (PID: 3324)
Reads settings of System Certificates
- iexplore.exe (PID: 3324)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3324)
Creates files in the user directory
- iexplore.exe (PID: 3324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| HTTPEquivXUACompatible: | IE=edge |
|---|---|
| viewport: | width=device-width, minimum-scale=1, initial-scale=1, user-scalable=no |
| pinterest: | nopin |
| referrer: | origin |
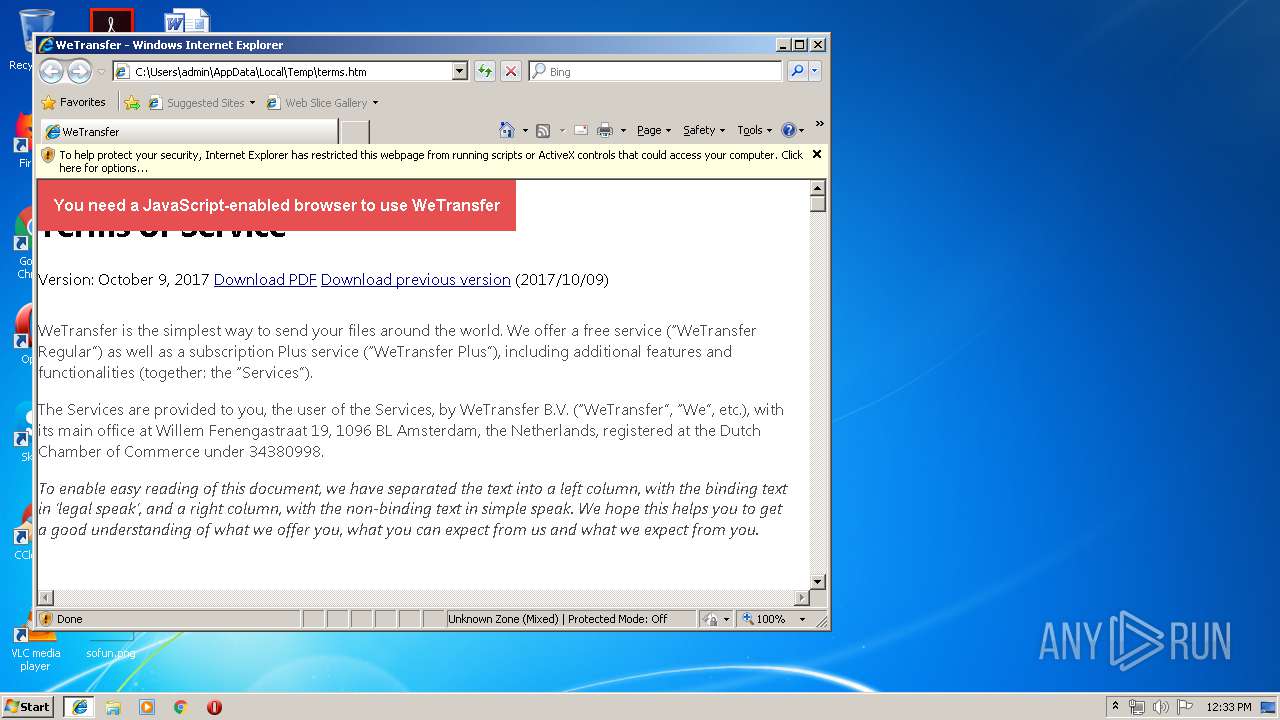
| Description: | WeTransfer is the simplest way to send your files around the world. Share large files up to 2GB for free. |
| Author: | WeTransfer |
| applicationName: | WeTransfer |
| csrfParam: | authenticity_token |
| csrfToken: | OiZ+APz75lxOMV/sCU+pfm8BIc4Fm+zAwPj+7IAfA5LG5IKj4lg3Kce3nuMJxLaI1ofdNmH3/BT5h2I8k855FQ== |
| Title: | WeTransfer |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
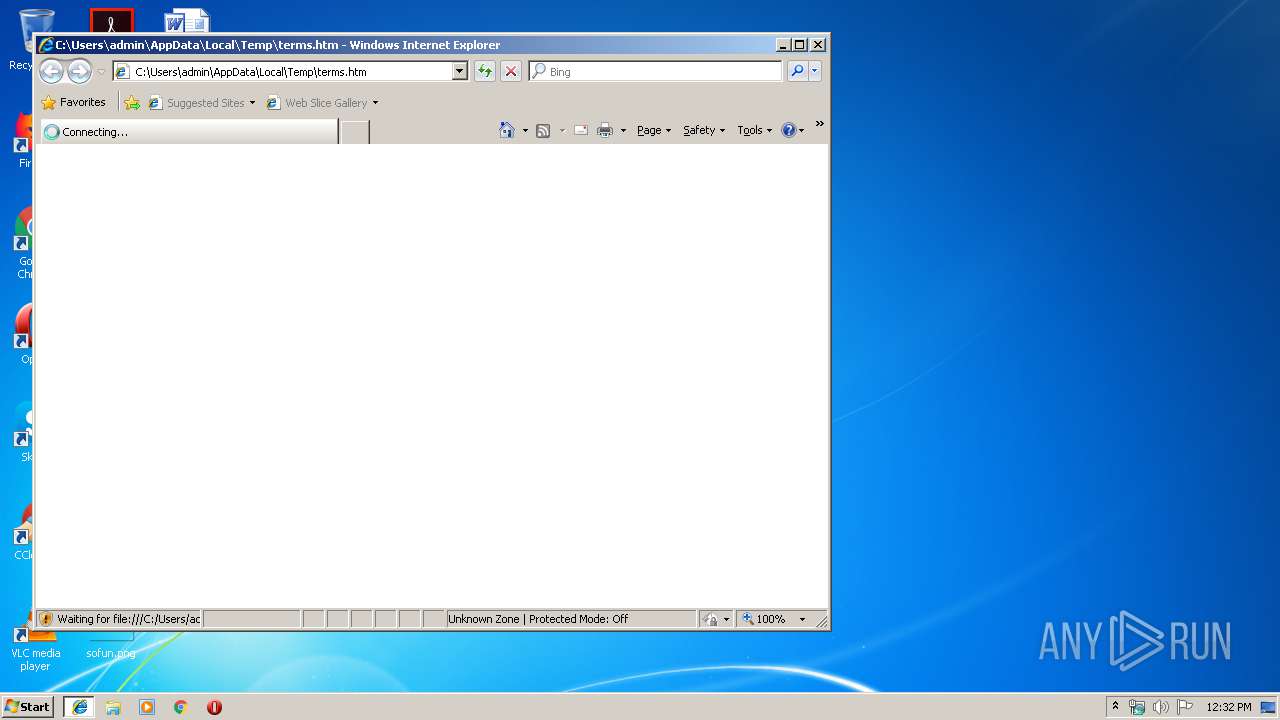
| 2932 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\terms.htm | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3324 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2932 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
429
Read events
339
Write events
83
Delete events
7
Modification events
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {F3A2564F-7AF2-11E9-B3B3-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070500010014000B0020001F000302 | |||
Executable files
0
Suspicious files
9
Text files
14
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabEF7F.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarEF80.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabEF90.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarEF91.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabEFA2.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarEFA3.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabF021.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarF022.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
18
DNS requests
10
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3324 | iexplore.exe | GET | 200 | 195.138.255.8:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | DE | compressed | 56.1 Kb | whitelisted |
3324 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.1 Kb | whitelisted |
3324 | iexplore.exe | GET | 200 | 52.85.182.11:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3324 | iexplore.exe | GET | 200 | 52.85.182.216:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3324 | iexplore.exe | OPTIONS | 400 | 172.217.22.104:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3324 | iexplore.exe | OPTIONS | 400 | 172.217.22.104:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3324 | iexplore.exe | OPTIONS | 400 | 172.217.22.104:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3324 | iexplore.exe | OPTIONS | 400 | 172.217.22.104:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3324 | iexplore.exe | OPTIONS | 400 | 172.217.22.104:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3324 | iexplore.exe | OPTIONS | 400 | 172.217.22.104:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3324 | iexplore.exe | 172.217.22.104:80 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3324 | iexplore.exe | 195.138.255.8:80 | www.download.windowsupdate.com | AS33891 Netzbetrieb GmbH | DE | suspicious |
4 | System | 172.217.22.104:139 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3324 | iexplore.exe | 52.85.182.216:80 | x.ss2.us | Amazon.com, Inc. | US | suspicious |
3324 | iexplore.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4 | System | 172.217.22.104:445 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2932 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3324 | iexplore.exe | 54.192.203.147:443 | prod-cdn.wetransfer.net | Amazon.com, Inc. | US | unknown |
3324 | iexplore.exe | 52.85.182.11:80 | x.ss2.us | Amazon.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
prod-cdn.wetransfer.net |
| whitelisted |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
dns.msftncsi.com |
| shared |
Threats
10 ETPRO signatures available at the full report