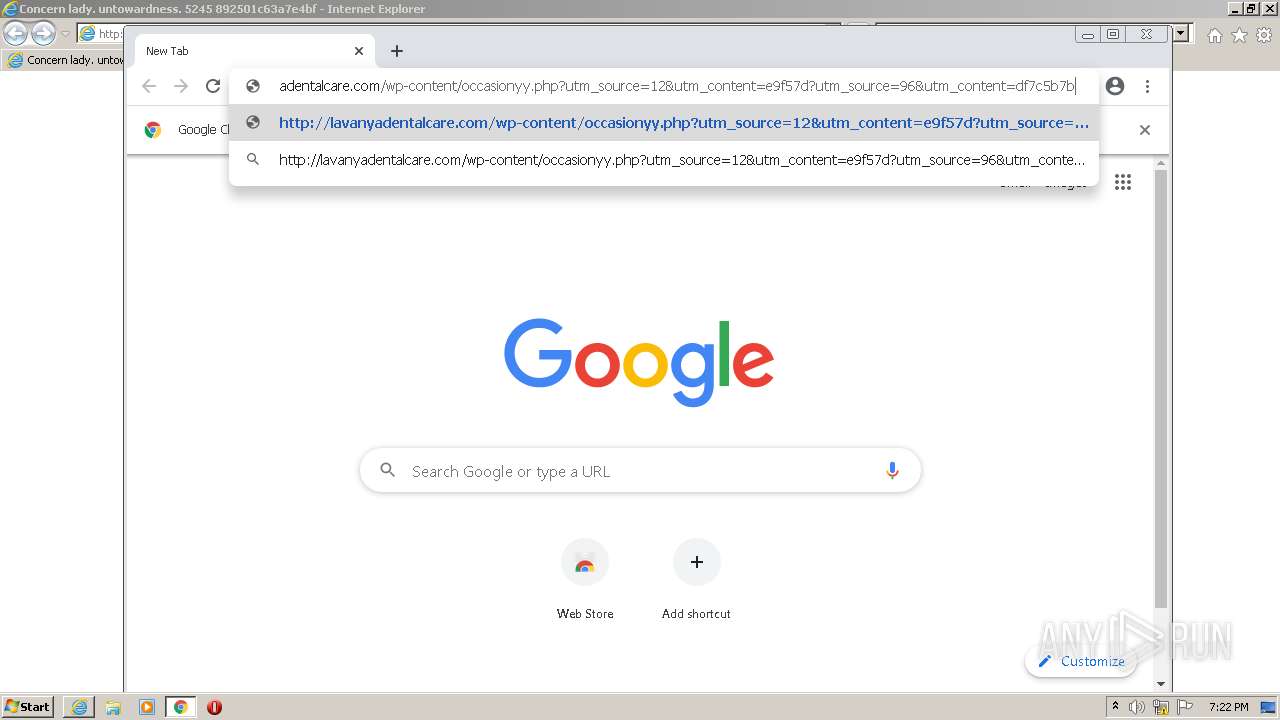
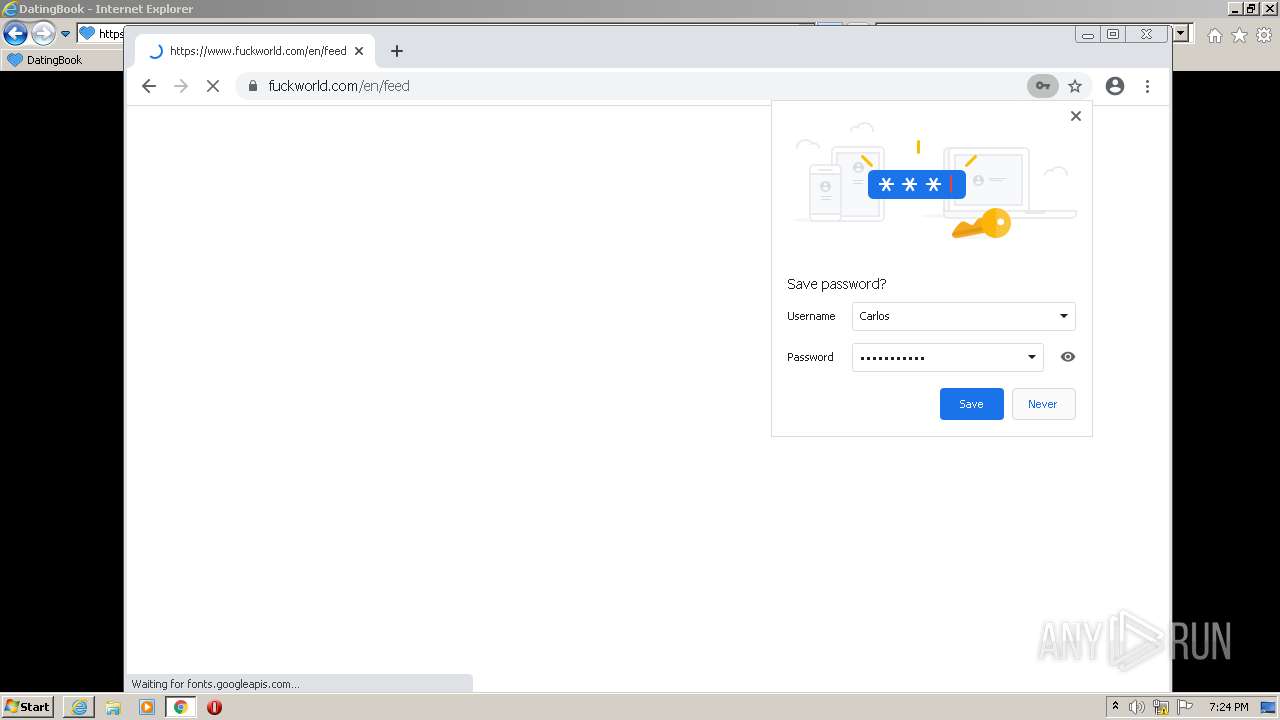
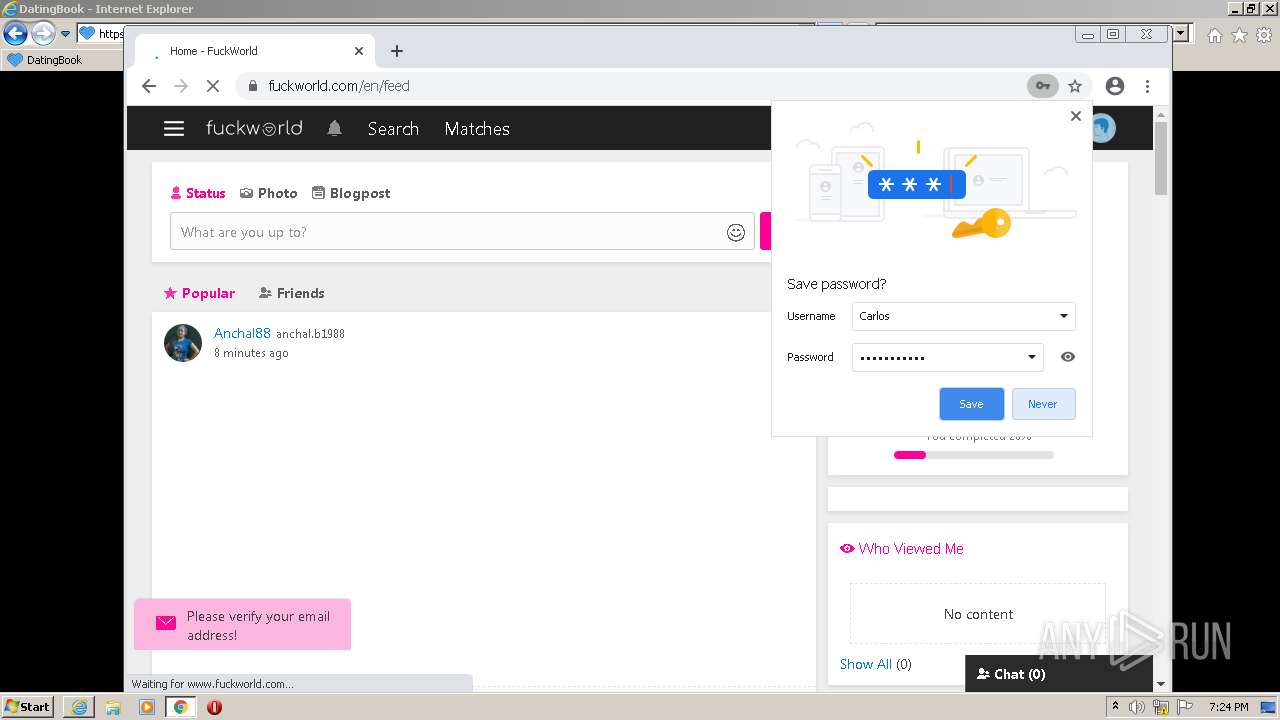
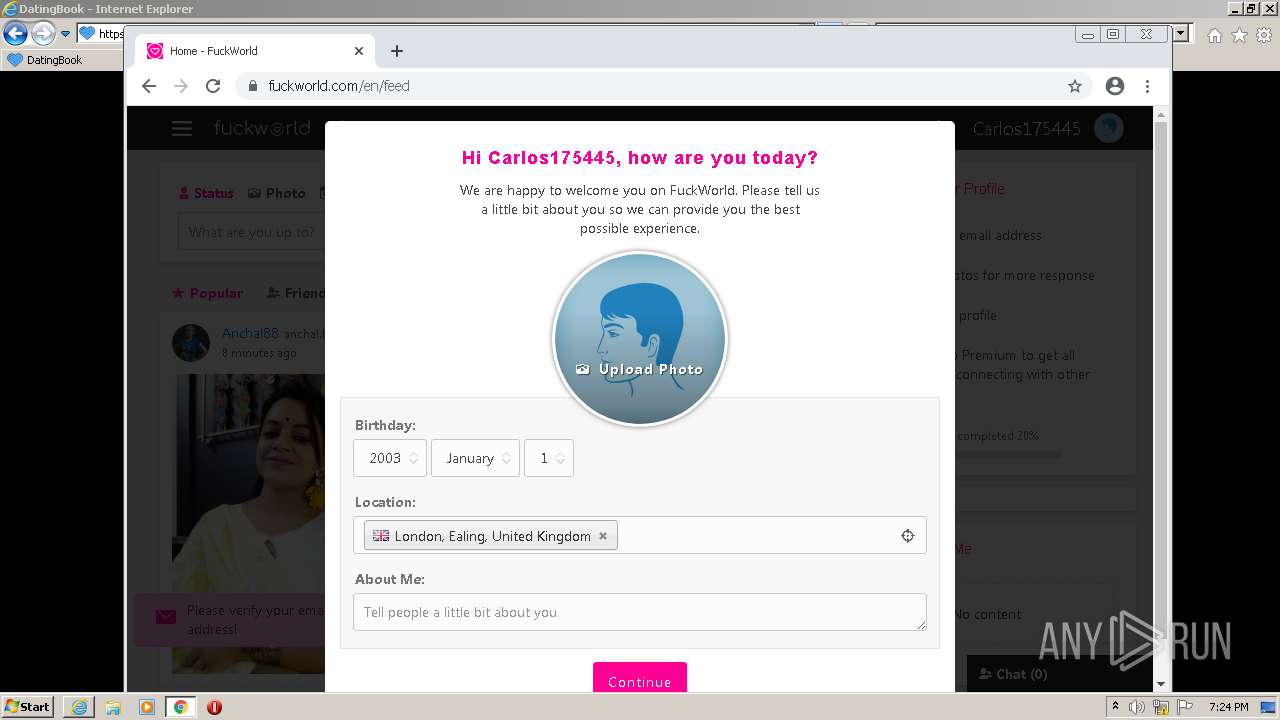
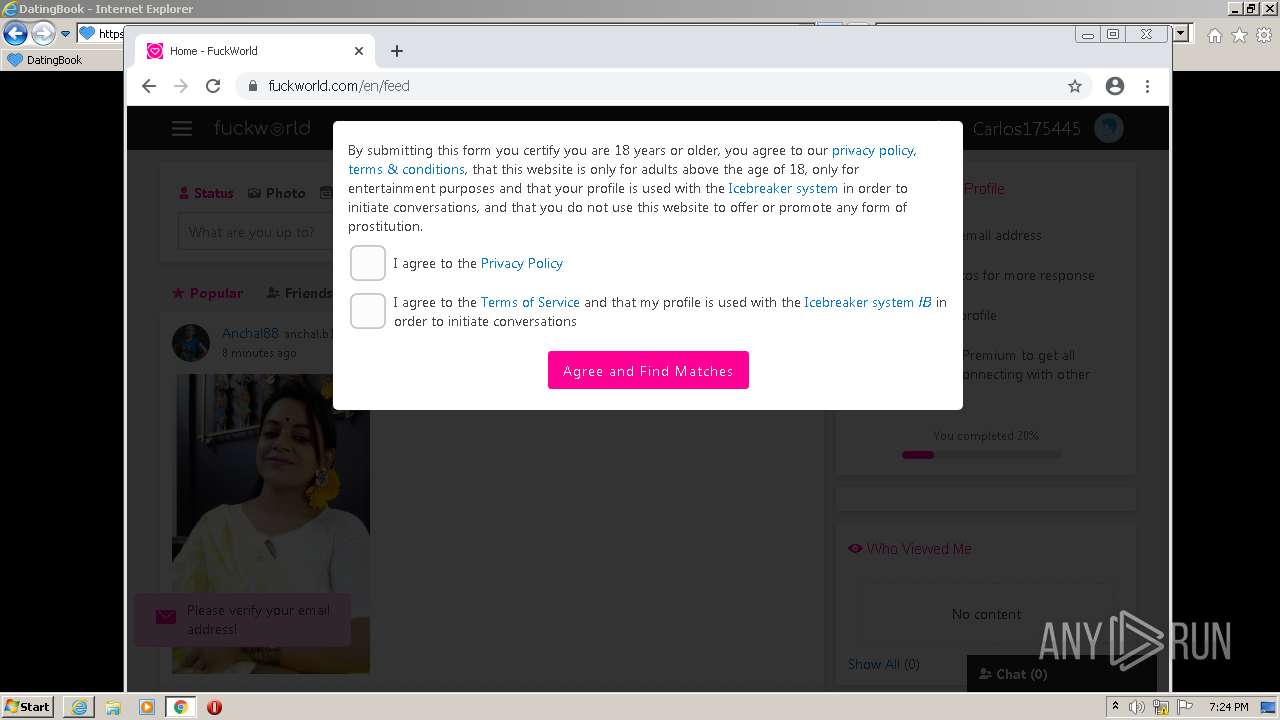
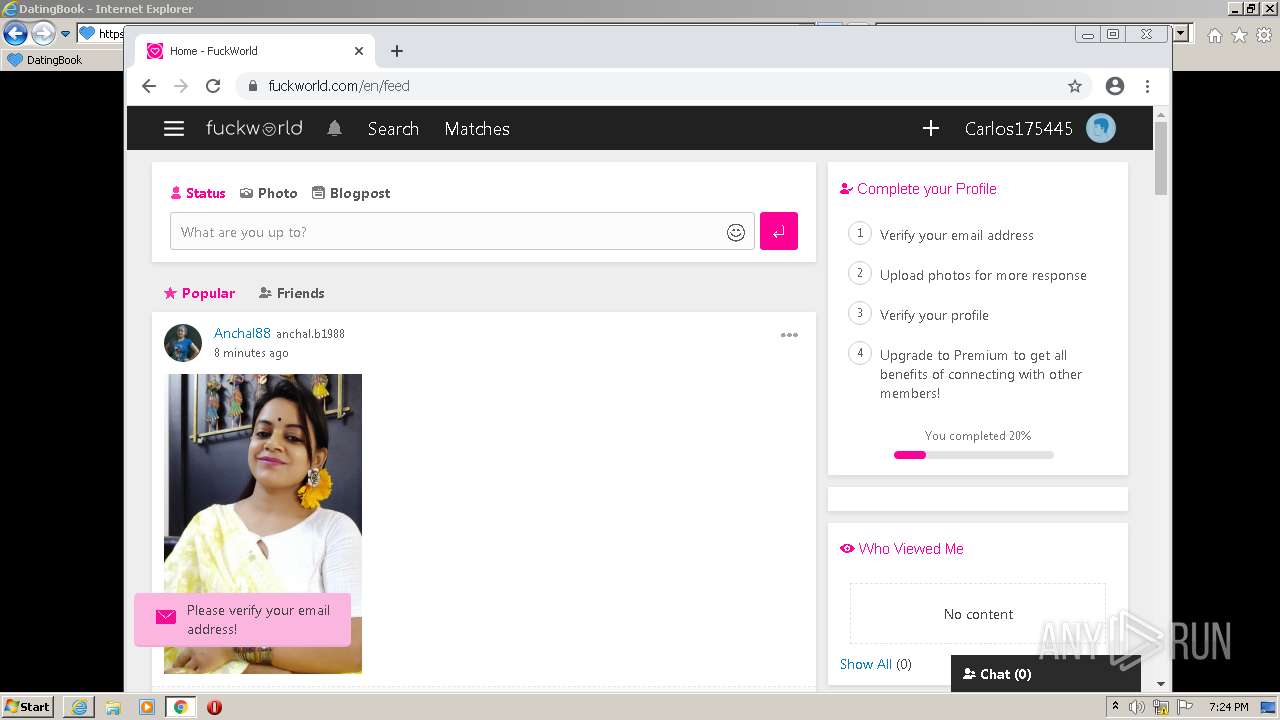
| URL: | http://lavanyadentalcare.com/wp-content/occasionyy.php?utm_source=12&utm_content=e9f57d?utm_source=96&utm_content=df7c5b7b |
| Full analysis: | https://app.any.run/tasks/a02a796c-163c-4a24-841e-c0e937c00969 |
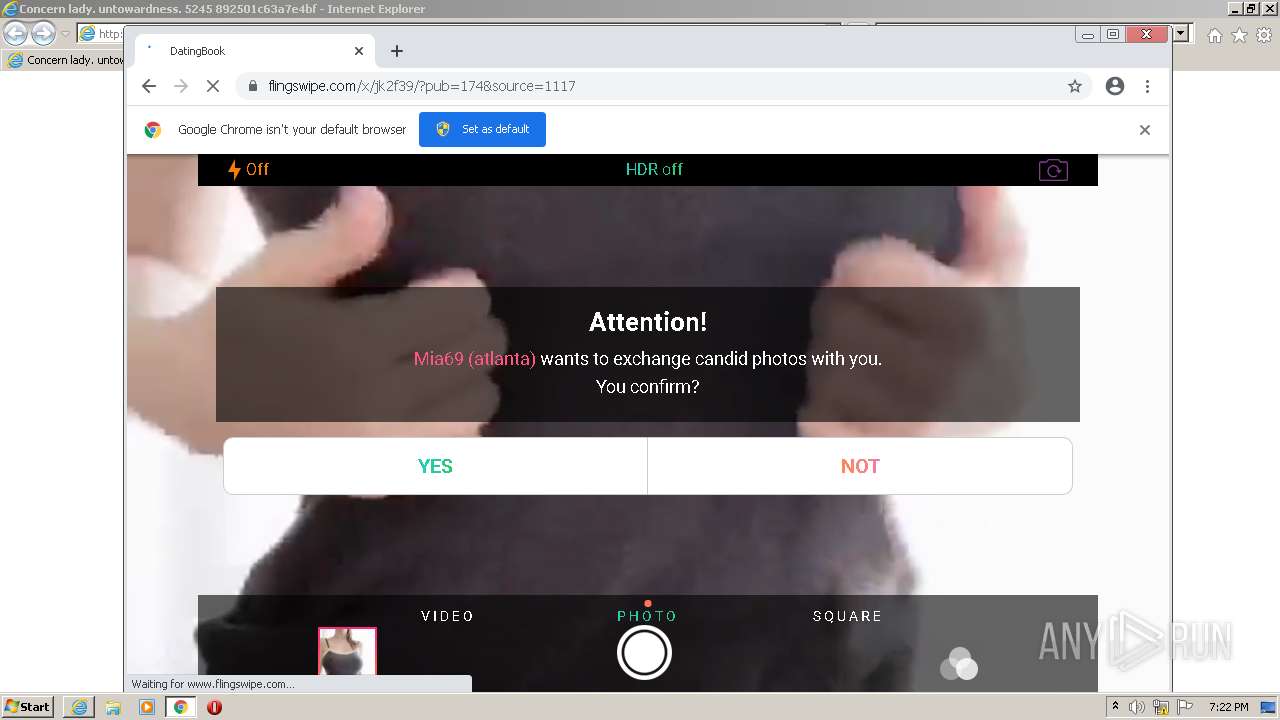
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2022, 19:21:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BAA4AEBE87A2CA8EDC1E0EDF3B1DC912 |
| SHA1: | 0E3273924C5E60EF26492C4720597A2208851ED3 |
| SHA256: | 01C49347194287130E28C826DAF840CA1B691B40D972B7F2A92714A21A6AC084 |
| SSDEEP: | 3:N1KSEIL1Be6ALGFVOlAQdG35VNeWwDKlAL+dQSBC6CWsQmKlAL+1Ln:CSTLe6AgVOlAuG35eWun6CWSALn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2884)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2340)
INFO
Reads the computer name
- iexplore.exe (PID: 1988)
- iexplore.exe (PID: 2884)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 1096)
- chrome.exe (PID: 492)
- chrome.exe (PID: 1552)
- chrome.exe (PID: 1124)
- chrome.exe (PID: 2656)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 2056)
Checks supported languages
- iexplore.exe (PID: 1988)
- iexplore.exe (PID: 2884)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 492)
- chrome.exe (PID: 3936)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 2024)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 1096)
- chrome.exe (PID: 2812)
- chrome.exe (PID: 1552)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 3836)
- chrome.exe (PID: 3268)
- chrome.exe (PID: 1636)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 984)
- chrome.exe (PID: 3204)
- chrome.exe (PID: 1124)
- chrome.exe (PID: 3332)
- chrome.exe (PID: 2656)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 684)
- chrome.exe (PID: 3396)
- chrome.exe (PID: 3992)
- chrome.exe (PID: 2056)
- chrome.exe (PID: 3700)
- chrome.exe (PID: 516)
- chrome.exe (PID: 376)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 3224)
Changes internet zones settings
- iexplore.exe (PID: 1988)
Manual execution by user
- chrome.exe (PID: 2340)
Application launched itself
- iexplore.exe (PID: 1988)
- chrome.exe (PID: 2340)
Reads internet explorer settings
- iexplore.exe (PID: 2884)
Checks Windows Trust Settings
- iexplore.exe (PID: 1988)
- iexplore.exe (PID: 2884)
Reads settings of System Certificates
- iexplore.exe (PID: 1988)
- chrome.exe (PID: 492)
- iexplore.exe (PID: 2884)
Reads the hosts file
- chrome.exe (PID: 2340)
- chrome.exe (PID: 492)
Creates files in the user directory
- iexplore.exe (PID: 1988)
- iexplore.exe (PID: 2884)
Changes settings of System certificates
- iexplore.exe (PID: 1988)
Reads the date of Windows installation
- chrome.exe (PID: 2656)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
33
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,17524753977986483709,14021339972605514642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1056,17524753977986483709,14021339972605514642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1296 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,17524753977986483709,14021339972605514642,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1732 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,17524753977986483709,14021339972605514642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3416 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,17524753977986483709,14021339972605514642,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1056,17524753977986483709,14021339972605514642,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1132 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,17524753977986483709,14021339972605514642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,17524753977986483709,14021339972605514642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3324 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,17524753977986483709,14021339972605514642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3672 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1988 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://lavanyadentalcare.com/wp-content/occasionyy.php?utm_source=12&utm_content=e9f57d?utm_source=96&utm_content=df7c5b7b" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
31 056
Read events
30 765
Write events
281
Delete events
10
Modification events
| (PID) Process: | (1988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30940046 | |||
| (PID) Process: | (1988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30940046 | |||
| (PID) Process: | (1988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
219
Text files
238
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62001FEF-924.pma | — | |
MD5:— | SHA256:— | |||
| 1988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 1988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2884 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\occasionyy[2].htm | html | |
MD5:— | SHA256:— | |||
| 1988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 1988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 2884 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\occasionyy[1].htm | html | |
MD5:— | SHA256:— | |||
| 1988 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 1988 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
132
DNS requests
93
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
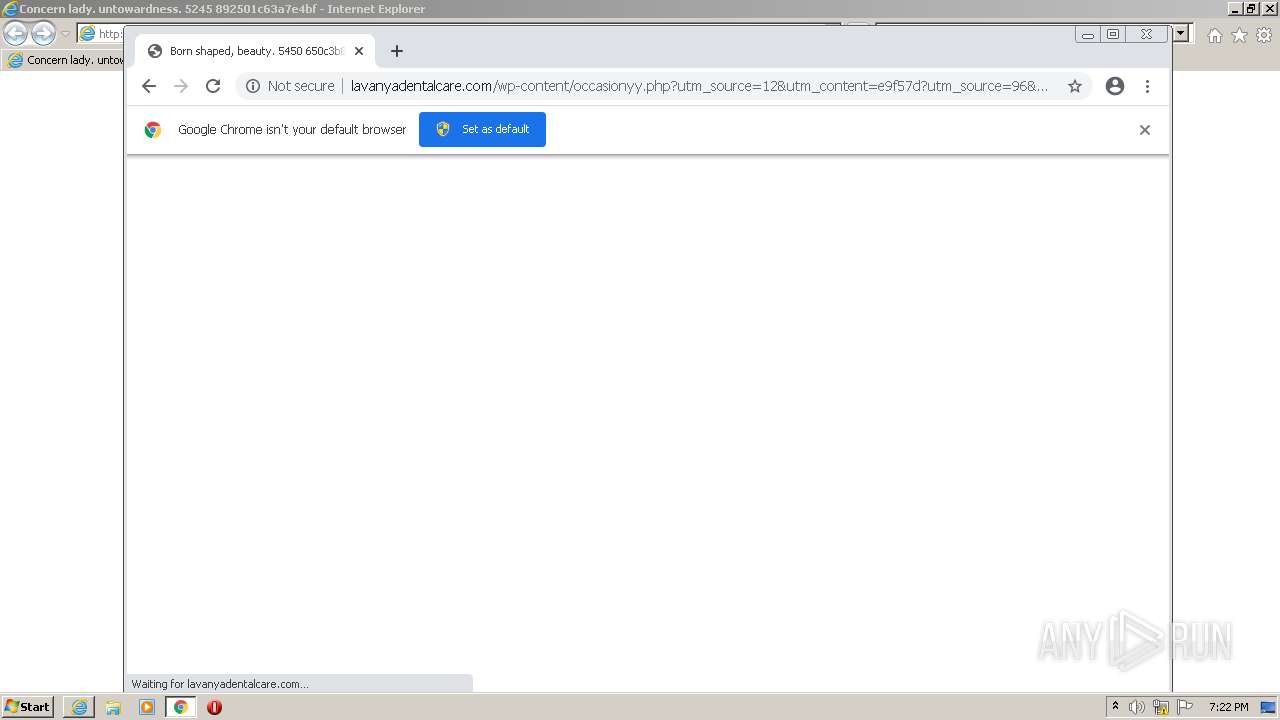
2884 | iexplore.exe | GET | 200 | 45.114.246.131:80 | http://lavanyadentalcare.com/wp-content/occasionyy.php?utm_source=12&utm_content=e9f57d?utm_source=96&utm_content=df7c5b7b | IN | html | 5.00 Kb | suspicious |
1988 | iexplore.exe | GET | 500 | 45.114.246.131:80 | http://lavanyadentalcare.com/favicon.ico | IN | html | 632 b | suspicious |
1988 | iexplore.exe | GET | 500 | 45.114.246.131:80 | http://lavanyadentalcare.com/favicon.ico | IN | html | 787 b | suspicious |
492 | chrome.exe | GET | 500 | 45.114.246.131:80 | http://lavanyadentalcare.com/favicon.ico | IN | html | 693 b | suspicious |
2884 | iexplore.exe | GET | 200 | 45.114.246.131:80 | http://lavanyadentalcare.com/wp-content/occasionyy.php?utm_source=12&utm_content=e9f57d?utm_source=96&utm_content=df7c5b7b | IN | html | 5.15 Kb | suspicious |
1988 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
492 | chrome.exe | GET | 200 | 45.114.246.131:80 | http://lavanyadentalcare.com/wp-content/occasionyy.php?utm_source=12&utm_content=e9f57d?utm_source=96&utm_content=df7c5b7b | IN | html | 5.35 Kb | suspicious |
1988 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
492 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAtIgyHhzCAgf0Woj6GgeOA%3D | US | der | 471 b | whitelisted |
2884 | iexplore.exe | GET | 200 | 143.204.101.195:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2884 | iexplore.exe | 45.114.246.131:80 | lavanyadentalcare.com | CtrlS Datacenters Ltd. | IN | suspicious |
1988 | iexplore.exe | 45.114.246.131:80 | lavanyadentalcare.com | CtrlS Datacenters Ltd. | IN | suspicious |
1988 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 23.32.238.201:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
1988 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1988 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1988 | iexplore.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
1988 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
492 | chrome.exe | 142.250.184.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lavanyadentalcare.com |
| suspicious |
www.microsoft.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1988 | iexplore.exe | Web Application Attack | ET WEB_CLIENT Possible HTTP 500 XSS Attempt (External Source) |
1988 | iexplore.exe | Web Application Attack | ET WEB_CLIENT Possible HTTP 500 XSS Attempt (External Source) |
1988 | iexplore.exe | Web Application Attack | ET WEB_CLIENT Possible HTTP 500 XSS Attempt (External Source) |
492 | chrome.exe | Web Application Attack | ET WEB_CLIENT Possible HTTP 500 XSS Attempt (External Source) |
492 | chrome.exe | Web Application Attack | ET WEB_CLIENT Possible HTTP 500 XSS Attempt (External Source) |