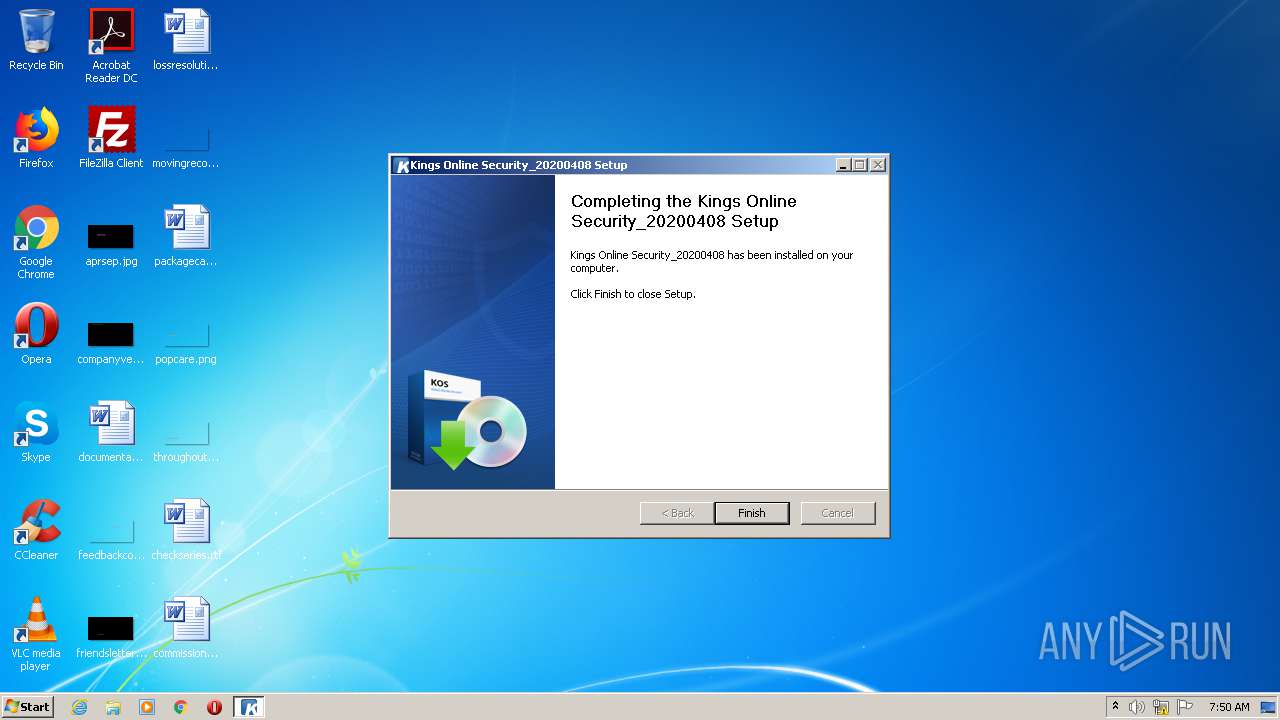
| File name: | KOS_Setup.exe |
| Full analysis: | https://app.any.run/tasks/af6bddd0-fc1c-4a54-8e69-94612089898a |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 06:49:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1DB7596A7E5DF1521C4490E25488AEE5 |
| SHA1: | 29342E4AF1427D26054B96D5D8730DECDD32C51F |
| SHA256: | 01800A52019B944CCE61DF057E403FCE4541524FA7A4D1FCA636E976FF86D2AD |
| SSDEEP: | 196608:isMhC6GNrTOlVpfyOGWF8LwdqEGegUidL6k1+n3G/VQPuLys:3IC6krYp6OVKM8reMd3dQGLys |
MALICIOUS
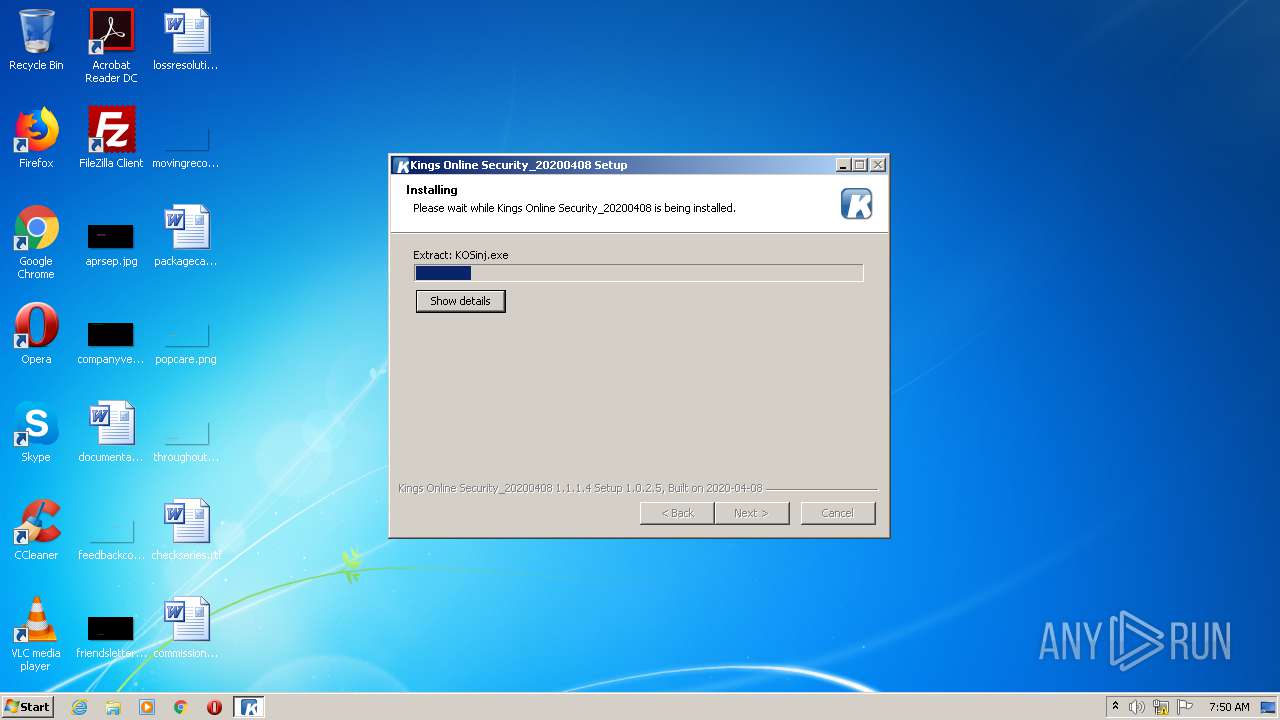
Loads dropped or rewritten executable
- KOS_Setup.exe (PID: 3508)
- regsvr32.exe (PID: 2352)
- regsvr32.exe (PID: 3412)
- KOSinj.exe (PID: 3460)
Application was dropped or rewritten from another process
- KOS_Update.exe (PID: 312)
- KOSSvc.exe (PID: 3924)
- KOS_Update.exe (PID: 1200)
- KOSinj.exe (PID: 3460)
- nsBBE6.tmp (PID: 1440)
- nsBA20.tmp (PID: 1744)
- nsBD2F.tmp (PID: 2688)
Registers / Runs the DLL via REGSVR32.EXE
- nsBD2F.tmp (PID: 2688)
- nsBBE6.tmp (PID: 1440)
Changes settings of System certificates
- KOSinj.exe (PID: 3460)
- KOSSvc.exe (PID: 3924)
Actions looks like stealing of personal data
- KOSinj.exe (PID: 3460)
SUSPICIOUS
Executable content was dropped or overwritten
- KOS_Setup.exe (PID: 3508)
Creates files in the Windows directory
- KOS_Setup.exe (PID: 3508)
- KOSSvc.exe (PID: 3924)
Starts application with an unusual extension
- KOS_Setup.exe (PID: 3508)
Reads Internet Cache Settings
- KOS_Update.exe (PID: 312)
Executed as Windows Service
- KOSSvc.exe (PID: 3924)
Creates COM task schedule object
- regsvr32.exe (PID: 3412)
Removes files from Windows directory
- KOSSvc.exe (PID: 3924)
Creates files in the user directory
- KOSinj.exe (PID: 3460)
Adds / modifies Windows certificates
- KOSinj.exe (PID: 3460)
- KOSSvc.exe (PID: 3924)
Creates a software uninstall entry
- KOS_Setup.exe (PID: 3508)
INFO
Reads settings of System Certificates
- KOSSvc.exe (PID: 3924)
- KOSinj.exe (PID: 3460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:19:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28672 |
| InitializedDataSize: | 445952 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x39e3 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.1.4 |
| ProductVersionNumber: | 1.1.1.4 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
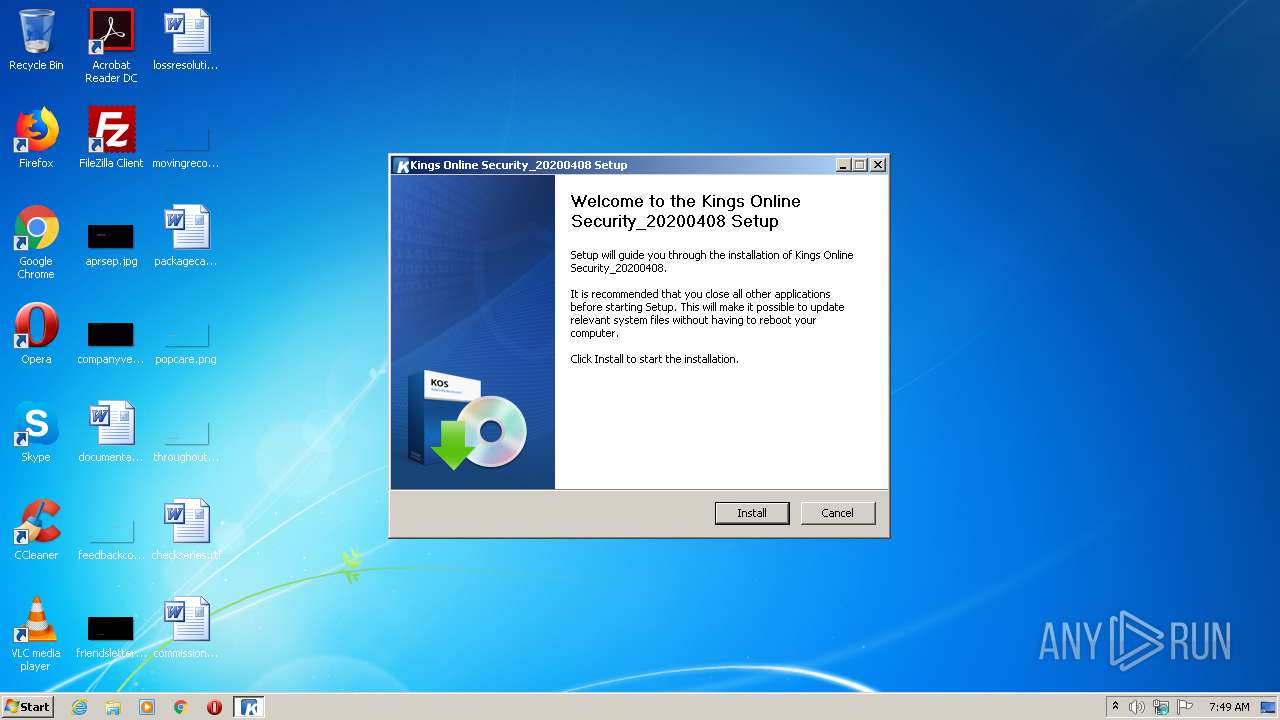
| Comments: | Kings Online Security_20200408 Setup |
| CompanyName: | Kings Information & Network Co., Ltd. |
| FileDescription: | Kings Online Security_20200408 1.1.1.4 Setup 1.0.2.5, Built on 2020-04-08 |
| FileVersion: | 1.1.1.4 |
| LegalCopyright: | Copyright(c) 2017 Kings Information & Network Co., Ltd. |
| ProductName: | Kings Online Security_20200408 |
| ProductVersion: | 1.1.1.4 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:19:59 |
| Detected languages: |
|
| Comments: | Kings Online Security_20200408 Setup |
| CompanyName: | Kings Information & Network Co., Ltd. |
| FileDescription: | Kings Online Security_20200408 1.1.1.4 Setup 1.0.2.5, Built on 2020-04-08 |
| FileVersion: | 1.1.1.4 |
| LegalCopyright: | Copyright(c) 2017 Kings Information & Network Co., Ltd. |
| ProductName: | Kings Online Security_20200408 |
| ProductVersion: | 1.1.1.4 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:19:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006F10 | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49788 |
.rdata | 0x00008000 | 0x00002A92 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39389 |
.data | 0x0000B000 | 0x00067EBC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.47278 |
.ndata | 0x00073000 | 0x00109000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0017C000 | 0x00008F48 | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.44437 |
.reloc | 0x00185000 | 0x00000F8A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 2.07077 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21712 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.25211 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 4.51884 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 4.16479 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.62308 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
205 | 2.68176 | 494 | UNKNOWN | English - United States | RT_DIALOG |
206 | 2.86295 | 228 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
49
Monitored processes
11
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Kings\KOS\KOS_Update.exe" | C:\Kings\KOS\KOS_Update.exe | nsBA20.tmp | ||||||||||||
User: admin Company: Kings Information & Network Co., Ltd Integrity Level: HIGH Description: KOS Updater Exit code: 1 Version: 1.0.1.0 Modules
| |||||||||||||||
| 1200 | "C:\Kings\KOS\KOS_Update.exe" | C:\Kings\KOS\KOS_Update.exe | KOSSvc.exe | ||||||||||||
User: SYSTEM Company: Kings Information & Network Co., Ltd Integrity Level: SYSTEM Description: KOS Updater Exit code: 1 Version: 1.0.1.0 Modules
| |||||||||||||||
| 1440 | "C:\Users\admin\AppData\Local\Temp\nsjDD5B.tmp\nsBBE6.tmp" "C:\Windows\system32\regsvr32.exe" /u /s "C:\Kings\KOS\kosldr.dll" | C:\Users\admin\AppData\Local\Temp\nsjDD5B.tmp\nsBBE6.tmp | — | KOS_Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 5 Modules
| |||||||||||||||
| 1744 | "C:\Users\admin\AppData\Local\Temp\nsjDD5B.tmp\nsBA20.tmp" "C:\Kings\KOS\KOS_Update.exe" | C:\Users\admin\AppData\Local\Temp\nsjDD5B.tmp\nsBA20.tmp | — | KOS_Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1844 | "C:\Users\admin\AppData\Local\Temp\KOS_Setup.exe" | C:\Users\admin\AppData\Local\Temp\KOS_Setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Kings Information & Network Co., Ltd. Integrity Level: MEDIUM Description: Kings Online Security_20200408 1.1.1.4 Setup 1.0.2.5, Built on 2020-04-08 Exit code: 3221226540 Version: 1.1.1.4 Modules
| |||||||||||||||
| 2352 | "C:\Windows\system32\regsvr32.exe" /u /s "C:\Kings\KOS\kosldr.dll" | C:\Windows\system32\regsvr32.exe | — | nsBBE6.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2688 | "C:\Users\admin\AppData\Local\Temp\nsjDD5B.tmp\nsBD2F.tmp" "C:\Windows\system32\regsvr32.exe" /s "C:\Kings\KOS\kosldr.dll" | C:\Users\admin\AppData\Local\Temp\nsjDD5B.tmp\nsBD2F.tmp | — | KOS_Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3412 | "C:\Windows\system32\regsvr32.exe" /s "C:\Kings\KOS\kosldr.dll" | C:\Windows\system32\regsvr32.exe | — | nsBD2F.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3460 | "C:\Kings\KOS\KOSinj.exe" /P:1224 | C:\Kings\KOS\KOSinj.exe | KOSSvc.exe | ||||||||||||
User: admin Company: Kings Information & Network Co., Ltd Integrity Level: HIGH Description: KOSinj 20031201 Exit code: 0 Version: 1.0.8.6 Modules
| |||||||||||||||
| 3508 | "C:\Users\admin\AppData\Local\Temp\KOS_Setup.exe" | C:\Users\admin\AppData\Local\Temp\KOS_Setup.exe | explorer.exe | ||||||||||||
User: admin Company: Kings Information & Network Co., Ltd. Integrity Level: HIGH Description: Kings Online Security_20200408 1.1.1.4 Setup 1.0.2.5, Built on 2020-04-08 Exit code: 0 Version: 1.1.1.4 Modules
| |||||||||||||||
Total events
1 782
Read events
510
Write events
1 272
Delete events
0
Modification events
| (PID) Process: | (312) KOS_Update.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (312) KOS_Update.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (312) KOS_Update.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (312) KOS_Update.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (312) KOS_Update.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (312) KOS_Update.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (312) KOS_Update.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3412) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{517B6CA4-6A8E-401D-8685-2D0DB0678C86} |
| Operation: | write | Name: | |
Value: Kings Online Security Internet Explorer Non-ActiveX Loader | |||
| (PID) Process: | (3412) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\kosldr.dll |
| Operation: | write | Name: | AppID |
Value: {517B6CA4-6A8E-401D-8685-2D0DB0678C86} | |||
| (PID) Process: | (3412) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\KingsOnlineSecurity.Loader.1 |
| Operation: | write | Name: | |
Value: Kings Online Security Internet Explorer Non-ActiveX Loader Protocol | |||
Executable files
46
Suspicious files
0
Text files
3
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3508 | KOS_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsjDD5B.tmp\modern-wizard.bmp | image | |
MD5:— | SHA256:— | |||
| 3508 | KOS_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsjDD5B.tmp\AccessControl.dll | executable | |
MD5:— | SHA256:— | |||
| 3508 | KOS_Setup.exe | C:\Kings\KOS\KOSSvc.exe | executable | |
MD5:— | SHA256:— | |||
| 3508 | KOS_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsjDD5B.tmp\nsDialogs.dll | executable | |
MD5:4CCC4A742D4423F2F0ED744FD9C81F63 | SHA256:416133DD86C0DFF6B0FCAF1F46DFE97FDC85B37F90EFFB2D369164A8F7E13AE6 | |||
| 3508 | KOS_Setup.exe | C:\Kings\KOS\ProMDefense.dll | executable | |
MD5:FCD0FB3DE52F0C24E98DDF8C573FBEE2 | SHA256:647119F0630F495B6F36ED2793D82DB334D50FBDC03FFBDDACB0A9B88FEEAAD6 | |||
| 3508 | KOS_Setup.exe | C:\Kings\KOS\IDFApi.dll | executable | |
MD5:721C23833F29FAD54609CFFE0D60FE7A | SHA256:21DB520D43579AF121B23EFF7CCC6B0B9C0B9E80606D62661603AA7DD16CDD2D | |||
| 3508 | KOS_Setup.exe | C:\Kings\KOS\KOS_Update.exe | executable | |
MD5:5A72084AEA5832C519FB665AA28BA18D | SHA256:00BB185673327CD6EABAA0C00A226AA49A018311093F4F7D573468C663F5AA43 | |||
| 3508 | KOS_Setup.exe | C:\Kings\KOS\nspr4.dll | executable | |
MD5:76A287EB69989928A0271D0BB88506C6 | SHA256:5A5A6056F7BD58A9EB871B9F8476F4BC27DEE2286F1B149E2463499CEC9BE040 | |||
| 3508 | KOS_Setup.exe | C:\Kings\KOS\freebl3.dll | executable | |
MD5:1047A6BF43487A0248694A498DA63AD4 | SHA256:408395C8DE121F668181BB82446AD2BA8300E73A8F086C80DD6C663F42AD8D23 | |||
| 3508 | KOS_Setup.exe | C:\Kings\KOS\plc4.dll | executable | |
MD5:B47A32EBDFBD65B0F1D9A72C29B89A77 | SHA256:2CEF24146B2B2E5B96479429A713A67ED427D77EC155702FC553D2F52DD7C827 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
6
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
312 | KOS_Update.exe | GET | — | 14.0.113.209:80 | http://kings.nefficient.co.kr/kings/KOSNax/ | KR | — | — | malicious |
1200 | KOS_Update.exe | GET | — | 14.0.113.209:80 | http://kings.nefficient.co.kr/kings/KOSNax/ | KR | — | — | malicious |
3924 | KOSSvc.exe | GET | 404 | 14.0.113.209:80 | http://kings.nefficient.co.kr/kings/KOSNax/x86_KOS_Update/KOS_Update.ini | KR | xml | 345 b | malicious |
312 | KOS_Update.exe | GET | 404 | 14.0.113.209:80 | http://kings.nefficient.co.kr/kings/KOSNax/KOSUpdaterV1.xml | KR | xml | 345 b | malicious |
1200 | KOS_Update.exe | GET | 404 | 14.0.113.209:80 | http://kings.nefficient.co.kr/kings/KOSNax/KOSUpdaterV1.xml | KR | xml | 345 b | malicious |
3460 | KOSinj.exe | GET | 404 | 14.0.113.209:80 | http://kings.nefficient.co.kr/ | KR | xml | 345 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
312 | KOS_Update.exe | 14.0.113.209:80 | kings.nefficient.co.kr | — | KR | malicious |
3924 | KOSSvc.exe | 14.0.113.209:80 | kings.nefficient.co.kr | — | KR | malicious |
1200 | KOS_Update.exe | 14.0.113.209:80 | kings.nefficient.co.kr | — | KR | malicious |
3460 | KOSinj.exe | 14.0.113.209:80 | kings.nefficient.co.kr | — | KR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kings.nefficient.co.kr |
| malicious |
Threats
Process | Message |
|---|---|
KOS_Setup.exe | [KNSISPlugin] CVersionUtils::GetModuleVersion Enter |
KOS_Setup.exe | [KNSISPlugin] CheckUserPermission IsAdmin [1] |
KOS_Setup.exe | [KNSISPlugin] CVersionUtils::GetModuleVersion Leave |
KOS_Setup.exe | [KNSISPlugin] CVersionUtils::GetModuleVersion Enter |
KOS_Setup.exe | [KNSISPlugin] CheckUserPermission IsAdmin [1] |
KOS_Setup.exe | [KNSISPlugin] CVersionUtils::GetModuleVersion Leave |
KOS_Setup.exe | [KNSISPlugin] CheckUserPermission Leave |
KOS_Setup.exe | [KNSISPlugin] CheckUserPermission Leave |
KOS_Setup.exe | [KNSISPlugin] Initialize Enter |
KOS_Setup.exe | [KNSISPlugin] Initialize InstallDirectory [C:\Kings\KOS] |