| File name: | Office_2024_EN_64Bits.exe |
| Full analysis: | https://app.any.run/tasks/2507e422-0141-476a-ab17-c29c79b9e424 |
| Verdict: | Malicious activity |
| Analysis date: | November 17, 2024, 11:20:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 7408133E63AA3D775BEEDBA6EA6ED3E9 |
| SHA1: | C0C98105A43F1478E659CA675BE30AC56FE0BCB7 |
| SHA256: | 0157AFE7FBB8757A5F92BBB9D2DFBC2F06D9A1A8493B6D25E64A1735AC455811 |
| SSDEEP: | 98304:SfLIQ/3oou0LTVZOyCrFW+JdcIfrp41GzL6u4Ndl2etH7M5ozFhGW9rPhVGaiimE:8jaiqbNQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- Office_2024_EN_64Bits.exe (PID: 1732)
Reads Internet Explorer settings
- Office_2024_EN_64Bits.exe (PID: 1732)
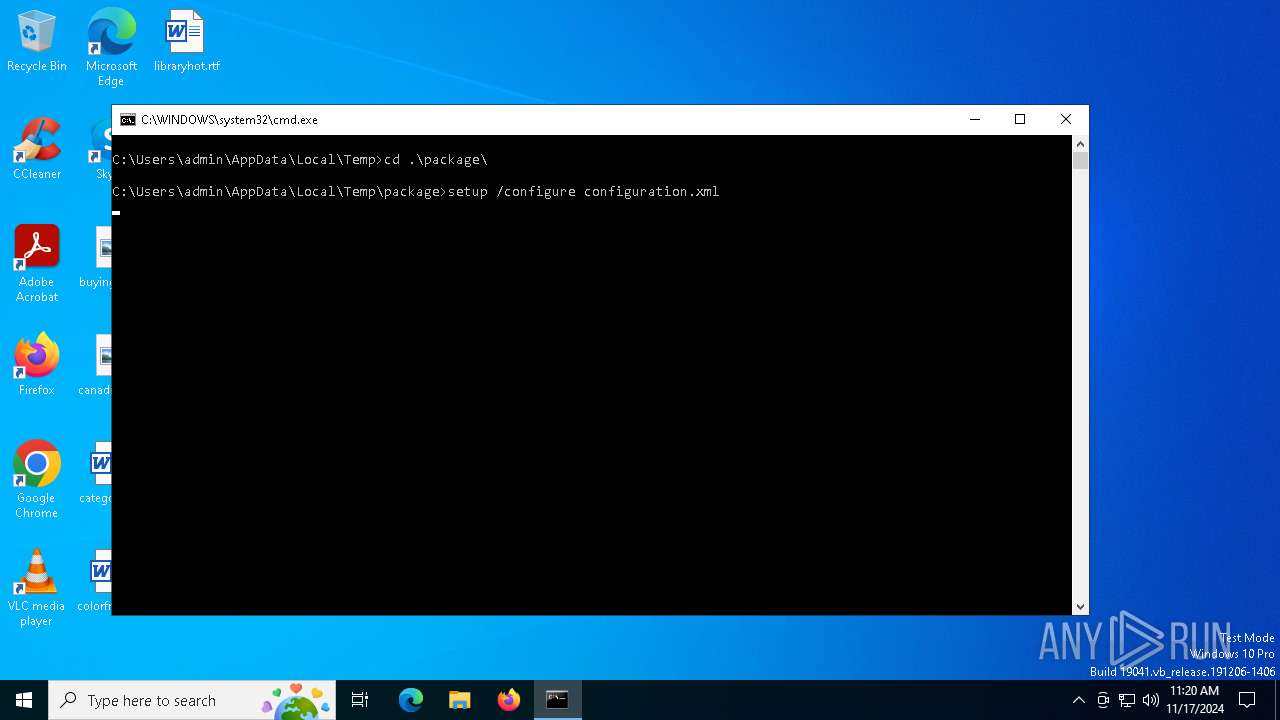
Executing commands from a ".bat" file
- Office_2024_EN_64Bits.exe (PID: 1732)
Process drops legitimate windows executable
- Office_2024_EN_64Bits.exe (PID: 1732)
The executable file from the user directory is run by the CMD process
- setup.exe (PID: 5652)
Reads security settings of Internet Explorer
- Office_2024_EN_64Bits.exe (PID: 1732)
- setup.exe (PID: 5652)
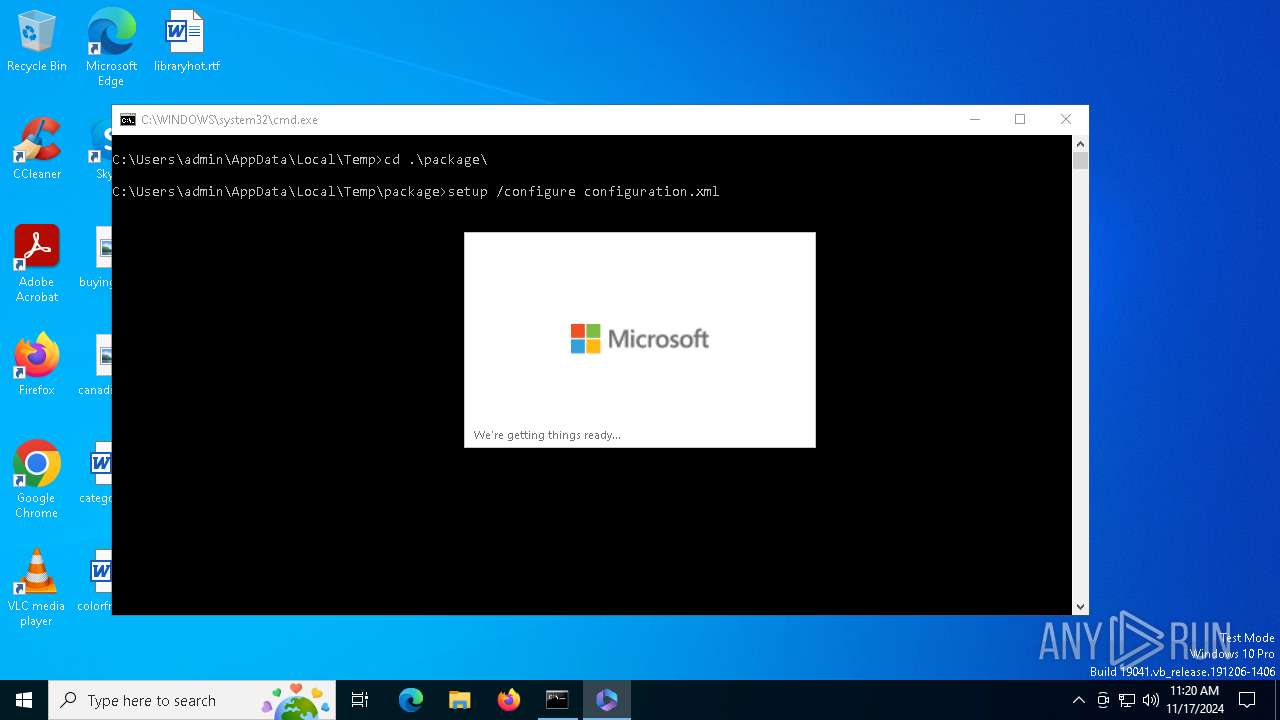
Starts a Microsoft application from unusual location
- setup.exe (PID: 6260)
- setup.exe (PID: 5652)
Executable content was dropped or overwritten
- Office_2024_EN_64Bits.exe (PID: 1732)
Starts CMD.EXE for commands execution
- Office_2024_EN_64Bits.exe (PID: 1732)
Application launched itself
- setup.exe (PID: 5652)
INFO
Checks supported languages
- Office_2024_EN_64Bits.exe (PID: 1732)
- setup.exe (PID: 5652)
Checks proxy server information
- Office_2024_EN_64Bits.exe (PID: 1732)
- setup.exe (PID: 5652)
Process checks computer location settings
- Office_2024_EN_64Bits.exe (PID: 1732)
- setup.exe (PID: 5652)
Reads the computer name
- Office_2024_EN_64Bits.exe (PID: 1732)
- setup.exe (PID: 5652)
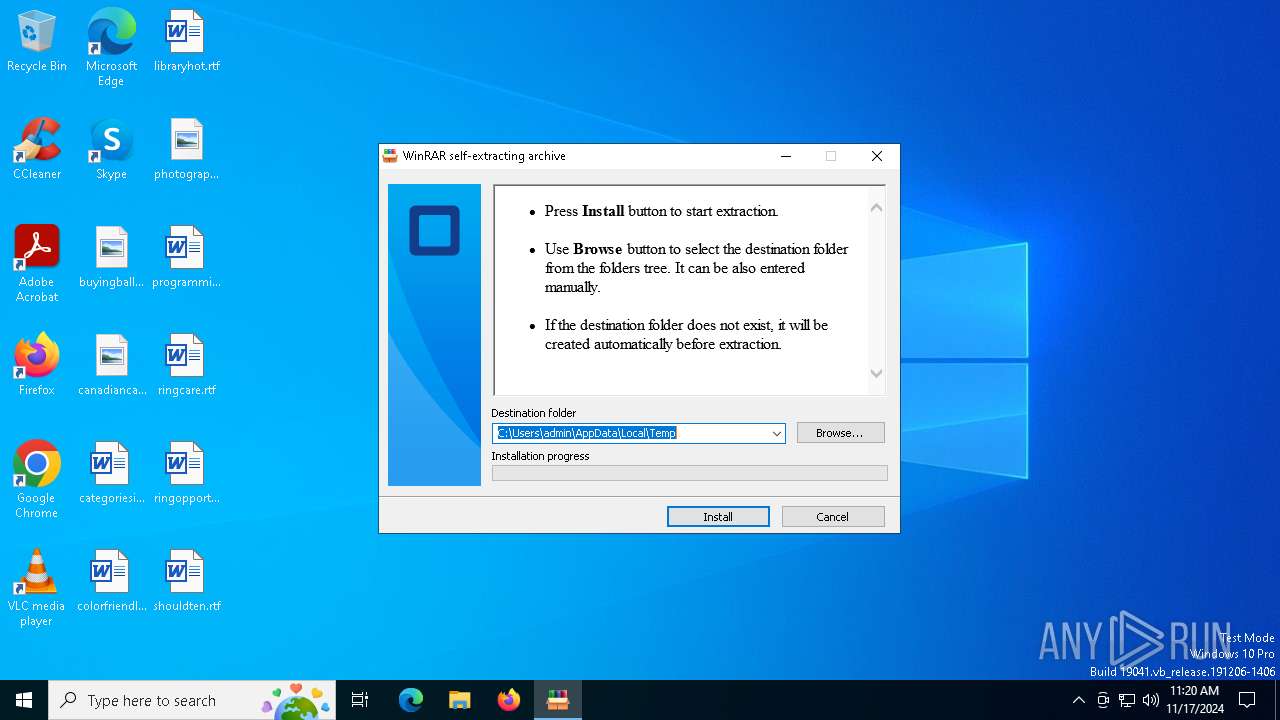
Create files in a temporary directory
- Office_2024_EN_64Bits.exe (PID: 1732)
- setup.exe (PID: 5652)
- setup.exe (PID: 6260)
Process checks whether UAC notifications are on
- setup.exe (PID: 5652)
The process uses the downloaded file
- setup.exe (PID: 5652)
- setup.exe (PID: 6260)
- Office_2024_EN_64Bits.exe (PID: 1732)
Reads the machine GUID from the registry
- setup.exe (PID: 5652)
Creates files or folders in the user directory
- setup.exe (PID: 5652)
Reads the software policy settings
- setup.exe (PID: 5652)
Reads Microsoft Office registry keys
- setup.exe (PID: 5652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:03 07:51:19+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 214528 |
| InitializedDataSize: | 263680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x21d50 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
139
Monitored processes
6
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1732 | "C:\Users\admin\AppData\Local\Temp\Office_2024_EN_64Bits.exe" | C:\Users\admin\AppData\Local\Temp\Office_2024_EN_64Bits.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
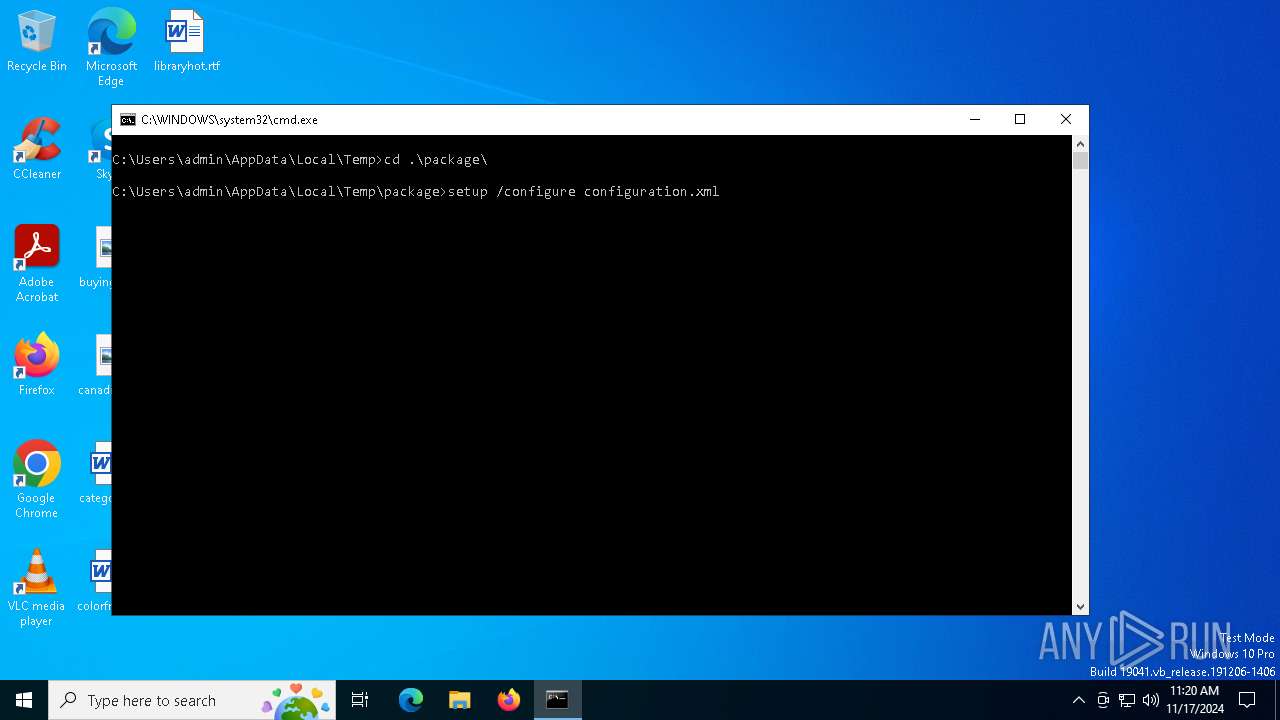
| 3644 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\start.bat" " | C:\Windows\SysWOW64\cmd.exe | — | Office_2024_EN_64Bits.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294967295 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4692 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5592 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
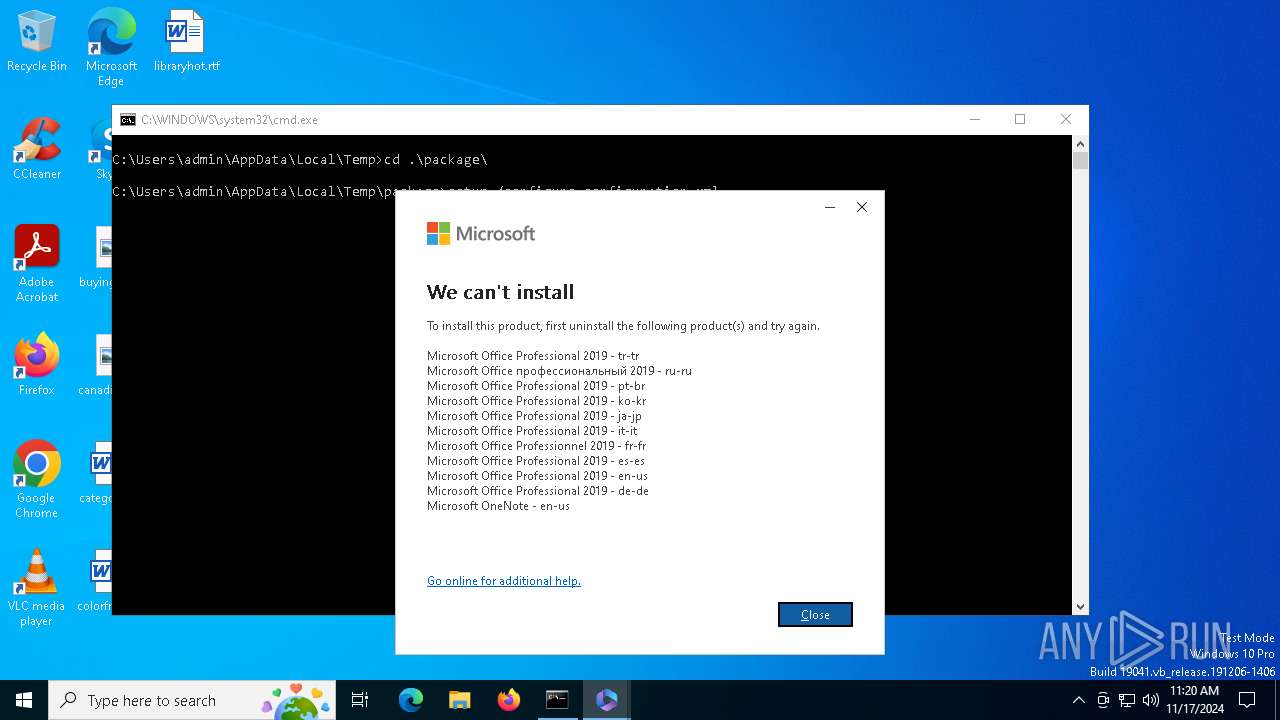
| 5652 | setup /configure configuration.xml | C:\Users\admin\AppData\Local\Temp\package\setup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft 365 and Office Exit code: 4294967295 Version: 16.0.17531.20046 Modules
| |||||||||||||||
| 6260 | "C:\Users\admin\AppData\Local\Temp\package\setup.exe" ELEVATED sid=S-1-5-21-1693682860-607145093-2874071422-1001 /configure configuration.xml | C:\Users\admin\AppData\Local\Temp\package\setup.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft 365 and Office Exit code: 4294967295 Version: 16.0.17531.20046 Modules
| |||||||||||||||
Total events
4 869
Read events
4 784
Write events
81
Delete events
4
Modification events
| (PID) Process: | (1732) Office_2024_EN_64Bits.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1732) Office_2024_EN_64Bits.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1732) Office_2024_EN_64Bits.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5652) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (5652) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (5652) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (5652) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (5652) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (5652) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (5652) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
Executable files
1
Suspicious files
6
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1732 | Office_2024_EN_64Bits.exe | C:\Users\admin\AppData\Local\Temp\package\Click To Run.bat | text | |
MD5:AD3ED1D41F9B51F7F203D56597C05958 | SHA256:413B8E555D8F42C56D22D6843708F7BFCB0BBEDB4F833BF3C89880665925BD14 | |||
| 1732 | Office_2024_EN_64Bits.exe | C:\Users\admin\AppData\Local\Temp\package\configuration.xml | text | |
MD5:B8A2F53FD00F8AC78982A497E2472497 | SHA256:D30E4B5CBF1C373DE24CC2BA9A660BD5006DDE136ACDFE30CF194701C77C1F64 | |||
| 6260 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | der | |
MD5:E34B3AB4EA53C6D5A01D1B51521EB189 | SHA256:5A42F5EE06AFDD9CD1CCCDA0F21700740E00DD6729424C4581CE4BE753FA6A55 | |||
| 6260 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\setup.exe.db | sqlite | |
MD5:D0DE7DB24F7B0C0FE636B34E253F1562 | SHA256:B6DC74E4A39FFA38ED8C93D58AADEB7E7A0674DAC1152AF413E9DA7313ADE6ED | |||
| 6260 | setup.exe | C:\Users\admin\AppData\Local\Temp\DESKTOP-JGLLJLD-20241117-1120a.log | text | |
MD5:ECBEEAA599D0A9F2AF6525198CEB4F33 | SHA256:5CCB297AC79BFBF4CECB11835C9E0CF1D71B3D1C24ACB168099F0EC10447B159 | |||
| 6260 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | binary | |
MD5:05A513F56BBCC2CC9F75423790EF3B36 | SHA256:5459B0858D45B39618F1666F18881A33C4046C5DA5E7E9E60110B18F86B845C1 | |||
| 6260 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\setup.exe.db-wal | binary | |
MD5:1692AC37924E93F7E9040B35E30791DB | SHA256:AB476D3A5A945224FB8BA2149BFE605A67C9423F7F0BE435FBBE56957FF5D418 | |||
| 6260 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\setup.exe.db-shm | binary | |
MD5:5CDFB5402F630198F5E486E3DACA6B5D | SHA256:5E6CC0E04448DAB5B5F0C84770A23695F80D94CC16F9022D3BC3035981E64BA7 | |||
| 1732 | Office_2024_EN_64Bits.exe | C:\Users\admin\AppData\Local\Temp\package\setup.exe | executable | |
MD5:7488D696F9A3D74E093B4C31EF7282C6 | SHA256:B03C4CC3C1377EE81B1F94DA126E58A30F484D4D935889538FAE1C650DD6828B | |||
| 5652 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\setup.exe.db-journal | binary | |
MD5:B88A85C21C2C3F4C3D37F1A1E3D8F3A0 | SHA256:13147F6FE67F59F4D7E7F5CA064E3081667D6A99B1DE90935184723974147129 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
40
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6260 | setup.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2236 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2236 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1588 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4360 | SearchApp.exe | 2.16.204.135:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6944 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
mobile.events.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |