| File name: | Office_2024_EN_64Bits.exe |
| Full analysis: | https://app.any.run/tasks/0553d27c-9985-441e-b7db-9ad3856fb3dd |
| Verdict: | Malicious activity |
| Analysis date: | November 17, 2024, 11:23:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 7408133E63AA3D775BEEDBA6EA6ED3E9 |
| SHA1: | C0C98105A43F1478E659CA675BE30AC56FE0BCB7 |
| SHA256: | 0157AFE7FBB8757A5F92BBB9D2DFBC2F06D9A1A8493B6D25E64A1735AC455811 |
| SSDEEP: | 98304:SfLIQ/3oou0LTVZOyCrFW+JdcIfrp41GzL6u4Ndl2etH7M5ozFhGW9rPhVGaiimE:8jaiqbNQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- Office_2024_EN_64Bits.exe (PID: 1336)
- setup.exe (PID: 3648)
Reads Microsoft Outlook installation path
- Office_2024_EN_64Bits.exe (PID: 1336)
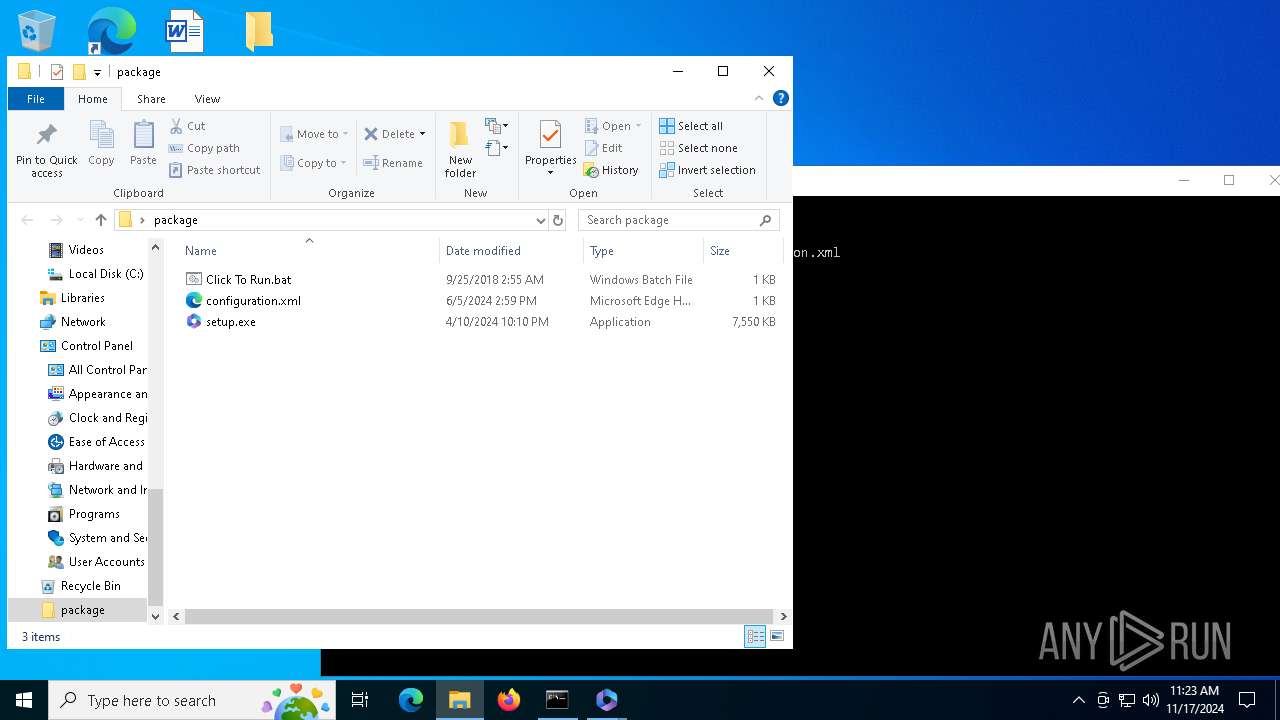
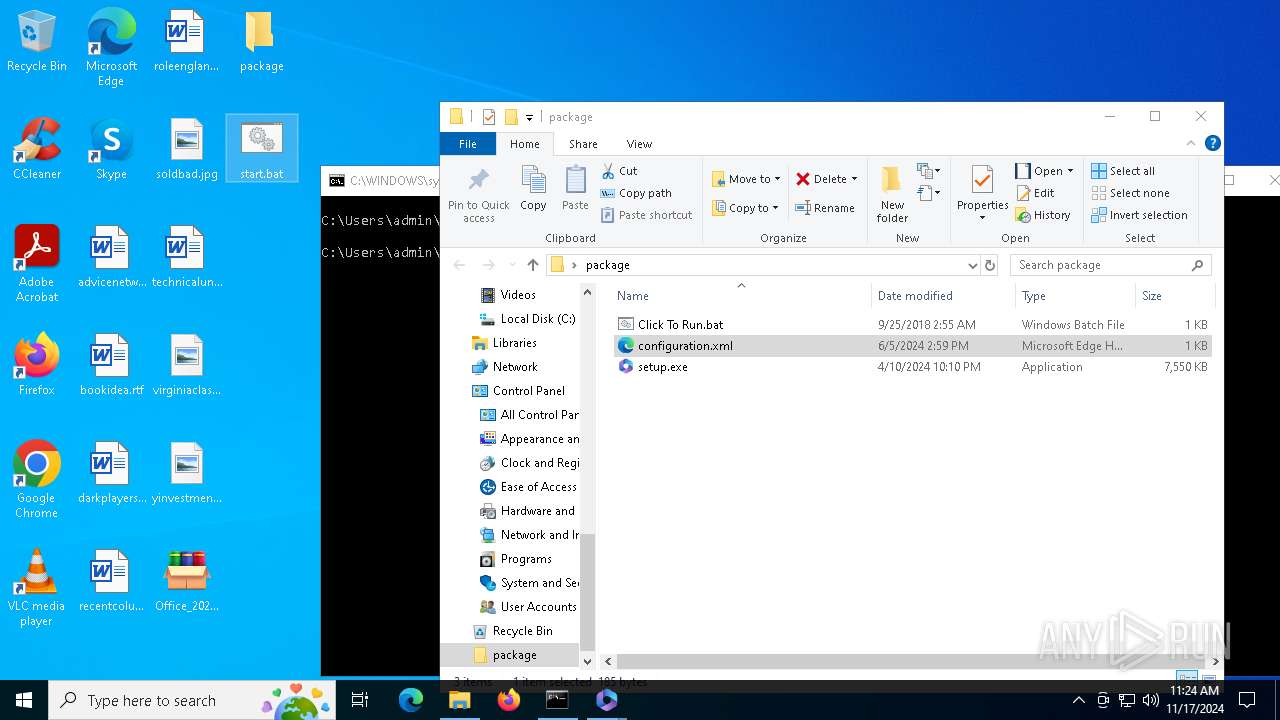
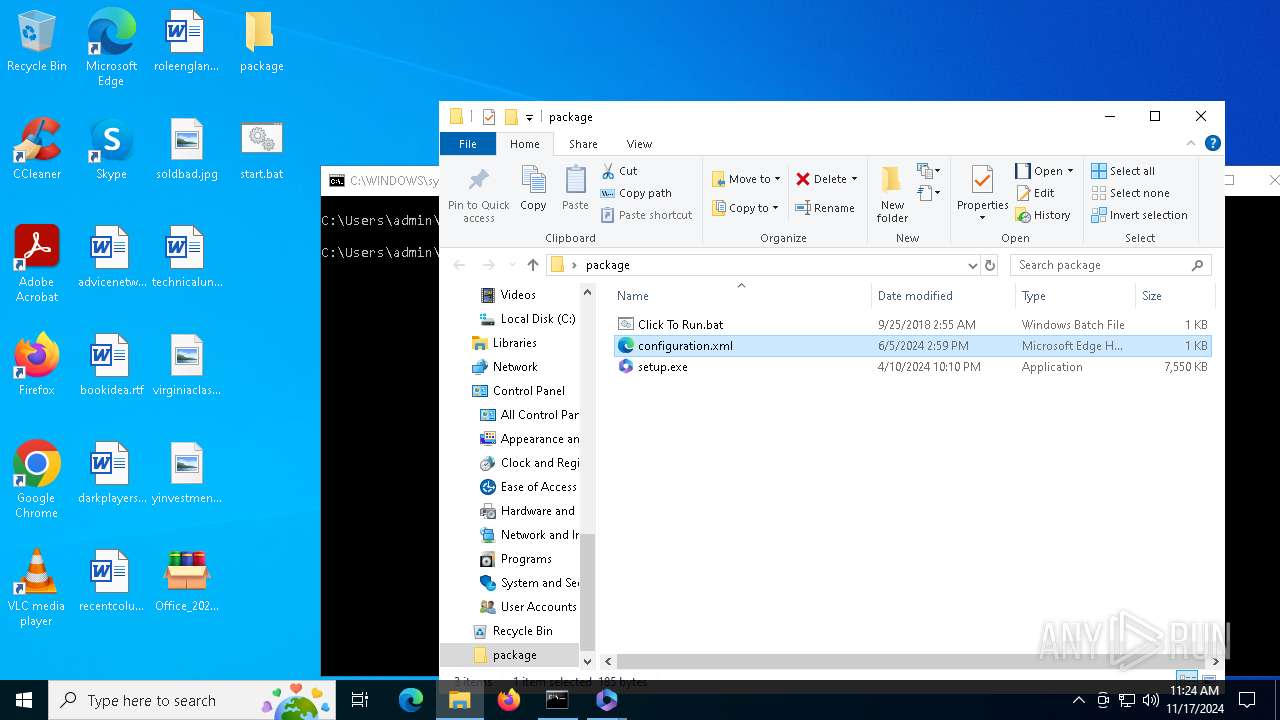
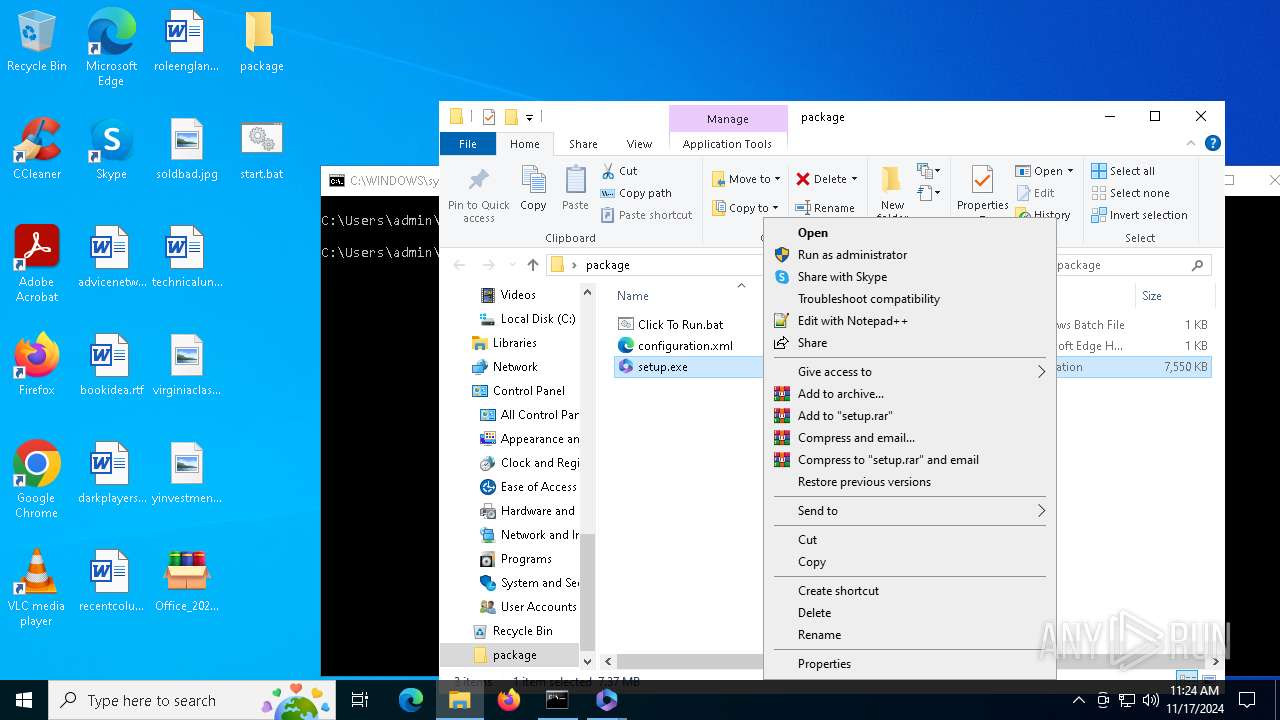
Process drops legitimate windows executable
- Office_2024_EN_64Bits.exe (PID: 1336)
Executable content was dropped or overwritten
- Office_2024_EN_64Bits.exe (PID: 1336)
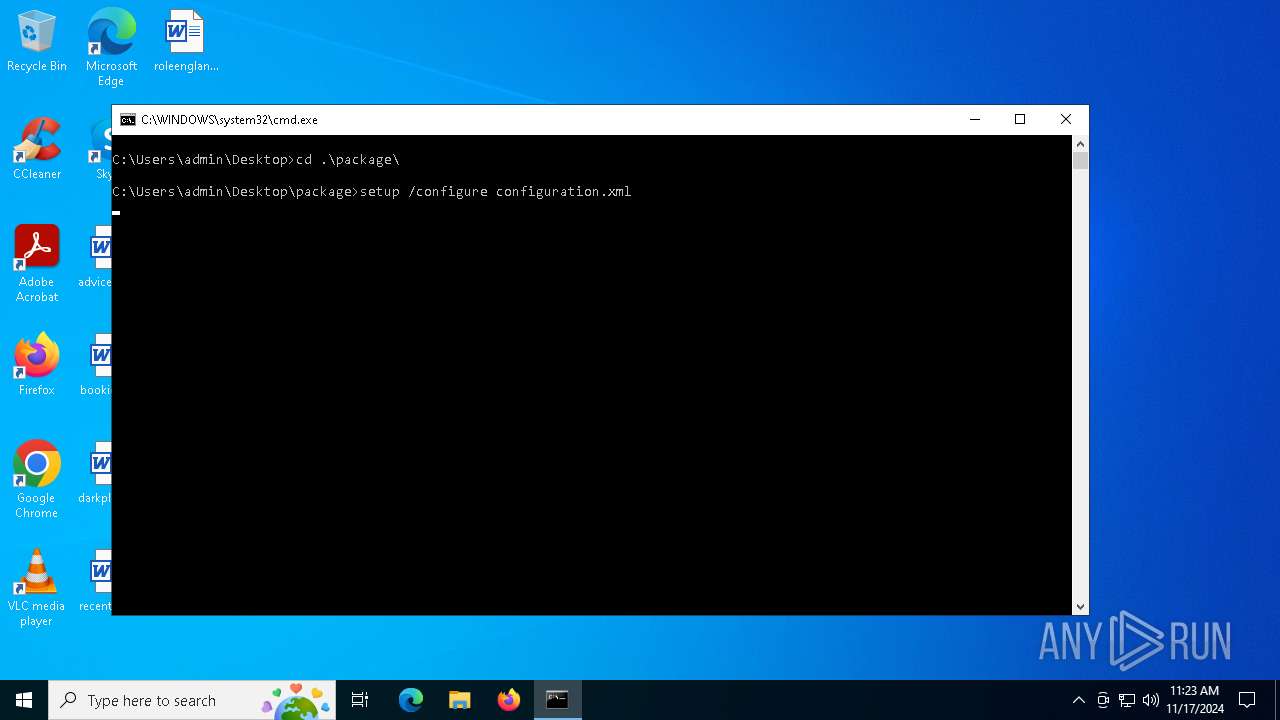
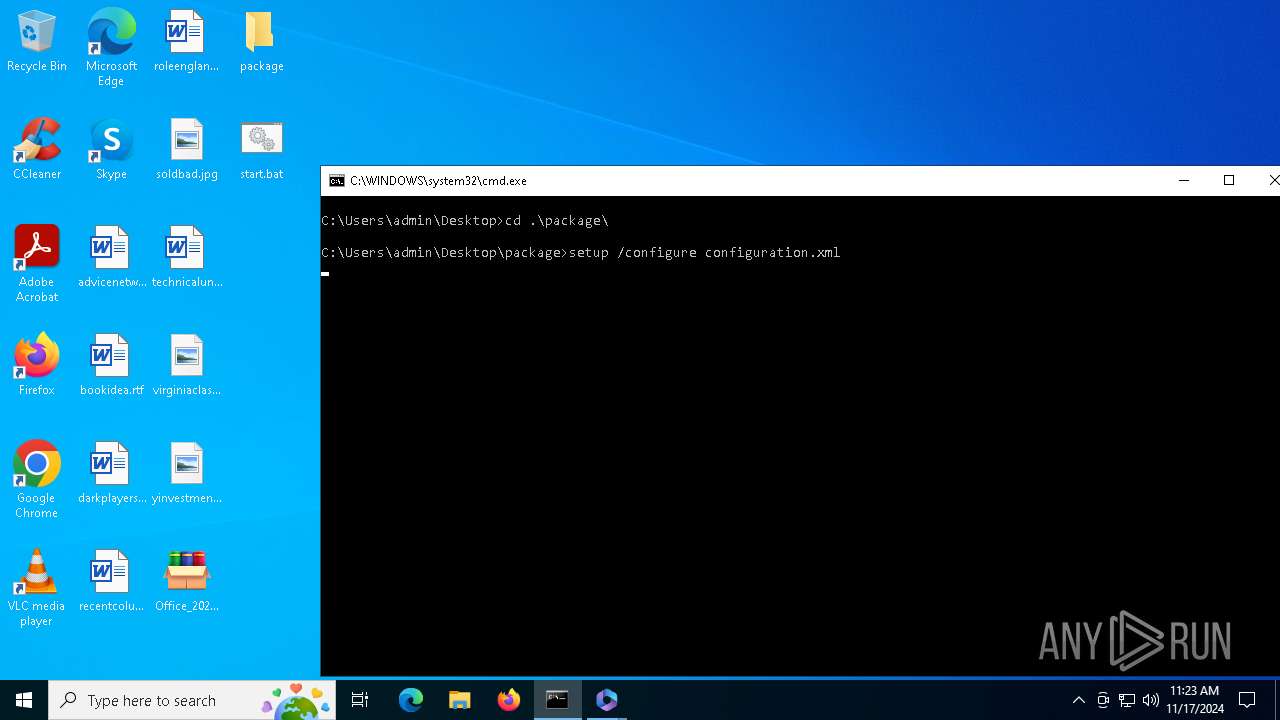
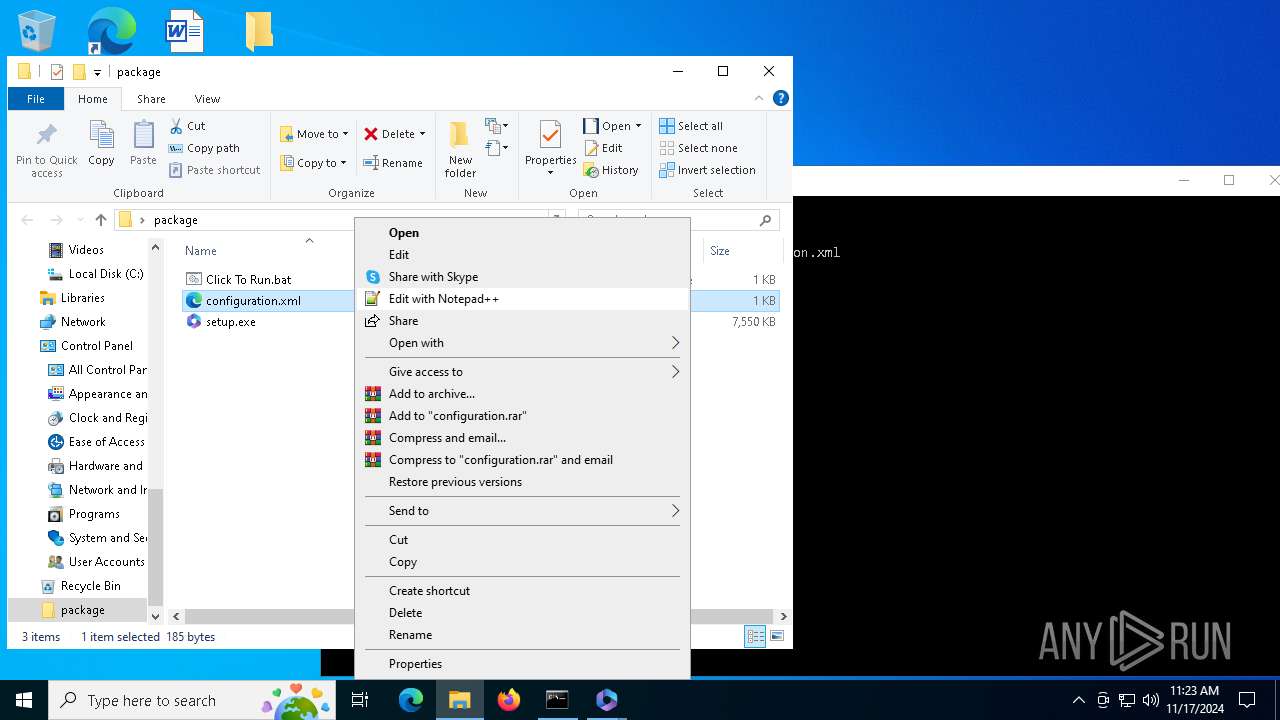
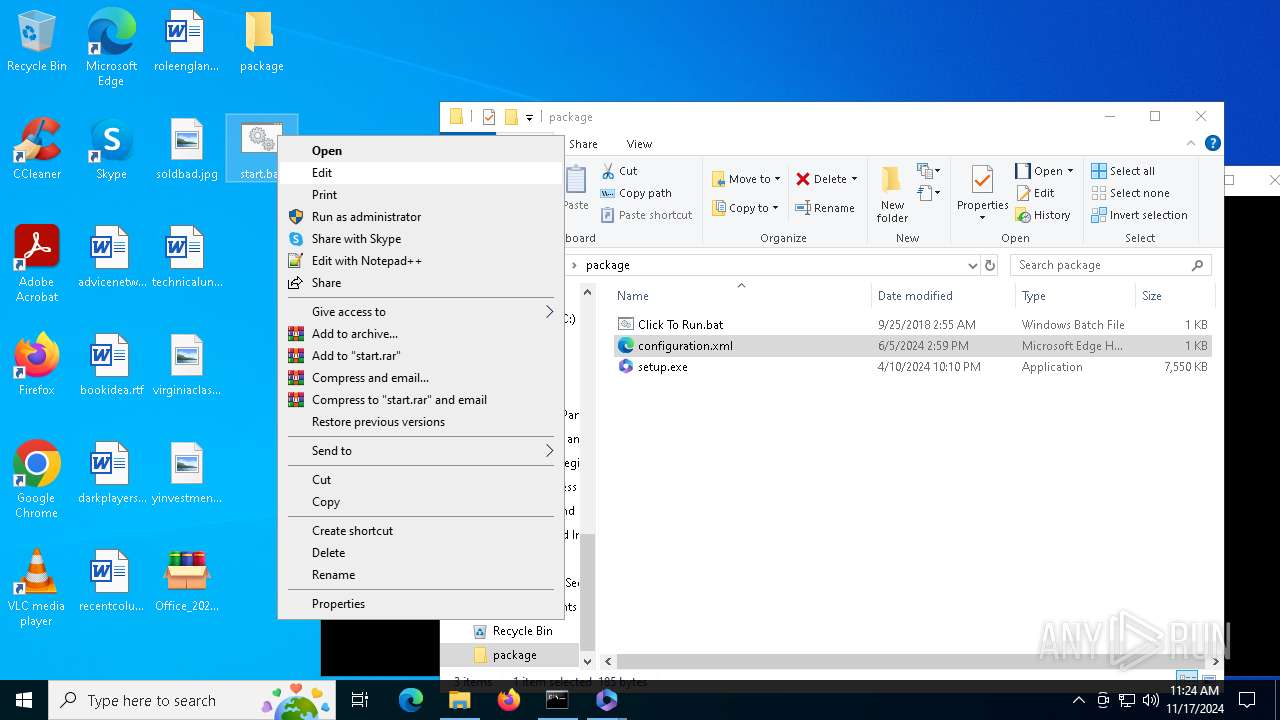
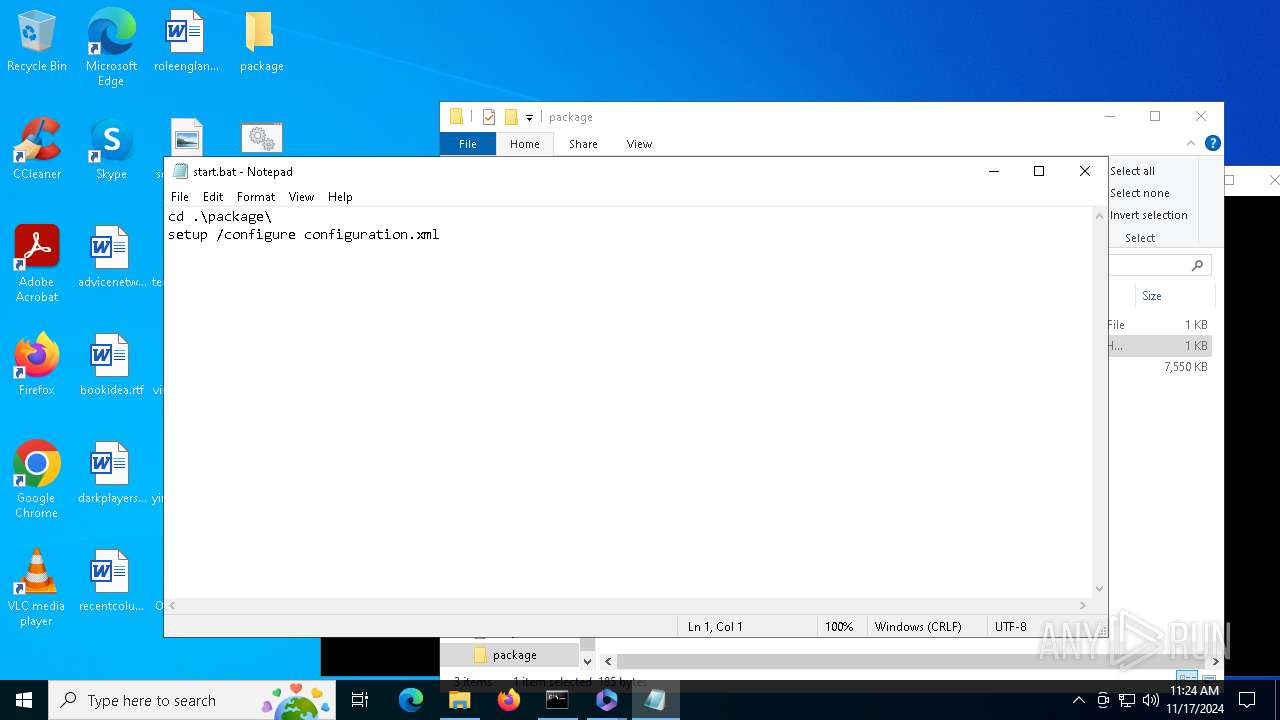
Executing commands from a ".bat" file
- Office_2024_EN_64Bits.exe (PID: 1336)
Starts CMD.EXE for commands execution
- Office_2024_EN_64Bits.exe (PID: 1336)
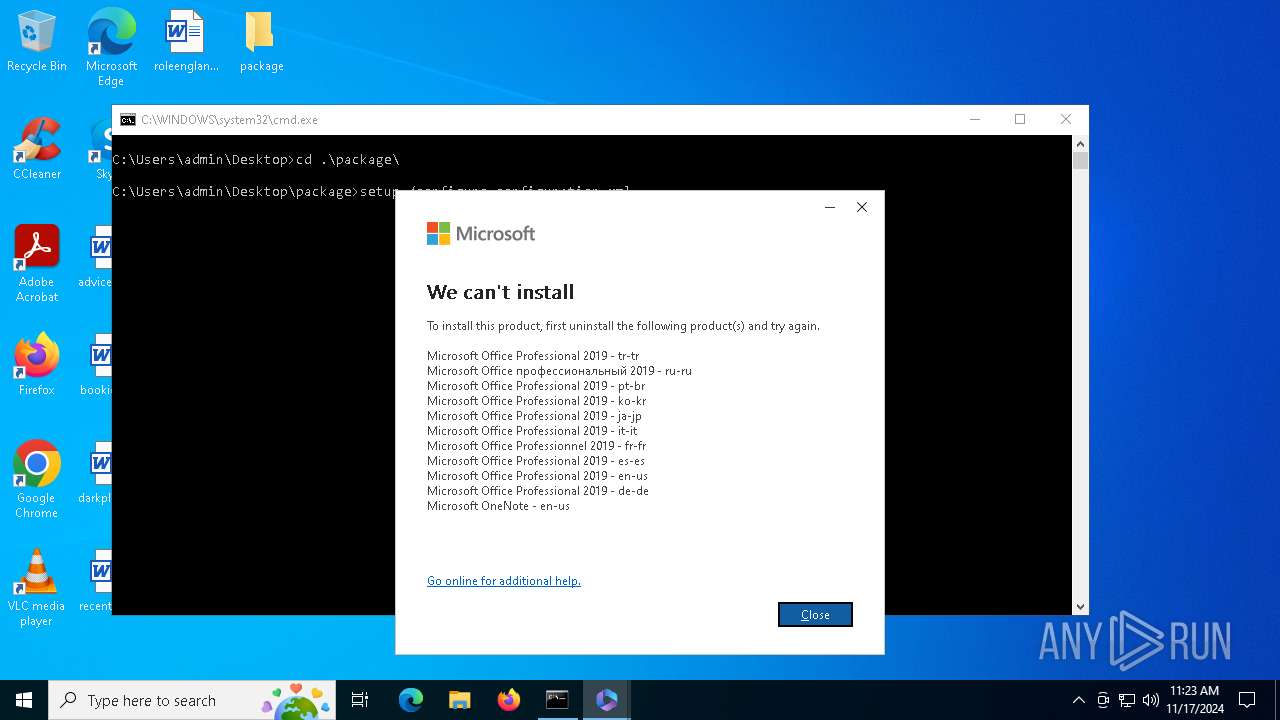
Starts a Microsoft application from unusual location
- setup.exe (PID: 3648)
- setup.exe (PID: 6752)
Reads Internet Explorer settings
- Office_2024_EN_64Bits.exe (PID: 1336)
Application launched itself
- setup.exe (PID: 3648)
INFO
Checks supported languages
- Office_2024_EN_64Bits.exe (PID: 1336)
- setup.exe (PID: 3648)
Reads the computer name
- Office_2024_EN_64Bits.exe (PID: 1336)
- setup.exe (PID: 3648)
Checks proxy server information
- Office_2024_EN_64Bits.exe (PID: 1336)
- setup.exe (PID: 3648)
The process uses the downloaded file
- Office_2024_EN_64Bits.exe (PID: 1336)
- setup.exe (PID: 3648)
Process checks computer location settings
- Office_2024_EN_64Bits.exe (PID: 1336)
- setup.exe (PID: 3648)
Reads the machine GUID from the registry
- setup.exe (PID: 3648)
Process checks whether UAC notifications are on
- setup.exe (PID: 3648)
Creates files or folders in the user directory
- setup.exe (PID: 3648)
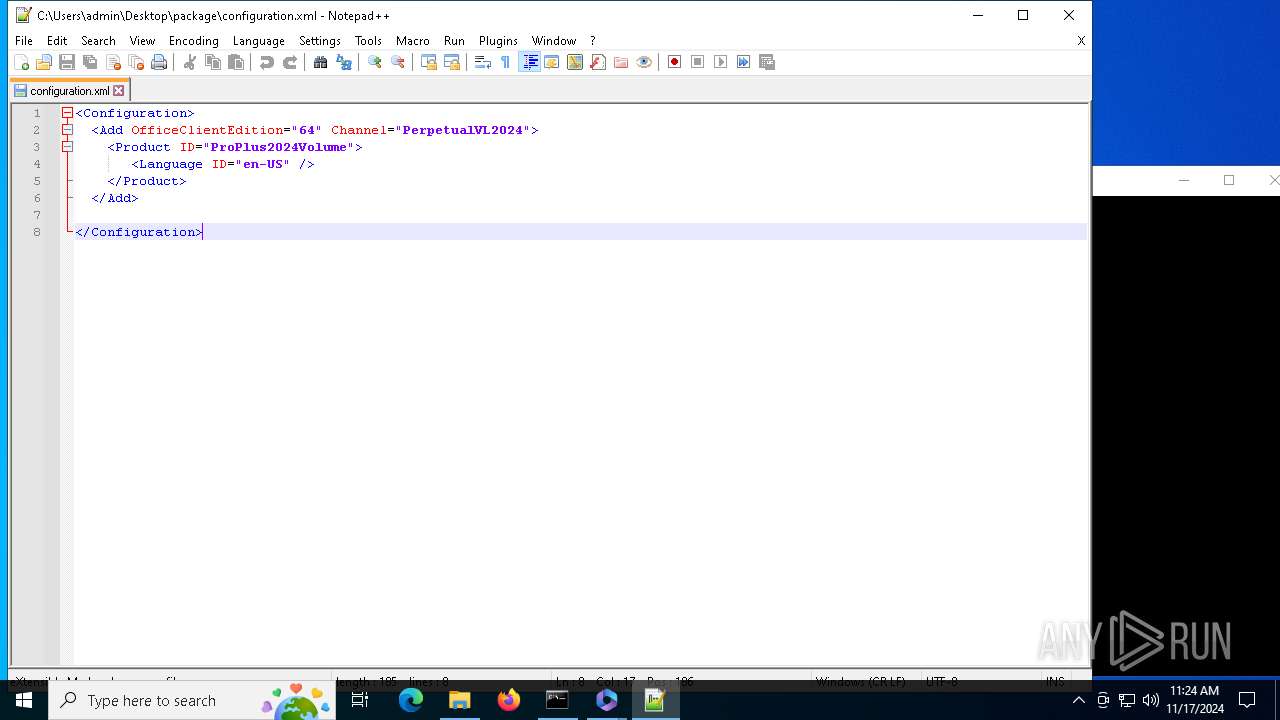
Manual execution by a user
- notepad++.exe (PID: 7144)
- notepad.exe (PID: 4956)
Sends debugging messages
- notepad++.exe (PID: 7144)
Reads Microsoft Office registry keys
- setup.exe (PID: 3648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:03 07:51:19+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 214528 |
| InitializedDataSize: | 263680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x21d50 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
142
Monitored processes
9
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 764 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\start.bat" " | C:\Windows\SysWOW64\cmd.exe | — | Office_2024_EN_64Bits.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1336 | "C:\Users\admin\Desktop\Office_2024_EN_64Bits.exe" | C:\Users\admin\Desktop\Office_2024_EN_64Bits.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
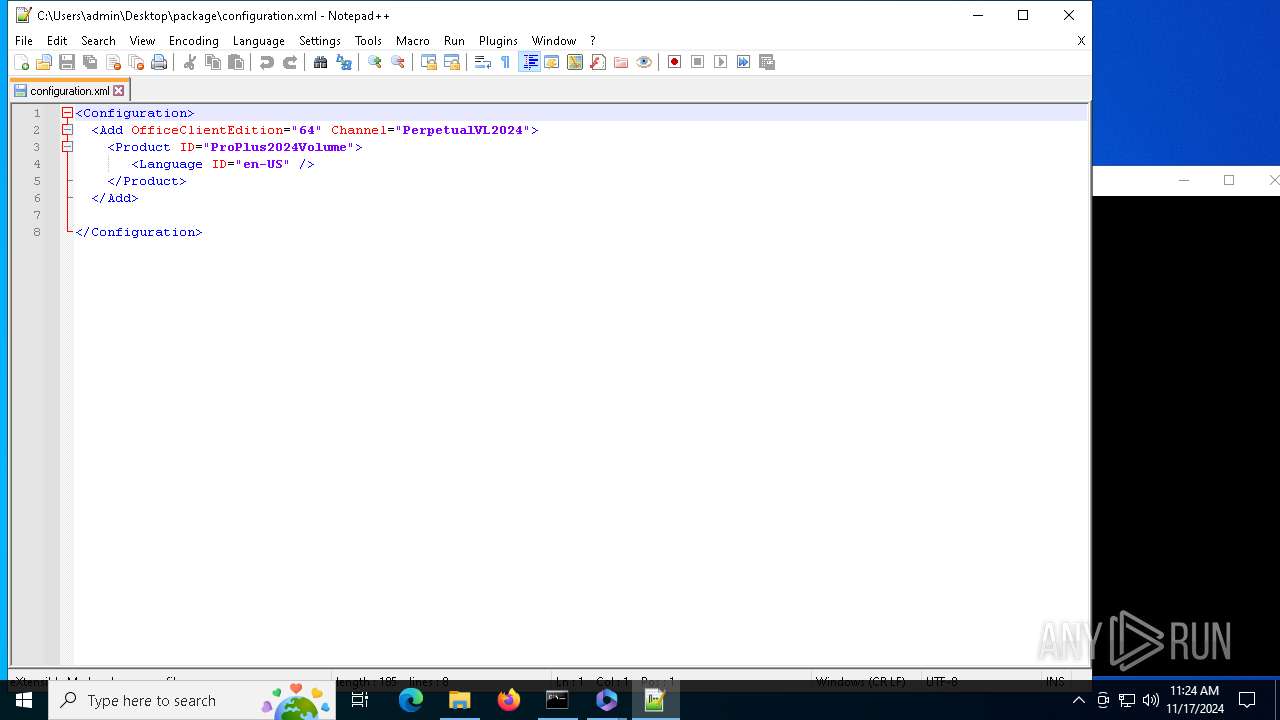
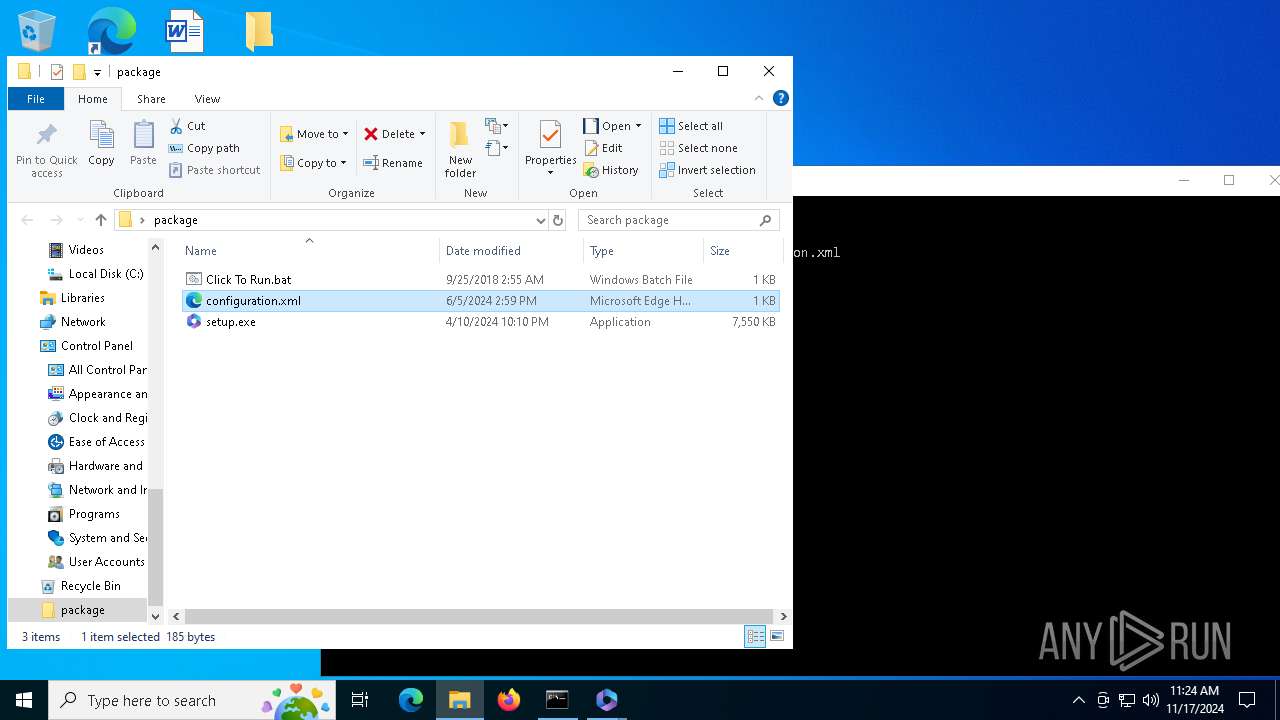
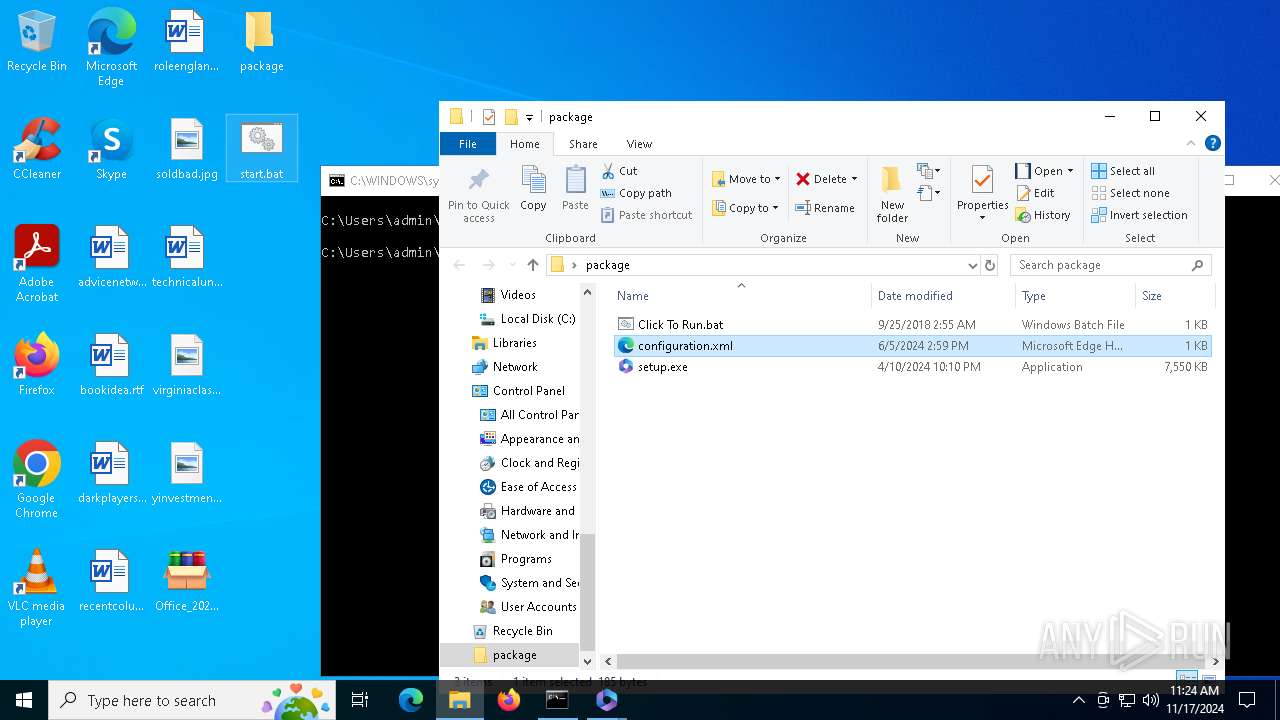
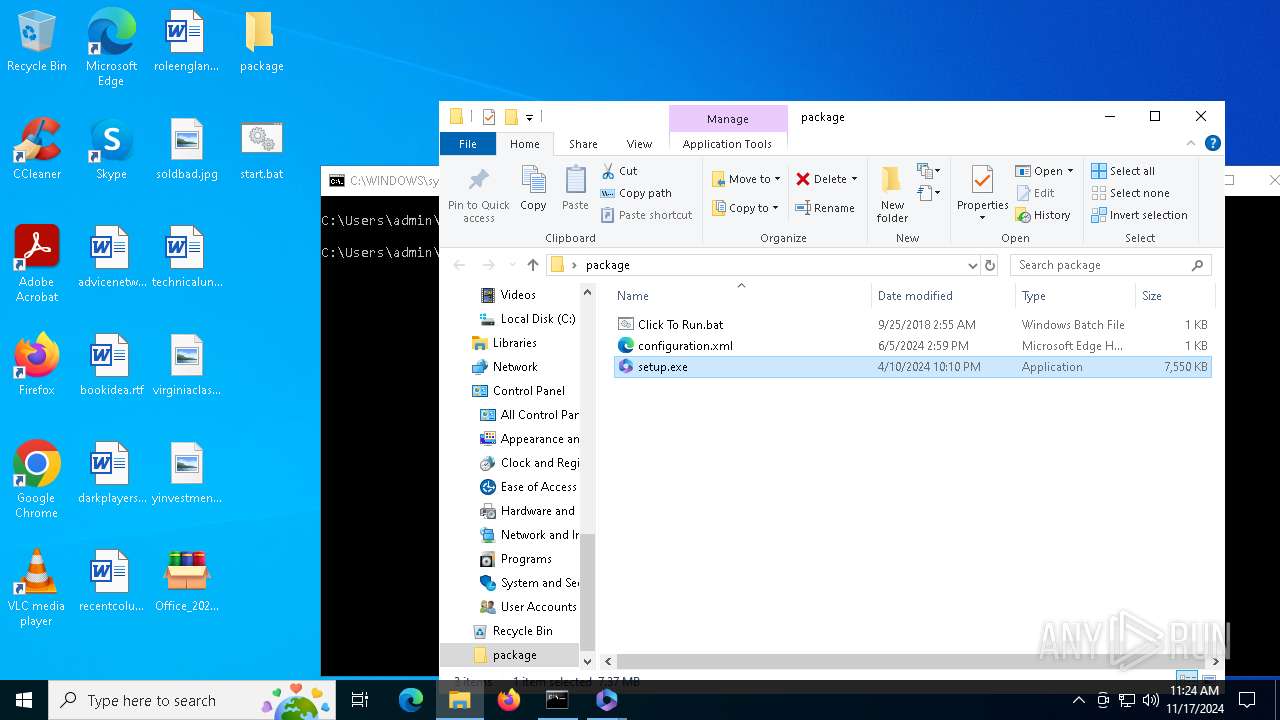
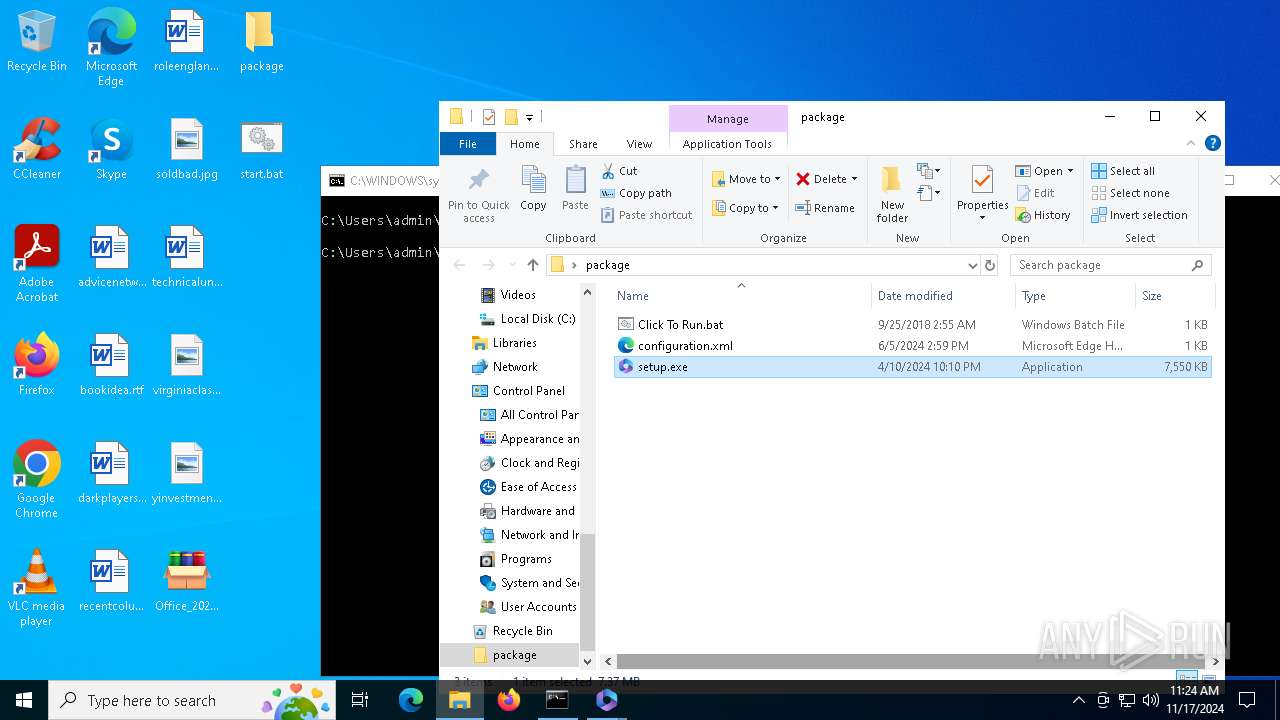
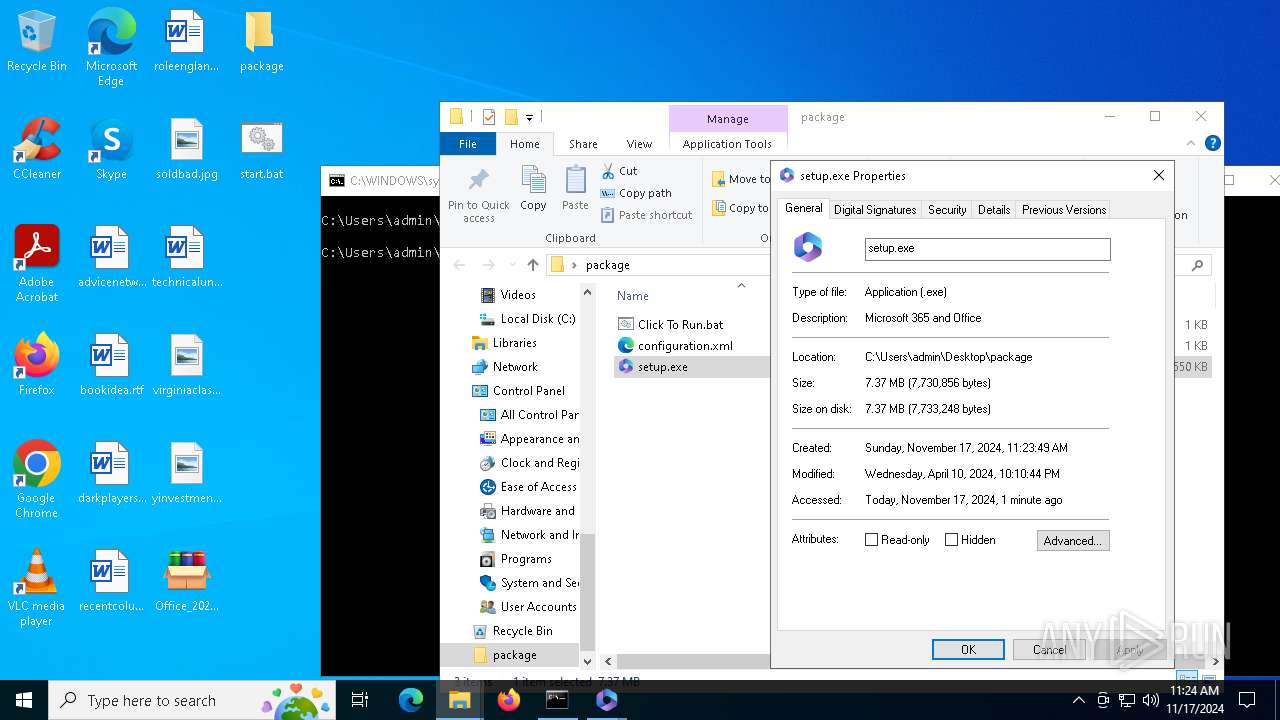
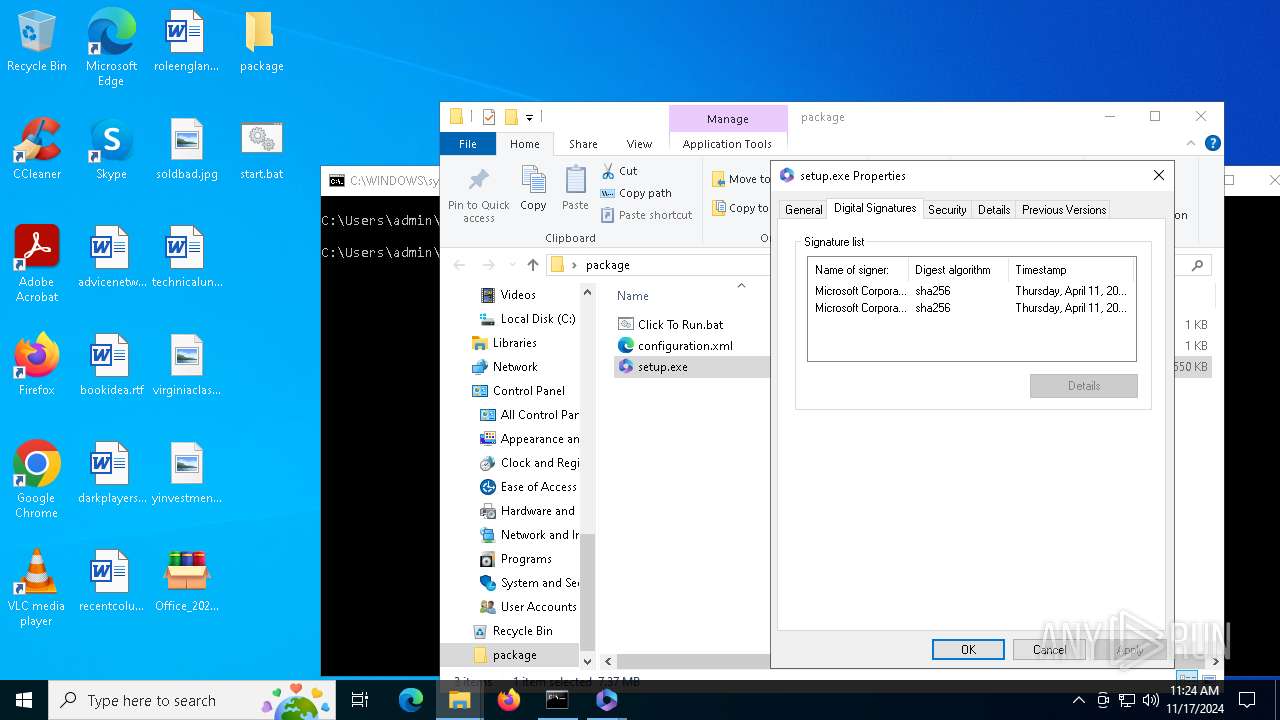
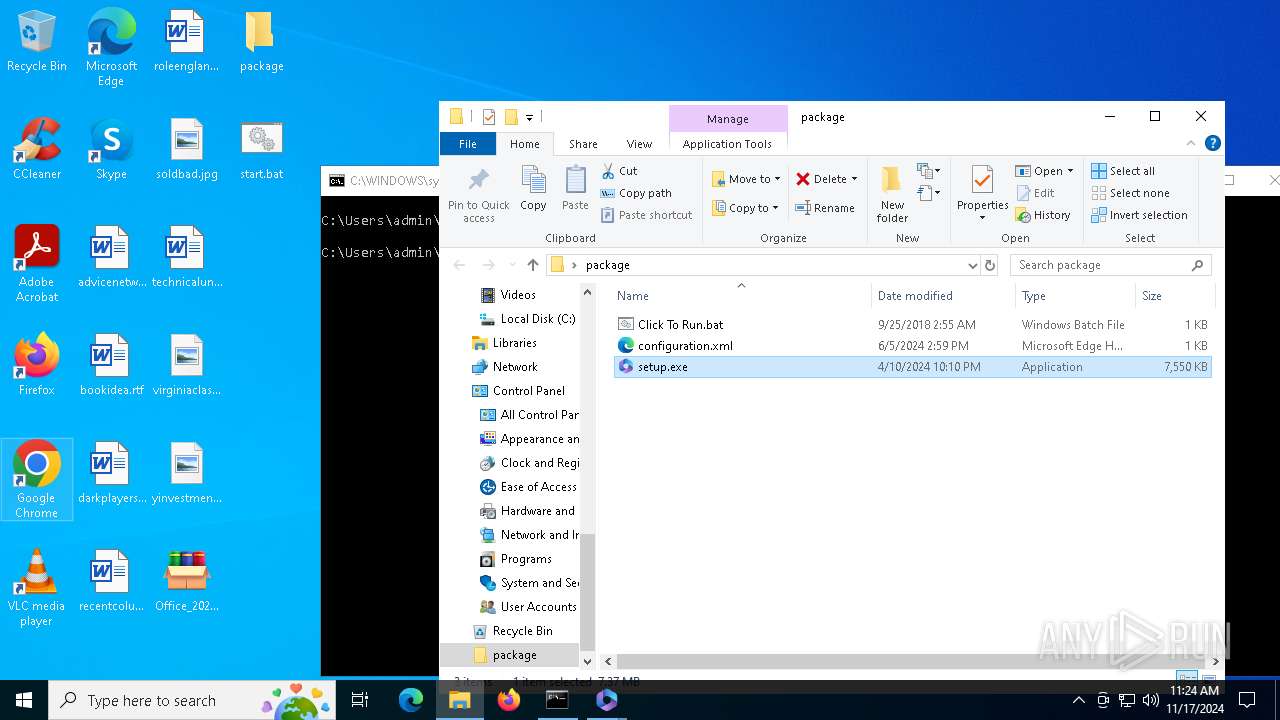
| 3648 | setup /configure configuration.xml | C:\Users\admin\Desktop\package\setup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft 365 and Office Version: 16.0.17531.20046 Modules
| |||||||||||||||
| 4956 | "C:\WINDOWS\System32\NOTEPAD.EXE" C:\Users\admin\Desktop\start.bat | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6400 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6752 | "C:\Users\admin\Desktop\package\setup.exe" ELEVATED sid=S-1-5-21-1693682860-607145093-2874071422-1001 /configure configuration.xml | C:\Users\admin\Desktop\package\setup.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft 365 and Office Version: 16.0.17531.20046 Modules
| |||||||||||||||
| 6792 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7144 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\package\configuration.xml" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
Total events
4 959
Read events
4 833
Write events
122
Delete events
4
Modification events
| (PID) Process: | (1336) Office_2024_EN_64Bits.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1336) Office_2024_EN_64Bits.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1336) Office_2024_EN_64Bits.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3648) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (3648) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (3648) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (3648) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (3648) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (3648) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (3648) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
Executable files
1
Suspicious files
7
Text files
10
Unknown types
0
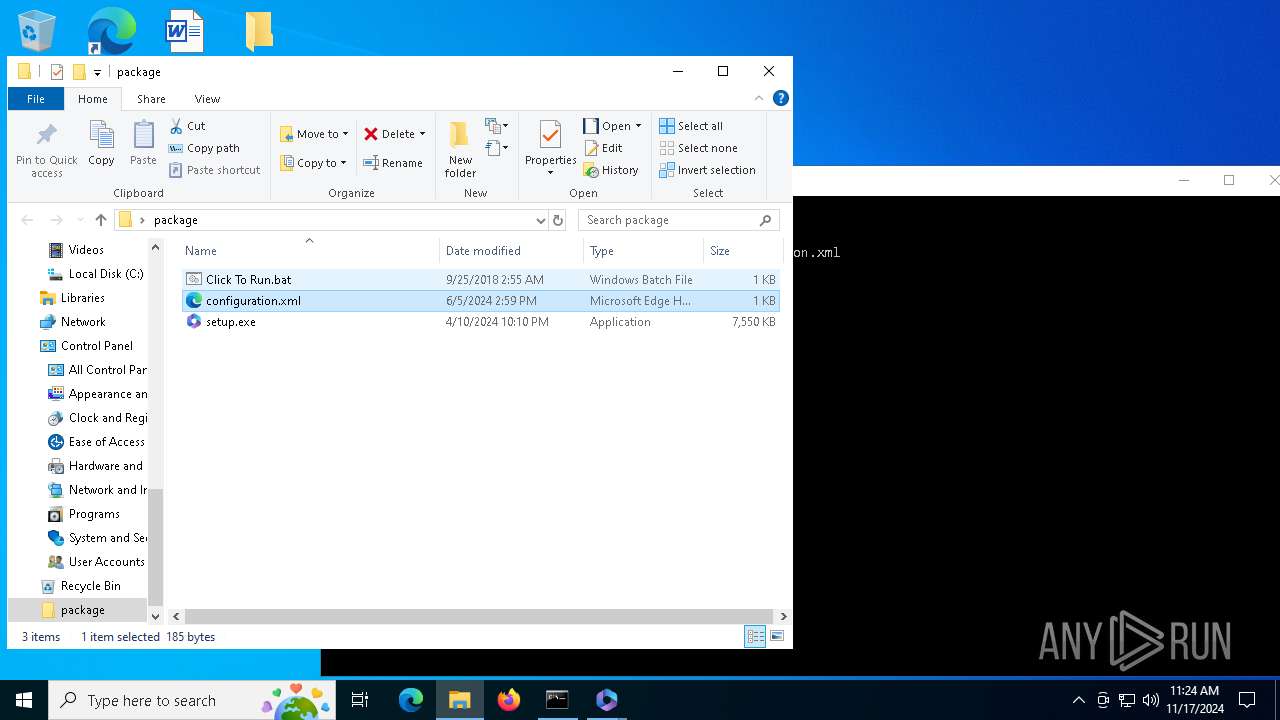
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6752 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | der | |
MD5:E34B3AB4EA53C6D5A01D1B51521EB189 | SHA256:5A42F5EE06AFDD9CD1CCCDA0F21700740E00DD6729424C4581CE4BE753FA6A55 | |||
| 6752 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\setup.exe.db | binary | |
MD5:D0DE7DB24F7B0C0FE636B34E253F1562 | SHA256:B6DC74E4A39FFA38ED8C93D58AADEB7E7A0674DAC1152AF413E9DA7313ADE6ED | |||
| 1336 | Office_2024_EN_64Bits.exe | C:\Users\admin\Desktop\package\setup.exe | executable | |
MD5:7488D696F9A3D74E093B4C31EF7282C6 | SHA256:B03C4CC3C1377EE81B1F94DA126E58A30F484D4D935889538FAE1C650DD6828B | |||
| 6752 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\setup.exe.db-shm | binary | |
MD5:A3A0F40F730B05F71180FE7F45DBF3C9 | SHA256:2B81083D332460762D2565BBB1281BD96DF166D6027A8CBF1BF312B7EB6D9B16 | |||
| 3648 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\setup.exe.db-journal | binary | |
MD5:EACE0DBAAD133C0166D7C26E6835A2DB | SHA256:2E45D8C2E876A38573DBEB235D9AAC5152BE0567EE120900405DCDBF0ACA37B2 | |||
| 7144 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:312281C4126FA897EF21A7E8CCB8D495 | SHA256:53B4BE3ED1CFD712E53542B30CFE30C5DB35CC48BE7C57727DFEC26C9E882E90 | |||
| 3648 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\7C5E5A51-575C-4A93-8CC4-7C4F3ADAD554 | xml | |
MD5:50505C22382E76AD0B8B21DF041EC53B | SHA256:0A22DC3A265F9A6AD25E8F20EE3F348105E4798F7724E3CE473B23CA6BC9F870 | |||
| 7144 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
| 7144 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:F11D96162BC521F5CF49FFE6B6841C9B | SHA256:BE9AEAEAB5A2E4899BA7E582274BA592C1B9BAF688B340A754B8EF32B23CFA9C | |||
| 7144 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:E9C3519DD2E1A87E6356D256C791D9E5 | SHA256:C7FD1A79116CC66BB2CC987BFC104FED5120C19784031F9FE7889E9775B545FB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
39
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 23.48.23.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
6752 | setup.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
2364 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6152 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
6152 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2464 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3648 | setup.exe | 52.109.76.240:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3648 | setup.exe | 52.113.194.132:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6944 | svchost.exe | 23.48.23.194:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6752 | setup.exe | 52.113.194.132:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
mobile.events.data.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|