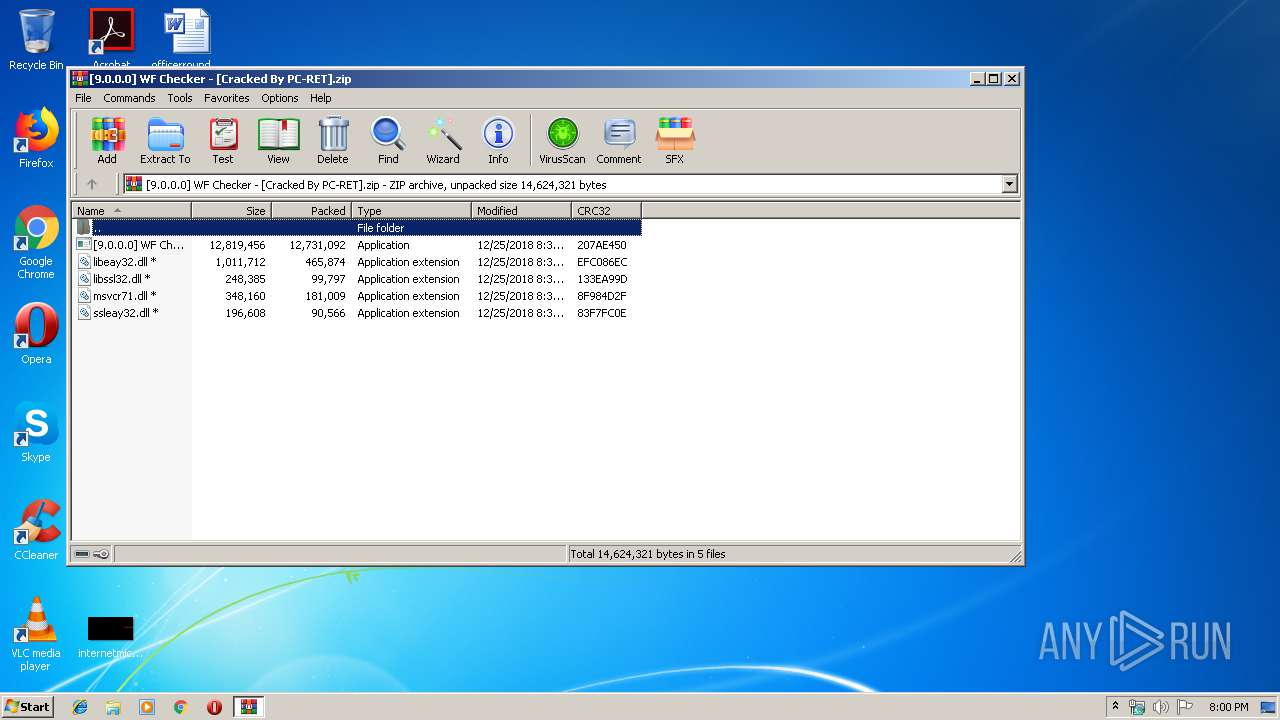
| File name: | [9.0.0.0] WF Checker - [Cracked By PC-RET].zip |
| Full analysis: | https://app.any.run/tasks/322f26ef-abf6-4381-af30-fa8d375ad539 |
| Verdict: | Malicious activity |
| Analysis date: | January 03, 2020, 19:59:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | DF5529B3C02A1DB9DE69741027301897 |
| SHA1: | 5634B42A1E879A5E0EB9DE10F3648D165B880E82 |
| SHA256: | 014E9D5C87B8DE138071B3B0A52F982C0330ED67906A1D00EB1C7EB455661AF5 |
| SSDEEP: | 393216:hL8rMQhUTlIQ0U1xaA3hY423b3z7kmuYDU:oM+qItUSsYRr3bTU |
MALICIOUS
Application was dropped or rewritten from another process
- [9.0.0.0] WF Checker.exe (PID: 2168)
Loads dropped or rewritten executable
- [9.0.0.0] WF Checker.exe (PID: 2168)
- SearchProtocolHost.exe (PID: 3528)
SUSPICIOUS
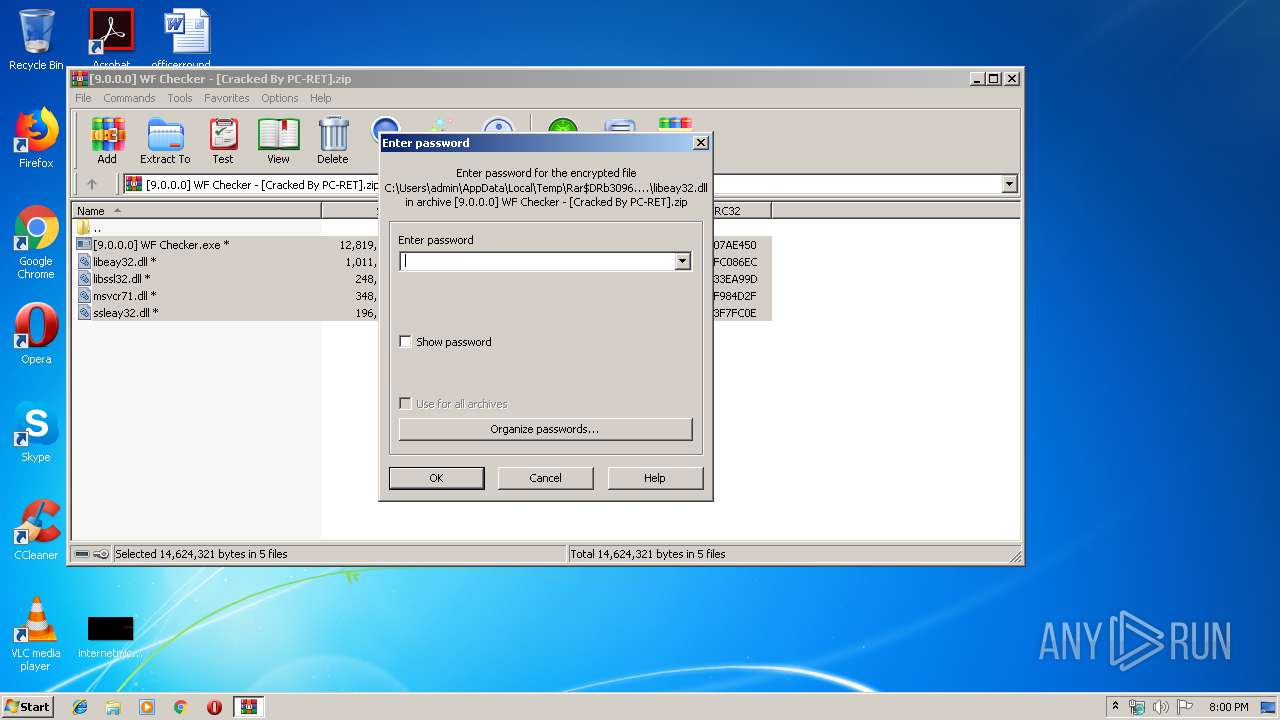
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3096)
- [9.0.0.0] WF Checker.exe (PID: 2168)
INFO
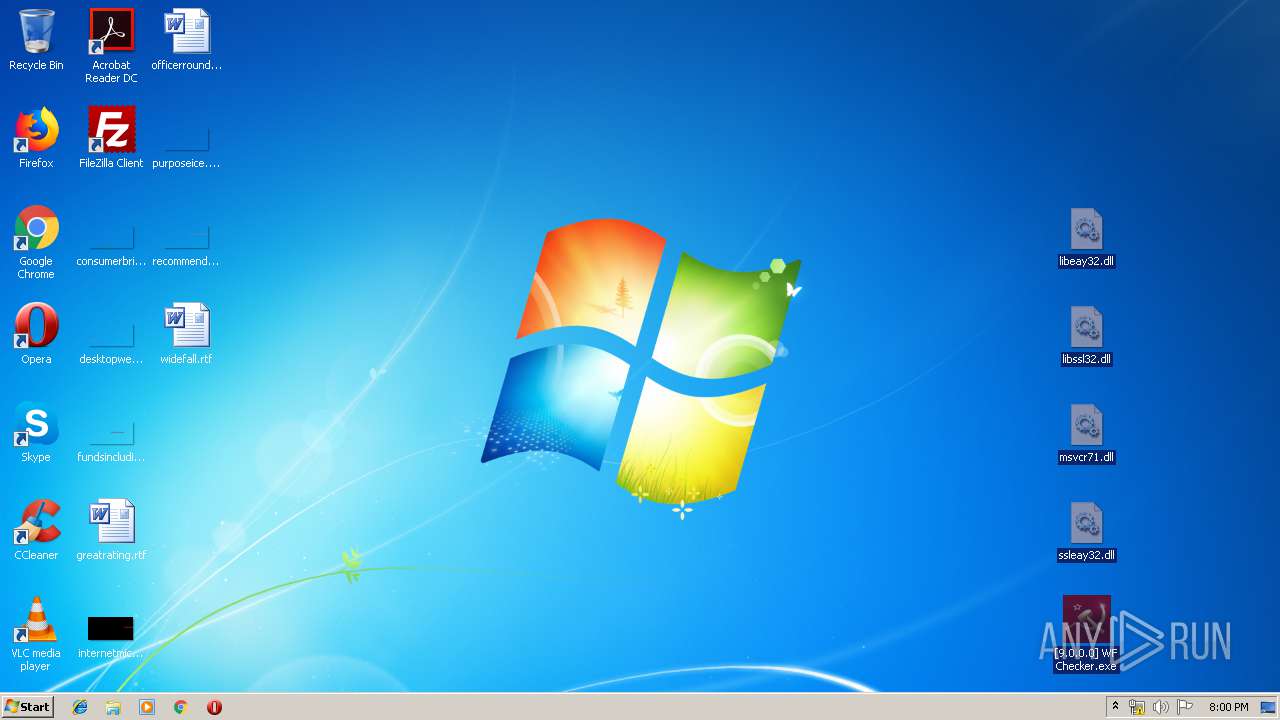
Manual execution by user
- [9.0.0.0] WF Checker.exe (PID: 2168)
Reads the hosts file
- [9.0.0.0] WF Checker.exe (PID: 2168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:12:25 11:32:06 |
| ZipCRC: | 0xefc086ec |
| ZipCompressedSize: | 465874 |
| ZipUncompressedSize: | 1011712 |
| ZipFileName: | libeay32.dll |
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2168 | "C:\Users\admin\Desktop\[9.0.0.0] WF Checker.exe" | C:\Users\admin\Desktop\[9.0.0.0] WF Checker.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3096 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\[9.0.0.0] WF Checker - [Cracked By PC-RET].zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3528 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
478
Read events
458
Write events
20
Delete events
0
Modification events
| (PID) Process: | (3096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3096) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\[9.0.0.0] WF Checker - [Cracked By PC-RET].zip | |||
| (PID) Process: | (3096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (3096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
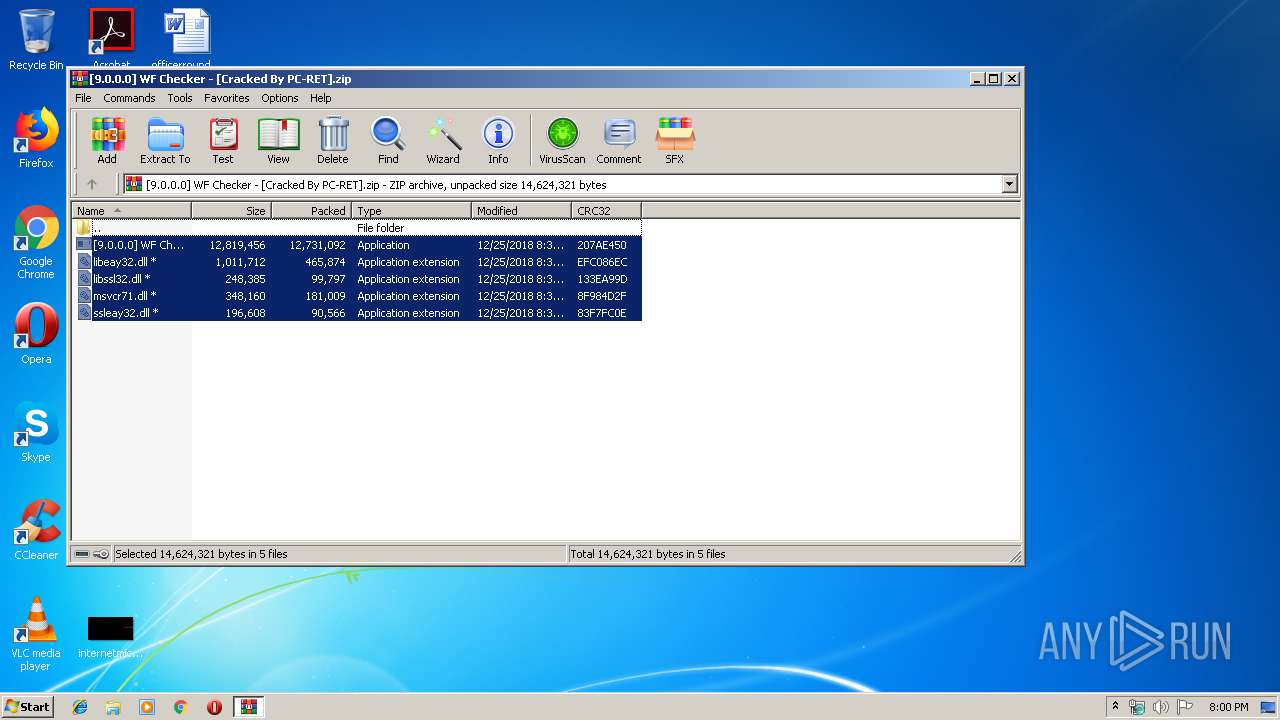
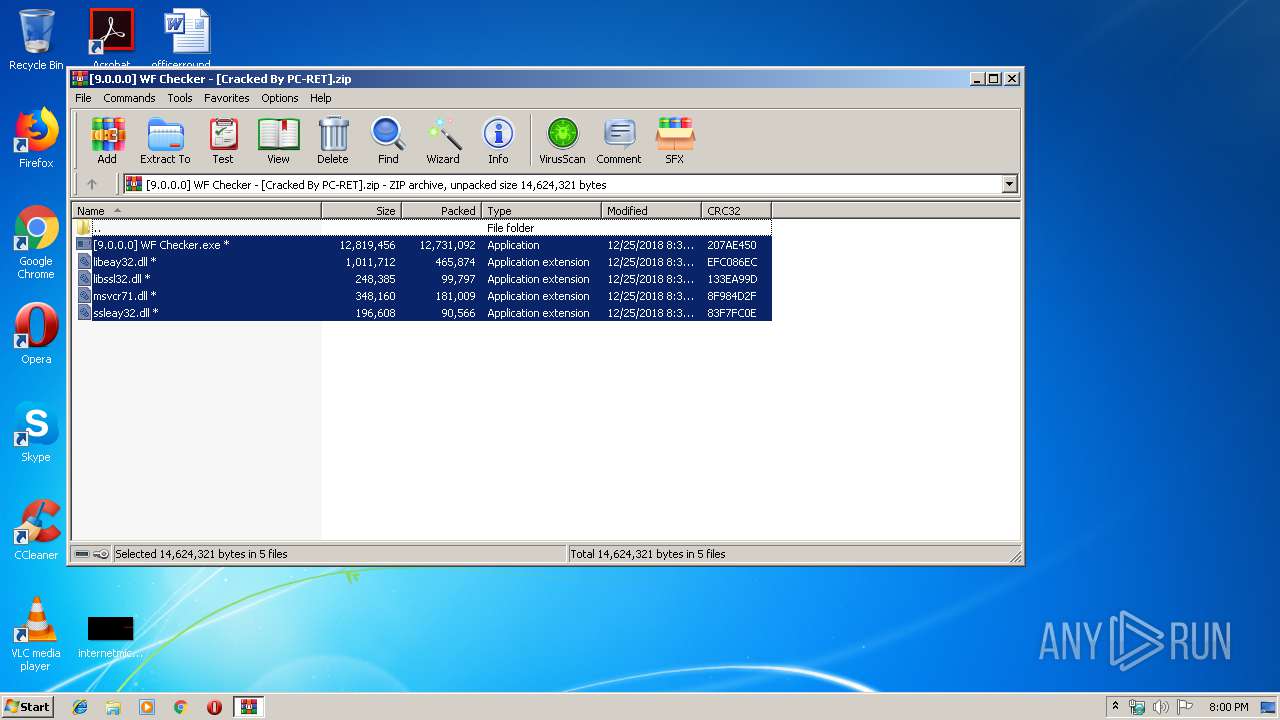
Dropped files
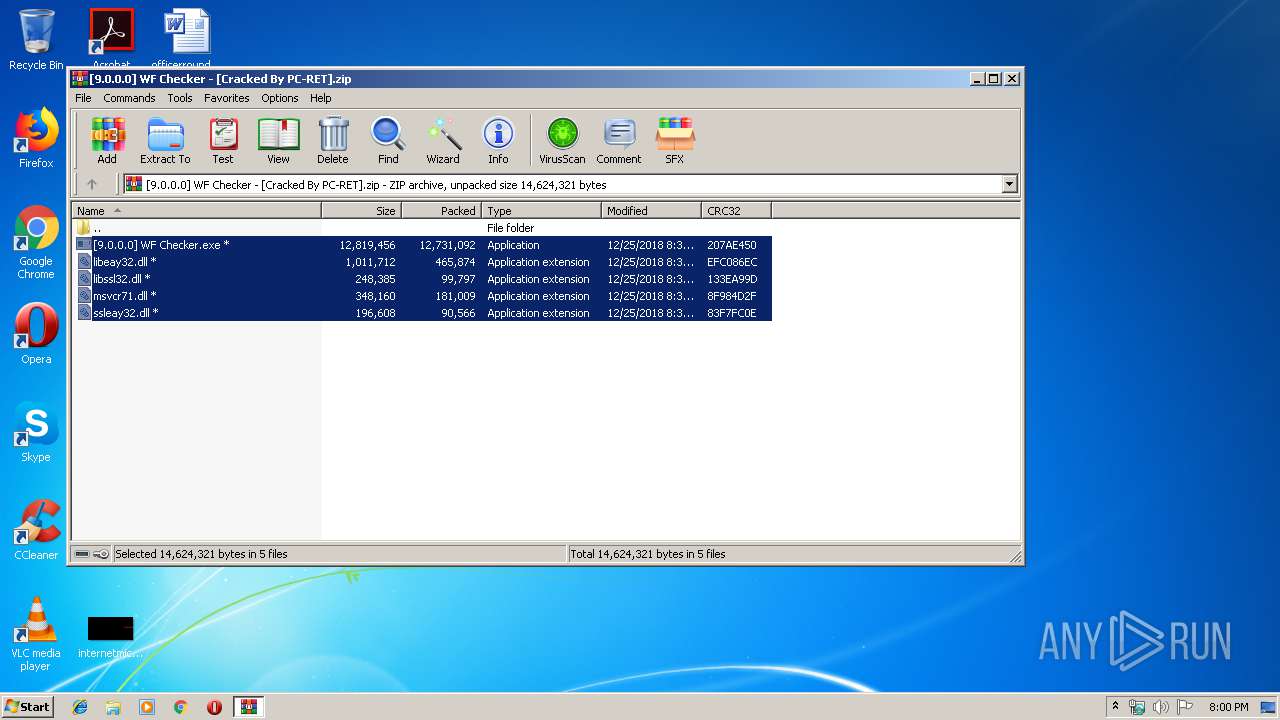
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3096 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3096.12960\libeay32.dll | — | |
MD5:— | SHA256:— | |||
| 3096 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3096.12960\libssl32.dll | — | |
MD5:— | SHA256:— | |||
| 3096 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3096.12960\msvcr71.dll | — | |
MD5:— | SHA256:— | |||
| 3096 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3096.12960\ssleay32.dll | — | |
MD5:— | SHA256:— | |||
| 3096 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3096.12960\[9.0.0.0] WF Checker.exe | executable | |
MD5:— | SHA256:— | |||
| 2168 | [9.0.0.0] WF Checker.exe | C:\Users\admin\AppData\Local\Temp\evb88CF.tmp | executable | |
MD5:— | SHA256:— | |||
| 2168 | [9.0.0.0] WF Checker.exe | C:\Users\admin\AppData\Local\Temp\evb8870.tmp | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
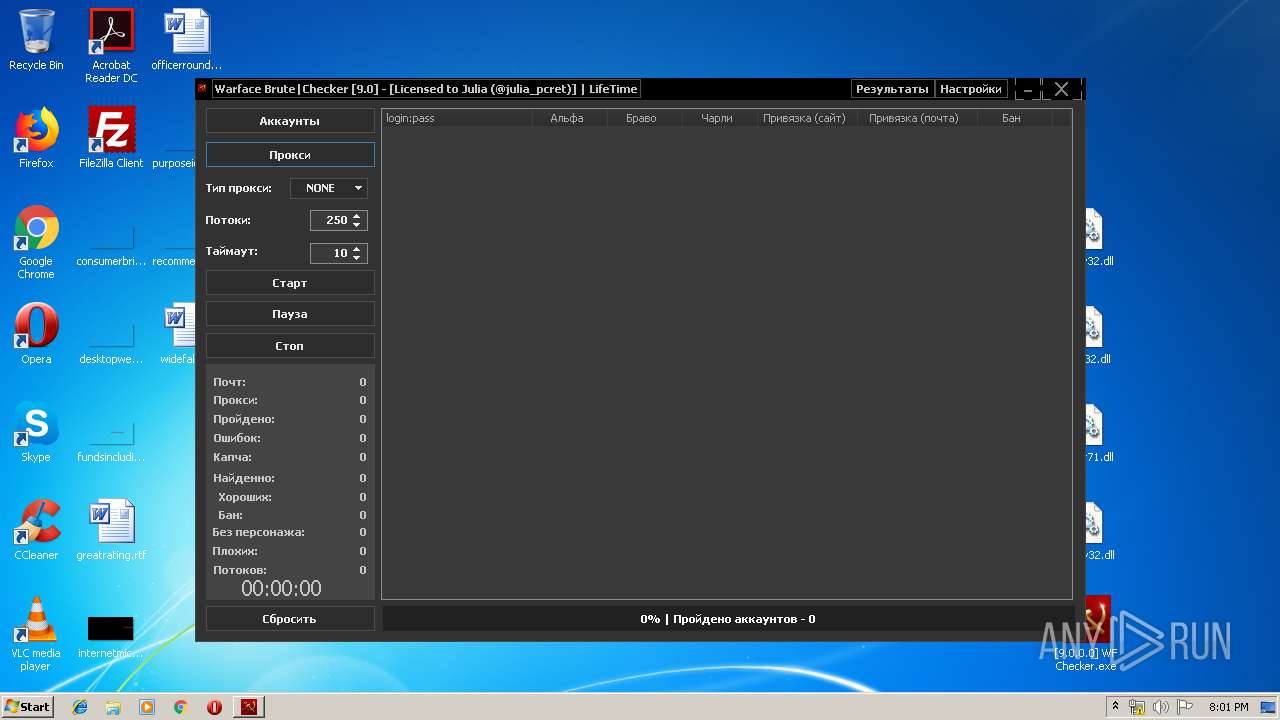
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
1
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2168 | [9.0.0.0] WF Checker.exe | POST | 200 | 185.179.191.128:80 | http://pushfd.su/PC-RET/Minaev_WFSoftWare/license.php | RU | text | 172 b | suspicious |
2168 | [9.0.0.0] WF Checker.exe | POST | 200 | 185.179.191.128:80 | http://pushfd.su/PC-RET/Minaev_WFSoftWare/token.php | RU | text | 566 b | suspicious |
2168 | [9.0.0.0] WF Checker.exe | GET | 200 | 185.179.191.128:80 | http://pushfd.su/PC-RET/Minaev_WFSoftWare/api.php?hwid=9C51577-143996E-83D7AAF-A9797A0&key=PFJTQUtleVZhbHVlPjxNb2R1bHVzPnhKcWxpLzViUUNWZFh5SGdGMGlXOVMwbGQ1aFp4eFdPUkRRam1FYzQ3MVpMRWNmMU90MTZocWZ2K08wNWVLUngzeVdkT3NqRXdQR0Z3elJDNTMrcnR2R1NyKzF4cXJlSGZnK3lpRDlpWHN5aEFJSlFMdmtLcHpPSlJTd2xZakVCdE1pblVwbHVnbXZtazAvaEk2dFVodTZJc0tKVFBob0tLWmNNQVM3aUVuVT08L01vZHVsdXM%2BPEV4cG9uZW50PkFRQUI8L0V4cG9uZW50PjwvUlNBS2V5VmFsdWU%2B | RU | text | 2.21 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2168 | [9.0.0.0] WF Checker.exe | 185.179.191.128:80 | pushfd.su | — | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pushfd.su |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
2168 | [9.0.0.0] WF Checker.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2168 | [9.0.0.0] WF Checker.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2168 | [9.0.0.0] WF Checker.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |