| File name: | PO20161_20.ISO |
| Full analysis: | https://app.any.run/tasks/3305ffac-5500-420c-a34e-e001d566c895 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 14:51:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-iso9660-image |
| File info: | UDF filesystem data (version 1.5) '' |
| MD5: | CE544902DC2547FA1316CF5E09663BA3 |
| SHA1: | 849085D7A7AC6E9F25C05722013D3D5E6FB25D46 |
| SHA256: | 0141A5D62CECA5A47A9166CC2F9EE871EF0E47D492CCCFCACB61B29A89F78944 |
| SSDEEP: | 6144:sVxX9kZV4qL69fD5x2NiRWtOBijSpujOnGktWp:UxX9kZV4D9LiwW06quqnu |
MALICIOUS
Application was dropped or rewritten from another process
- PO#20165_20.exe (PID: 3216)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2428)
Creates files in the user directory
- powershell.exe (PID: 2636)
Executes PowerShell scripts
- PO#20165_20.exe (PID: 3216)
INFO
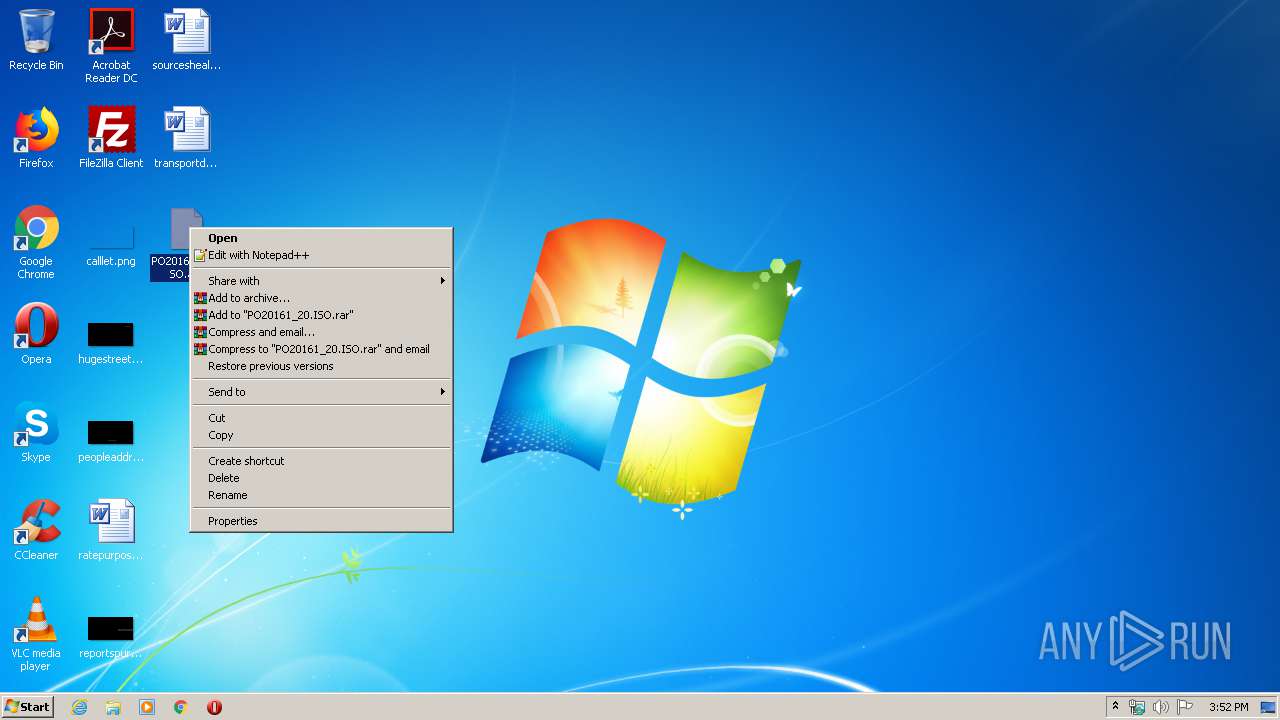
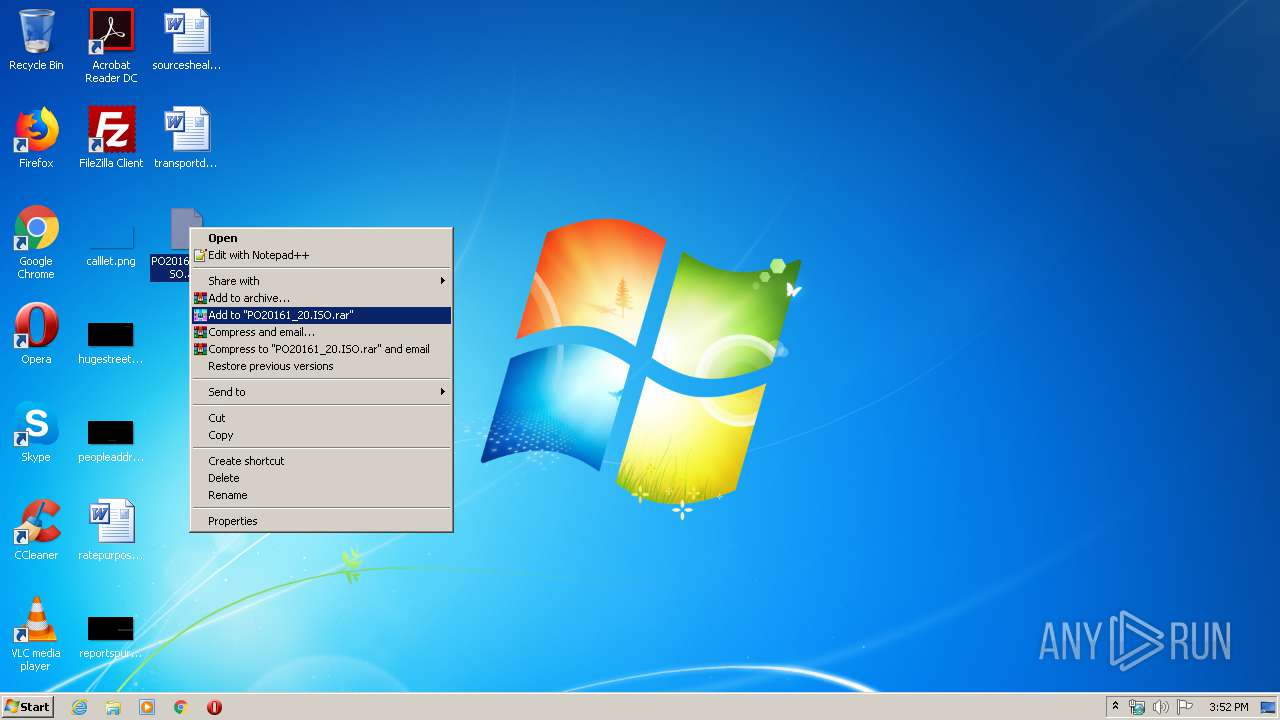
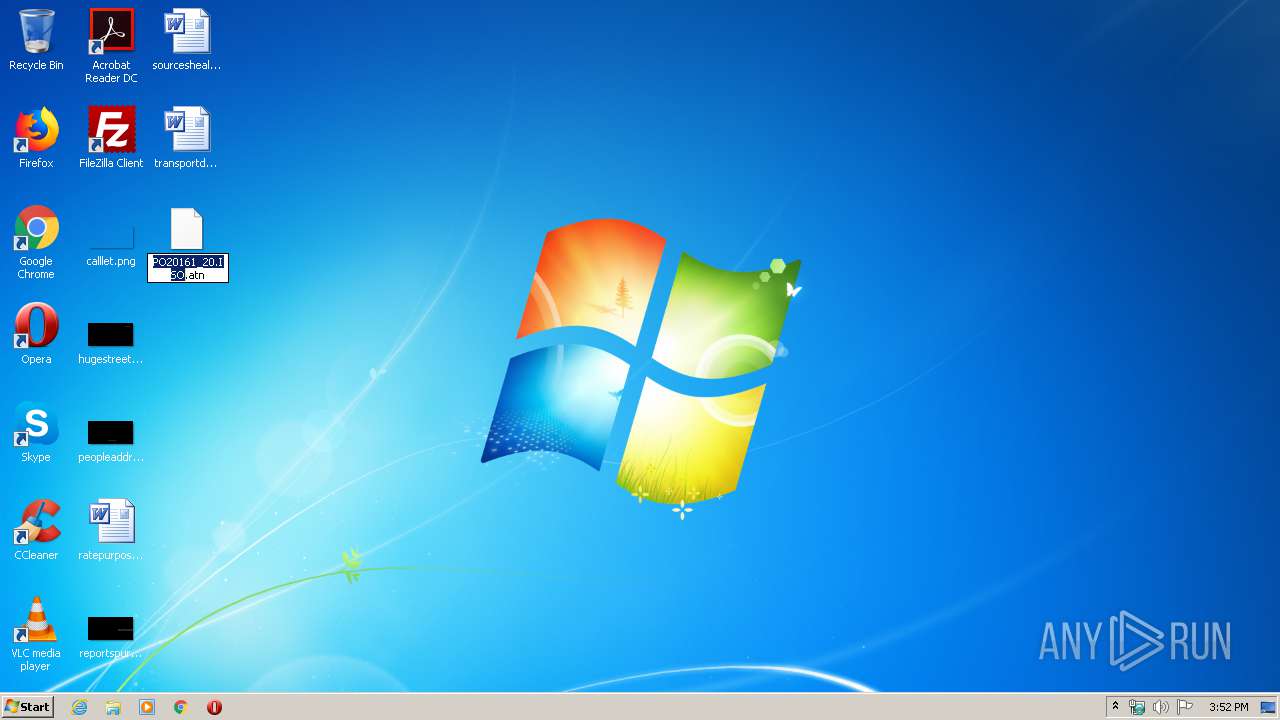
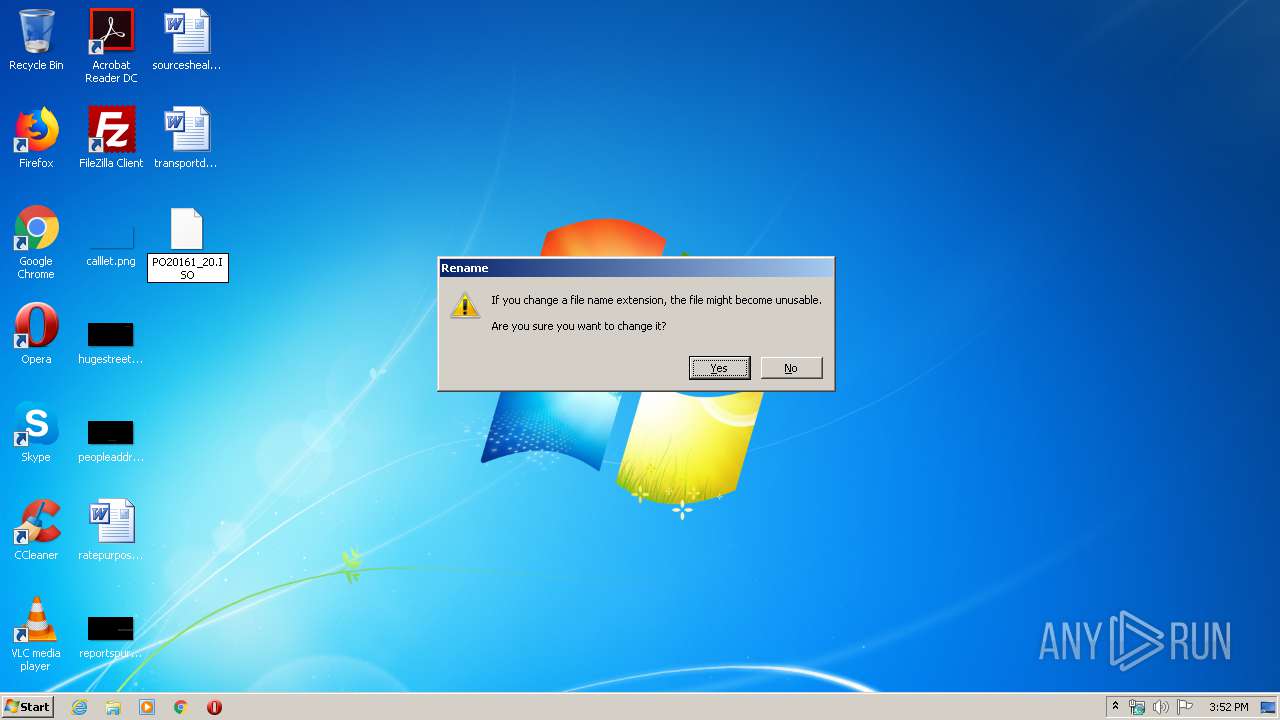
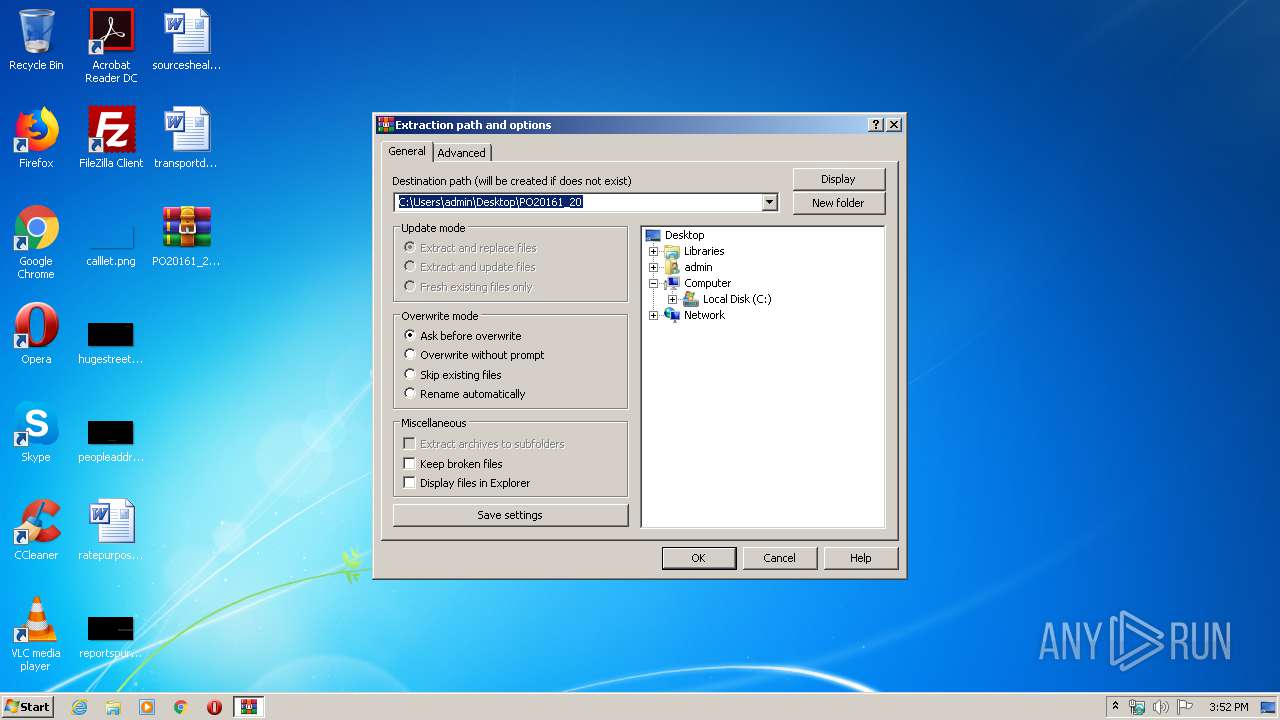
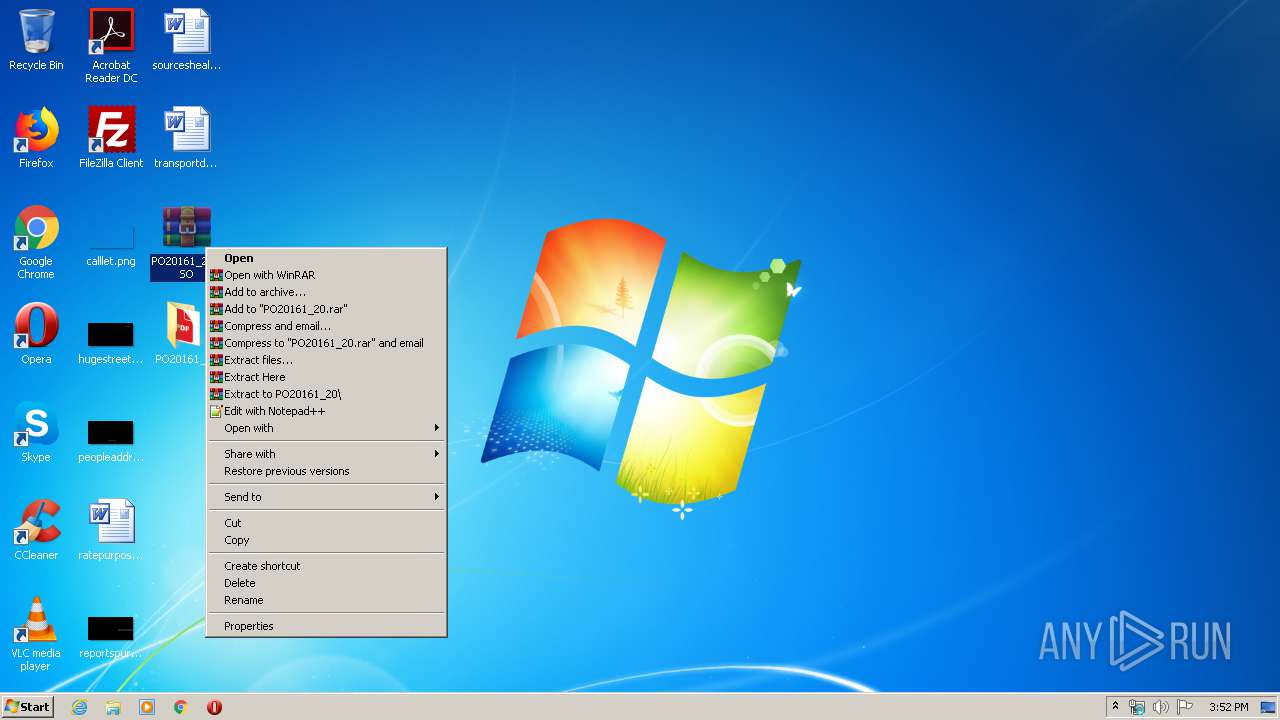
Manual execution by user
- WinRAR.exe (PID: 2428)
- PO#20165_20.exe (PID: 3216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .atn | | | Photoshop Action (37.5) |
|---|---|---|
| .gmc | | | Game Music Creator Music (8.4) |
| .abr | | | Adobe PhotoShop Brush (7.5) |
EXIF
ISO
| VolumeBlockCount: | 599 |
|---|---|
| VolumeBlockSize: | 2048 |
| RootDirectoryCreateDate: | 2020:03:25 18:26:18-07:00 |
| VolumeSetName: | UNDEFINED |
| Software: | IMGBURN V2.5.8.0 - THE ULTIMATE IMAGE BURNER! |
| VolumeCreateDate: | 2020:03:25 18:26:18.00-07:00 |
| VolumeModifyDate: | 2020:03:25 18:26:18.00-07:00 |
Composite
| VolumeSize: | 1198 kB |
|---|
Total processes
42
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
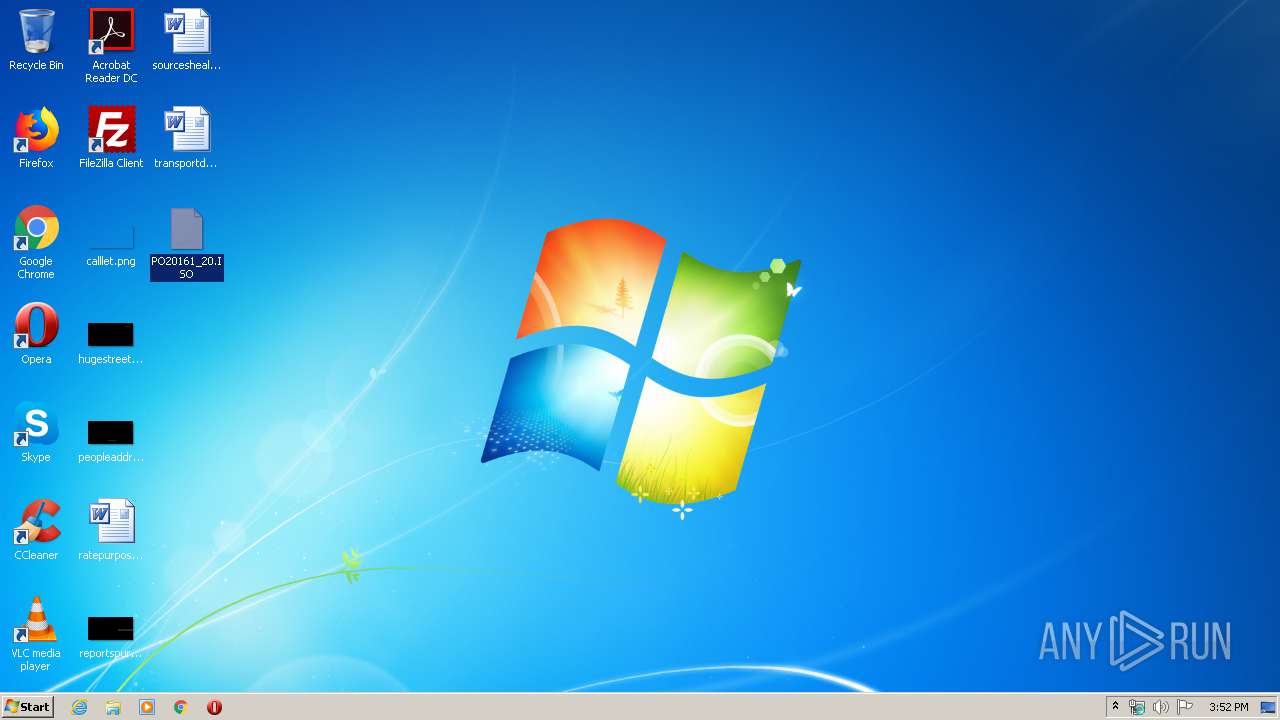
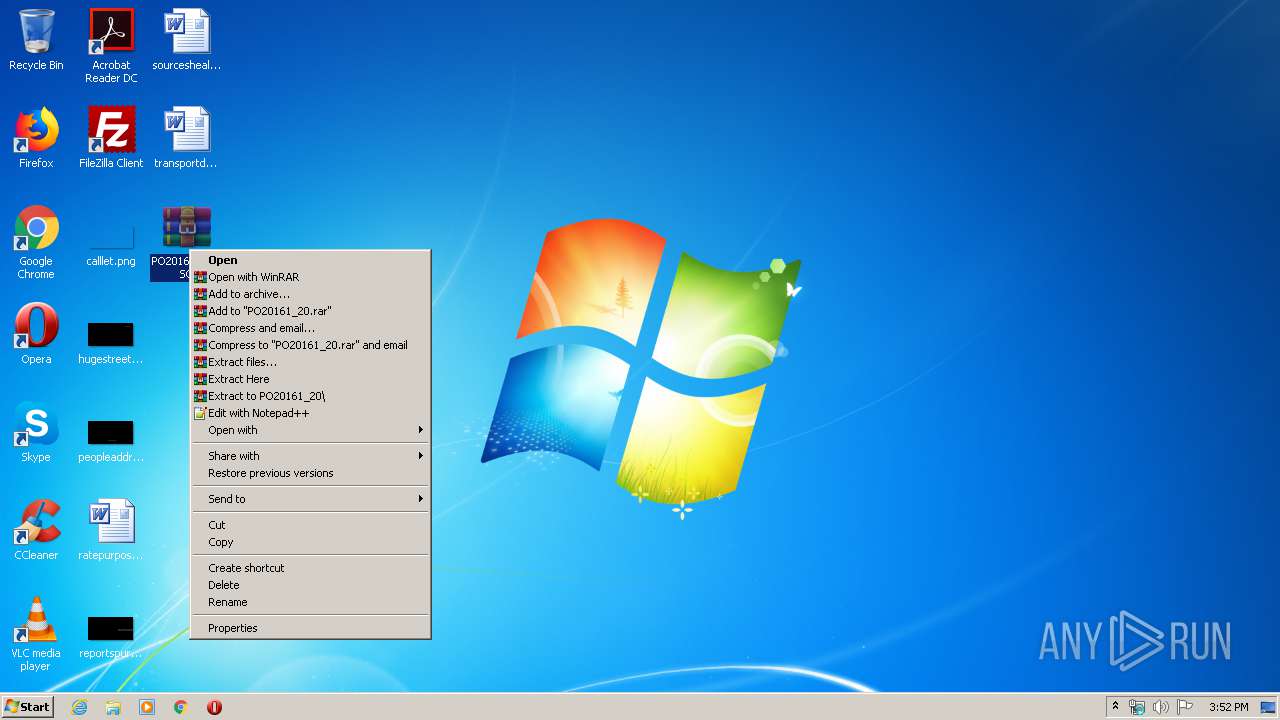
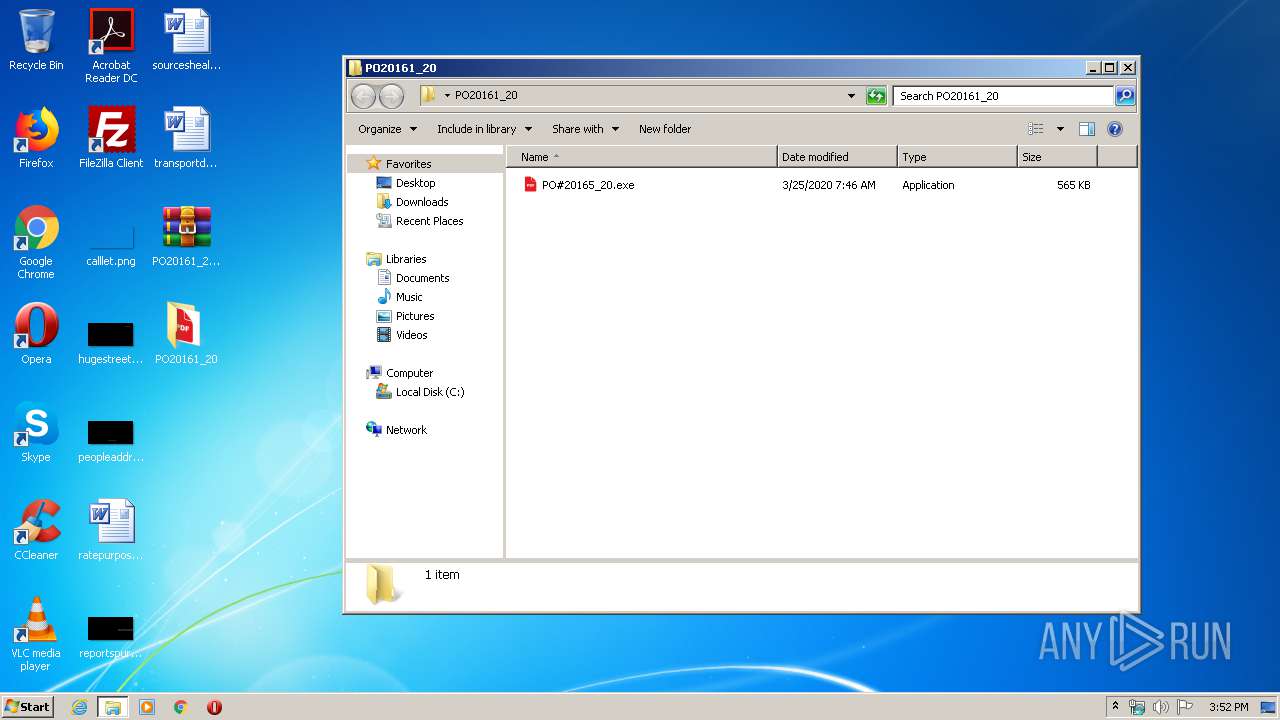
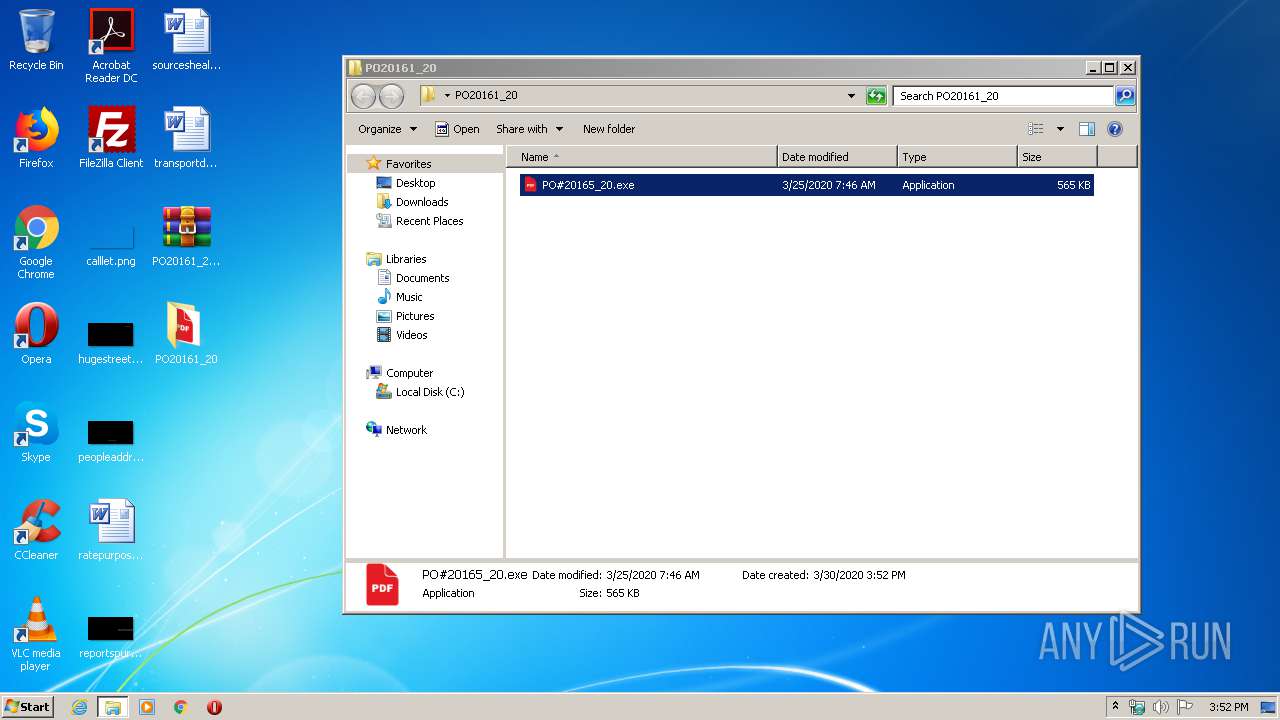
| 2428 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\PO20161_20.ISO" "?\" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2636 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -windo 1 -noexit -exec bypass -file "C:\Users\Public\xouymppp.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | PO#20165_20.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
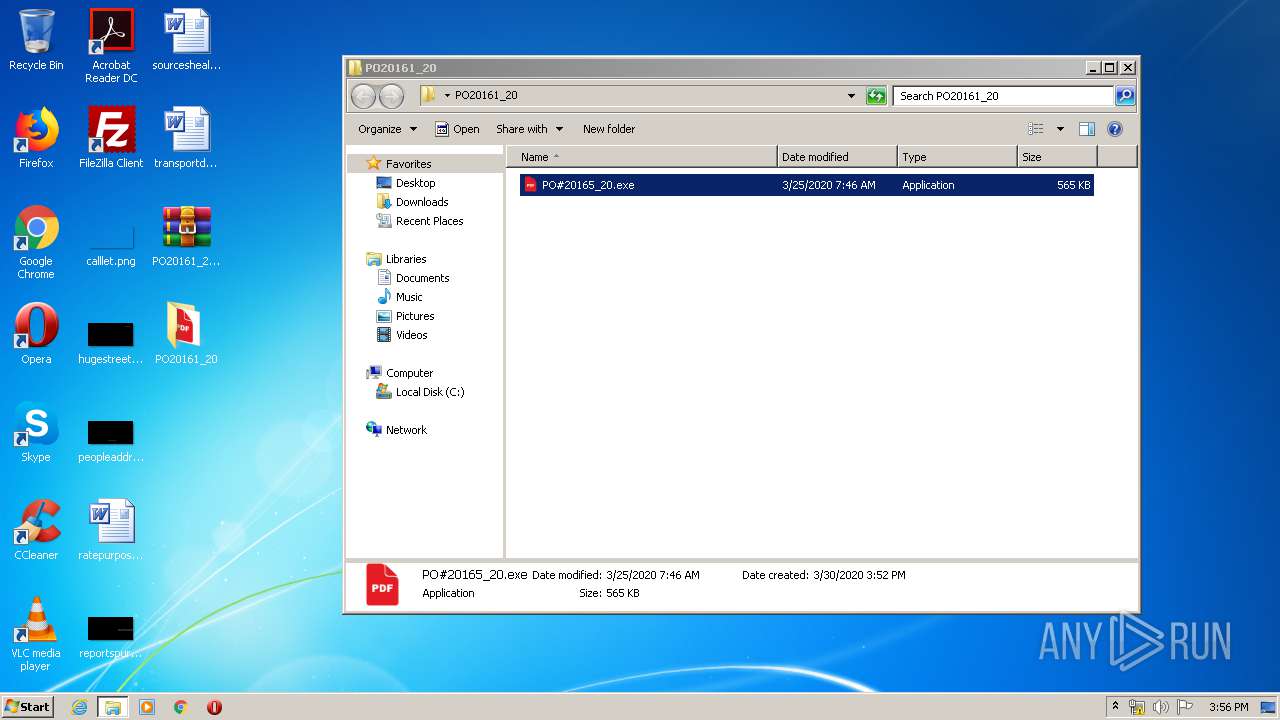
| 3216 | "C:\Users\admin\Desktop\PO20161_20\PO#20165_20.exe" | C:\Users\admin\Desktop\PO20161_20\PO#20165_20.exe | — | explorer.exe | |||||||||||
User: admin Company: Epic Games, Inc. Integrity Level: MEDIUM Description: CrashReportClient Exit code: 0 Version: 4.3.7.7 Modules
| |||||||||||||||
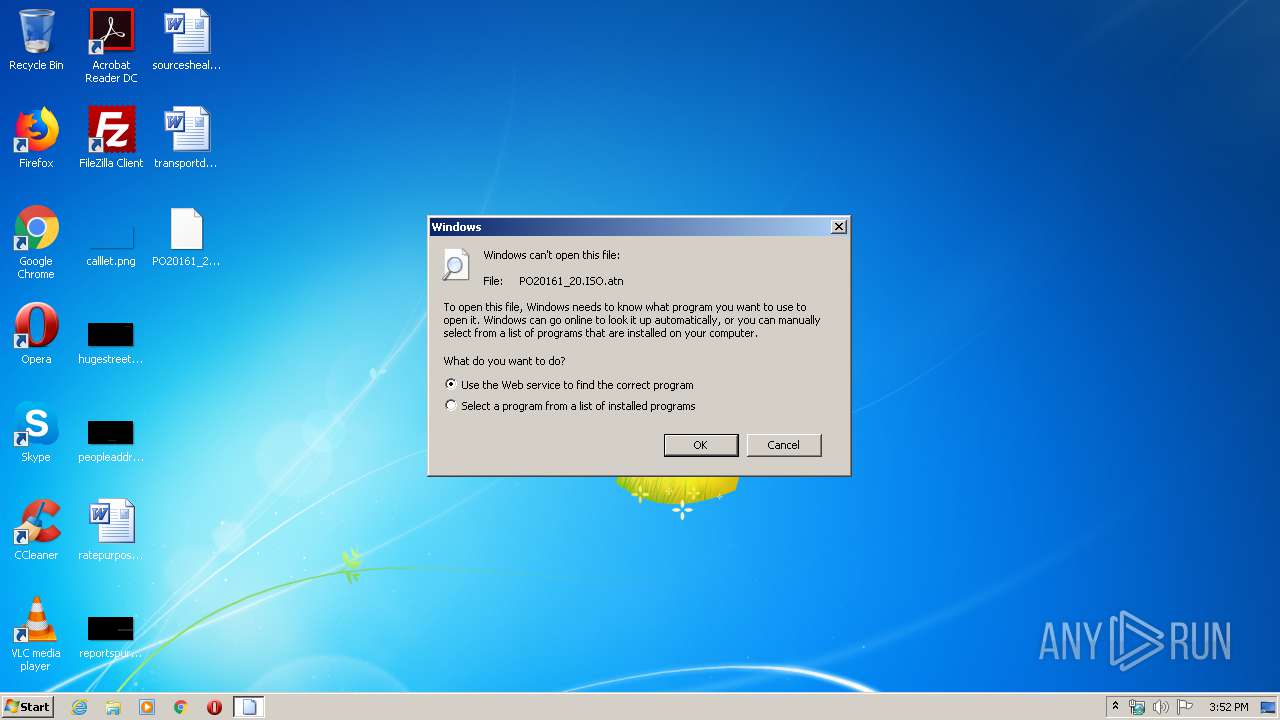
| 3820 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\PO20161_20.ISO.atn | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
418
Read events
351
Write events
67
Delete events
0
Modification events
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\PO20161_20 | |||
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2636) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3216) PO#20165_20.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2636 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\GBDUA86O04PLSGJZAPXW.temp | — | |
MD5:— | SHA256:— | |||
| 3216 | PO#20165_20.exe | C:\Users\Public\xouymppp.ps1 | text | |
MD5:— | SHA256:— | |||
| 2636 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFa6f46a.TMP | binary | |
MD5:— | SHA256:— | |||
| 2428 | WinRAR.exe | C:\Users\admin\Desktop\PO20161_20\PO#20165_20.exe | executable | |
MD5:— | SHA256:— | |||
| 2636 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report