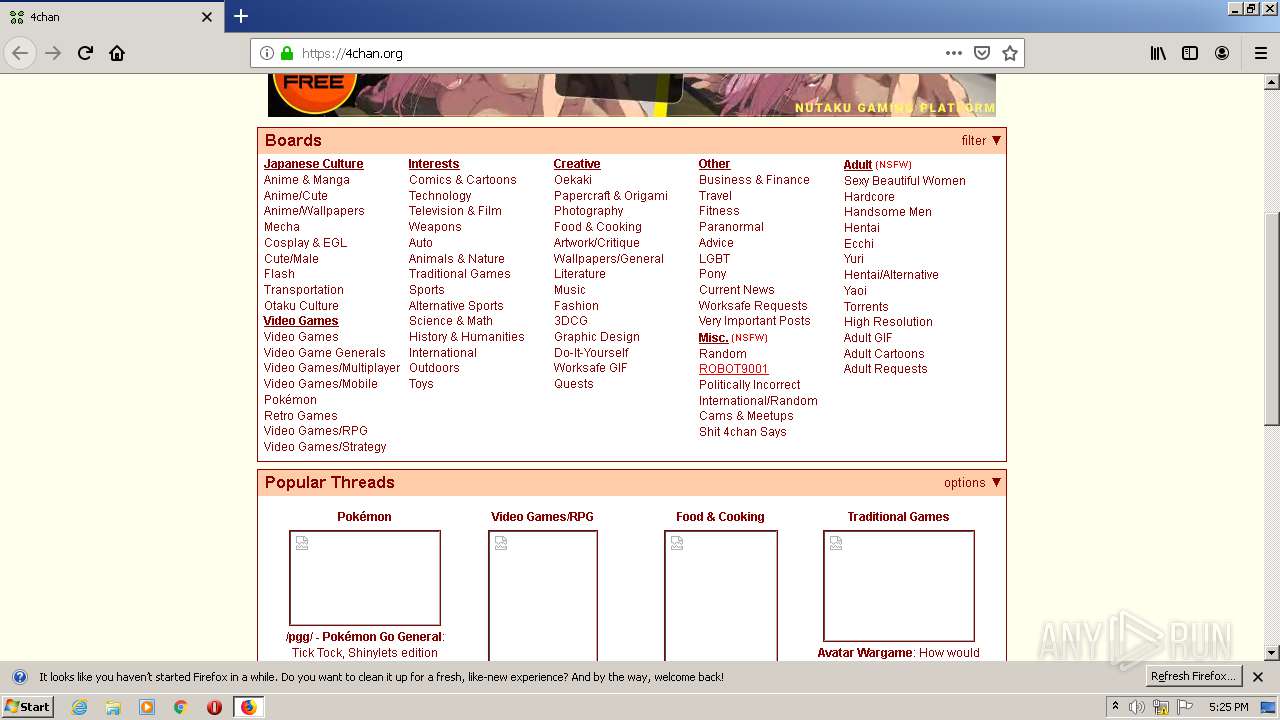
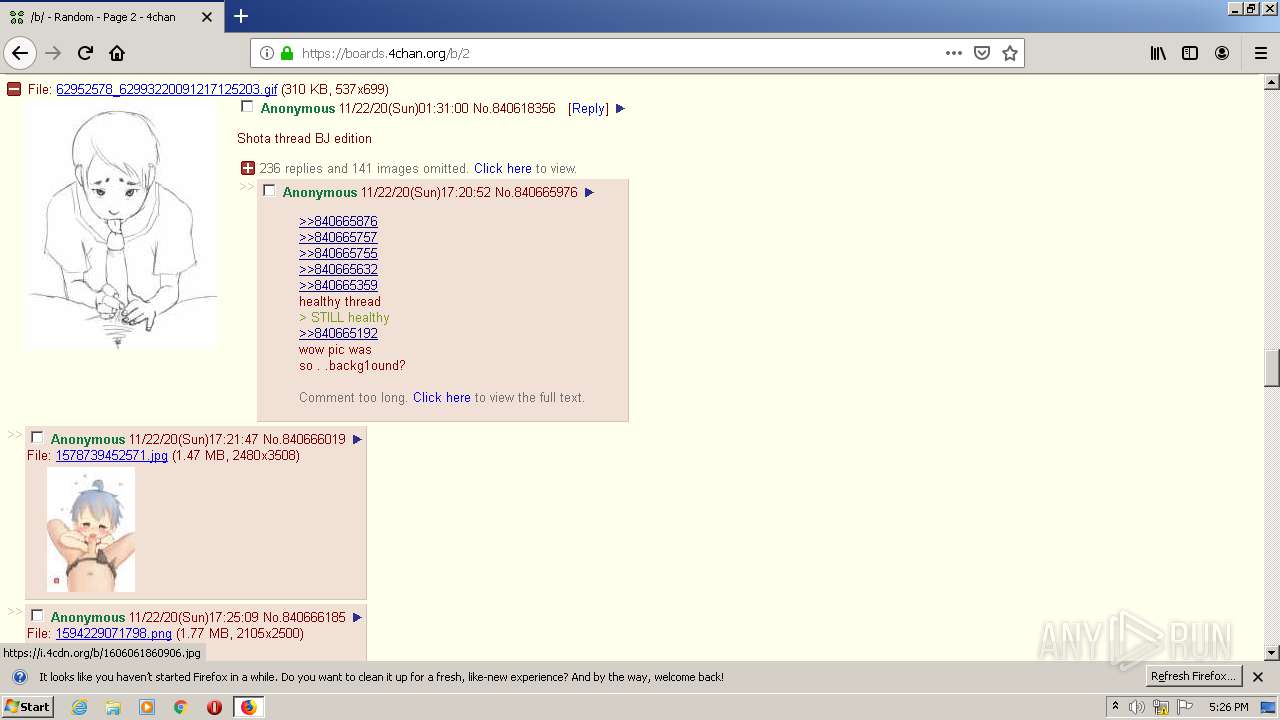
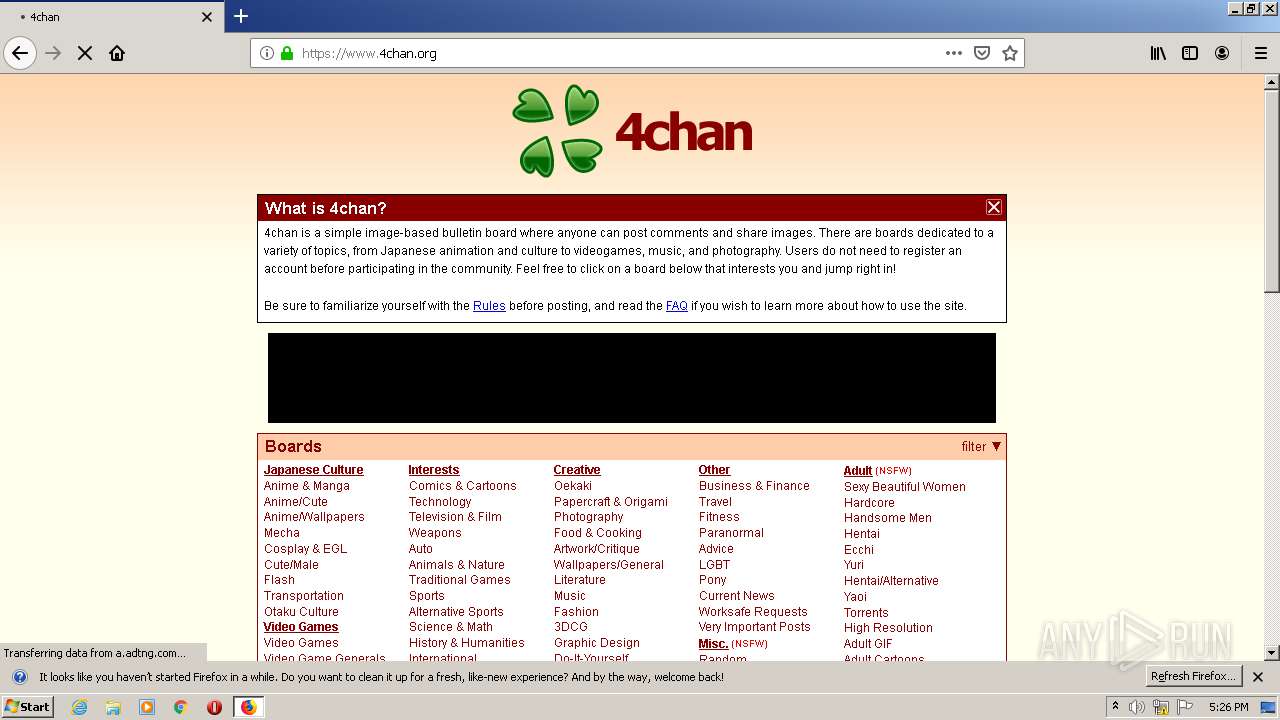
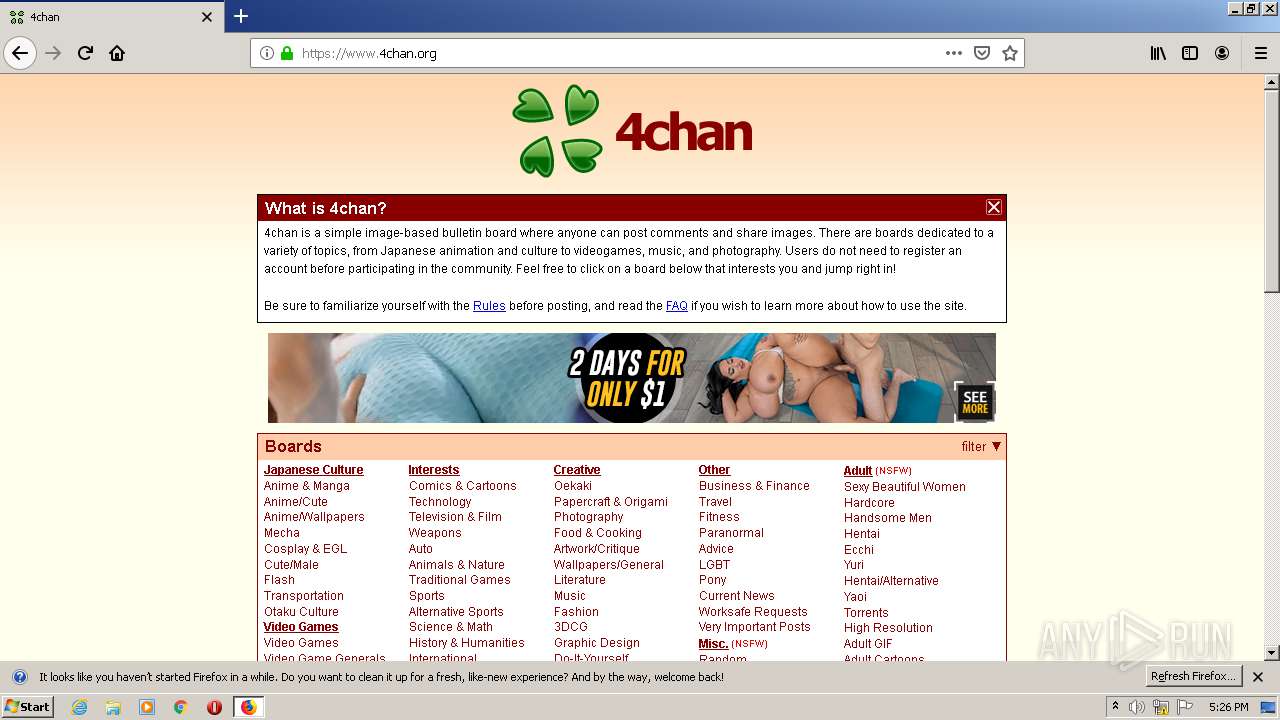
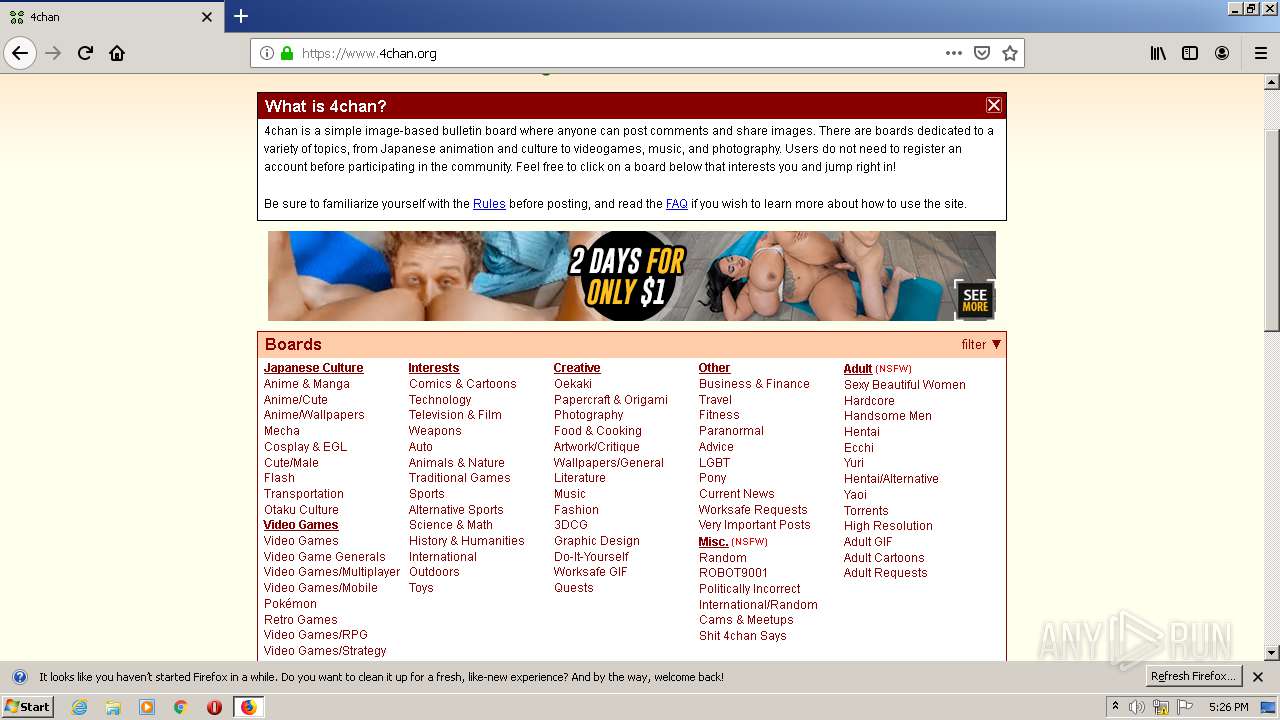
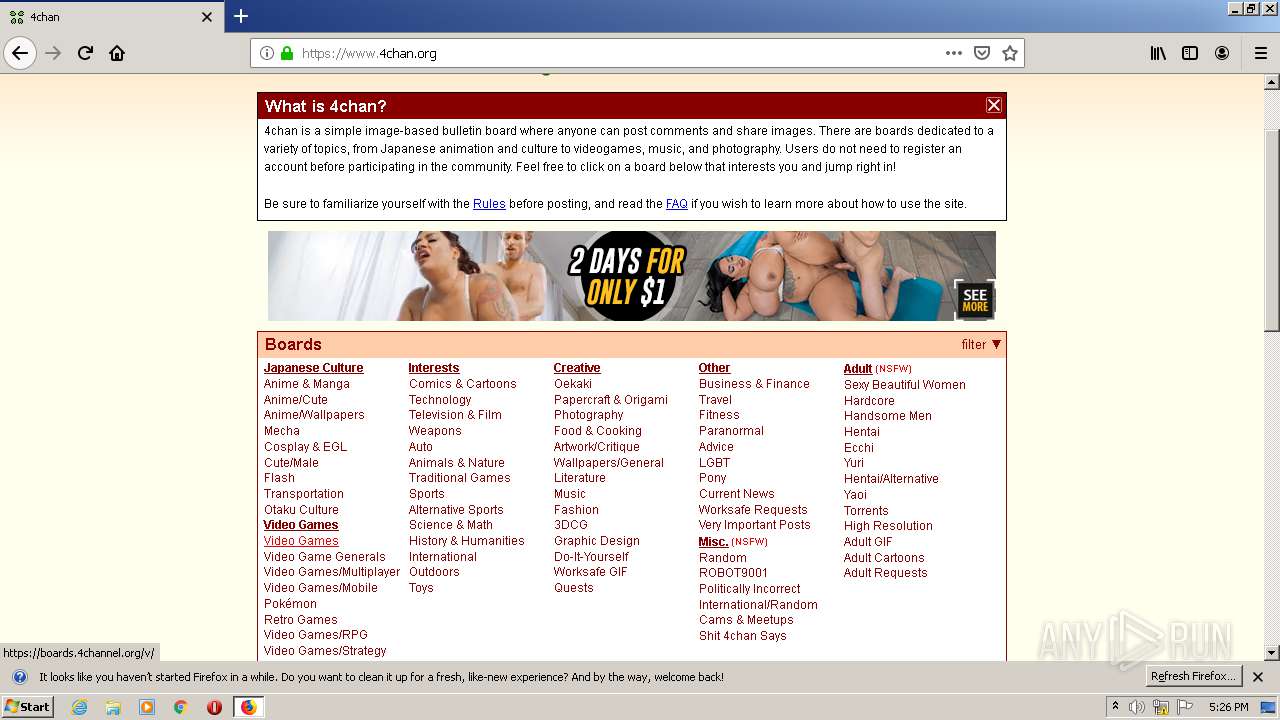
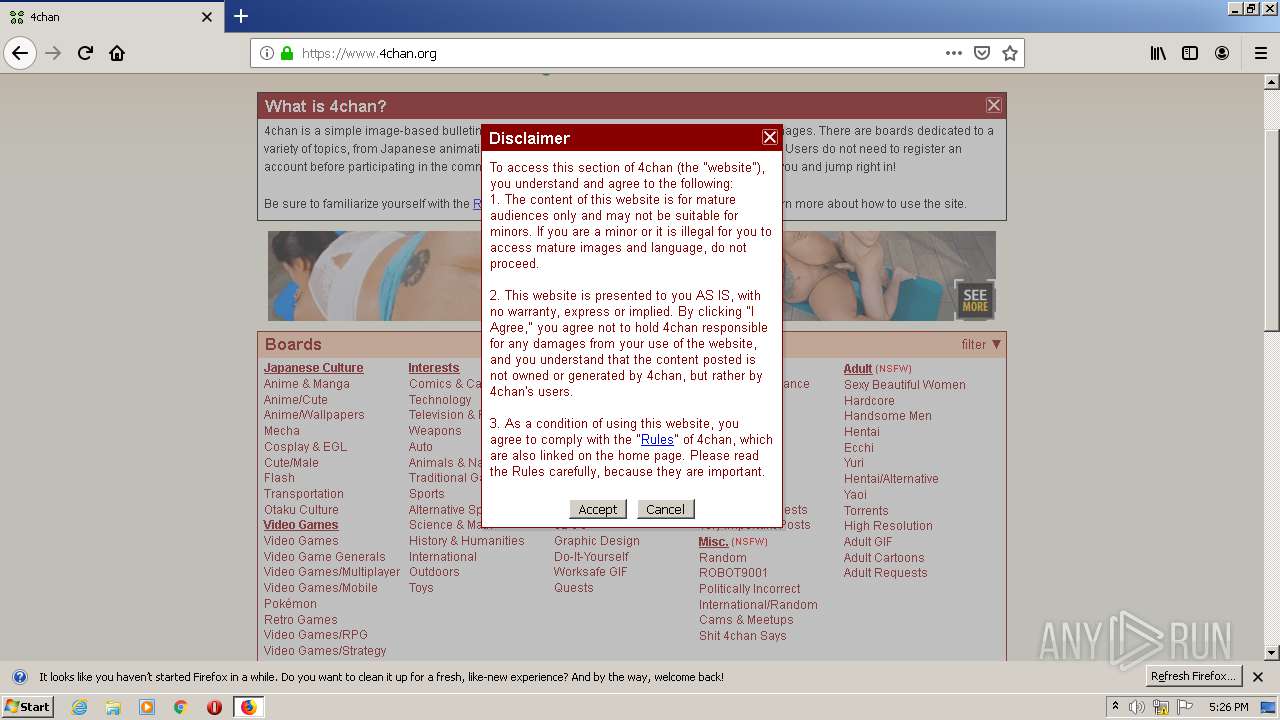
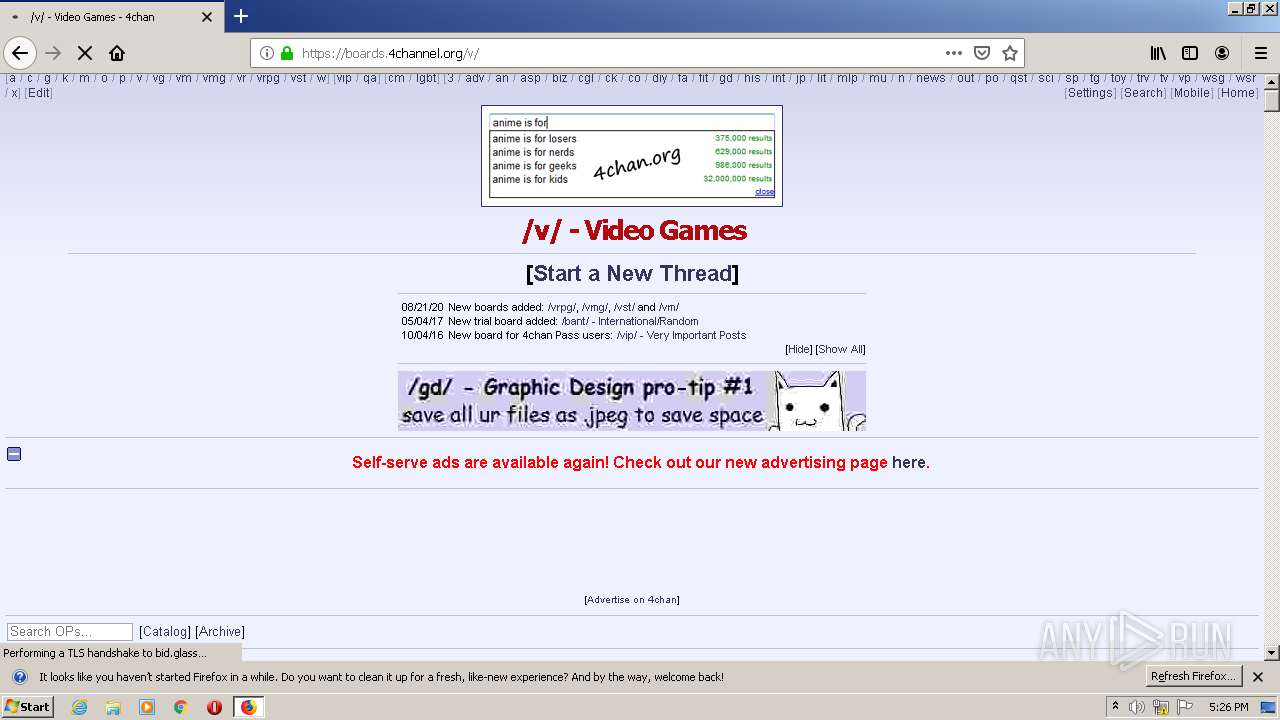
| URL: | https://4chan.org |
| Full analysis: | https://app.any.run/tasks/03e5bab6-24da-41fb-95ab-7da1b80bcaee |
| Verdict: | Malicious activity |
| Analysis date: | November 22, 2020, 17:25:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4BC8906CFE27D589F1610C442FD5E848 |
| SHA1: | 315695C8B04D0EB7FFEBEF4D0411F3EE30A34A4A |
| SHA256: | 014032E87E10CCCCC298C0FFBB5D2EB3C580175444277B7ADCBA000C310FA15E |
| SSDEEP: | 3:N8LLD:2Lf |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
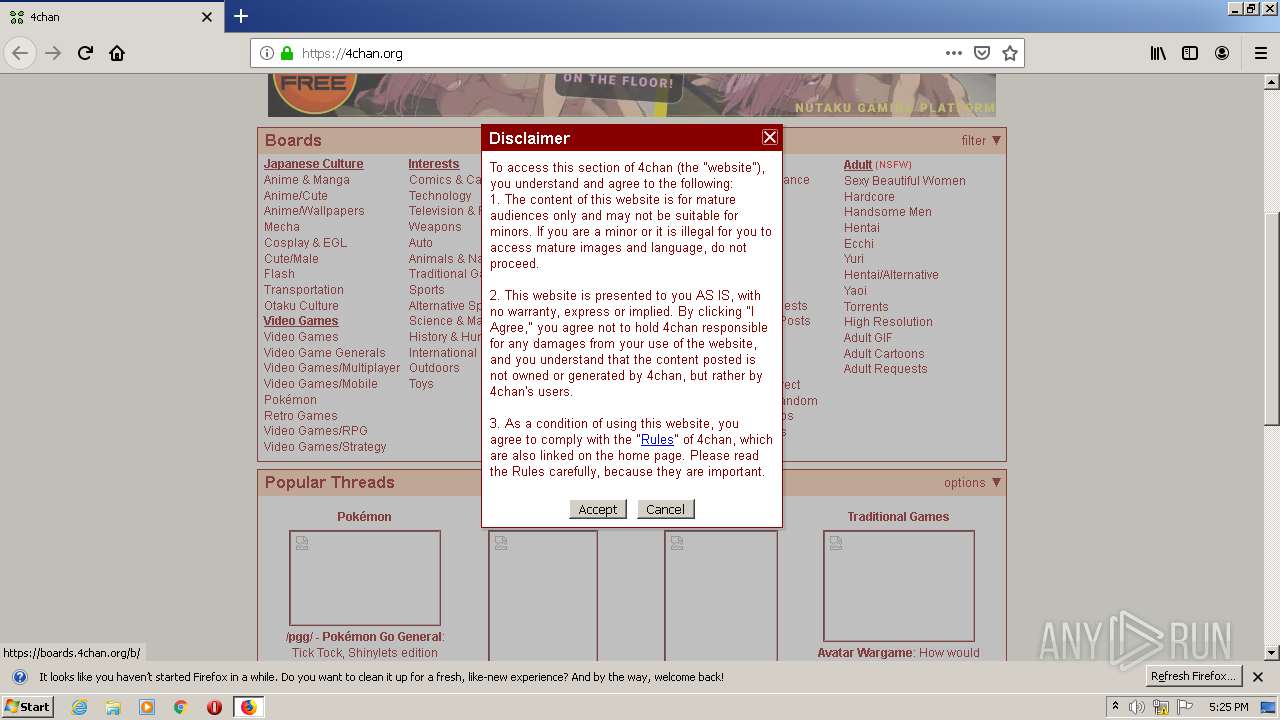
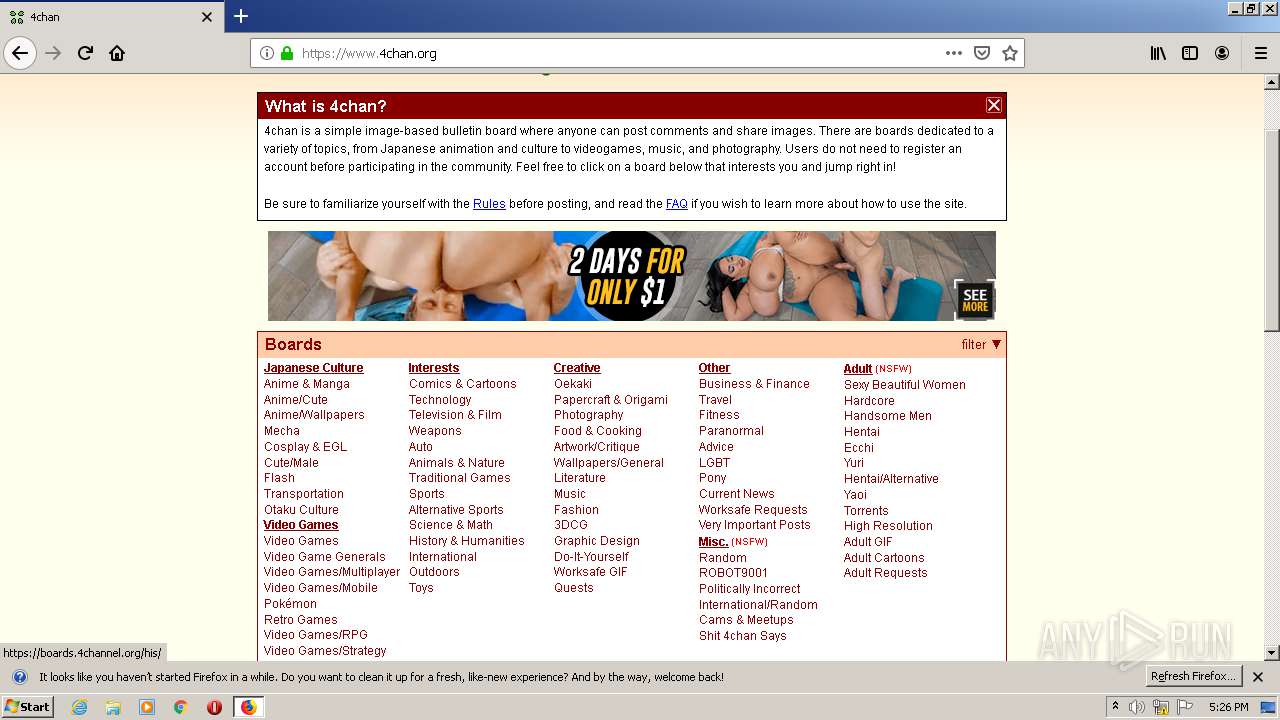
| 2248 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://4chan.org" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe |
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
91
DNS requests
190
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
— | — | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 279 b | whitelisted |
— | — | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
— | — | POST | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
— | — | POST | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
— | — | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 279 b | whitelisted |
— | — | POST | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/ | US | der | 471 b | whitelisted |
— | — | POST | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/ | US | der | 471 b | whitelisted |
— | — | POST | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/ | US | der | 471 b | whitelisted |
— | — | POST | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 104.16.62.249:443 | s.4cdn.org | Cloudflare Inc | US | shared |
— | — | 216.18.168.166:443 | a.adtng.com | Reflected Networks, Inc. | US | suspicious |
— | — | 172.217.22.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
— | — | 143.204.201.119:443 | snippets.cdn.mozilla.net | — | US | suspicious |
— | — | 205.185.208.20:443 | hw-cdn2.ang-content.com | Highwinds Network Group, Inc. | US | unknown |
— | — | 172.217.18.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
— | — | 44.237.178.15:443 | shavar.services.mozilla.com | University of California, San Diego | US | unknown |
— | — | 143.204.201.123:443 | tracking-protection.cdn.mozilla.net | — | US | malicious |
— | — | 143.204.201.62:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
4chan.org |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |