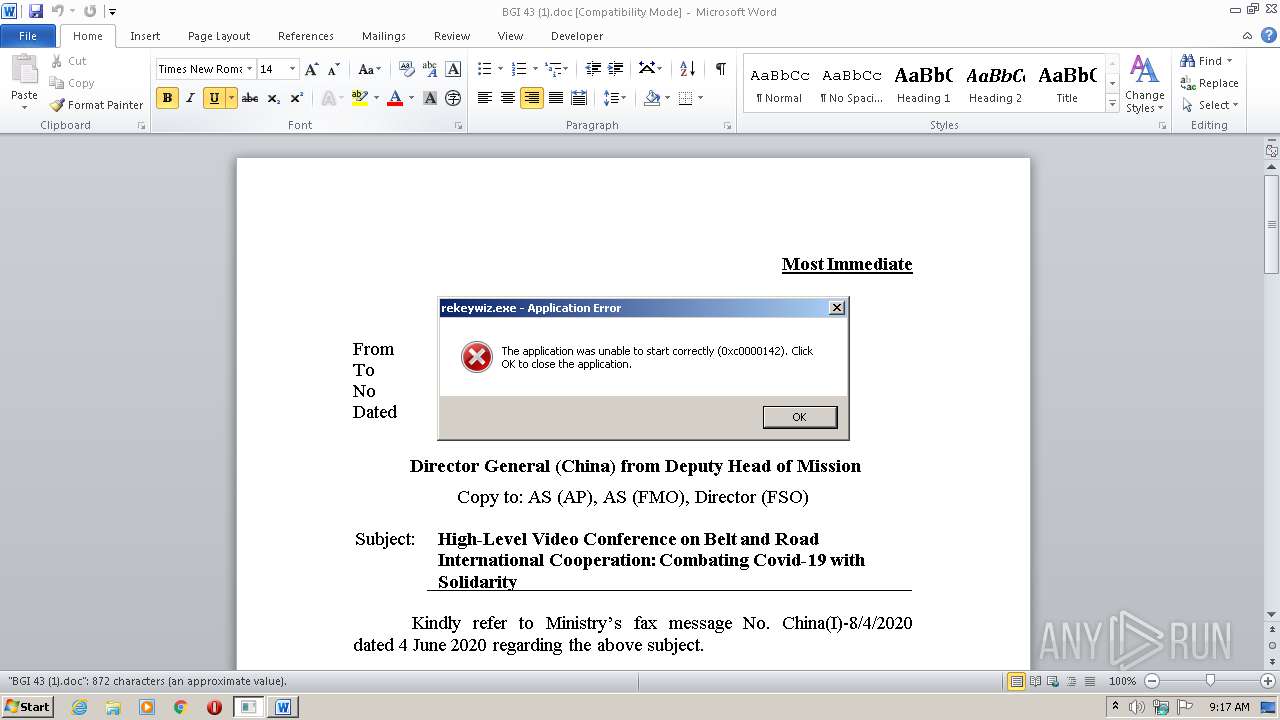
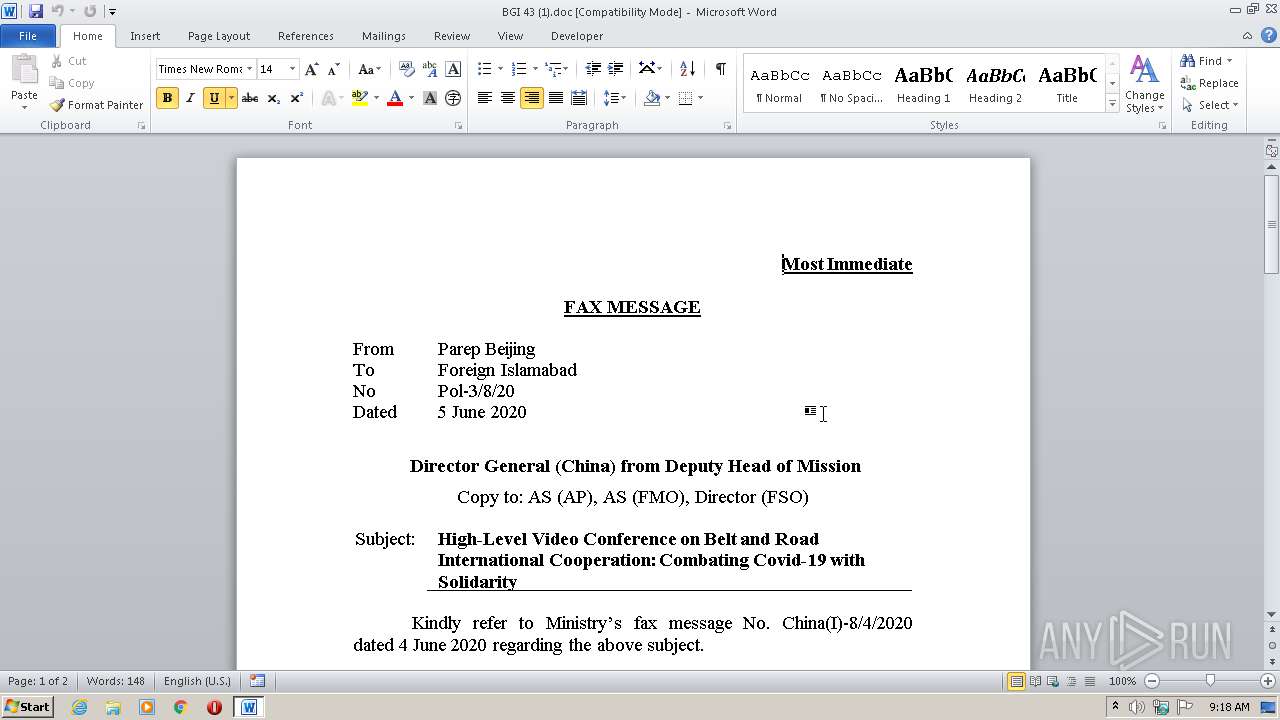
| File name: | BGI 43 (1).doc |
| Full analysis: | https://app.any.run/tasks/51928d52-3682-4907-9bb7-9c11a168b360 |
| Verdict: | Malicious activity |
| Analysis date: | July 15, 2020, 08:17:33 |
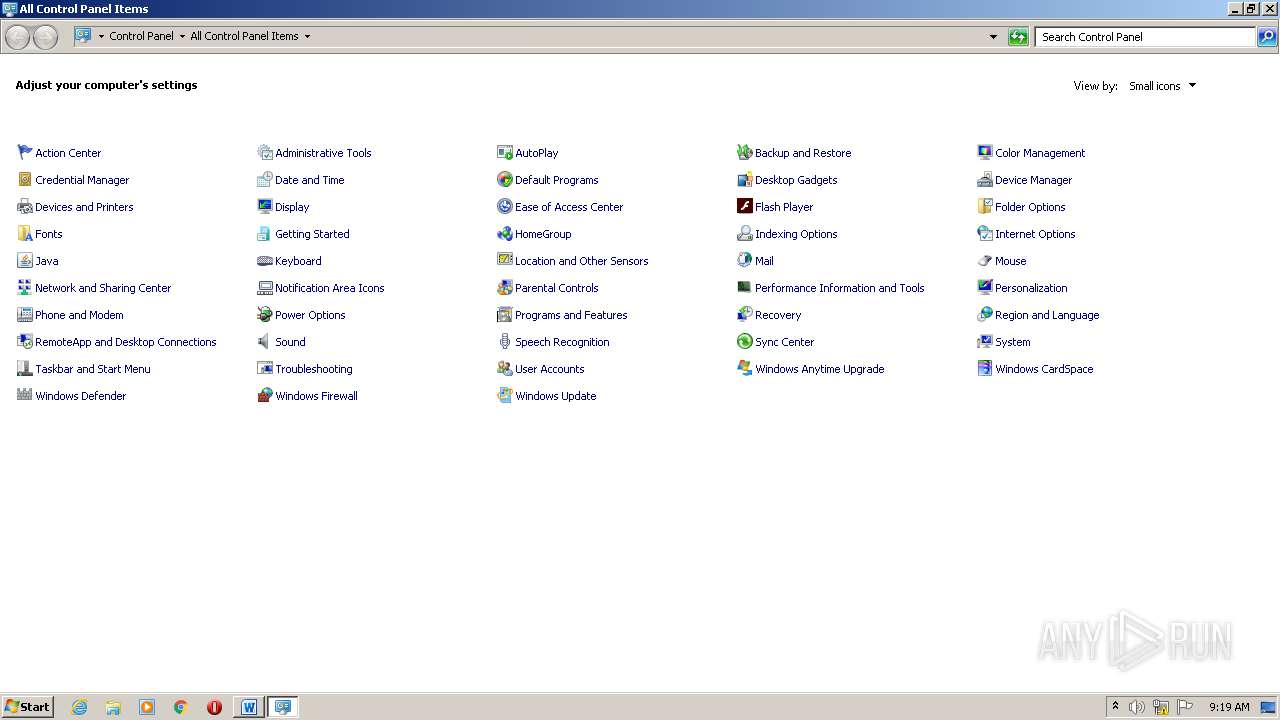
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 55A673D1985EBF1C65E6902F4BC6489B |
| SHA1: | 41FE8E491339A418EFE4B7EB4ECC78FCB5A81931 |
| SHA256: | 012DB1429D38232415B021EF951091D0894703724C26F50FD38785E6C5813AD8 |
| SSDEEP: | 6144:NTD0r6z+QSBVtUPFmC+R6qlucDZAmAePhfLxhErnf8JLBACIUz8:7IAGVNthEQJLiC/8 |
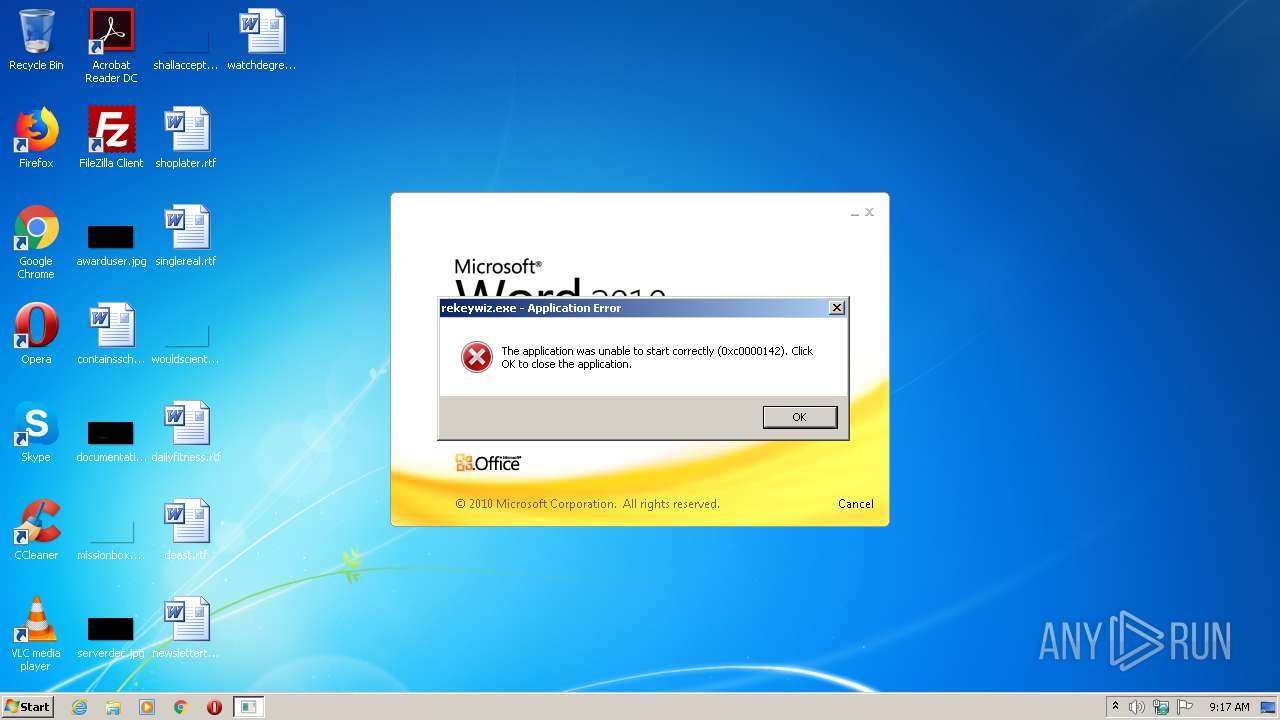
MALICIOUS
Application was dropped or rewritten from another process
- rekeywiz.exe (PID: 1844)
- rekeywiz.exe (PID: 480)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 304)
Changes the autorun value in the registry
- EQNEDT32.EXE (PID: 304)
Loads dropped or rewritten executable
- rekeywiz.exe (PID: 480)
SUSPICIOUS
Reads internet explorer settings
- EQNEDT32.EXE (PID: 304)
Executed via COM
- EQNEDT32.EXE (PID: 304)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 304)
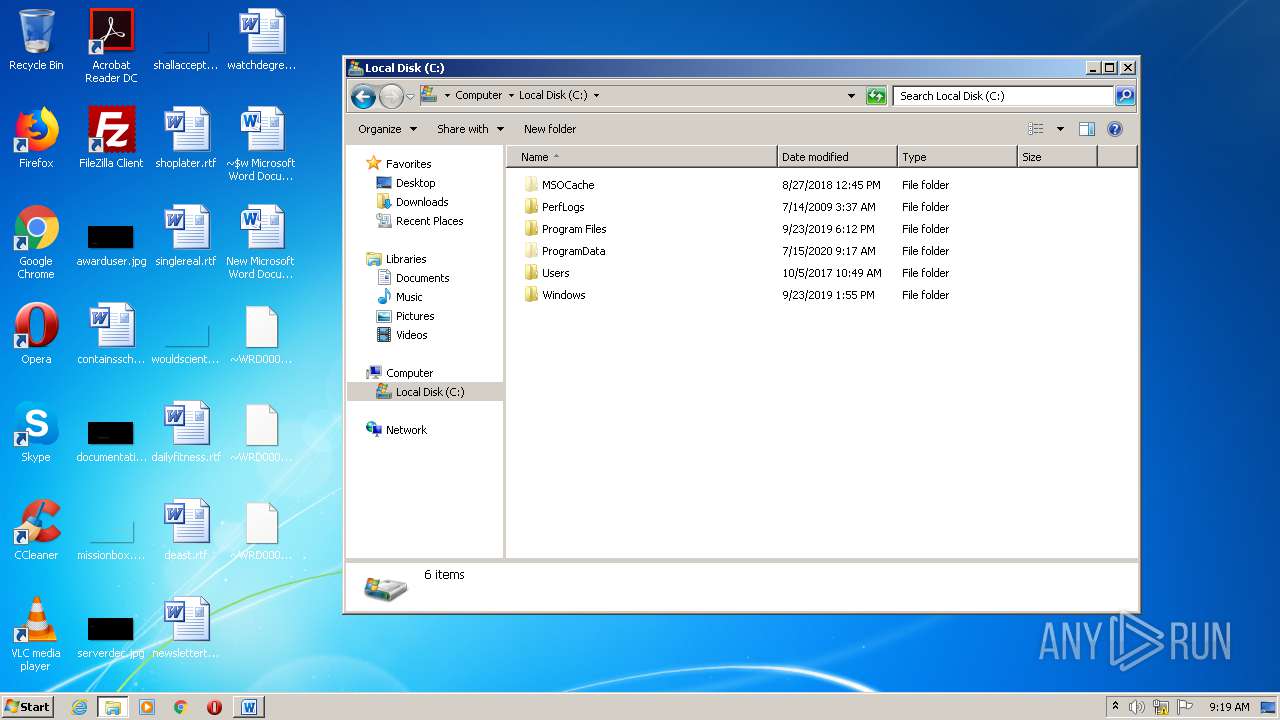
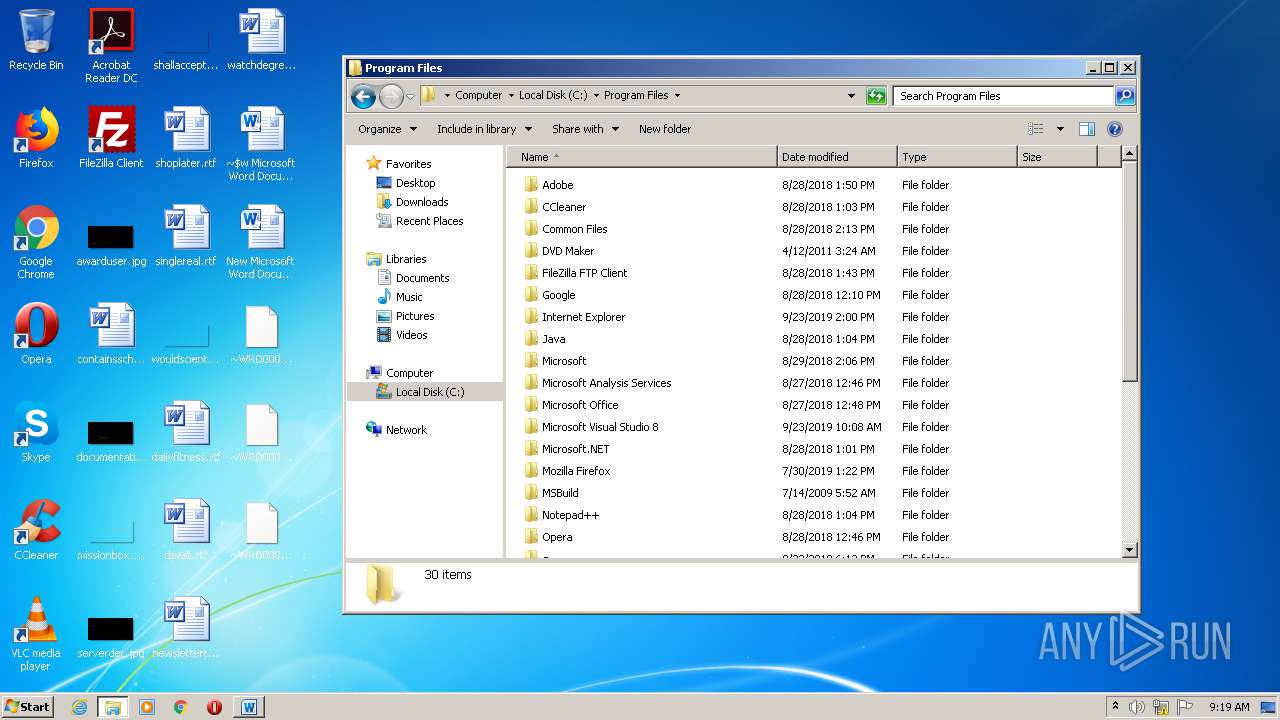
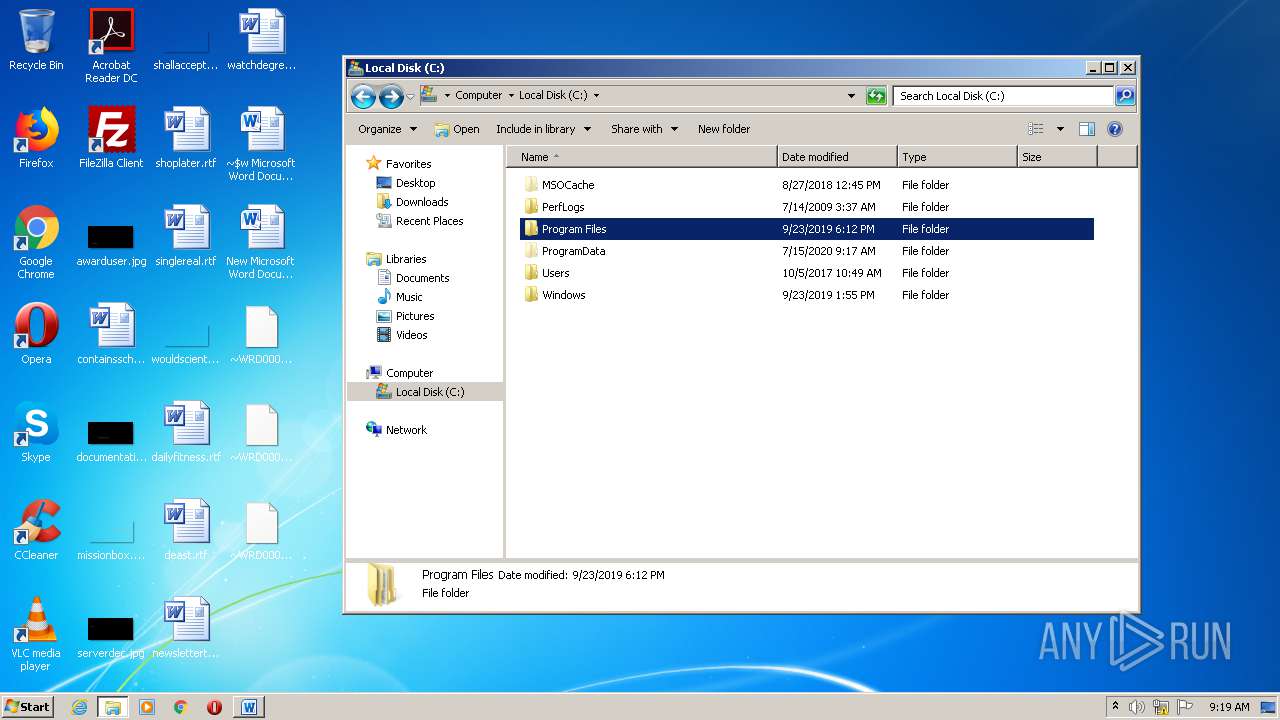
Creates files in the program directory
- EQNEDT32.EXE (PID: 304)
- rekeywiz.exe (PID: 480)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2416)
- WINWORD.EXE (PID: 2264)
- WINWORD.EXE (PID: 2956)
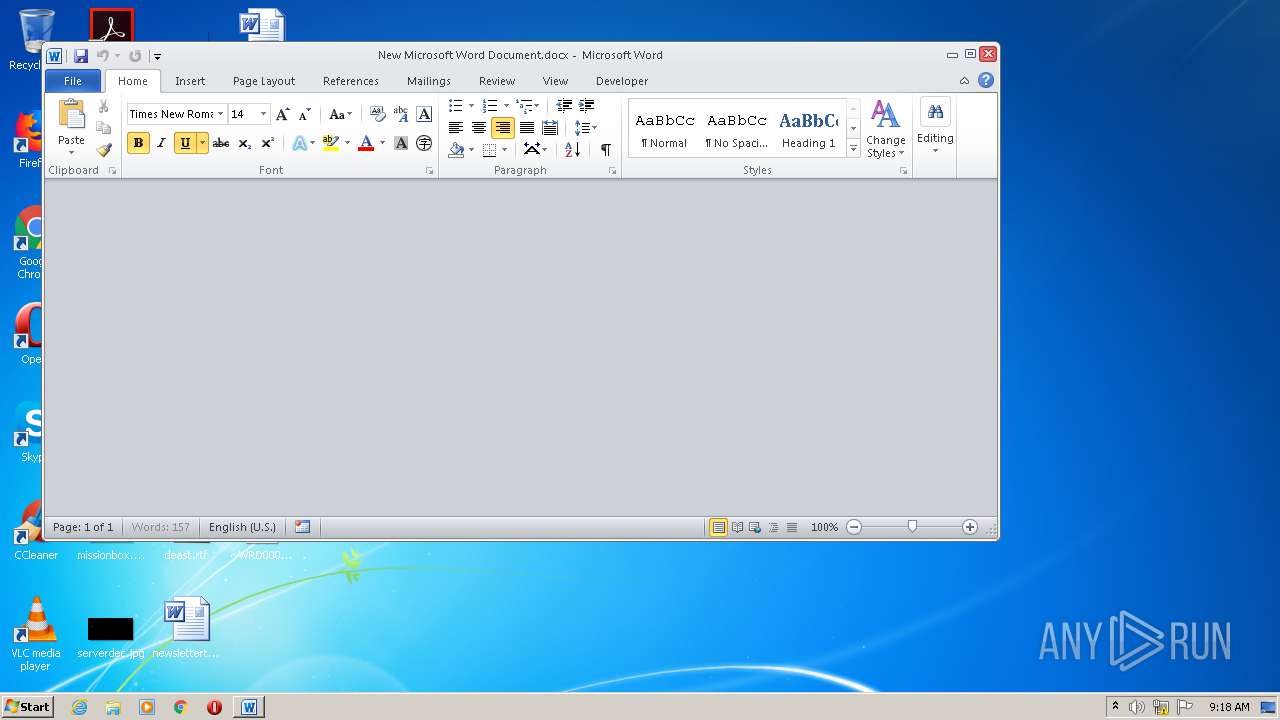
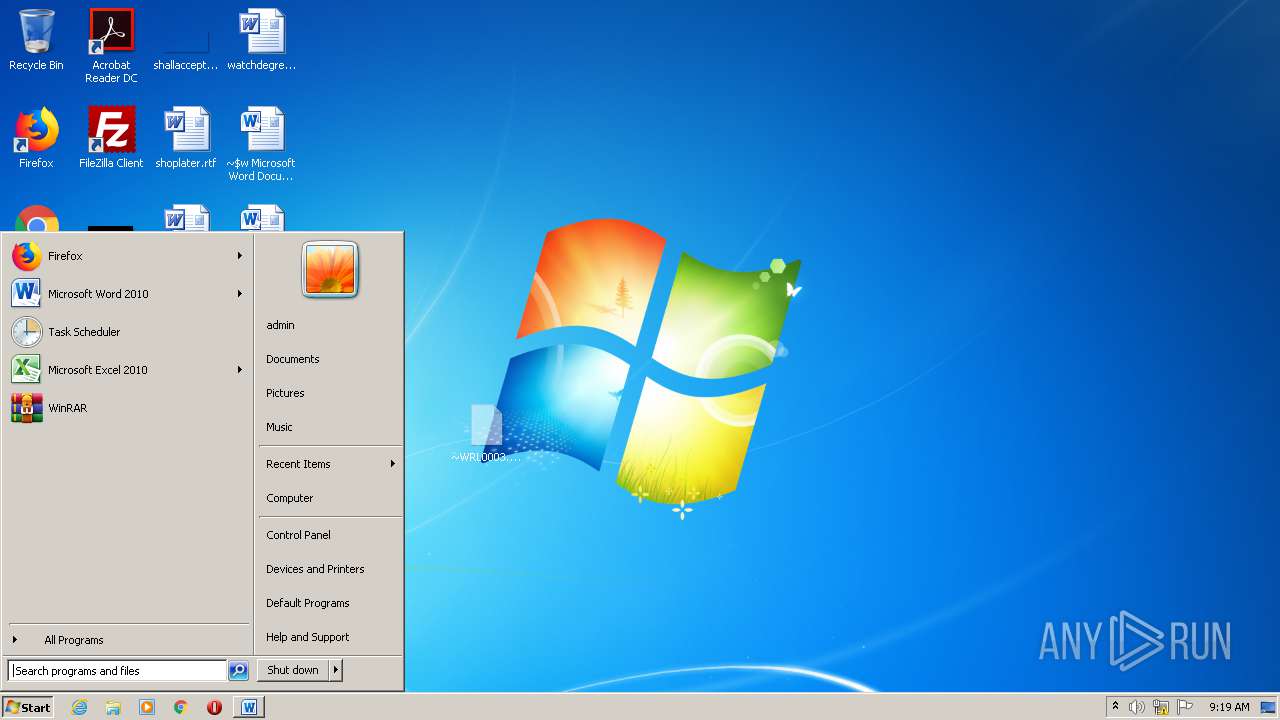
Manual execution by user
- WINWORD.EXE (PID: 2956)
- WINWORD.EXE (PID: 2264)
- rekeywiz.exe (PID: 480)
Creates files in the user directory
- WINWORD.EXE (PID: 2416)
Reads settings of System Certificates
- rekeywiz.exe (PID: 480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
| LastModifiedBy: | Administrator |
|---|---|
| CreateDate: | 2020:06:08 13:25:00 |
| ModifyDate: | 2020:06:08 13:27:00 |
| RevisionNumber: | 2 |
| TotalEditTime: | 2 minutes |
| Pages: | 1 |
| Words: | 152 |
| Characters: | 868 |
| CharactersWithSpaces: | 1018 |
| InternalVersionNumber: | 49247 |
Total processes
48
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
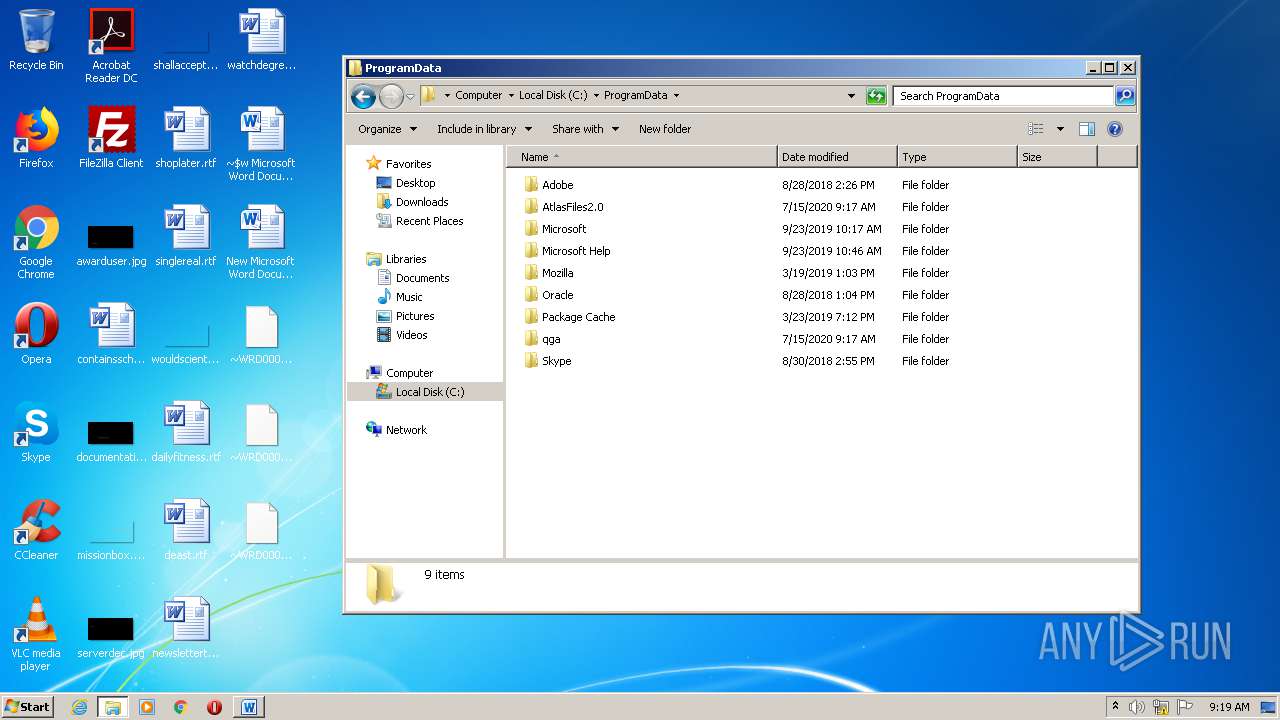
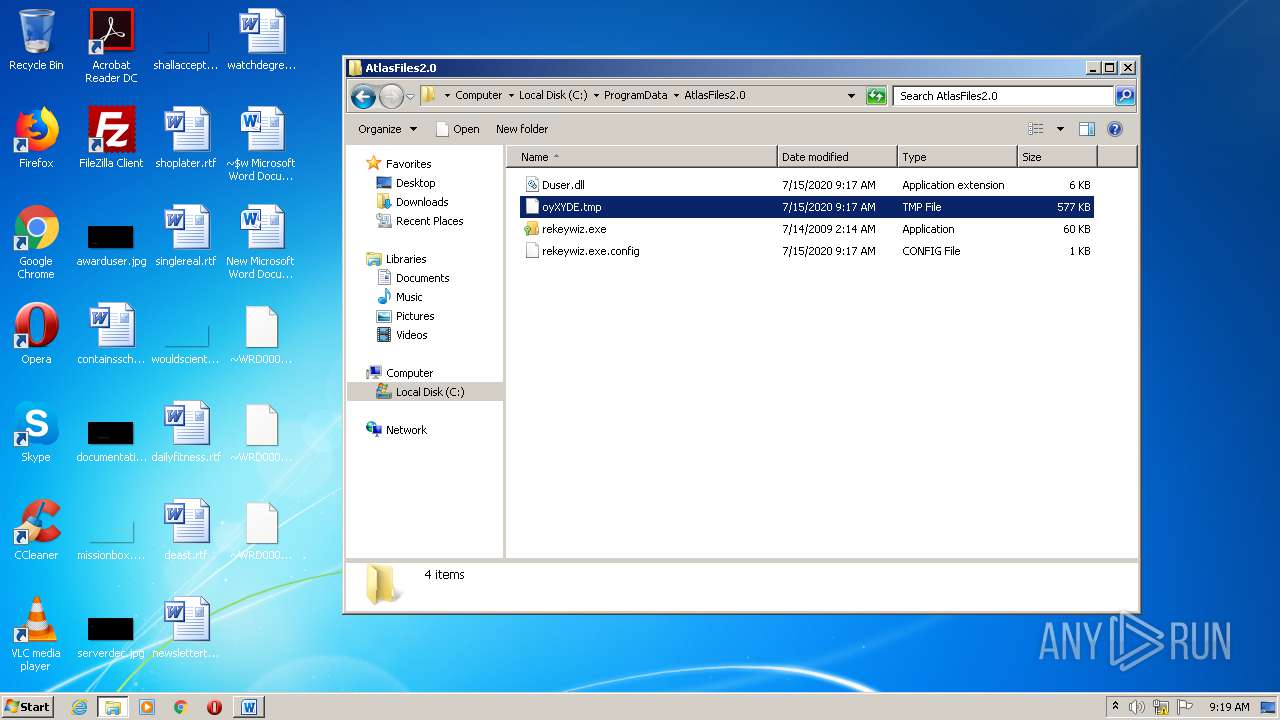
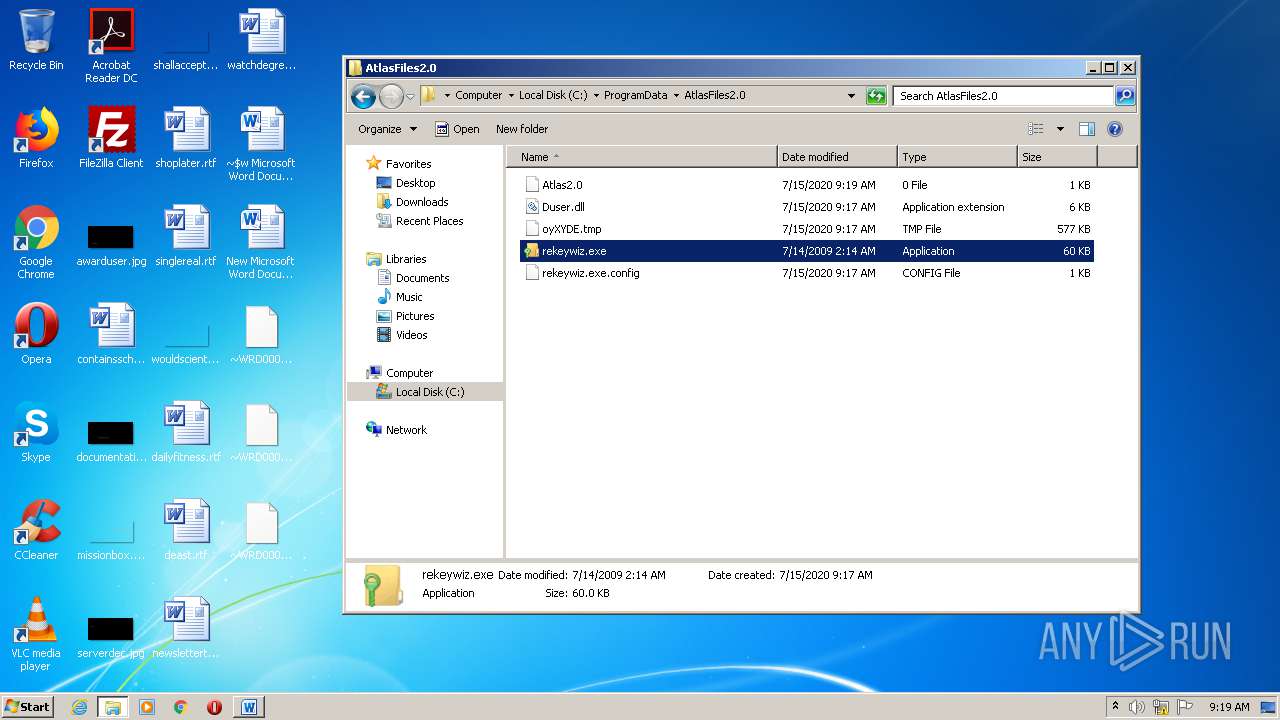
| 480 | "C:\ProgramData\AtlasFiles2.0\rekeywiz.exe" | C:\ProgramData\AtlasFiles2.0\rekeywiz.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: EFS REKEY wizard Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1844 | "C:\ProgramData\AtlasFiles2.0\rekeywiz.exe" | C:\ProgramData\AtlasFiles2.0\rekeywiz.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: EFS REKEY wizard Exit code: 3221225794 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
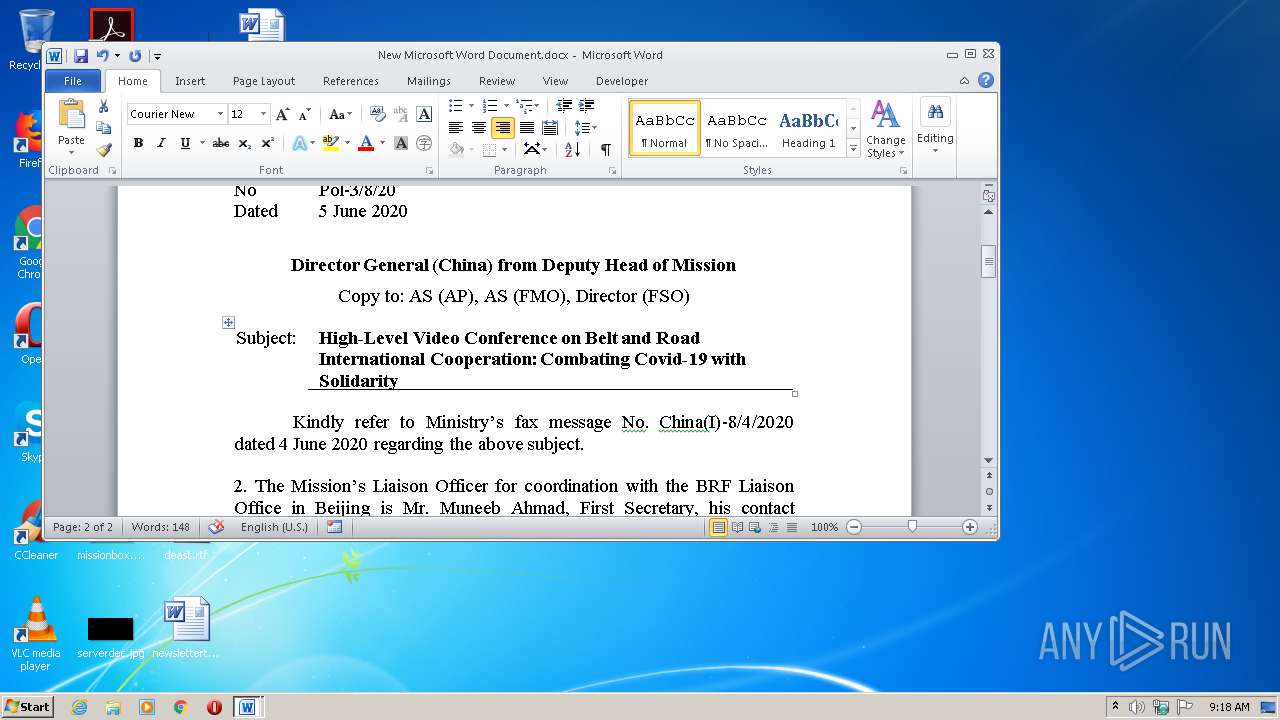
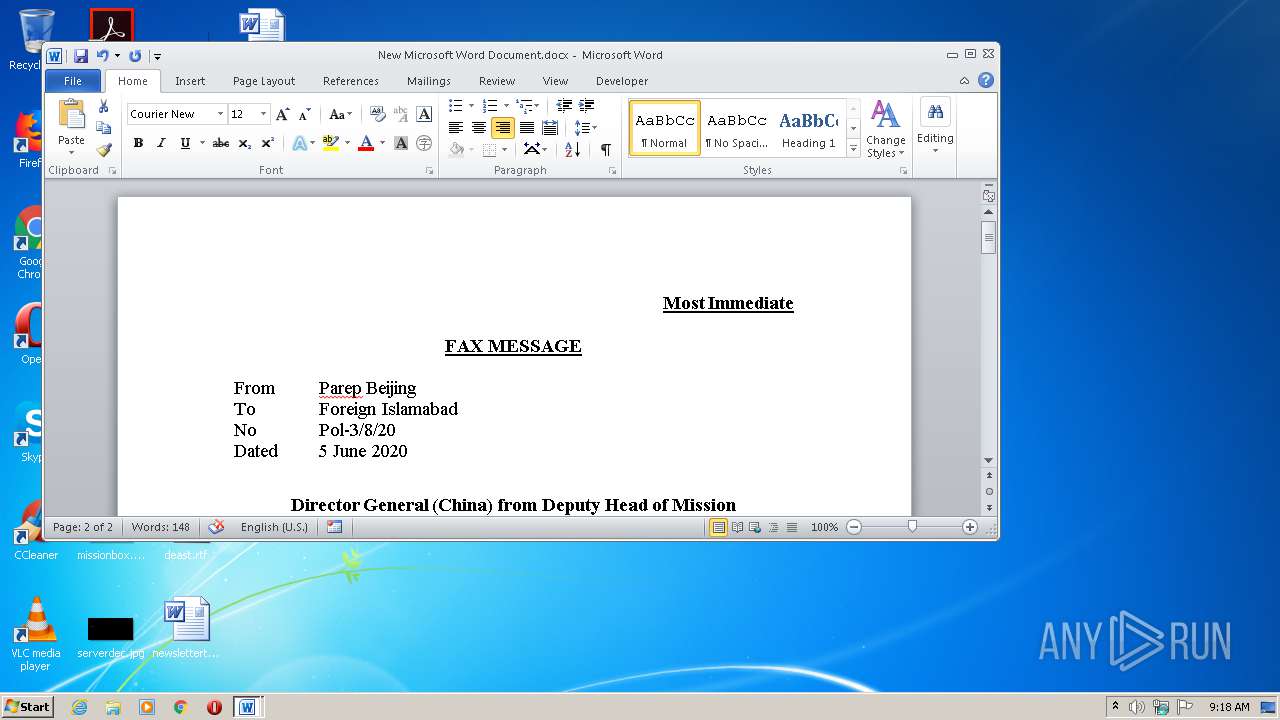
| 2264 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\New Microsoft Word Document.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\BGI 43 (1).doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\New Microsoft Word Document.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 742
Read events
1 541
Write events
820
Delete events
381
Modification events
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | e~9 |
Value: 657E390070090000010000000000000000000000 | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
7
Text files
13
Unknown types
7
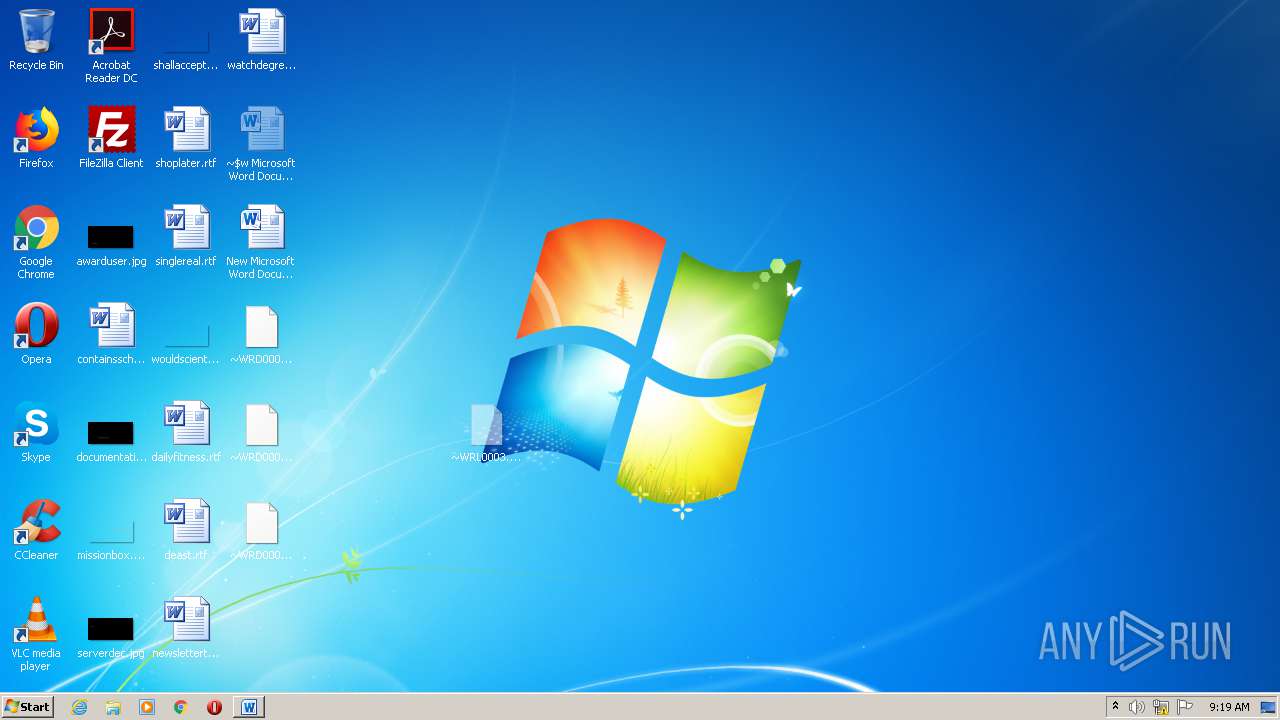
Dropped files
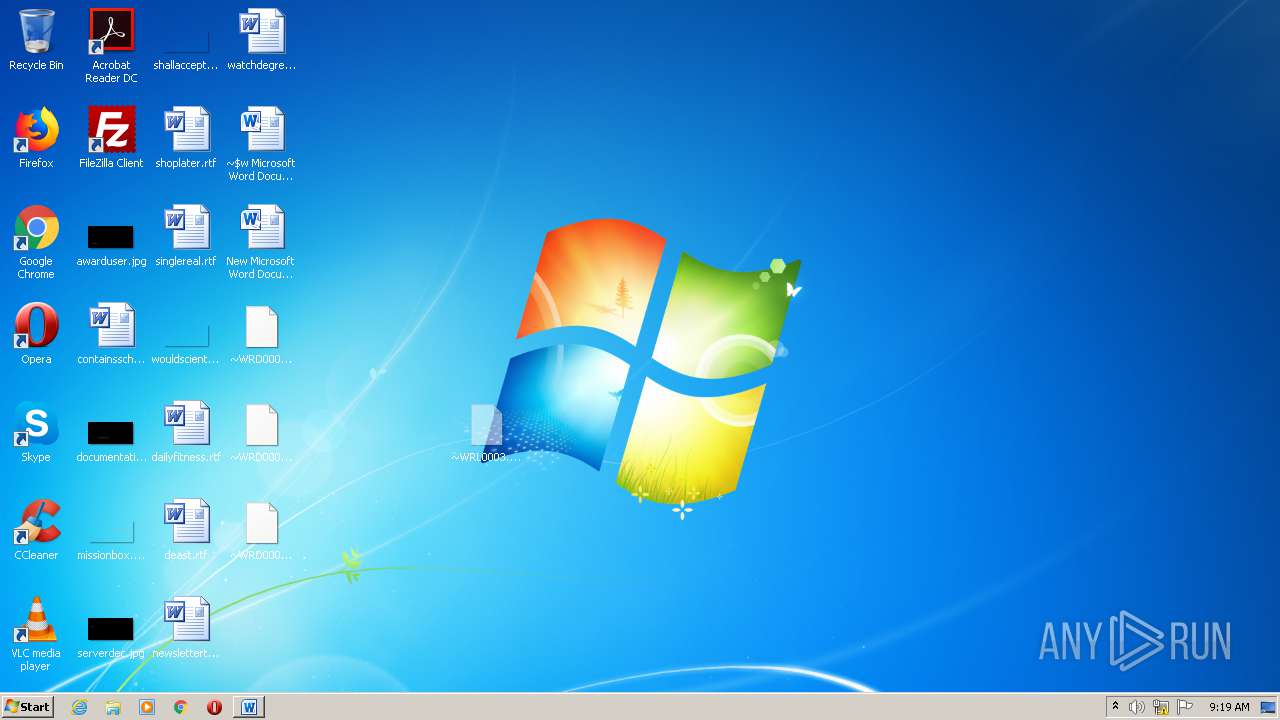
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2416 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9E65.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2264 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR1C4F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2956 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR1E14.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2416 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{E6F5D537-15F9-453E-B417-D8130CC1485C}.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | WINWORD.EXE | C:\Users\admin\Desktop\~WRD0002.tmp | — | |
MD5:— | SHA256:— | |||
| 480 | rekeywiz.exe | C:\Users\admin\AppData\Local\Temp\tmp32FF.tmp | — | |
MD5:— | SHA256:— | |||
| 480 | rekeywiz.exe | C:\Users\admin\AppData\Local\Temp\tmp5D9A.tmp | — | |
MD5:— | SHA256:— | |||
| 480 | rekeywiz.exe | C:\Users\admin\AppData\Roaming\AtlasDat2.0\dpmk0a5h.zs5.flc | — | |
MD5:— | SHA256:— | |||
| 480 | rekeywiz.exe | C:\Users\admin\AppData\Local\Temp\tmpBF7D.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
480 | rekeywiz.exe | 185.99.133.106:443 | r0dps.net | Zappie Host LLC | NZ | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
r0dps.net |
| unknown |