| File name: | Logger.exe |
| Full analysis: | https://app.any.run/tasks/7780c2e2-2676-4662-83b9-07ed1f482ec2 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 14:28:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 953E343651EBAED91029625293A73EC7 |
| SHA1: | A12B6488E666E477638E1855C8C7400CE920F69B |
| SHA256: | 0124CC0DDAD34BF7ACD5289DE40E1F18B33DDD8E5413370C01B2D353B488690D |
| SSDEEP: | 6144:tDKW1Lgbdl0TBBvjc/GPwumTv6hM6YfftXWKxUuZ8ndL:Fh1Lk70TnvjcZLDJlWKxUuOL |
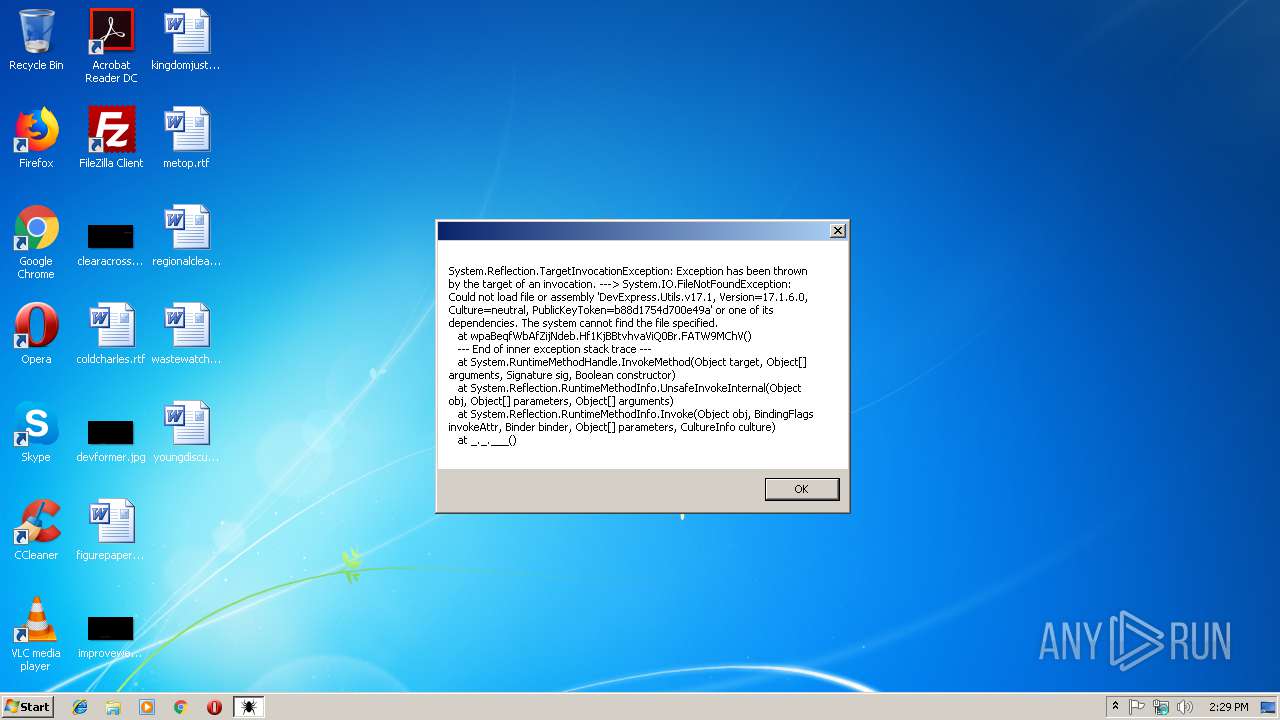
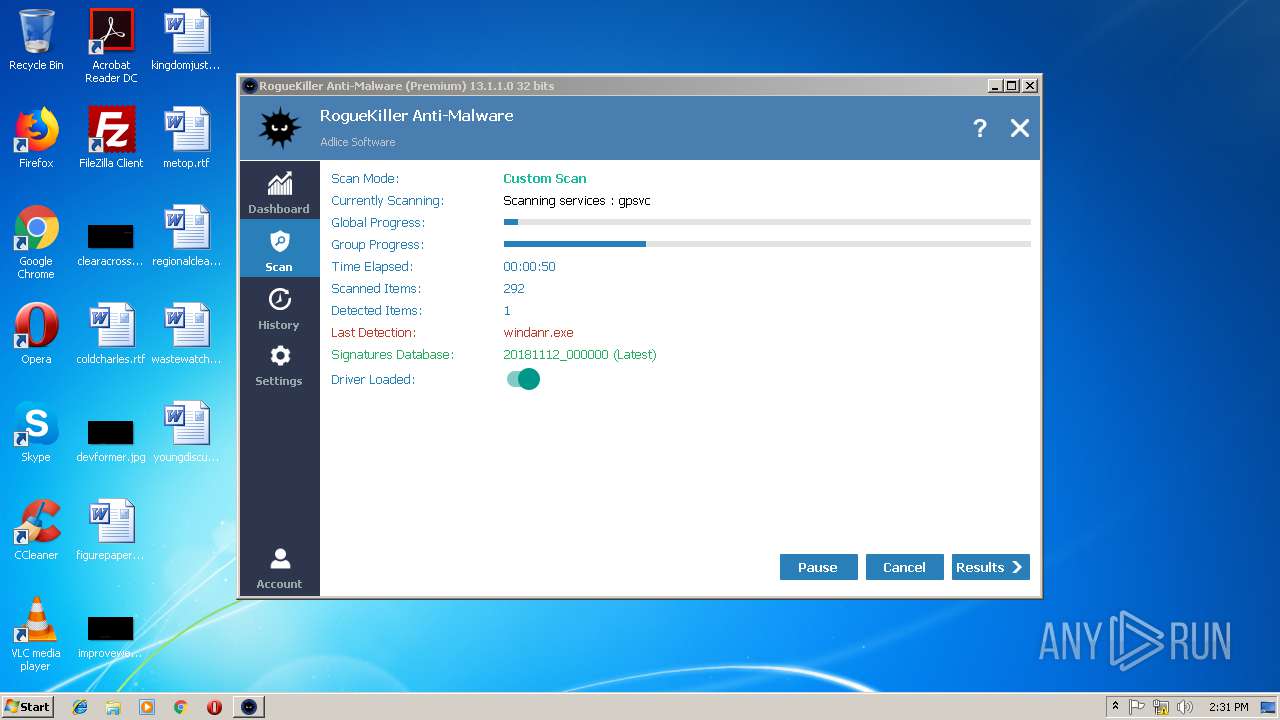
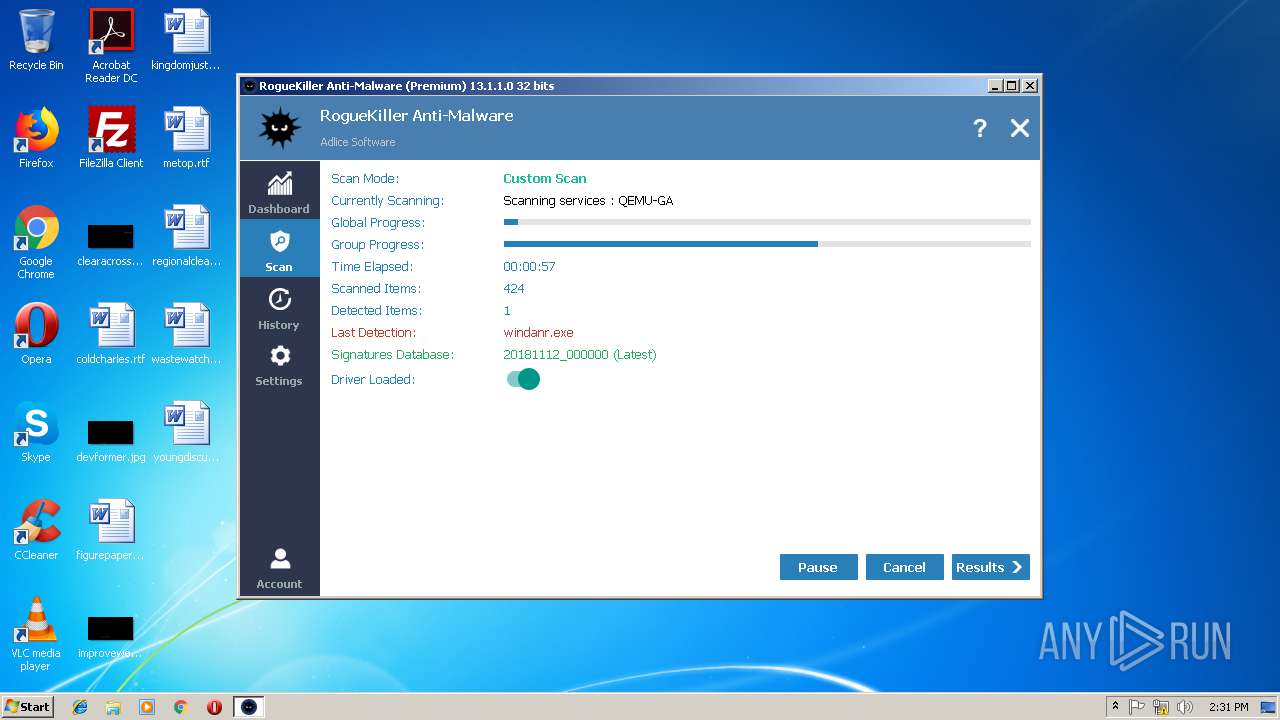
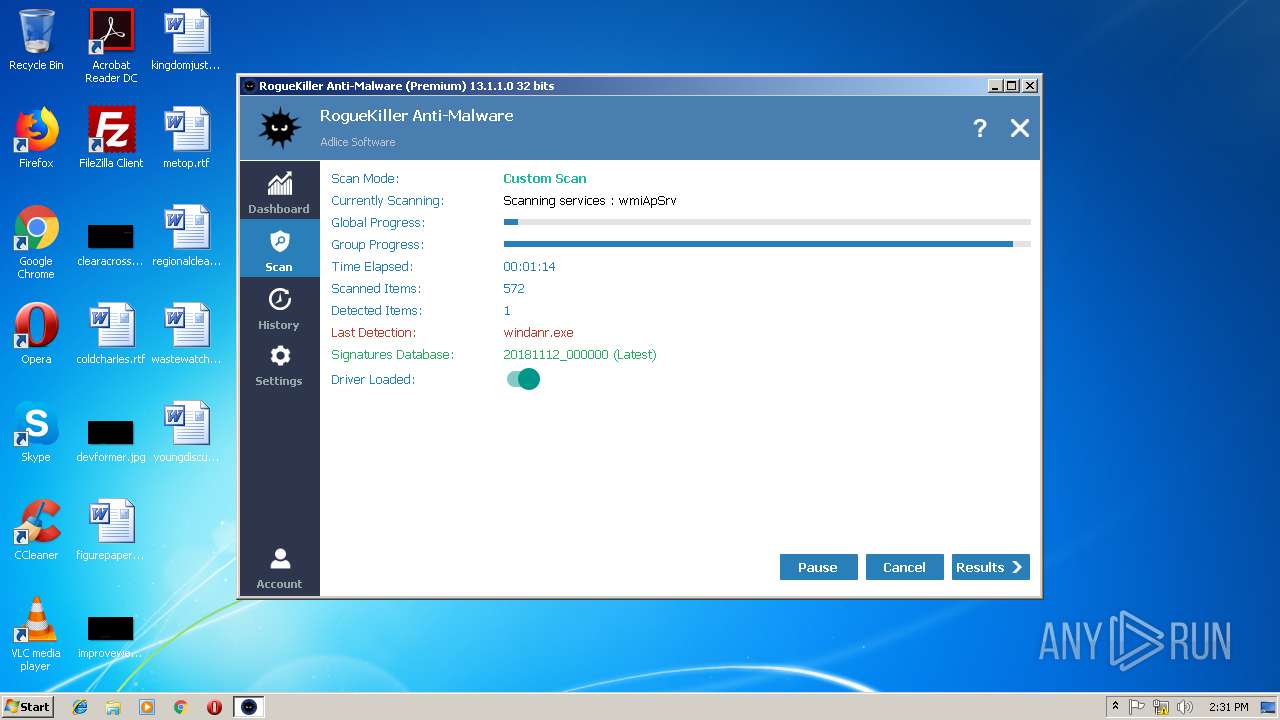
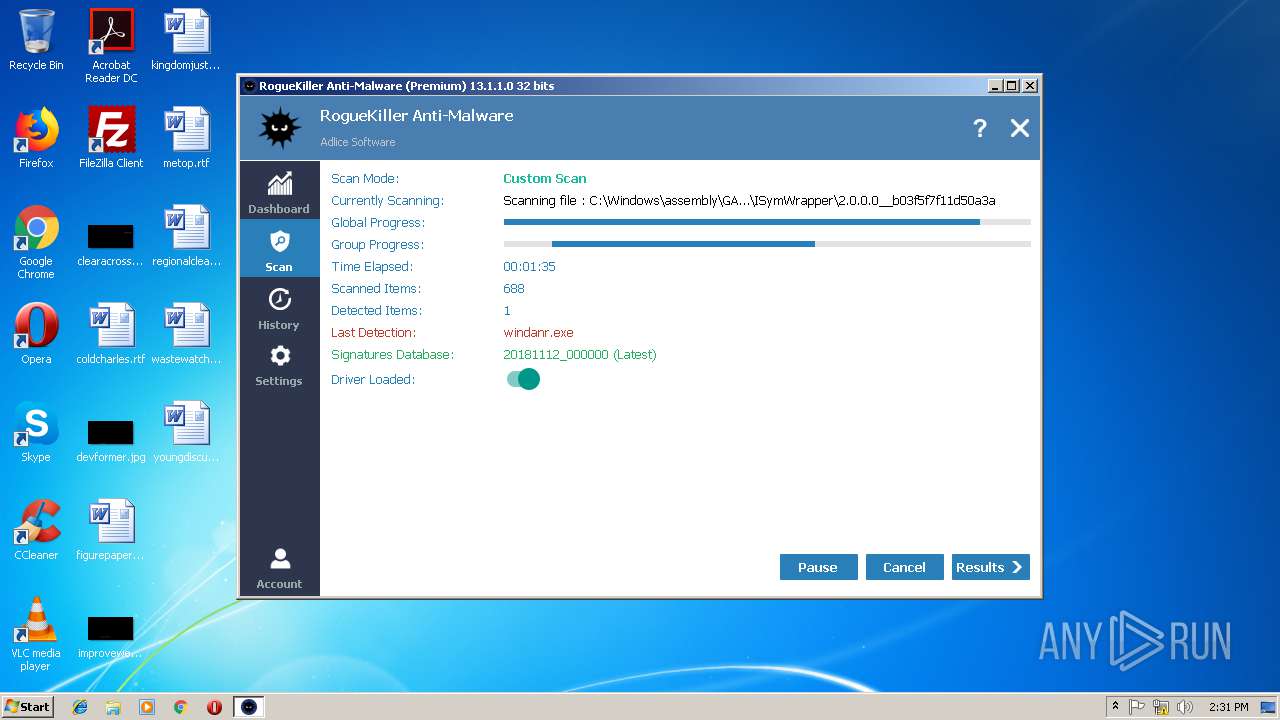
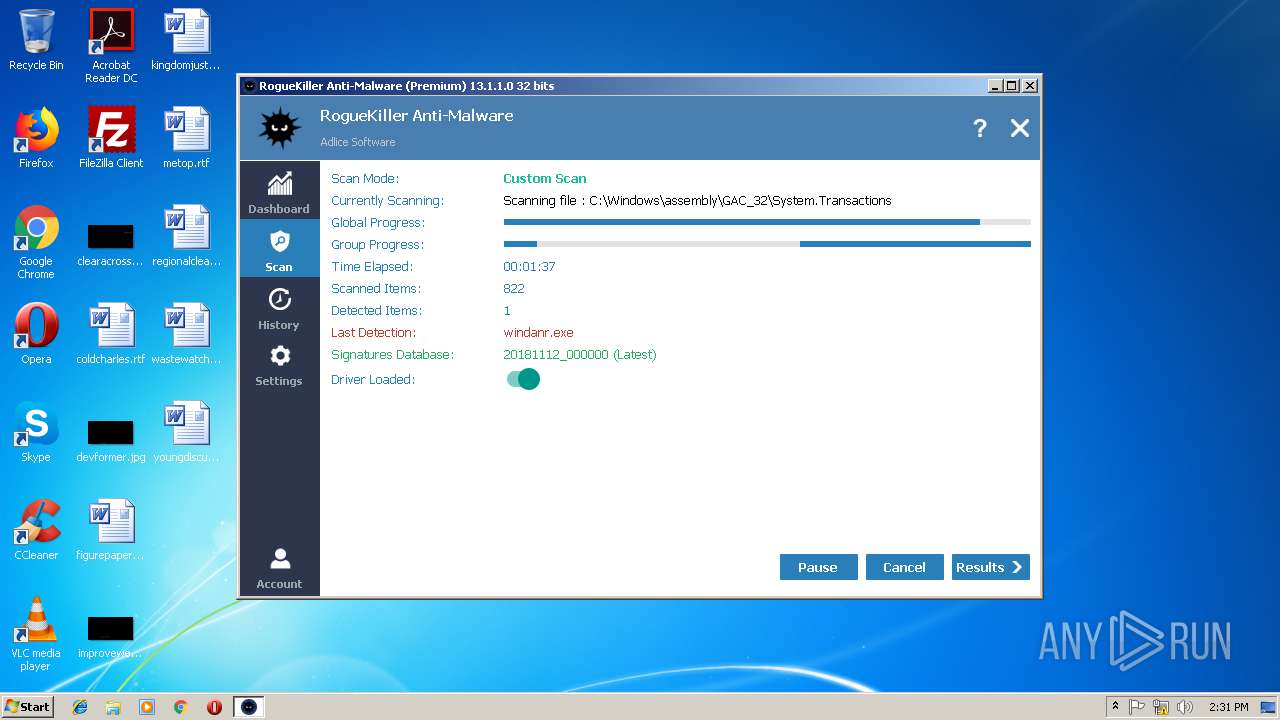
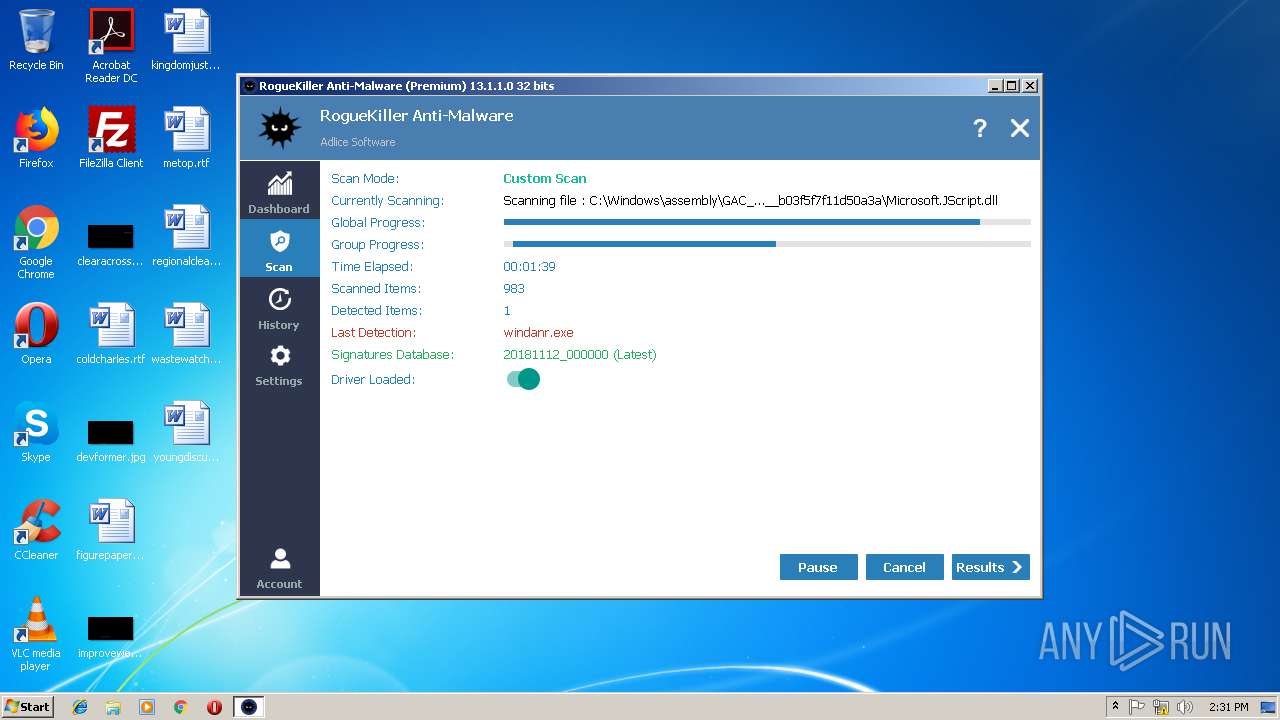
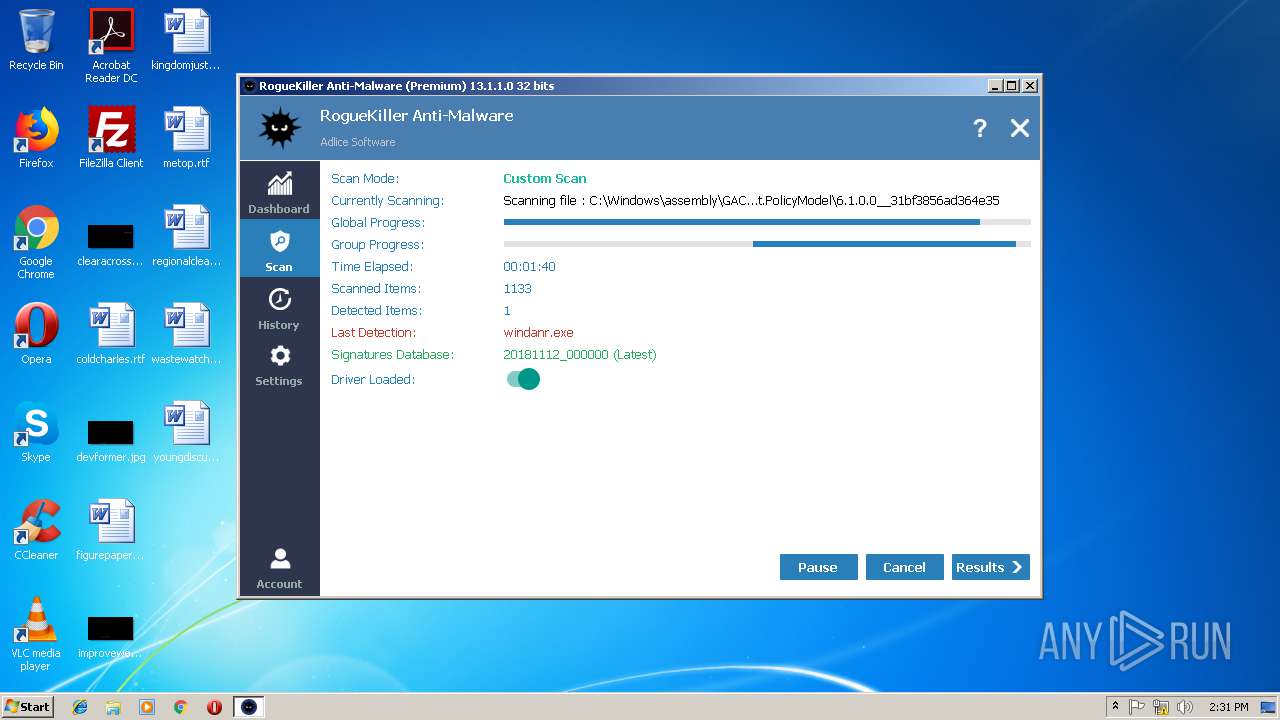
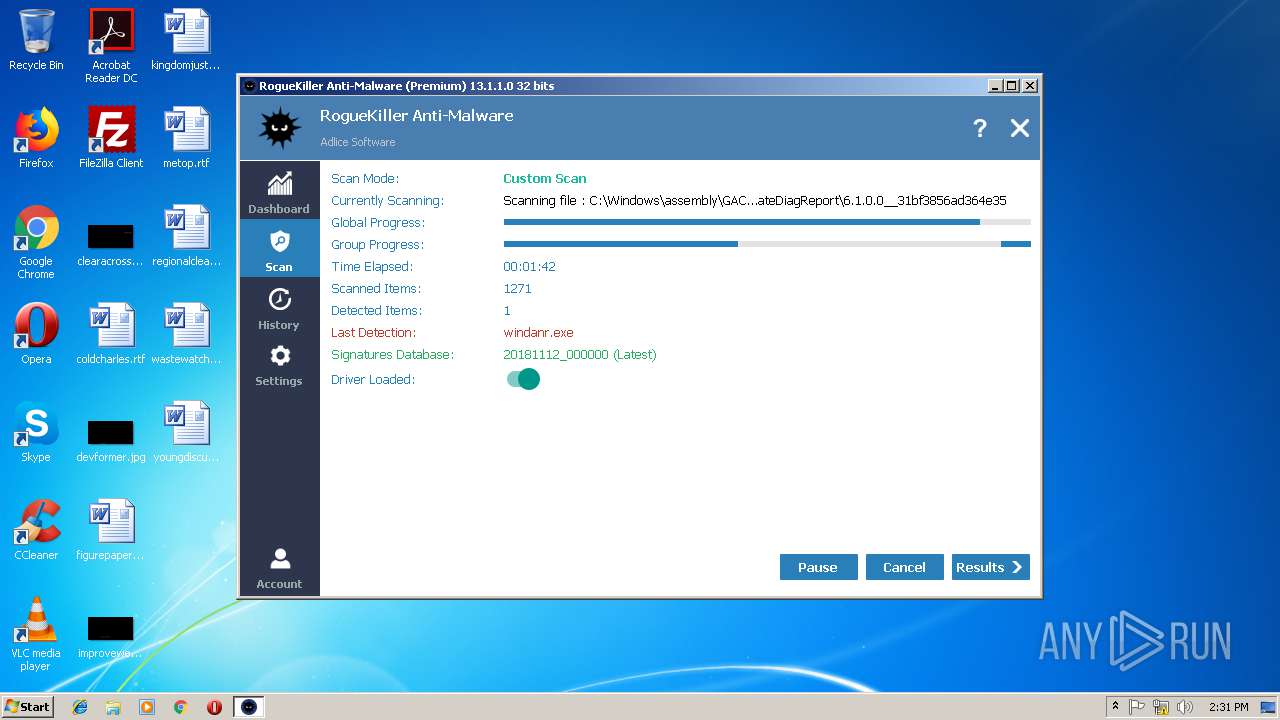
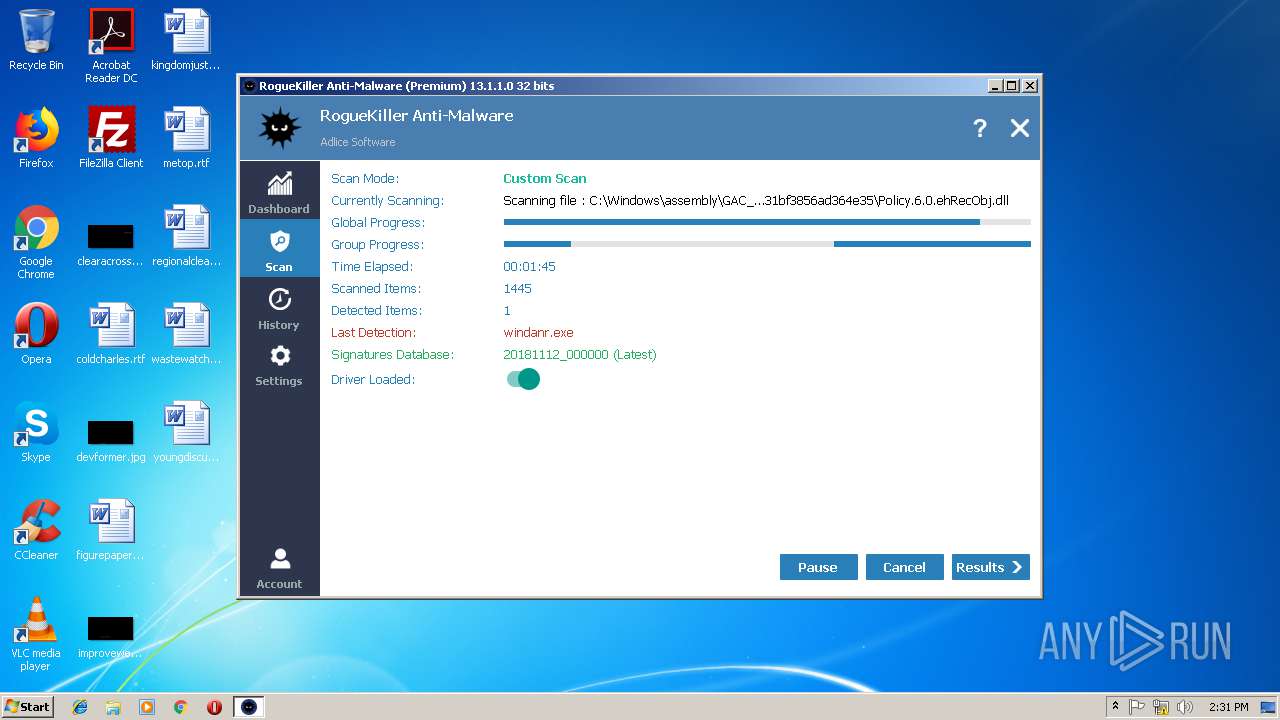
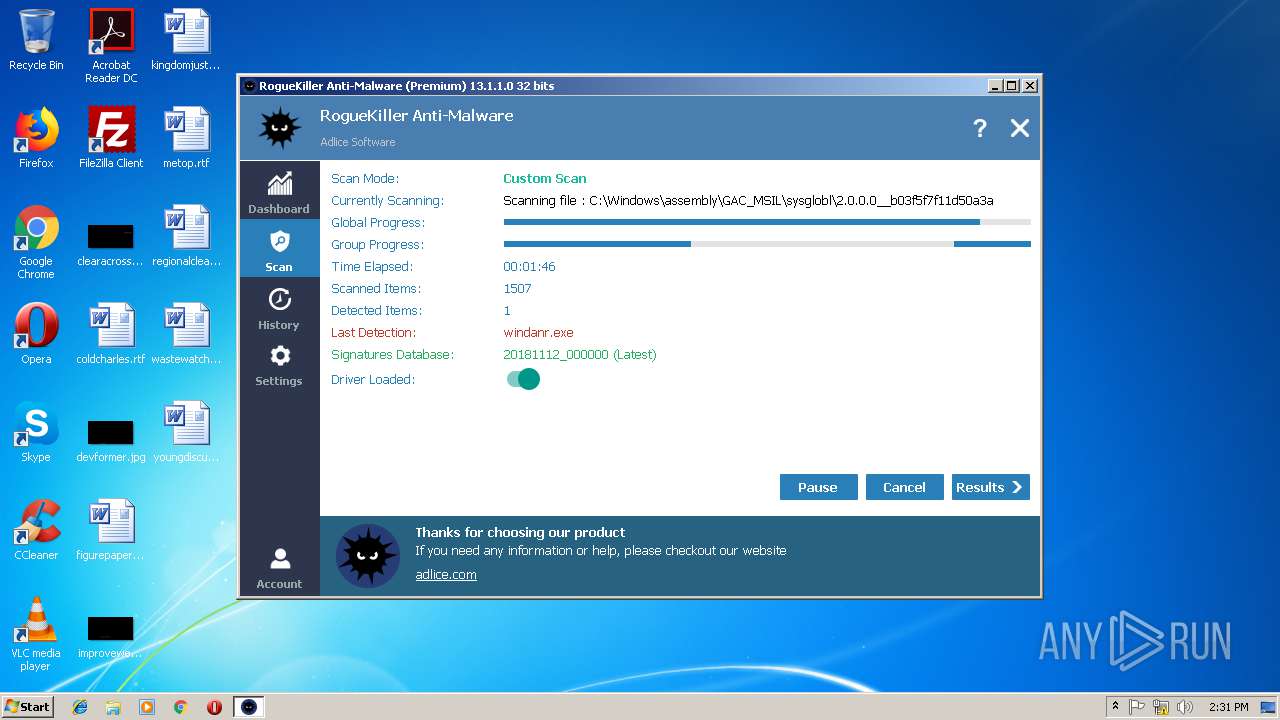
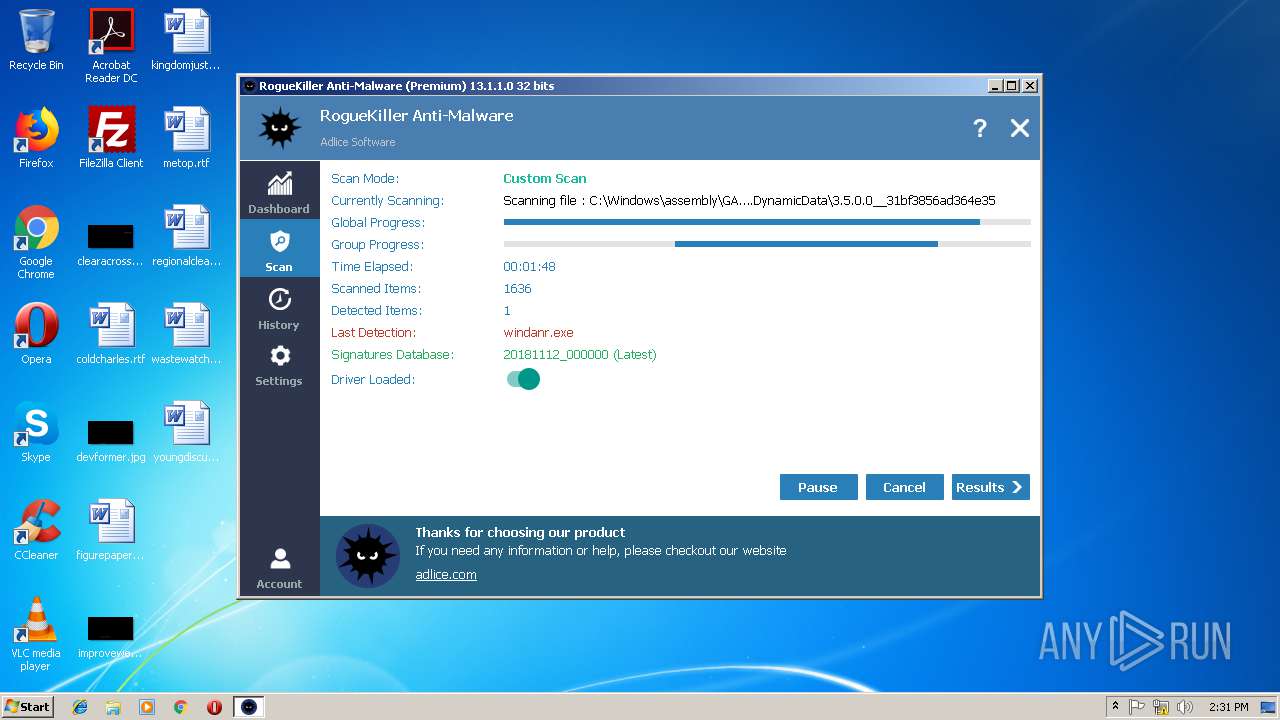
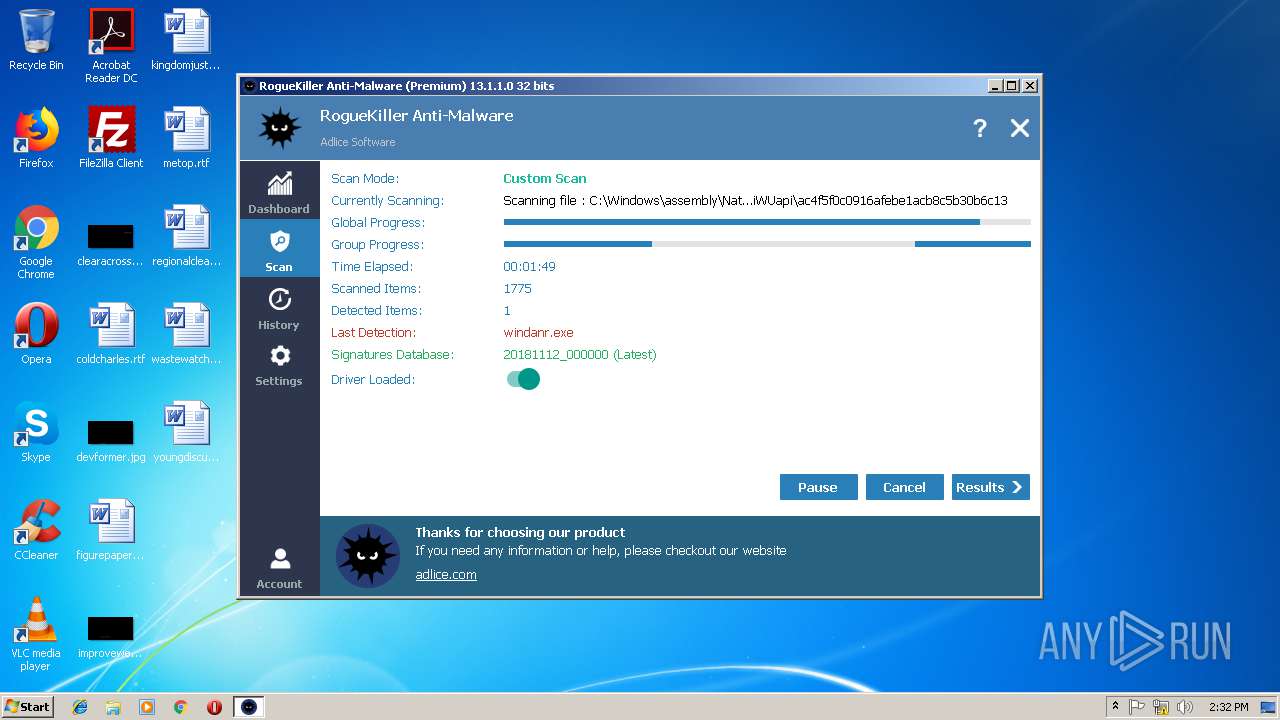
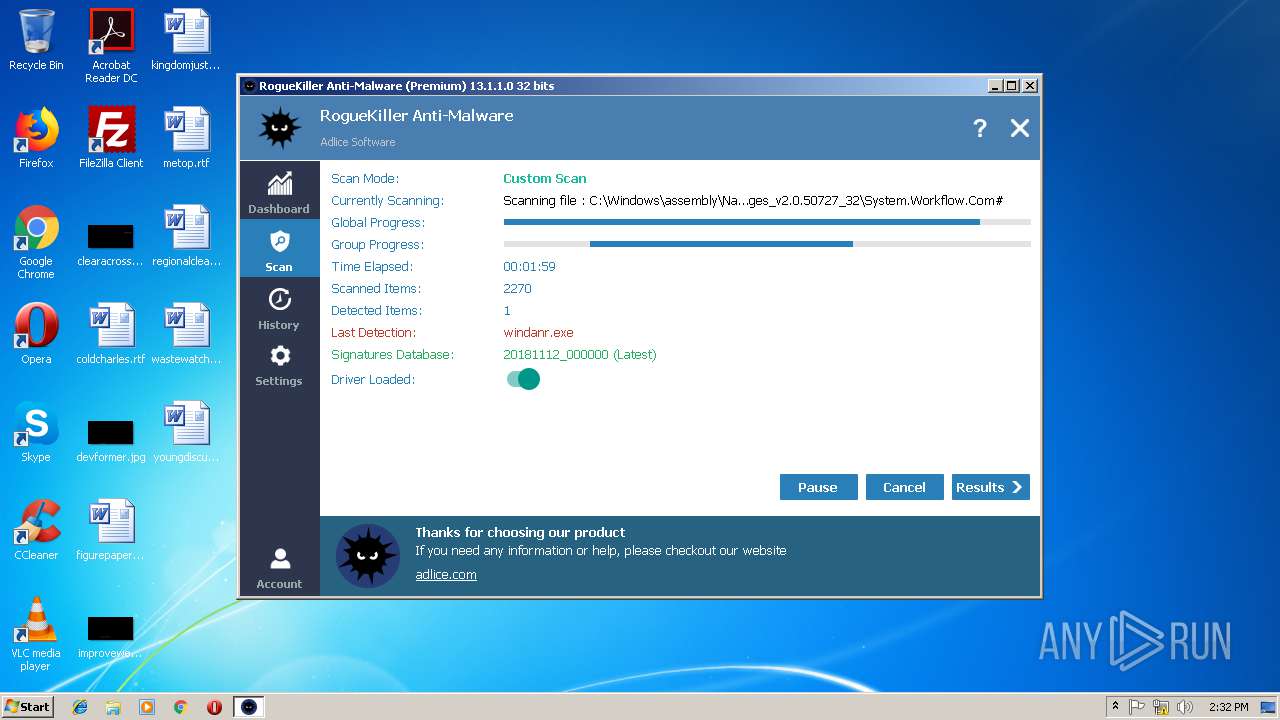
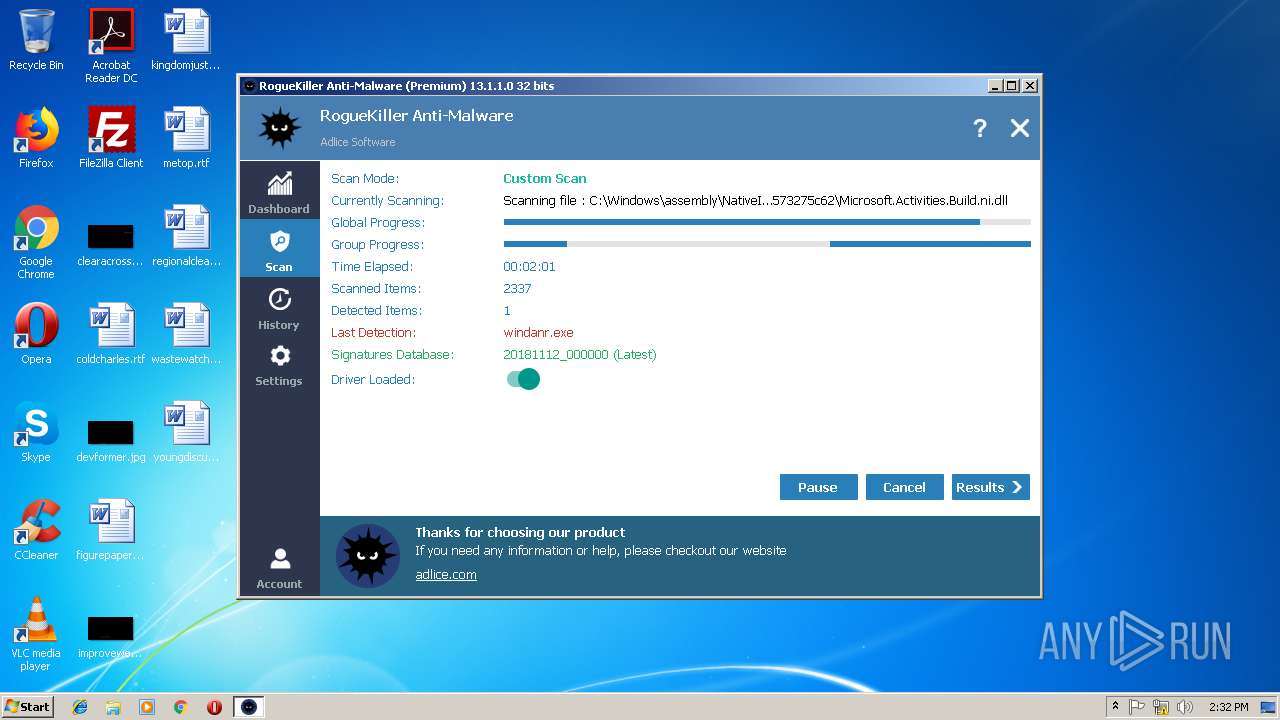
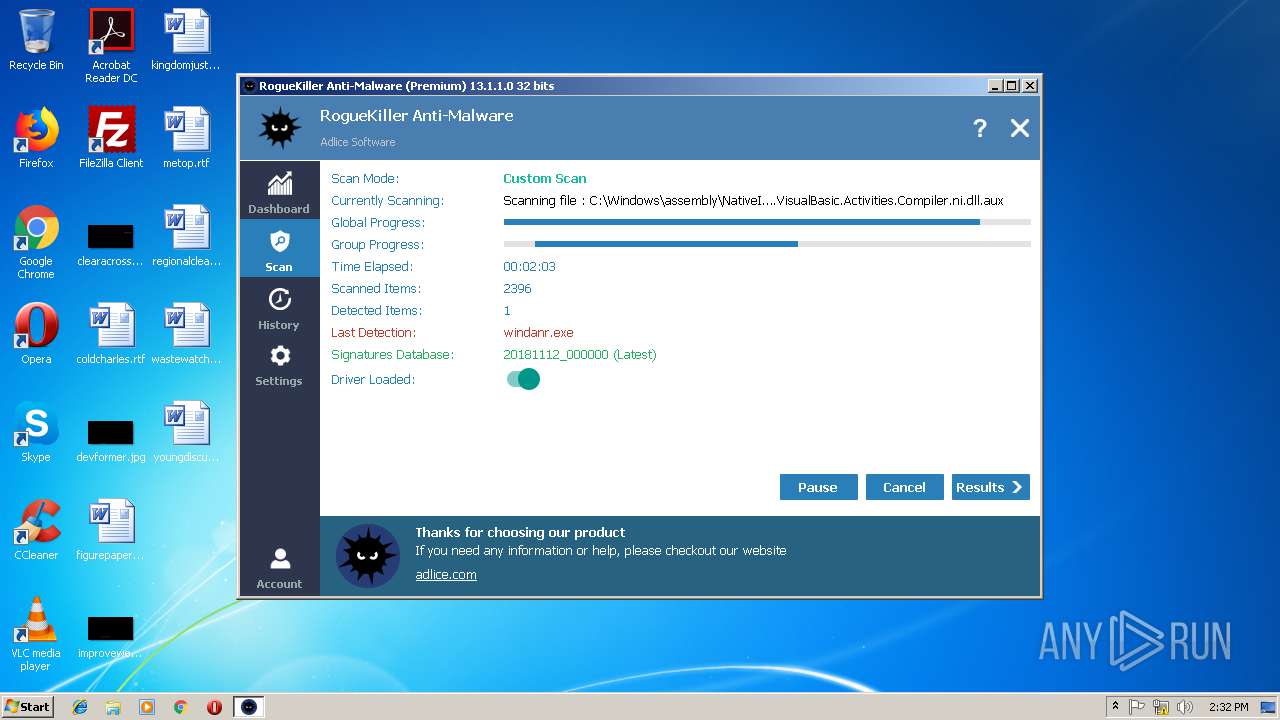
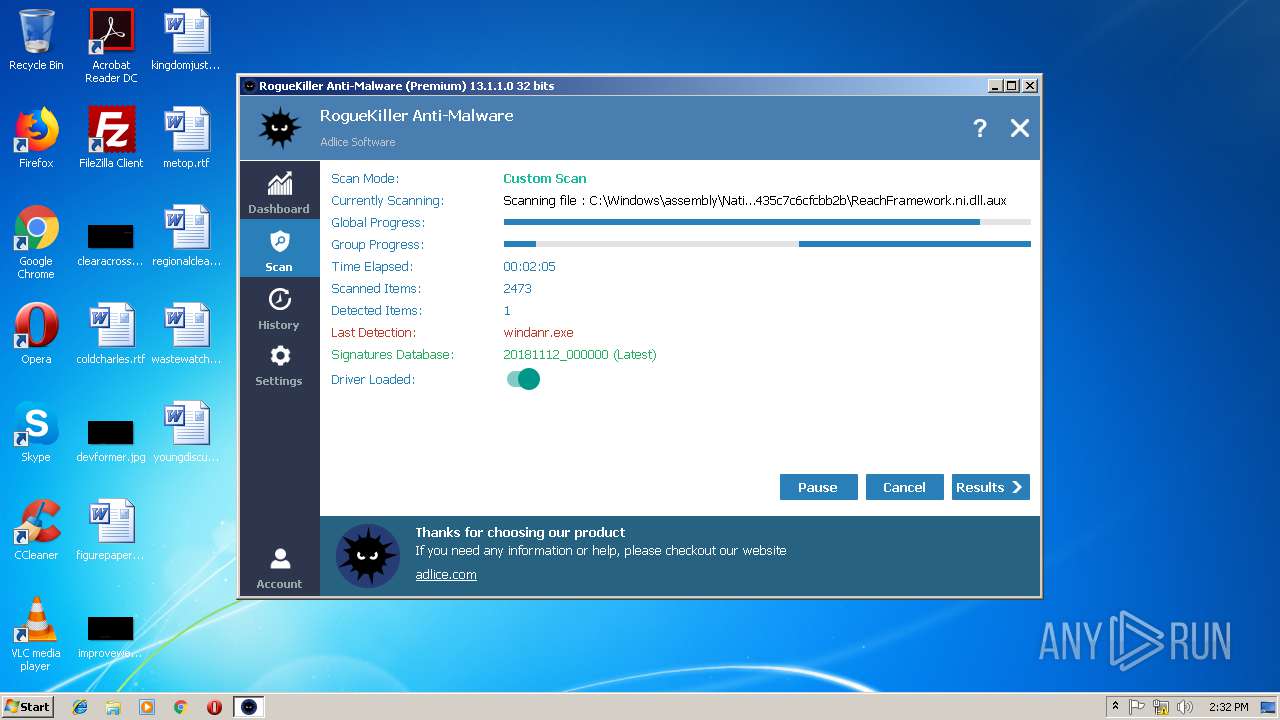
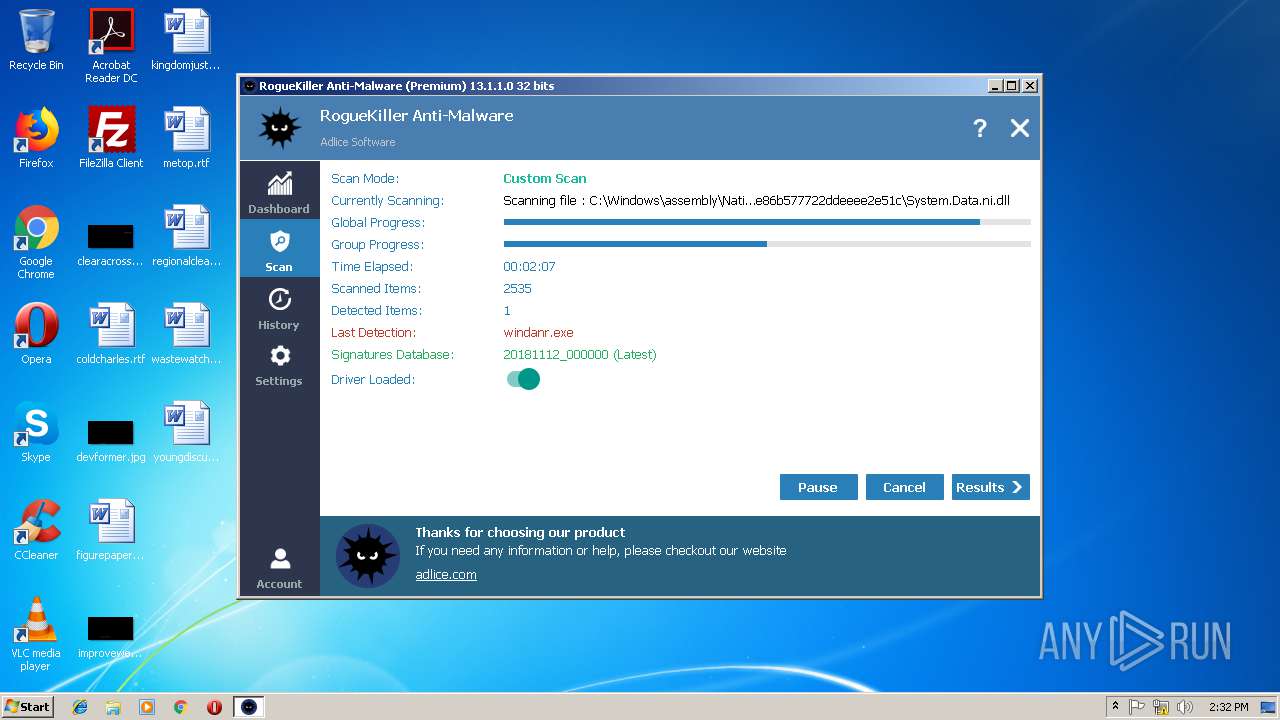
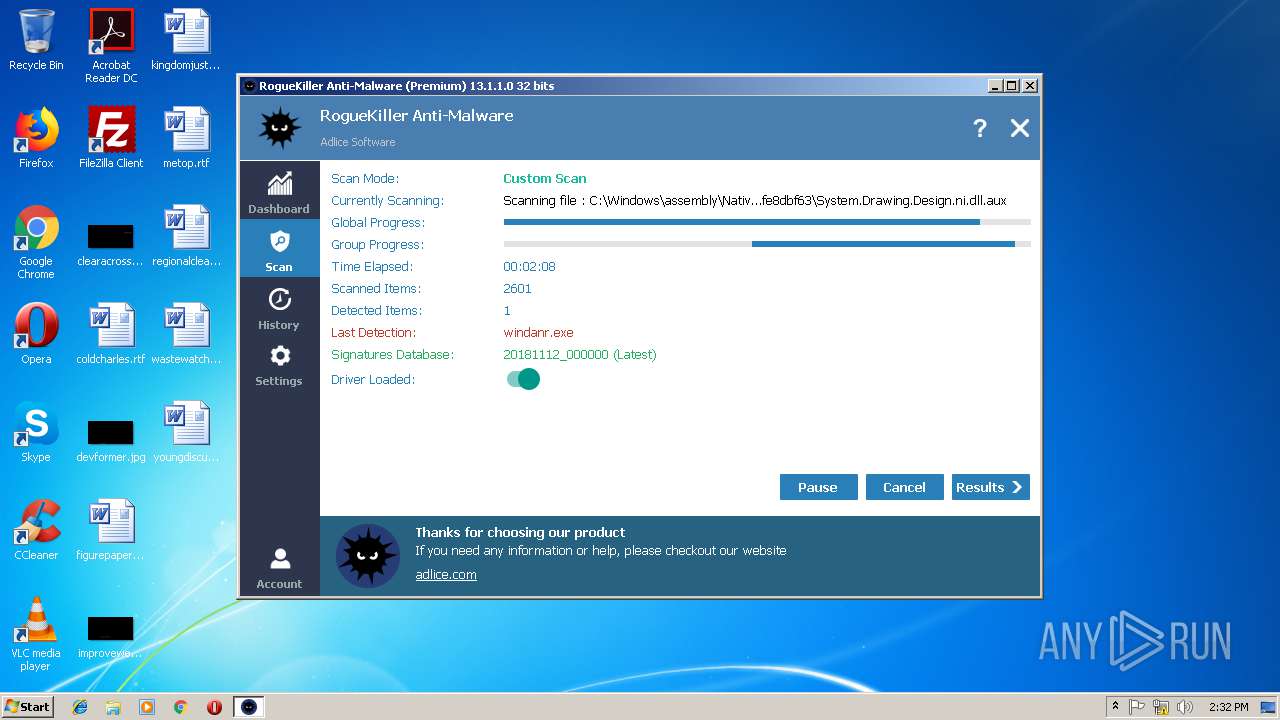
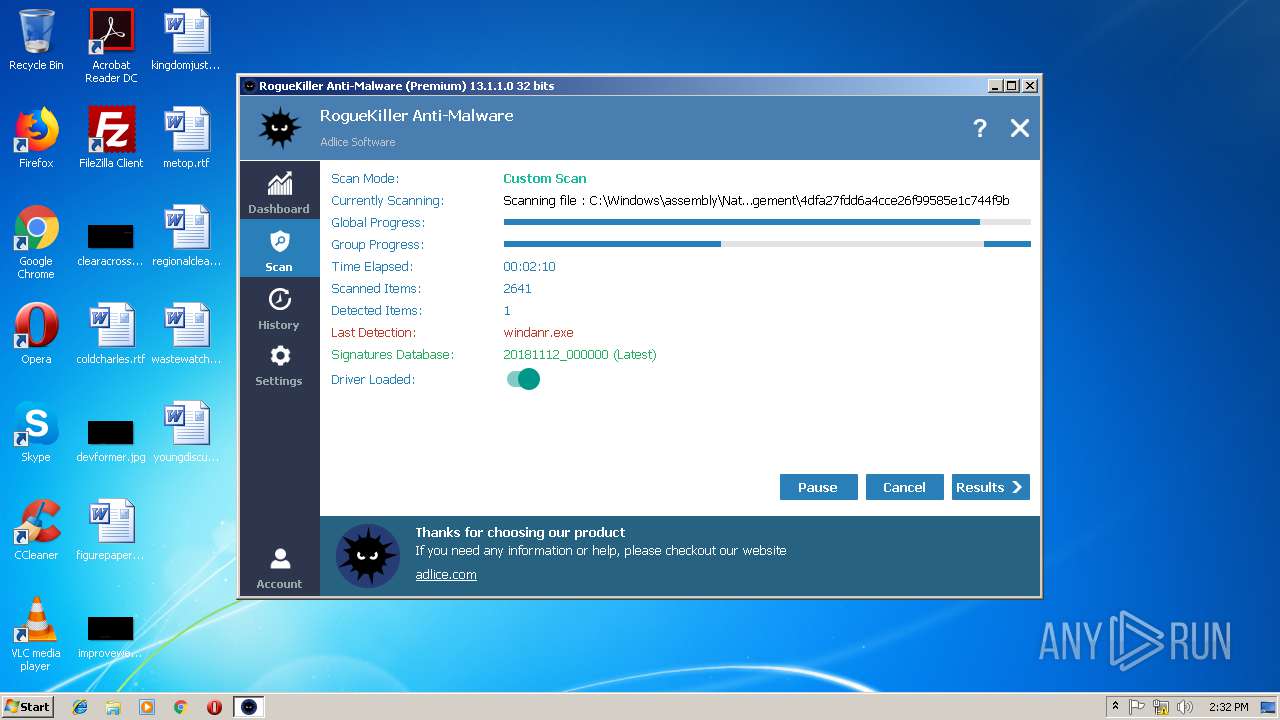
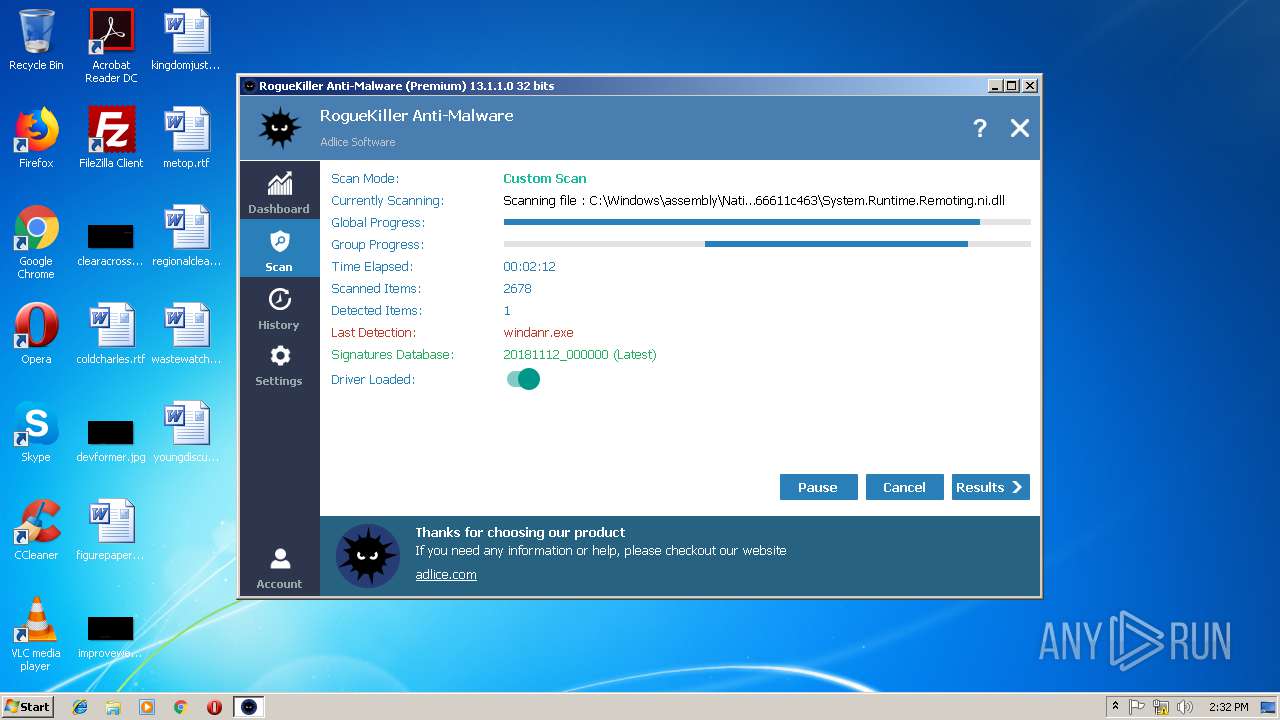
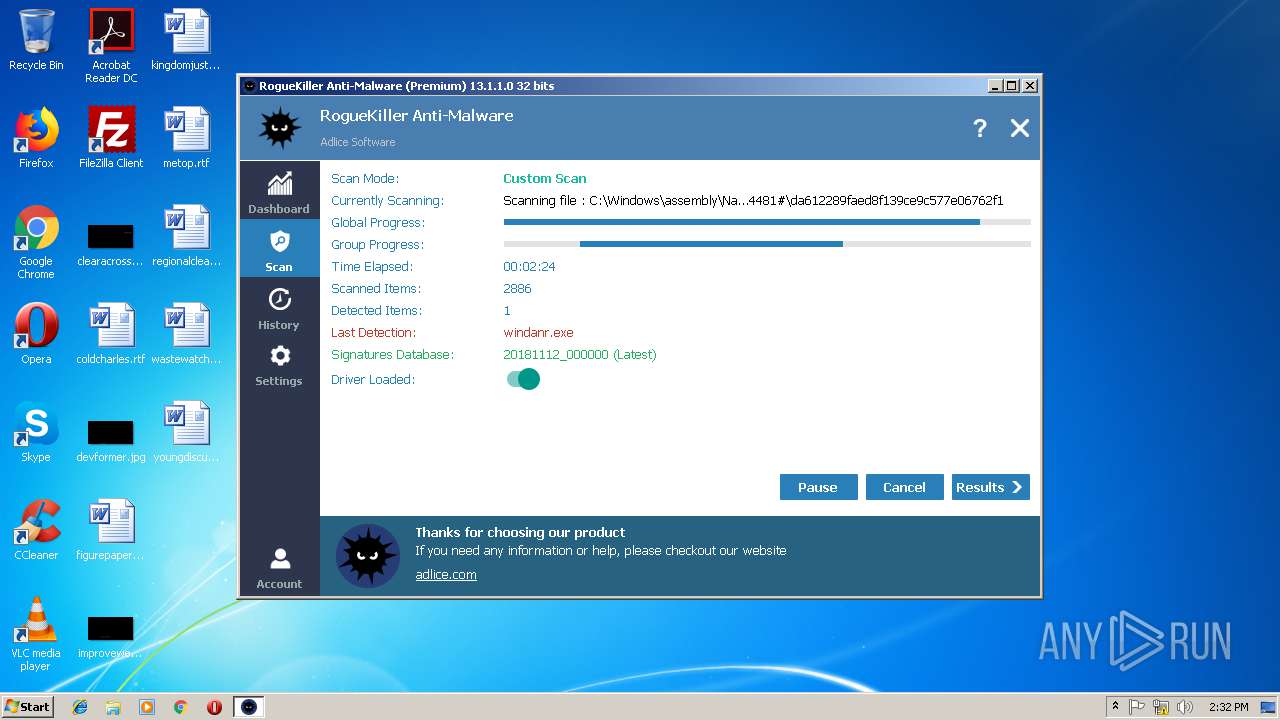
MALICIOUS
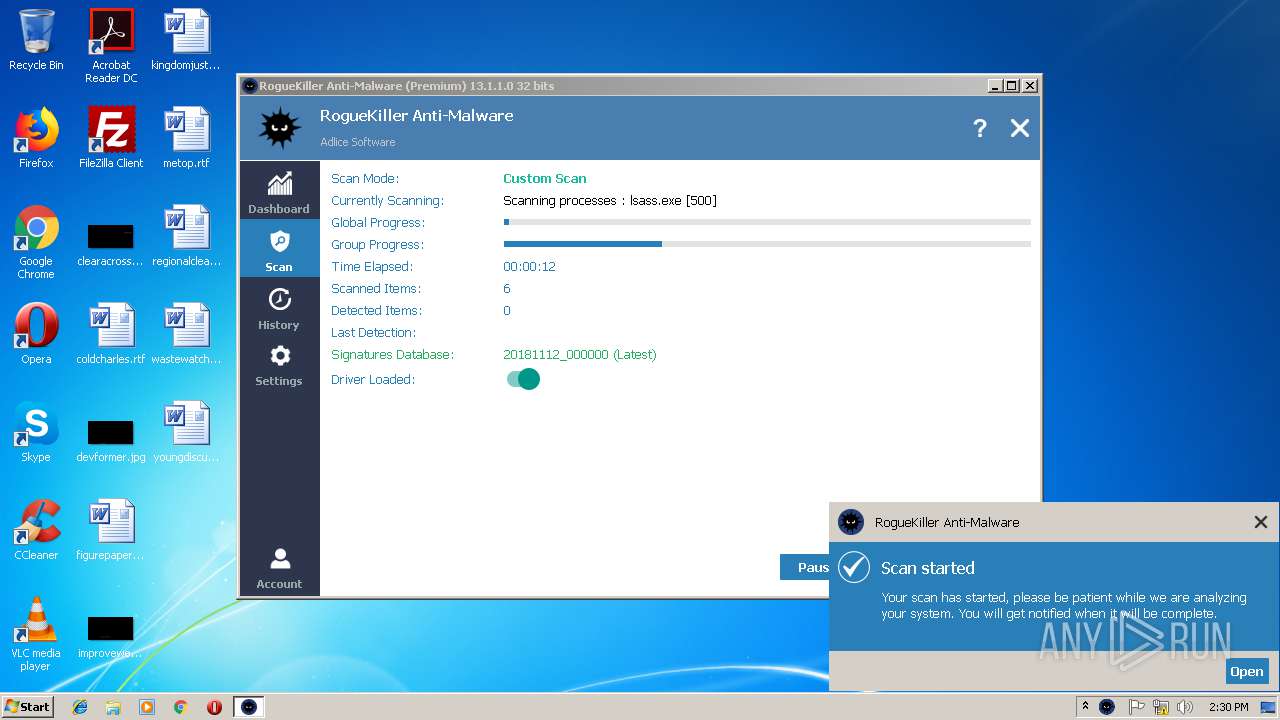
Loads the Task Scheduler COM API
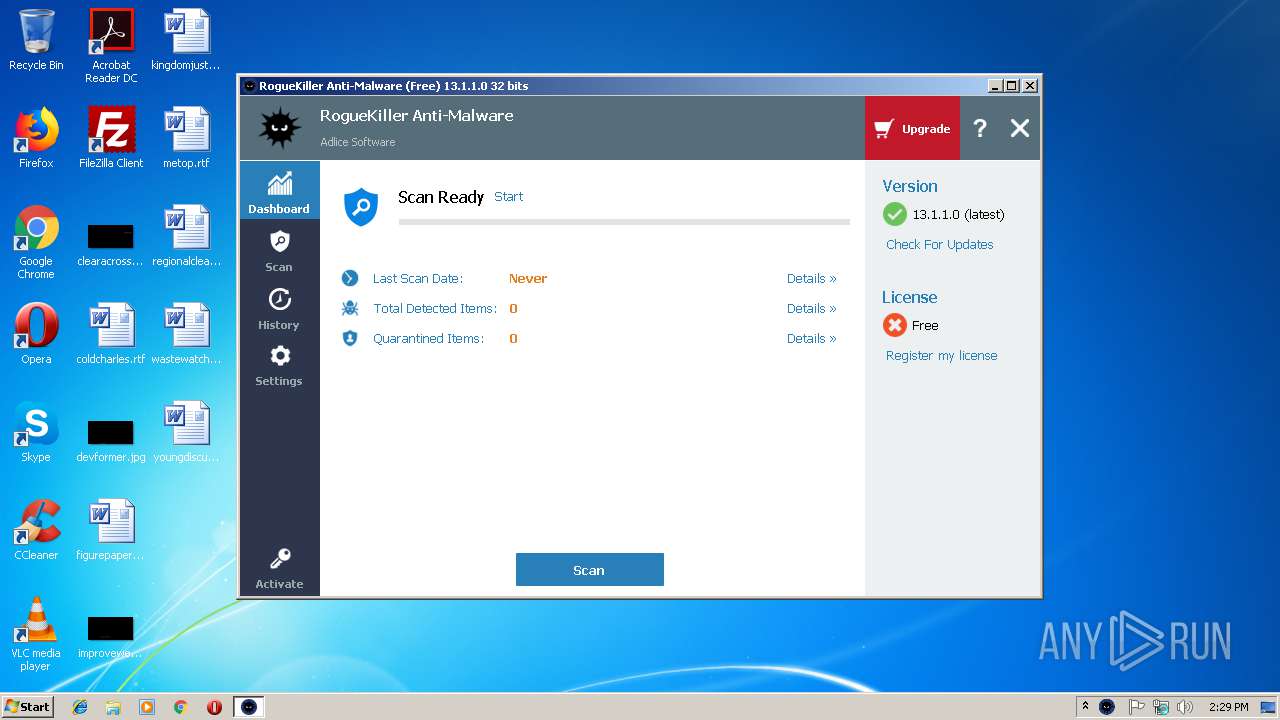
- RogueKiller[1].exe (PID: 3288)
Loads the Task Scheduler DLL interface
- RogueKiller[1].exe (PID: 3288)
Application was dropped or rewritten from another process
- RogueKiller[1].exe (PID: 3288)
- RogueKiller[1].exe (PID: 2264)
SUSPICIOUS
Executable content was dropped or overwritten
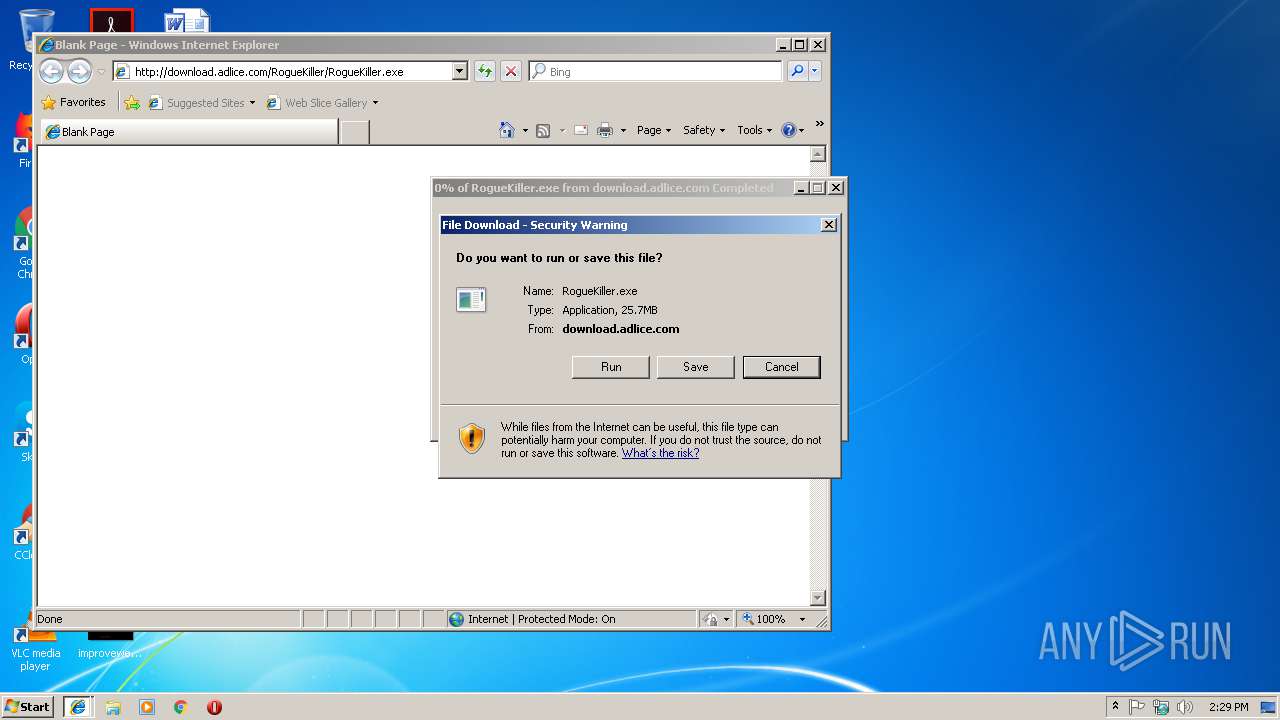
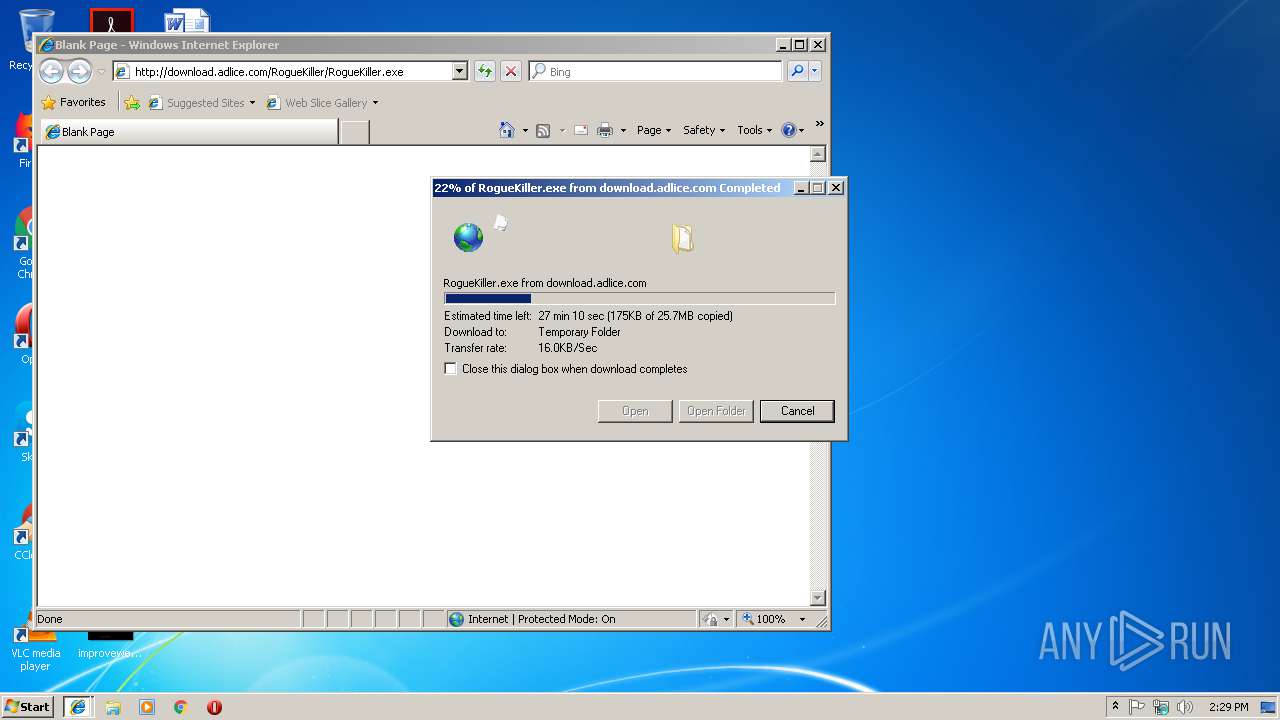
- iexplore.exe (PID: 3976)
- iexplore.exe (PID: 3508)
- RogueKiller[1].exe (PID: 3288)
Low-level read access rights to disk partition
- RogueKiller[1].exe (PID: 3288)
Reads Internet Cache Settings
- RogueKiller[1].exe (PID: 3288)
Creates files in the program directory
- RogueKiller[1].exe (PID: 3288)
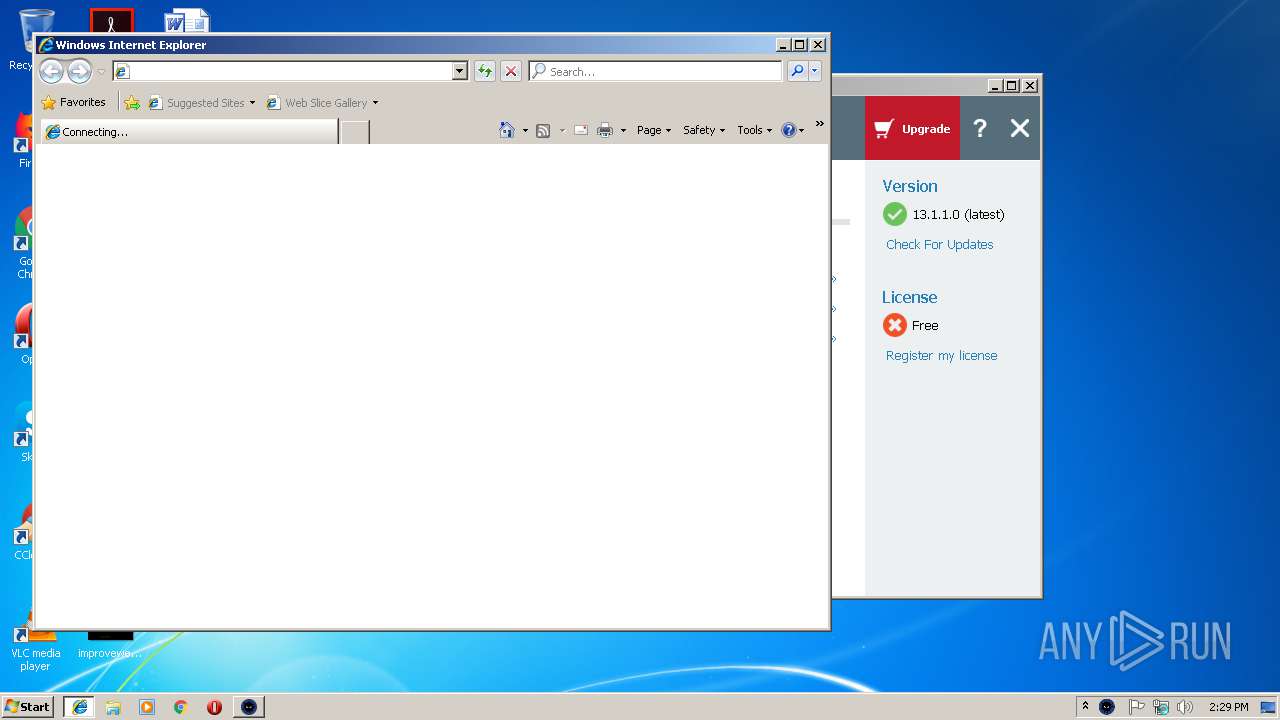
Starts Internet Explorer
- RogueKiller[1].exe (PID: 3288)
Creates files in the Windows directory
- RogueKiller[1].exe (PID: 3288)
Creates files in the driver directory
- RogueKiller[1].exe (PID: 3288)
Creates or modifies windows services
- RogueKiller[1].exe (PID: 3288)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 3108)
Reads Internet Cache Settings
- iexplore.exe (PID: 3976)
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 3772)
Application launched itself
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 3108)
Reads internet explorer settings
- iexplore.exe (PID: 3976)
- iexplore.exe (PID: 3772)
Changes settings of System certificates
- iexplore.exe (PID: 3772)
Creates files in the user directory
- iexplore.exe (PID: 3772)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3772)
Reads settings of System Certificates
- RogueKiller[1].exe (PID: 3288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:07:14 00:47:16+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 104448 |
| InitializedDataSize: | 352768 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcd2f |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | WindowsFormsApp1 |
| FileVersion: | 1.0.0.0 |
| InternalName: | WindowsFormsApp1.exe |
| LegalCopyright: | Copyright © 2018 |
| LegalTrademarks: | - |
| OriginalFileName: | WindowsFormsApp1.exe |
| ProductName: | WindowsFormsApp1 |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Jul-2012 22:47:16 |
| Debug artifacts: | |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | WindowsFormsApp1 |
| FileVersion: | 1.0.0.0 |
| InternalName: | WindowsFormsApp1.exe |
| LegalCopyright: | Copyright © 2018 |
| LegalTrademarks: | - |
| OriginalFilename: | WindowsFormsApp1.exe |
| ProductName: | WindowsFormsApp1 |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 13-Jul-2012 22:47:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00019718 | 0x00019800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.7486 |
.rdata | 0x0001B000 | 0x00006DB4 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.44296 |
.data | 0x00022000 | 0x000030C0 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.26259 |
.rsrc | 0x00026000 | 0x0004DDA4 | 0x0004DE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.26764 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 0.795976 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 0.966136 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 1.04558 | 21640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 1.0192 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 1.19463 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 1.34302 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 1.46106 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 1.61797 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
32512 | 3.03466 | 132 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
OLEAUT32.dll |
ole32.dll |
Total processes
42
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2264 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\RogueKiller[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\RogueKiller[1].exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3108 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://adlice.com/thanks-downloading-roguekiller/?utm_campaign=roguekiller&utm_source=soft&utm_medium=btn" | C:\Program Files\Internet Explorer\iexplore.exe | RogueKiller[1].exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3128 | "C:\Users\admin\AppData\Local\Temp\Logger.exe" | C:\Users\admin\AppData\Local\Temp\Logger.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsFormsApp1 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
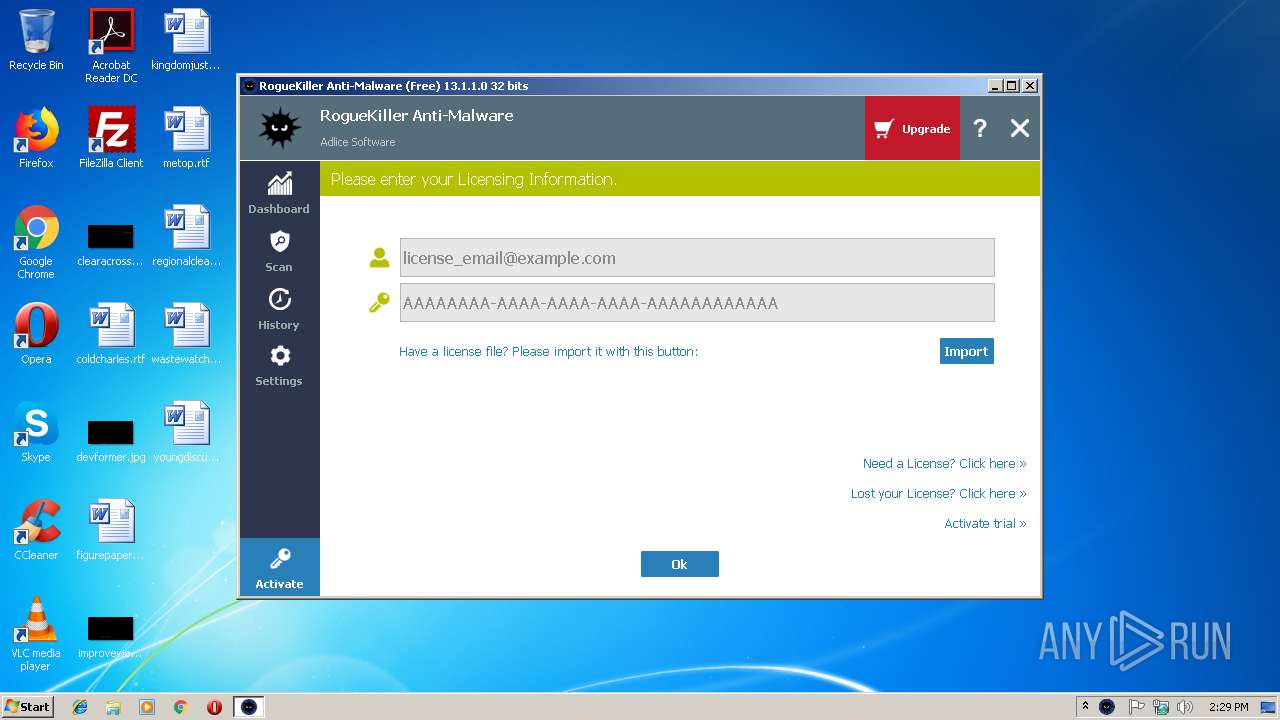
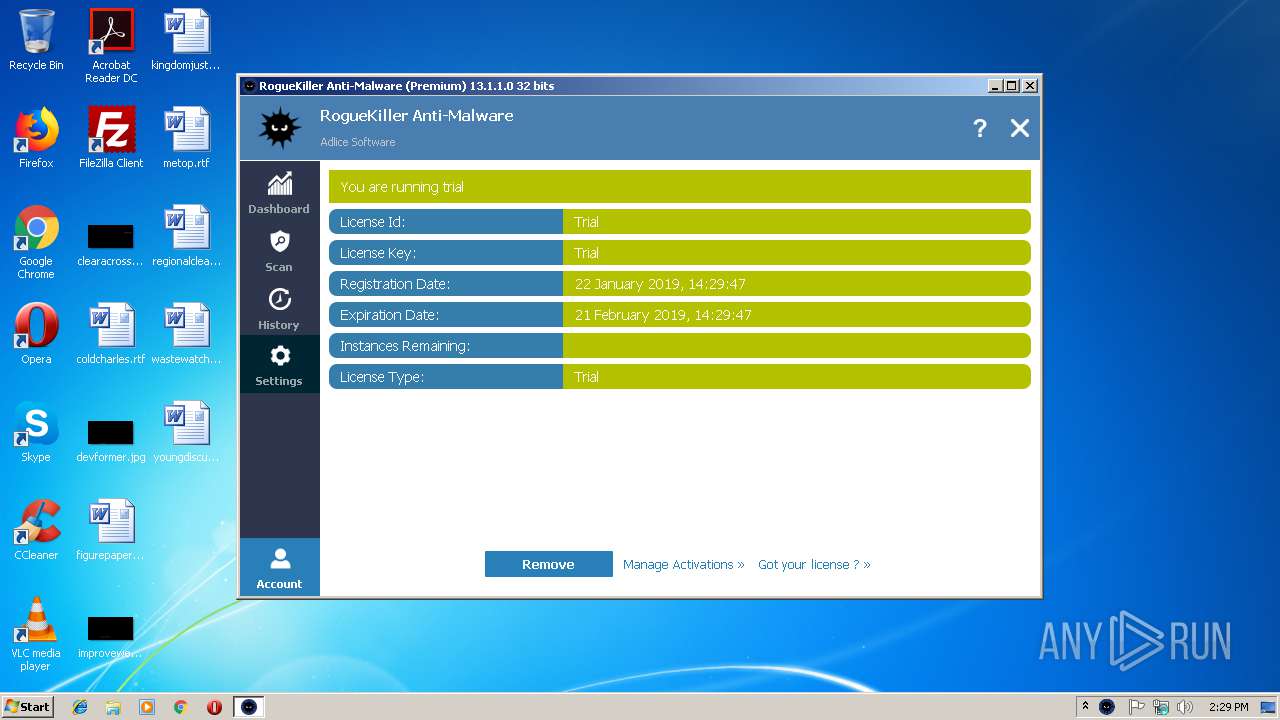
| 3288 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\RogueKiller[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\RogueKiller[1].exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3508 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3772 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3108 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3976 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3508 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 261
Read events
1 107
Write events
149
Delete events
5
Modification events
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {1E693559-1E52-11E9-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070100020016000E001D001B003500 | |||
Executable files
3
Suspicious files
15
Text files
49
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2D035D72D7BE98B2.TMP | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{4BBB6F4B-AC5C-11E8-969E-5254004AAD11}.dat | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF52AF27E23725547D.TMP | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2B5FA17000B18104.TMP | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{1E693559-1E52-11E9-91D7-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3772 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\thanks-downloading-roguekiller[1].txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
177
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3508 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3772 | iexplore.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODOECCAddTrustCA.crt | GB | der | 980 b | whitelisted |
3108 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
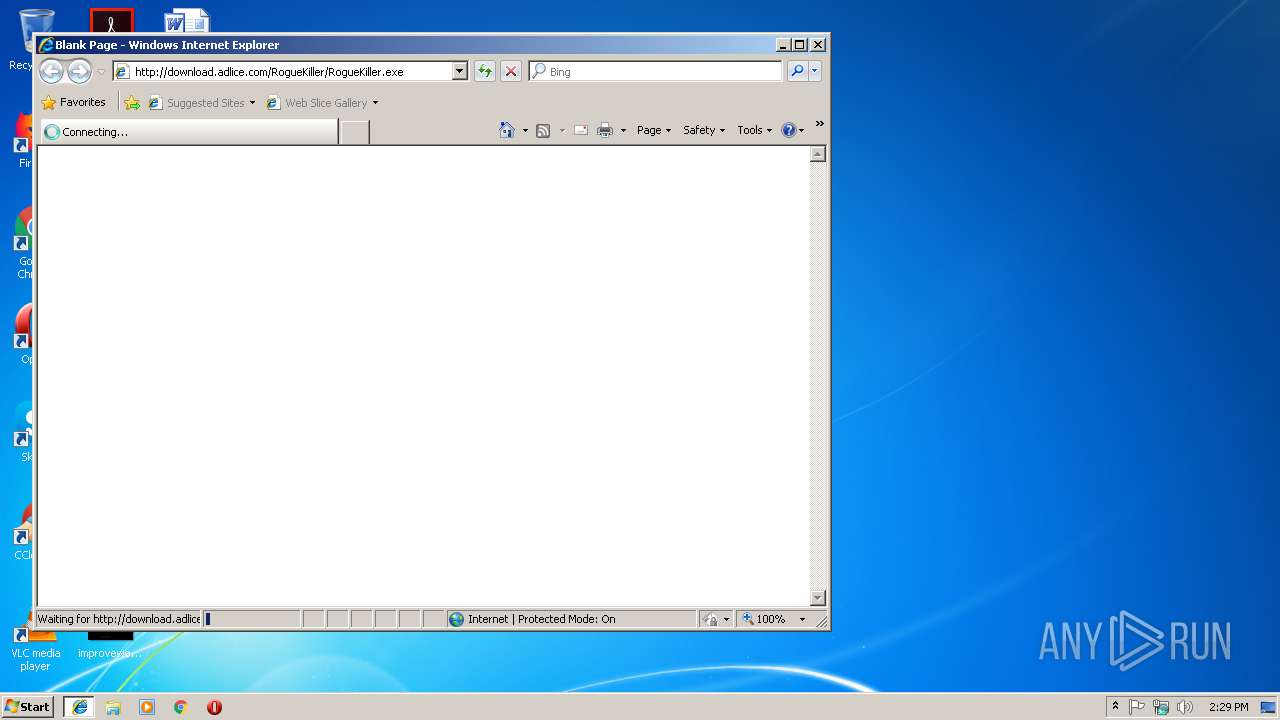
3976 | iexplore.exe | GET | 301 | 178.33.106.117:80 | http://download.adlice.com/RogueKiller/RogueKiller.exe | FR | html | 178 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3772 | iexplore.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3772 | iexplore.exe | 172.217.23.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3772 | iexplore.exe | 172.217.18.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3772 | iexplore.exe | 216.58.207.34:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3508 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3976 | iexplore.exe | 178.33.106.117:80 | download.adlice.com | OVH SAS | FR | suspicious |
3976 | iexplore.exe | 178.33.106.117:443 | download.adlice.com | OVH SAS | FR | suspicious |
3288 | RogueKiller[1].exe | 178.33.106.117:443 | download.adlice.com | OVH SAS | FR | suspicious |
3108 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3772 | iexplore.exe | 104.27.164.26:443 | adlice.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
download.adlice.com |
| whitelisted |
adlice.com |
| whitelisted |
crt.comodoca.com |
| whitelisted |
www.adlice.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
Threats
Process | Message |
|---|---|
RogueKiller[1].exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller[1].exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller[1].exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller[1].exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller[1].exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller[1].exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller[1].exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller[1].exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller[1].exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller[1].exe | libpng warning: iCCP: known incorrect sRGB profile
|