| File name: | RobloxPlayerLauncher.exe |
| Full analysis: | https://app.any.run/tasks/b402e745-0d44-4ea7-930a-d536f41dd68b |
| Verdict: | Malicious activity |
| Analysis date: | July 08, 2019, 04:18:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 95EAFB7BCE83CF641FAE3640236124E2 |
| SHA1: | 8267EF099ABFDF620686711F39B07A76BC6A30C3 |
| SHA256: | 0112F0BFC5B78F92AB95CCDBF007D60E7A378A991EC1B774922A96795B89315F |
| SSDEEP: | 24576:pf8WU435T0bEz/KlTU3/DuKLHDhh+EE5uKyTe83oBuY3thMEQ2PKdAwxZTn4o7qw:anQB0bELKpUbuWdh+X5uLTe83oBuY3tG |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- RobloxPlayerLauncher.exe (PID: 3076)
Modifies the open verb of a shell class
- RobloxPlayerLauncher.exe (PID: 3076)
Creates a software uninstall entry
- RobloxPlayerLauncher.exe (PID: 3076)
Creates files in the user directory
- RobloxPlayerLauncher.exe (PID: 3076)
Executable content was dropped or overwritten
- RobloxPlayerLauncher.exe (PID: 3076)
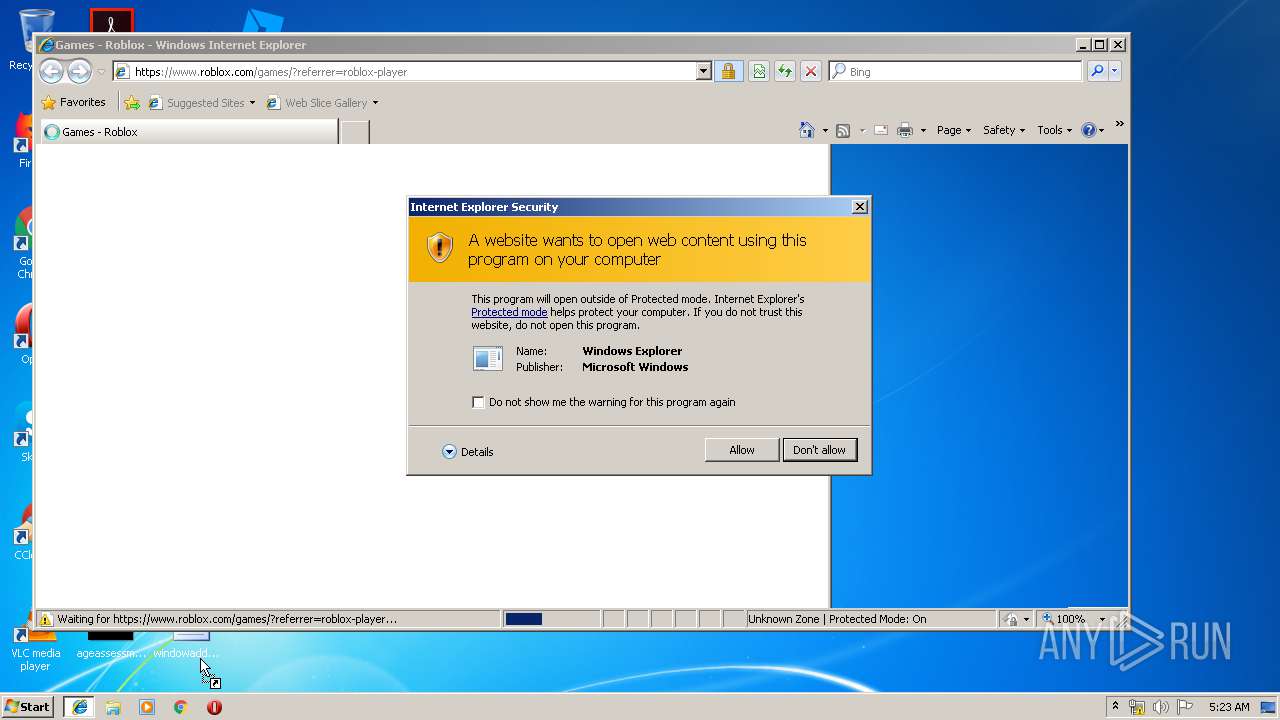
Starts Internet Explorer
- RobloxPlayerLauncher.exe (PID: 2616)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3020)
Reads Internet Cache Settings
- iexplore.exe (PID: 3224)
Dropped object may contain Bitcoin addresses
- RobloxPlayerLauncher.exe (PID: 3076)
Manual execution by user
- RobloxPlayerLauncher.exe (PID: 2616)
Application launched itself
- iexplore.exe (PID: 3020)
Creates files in the user directory
- iexplore.exe (PID: 3224)
Reads internet explorer settings
- iexplore.exe (PID: 3224)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3020)
Changes settings of System certificates
- iexplore.exe (PID: 3020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:20 22:55:22+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 847872 |
| InitializedDataSize: | 780288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5af33 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.6.3.51533 |
| ProductVersionNumber: | 1.6.3.51533 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Roblox Corporation |
| FileDescription: | Roblox |
| FileVersion: | 1, 6, 3, 313677 |
| LegalCopyright: | Copyright © 2019 Roblox Corporation. All rights reserved. |
| OriginalFileName: | Roblox.exe |
| ProductName: | Roblox Bootstrapper |
| ProductVersion: | 1, 6, 3, 313677 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Jun-2019 20:55:22 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| Debug artifacts: |
|
| CompanyName: | Roblox Corporation |
| FileDescription: | Roblox |
| FileVersion: | 1, 6, 3, 313677 |
| LegalCopyright: | Copyright © 2019 Roblox Corporation. All rights reserved. |
| OriginalFilename: | Roblox.exe |
| ProductName: | Roblox Bootstrapper |
| ProductVersion: | 1, 6, 3, 313677 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000140 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 20-Jun-2019 20:55:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000CEFA7 | 0x000CF000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63119 |
.rdata | 0x000D0000 | 0x000439E6 | 0x00043A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.74109 |
.data | 0x00114000 | 0x00056288 | 0x00004A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.73824 |
.tls | 0x0016B000 | 0x0000000D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.gfids | 0x0016C000 | 0x00000188 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.38032 |
CPADinfo( | 0x0016D000 | 0x00000028 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.122276 |
.rsrc | 0x0016E000 | 0x00019268 | 0x00019400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.00673 |
.reloc | 0x00188000 | 0x0000AEA0 | 0x0000B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64064 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.33374 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.78815 | 76 | UNKNOWN | Process Default Language | RT_GROUP_ICON |
3 | 4.77404 | 4264 | UNKNOWN | Process Default Language | RT_ICON |
4 | 4.46883 | 16672 | UNKNOWN | Process Default Language | RT_ICON |
5 | 4.5291 | 9640 | UNKNOWN | Process Default Language | RT_ICON |
7 | 3.38178 | 488 | UNKNOWN | Portuguese - Brazil | RT_STRING |
8 | 3.32834 | 602 | UNKNOWN | Portuguese - Brazil | RT_STRING |
130 | 3.12907 | 254 | UNKNOWN | Process Default Language | RT_DIALOG |
131 | 2 | 8 | UNKNOWN | Process Default Language | RT_ACCELERATOR |
157 | 7.30906 | 665 | UNKNOWN | Process Default Language | PNG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
POWRPROF.dll |
PSAPI.DLL |
SHELL32.dll |
SHLWAPI.dll |
SensApi.dll |
USER32.dll |
Total processes
42
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2452 | C:\Users\admin\AppData\Local\Roblox\Versions\version-536bcde179ed49c8\RobloxPlayerLauncher.exe --crashpad --no-rate-limit --database=C:\Users\admin\AppData\Local\Temp\crashpad_roblox --metrics-dir=C:\Users\admin\AppData\Local\Temp\crashpad_roblox --url=https://upload.crashes.rbxinfra.com/post --annotation=UploadAttachmentKiloByteLimit=100 --annotation=UploadPercentage=100 --annotation=format=minidump --annotation=token=a2440b0bfdada85f34d79b43839f2b49ea6bba474bd7d126e844bc119271a1c3 --initial-client-data=0x55c,0x560,0x564,0x558,0x56c,0x1ba184,0x1ba194,0x1ba1a4 | C:\Users\admin\AppData\Local\Roblox\Versions\version-536bcde179ed49c8\RobloxPlayerLauncher.exe | RobloxPlayerLauncher.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 0 Version: 1, 6, 3, 313677 Modules
| |||||||||||||||
| 2616 | "C:\Users\admin\AppData\Local\Roblox\Versions\version-536bcde179ed49c8\RobloxPlayerLauncher.exe" -browser | C:\Users\admin\AppData\Local\Roblox\Versions\version-536bcde179ed49c8\RobloxPlayerLauncher.exe | explorer.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 0 Version: 1, 6, 3, 313677 Modules
| |||||||||||||||
| 3020 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | RobloxPlayerLauncher.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3076 | "C:\Users\admin\AppData\Local\Temp\RobloxPlayerLauncher.exe" | C:\Users\admin\AppData\Local\Temp\RobloxPlayerLauncher.exe | explorer.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 0 Version: 1, 6, 3, 313677 Modules
| |||||||||||||||
| 3224 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3020 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3260 | C:\Users\admin\AppData\Local\Temp\RobloxPlayerLauncher.exe --crashpad --no-rate-limit --database=C:\Users\admin\AppData\Local\Temp\crashpad_roblox --metrics-dir=C:\Users\admin\AppData\Local\Temp\crashpad_roblox --url=https://upload.crashes.rbxinfra.com/post --annotation=UploadAttachmentKiloByteLimit=100 --annotation=UploadPercentage=100 --annotation=format=minidump --annotation=token=a2440b0bfdada85f34d79b43839f2b49ea6bba474bd7d126e844bc119271a1c3 --initial-client-data=0x55c,0x560,0x564,0x558,0x56c,0x145a184,0x145a194,0x145a1a4 | C:\Users\admin\AppData\Local\Temp\RobloxPlayerLauncher.exe | RobloxPlayerLauncher.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 0 Version: 1, 6, 3, 313677 Modules
| |||||||||||||||
Total events
1 032
Read events
853
Write events
177
Delete events
2
Modification events
| (PID) Process: | (3076) RobloxPlayerLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RobloxPlayerLauncher_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3076) RobloxPlayerLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RobloxPlayerLauncher_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3076) RobloxPlayerLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RobloxPlayerLauncher_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3076) RobloxPlayerLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RobloxPlayerLauncher_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3076) RobloxPlayerLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RobloxPlayerLauncher_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3076) RobloxPlayerLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RobloxPlayerLauncher_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3076) RobloxPlayerLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RobloxPlayerLauncher_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3076) RobloxPlayerLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RobloxPlayerLauncher_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3076) RobloxPlayerLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RobloxPlayerLauncher_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3076) RobloxPlayerLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RobloxPlayerLauncher_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
3
Suspicious files
84
Text files
1 483
Unknown types
174
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3076 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@roblox[1].txt | — | |
MD5:— | SHA256:— | |||
| 3076 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Temp\Cab6923.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Temp\Tar6924.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Temp\Cab6945.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Temp\Tar6946.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Temp\Cab6A02.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Temp\Tar6A03.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Temp\RBX-9D4DA0E2.tmp | — | |
MD5:— | SHA256:— | |||
| 3260 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\application[1] | text | |
MD5:— | SHA256:— | |||
| 3076 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\application[1] | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
26
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3224 | iexplore.exe | GET | 301 | 209.206.41.230:80 | http://www.roblox.com/games/?referrer=roblox-player | US | html | 173 b | whitelisted |
3076 | RobloxPlayerLauncher.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
3076 | RobloxPlayerLauncher.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/47BEABC922EAE80E78783462A79F45C254FDE68B.crt | US | der | 969 b | whitelisted |
3020 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3076 | RobloxPlayerLauncher.exe | 104.109.74.223:443 | clientsettingscdn.roblox.com | Akamai International B.V. | NL | whitelisted |
3076 | RobloxPlayerLauncher.exe | 209.206.41.150:443 | ephemeralcounters.api.roblox.com | Roblox | US | unknown |
3260 | RobloxPlayerLauncher.exe | 104.109.74.223:443 | clientsettingscdn.roblox.com | Akamai International B.V. | NL | whitelisted |
3260 | RobloxPlayerLauncher.exe | 209.206.41.150:443 | ephemeralcounters.api.roblox.com | Roblox | US | unknown |
3076 | RobloxPlayerLauncher.exe | 209.206.41.230:443 | www.roblox.com | Roblox | US | suspicious |
3076 | RobloxPlayerLauncher.exe | 178.79.208.35:443 | setup.rbxcdn.com | Limelight Networks, Inc. | IT | unknown |
3020 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2452 | RobloxPlayerLauncher.exe | 104.109.74.223:443 | clientsettingscdn.roblox.com | Akamai International B.V. | NL | whitelisted |
2452 | RobloxPlayerLauncher.exe | 209.206.41.151:443 | ephemeralcounters.api.roblox.com | Roblox | US | suspicious |
— | — | 209.206.41.230:80 | www.roblox.com | Roblox | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientsettingscdn.roblox.com |
| whitelisted |
ephemeralcounters.api.roblox.com |
| whitelisted |
www.roblox.com |
| whitelisted |
setup.rbxcdn.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
ec2-54-165-151-168.compute-1.amazonaws.com |
| unknown |
www.bing.com |
| whitelisted |
static.rbxcdn.com |
| whitelisted |
authsite.roblox.com |
| whitelisted |
js.rbxcdn.com |
| whitelisted |