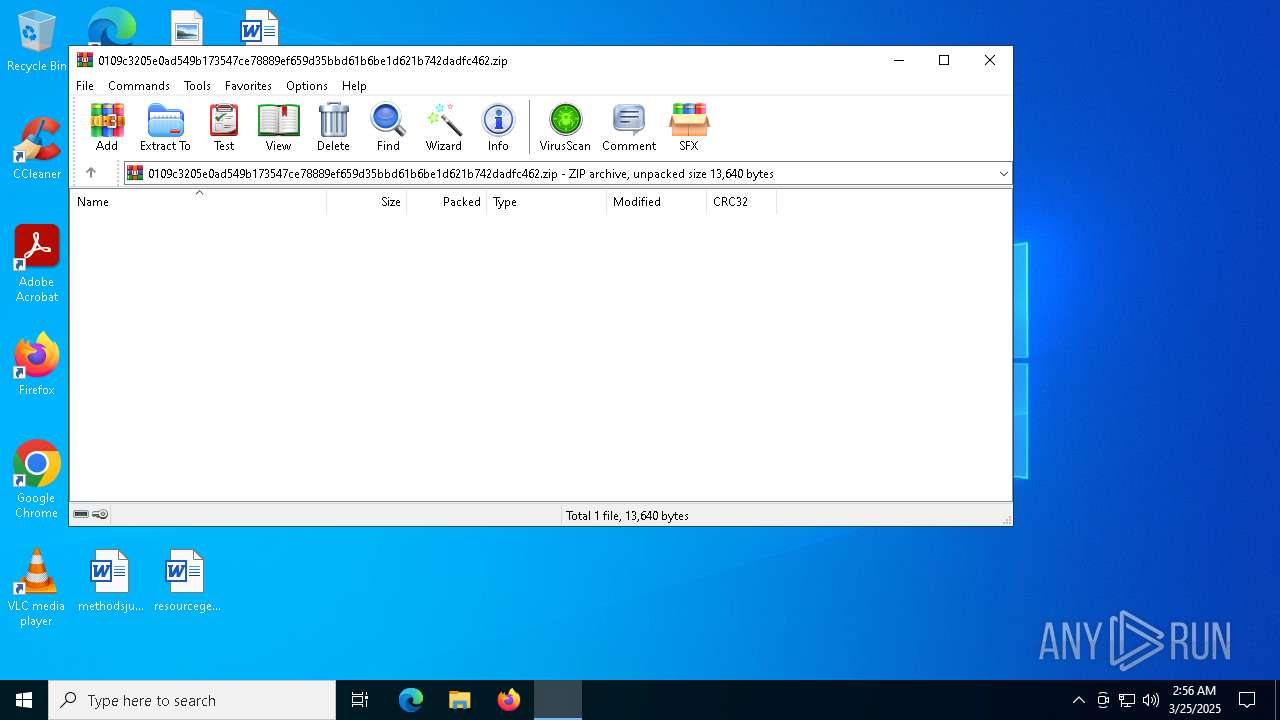
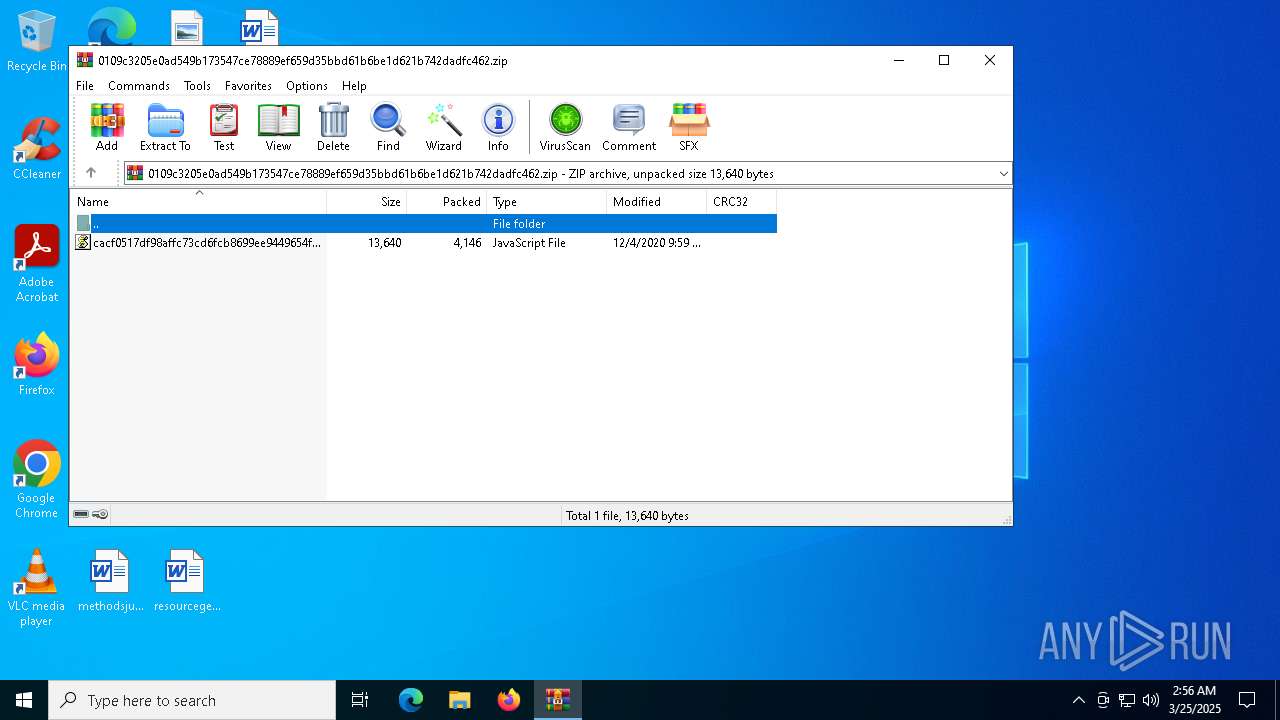
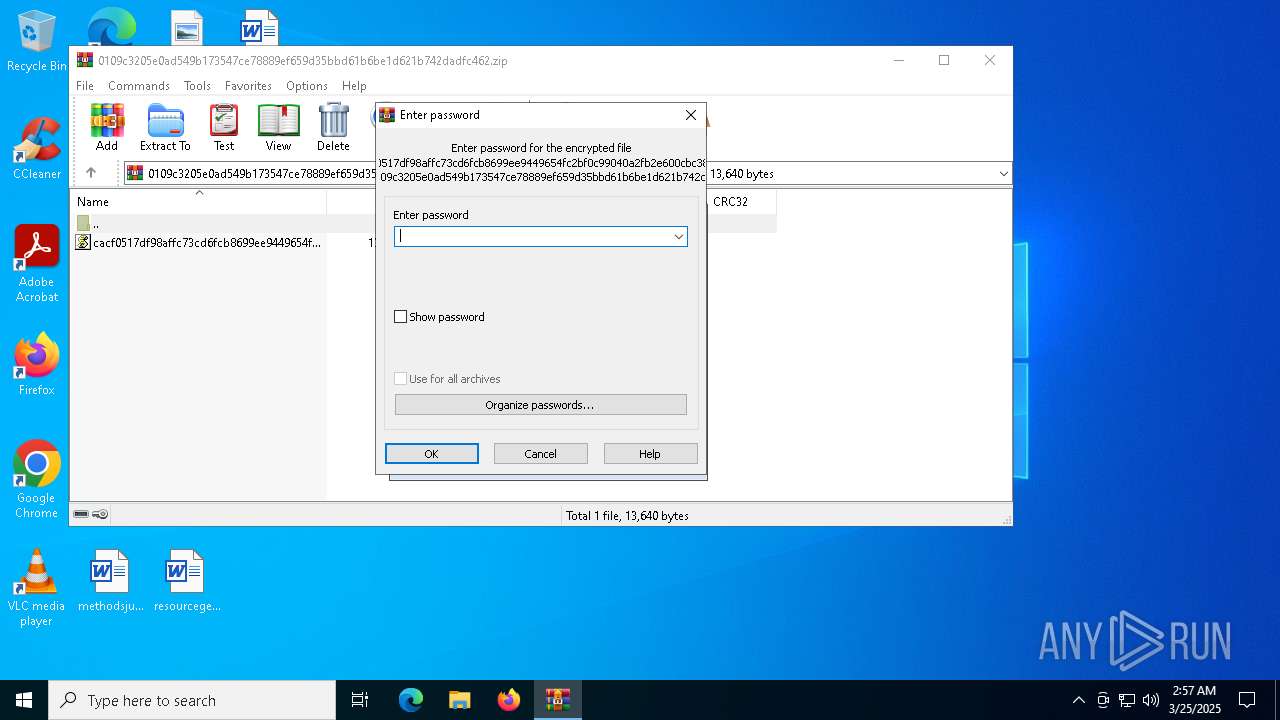
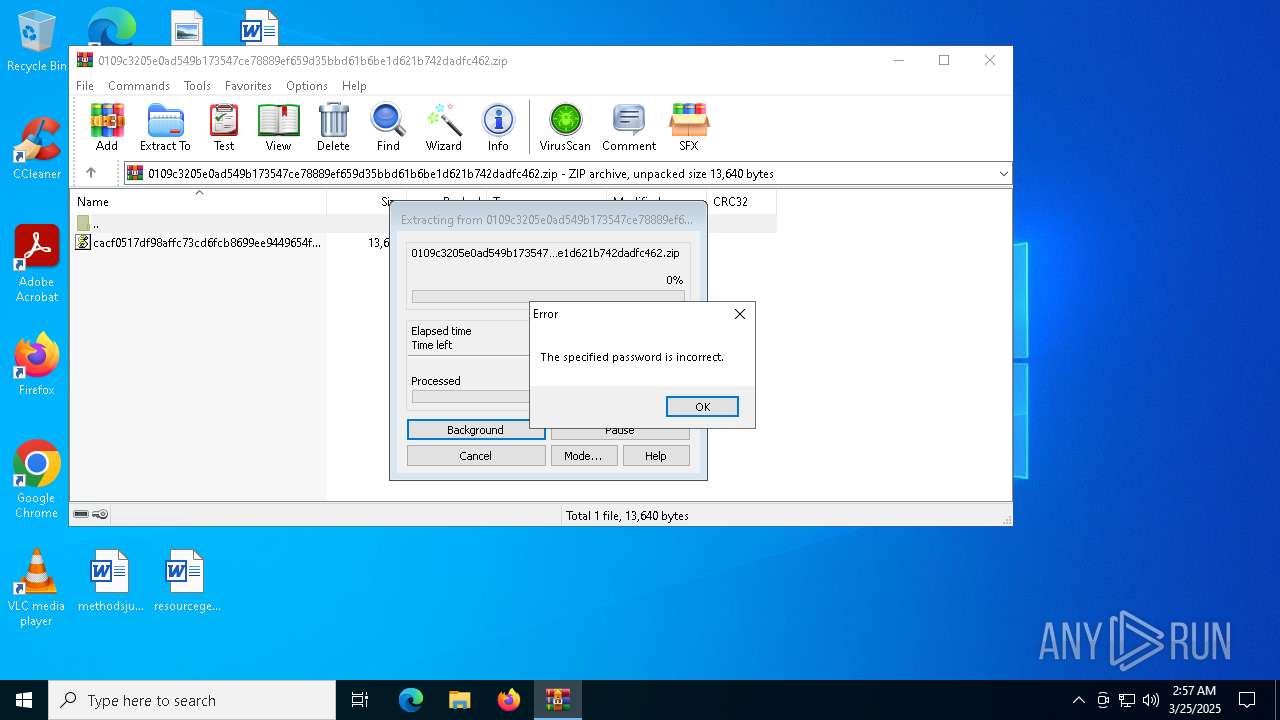
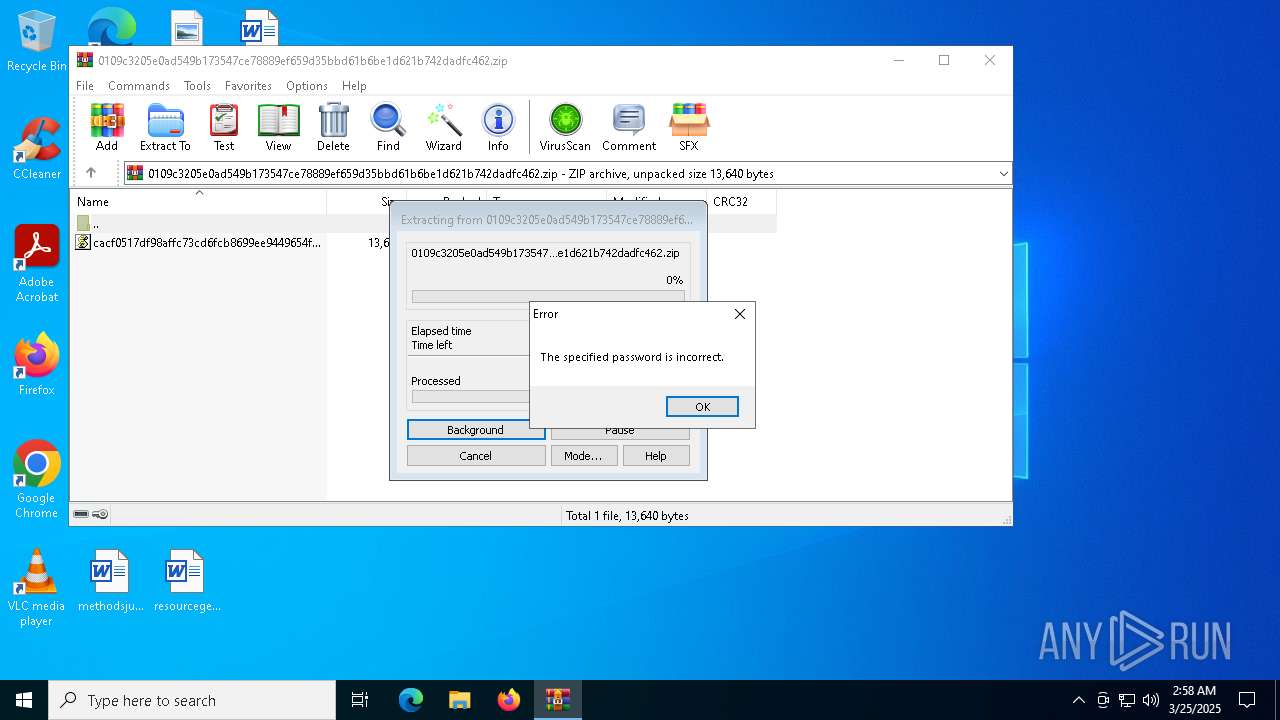
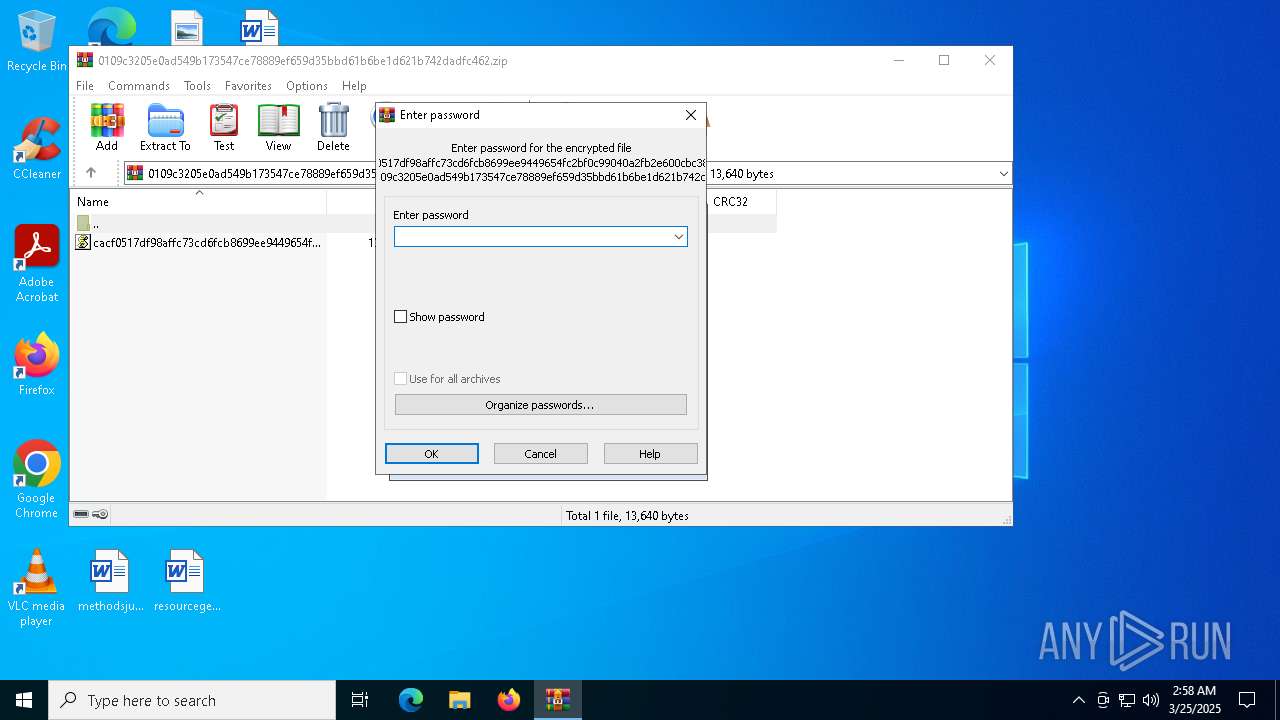
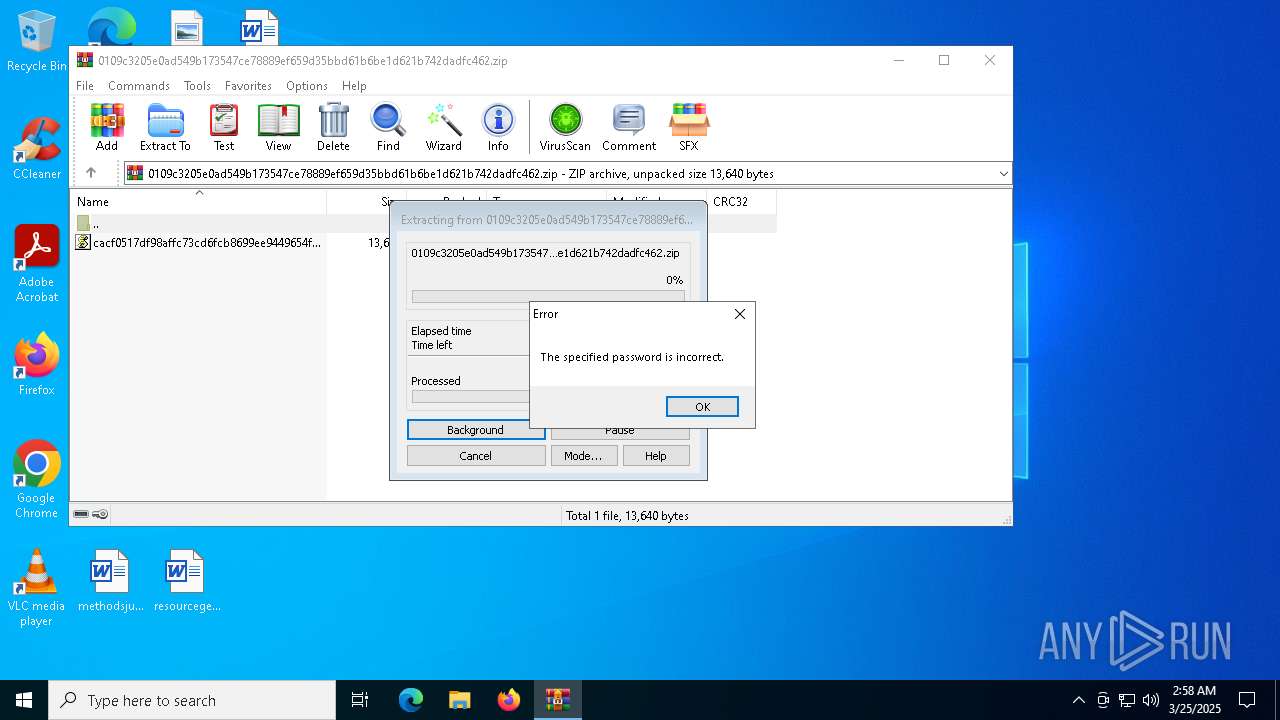
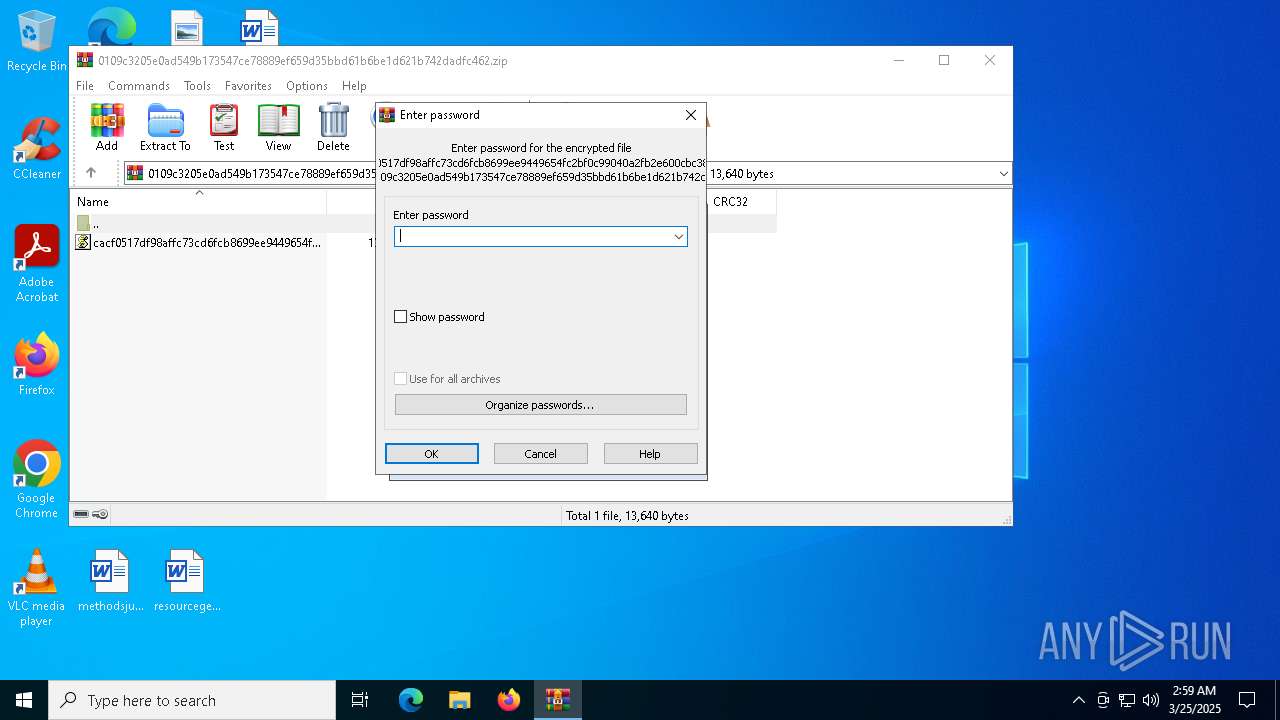
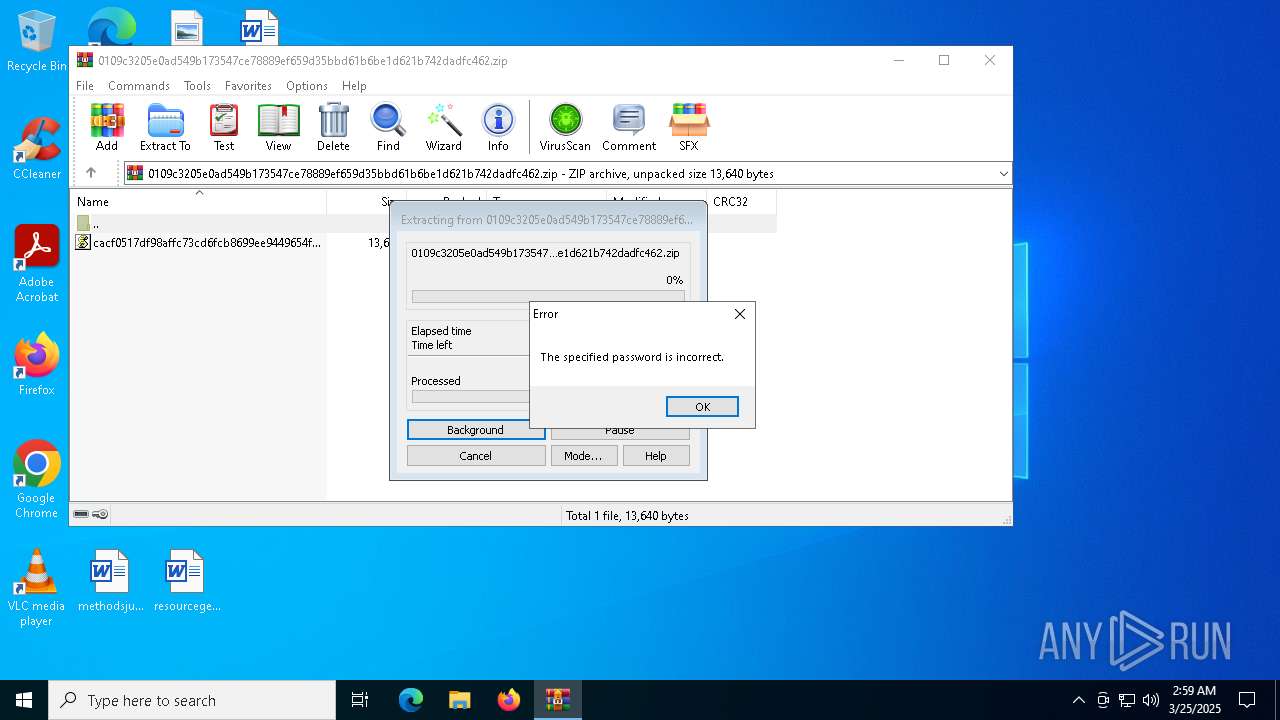
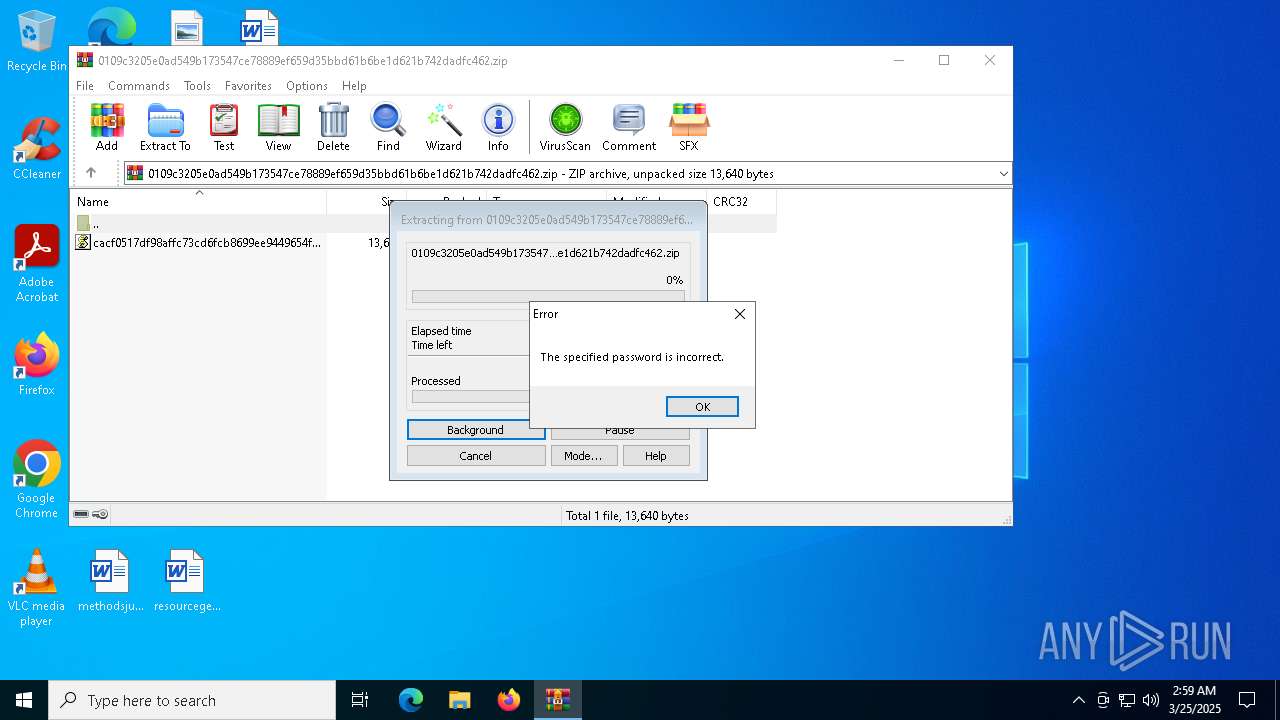
| File name: | 0109c3205e0ad549b173547ce78889ef659d35bbd61b6be1d621b742dadfc462.zip |
| Full analysis: | https://app.any.run/tasks/1a5a96f2-3a38-4fb1-b8be-1e542b026573 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 02:56:49 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| MIME: | application/zip |
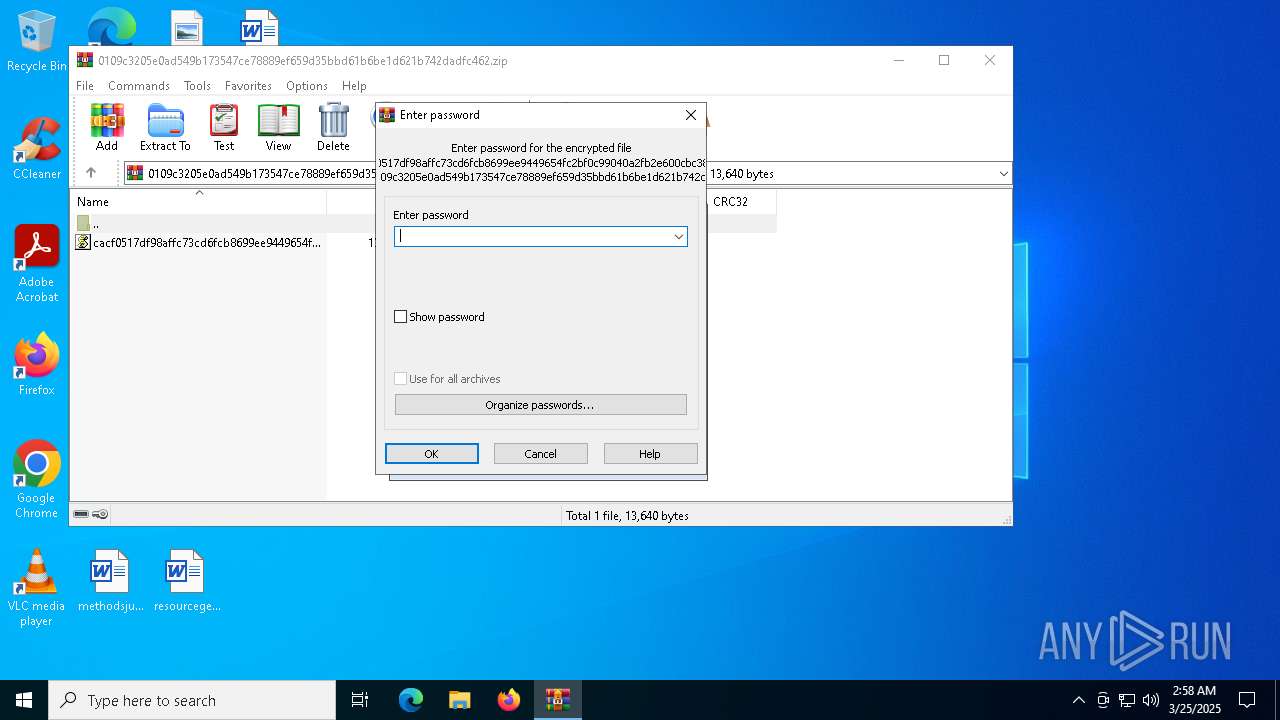
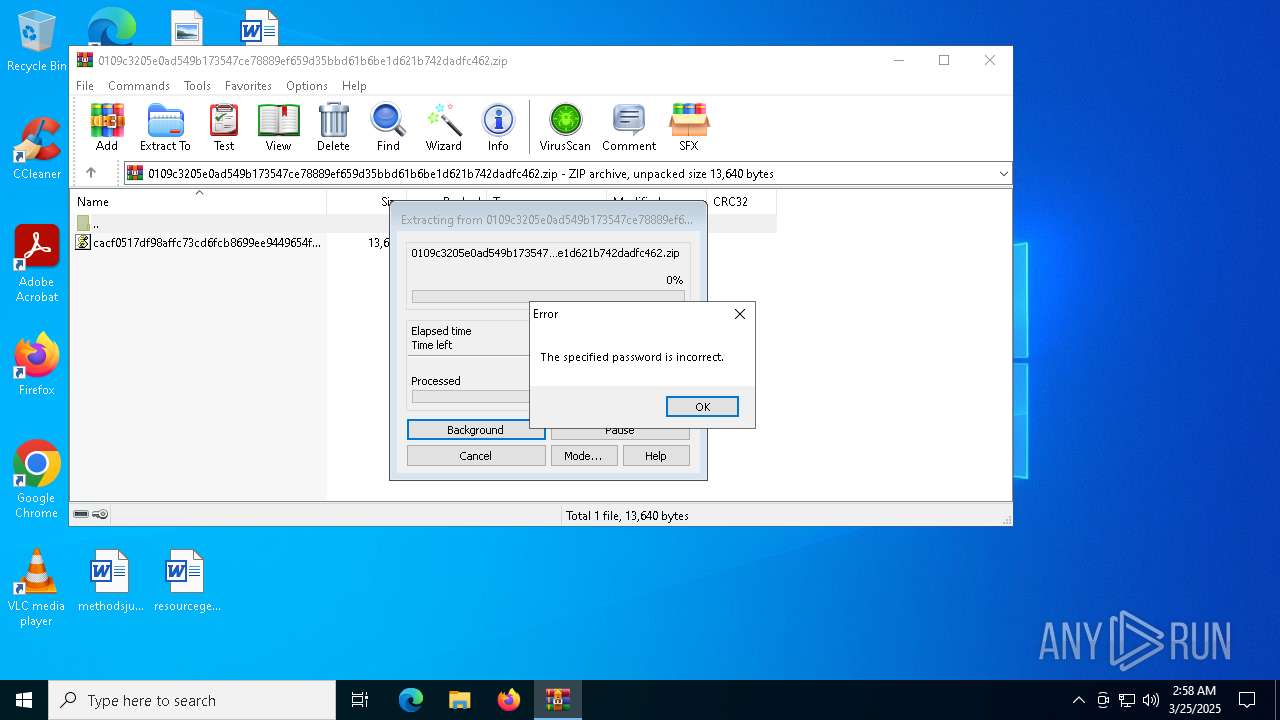
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 76D90B5E5AE45A77D2226BA3201EF2AA |
| SHA1: | 6D41F43C1AF30CD297E80F08115FC435E09731DF |
| SHA256: | 0109C3205E0AD549B173547CE78889EF659D35BBD61B6BE1D621B742DADFC462 |
| SSDEEP: | 96:sGHns1Mxro33+Y0SSPpGJMtxzlKyvSs/6dhqTvyaV7zBYPe36q0MjlAE:o33OSSPpGiT3sqTvHlMevx |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7800)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 7932)
Gets username (SCRIPT)
- wscript.exe (PID: 7932)
Uses base64 encoding (SCRIPT)
- wscript.exe (PID: 7932)
Gets %windir% folder path (SCRIPT)
- wscript.exe (PID: 7932)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 7932)
Reads the value of a key from the registry (SCRIPT)
- wscript.exe (PID: 7932)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 7932)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 7932)
Accesses information about the status of the installed antivirus(Win32_AntivirusProduct) via WMI (SCRIPT)
- wscript.exe (PID: 7932)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 7932)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 7932)
SUSPICIOUS
Changes charset (SCRIPT)
- wscript.exe (PID: 7932)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 7932)
Script creates XML DOM node (SCRIPT)
- wscript.exe (PID: 7932)
Gets computer name (SCRIPT)
- wscript.exe (PID: 7932)
Gets name of the script (SCRIPT)
- wscript.exe (PID: 7932)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 7932)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 7932)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 7932)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7932)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 7932)
Creates XML DOM element (SCRIPT)
- wscript.exe (PID: 7932)
Reads data from a binary Stream object (SCRIPT)
- wscript.exe (PID: 7932)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 7932)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 7932)
Accesses WMI object caption (SCRIPT)
- wscript.exe (PID: 7932)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 7932)
Accesses antivirus product name via WMI (SCRIPT)
- wscript.exe (PID: 7932)
Accesses WMI object display name (SCRIPT)
- wscript.exe (PID: 7932)
Connects to unusual port
- wscript.exe (PID: 7932)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 7932)
Accesses operating system name via WMI (SCRIPT)
- wscript.exe (PID: 7932)
INFO
Manual execution by a user
- wscript.exe (PID: 7932)
Checks proxy server information
- wscript.exe (PID: 7932)
- slui.exe (PID: 7344)
Reads the software policy settings
- slui.exe (PID: 7344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:12:04 09:59:52 |
| ZipCRC: | 0x57120813 |
| ZipCompressedSize: | 4146 |
| ZipUncompressedSize: | 13640 |
| ZipFileName: | cacf0517df98affc73cd6fcb8699ee9449654fc2bf0c99040a2fb2e600cbc380.js |
Total processes
126
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7344 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7800 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\0109c3205e0ad549b173547ce78889ef659d35bbd61b6be1d621b742dadfc462.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7932 | "C:\Windows\System32\WScript.exe" C:\Users\admin\Desktop\cacf0517df98affc73cd6fcb8699ee9449654fc2bf0c99040a2fb2e600cbc380.js | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
5 776
Read events
5 761
Write events
15
Delete events
0
Modification events
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\0109c3205e0ad549b173547ce78889ef659d35bbd61b6be1d621b742dadfc462.zip | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
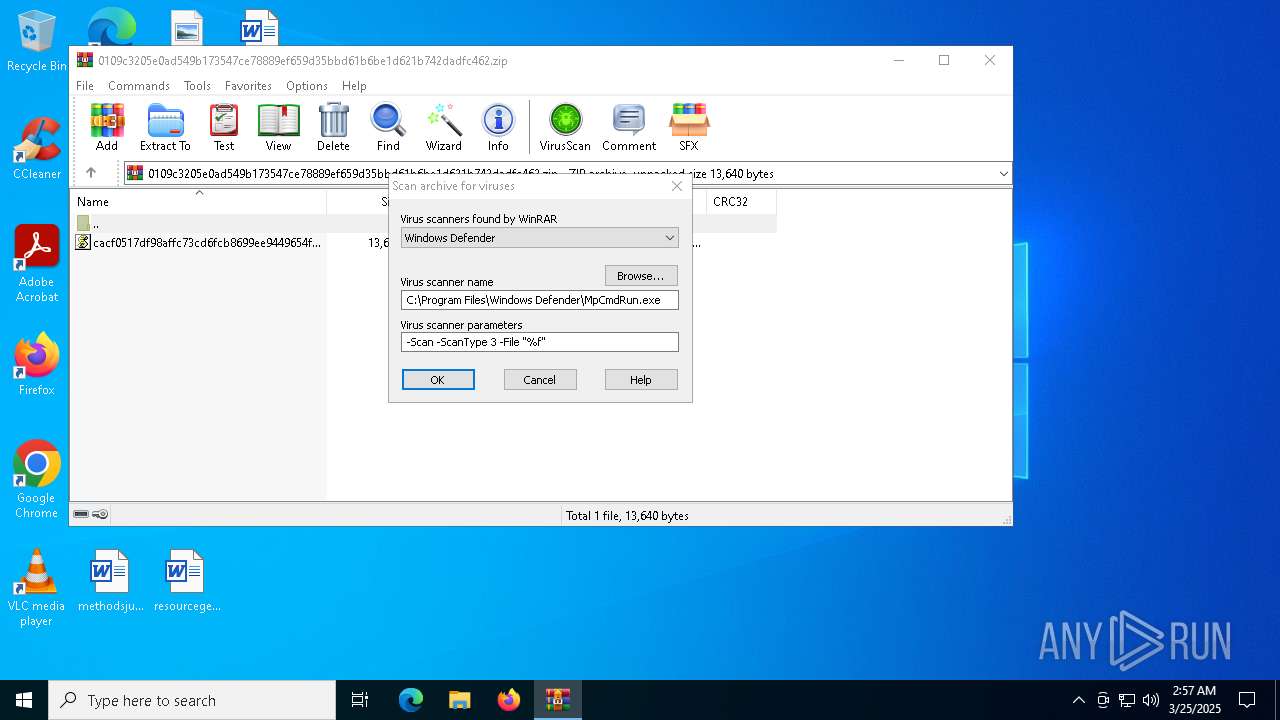
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
23
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7932 | wscript.exe | POST | — | 185.250.240.7:2121 | http://185.250.240.7:2121/Vre | unknown | — | — | unknown |
2104 | svchost.exe | GET | 200 | 88.221.110.122:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7932 | wscript.exe | POST | — | 185.250.240.7:2121 | http://185.250.240.7:2121/Vre | unknown | — | — | unknown |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 88.221.110.122:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7932 | wscript.exe | 185.250.240.7:2121 | — | Sistemdc webhosting and server services | TR | unknown |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7568 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7344 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |