| File name: | dotnet-runtime-6.0.29-win-x64.exe |
| Full analysis: | https://app.any.run/tasks/893aa711-c52f-4c7e-9bb2-a5ceb97e7f8a |
| Verdict: | Malicious activity |
| Analysis date: | August 15, 2024, 02:29:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 91E79AF43355CBBED8892891BA7EB3AC |
| SHA1: | EC21493B6E96BBCEA54FB2568A93EC7F1A52EADD |
| SHA256: | 0102C4018456F4A6BC5FE427C883F7FEF8441AF6BDA9D0260E5BD144786A1170 |
| SSDEEP: | 24576:T+nqjgMAK2LBwVi6R39RdH9VX5bHoailFnyrSOQ9:T+nqjgMAK2LBwVi6R39PH9VXBHoagZyA |
MALICIOUS
Changes the autorun value in the registry
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6328)
SUSPICIOUS
Drops the executable file immediately after the start
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6420)
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6444)
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6328)
Process drops legitimate windows executable
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6420)
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6328)
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6444)
Starts itself from another location
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6444)
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6420)
Starts a Microsoft application from unusual location
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6420)
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6444)
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6328)
Executable content was dropped or overwritten
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6420)
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6444)
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6328)
Reads the date of Windows installation
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6444)
Searches for installed software
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6328)
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6444)
Creates a software uninstall entry
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6328)
Reads security settings of Internet Explorer
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6444)
INFO
Checks supported languages
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6328)
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6420)
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6444)
Create files in a temporary directory
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6420)
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6444)
Reads the computer name
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6444)
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6328)
Process checks computer location settings
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6444)
Creates files in the program directory
- dotnet-runtime-6.0.29-win-x64.exe (PID: 6328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:22 15:58:18+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 302080 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e082 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.29.33521 |
| ProductVersionNumber: | 6.0.29.33521 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
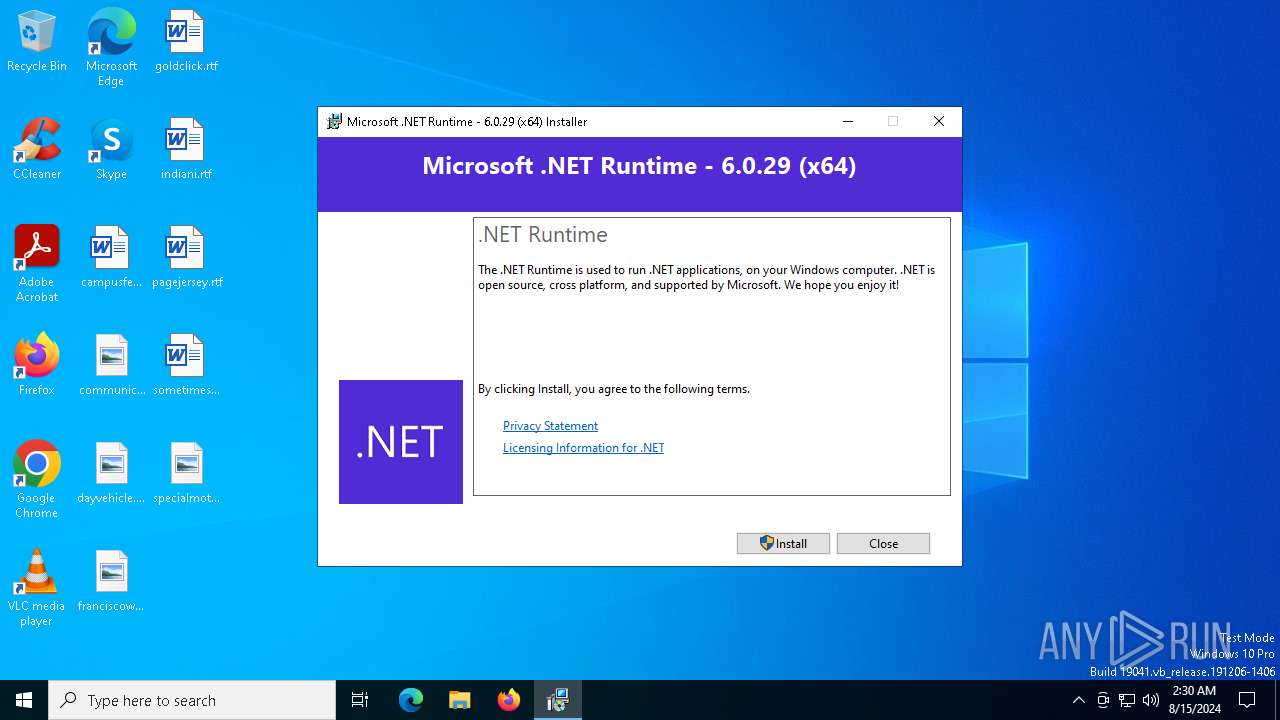
| FileDescription: | Microsoft .NET Runtime - 6.0.29 (x64) |
| FileVersion: | 6.0.29.33521 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFileName: | dotnet-runtime-6.0.29-win-x64.exe |
| ProductName: | Microsoft .NET Runtime - 6.0.29 (x64) |
| ProductVersion: | 6.0.29.33521 |
Total processes
134
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6328 | "C:\Users\admin\AppData\Local\Temp\{22741D11-2CBD-4476-AB22-A344F4681F0C}\.be\dotnet-runtime-6.0.29-win-x64.exe" -q -burn.elevated BurnPipe.{D4E8DA73-BF13-44BB-B8C4-050E36CEF0B1} {93BBE9EA-4CF6-42F2-9133-6518506EB6F2} 6444 | C:\Users\admin\AppData\Local\Temp\{22741D11-2CBD-4476-AB22-A344F4681F0C}\.be\dotnet-runtime-6.0.29-win-x64.exe | dotnet-runtime-6.0.29-win-x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Runtime - 6.0.29 (x64) Exit code: 1 Version: 6.0.29.33521 Modules
| |||||||||||||||
| 6420 | "C:\Users\admin\AppData\Local\Temp\dotnet-runtime-6.0.29-win-x64.exe" | C:\Users\admin\AppData\Local\Temp\dotnet-runtime-6.0.29-win-x64.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Runtime - 6.0.29 (x64) Exit code: 1 Version: 6.0.29.33521 Modules
| |||||||||||||||
| 6444 | "C:\Users\admin\AppData\Local\Temp\{865B44ED-3A7D-45CC-90C8-9B6D13CD7319}\.cr\dotnet-runtime-6.0.29-win-x64.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\dotnet-runtime-6.0.29-win-x64.exe" -burn.filehandle.attached=580 -burn.filehandle.self=696 | C:\Users\admin\AppData\Local\Temp\{865B44ED-3A7D-45CC-90C8-9B6D13CD7319}\.cr\dotnet-runtime-6.0.29-win-x64.exe | dotnet-runtime-6.0.29-win-x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Runtime - 6.0.29 (x64) Exit code: 1 Version: 6.0.29.33521 Modules
| |||||||||||||||
Total events
4 072
Read events
4 031
Write events
34
Delete events
7
Modification events
| (PID) Process: | (6444) dotnet-runtime-6.0.29-win-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6444) dotnet-runtime-6.0.29-win-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6444) dotnet-runtime-6.0.29-win-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6444) dotnet-runtime-6.0.29-win-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6328) dotnet-runtime-6.0.29-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{d052745b-efe5-4690-886d-1d425a24a8a3} |
| Operation: | write | Name: | BundleCachePath |
Value: C:\ProgramData\Package Cache\{d052745b-efe5-4690-886d-1d425a24a8a3}\dotnet-runtime-6.0.29-win-x64.exe | |||
| (PID) Process: | (6328) dotnet-runtime-6.0.29-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{d052745b-efe5-4690-886d-1d425a24a8a3} |
| Operation: | write | Name: | BundleUpgradeCode |
Value: {B19A028F-5C89-7AF4-5102-0F8ED67CCACA} | |||
| (PID) Process: | (6328) dotnet-runtime-6.0.29-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{d052745b-efe5-4690-886d-1d425a24a8a3} |
| Operation: | write | Name: | BundleAddonCode |
Value: | |||
| (PID) Process: | (6328) dotnet-runtime-6.0.29-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{d052745b-efe5-4690-886d-1d425a24a8a3} |
| Operation: | write | Name: | BundleDetectCode |
Value: | |||
| (PID) Process: | (6328) dotnet-runtime-6.0.29-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{d052745b-efe5-4690-886d-1d425a24a8a3} |
| Operation: | write | Name: | BundlePatchCode |
Value: | |||
| (PID) Process: | (6328) dotnet-runtime-6.0.29-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{d052745b-efe5-4690-886d-1d425a24a8a3} |
| Operation: | write | Name: | BundleVersion |
Value: 6.0.29.33521 | |||
Executable files
5
Suspicious files
1
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6444 | dotnet-runtime-6.0.29-win-x64.exe | C:\Users\admin\AppData\Local\Temp\{22741D11-2CBD-4476-AB22-A344F4681F0C}\.ba\wixstdba.dll | executable | |
MD5:4356EE50F0B1A878E270614780DDF095 | SHA256:41A8787FDC9467F563438DABA4131191AA1EB588A81BEB9A89FE8BD886C16104 | |||
| 6444 | dotnet-runtime-6.0.29-win-x64.exe | C:\Users\admin\AppData\Local\Temp\{22741D11-2CBD-4476-AB22-A344F4681F0C}\.ba\1028\thm.wxl | xml | |
MD5:518E7650B3AD6218E1CE96E156DF544A | SHA256:50109347FC59574721AA233C5D4C1088DE5D57A89DDCEA02D388C79676D39F16 | |||
| 6444 | dotnet-runtime-6.0.29-win-x64.exe | C:\Users\admin\AppData\Local\Temp\{22741D11-2CBD-4476-AB22-A344F4681F0C}\.ba\thm.wxl | xml | |
MD5:F44C2959EEEFF784D8ACA917A909D906 | SHA256:835AA38B22480E84CCDF9F925EF2CD640E015BC2077674A6313C5175EA3DB5BE | |||
| 6444 | dotnet-runtime-6.0.29-win-x64.exe | C:\Users\admin\AppData\Local\Temp\{22741D11-2CBD-4476-AB22-A344F4681F0C}\.ba\bg.png | image | |
MD5:9EB0320DFBF2BD541E6A55C01DDC9F20 | SHA256:9095BF7B6BAA0107B40A4A6D727215BE077133A190F4CA9BD89A176842141E79 | |||
| 6444 | dotnet-runtime-6.0.29-win-x64.exe | C:\Users\admin\AppData\Local\Temp\{22741D11-2CBD-4476-AB22-A344F4681F0C}\.ba\thm.xml | xml | |
MD5:302563A713B142EE41B59E3EEAC53A90 | SHA256:83CA096F7BA2C83FC3B3AEB697B8139A788FA35EB8632943E26BB9FFF7C78E63 | |||
| 6444 | dotnet-runtime-6.0.29-win-x64.exe | C:\Users\admin\AppData\Local\Temp\{22741D11-2CBD-4476-AB22-A344F4681F0C}\.ba\1033\thm.wxl | xml | |
MD5:F44C2959EEEFF784D8ACA917A909D906 | SHA256:835AA38B22480E84CCDF9F925EF2CD640E015BC2077674A6313C5175EA3DB5BE | |||
| 6444 | dotnet-runtime-6.0.29-win-x64.exe | C:\Users\admin\AppData\Local\Temp\{22741D11-2CBD-4476-AB22-A344F4681F0C}\.ba\1029\thm.wxl | xml | |
MD5:62260E884C9B7CC3F1453B4E059F09D4 | SHA256:1C563D1CDF06DDF607E94489E01B4C70BFF1820A1562E824D6DCEB0456B9124D | |||
| 6444 | dotnet-runtime-6.0.29-win-x64.exe | C:\Users\admin\AppData\Local\Temp\{22741D11-2CBD-4476-AB22-A344F4681F0C}\.ba\1036\thm.wxl | xml | |
MD5:FFB77946C049ECAFE87D57BDA01045D7 | SHA256:A2F0CBA58116B70830372C37DA0B259095D3B730F36E801A5B52B00654322BEE | |||
| 6444 | dotnet-runtime-6.0.29-win-x64.exe | C:\Users\admin\AppData\Local\Temp\{22741D11-2CBD-4476-AB22-A344F4681F0C}\.ba\1041\thm.wxl | xml | |
MD5:8627C1D72F5C99A74FD7EAD45316CECF | SHA256:EF0D093C7BD7213564243B81DA51E146583D3576F3A9F2365B75AB7012E4DA0E | |||
| 6444 | dotnet-runtime-6.0.29-win-x64.exe | C:\Users\admin\AppData\Local\Temp\{22741D11-2CBD-4476-AB22-A344F4681F0C}\.ba\1040\thm.wxl | xml | |
MD5:7C3142782A0EB8F5589FF31717DA1947 | SHA256:B5364CF42473D7453BA71C640018CA948D4B9A6B327BE588C52F0BD791ED348E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
41
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4316 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6520 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6532 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6560 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4708 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5336 | SearchApp.exe | 2.23.209.182:443 | www.bing.com | Akamai International B.V. | GB | unknown |
4316 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4316 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |