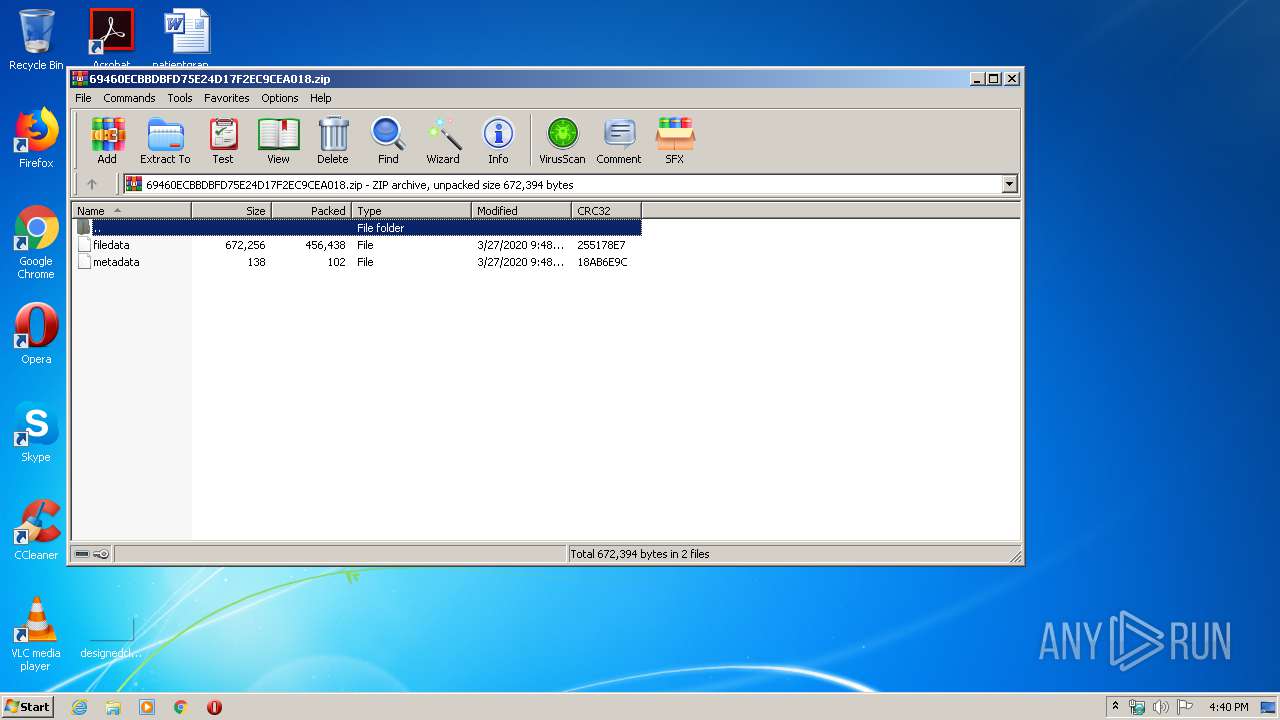
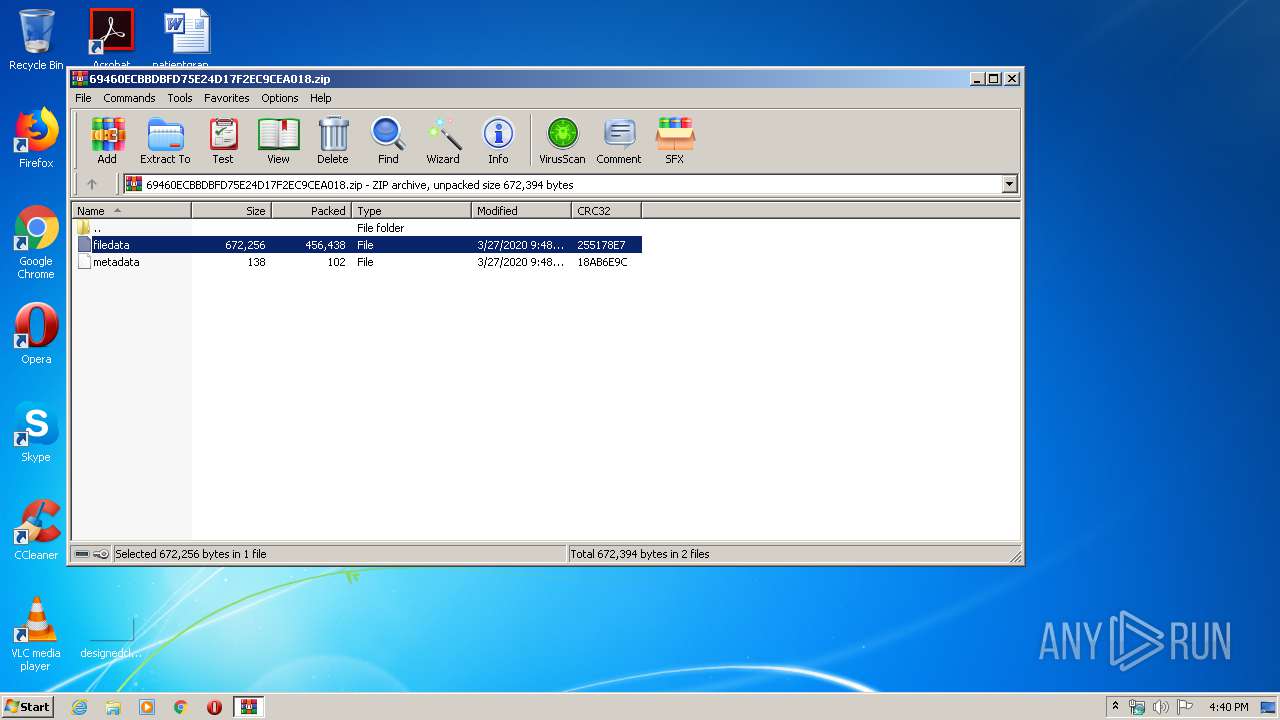
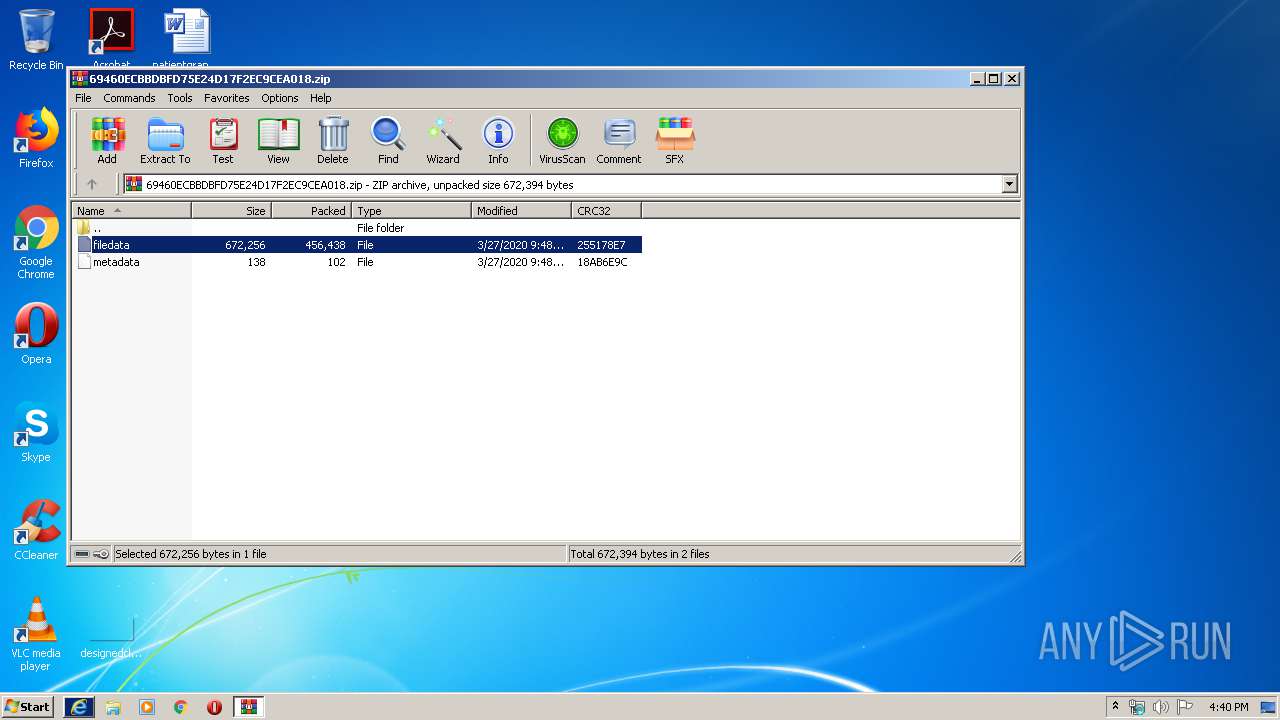
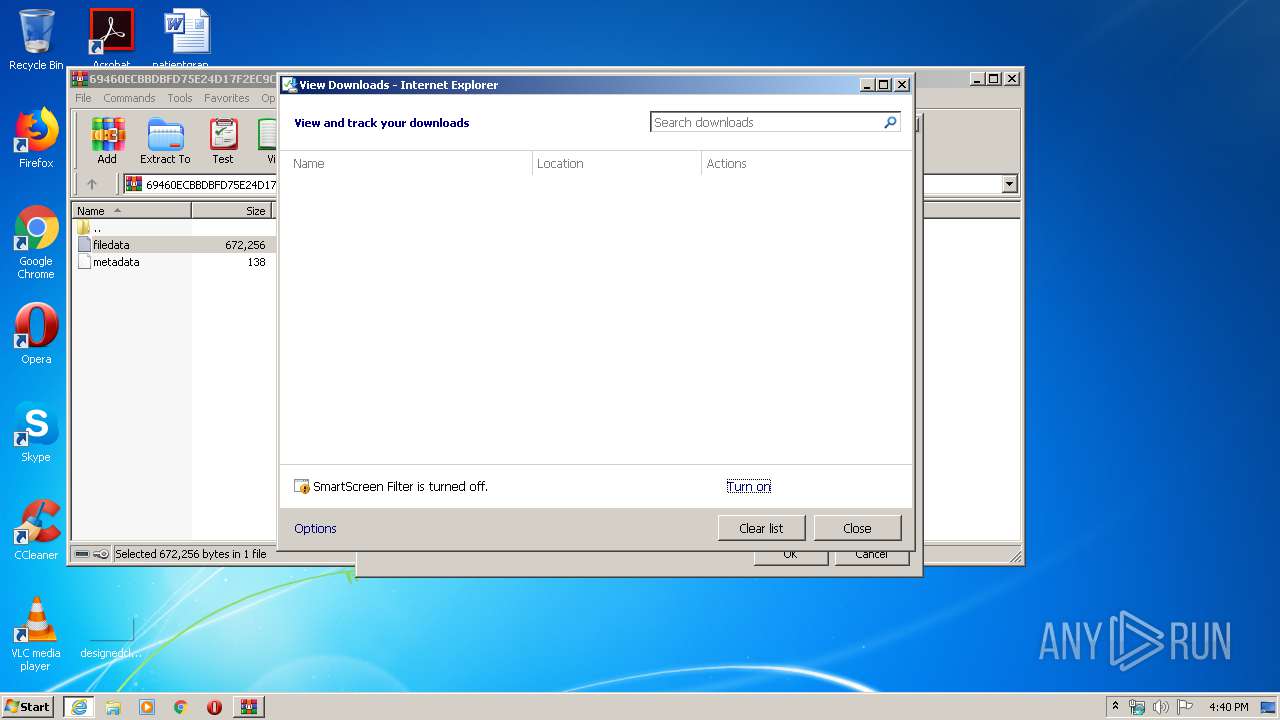
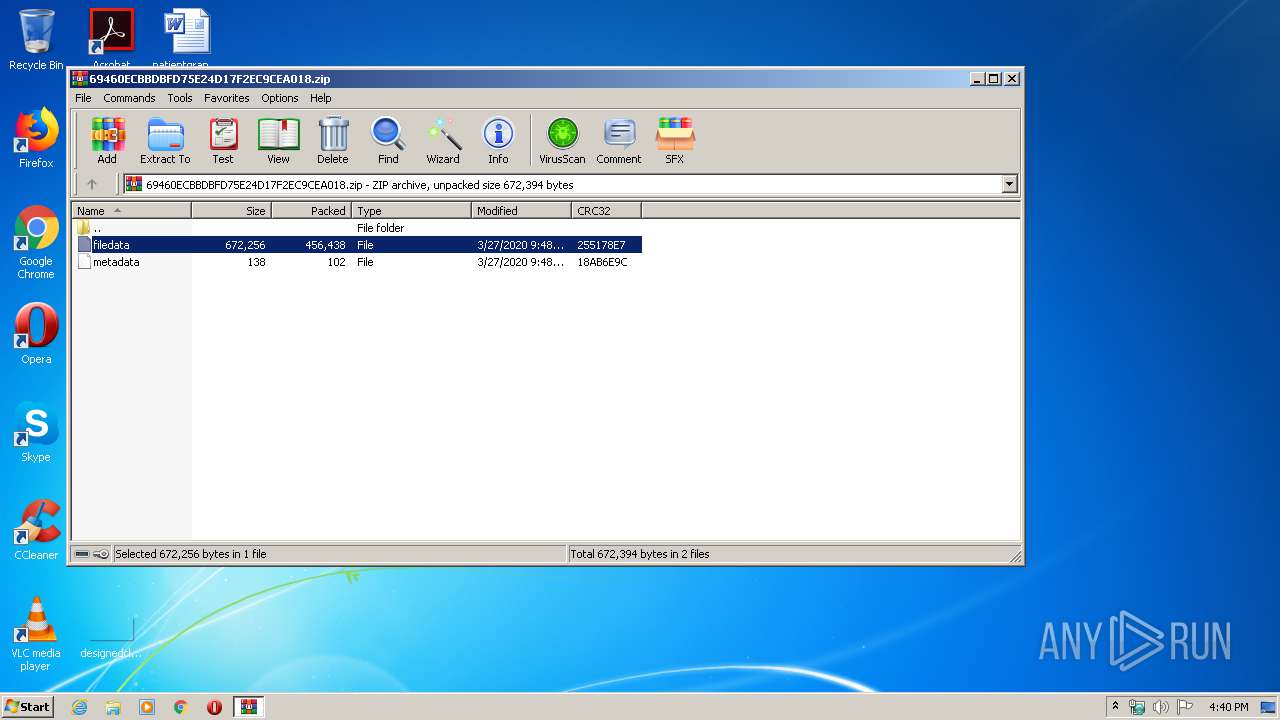
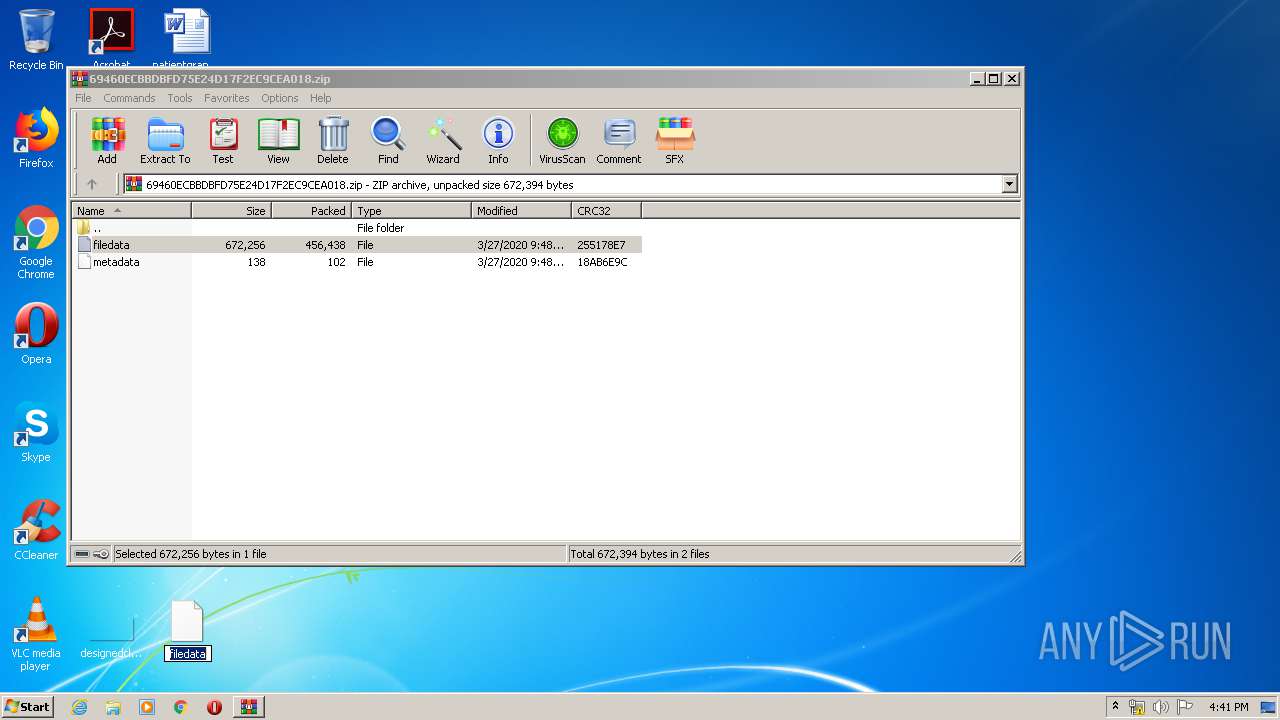
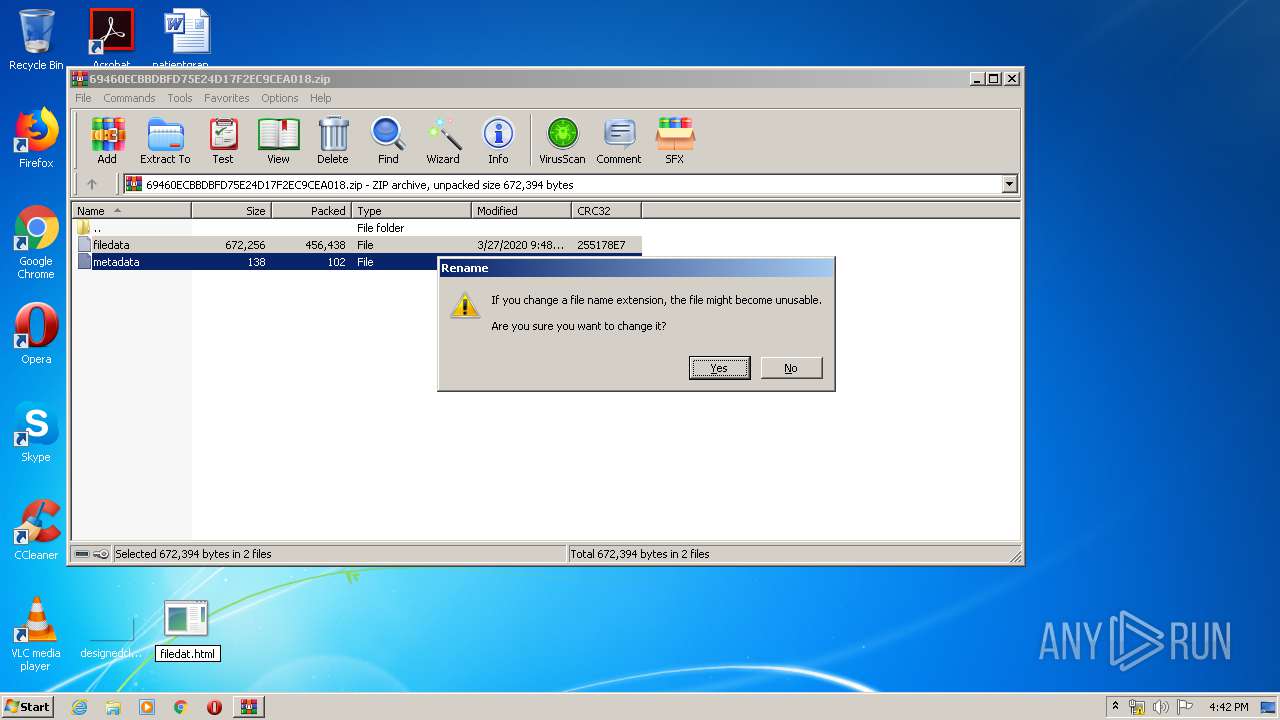
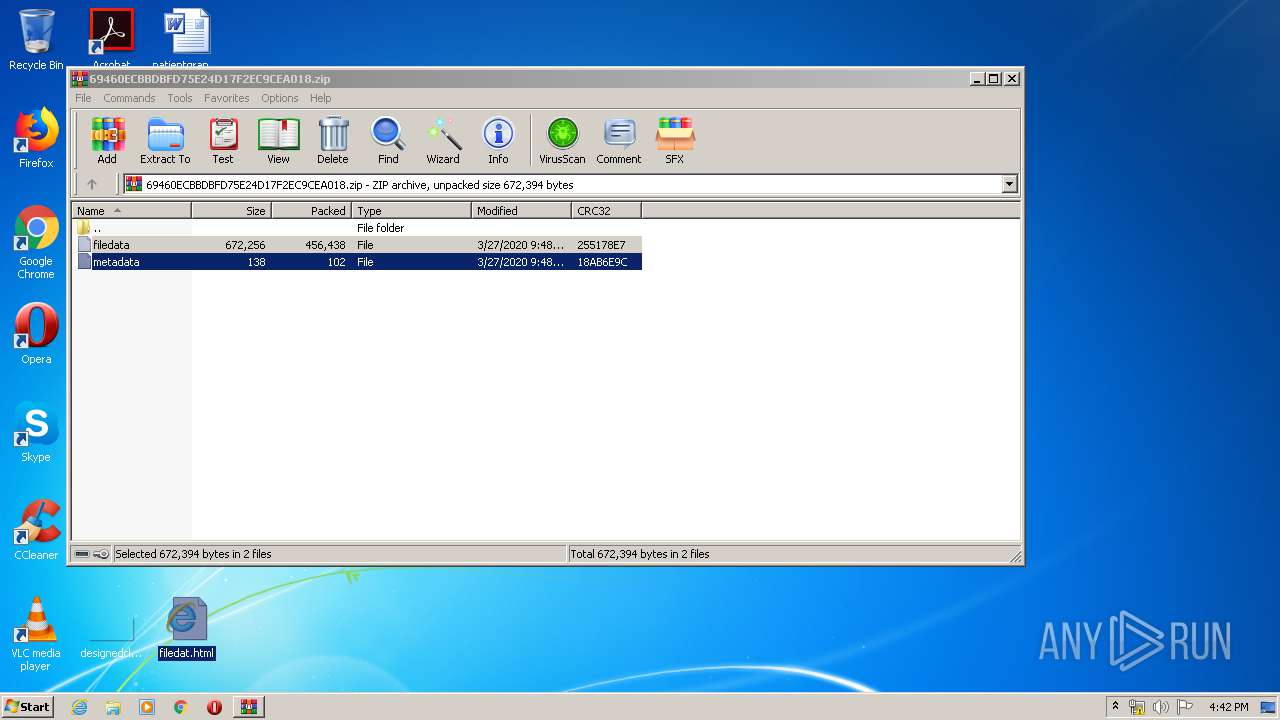
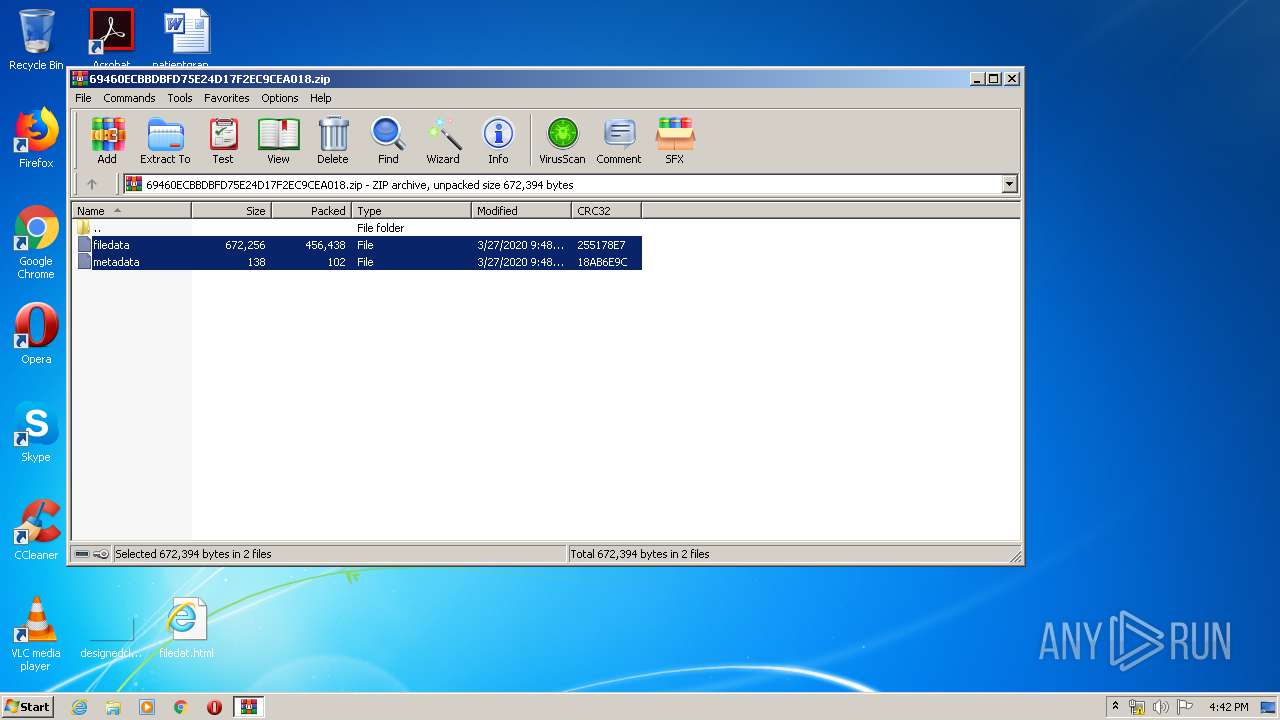
| File name: | 69460ECBBDBFD75E24D17F2EC9CEA018.zip |
| Full analysis: | https://app.any.run/tasks/7458e1c4-1bea-495e-902f-53b72e507586 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 15:39:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 28AEEC0ECE912604640B565B3516425D |
| SHA1: | 80BF49485E4BDFFF9759A361A87585F89F1063D9 |
| SHA256: | 010007346778C5FFAFF4B237B641011108717E2A50578C02E8E33DE08C3CB18A |
| SSDEEP: | 12288:bm0K08wzy0GKH+GoMm49svP7AJEGtgMN132Wo7ES+vxx:brVzcw+c6vP7AZOZr+vxx |
MALICIOUS
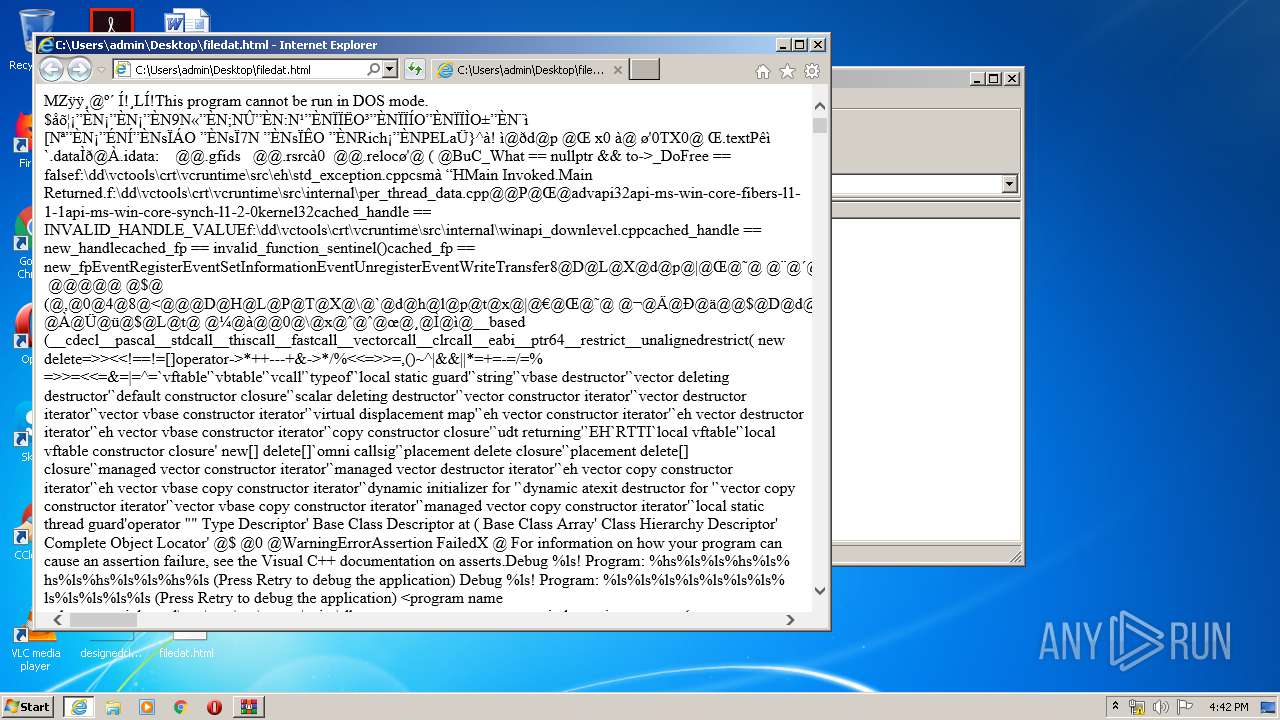
Loads dropped or rewritten executable
- svchost.exe (PID: 860)
- explorer.exe (PID: 372)
- SearchProtocolHost.exe (PID: 3548)
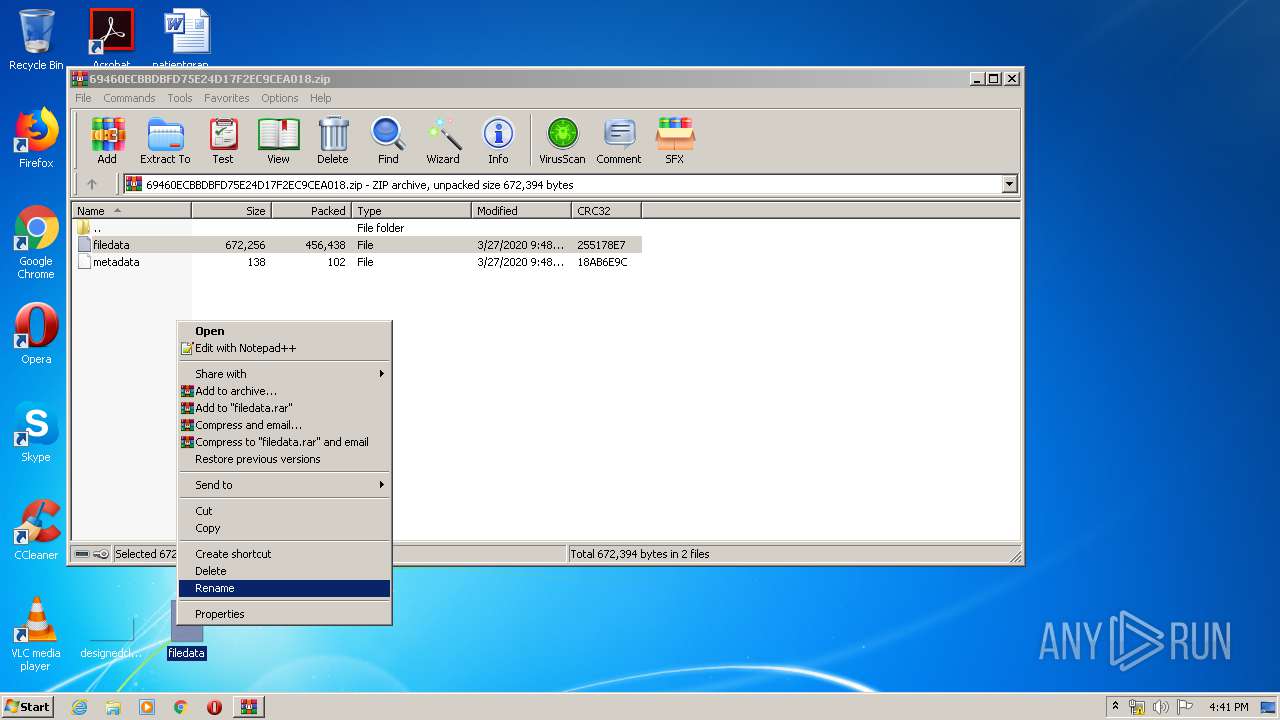
Renames files like Ransomware
- explorer.exe (PID: 372)
SUSPICIOUS
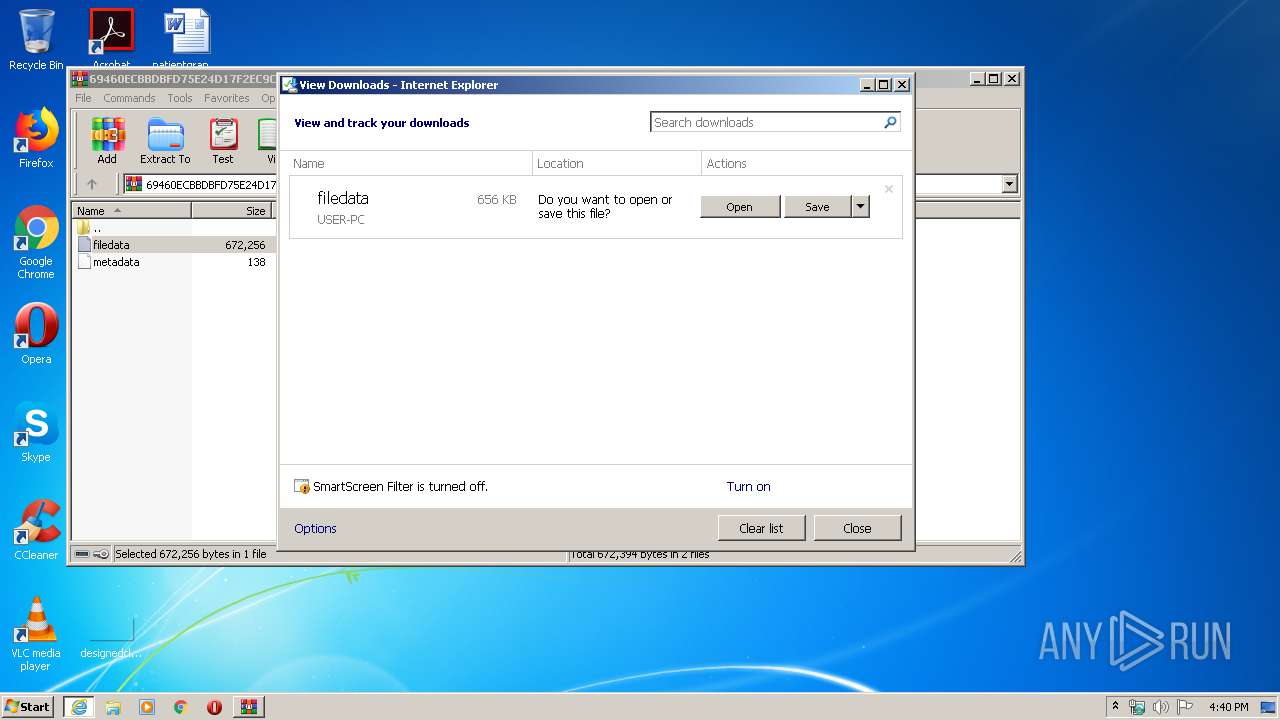
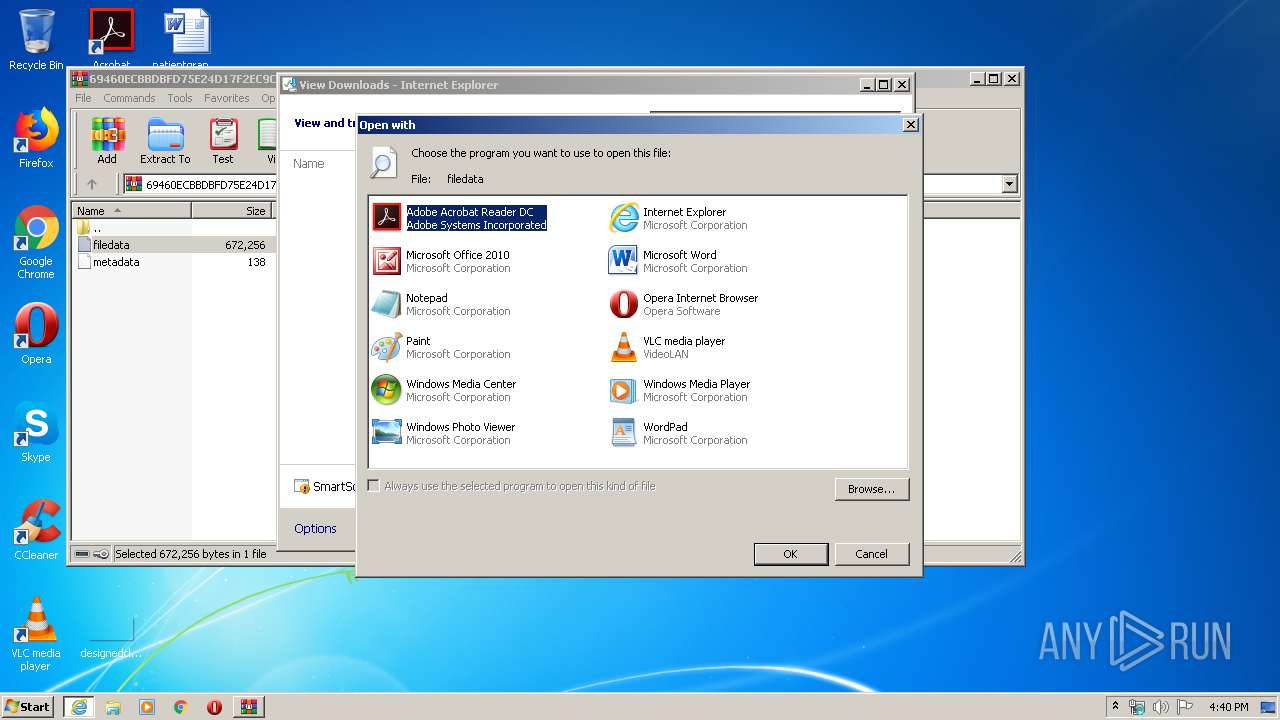
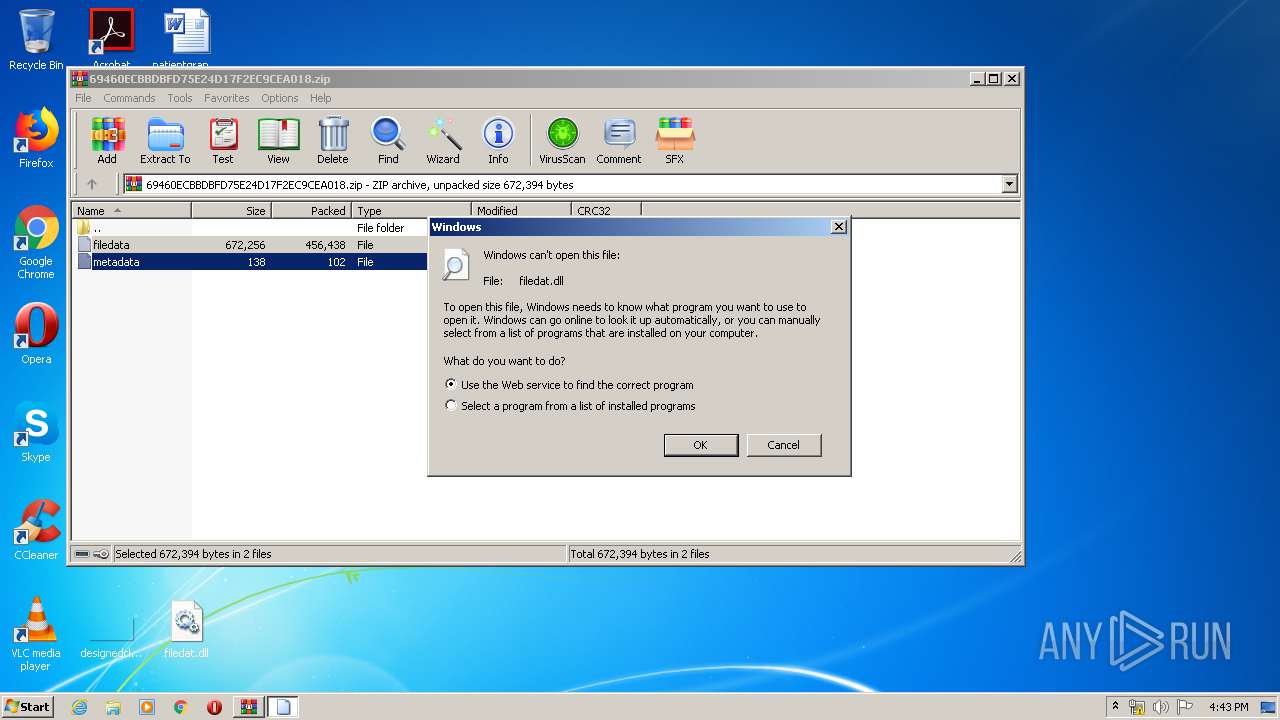
Starts Internet Explorer
- rundll32.exe (PID: 1116)
- explorer.exe (PID: 372)
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 872)
Creates files in the user directory
- explorer.exe (PID: 372)
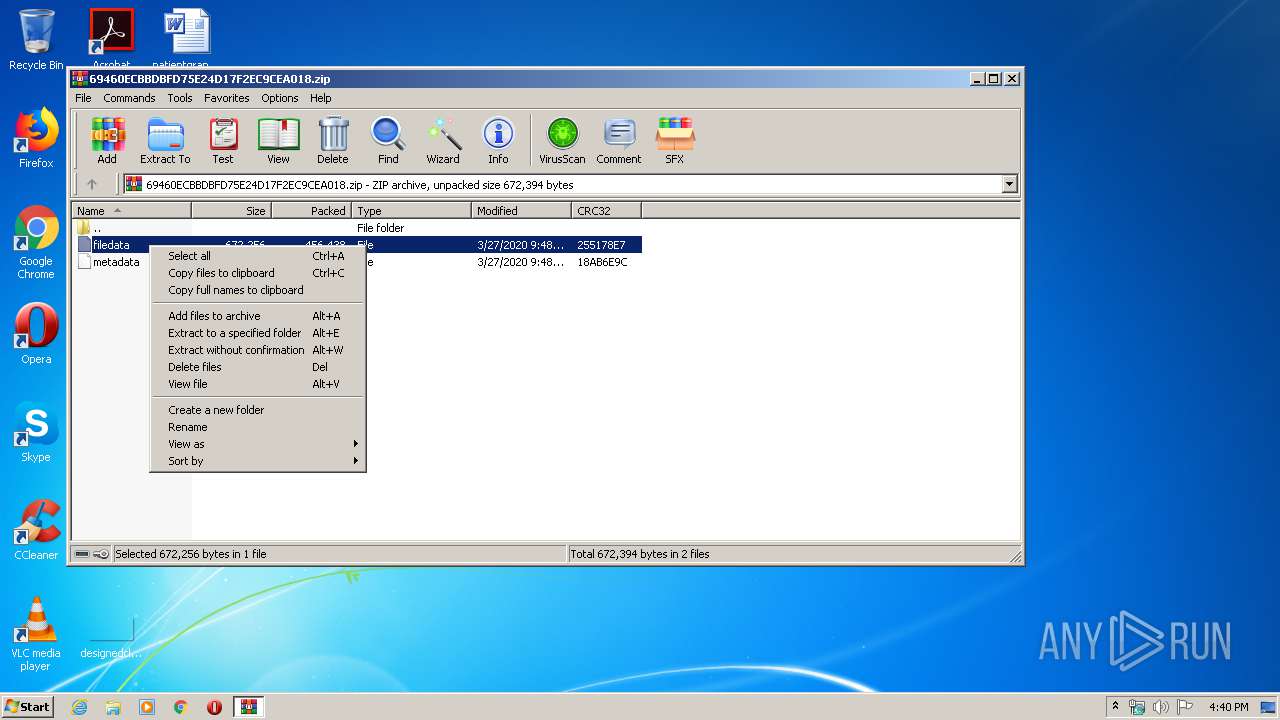
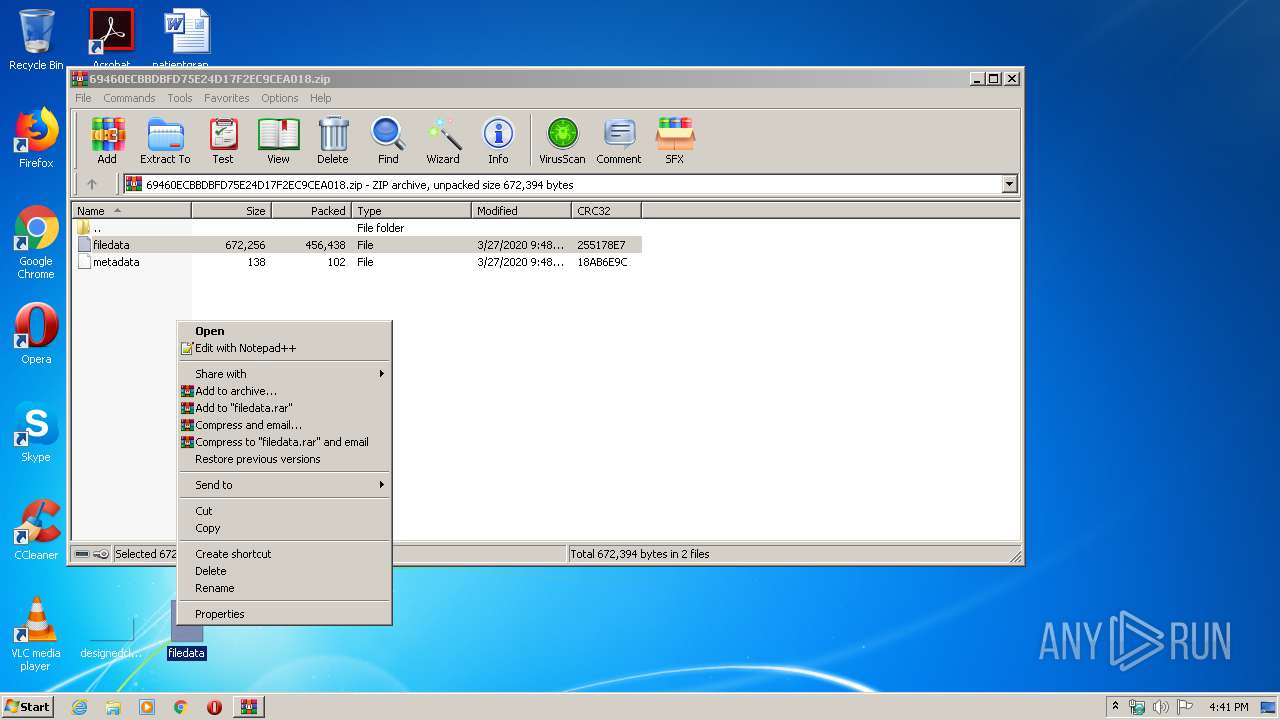
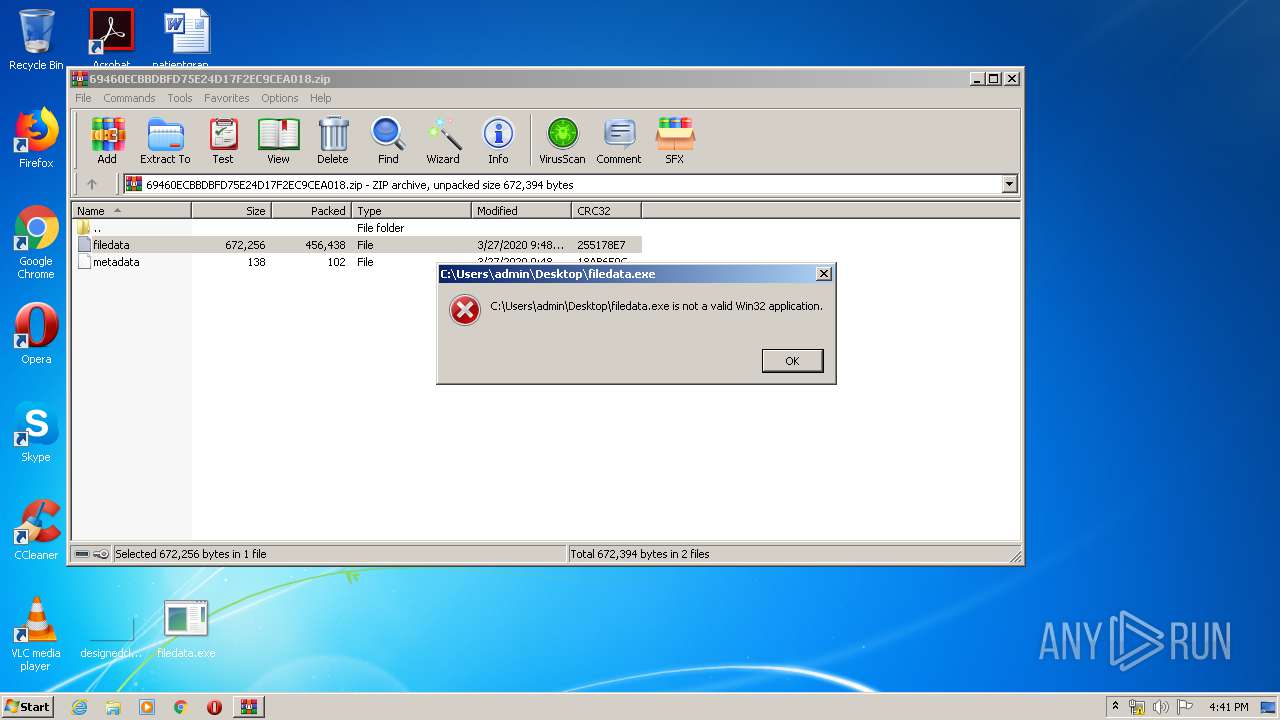
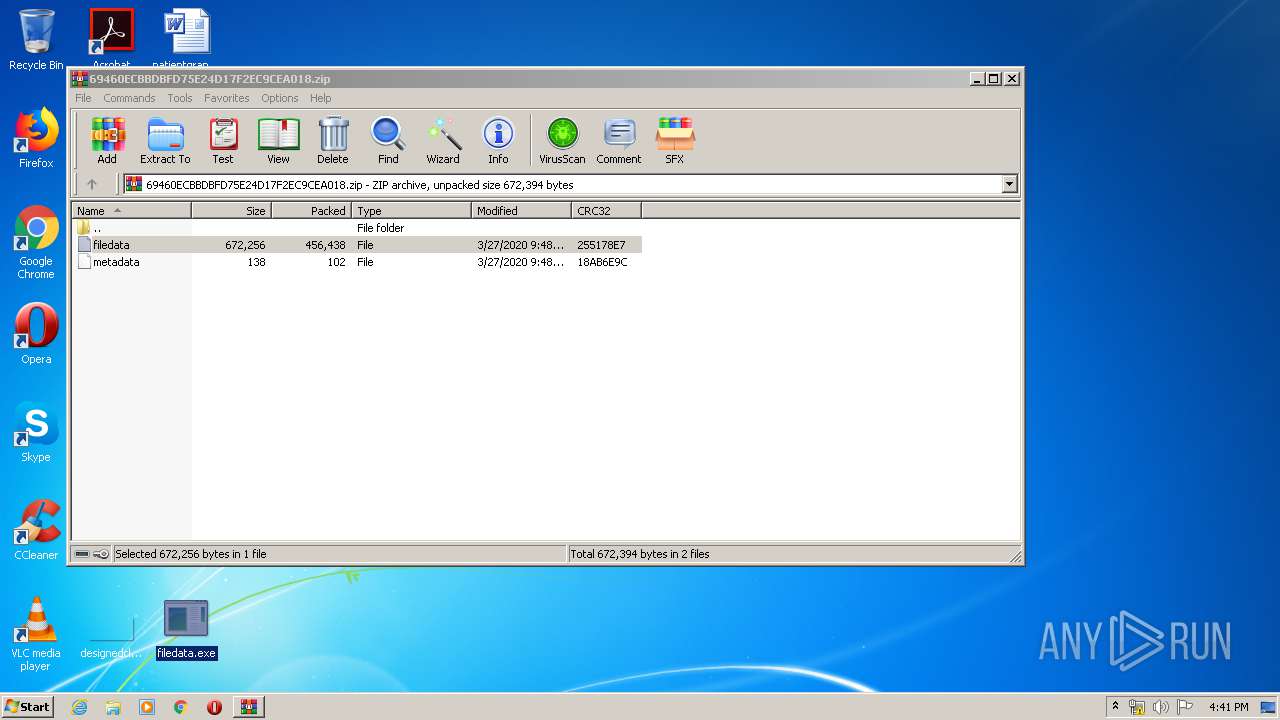
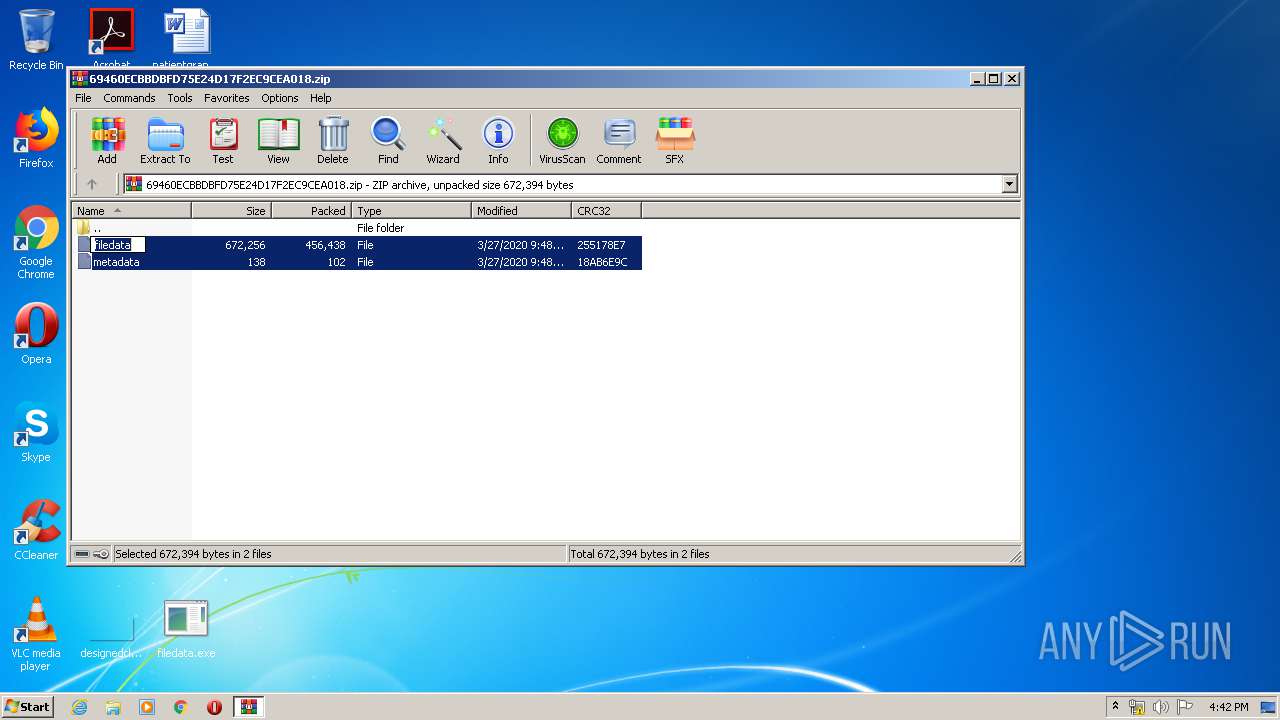
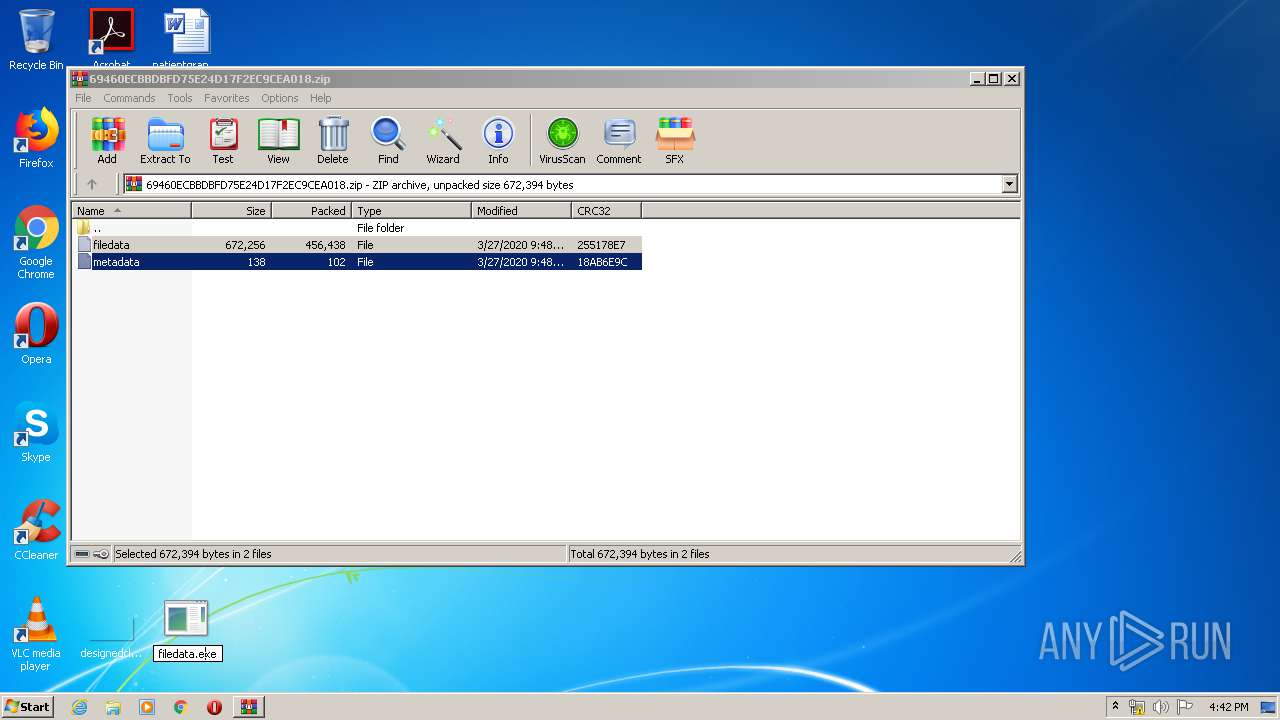
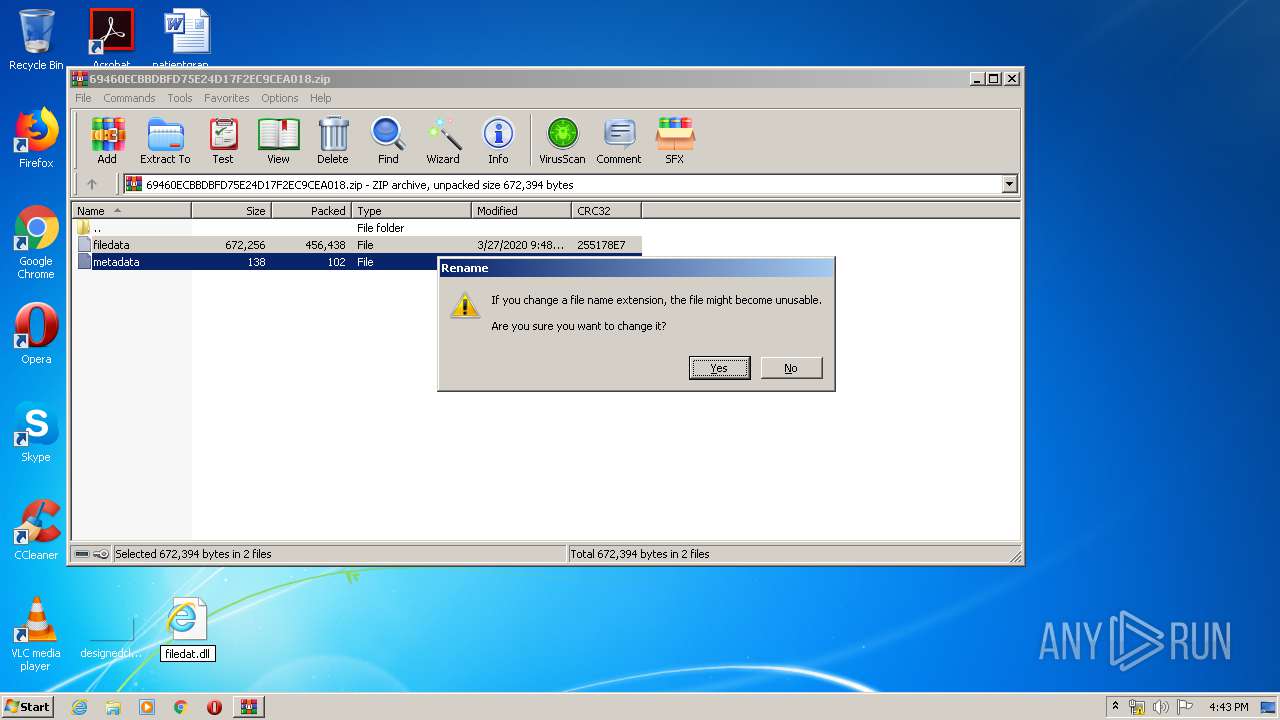
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1456)
- explorer.exe (PID: 372)
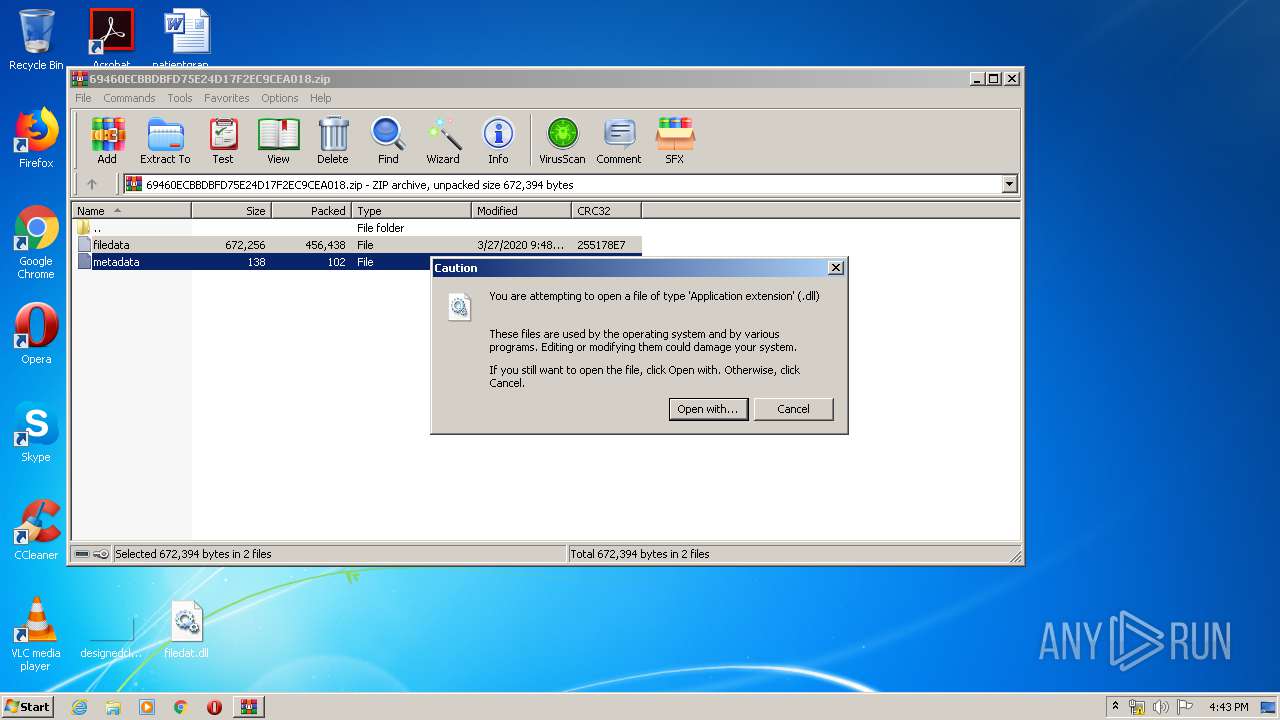
Uses RUNDLL32.EXE to load library
- iexplore.exe (PID: 660)
- WinRAR.exe (PID: 1456)
- explorer.exe (PID: 372)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 660)
- iexplore.exe (PID: 2556)
Application launched itself
- AcroRd32.exe (PID: 872)
- iexplore.exe (PID: 660)
Modifies the phishing filter of IE
- iexplore.exe (PID: 660)
Changes internet zones settings
- iexplore.exe (PID: 660)
- iexplore.exe (PID: 2556)
Reads the hosts file
- RdrCEF.exe (PID: 3488)
Reads internet explorer settings
- iexplore.exe (PID: 2516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:03:27 09:48:04 |
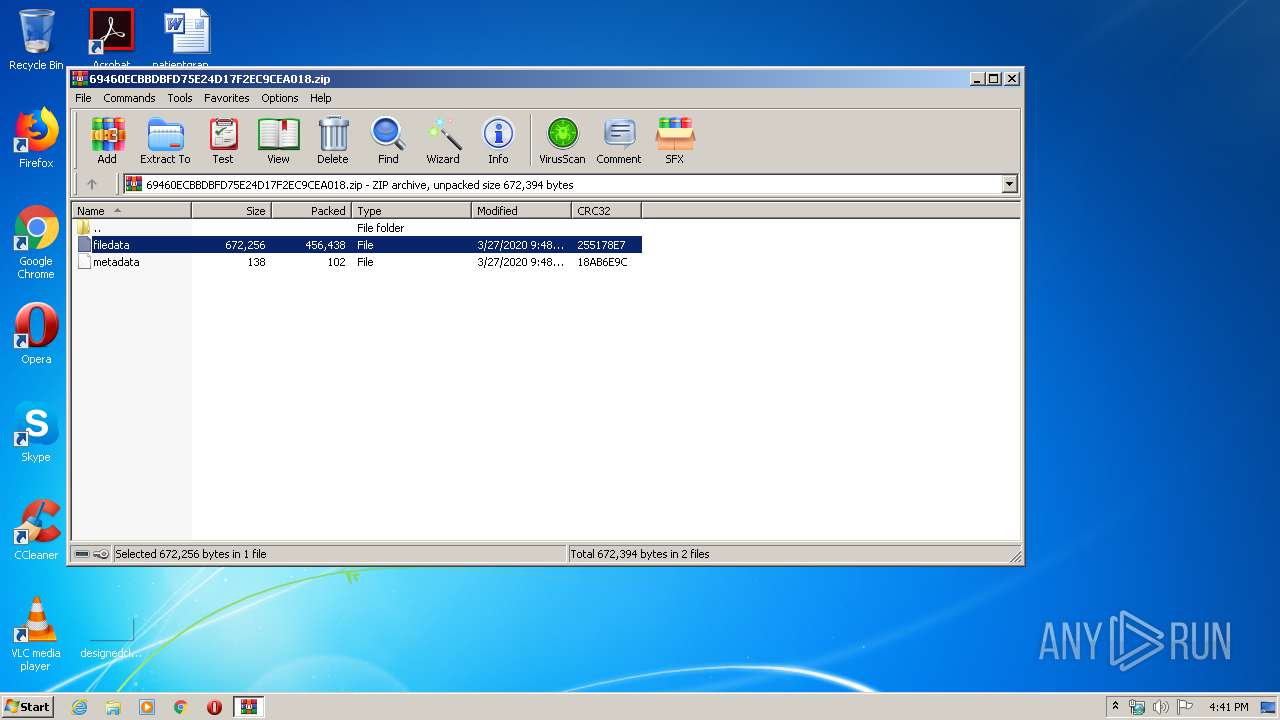
| ZipCRC: | 0x255178e7 |
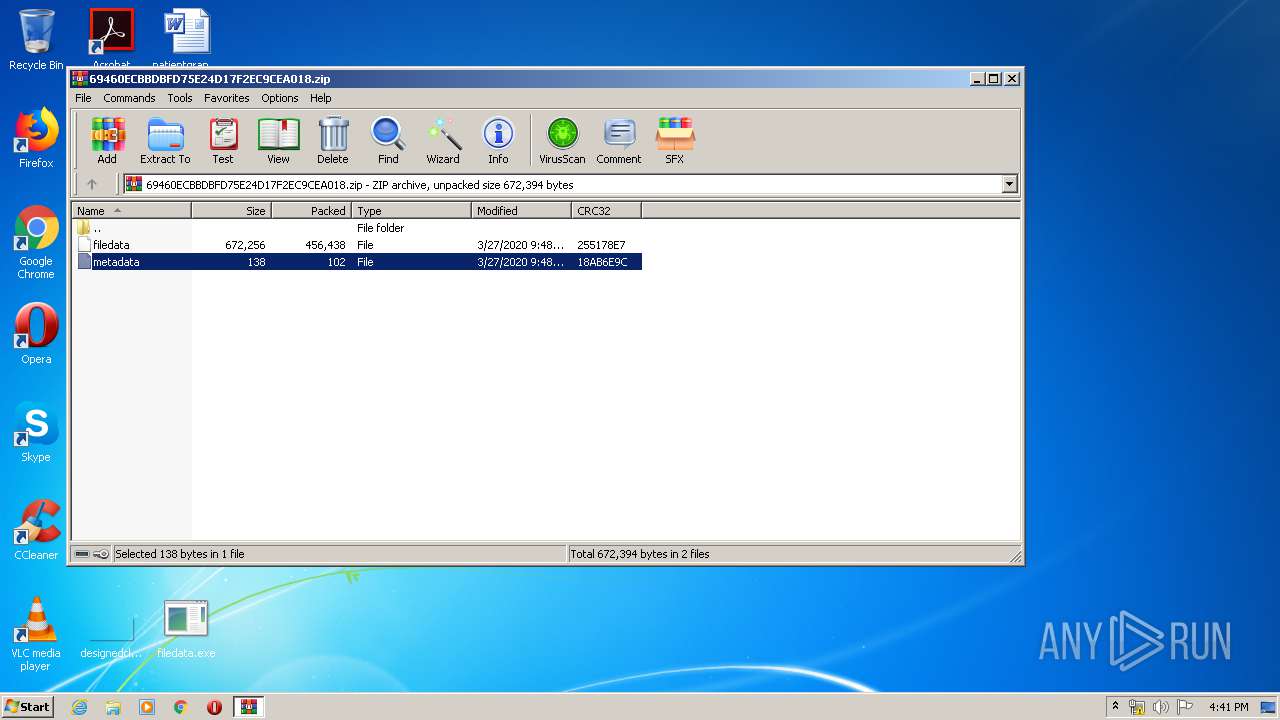
| ZipCompressedSize: | 456438 |
| ZipUncompressedSize: | 672256 |
| ZipFileName: | filedata |
Total processes
55
Monitored processes
16
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
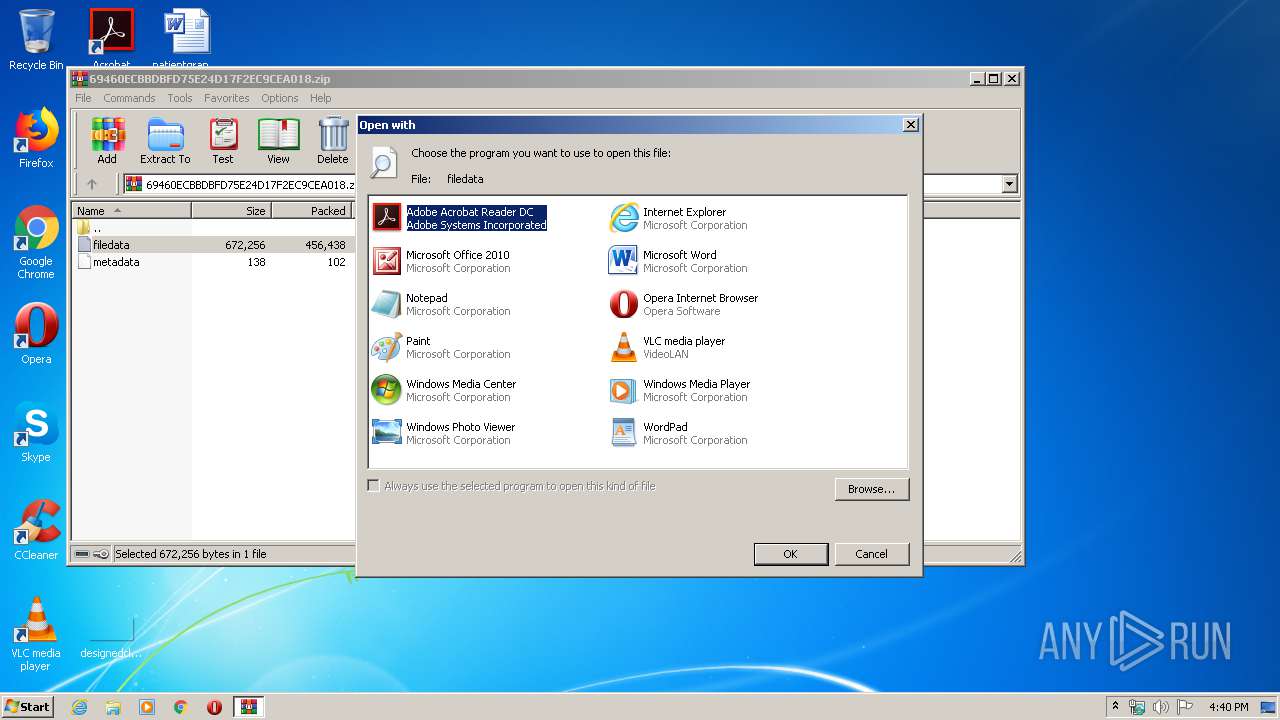
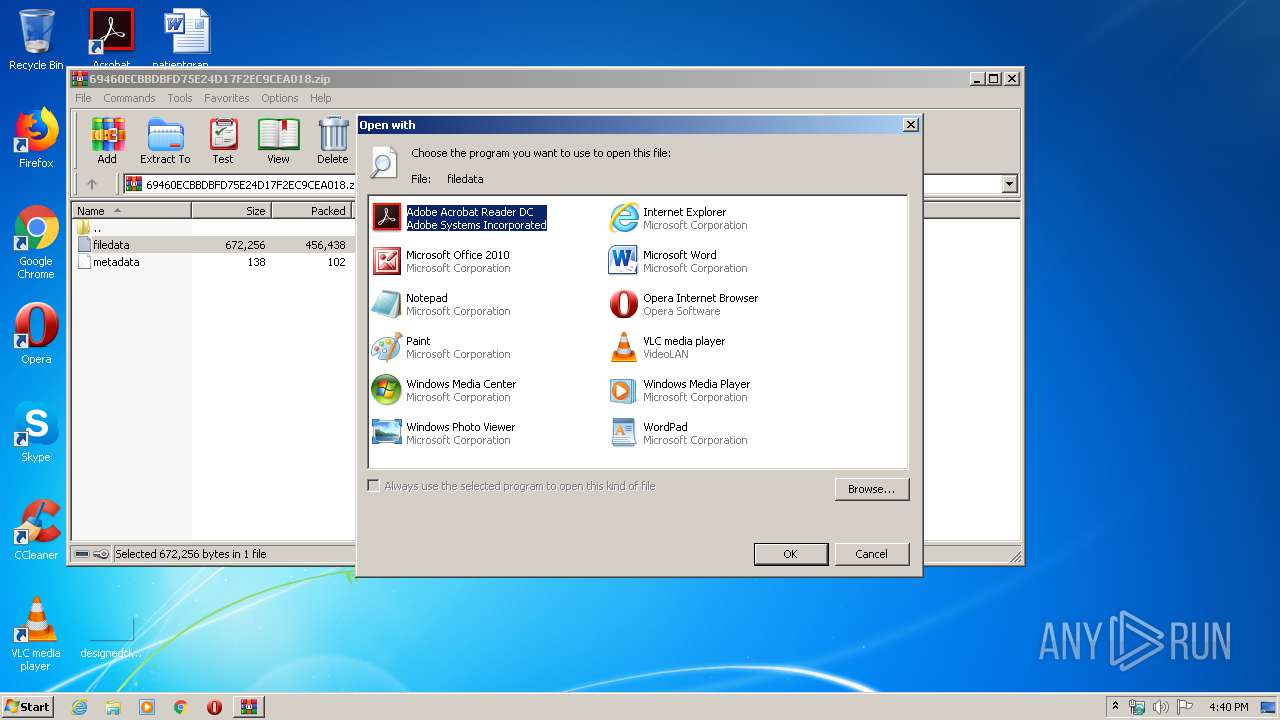
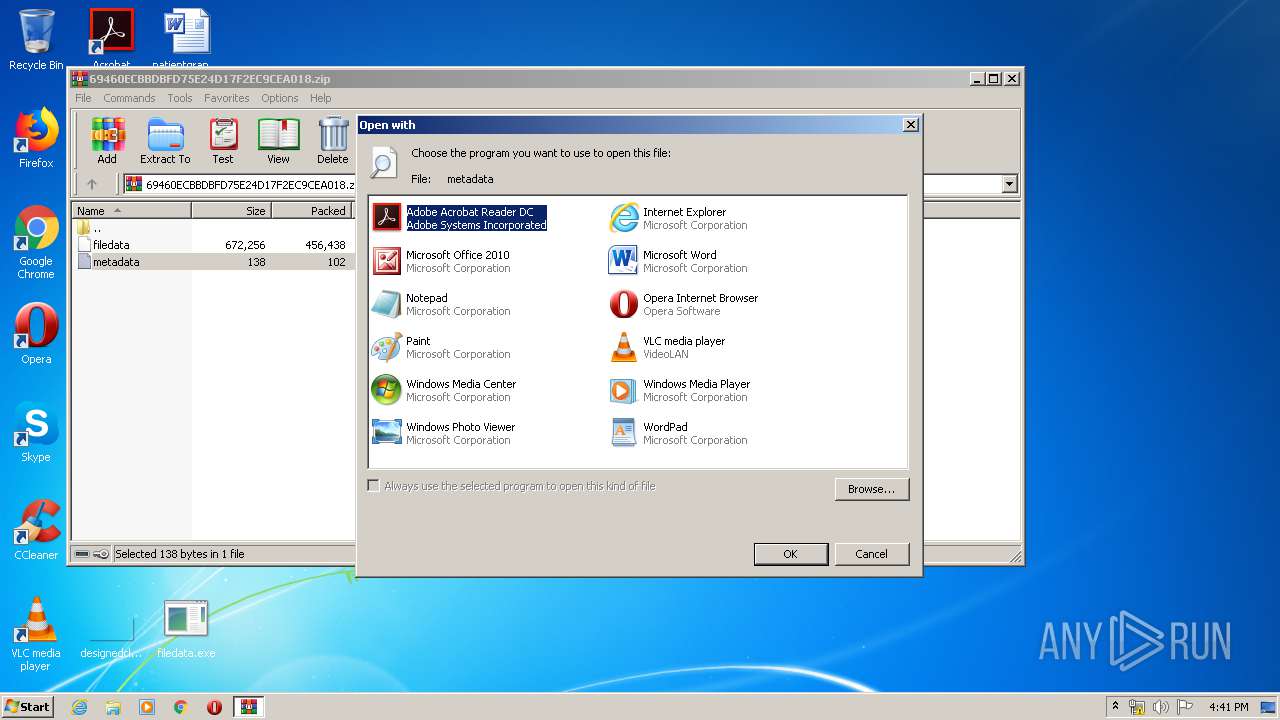
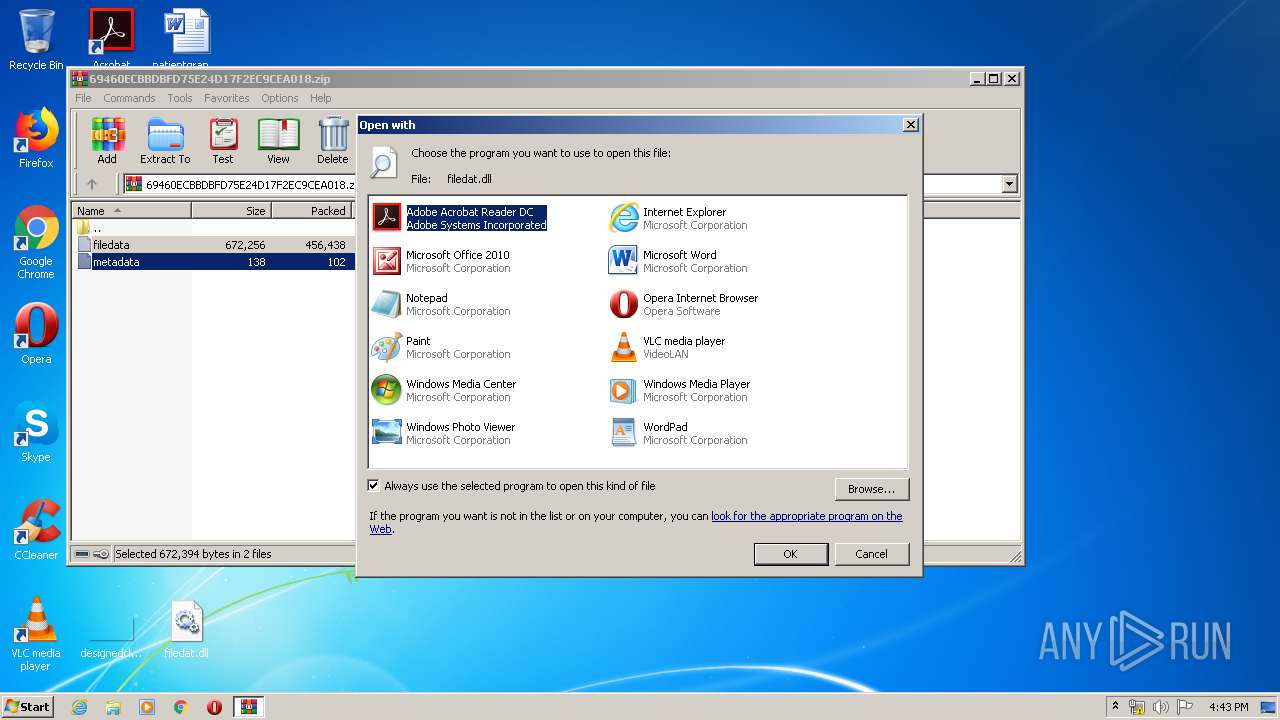
| 256 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIa1456.15384\filedata | C:\Windows\system32\rundll32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
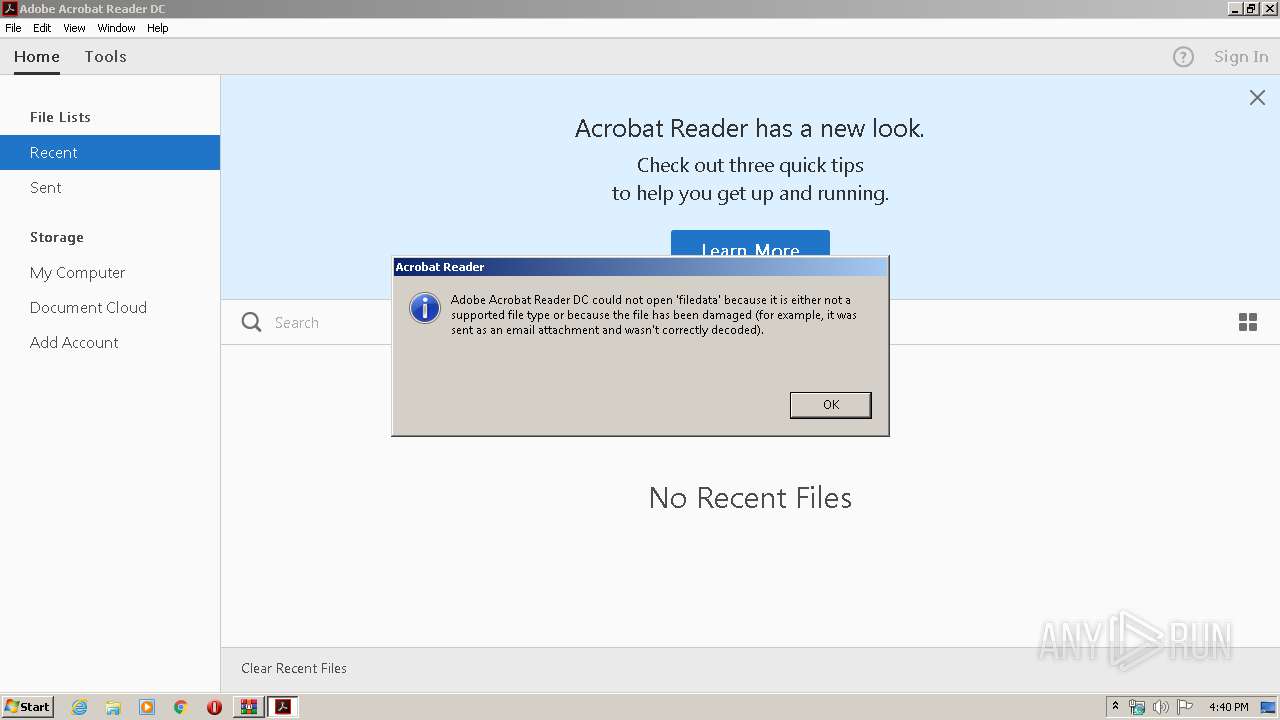
| 348 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\AppData\Local\Temp\Rar$DIa1456.15384\filedata" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 660 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa1456.15384\filedata | C:\Program Files\Internet Explorer\iexplore.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 860 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 872 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa1456.15384\filedata" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1116 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIa1456.15384\filedata | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
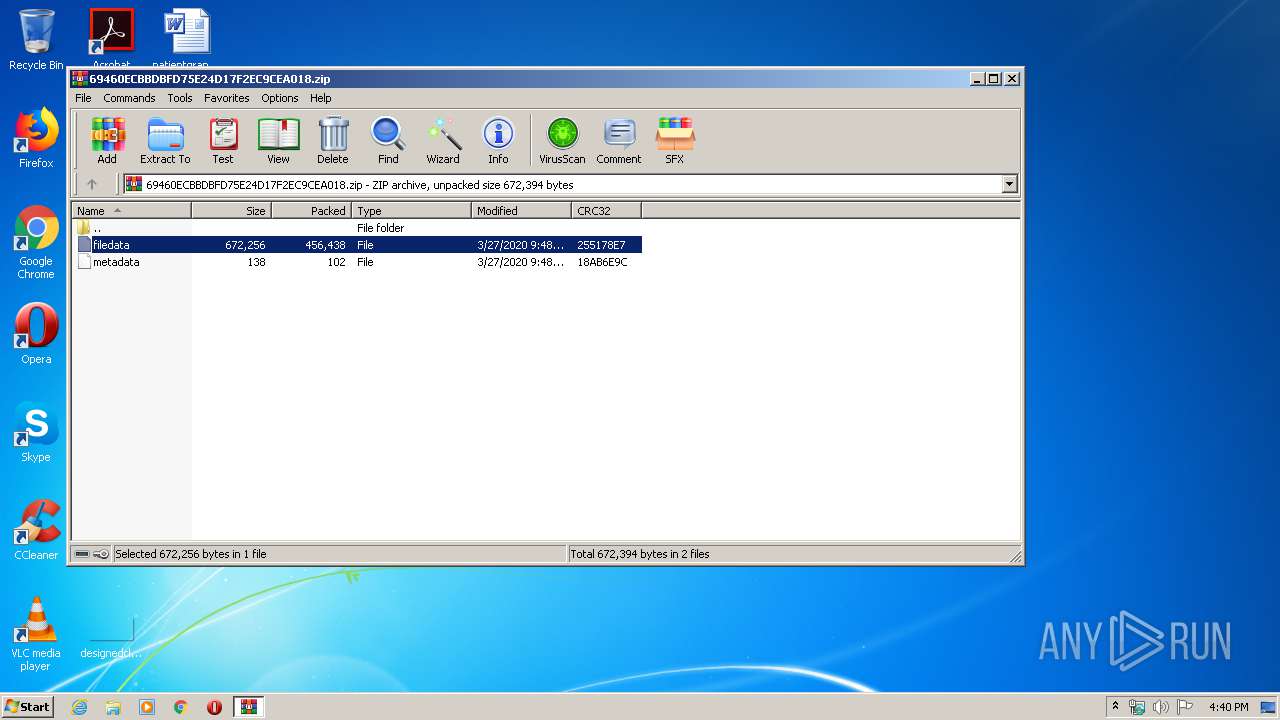
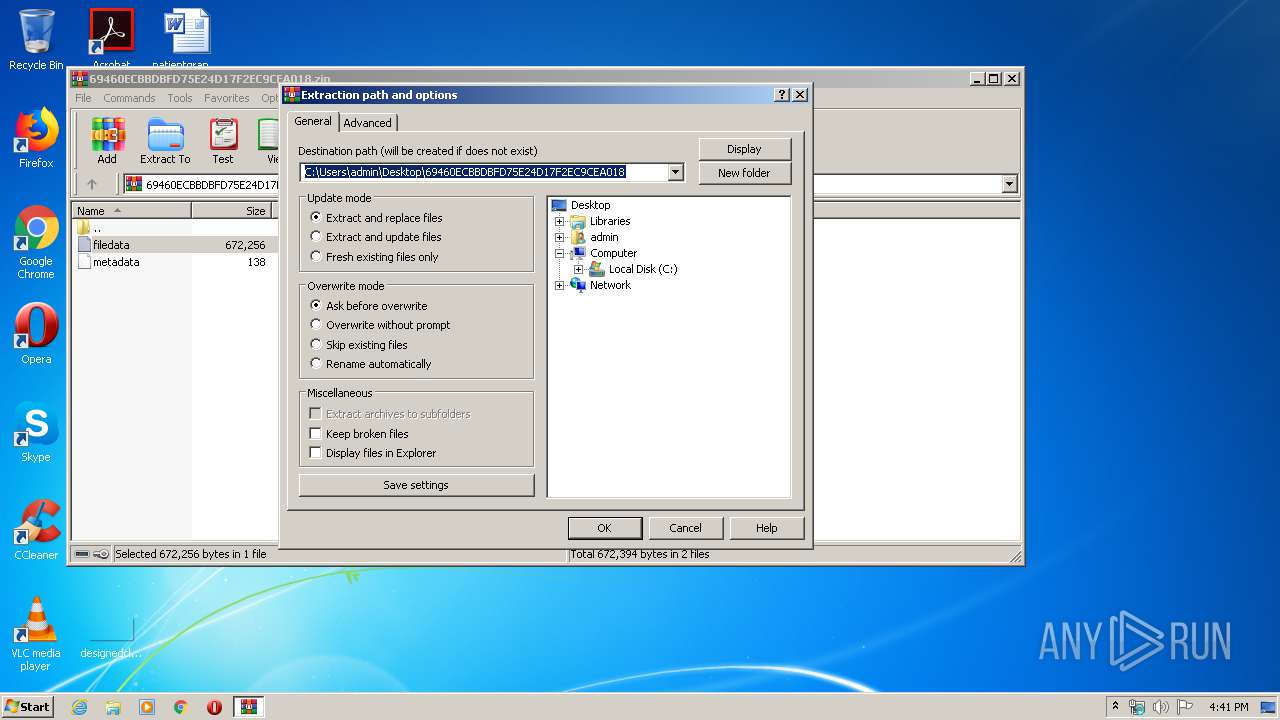
| 1456 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\69460ECBBDBFD75E24D17F2EC9CEA018.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2556 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2556 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\Desktop\filedat.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 896
Read events
6 459
Write events
433
Delete events
4
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\69460ECBBDBFD75E24D17F2EC9CEA018.zip | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
Executable files
5
Suspicious files
7
Text files
2
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 660 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8AA90E3E2BCC4374.TMP | — | |
MD5:— | SHA256:— | |||
| 660 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7D6B92012EC9B465.TMP | — | |
MD5:— | SHA256:— | |||
| 660 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{C905F75D-729C-11EA-972D-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 348 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF27A66287331B5DF9.TMP | — | |
MD5:— | SHA256:— | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2442297F4F024665.TMP | — | |
MD5:— | SHA256:— | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2BE29D238F3D2752.TMP | — | |
MD5:— | SHA256:— | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFEA365E3C84F1C1BA.TMP | — | |
MD5:— | SHA256:— | |||
| 860 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2556 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |