| File name: | ldr.exe |
| Full analysis: | https://app.any.run/tasks/a51c9831-3efc-45c4-8547-e78932da9863 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2024, 14:25:11 |
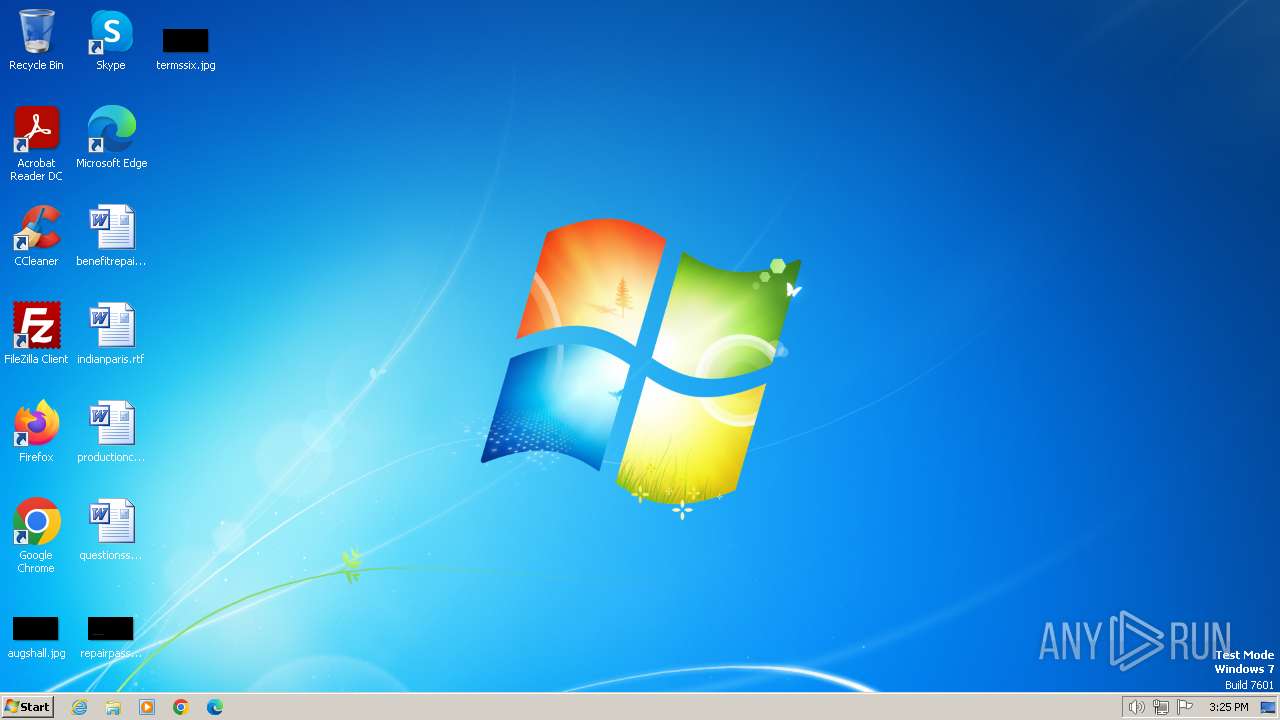
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 77AAD74C2A9ED87342194C41ECA6B62D |
| SHA1: | 54931D97102C5E393B0A0ADFE693CE4784710E4A |
| SHA256: | 00CA2DA926E0CA08C52D9AE4A41862BCD84DE5048539E3DD9BDD56C0993BB2A3 |
| SSDEEP: | 6144:ouwbUamw3+QmMF+IrEucXf+yDFIlfSC1:q+gEIrEZXmyDpC1 |
MALICIOUS
Drops the executable file immediately after the start
- ldr.exe (PID: 2124)
SUSPICIOUS
Reads security settings of Internet Explorer
- ldr.exe (PID: 2124)
Reads the Internet Settings
- ldr.exe (PID: 2124)
Connects to the server without a host name
- ldr.exe (PID: 2124)
INFO
Checks supported languages
- ldr.exe (PID: 2124)
Checks proxy server information
- ldr.exe (PID: 2124)
Reads the computer name
- ldr.exe (PID: 2124)
Reads the machine GUID from the registry
- ldr.exe (PID: 2124)
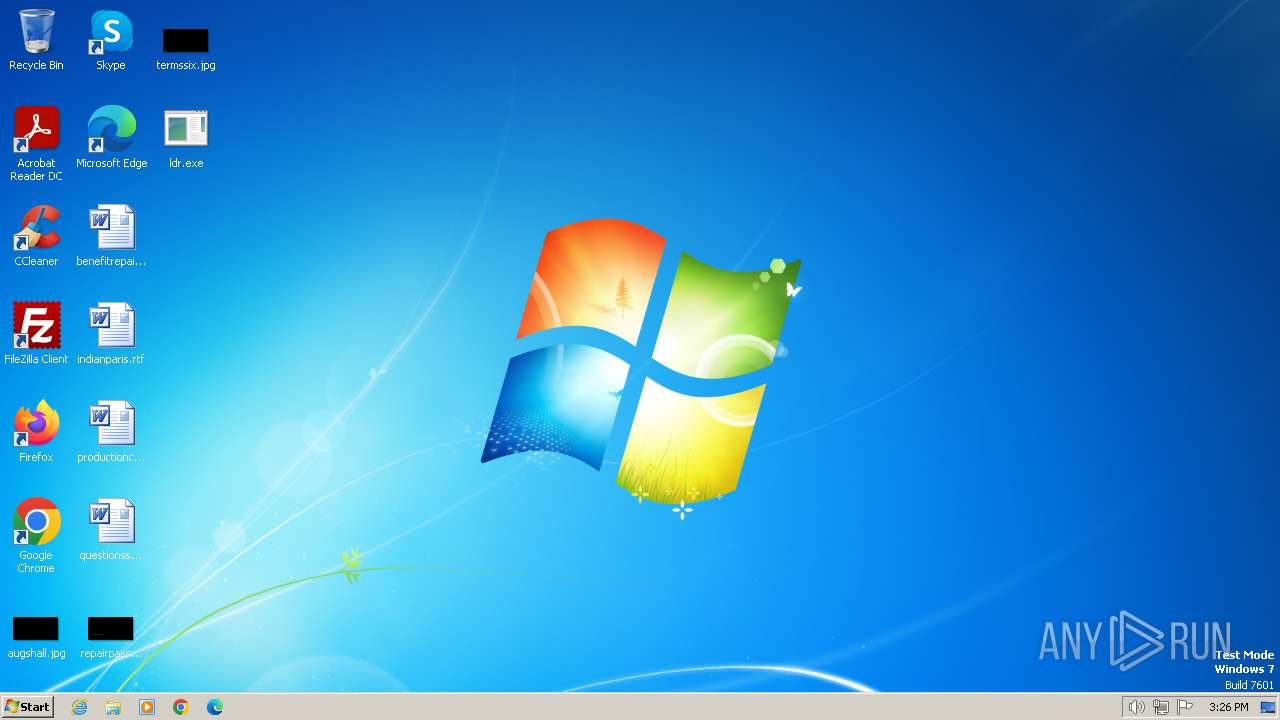
Manual execution by a user
- explorer.exe (PID: 1824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:04:01 14:24:22+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 122880 |
| InitializedDataSize: | 67584 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x69c2 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
39
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1824 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2124 | "C:\Users\admin\Desktop\ldr.exe" | C:\Users\admin\Desktop\ldr.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
760
Read events
734
Write events
20
Delete events
6
Modification events
| (PID) Process: | (2124) ldr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2124) ldr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (2124) ldr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (2124) ldr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (2124) ldr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (2124) ldr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005C010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2124) ldr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2124) ldr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2124) ldr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2124) ldr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
6
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2124 | ldr.exe | GET | 404 | 193.233.132.167:80 | http://193.233.132.167/lend/1 | unknown | — | — | unknown |
2124 | ldr.exe | GET | 404 | 193.233.132.167:80 | http://193.233.132.167/lend/3 | unknown | — | — | unknown |
2124 | ldr.exe | GET | 404 | 193.233.132.167:80 | http://193.233.132.167/lend/2 | unknown | — | — | unknown |
2124 | ldr.exe | GET | 404 | 193.233.132.167:80 | http://193.233.132.167/lend/4 | unknown | — | — | unknown |
2124 | ldr.exe | GET | 404 | 193.233.132.167:80 | http://193.233.132.167/lend/5 | unknown | — | — | unknown |
2124 | ldr.exe | GET | 404 | 193.233.132.167:80 | http://193.233.132.167/lend/6 | unknown | — | — | unknown |
2124 | ldr.exe | GET | 404 | 193.233.132.167:80 | http://193.233.132.167/lend/7 | unknown | — | — | unknown |
2124 | ldr.exe | GET | 404 | 193.233.132.167:80 | http://193.233.132.167/lend/9 | unknown | — | — | unknown |
2124 | ldr.exe | GET | 404 | 193.233.132.167:80 | http://193.233.132.167/lend/10 | unknown | — | — | unknown |
2124 | ldr.exe | GET | 404 | 193.233.132.167:80 | http://193.233.132.167/lend/8 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2124 | ldr.exe | 193.233.132.167:80 | — | ATT-INTERNET4 | US | unknown |