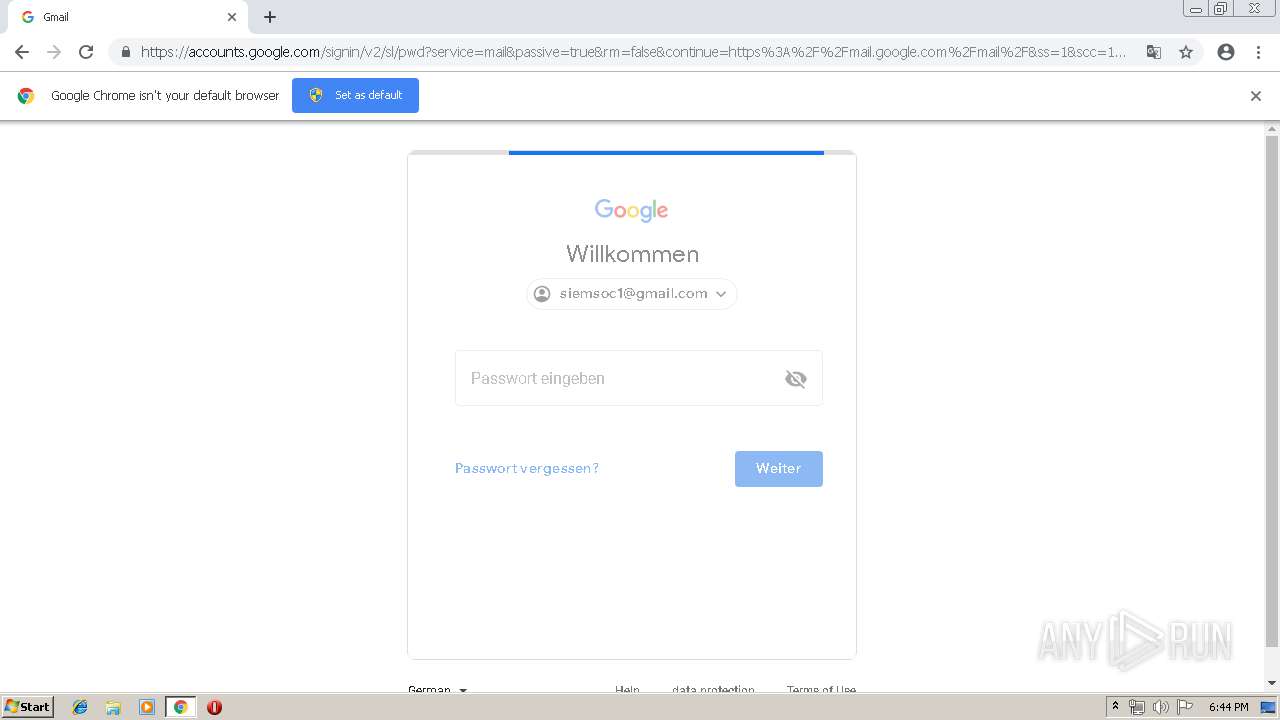
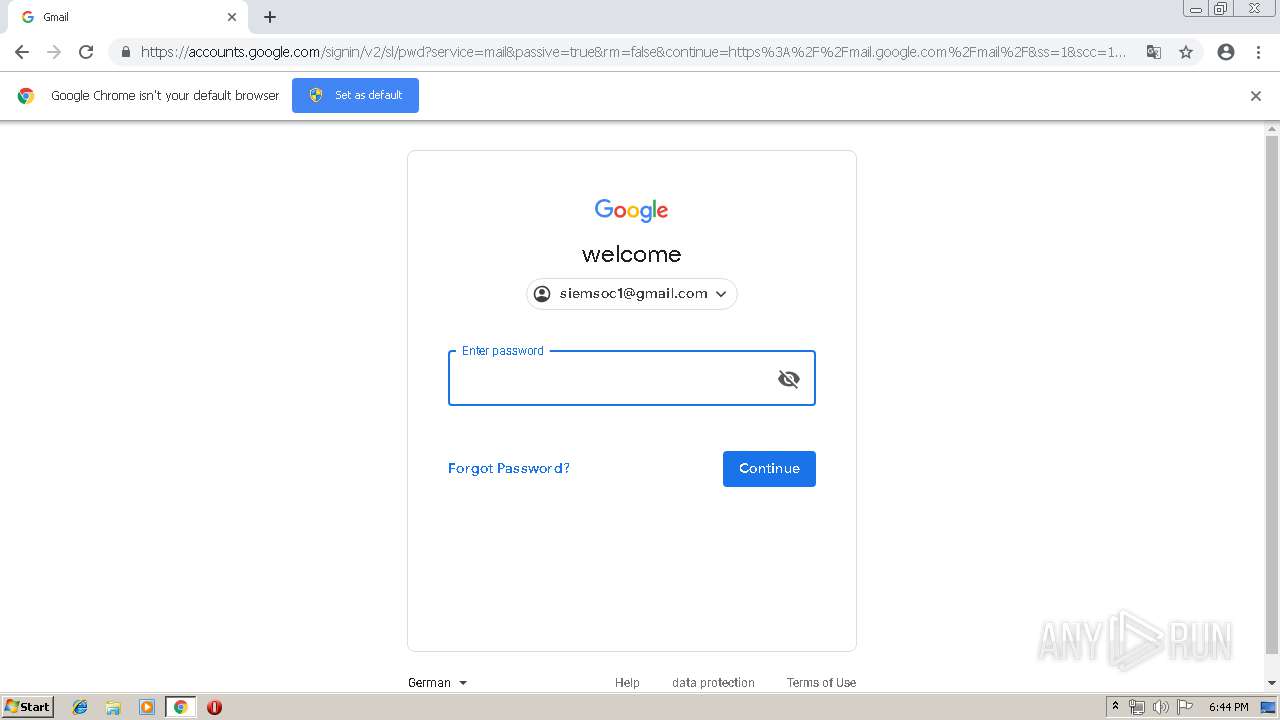
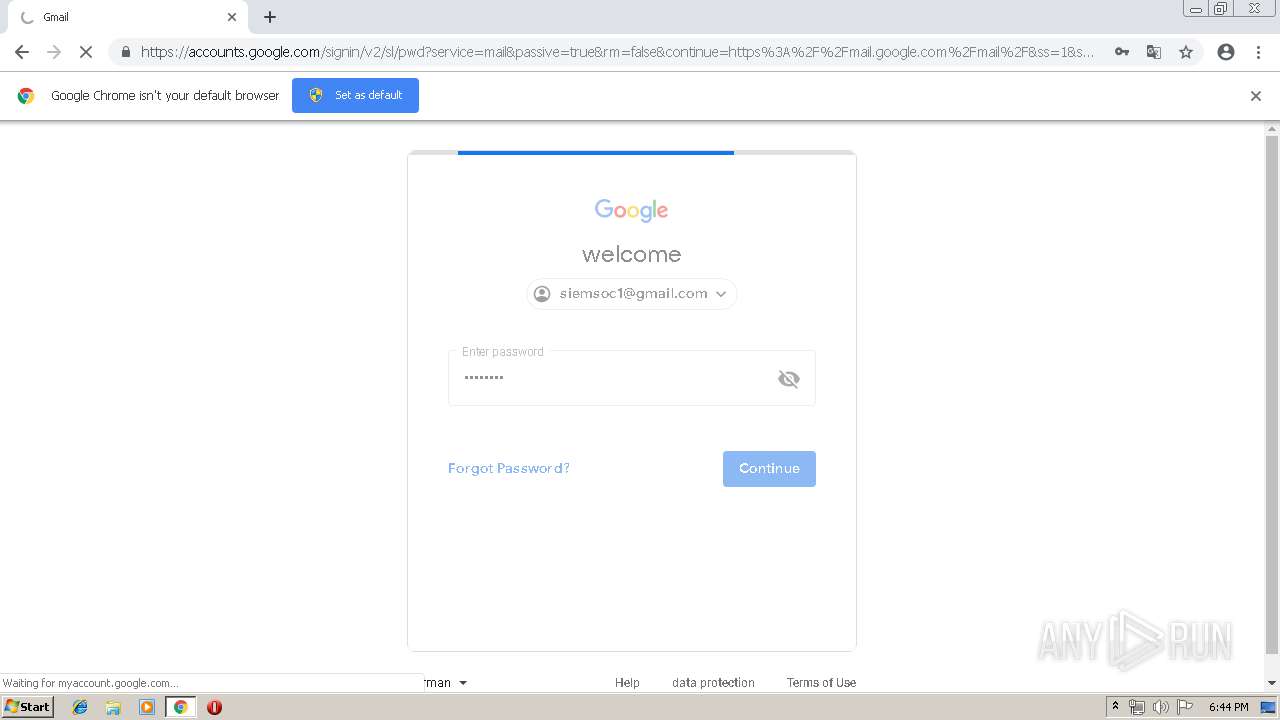
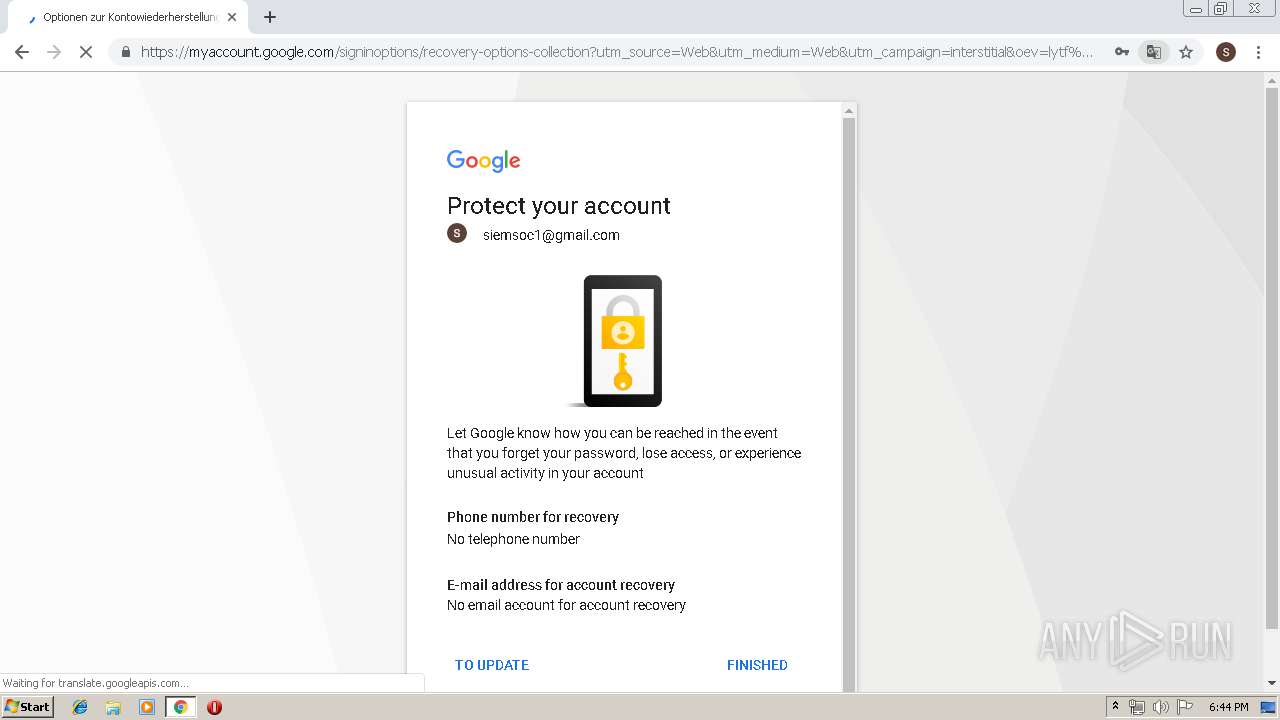
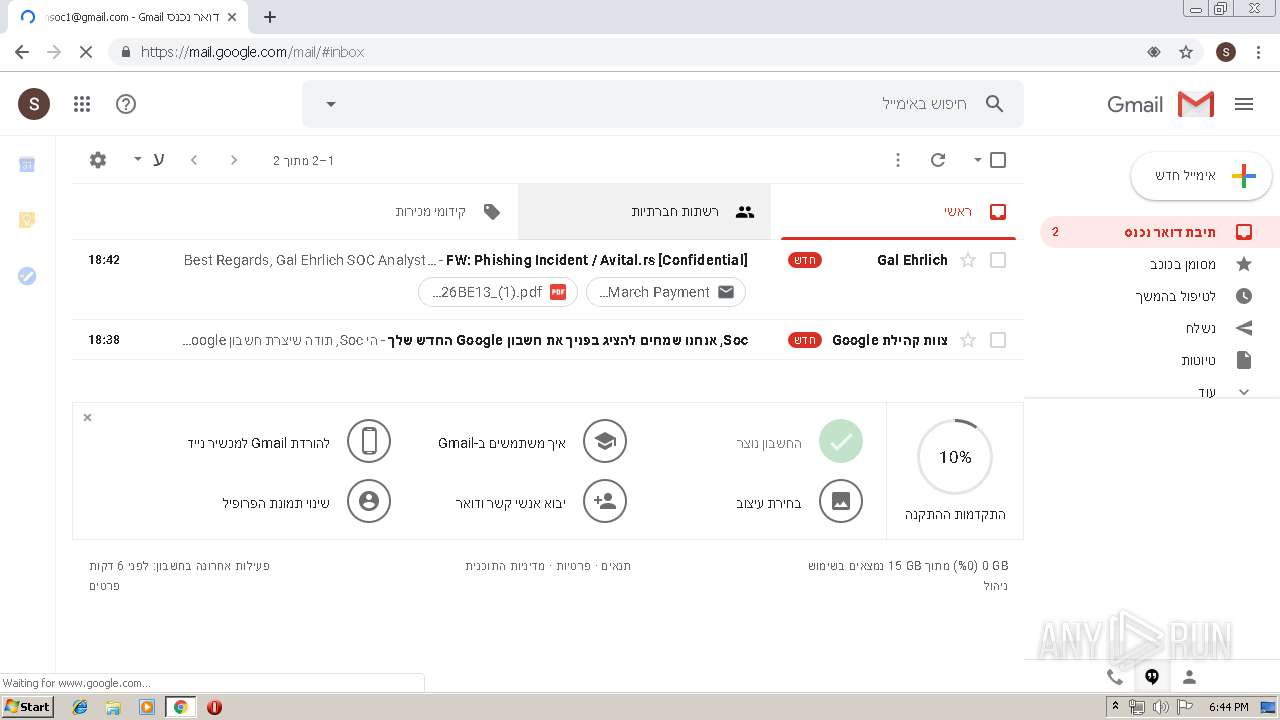
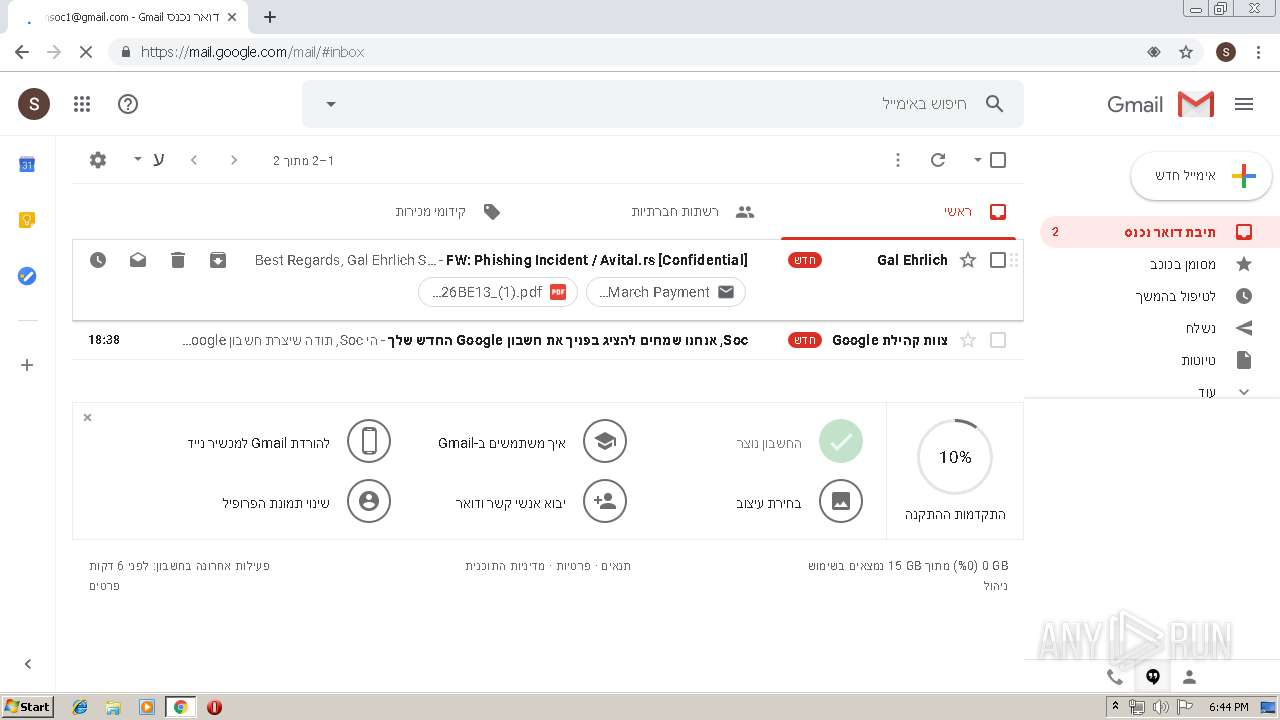
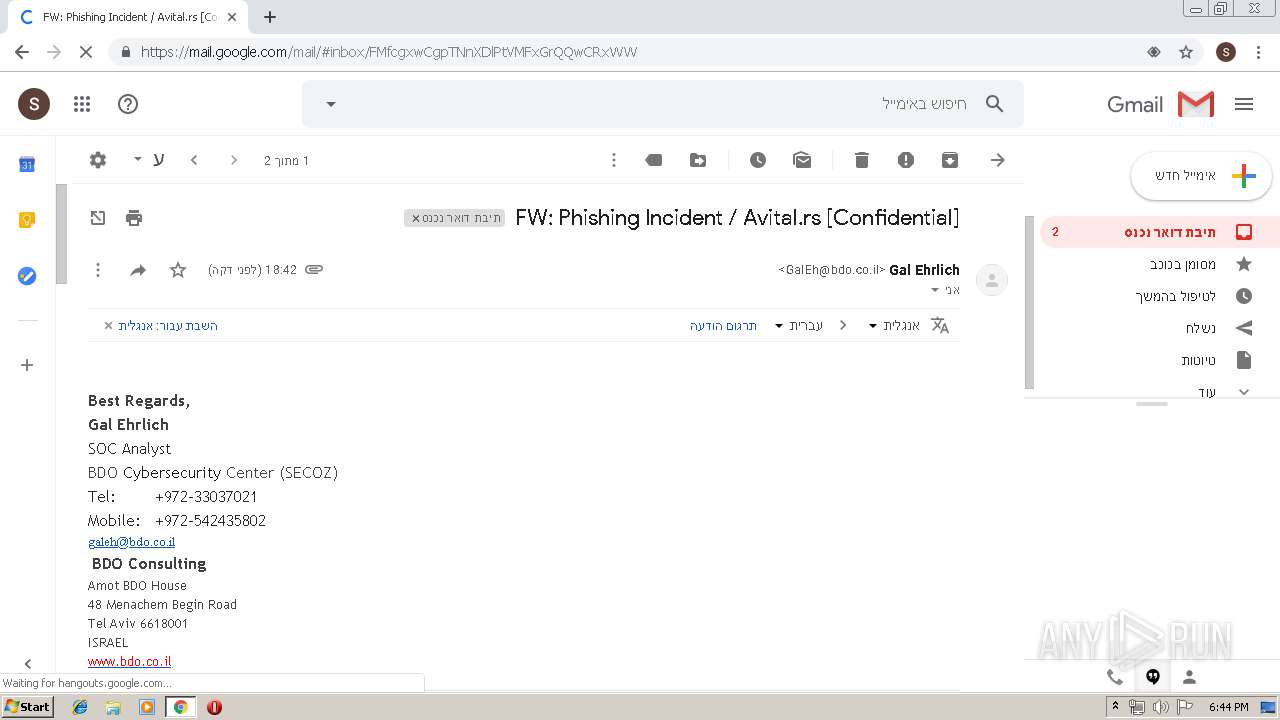
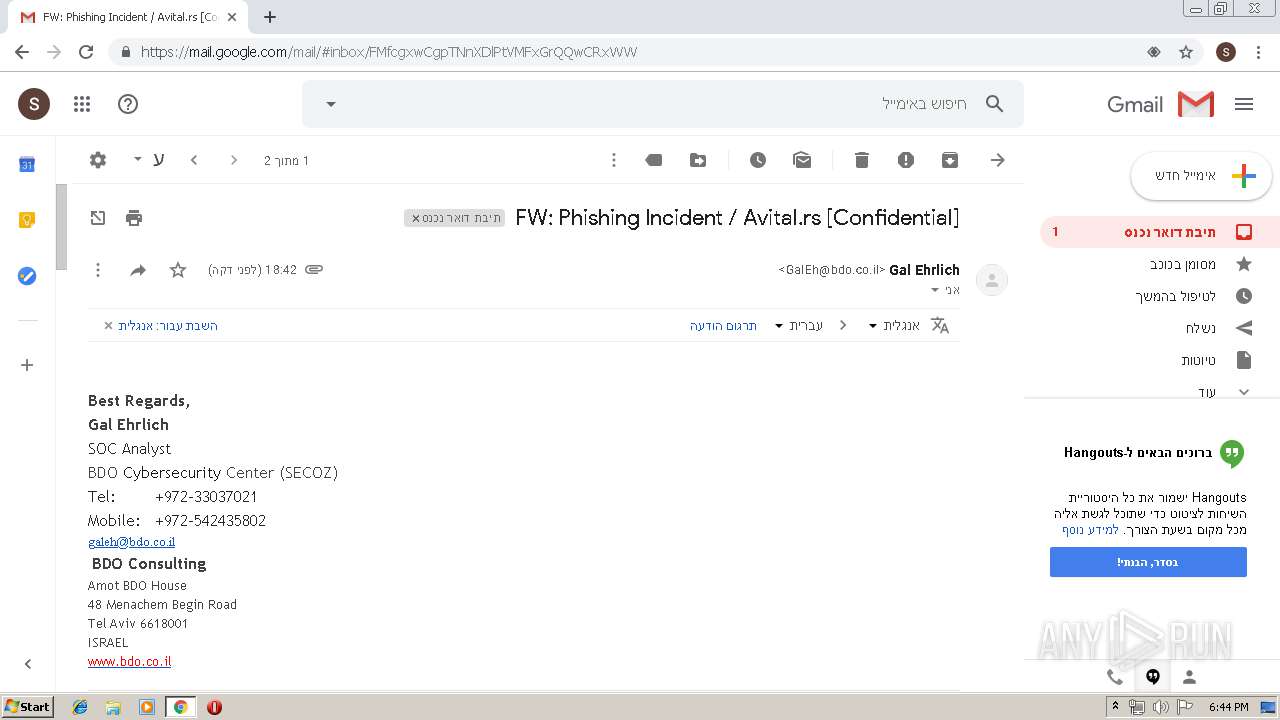
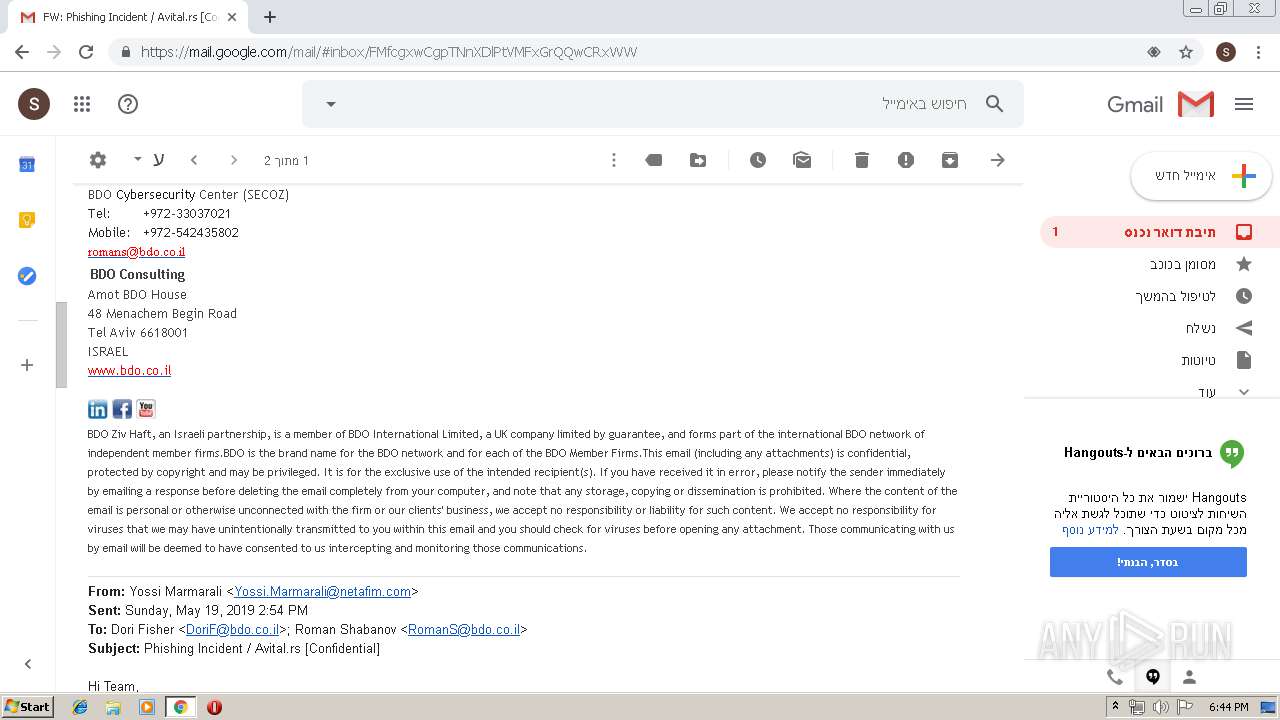
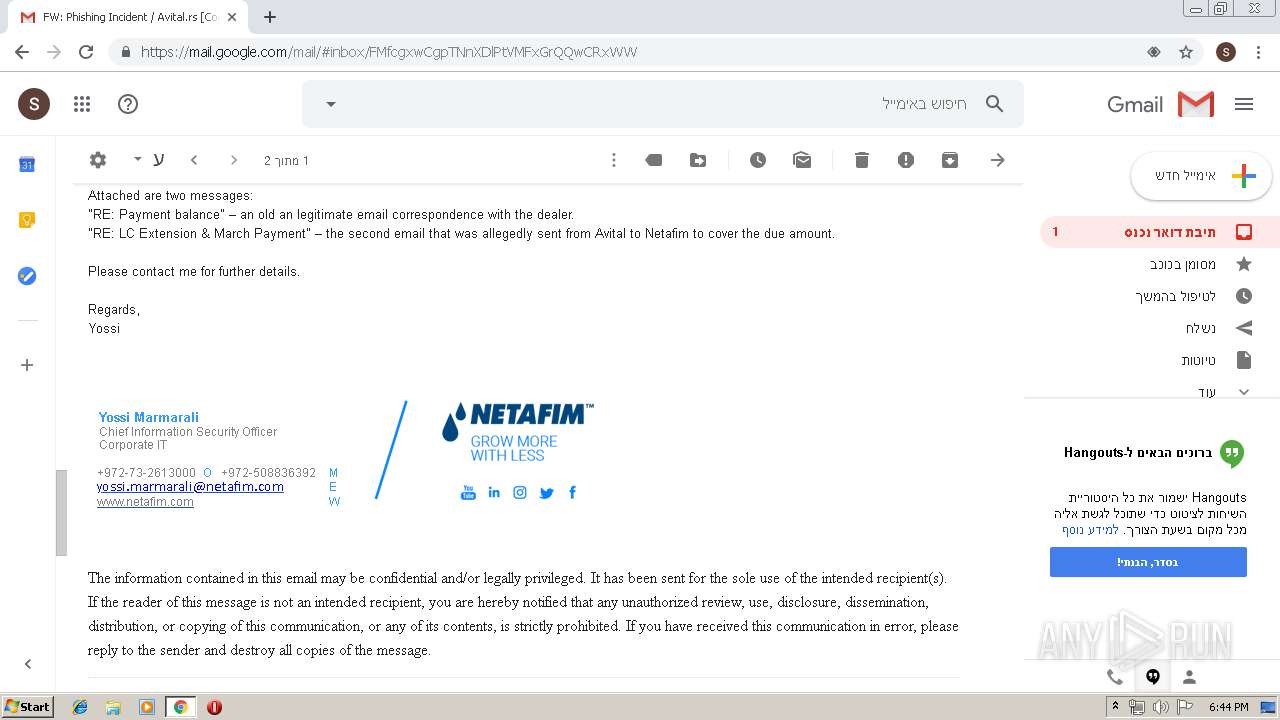
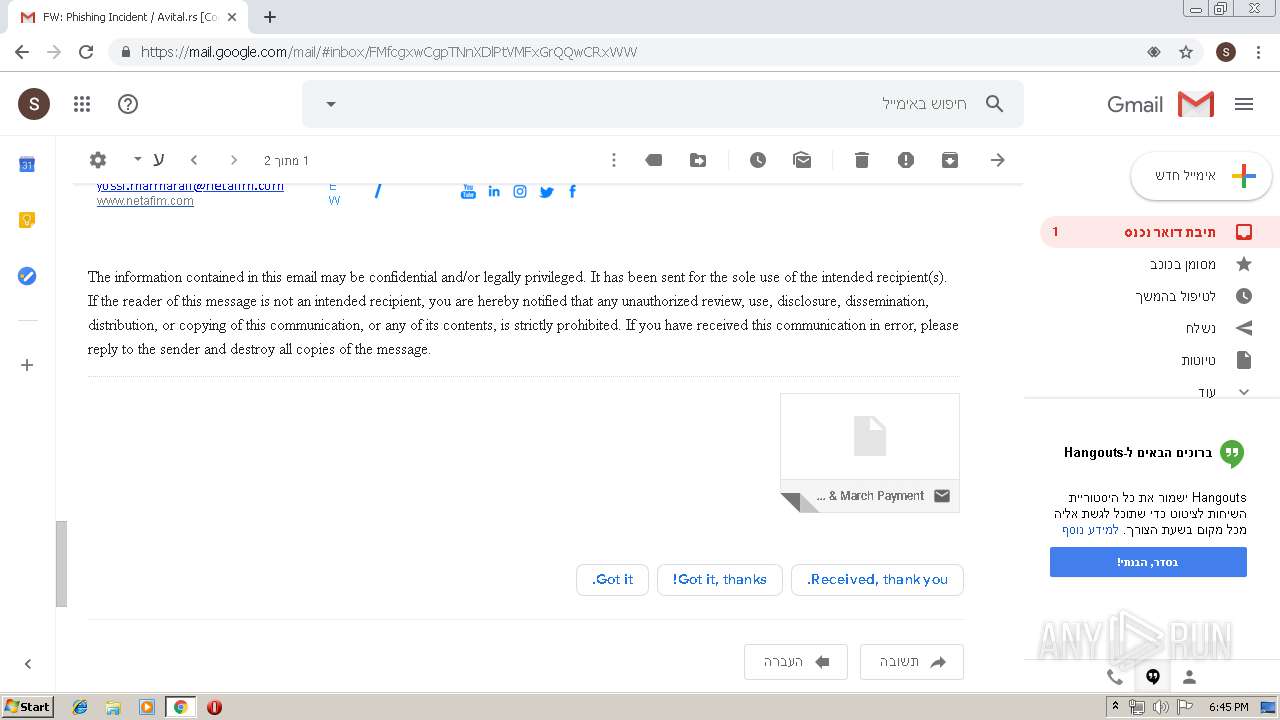
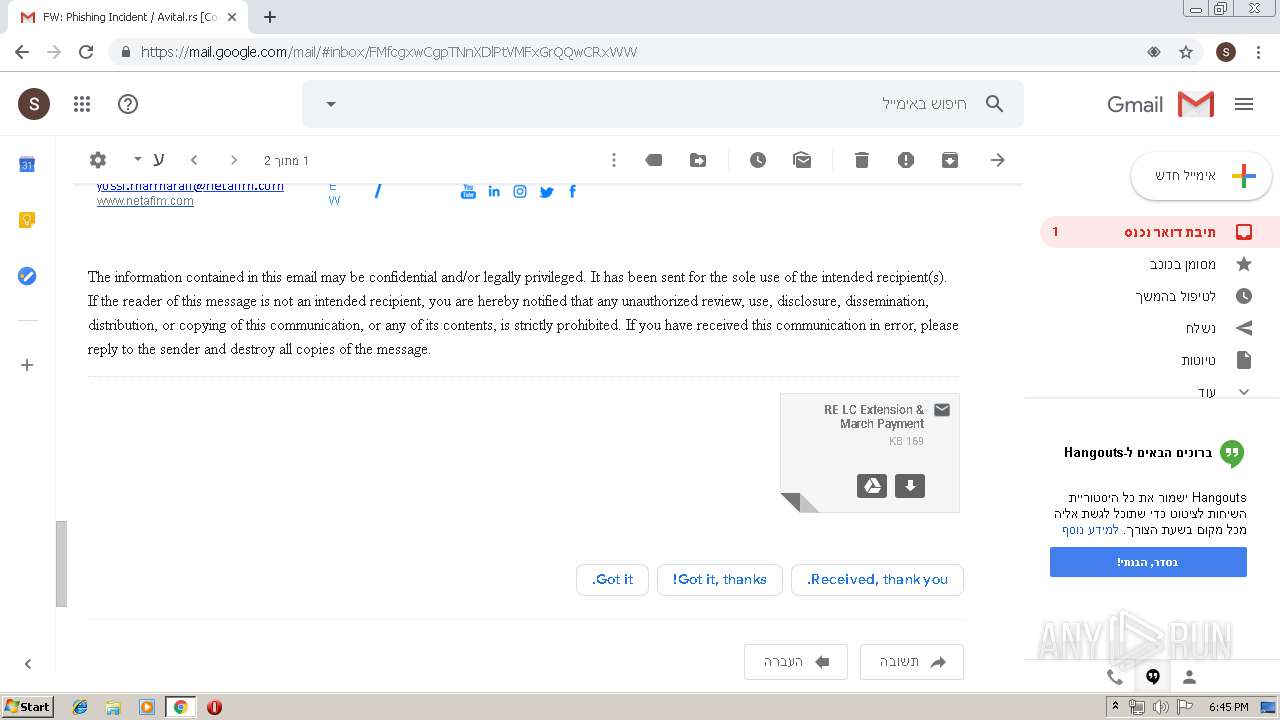
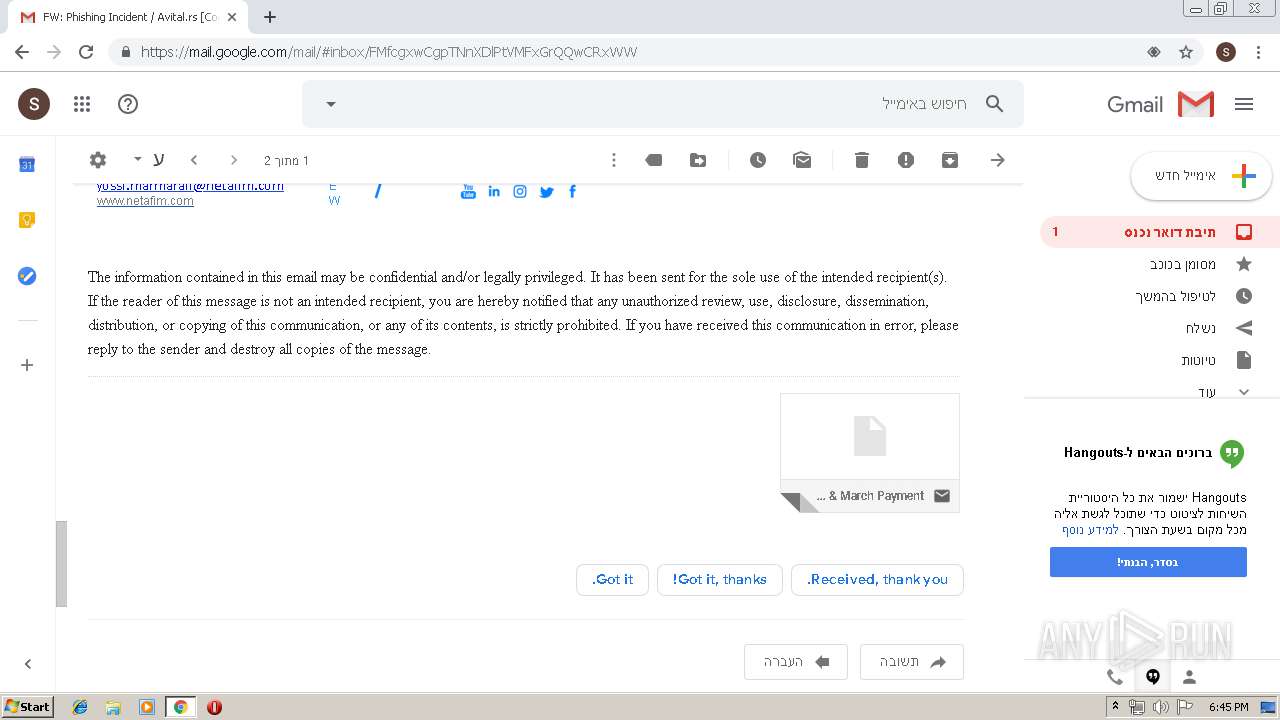
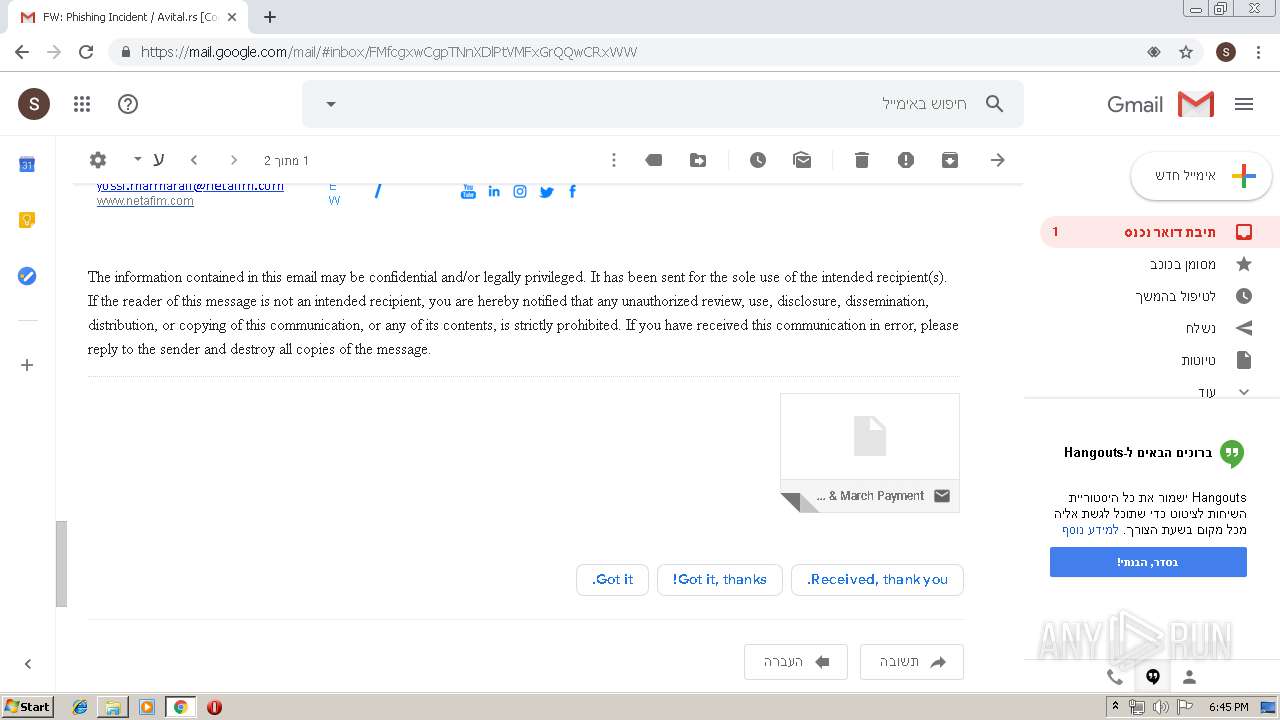
| URL: | https://gmail.com |
| Full analysis: | https://app.any.run/tasks/23eb0fd2-98c4-435d-8648-5b343dc6182a |
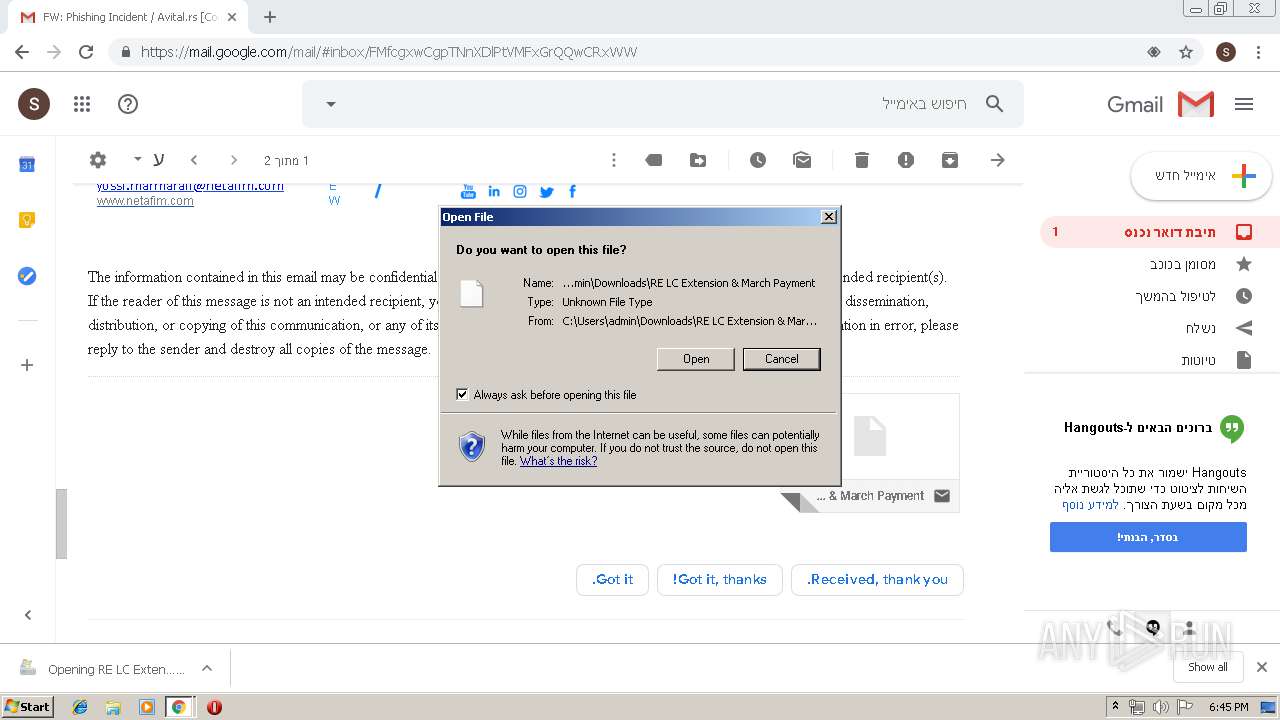
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 17:43:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7DEF1387568EC38373F52388F86B06BF |
| SHA1: | 8058B17B954586A7129730DC0F4839ABDBE49D3F |
| SHA256: | 00A70AB52EC14EC918A2DDCBEA5960E7940CBB7715843317E0B07F4283B8F632 |
| SSDEEP: | 3:N8pqn:2cn |
MALICIOUS
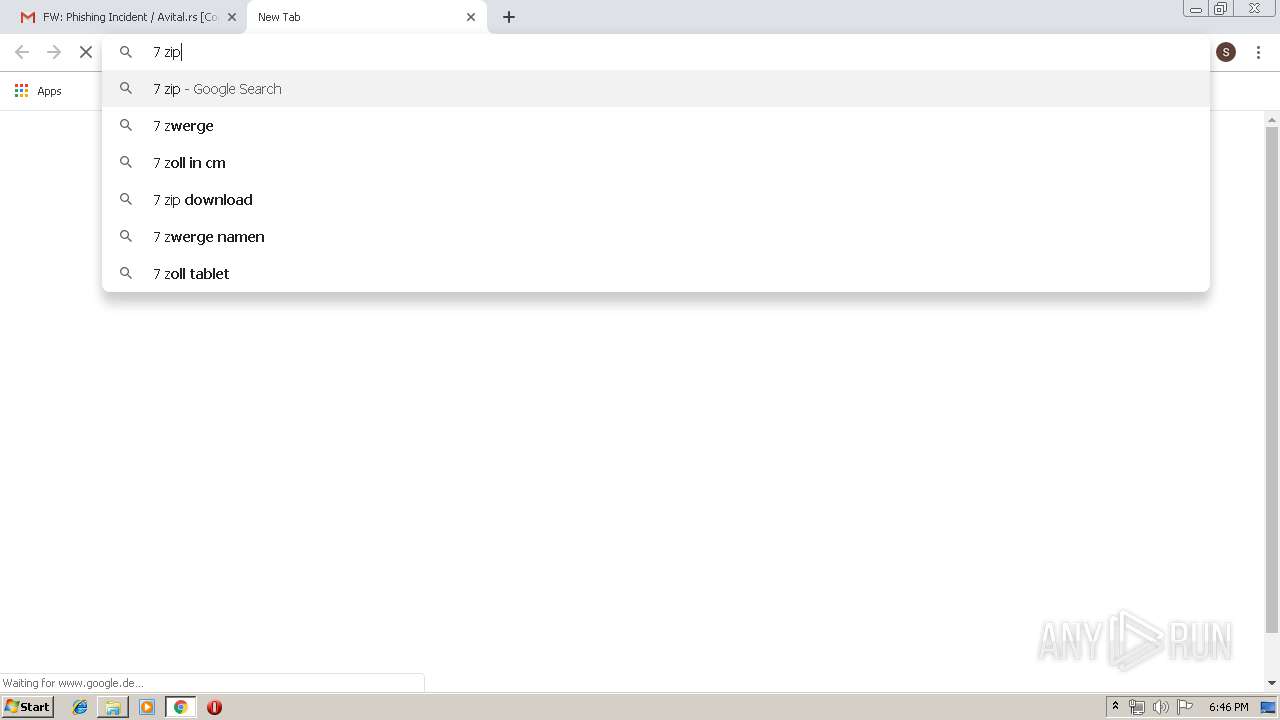
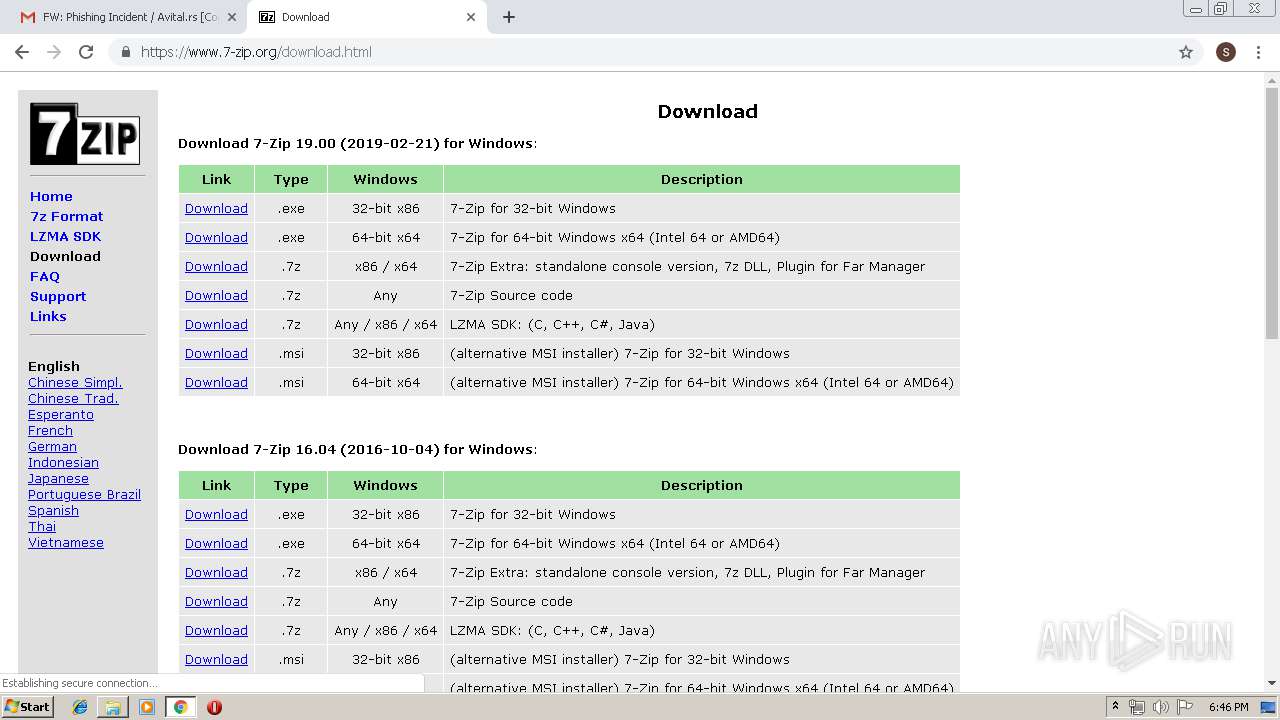
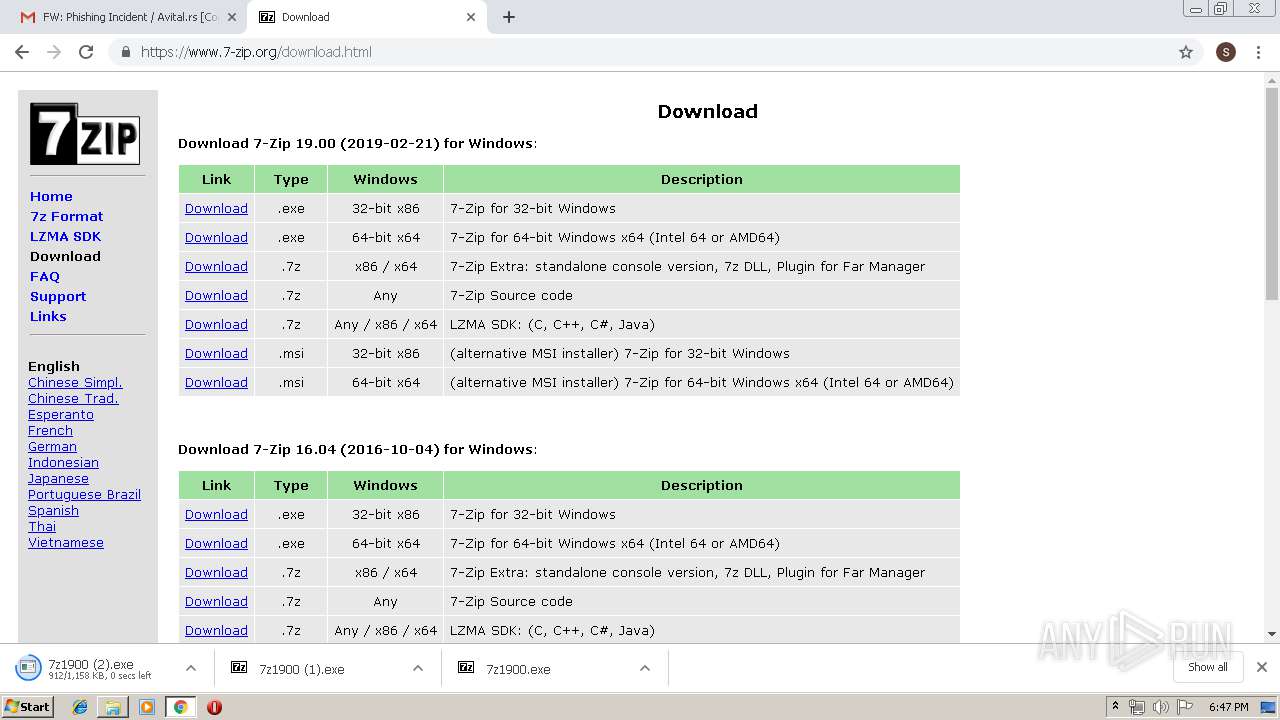
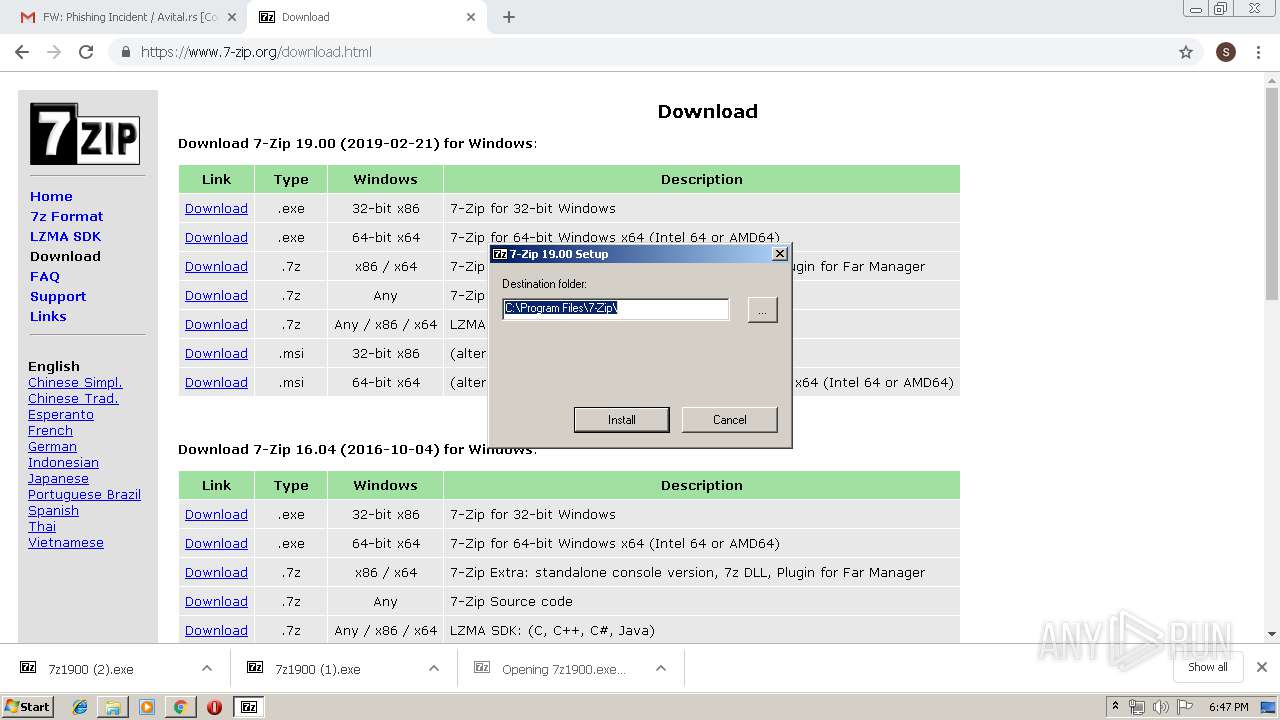
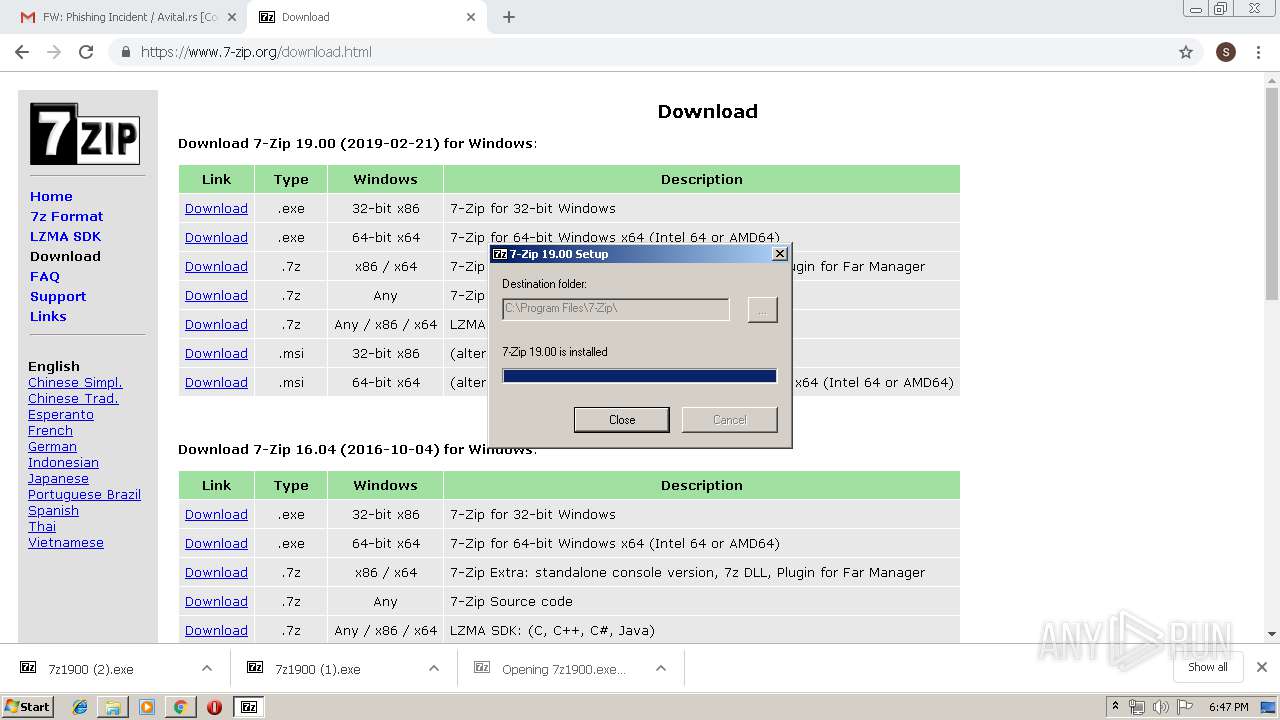
Application was dropped or rewritten from another process
- 7zG.exe (PID: 800)
- 7z1900.exe (PID: 2148)
- 7z1900.exe (PID: 2664)
Loads dropped or rewritten executable
- 7zG.exe (PID: 800)
- svchost.exe (PID: 840)
- explorer.exe (PID: 2036)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 2036)
- chrome.exe (PID: 2840)
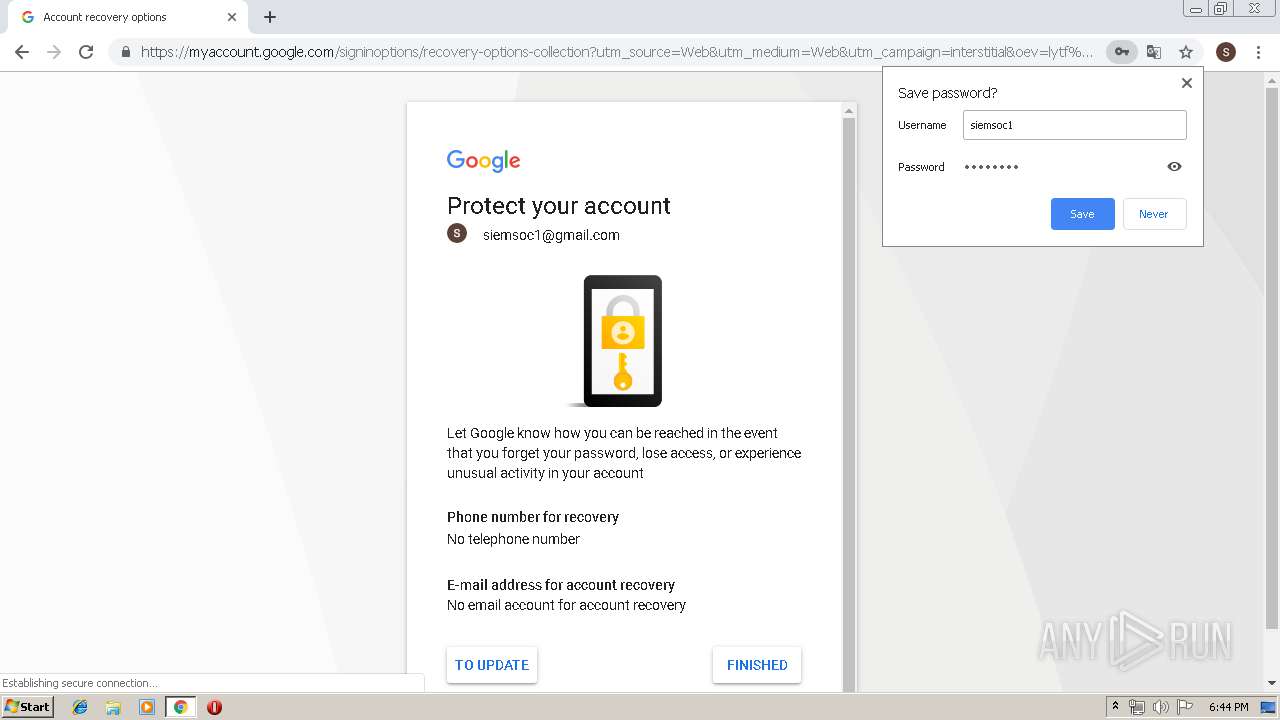
Modifies files in Chrome extension folder
- chrome.exe (PID: 2840)
Executable content was dropped or overwritten
- chrome.exe (PID: 2840)
- 7z1900.exe (PID: 2664)
Creates files in the user directory
- explorer.exe (PID: 2036)
Creates files in the program directory
- 7z1900.exe (PID: 2664)
Creates a software uninstall entry
- 7z1900.exe (PID: 2664)
Creates COM task schedule object
- 7z1900.exe (PID: 2664)
INFO
Application launched itself
- chrome.exe (PID: 2840)
- RdrCEF.exe (PID: 3108)
Reads Internet Cache Settings
- chrome.exe (PID: 2840)
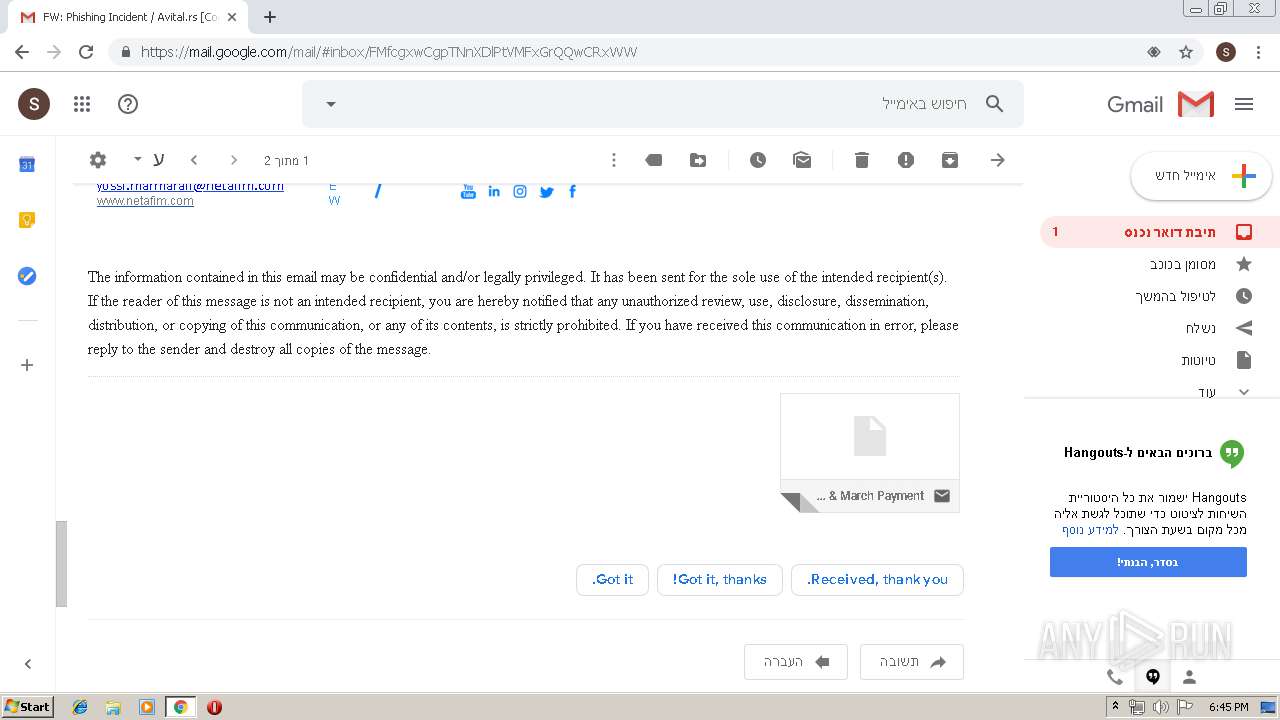
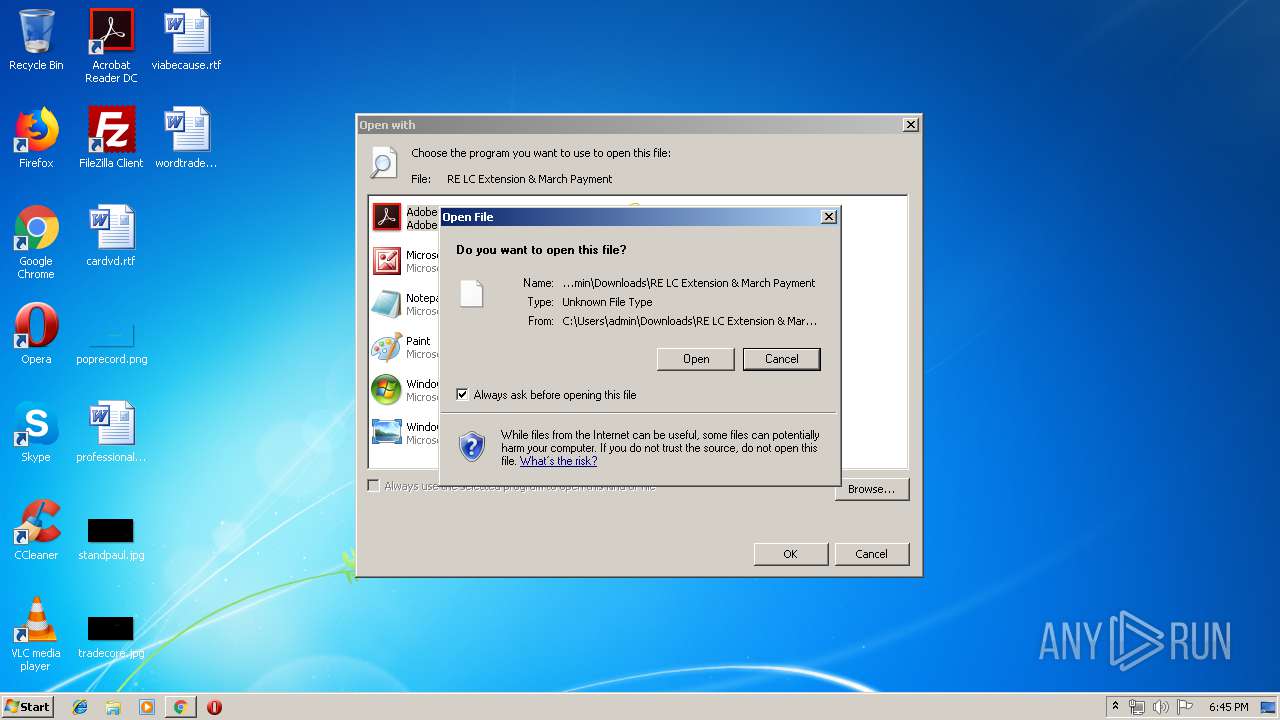
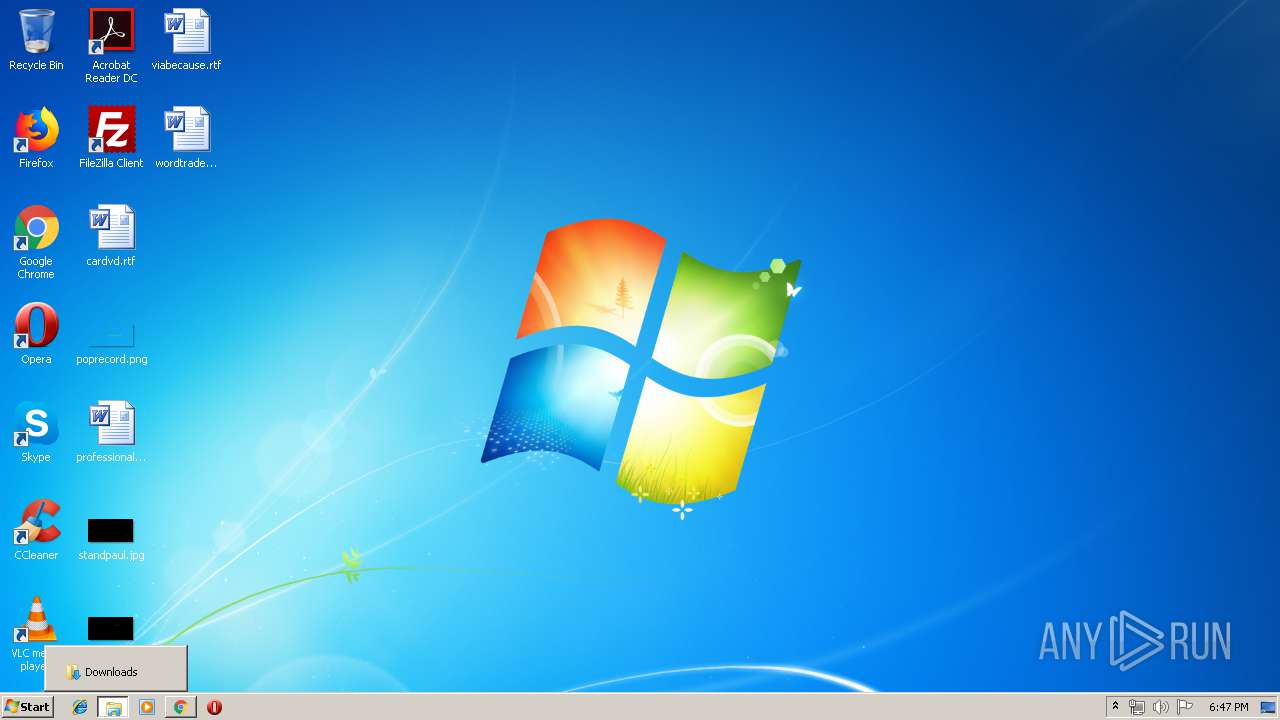
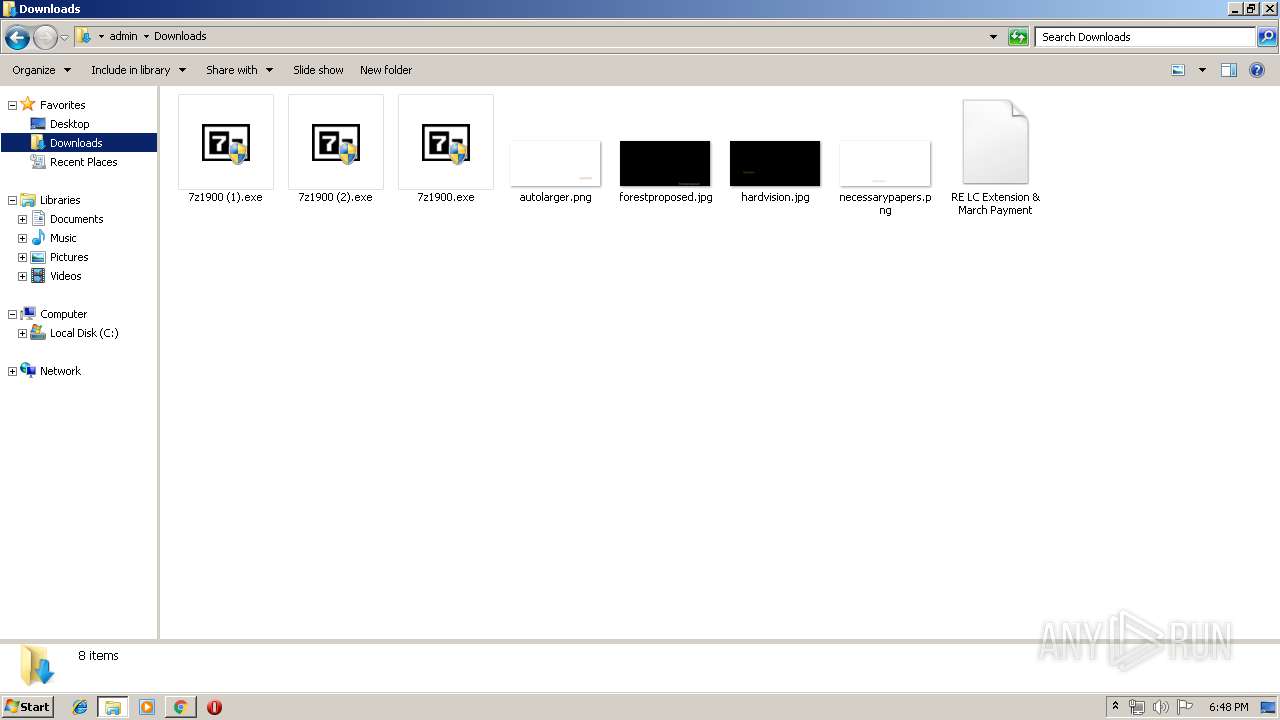
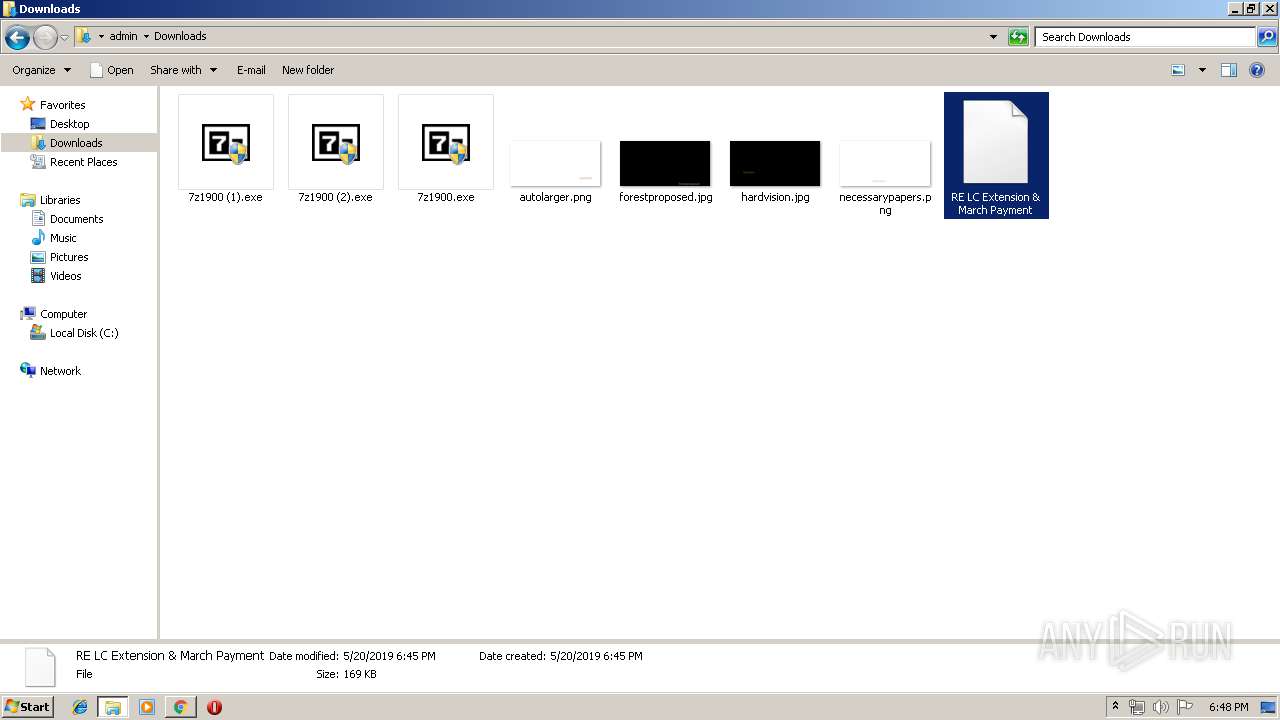
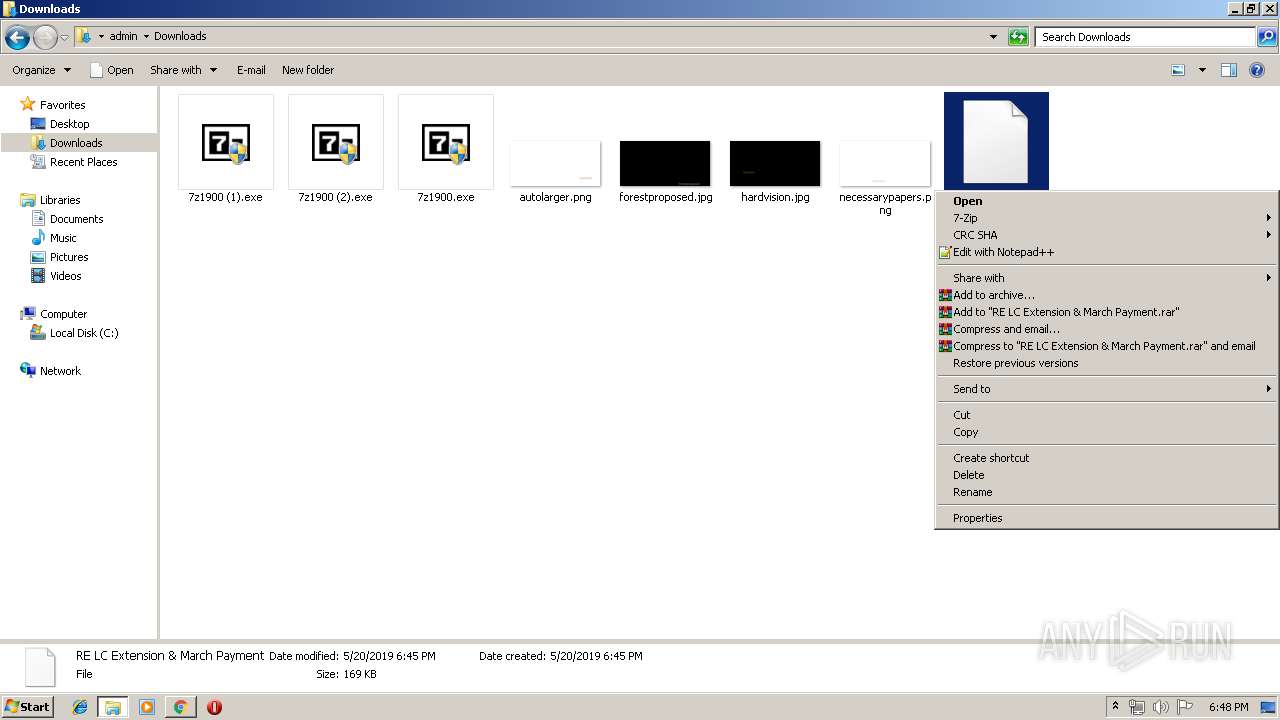
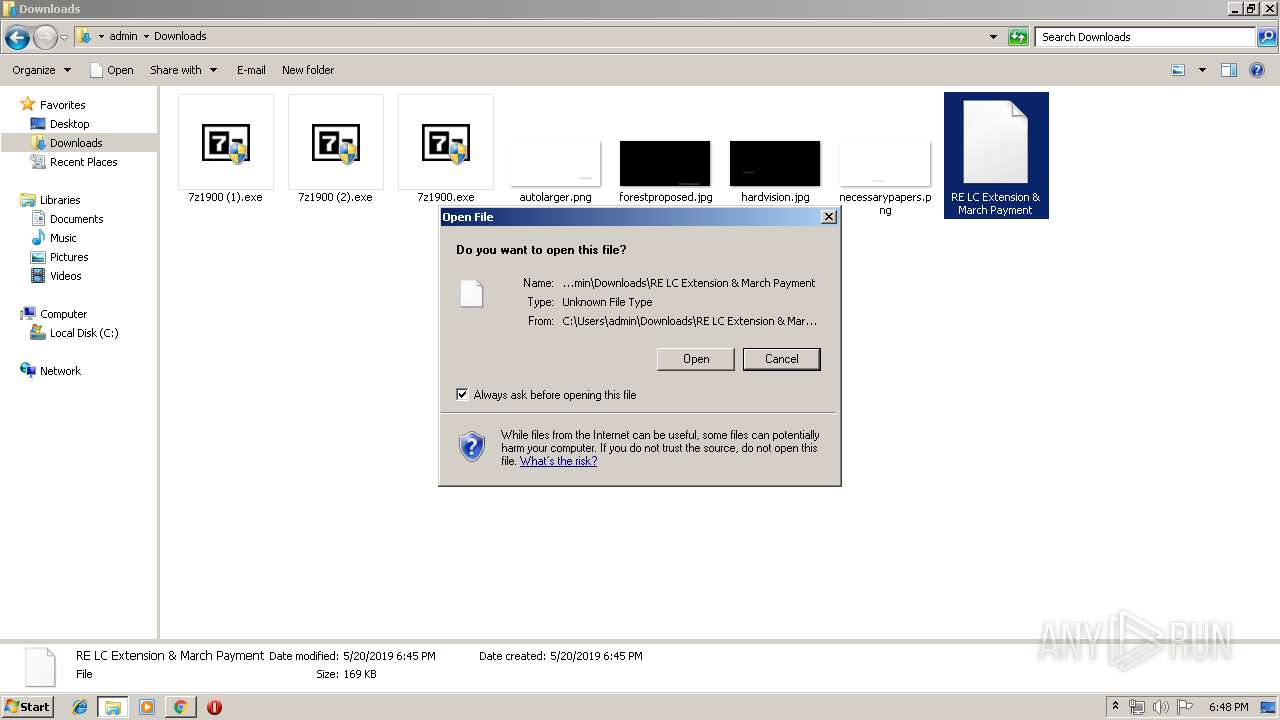
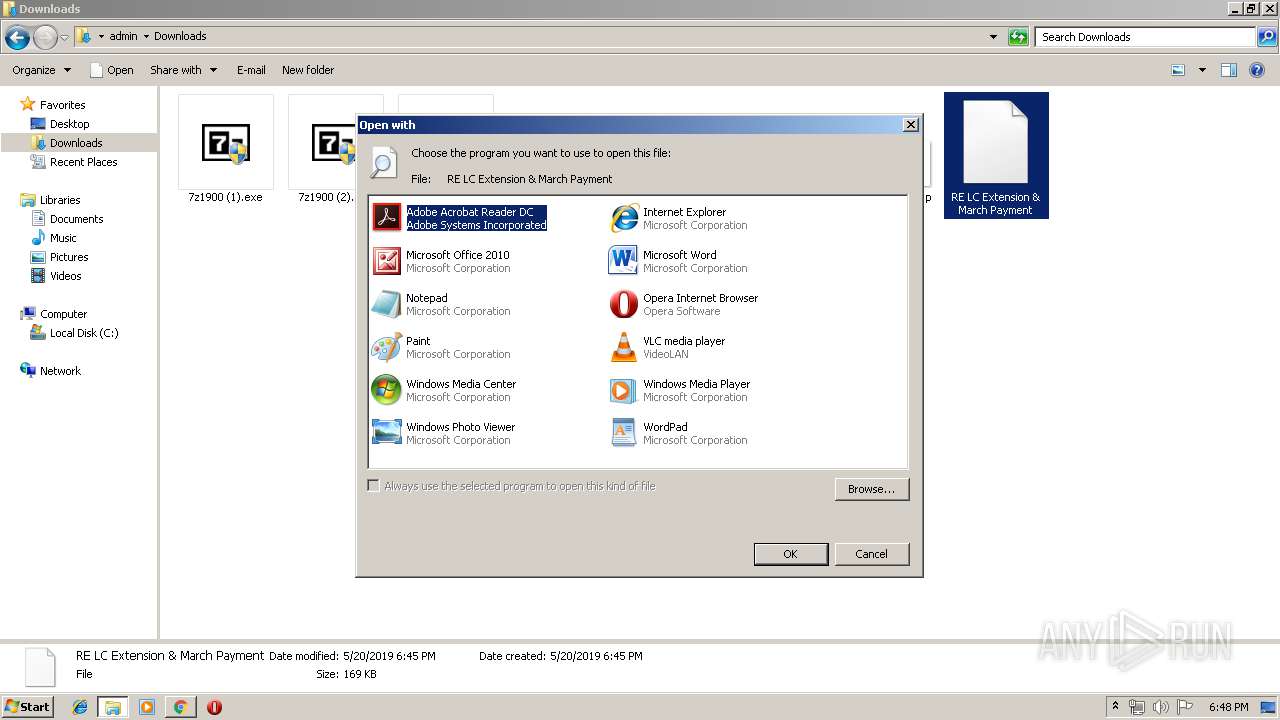
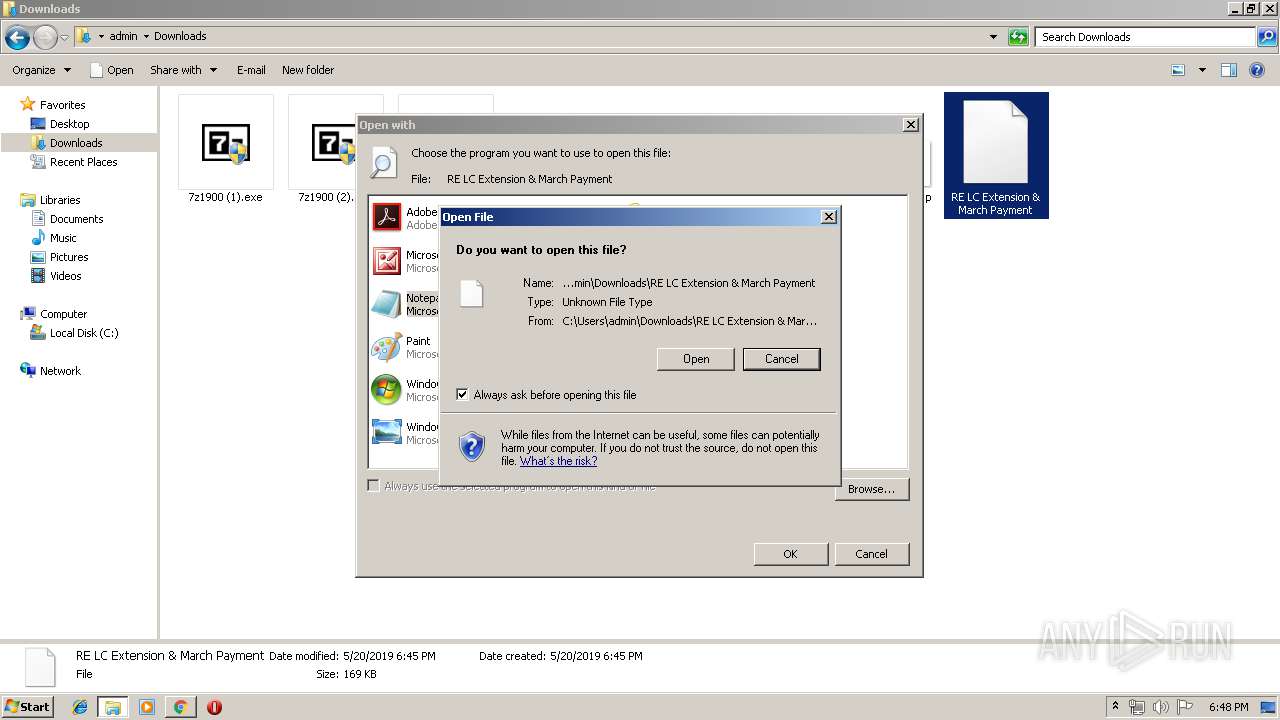
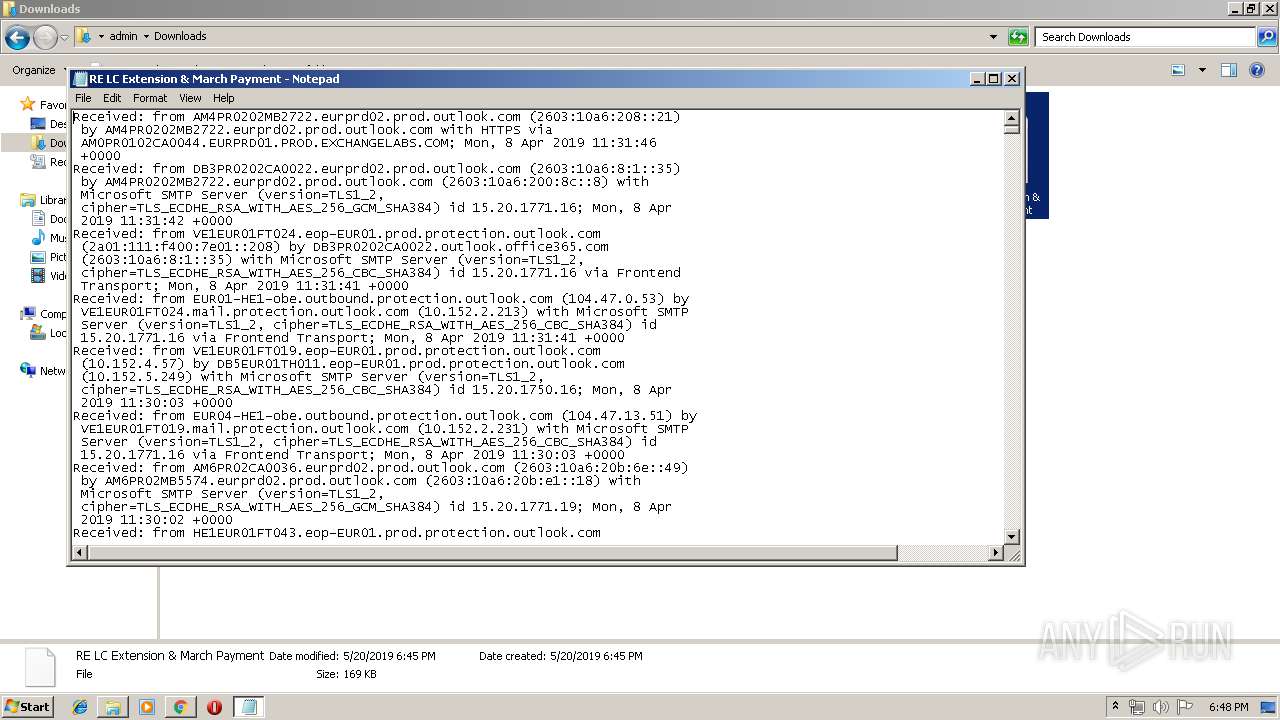
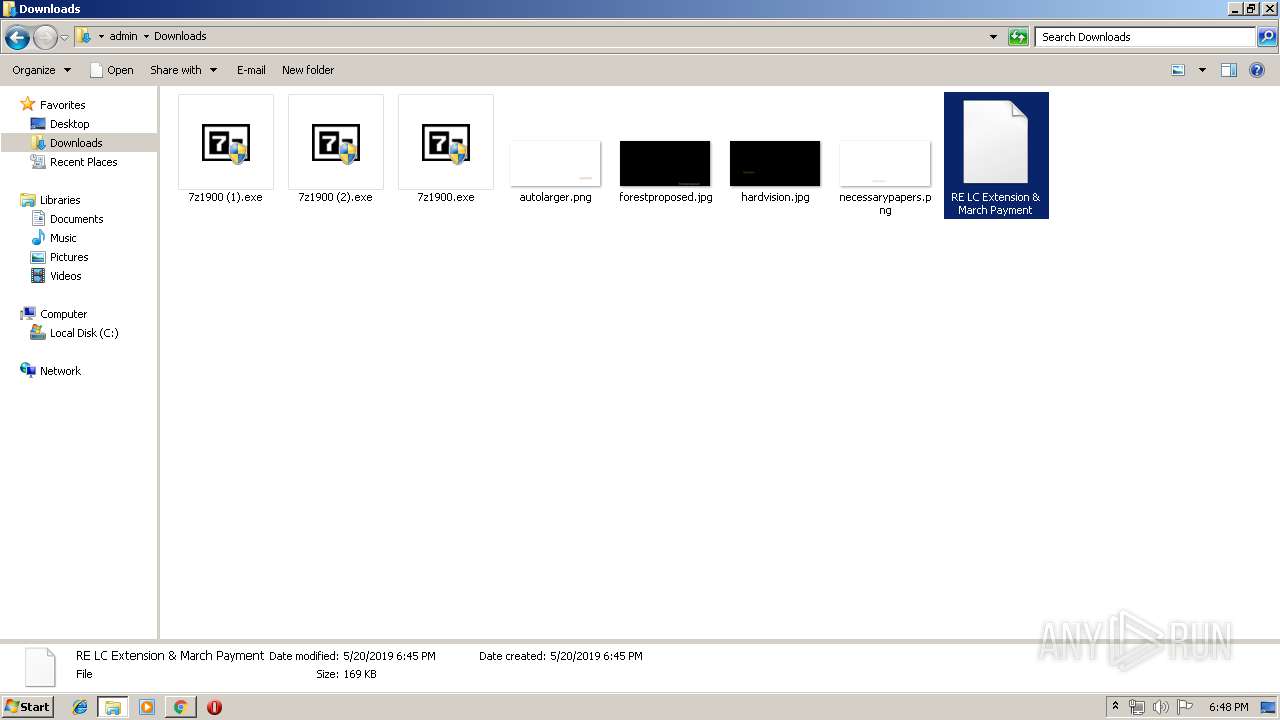
Manual execution by user
- explorer.exe (PID: 3652)
- explorer.exe (PID: 3608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
93
Monitored processes
53
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9465362602845780446 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9465362602845780446 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
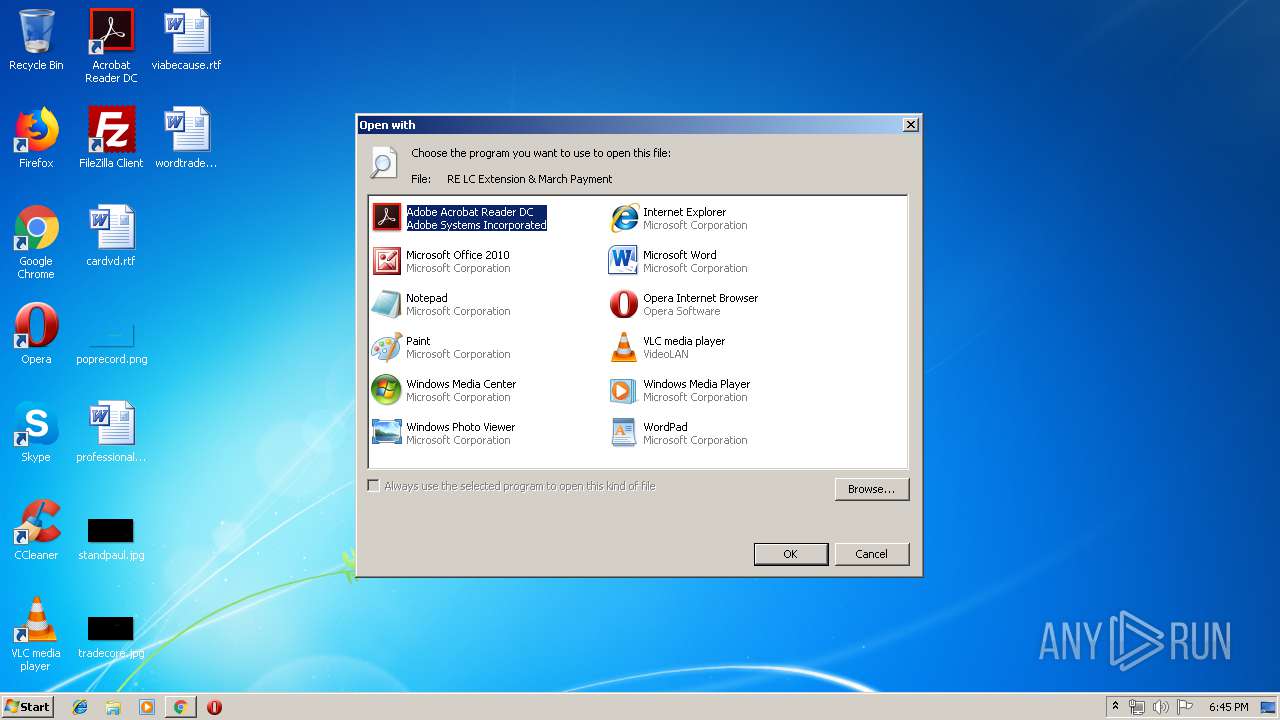
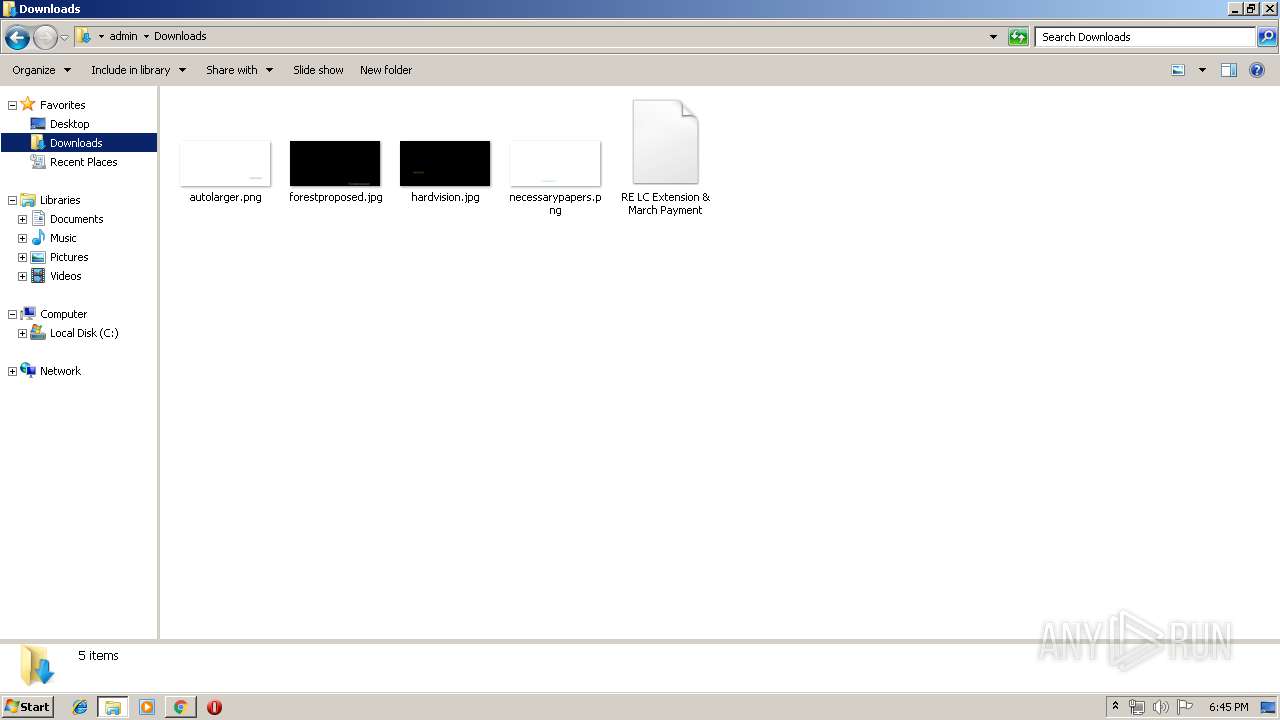
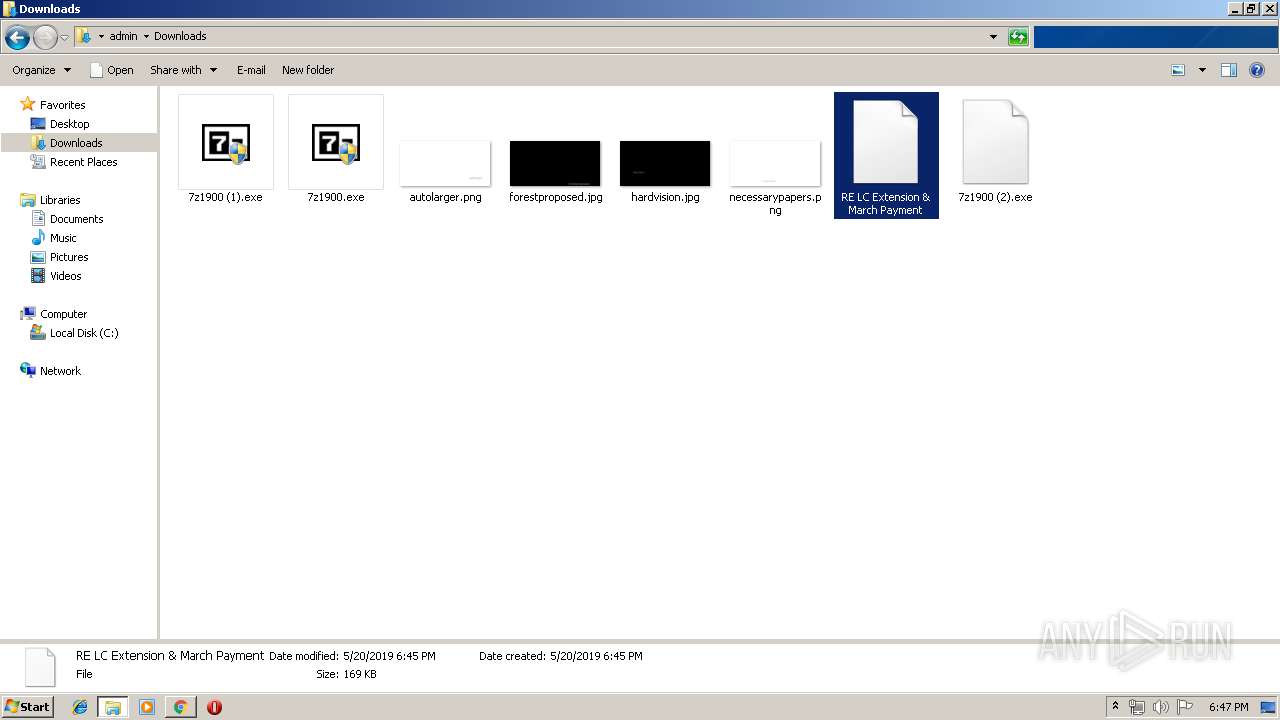
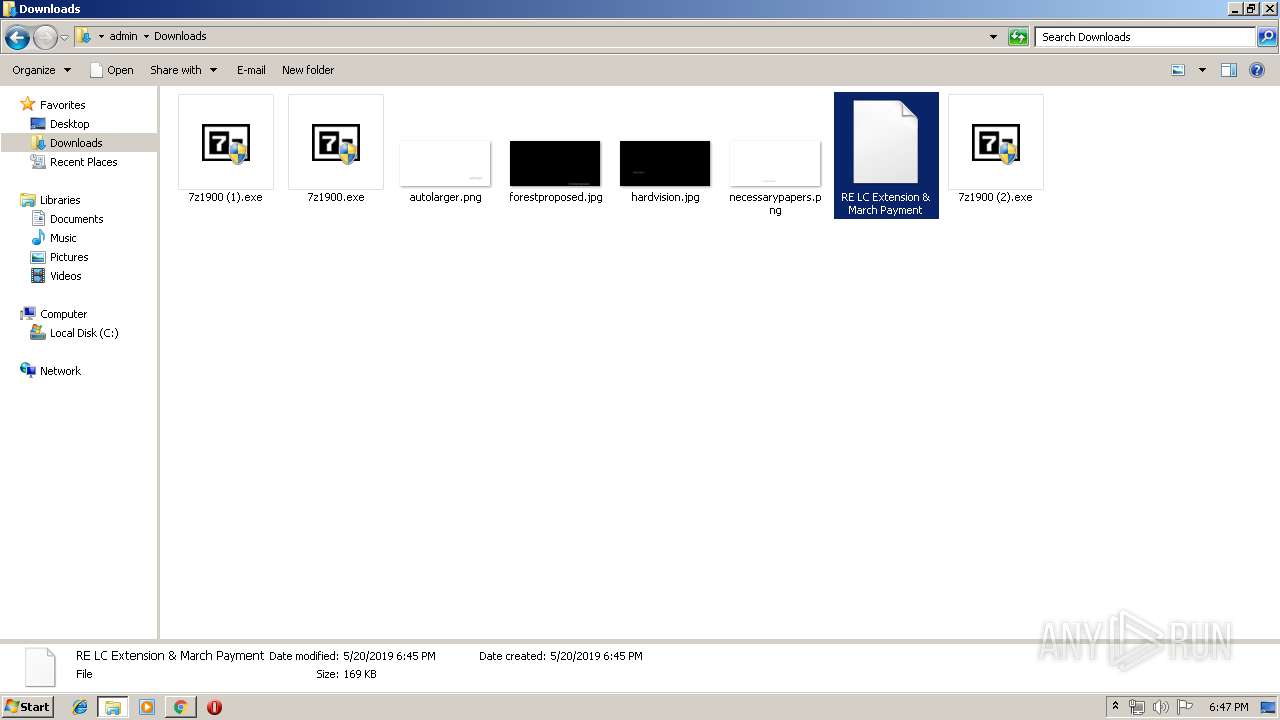
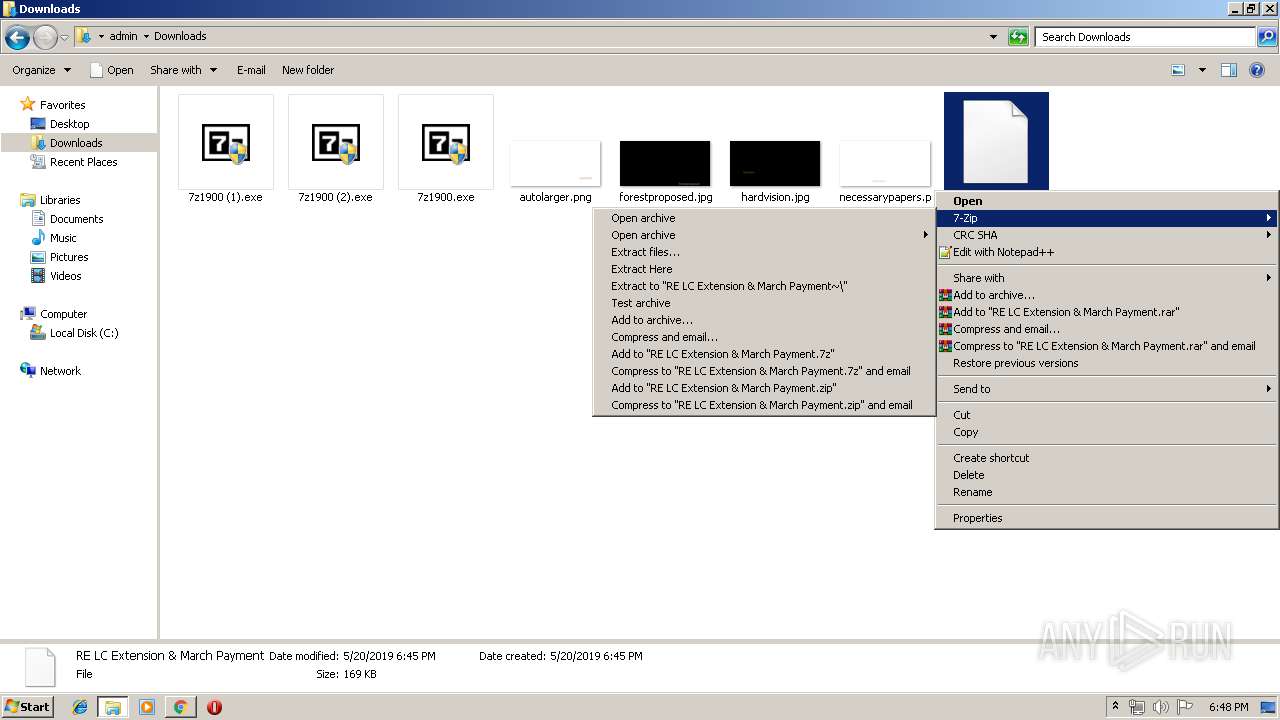
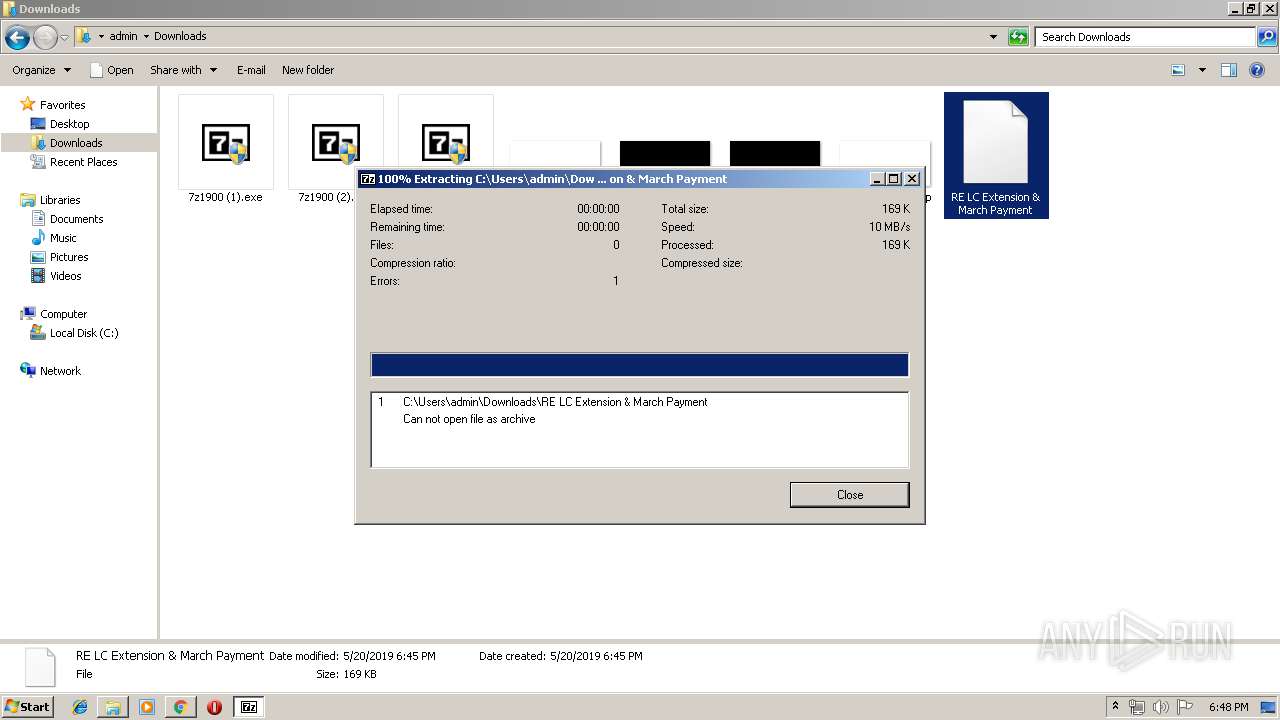
| 800 | "C:\Program Files\7-Zip\7zG.exe" x -o"C:\Users\admin\Downloads\RE LC Extension & March Payment~\" -spe -an -ai#7zMap12840:116:7zEvent29739 | C:\Program Files\7-Zip\7zG.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip GUI Exit code: 2 Version: 19.00 Modules
| |||||||||||||||
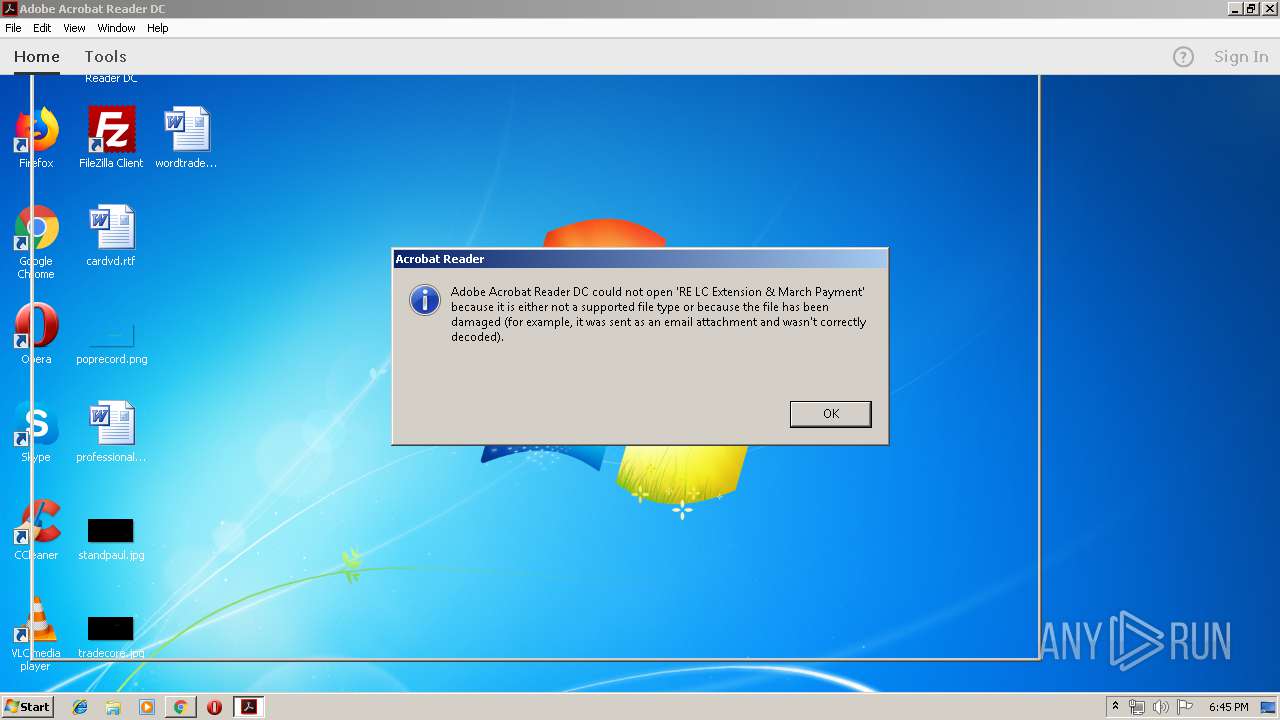
| 828 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\Downloads\RE LC Extension & March Payment" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 840 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 932 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\Downloads\RE LC Extension & March Payment" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=534532459638767326 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=534532459638767326 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2776296777326200985 --mojo-platform-channel-handle=4076 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13599366768862214688 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13599366768862214688 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7813522863641873469 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7813522863641873469 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2768 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2084685416525805810 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2084685416525805810 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
5 033
Read events
4 316
Write events
707
Delete events
10
Modification events
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2840-13202847849067250 |
Value: 259 | |||
Executable files
14
Suspicious files
262
Text files
330
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\da81ad3d-0ad4-42d4-af9b-1190a0267d60.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
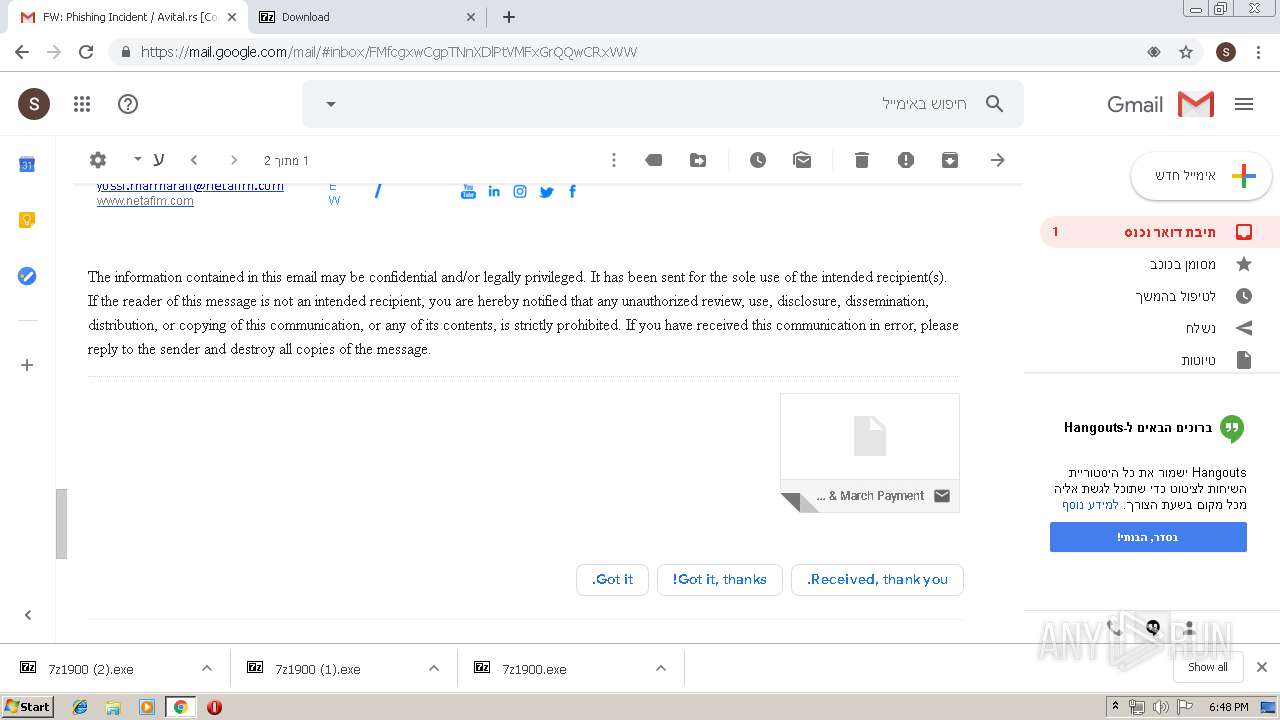
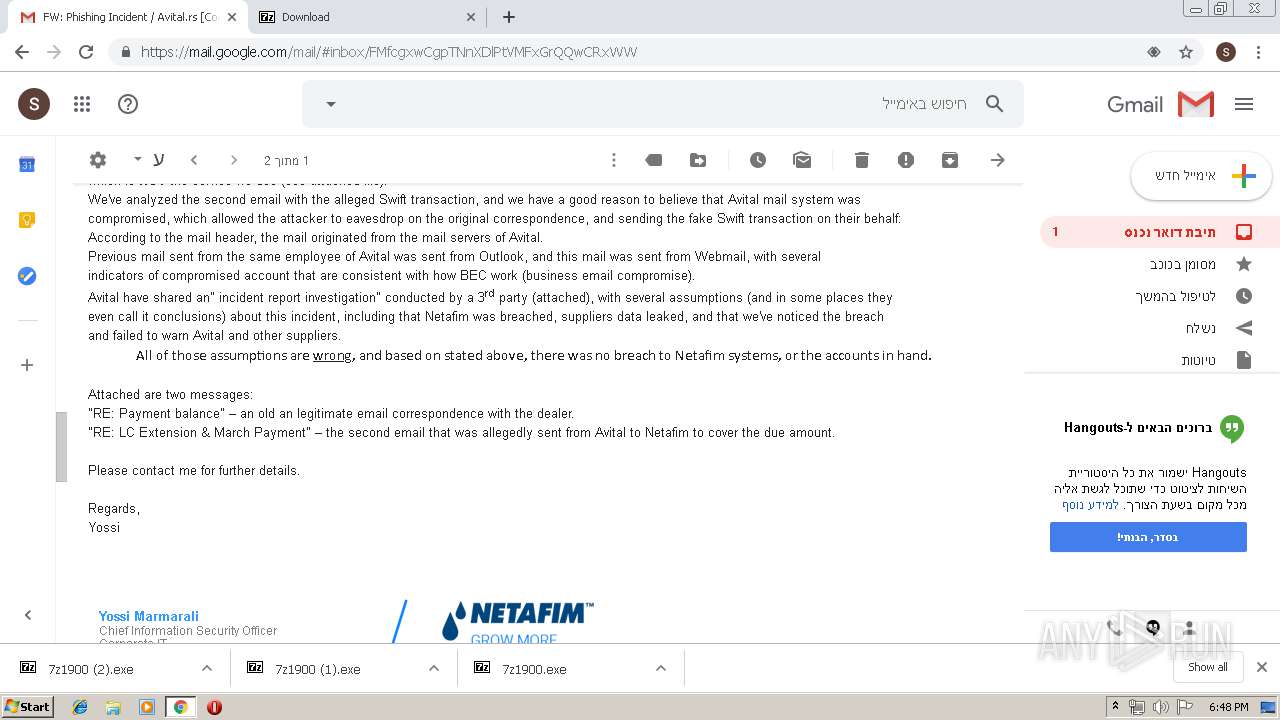
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
65
DNS requests
44
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2840 | chrome.exe | GET | 200 | 173.194.5.234:80 | http://r5---sn-aigzrn7l.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=89.249.73.20&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1558374140&mv=m&pl=25&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2840 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 503 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2840 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
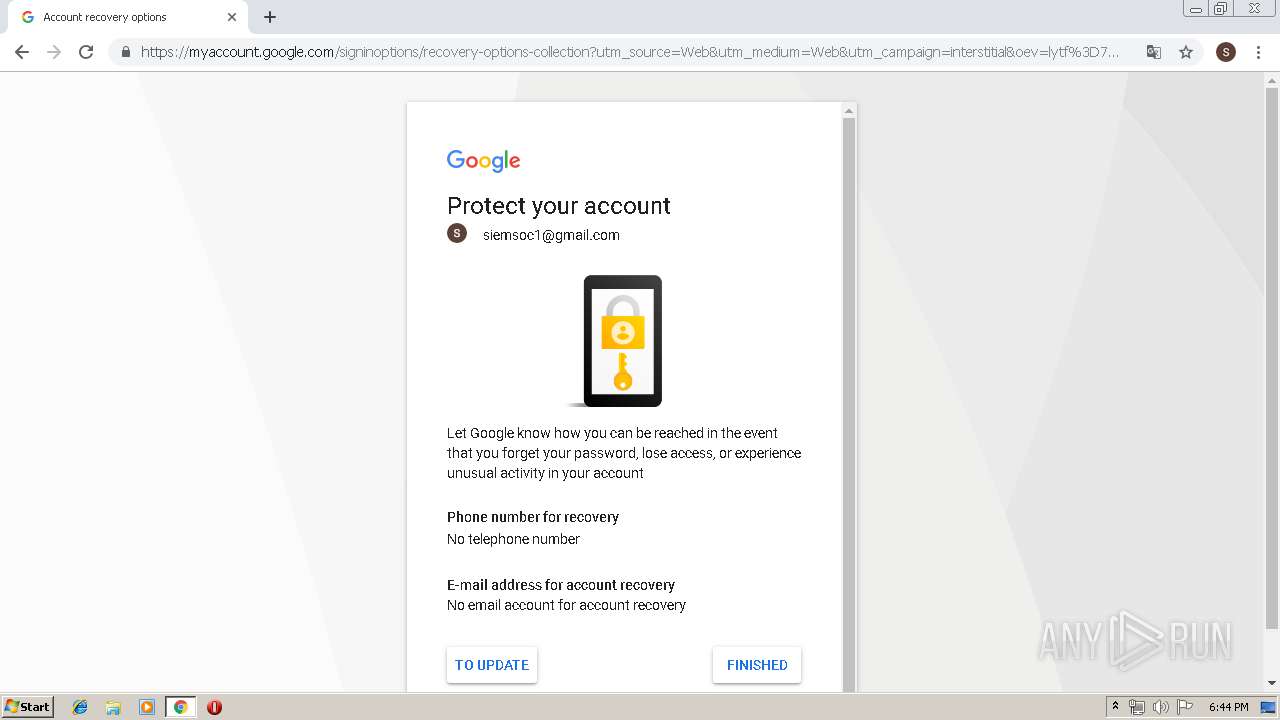
2840 | chrome.exe | 216.58.210.5:443 | gmail.com | Google Inc. | US | whitelisted |
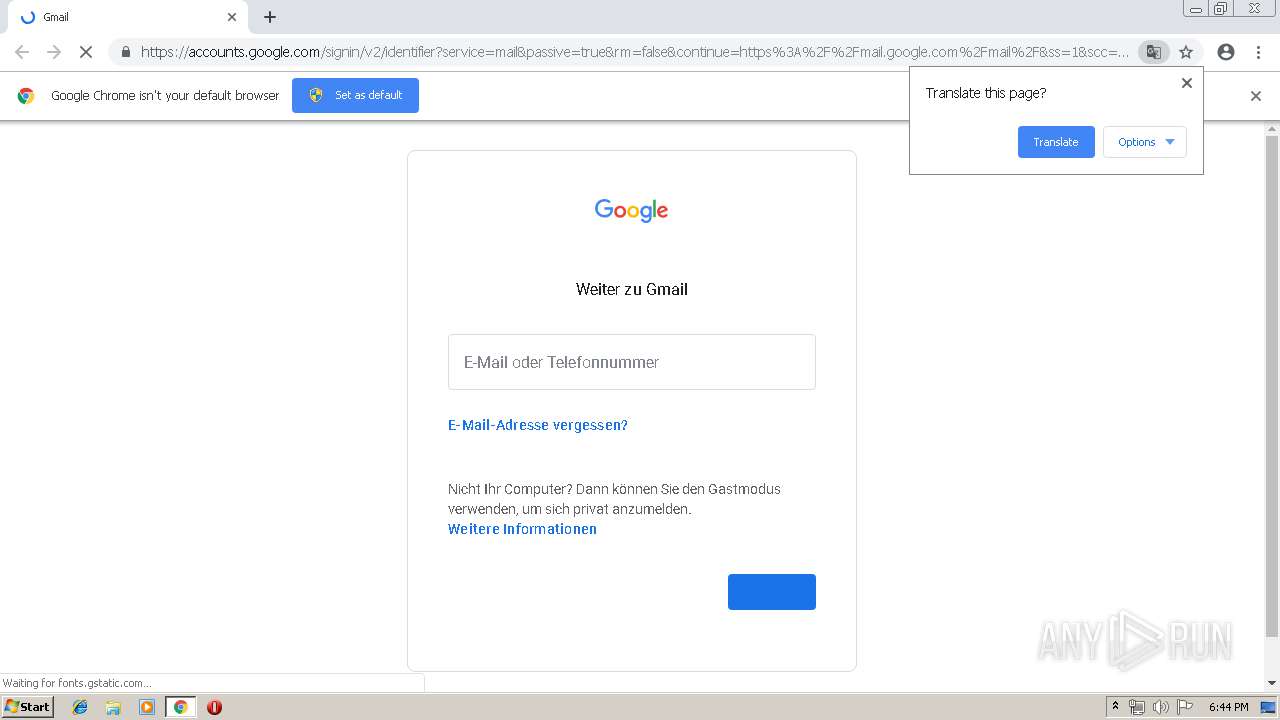
2840 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2840 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
2840 | chrome.exe | 172.217.18.101:443 | mail.google.com | Google Inc. | US | whitelisted |
2840 | chrome.exe | 172.217.22.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2840 | chrome.exe | 172.217.16.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
2840 | chrome.exe | 172.217.22.10:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
2840 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2840 | chrome.exe | 216.58.206.14:443 | accounts.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
gmail.com |
| shared |
accounts.google.com |
| shared |
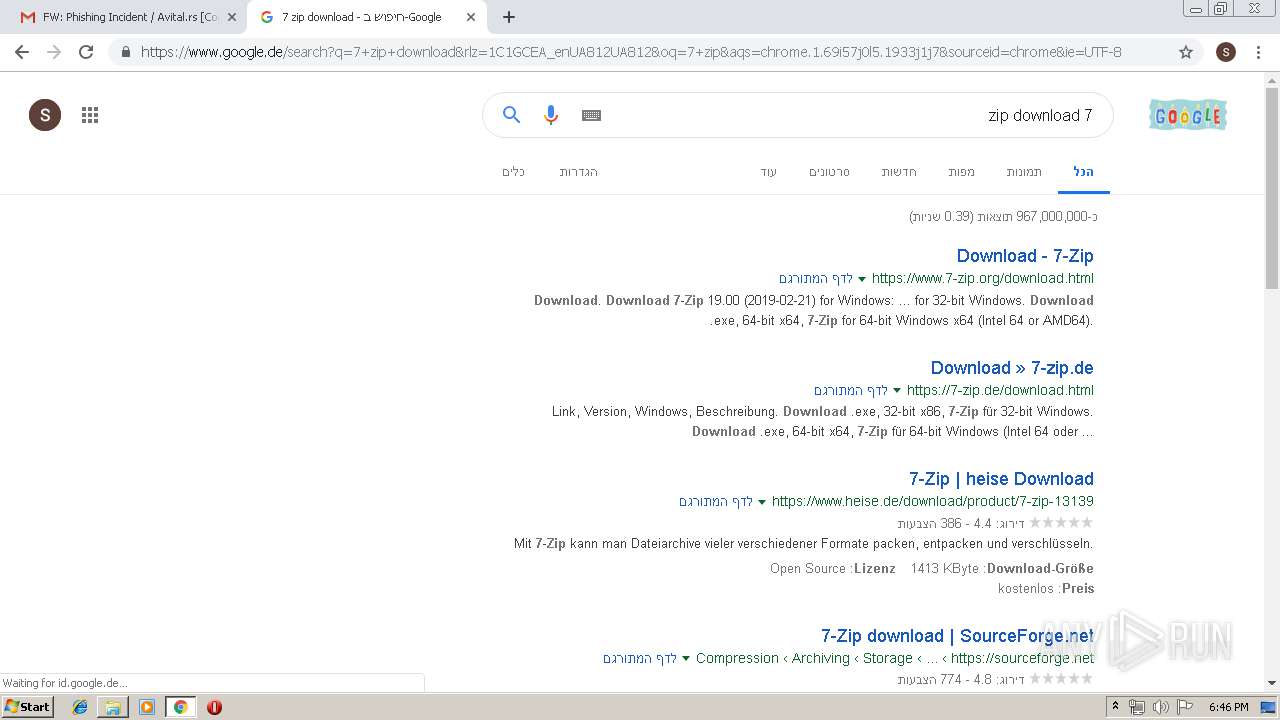
www.google.com |
| malicious |
mail.google.com |
| shared |
fonts.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
accounts.youtube.com |
| whitelisted |