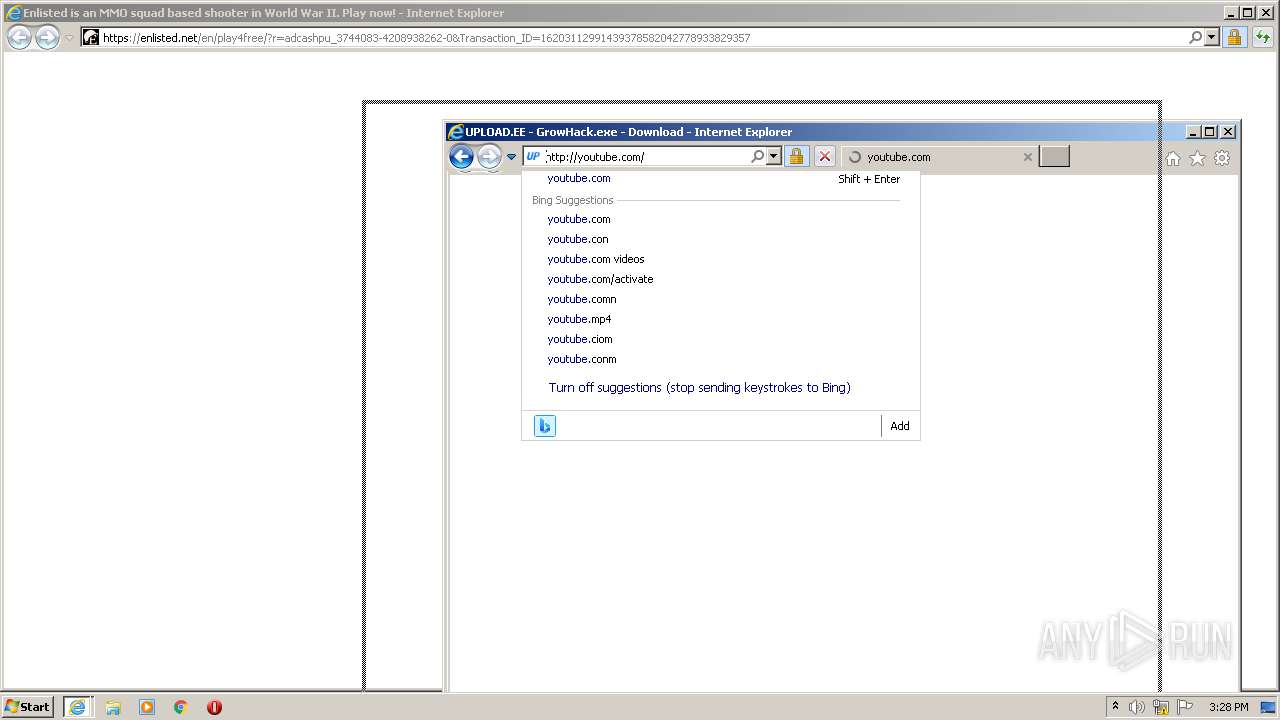
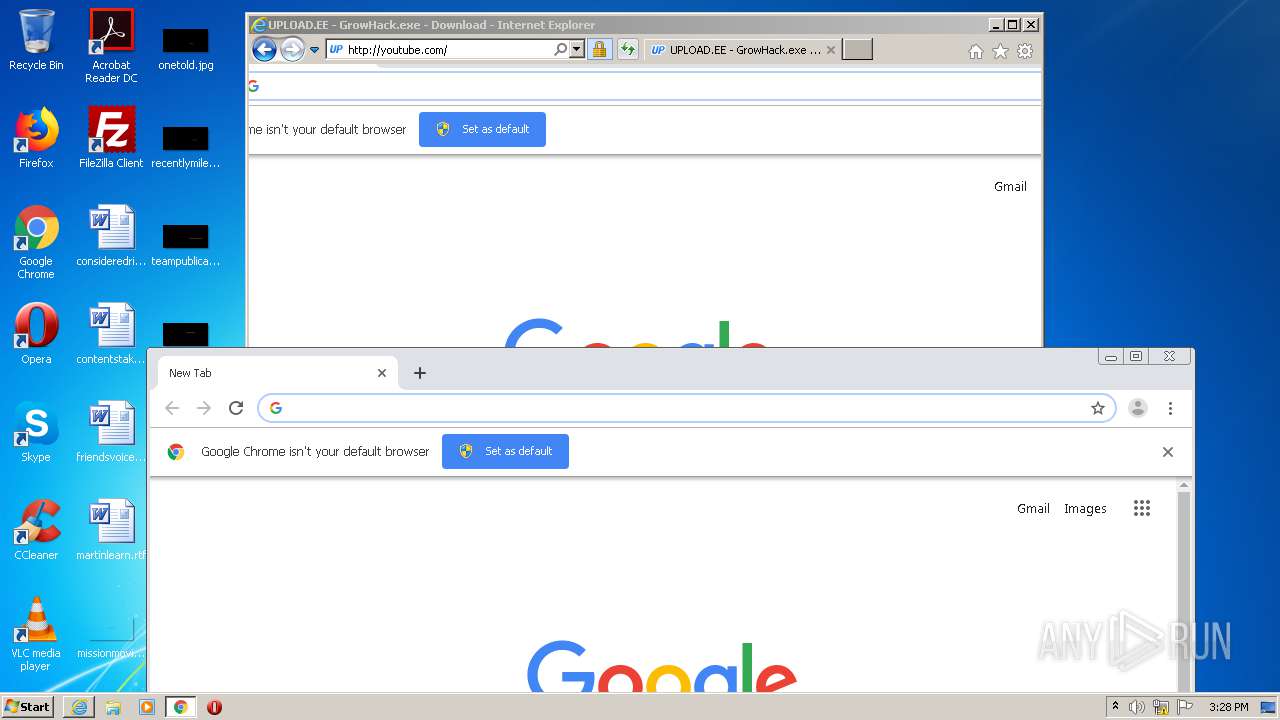
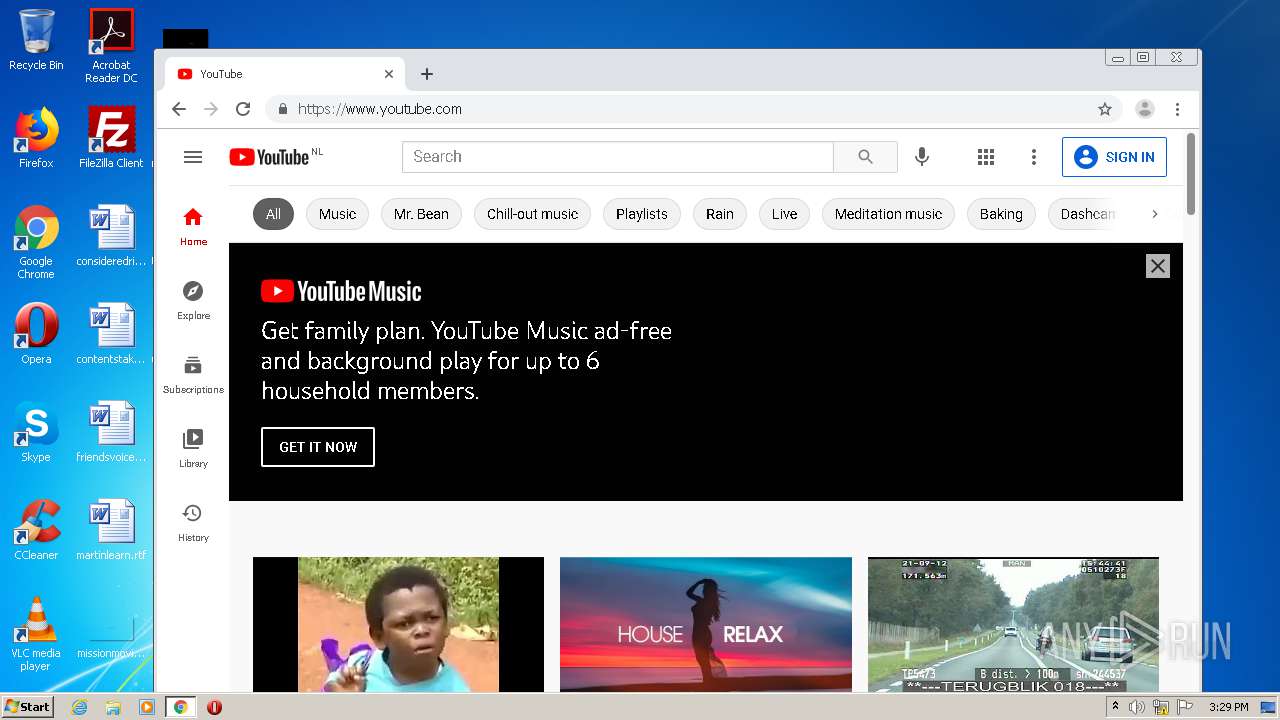
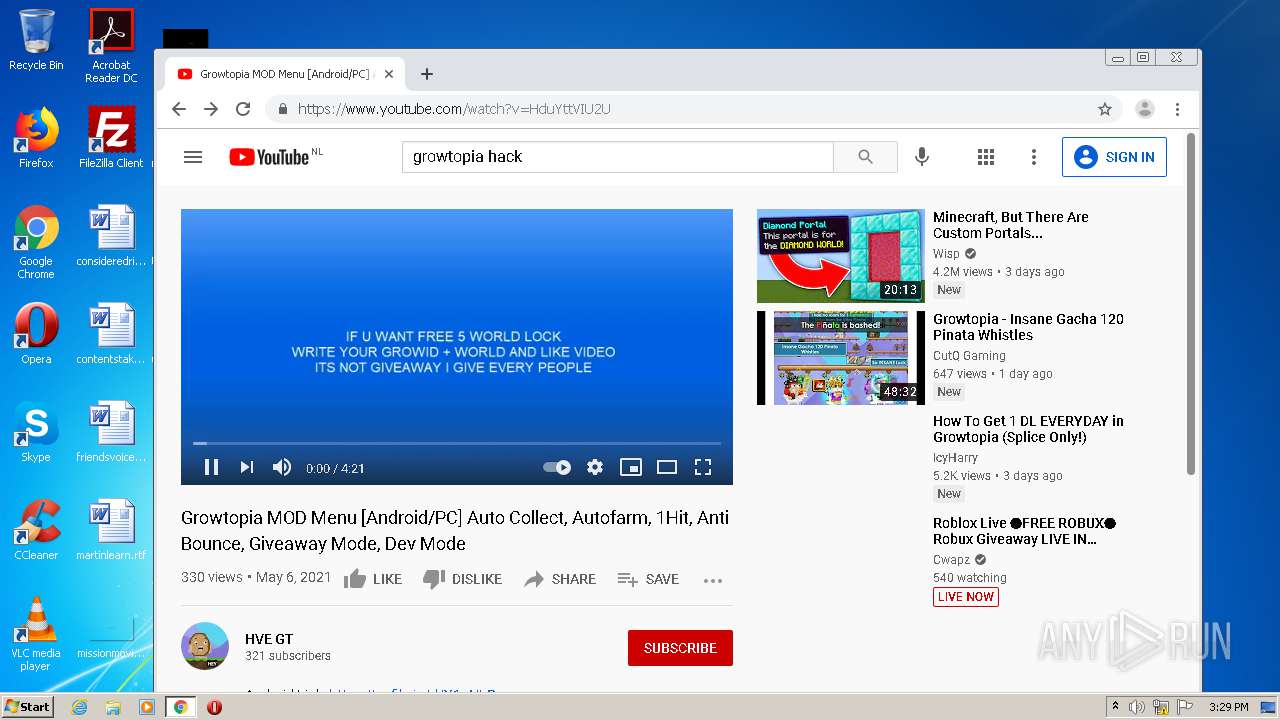
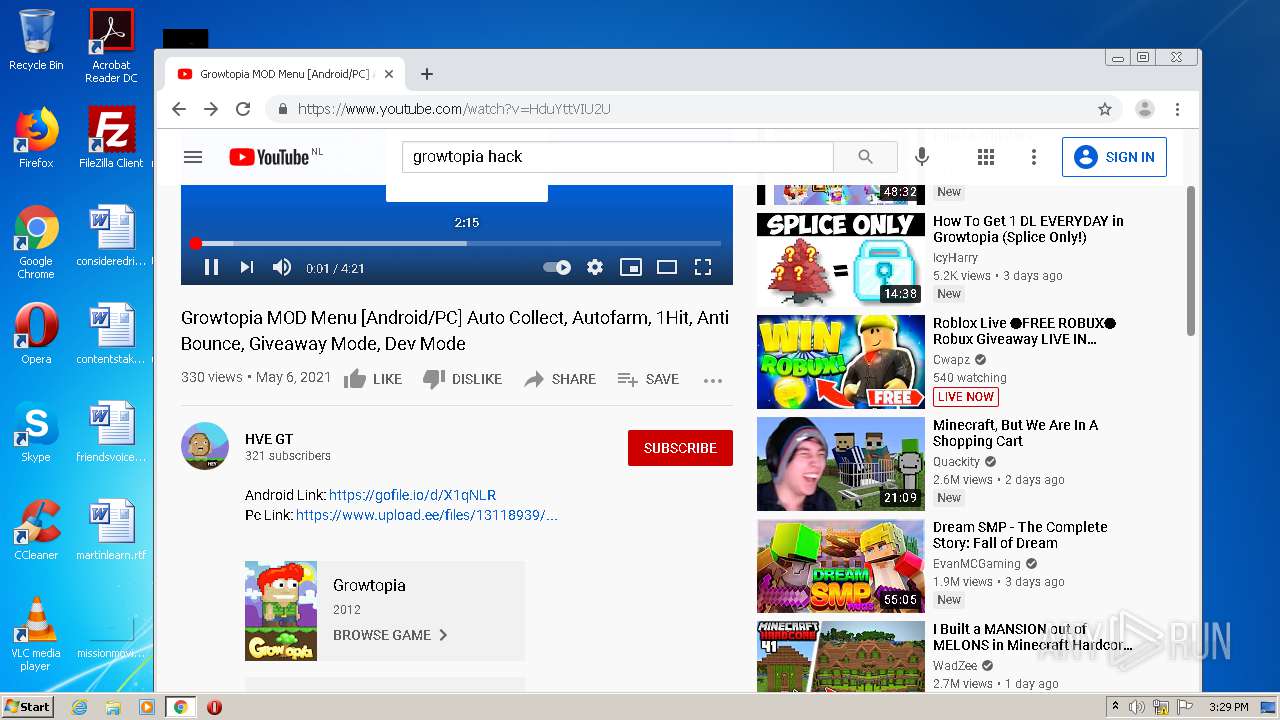
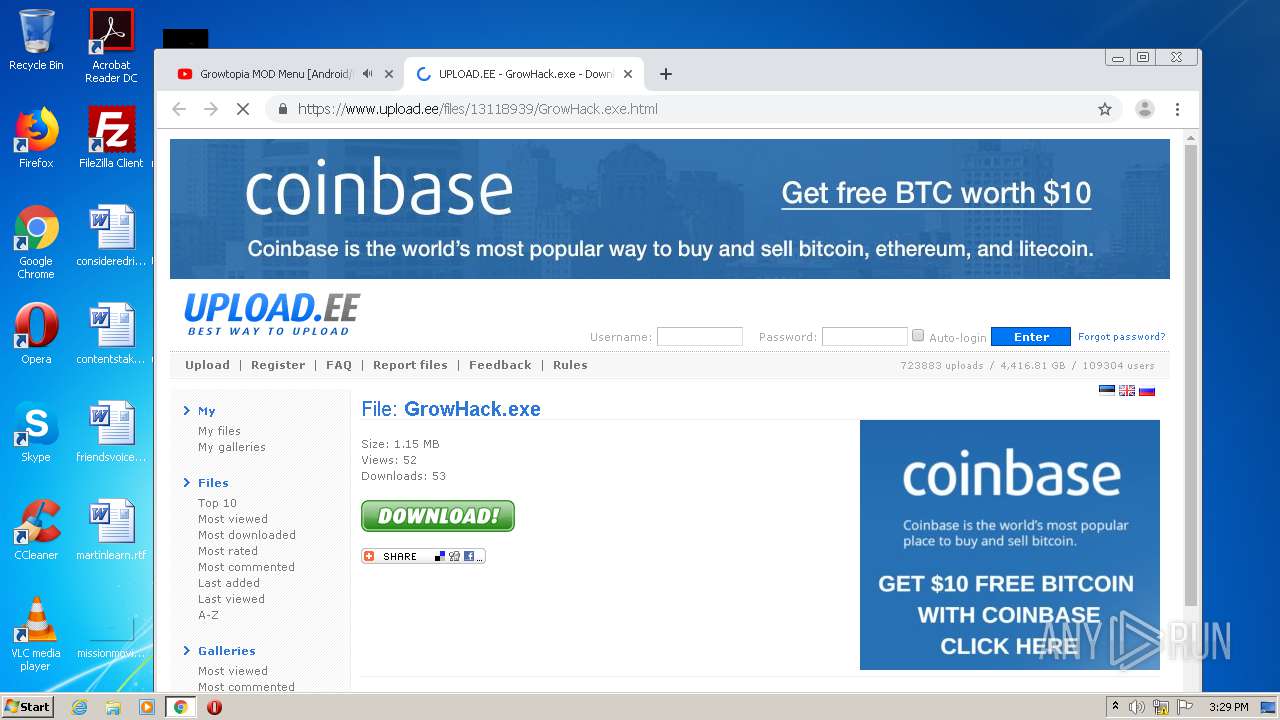
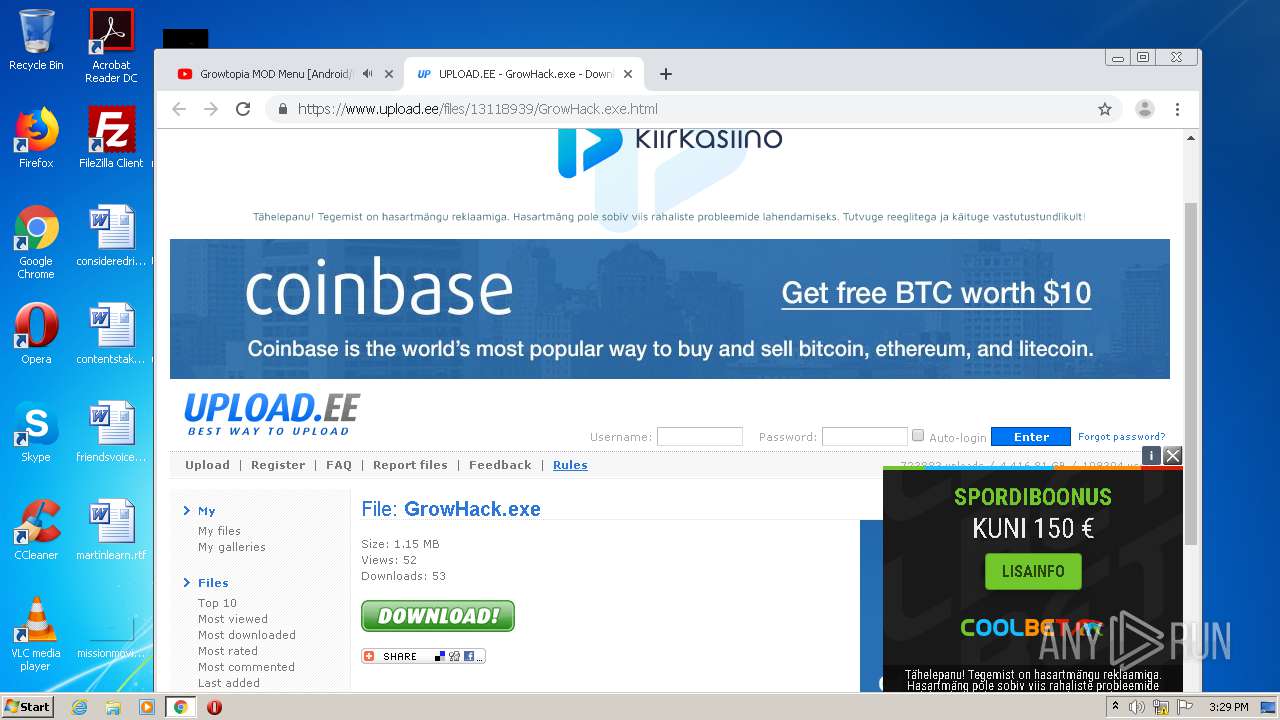
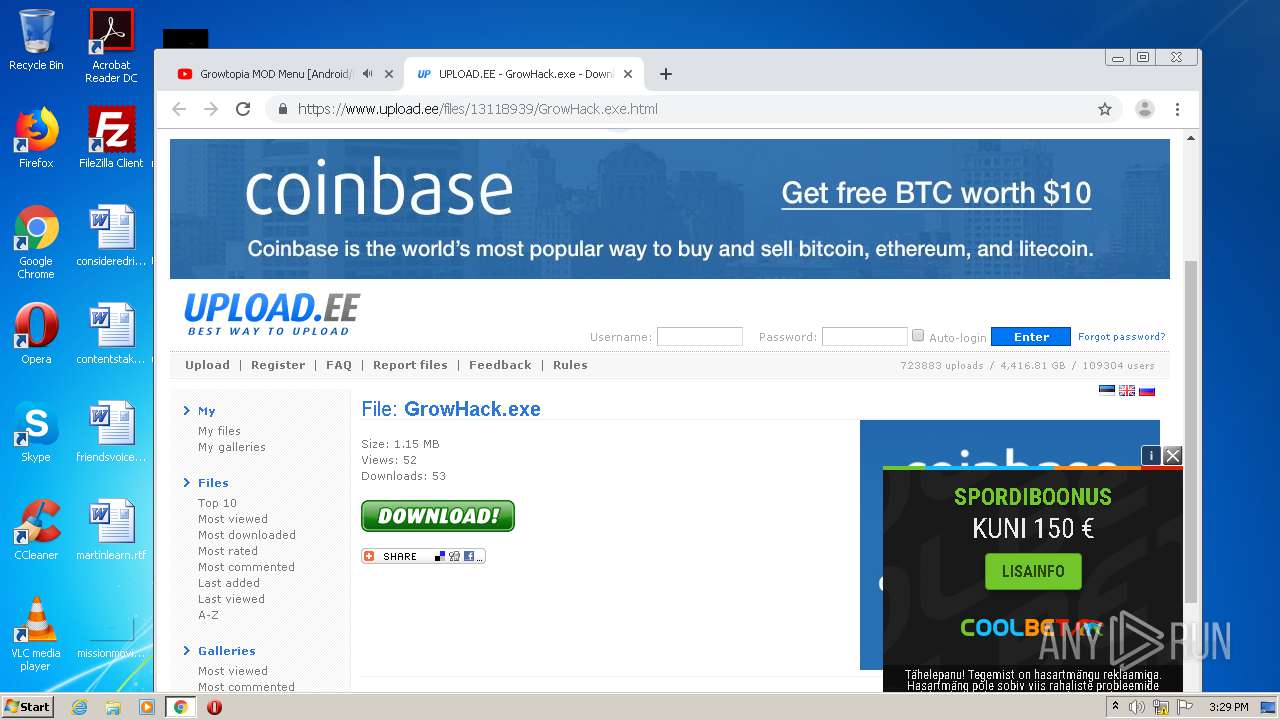
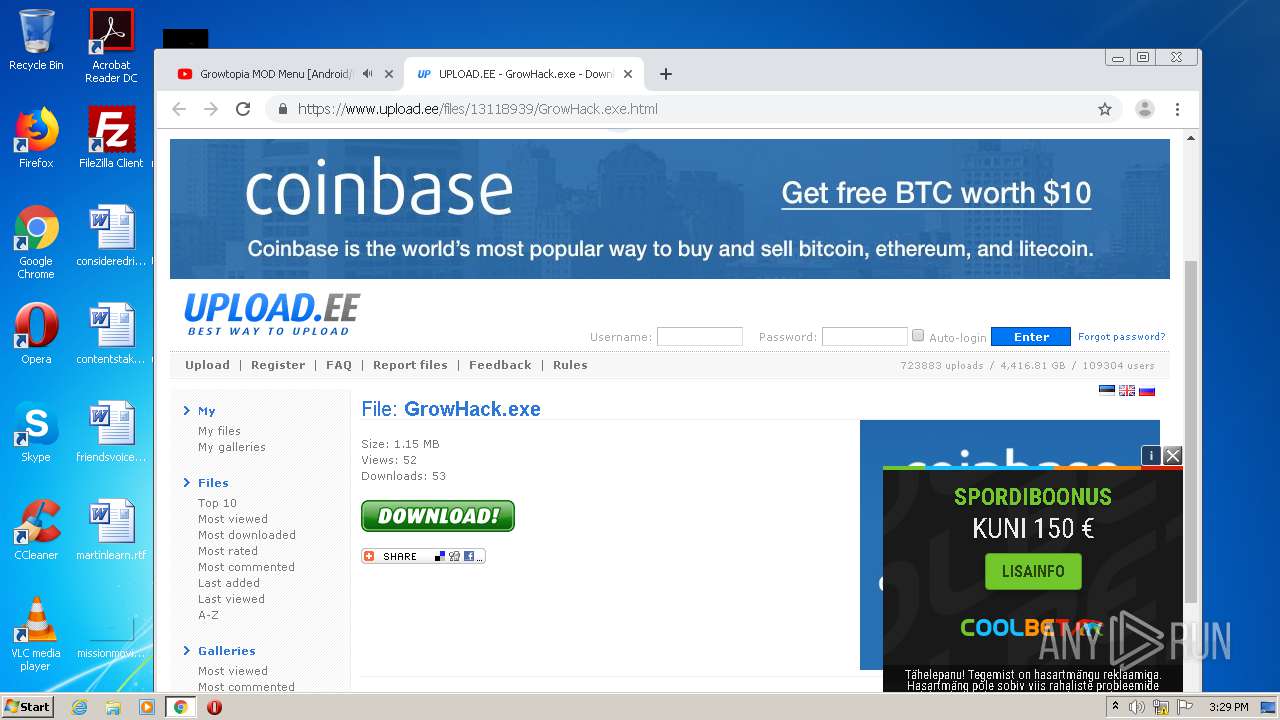
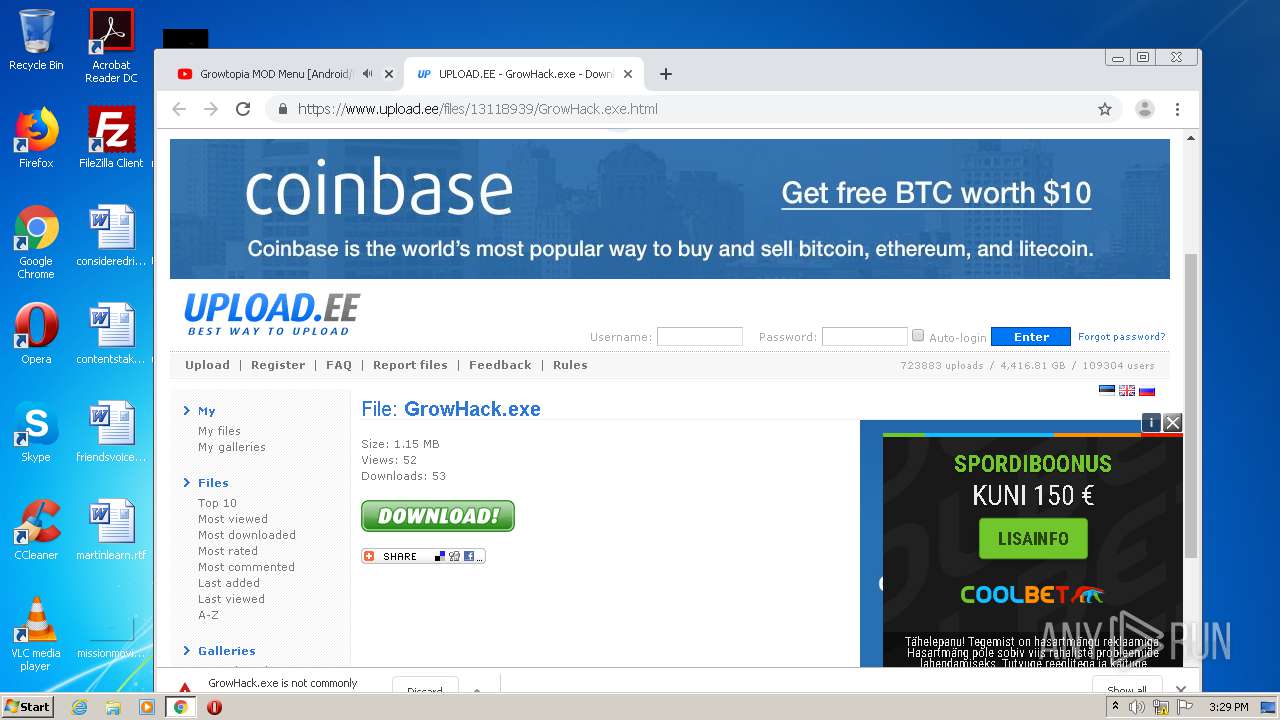
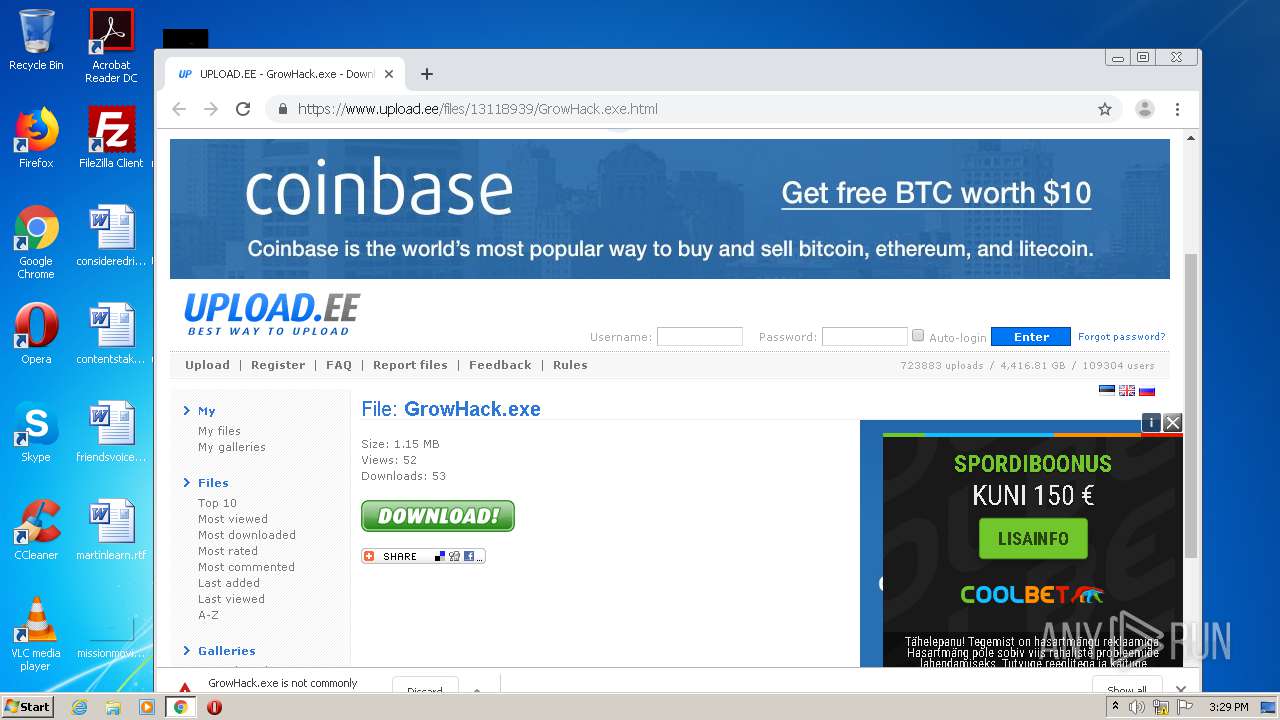
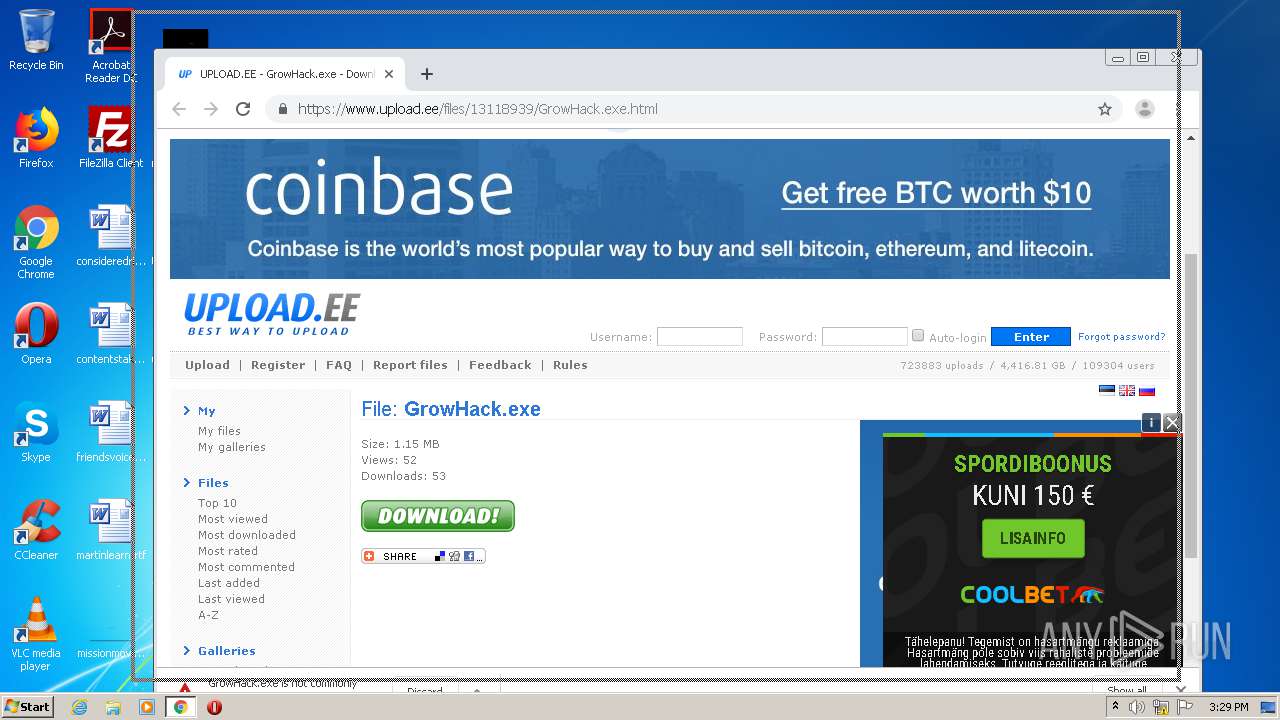
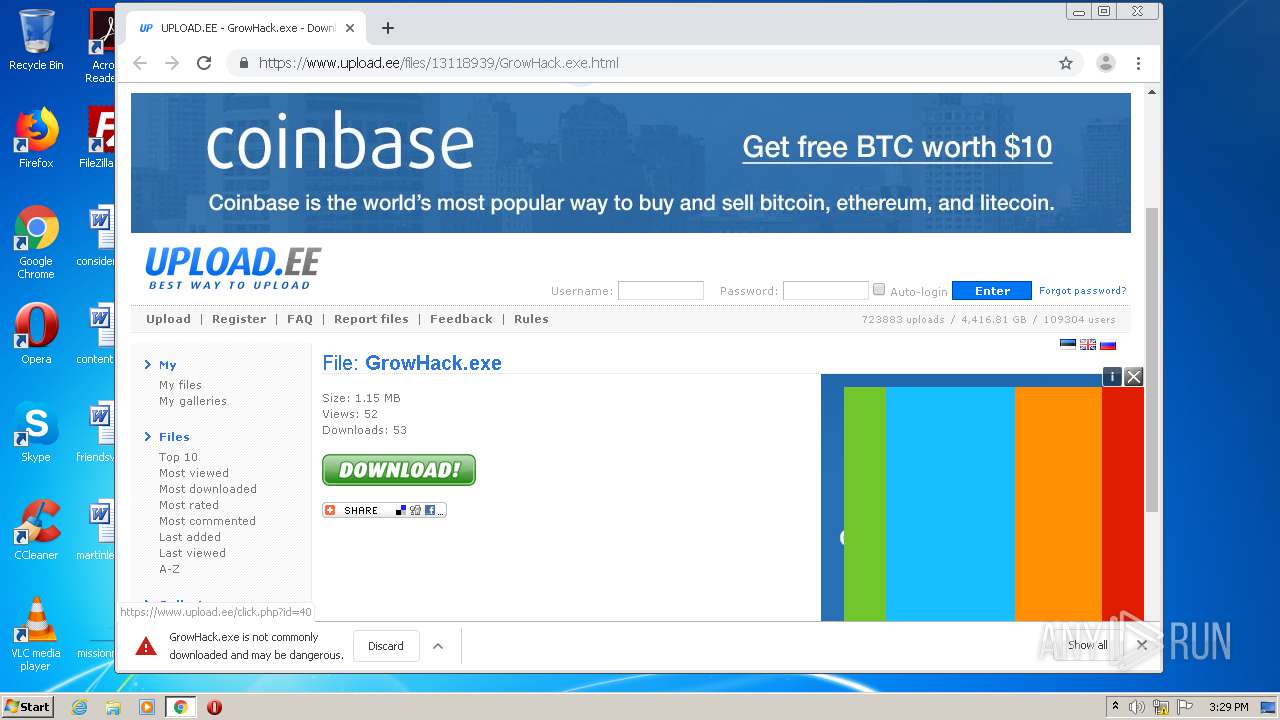
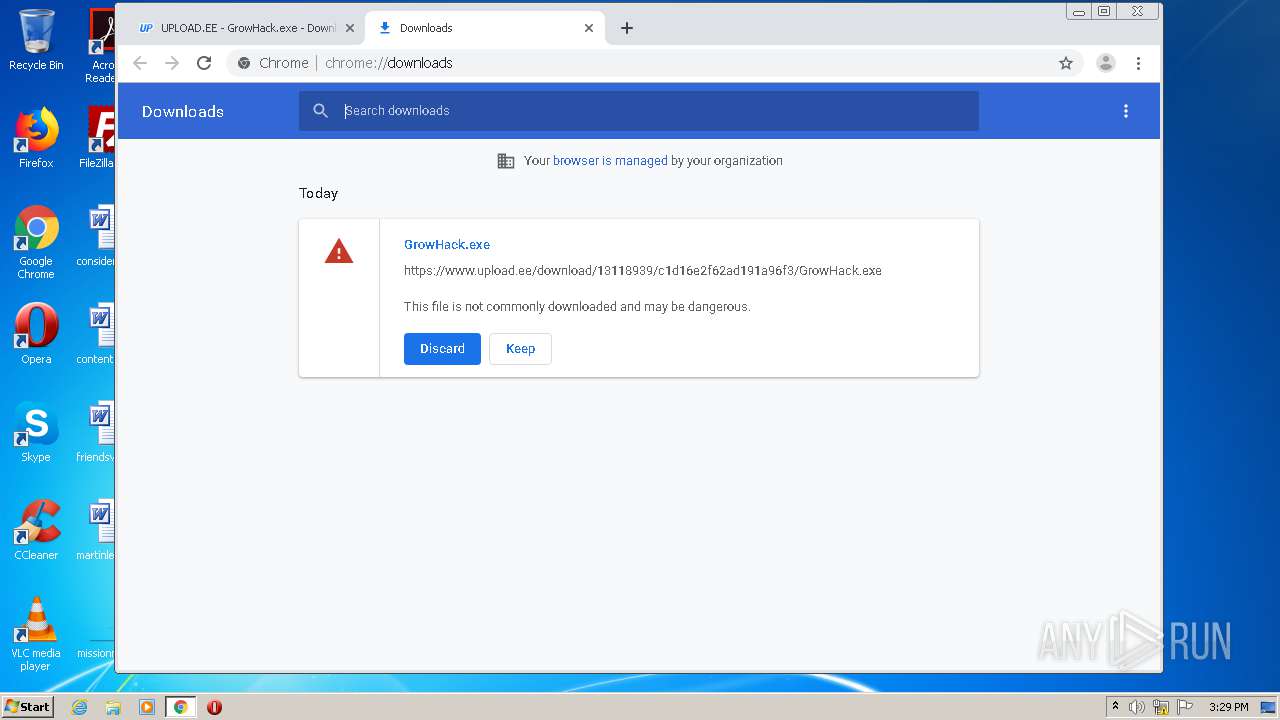
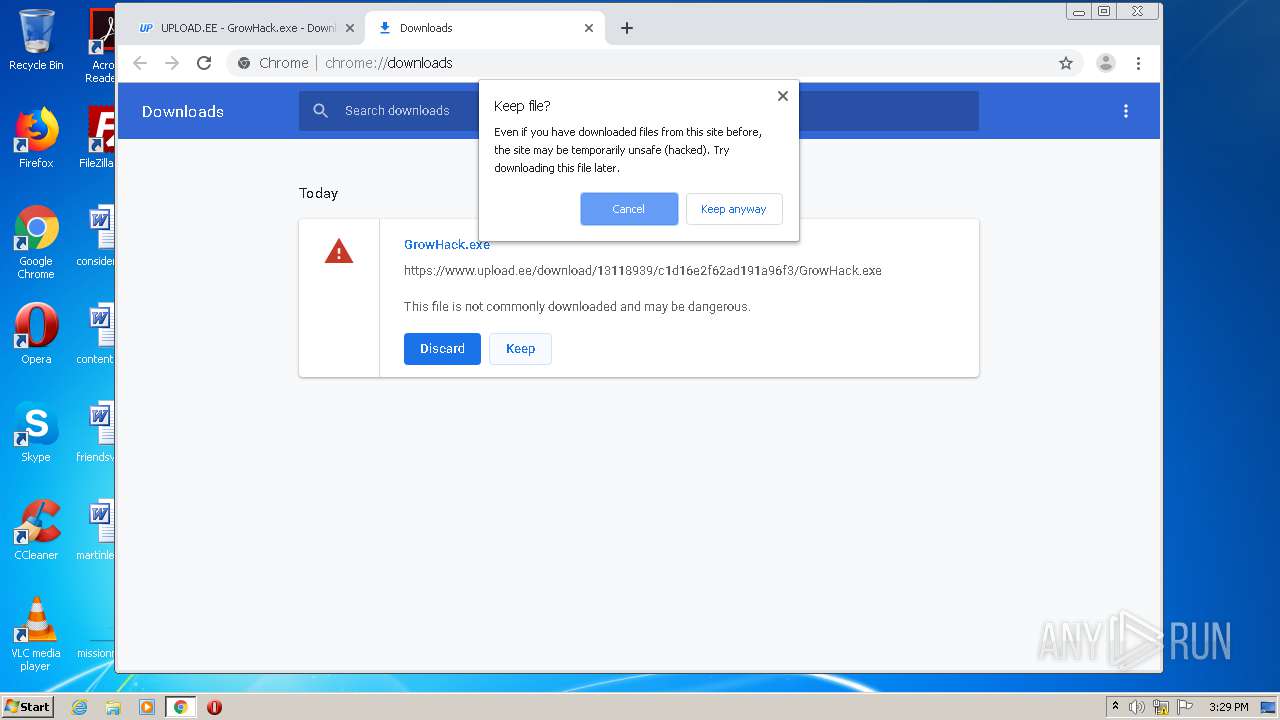
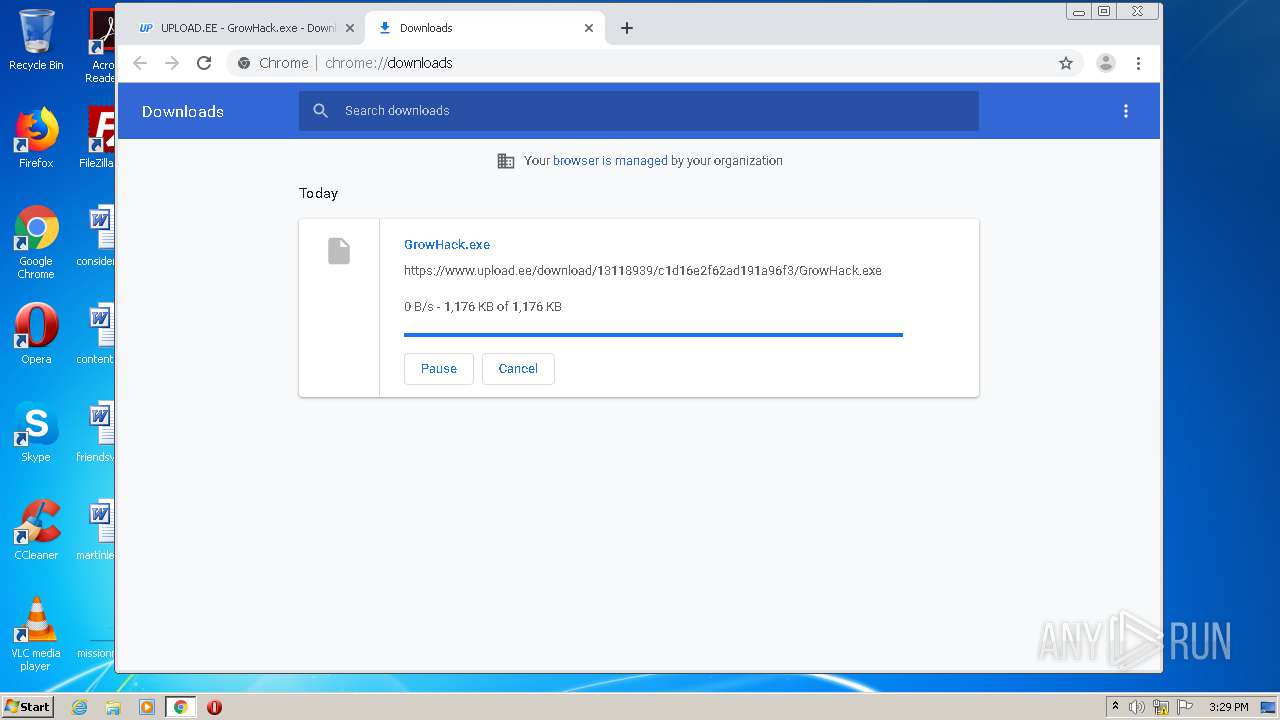
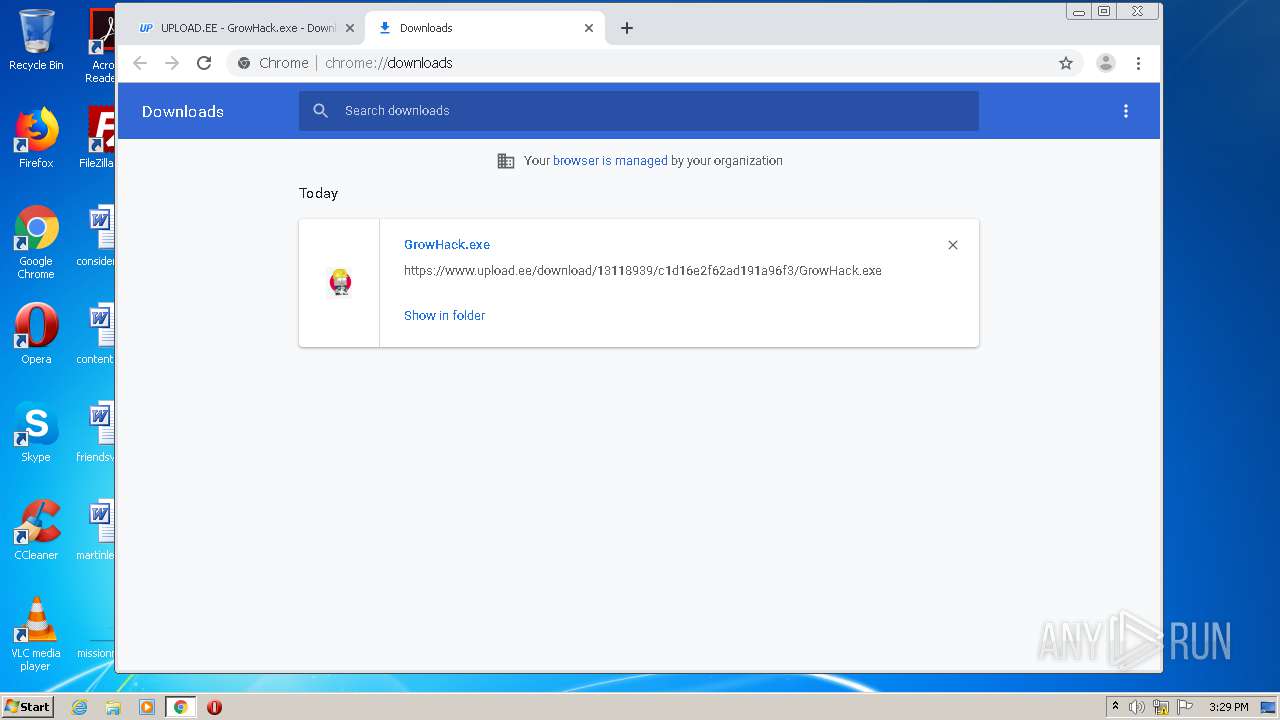
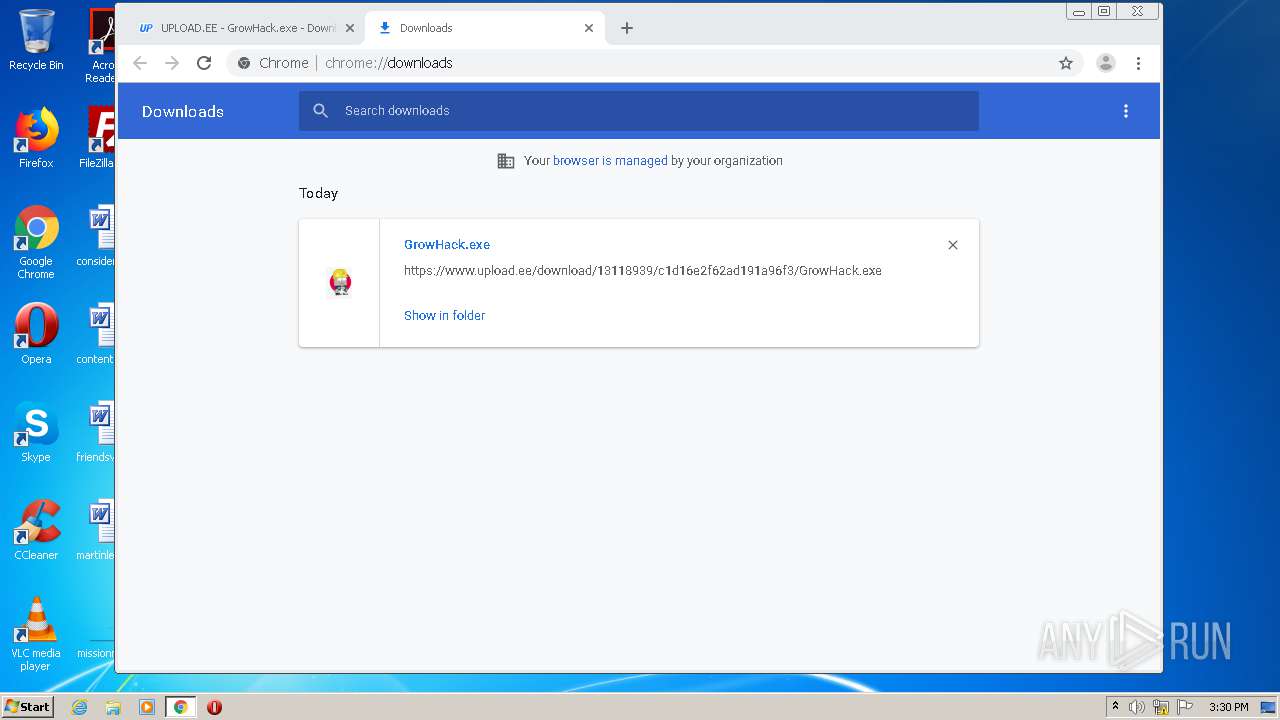
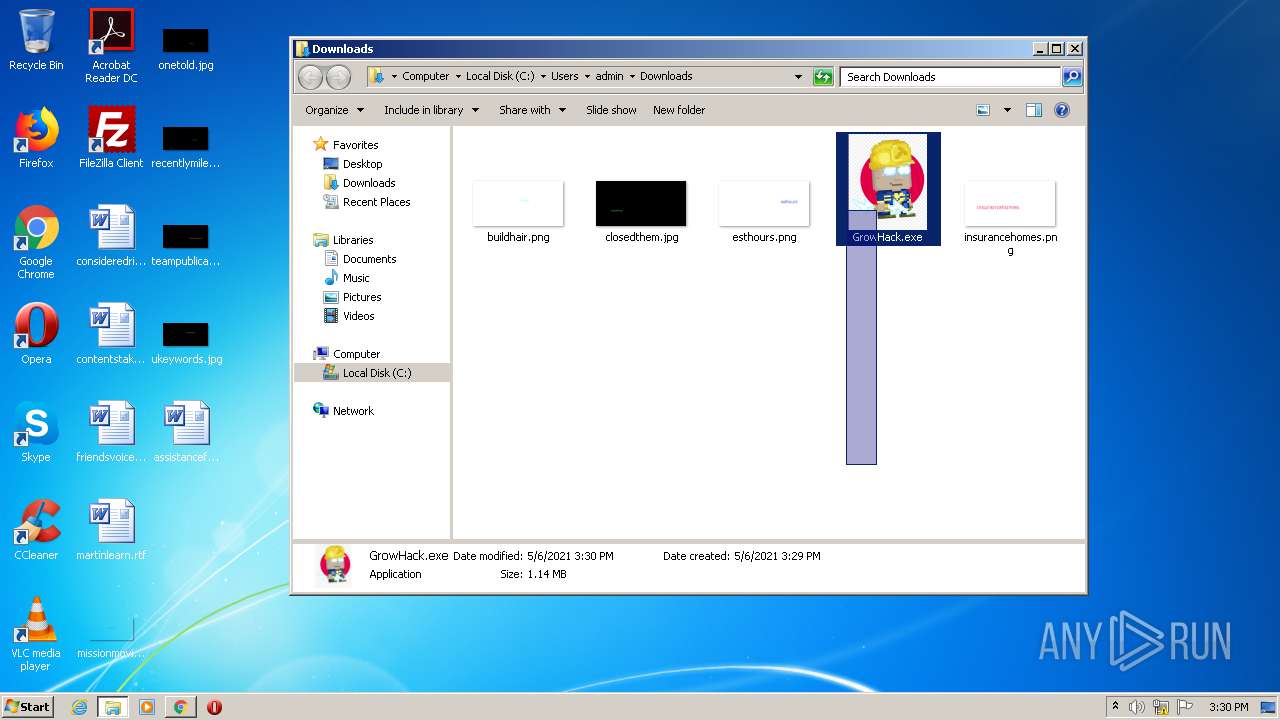
| URL: | https://www.upload.ee/files/13118939/GrowHack.exe.html |
| Full analysis: | https://app.any.run/tasks/0ff00c5b-06f4-45d4-850c-9ebd3034b699 |
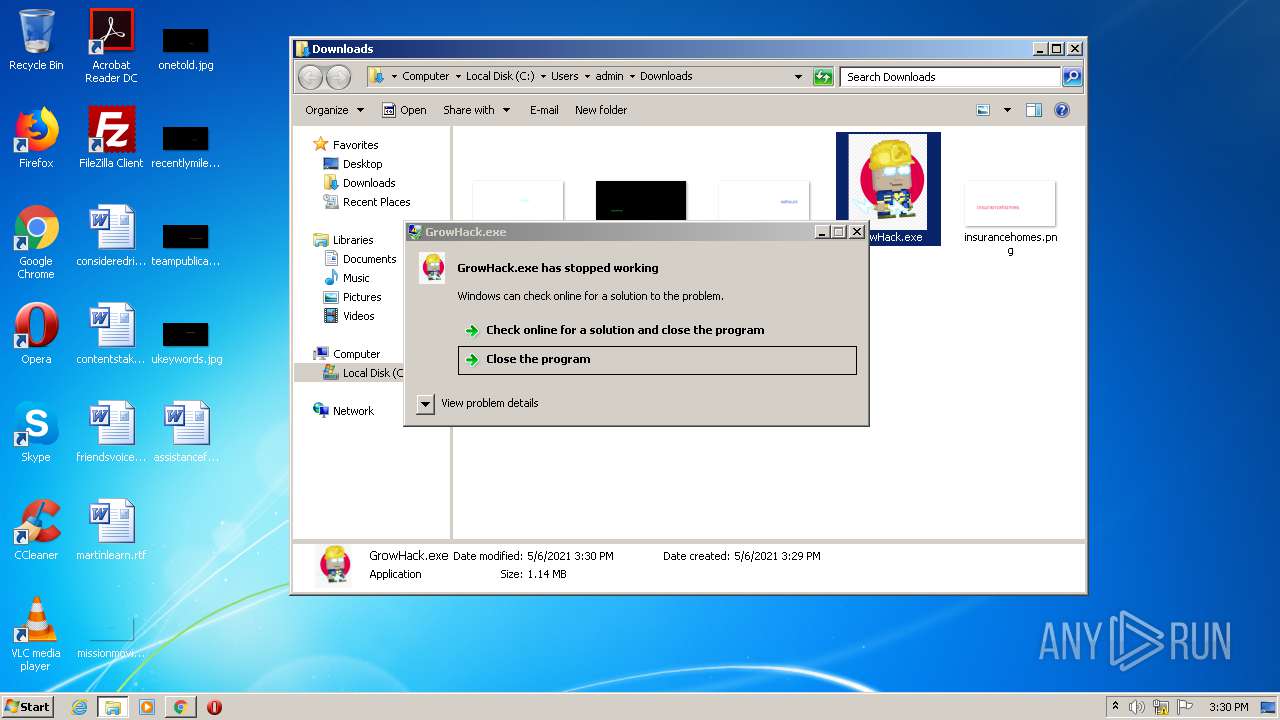
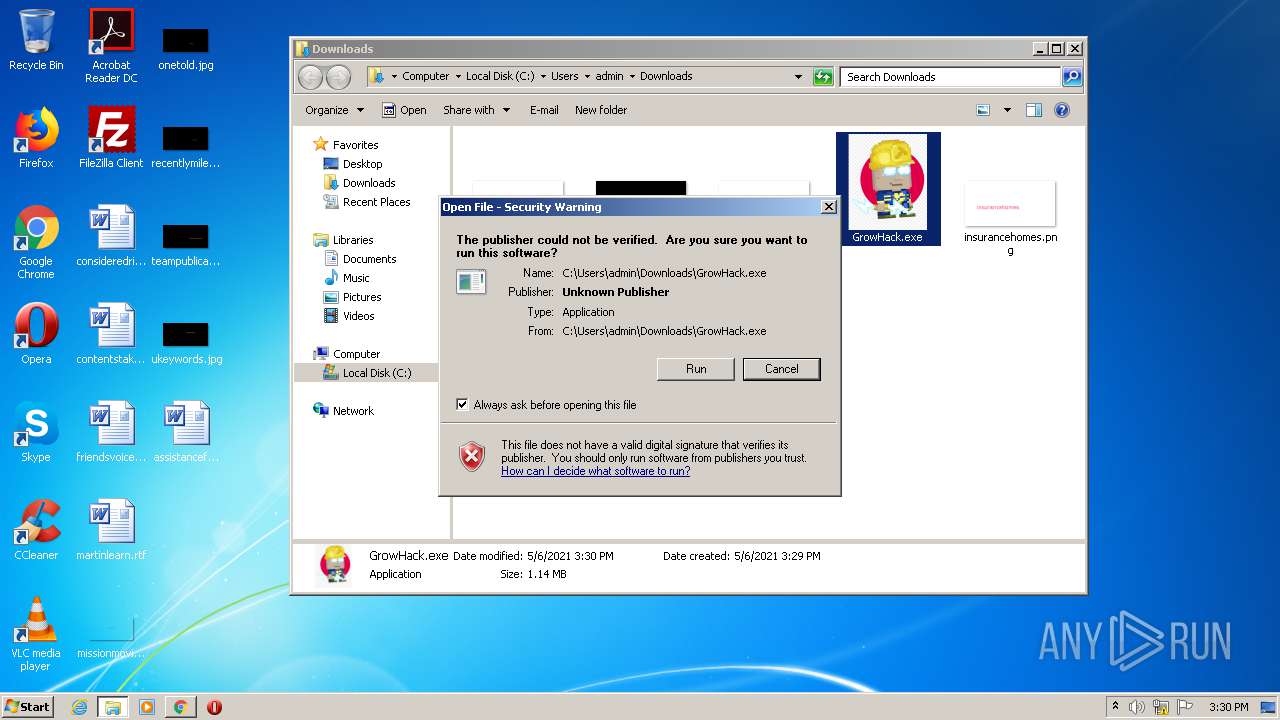
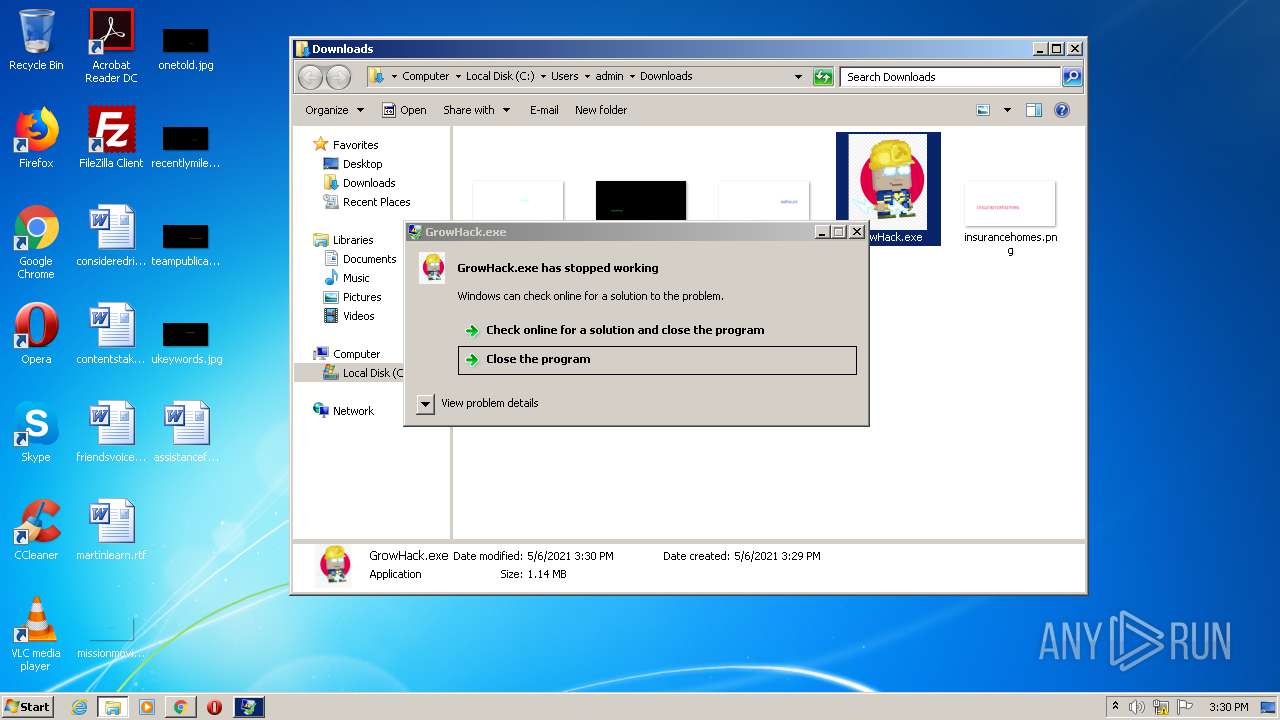
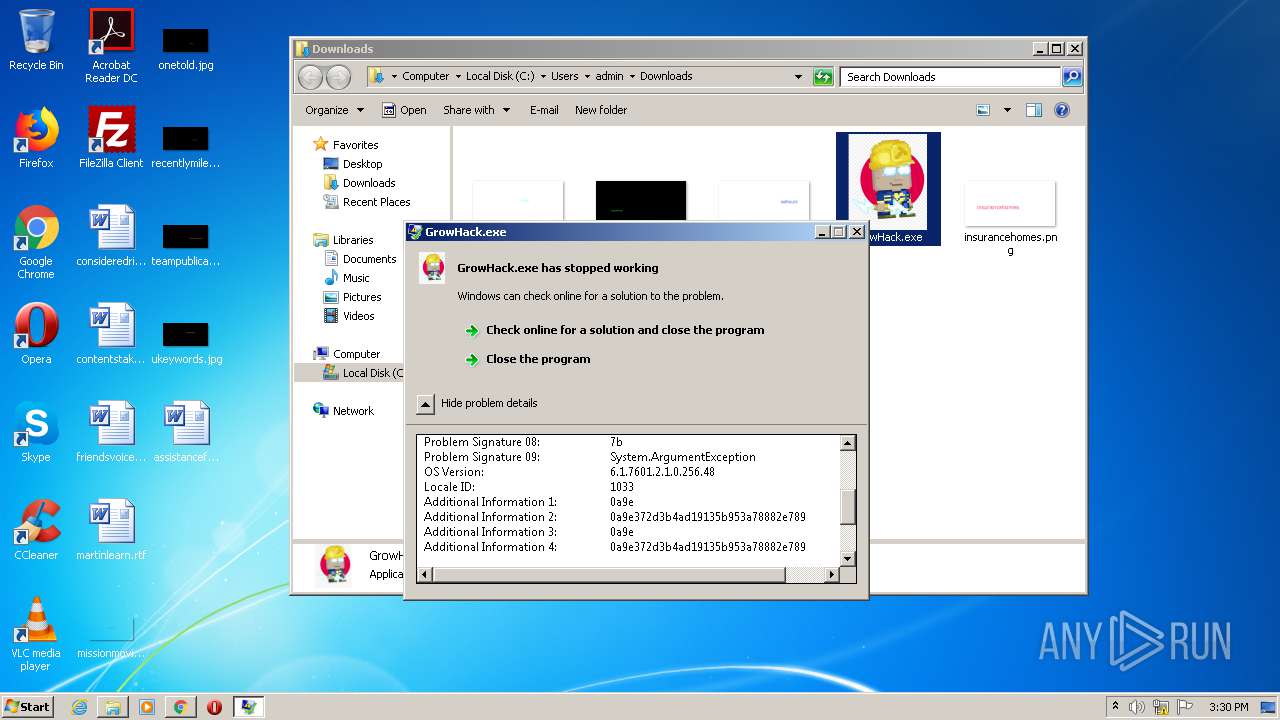
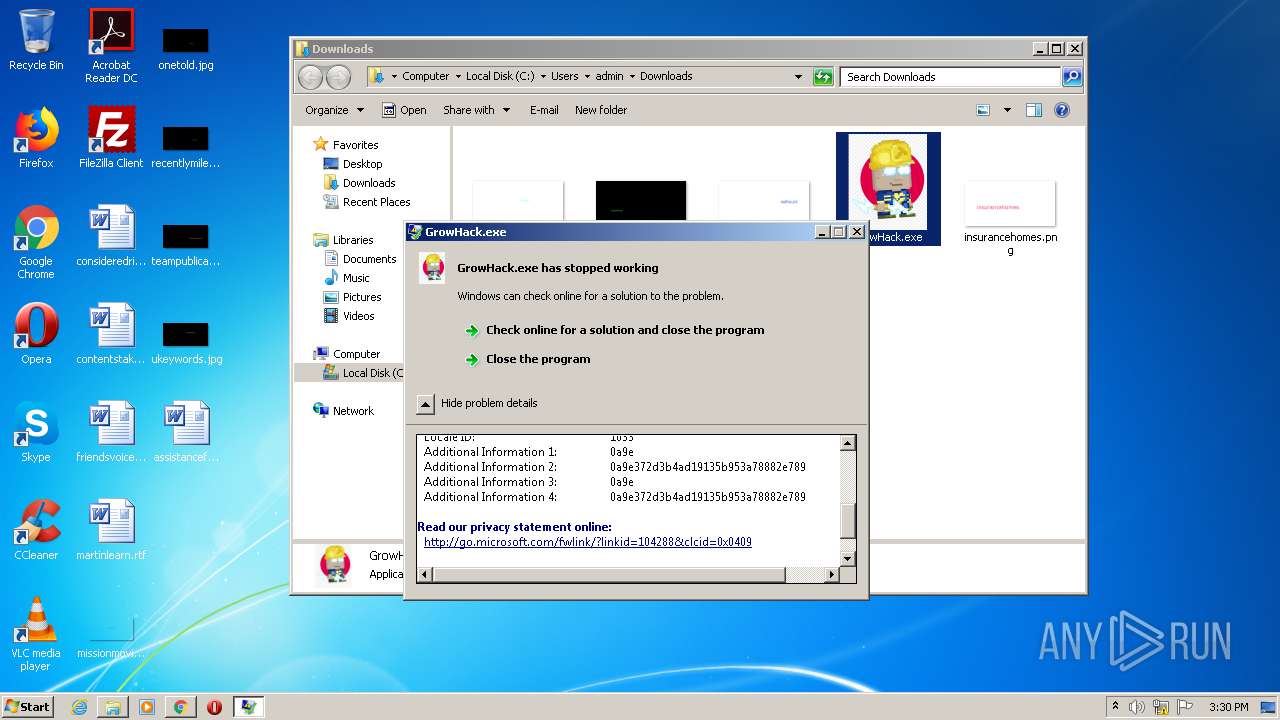
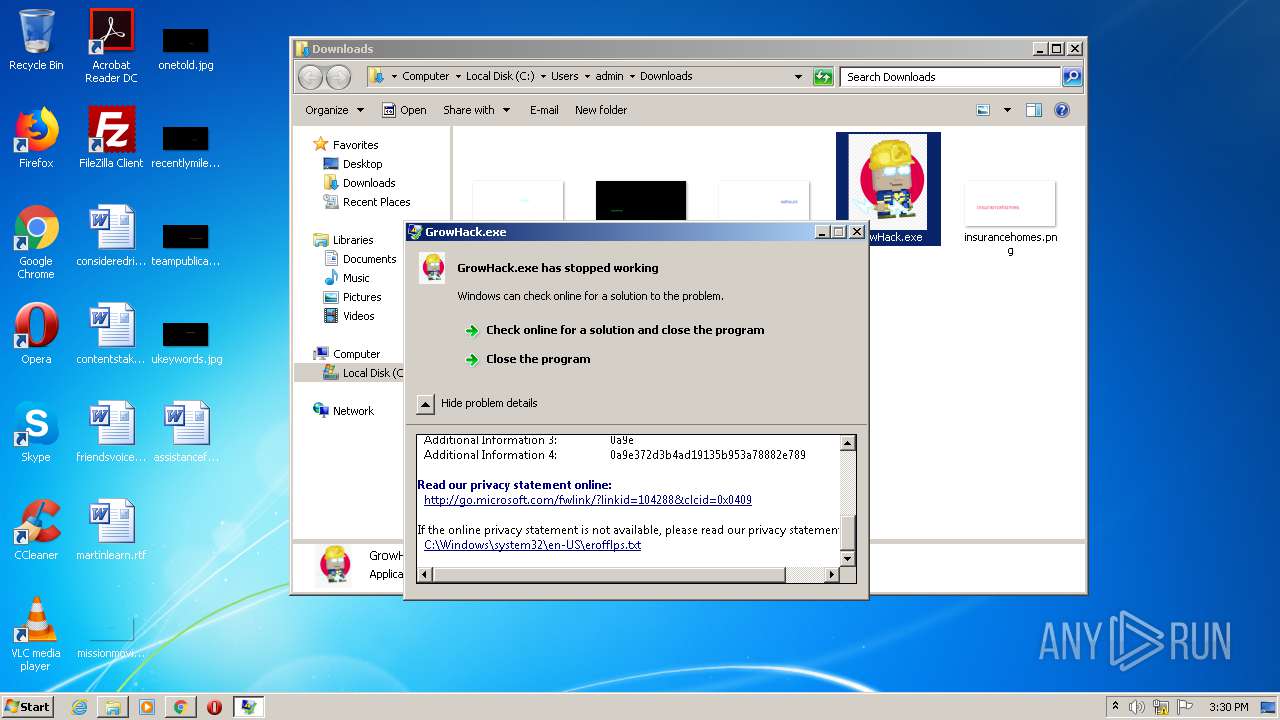
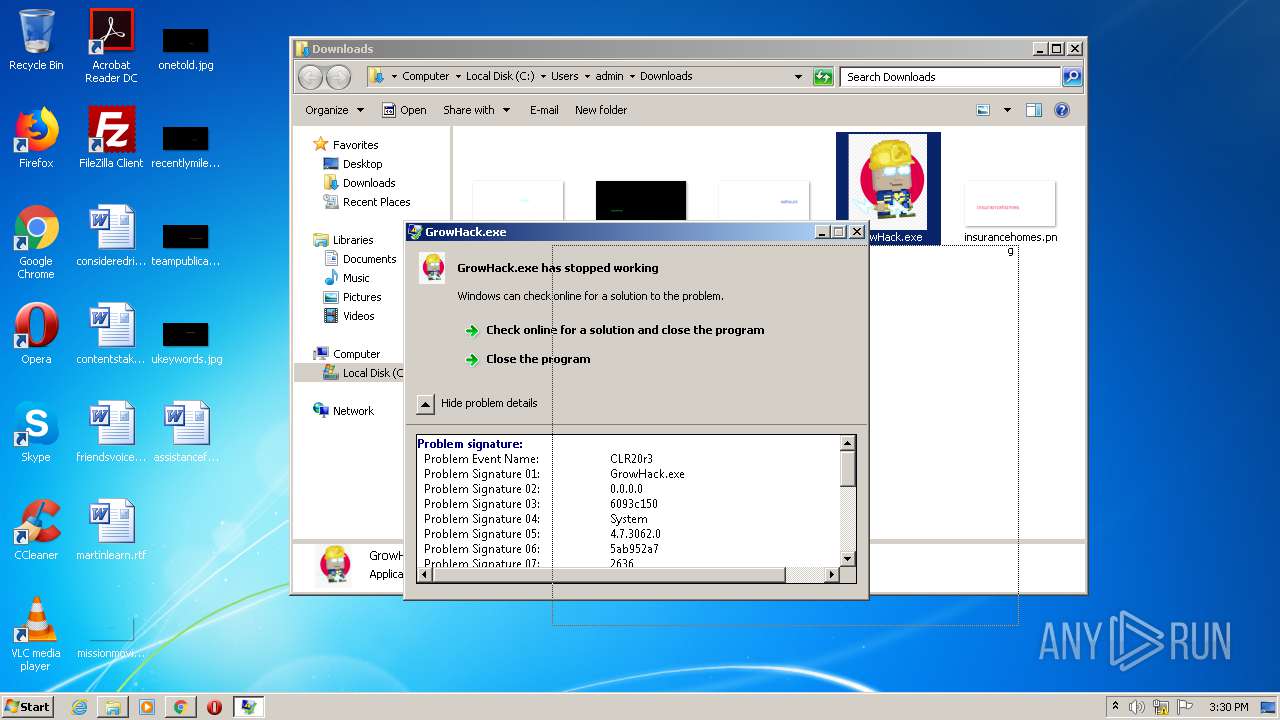
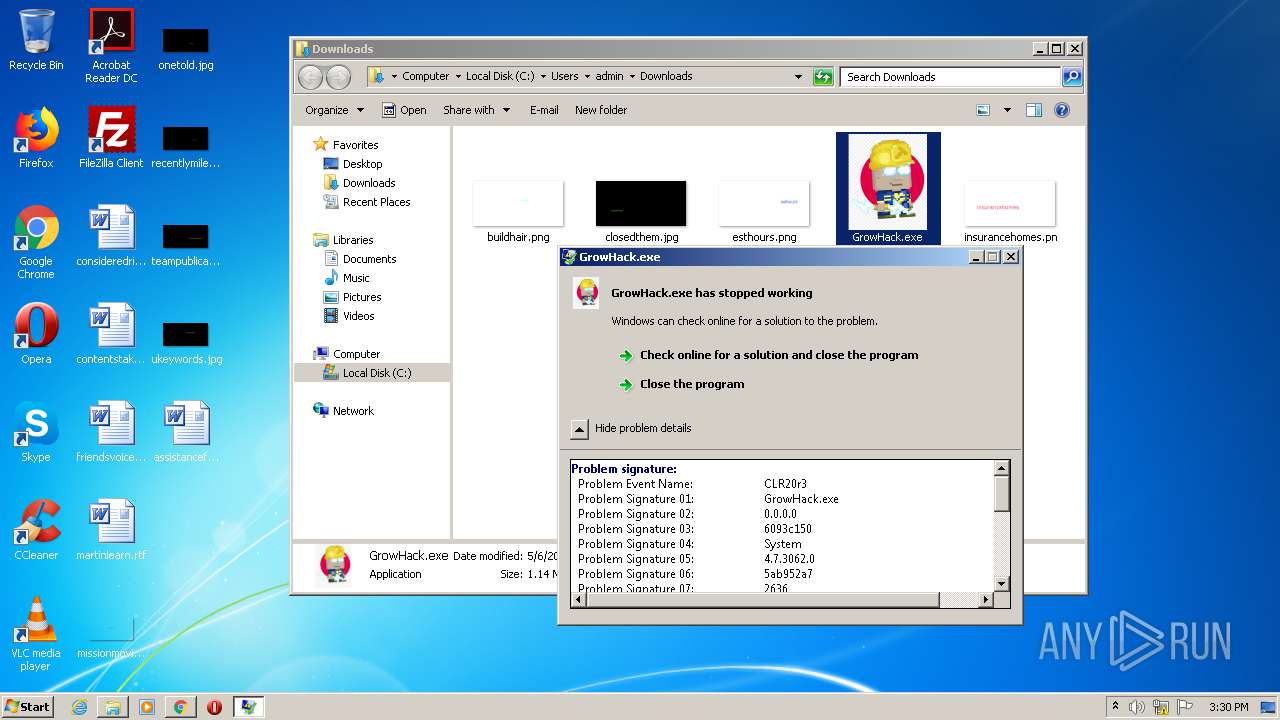
| Verdict: | Malicious activity |
| Analysis date: | May 06, 2021, 14:27:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C24C2A2526AAE5548ADF3010CA6903DC |
| SHA1: | 88D8E87DC0EA6788257233120AF7C3C1B1A25321 |
| SHA256: | 009420FE6043995AC3F1B5D924CDABA32836B9B589FD4E2A9865664843F5DBAC |
| SSDEEP: | 3:N8DSLr7MJmUT4zD5G:2OLr0ag |
MALICIOUS
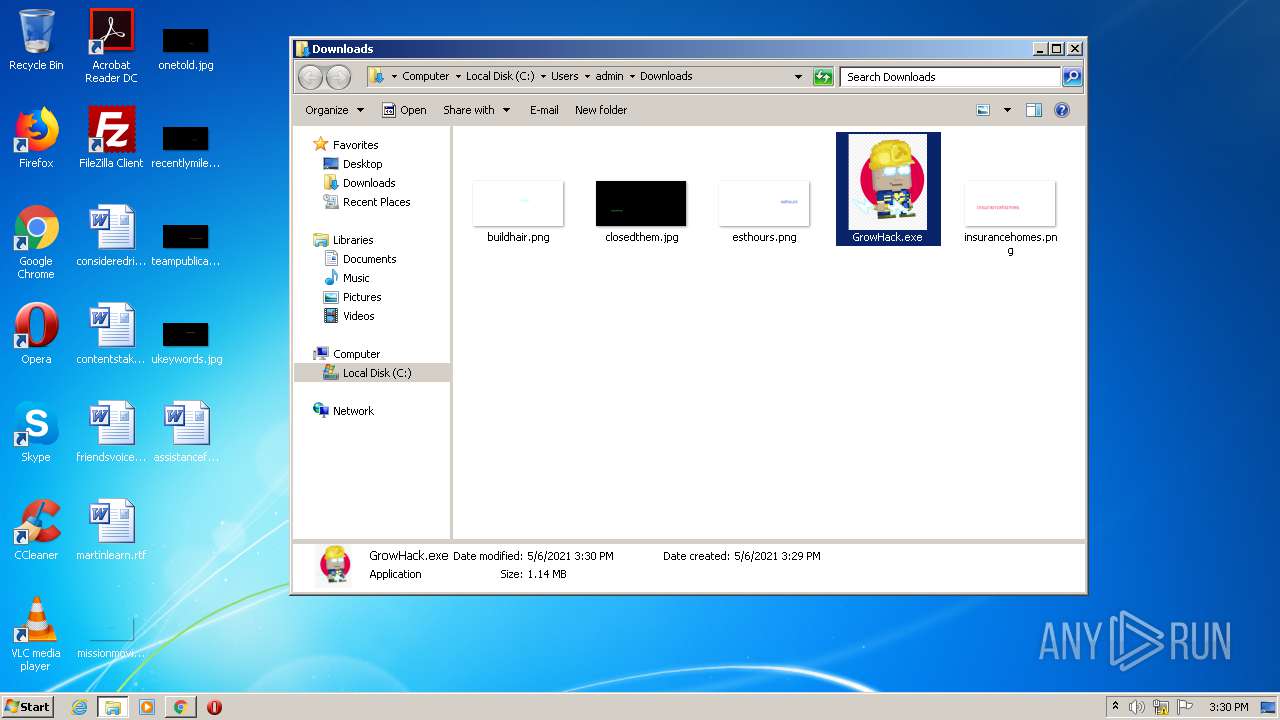
Writes to a start menu file
- GrowHack.exe (PID: 3668)
- GrowHack.exe (PID: 656)
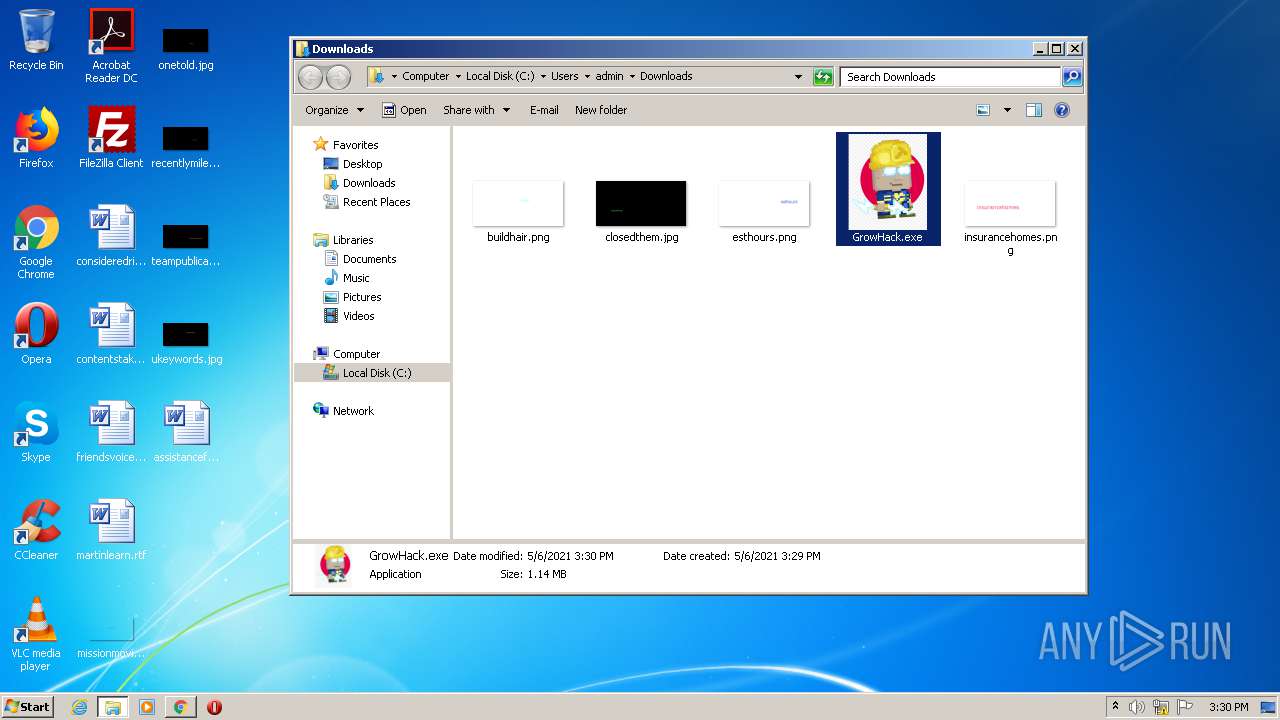
Application was dropped or rewritten from another process
- GrowHack.exe (PID: 656)
- GrowHack.exe (PID: 3668)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3844)
- GrowHack.exe (PID: 3668)
- GrowHack.exe (PID: 656)
Drops a file with a compile date too recent
- chrome.exe (PID: 3844)
- GrowHack.exe (PID: 3668)
- GrowHack.exe (PID: 656)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3844)
Creates files in the user directory
- GrowHack.exe (PID: 3668)
- GrowHack.exe (PID: 656)
INFO
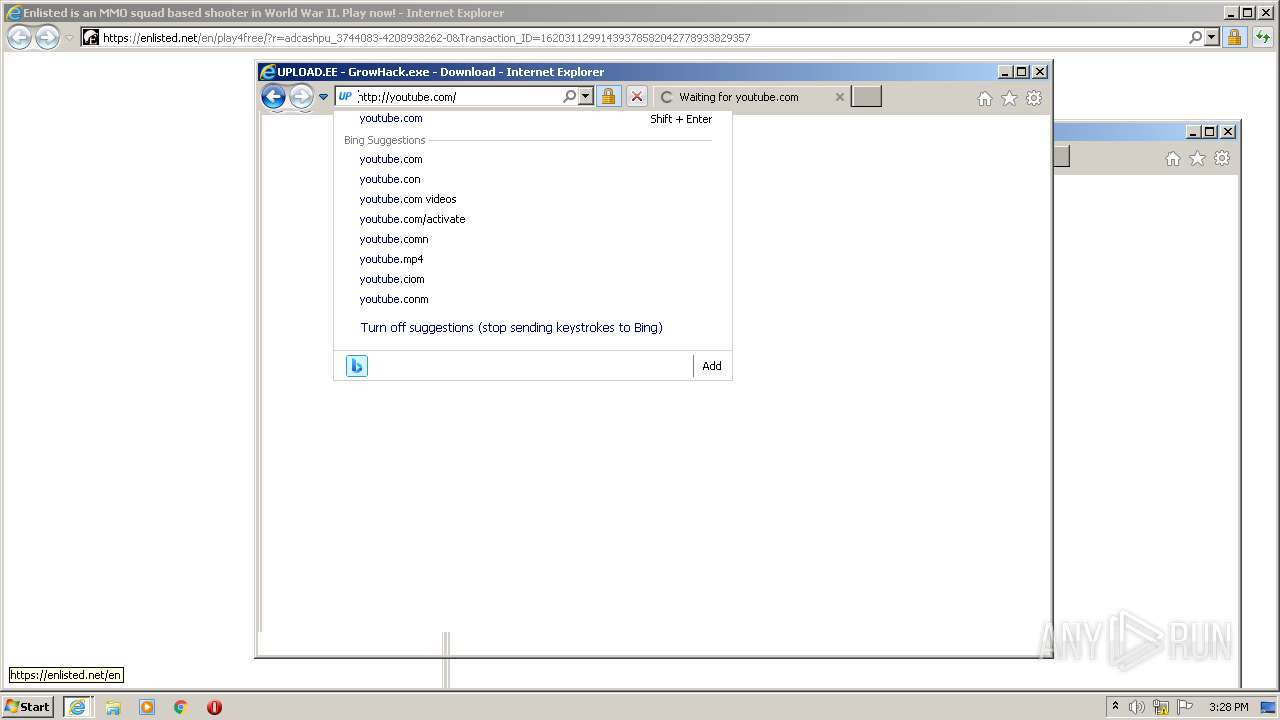
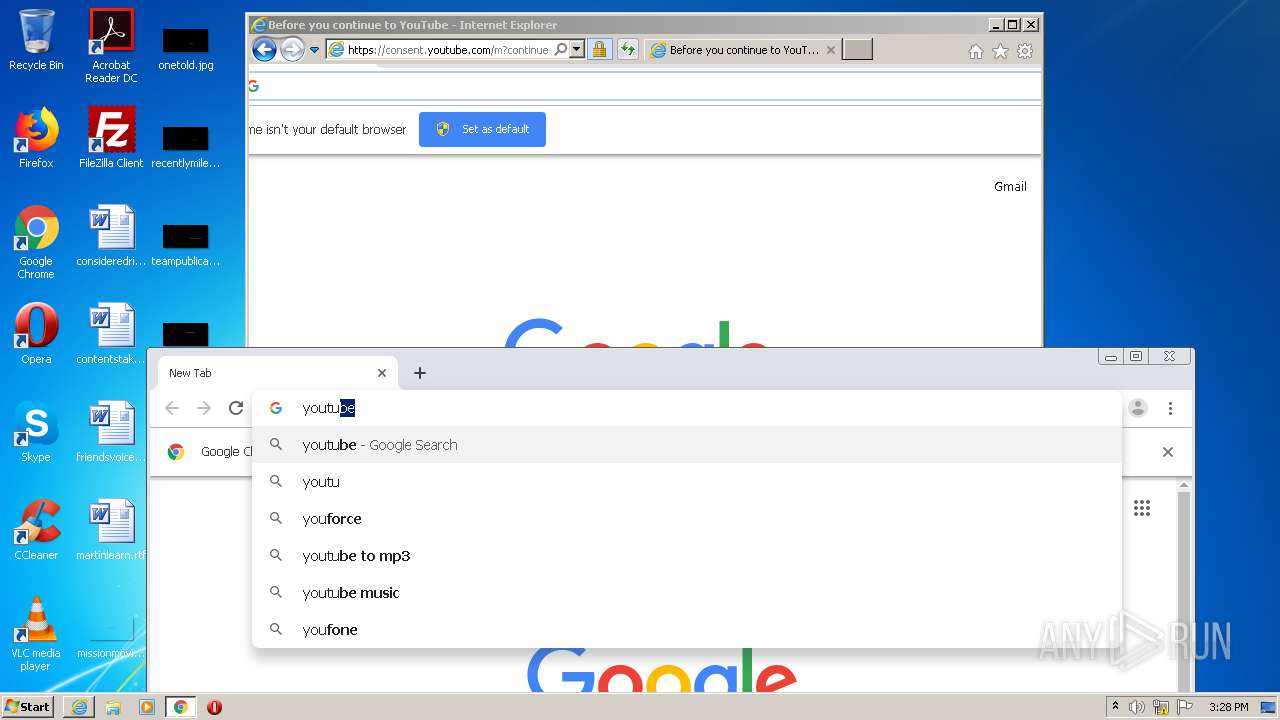
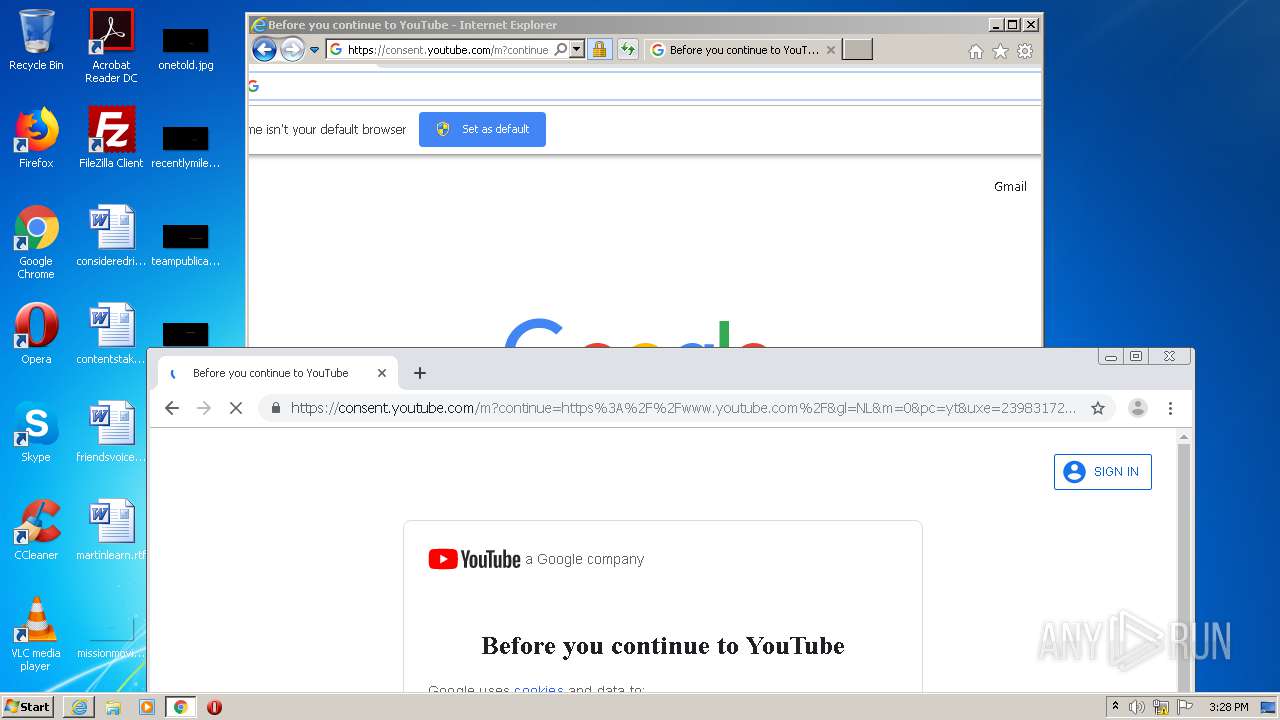
Application launched itself
- iexplore.exe (PID: 560)
- chrome.exe (PID: 3844)
Creates files in the user directory
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 3452)
- iexplore.exe (PID: 560)
- chrome.exe (PID: 3844)
Reads internet explorer settings
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 3452)
Reads settings of System Certificates
- iexplore.exe (PID: 560)
- iexplore.exe (PID: 3452)
- iexplore.exe (PID: 3860)
Changes settings of System certificates
- iexplore.exe (PID: 560)
Adds / modifies Windows certificates
- iexplore.exe (PID: 560)
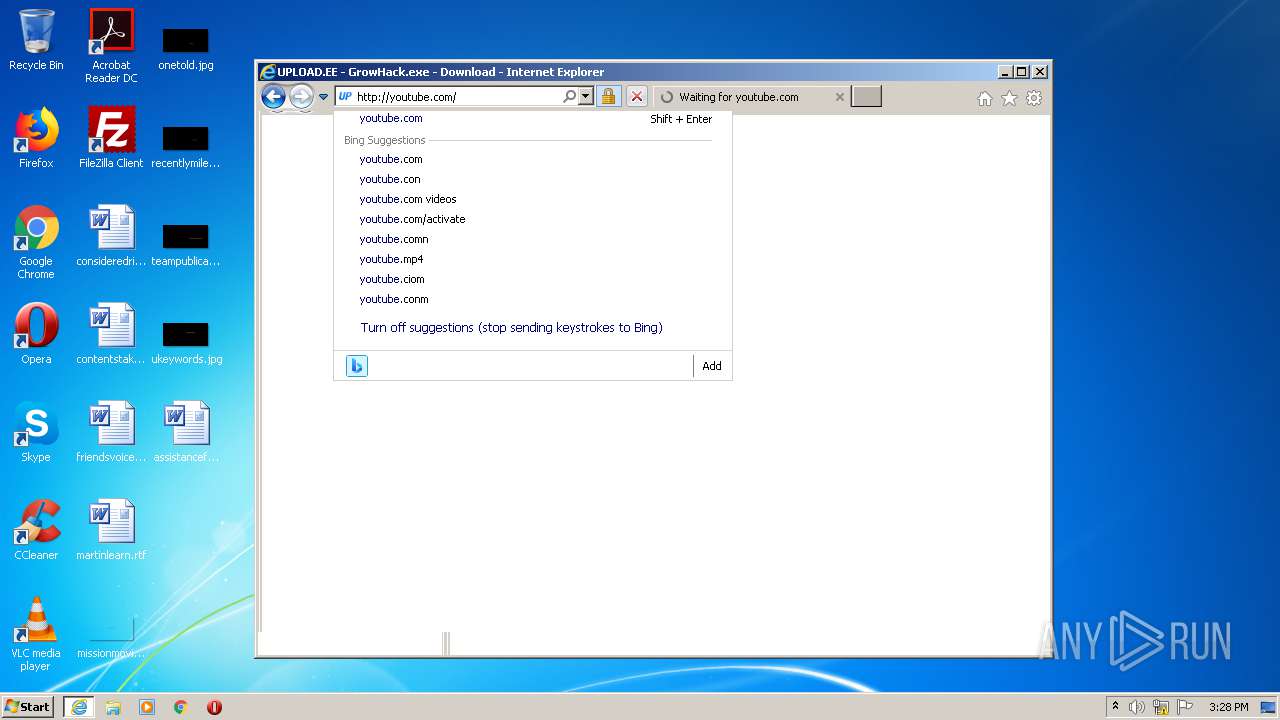
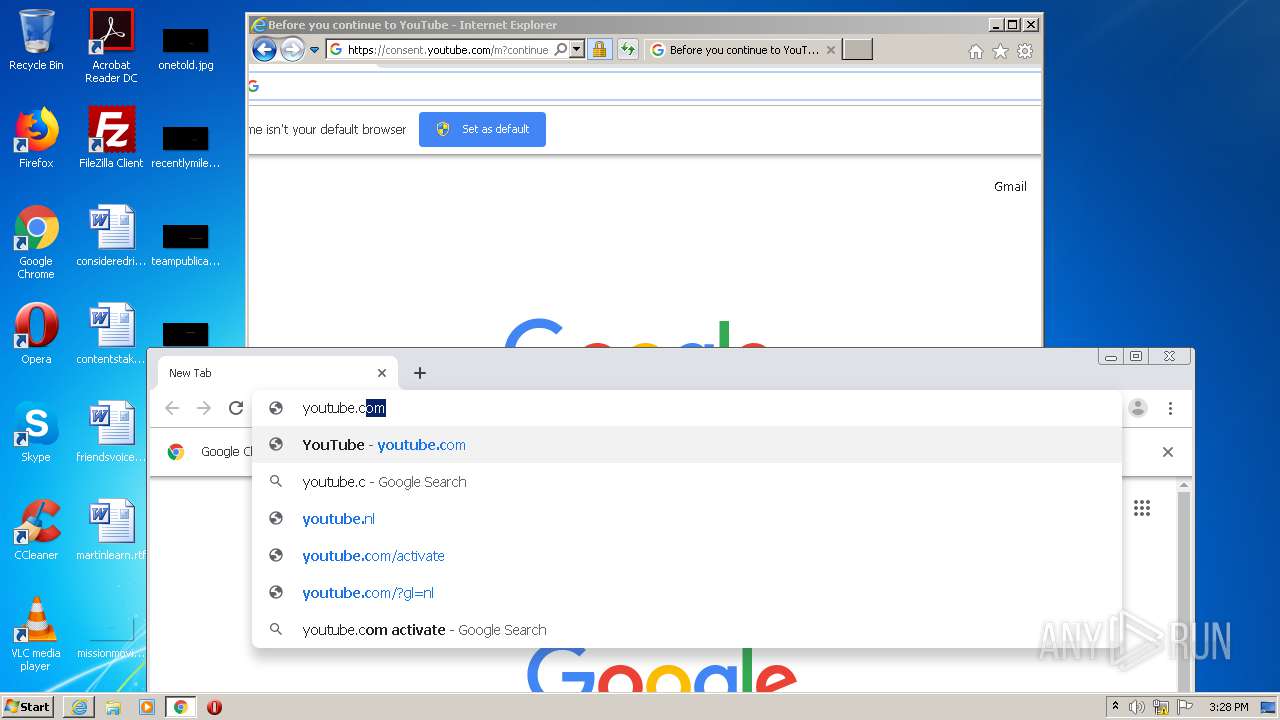
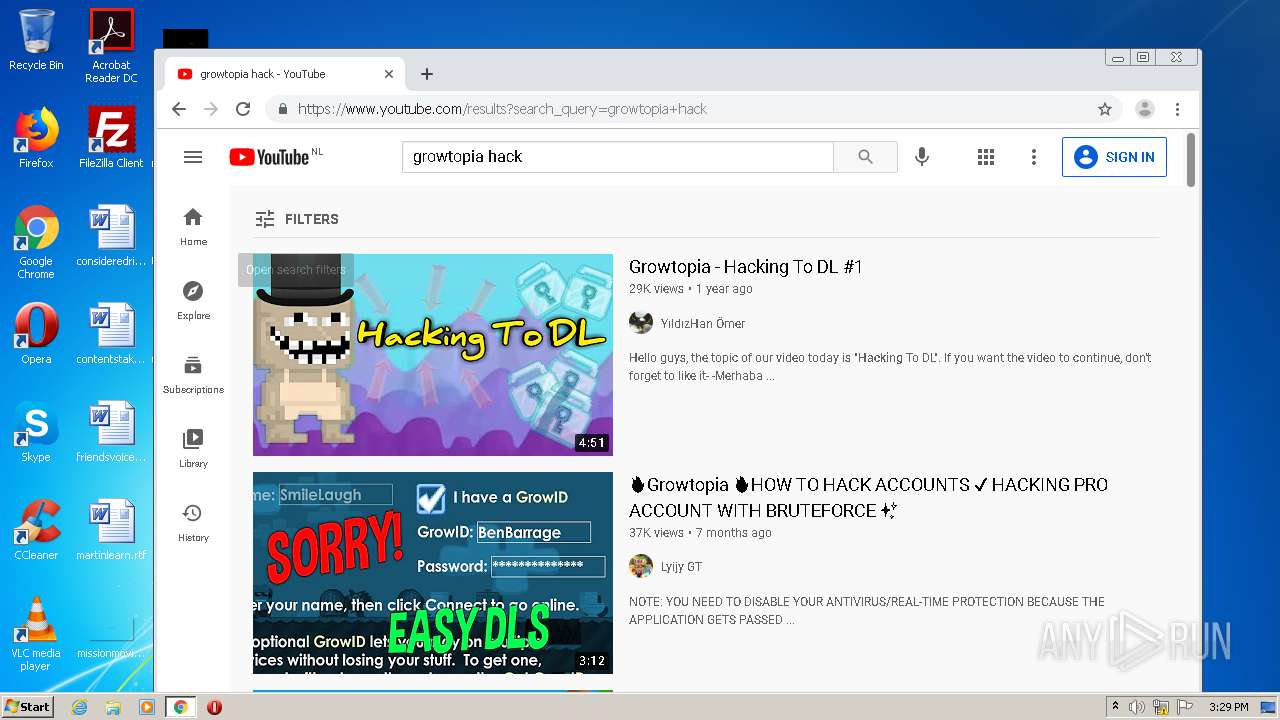
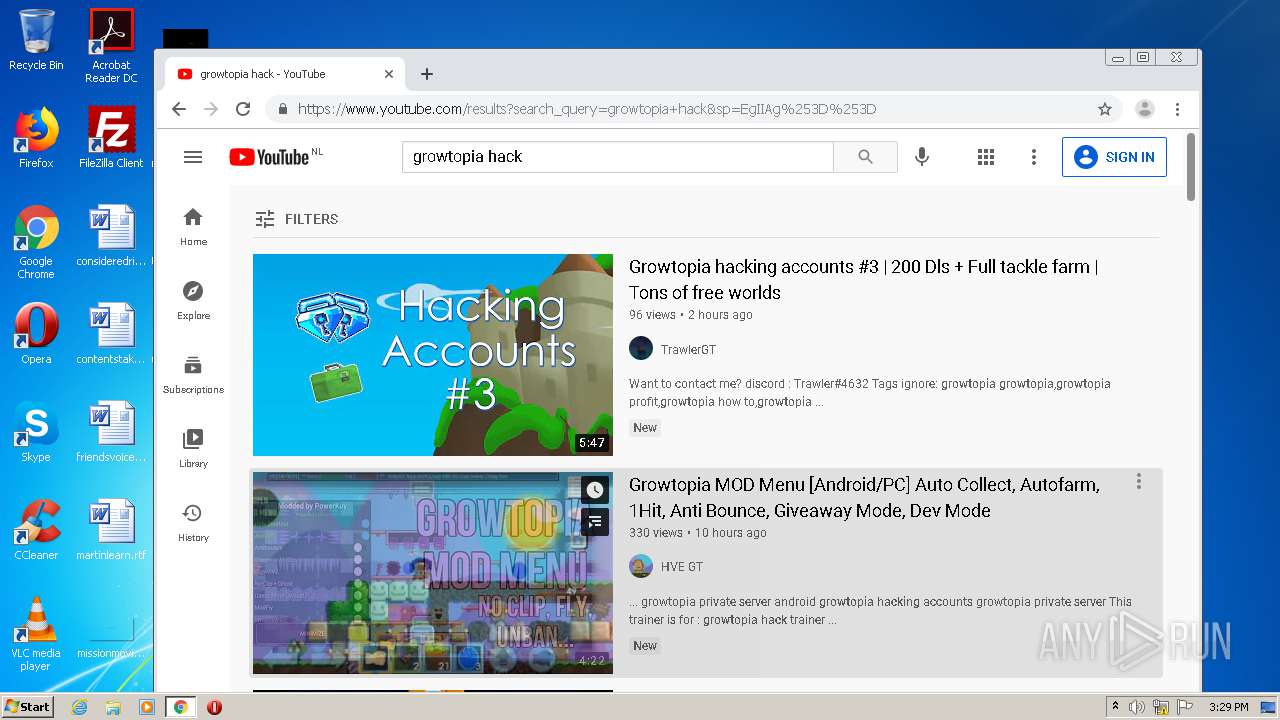
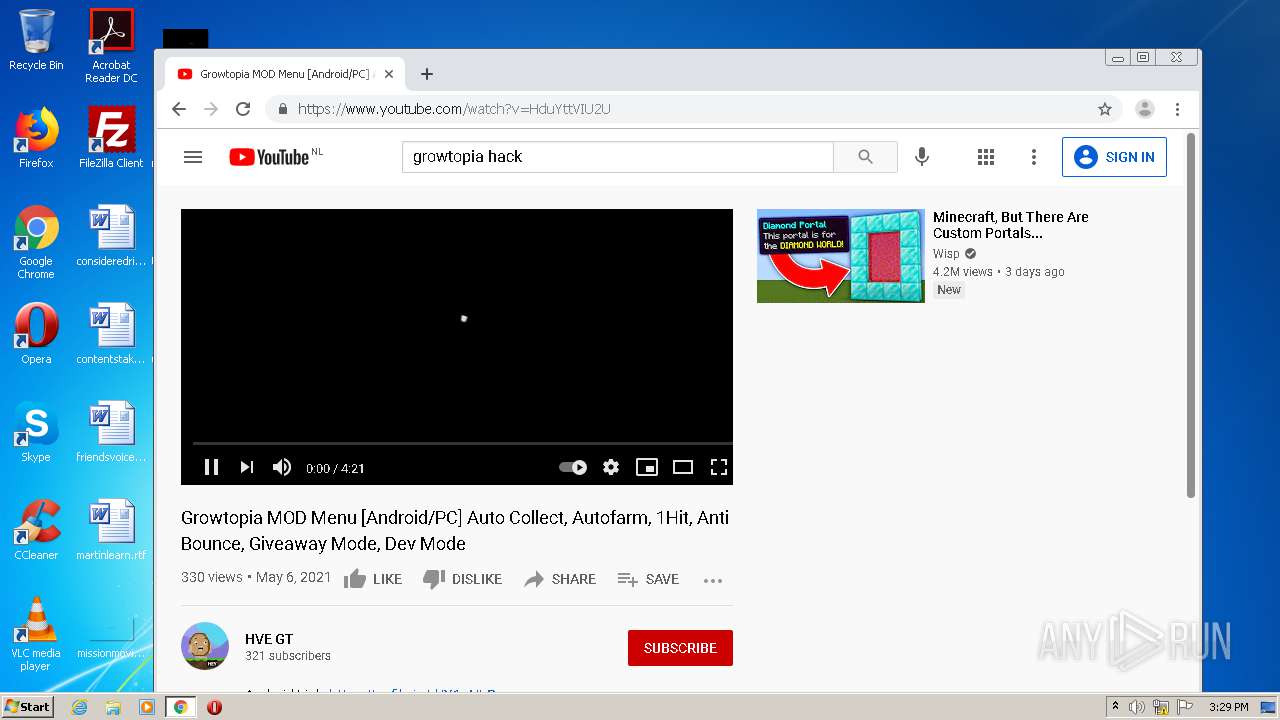
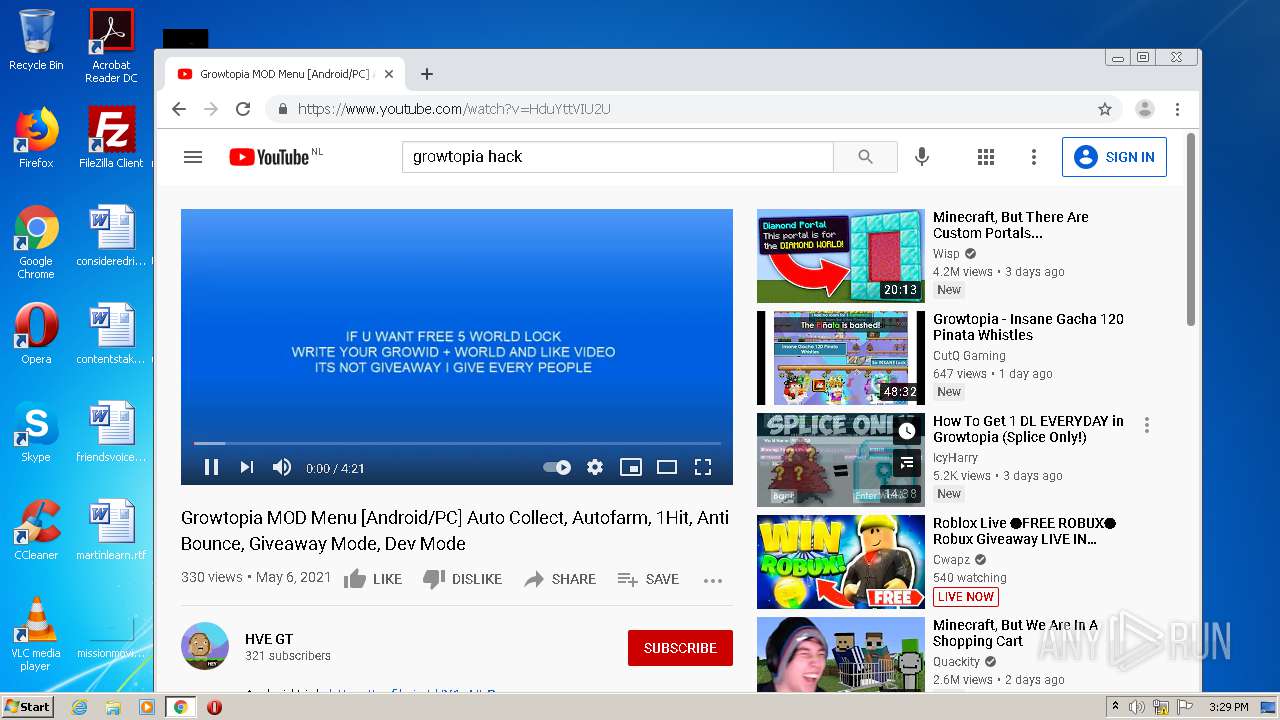
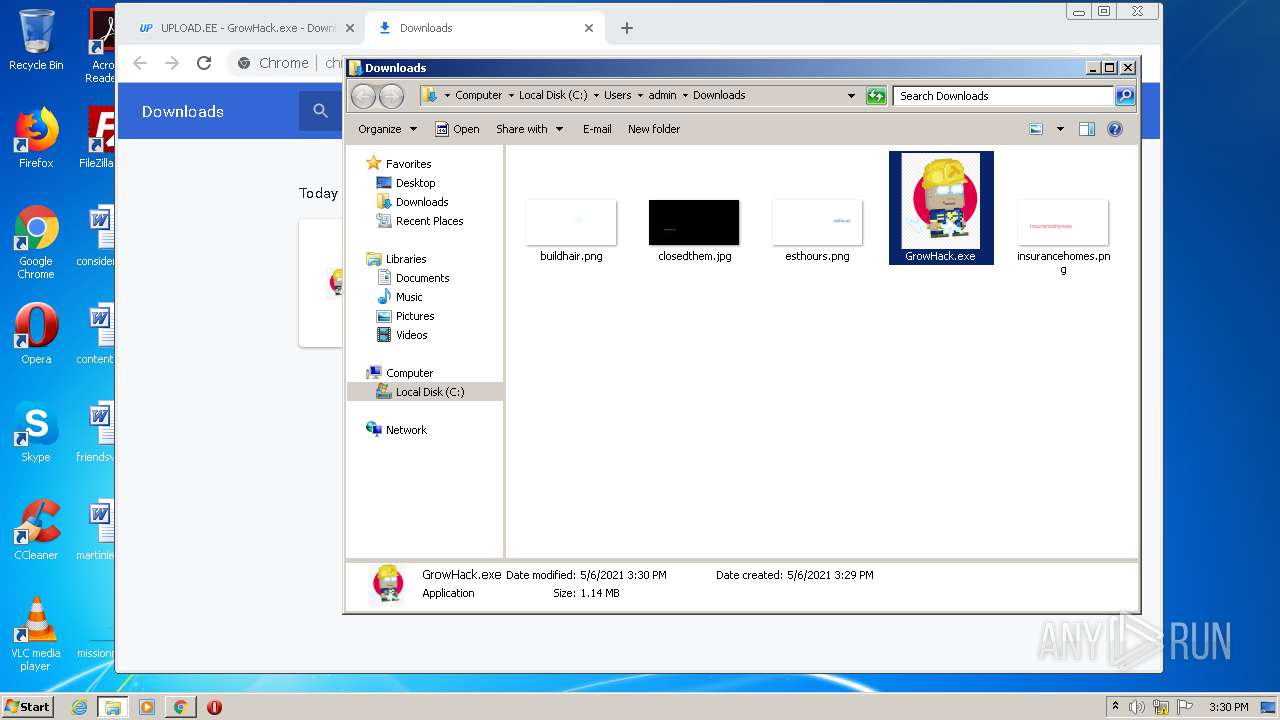
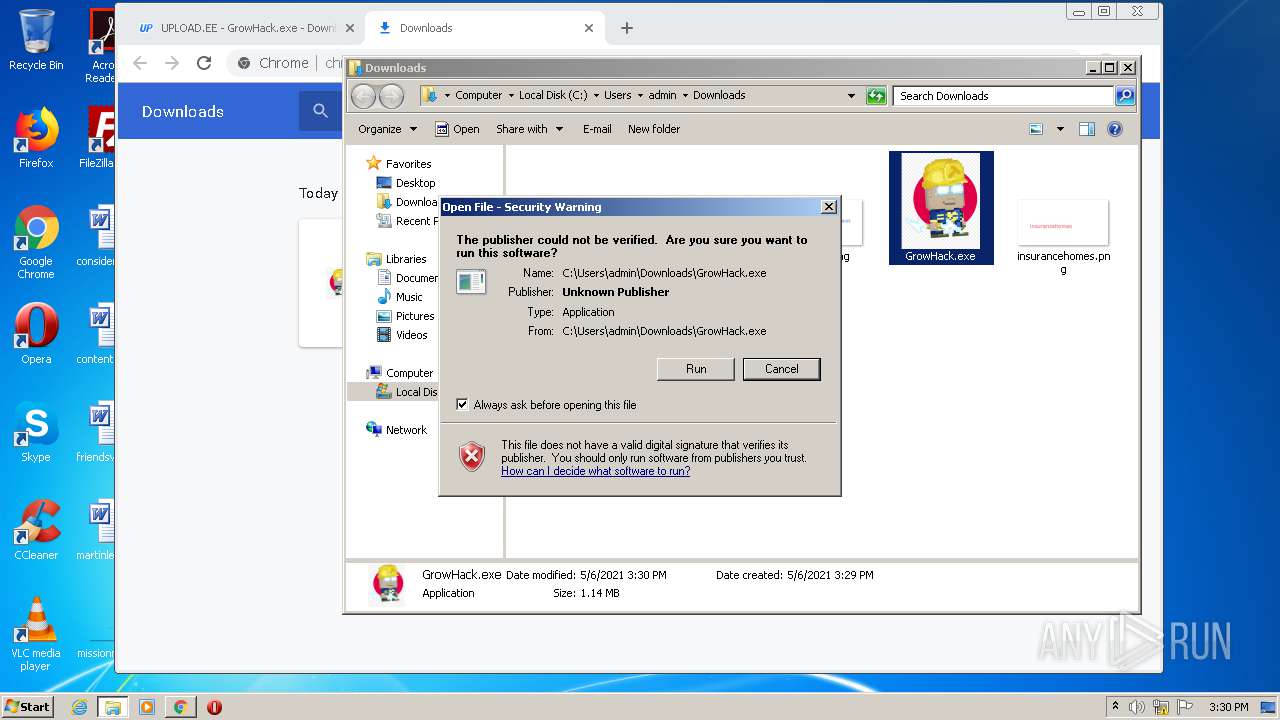
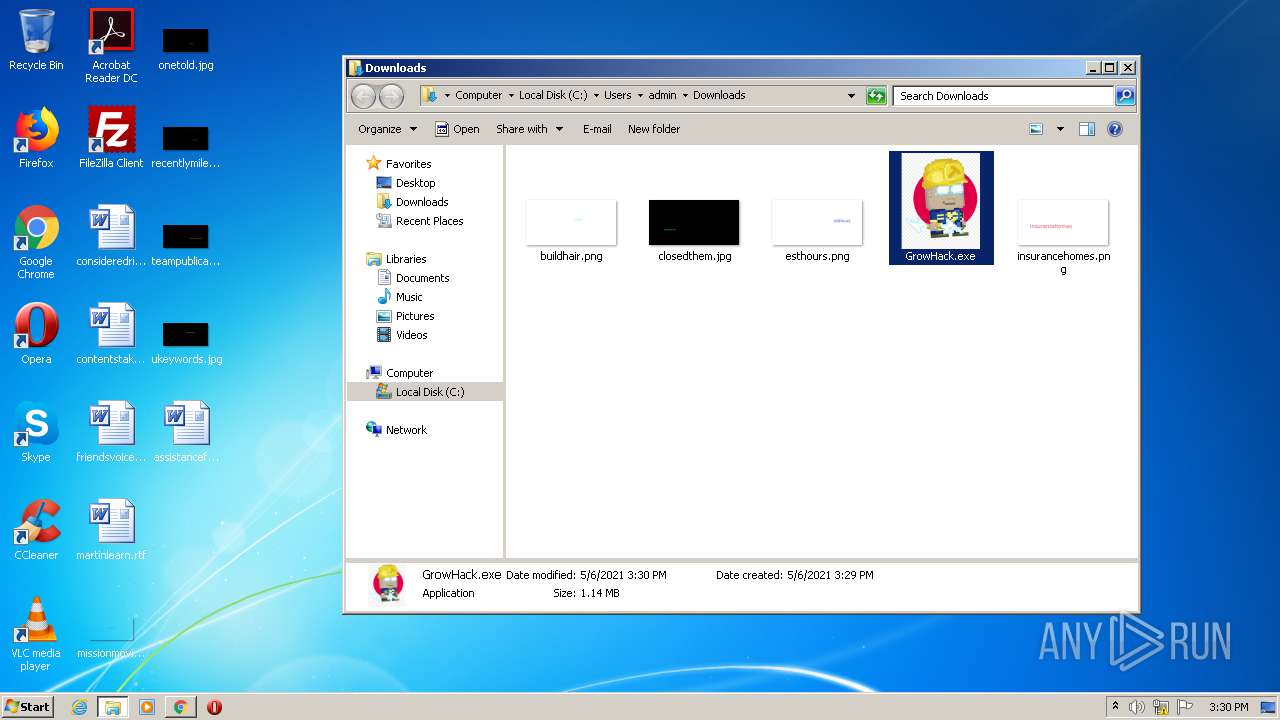
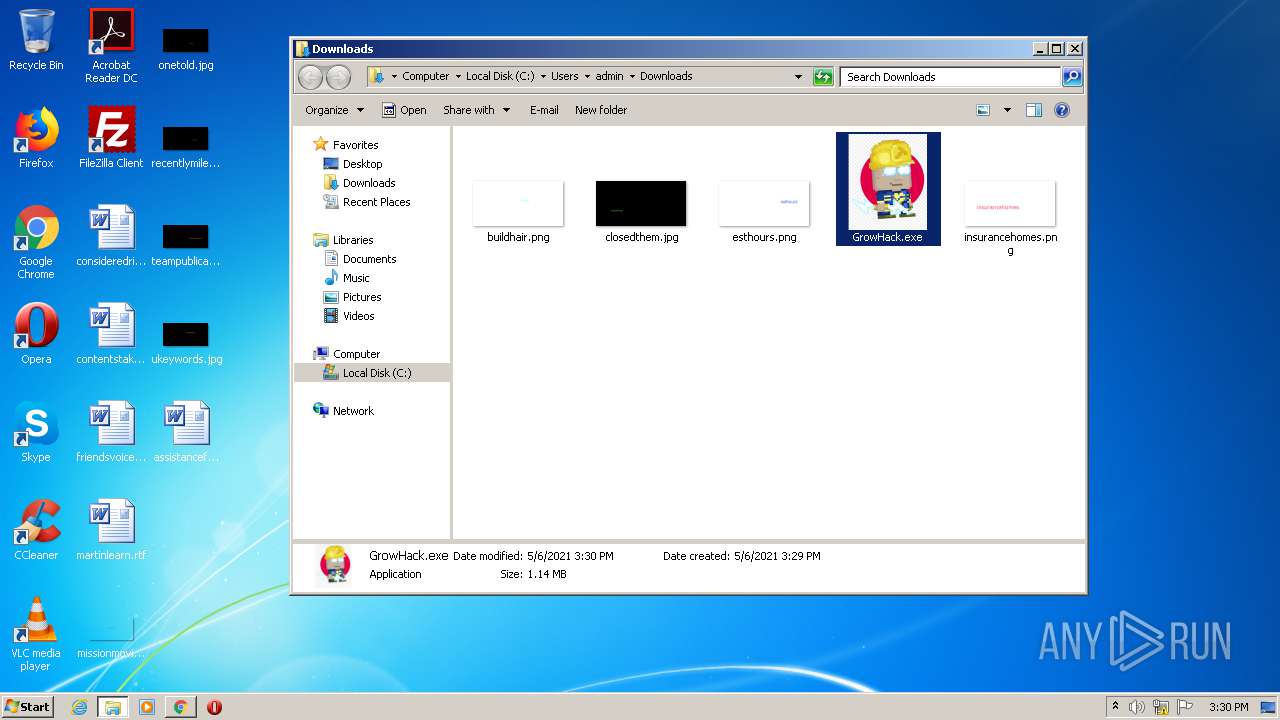
Manual execution by user
- chrome.exe (PID: 3844)
- GrowHack.exe (PID: 3668)
- GrowHack.exe (PID: 656)
Reads the hosts file
- chrome.exe (PID: 3844)
- chrome.exe (PID: 1772)
Changes internet zones settings
- iexplore.exe (PID: 560)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
100
Monitored processes
54
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,5868242538207029839,11103750155888576828,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4993771682677298098 --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4400 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 560 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.upload.ee/files/13118939/GrowHack.exe.html" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,5868242538207029839,11103750155888576828,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13806032505471418723 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4404 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,5868242538207029839,11103750155888576828,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6221792351452387473 --mojo-platform-channel-handle=3772 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,5868242538207029839,11103750155888576828,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4577874378266446864 --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4748 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
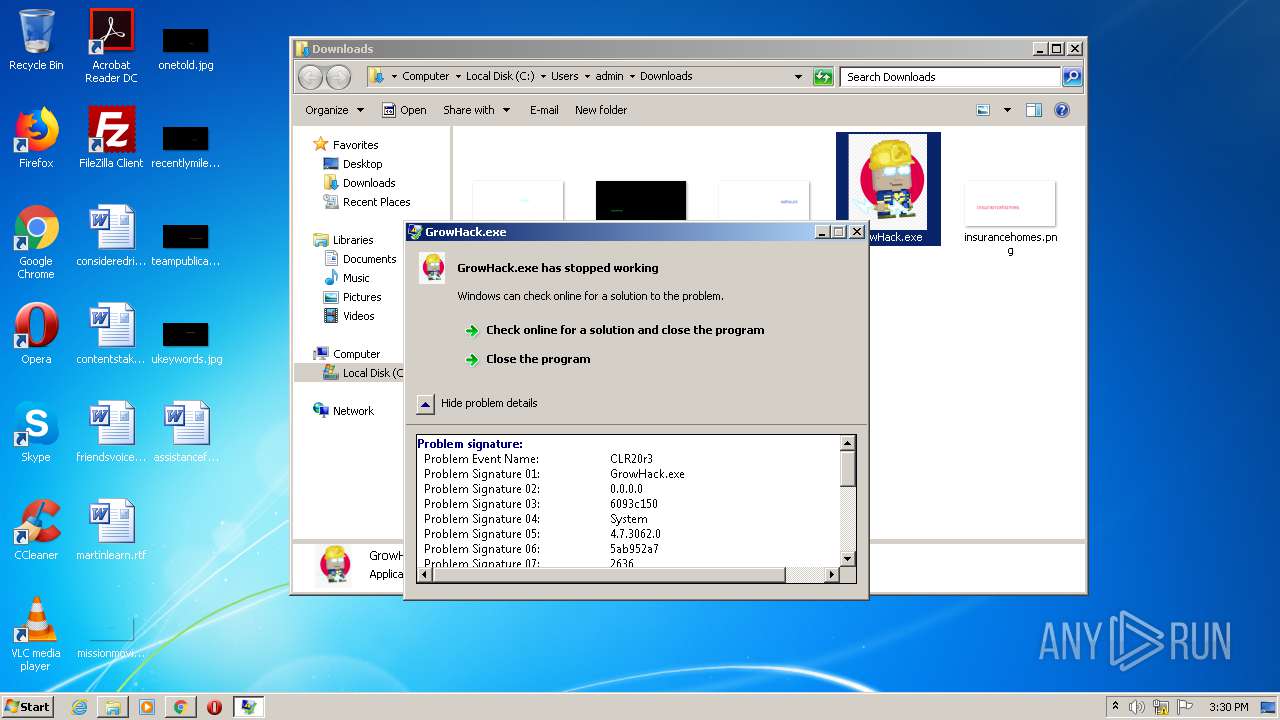
| 656 | "C:\Users\admin\Downloads\GrowHack.exe" | C:\Users\admin\Downloads\GrowHack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 3762504530 Version: 0.0.0.0 Modules
| |||||||||||||||
| 812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,5868242538207029839,11103750155888576828,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6116778550471994280 --mojo-platform-channel-handle=2836 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,5868242538207029839,11103750155888576828,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4826739111415889529 --renderer-client-id=45 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,5868242538207029839,11103750155888576828,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4558312613083655322 --mojo-platform-channel-handle=3440 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,5868242538207029839,11103750155888576828,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12336420172886921147 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 879
Read events
2 414
Write events
455
Delete events
10
Modification events
| (PID) Process: | (560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 4207765782 | |||
| (PID) Process: | (560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30884483 | |||
| (PID) Process: | (560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
6
Suspicious files
235
Text files
489
Unknown types
64
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3860 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab753B.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar753C.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_86C2A03C133240EC4C95180B9FD368BB | der | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\cbb_small[1].jpg | image | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_86C2A03C133240EC4C95180B9FD368BB | binary | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\709A8EC0F6D3194AD001E9041914421F_E172EF98249A059D307448253E7A9453 | der | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\6L3J4UZT.txt | text | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\cbc_small[1].jpg | image | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\GrowHack.exe[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
214
DNS requests
116
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3860 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
560 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQDTLD66ZGKfcbP05RyVd3jJ | US | der | 472 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEDvBKQuWMzhNCQAAAABiFes%3D | US | der | 471 b | whitelisted |
560 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3860 | iexplore.exe | GET | 200 | 95.101.89.75:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgOAg%2BYpRrSvQxYvdZGRicfwjA%3D%3D | unknown | der | 503 b | shared |
3860 | iexplore.exe | GET | 200 | 95.101.89.35:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
3860 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCXZtUP98pi%2BwkAAAAAYhXq | US | der | 472 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 95.101.89.66:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3860 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3860 | iexplore.exe | 104.96.40.109:443 | s7.addthis.com | Akamai Technologies, Inc. | NL | unknown |
3860 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
3860 | iexplore.exe | 184.30.25.161:443 | z.moatads.com | GTT Communications Inc. | US | suspicious |
3860 | iexplore.exe | 142.250.74.194:443 | googleads.g.doubleclick.net | Google Inc. | US | suspicious |
3860 | iexplore.exe | 172.217.16.131:80 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3860 | iexplore.exe | 212.47.222.21:443 | serving.bepolite.eu | Linx Telecommunications B.V. | EE | suspicious |
560 | iexplore.exe | 131.253.33.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3860 | iexplore.exe | 172.67.189.120:443 | superonclick.com | — | US | suspicious |
3860 | iexplore.exe | 172.217.23.98:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.upload.ee |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
www.tradeadexchange.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |